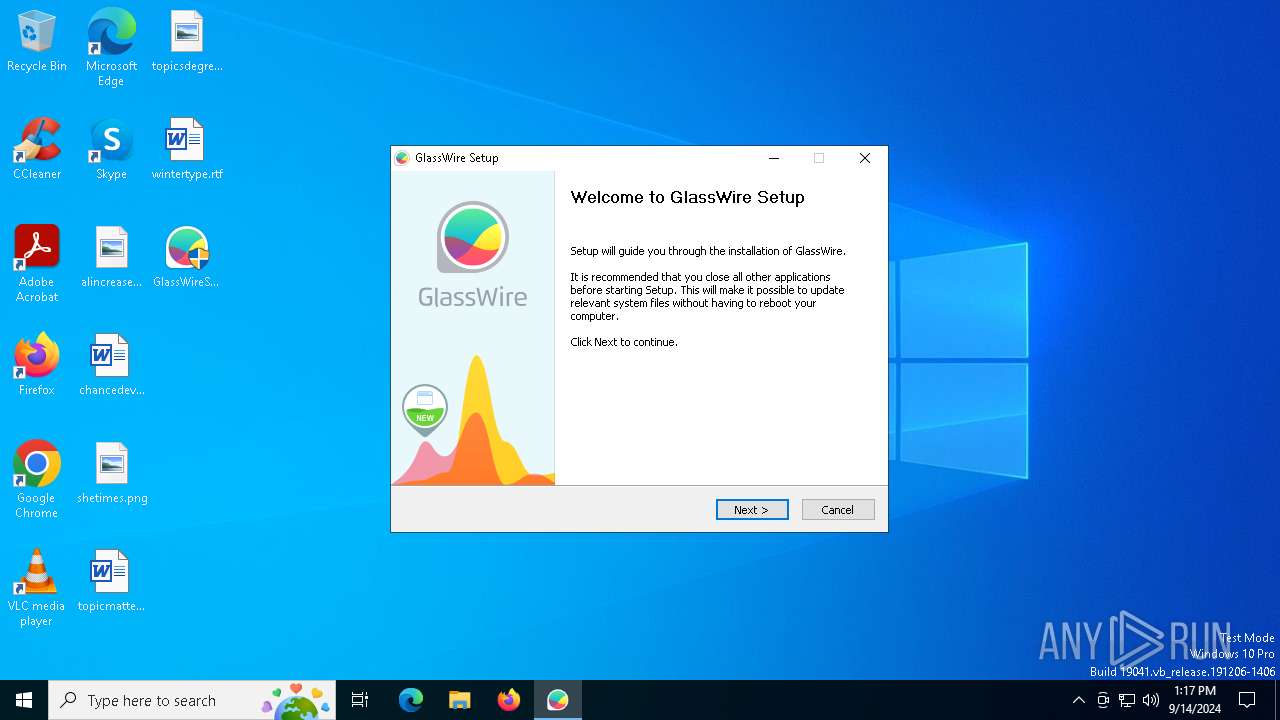
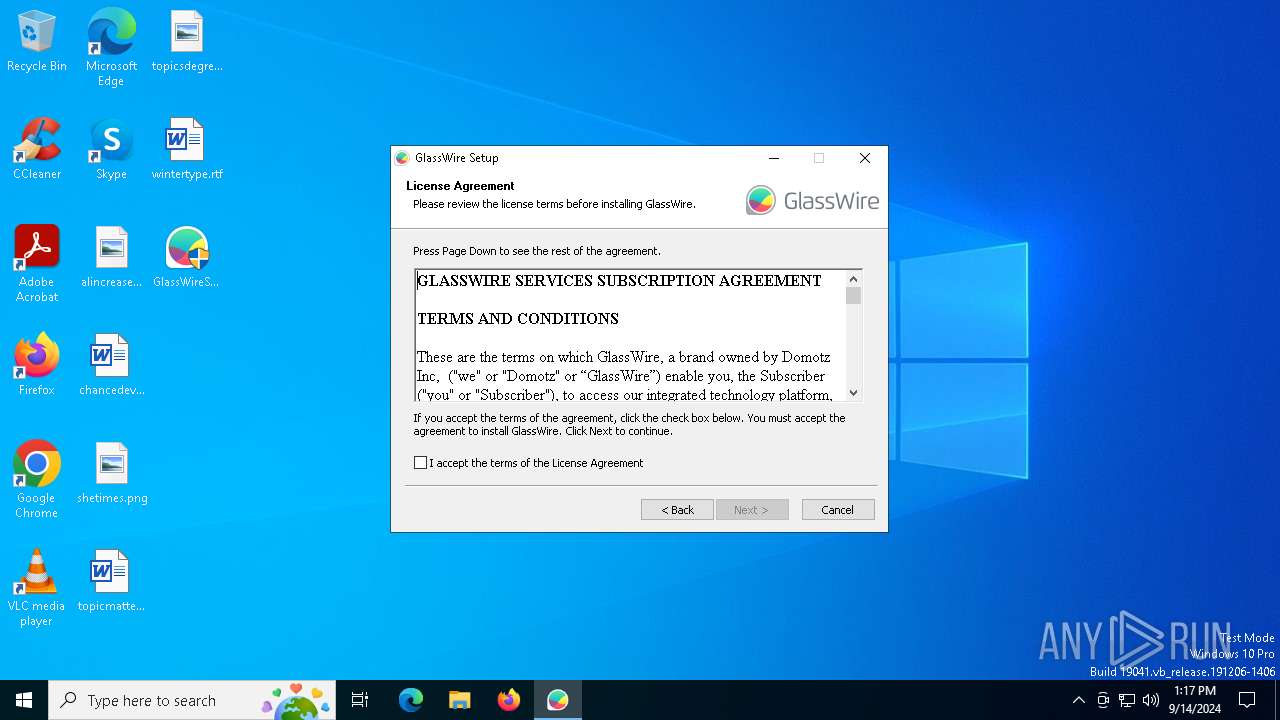
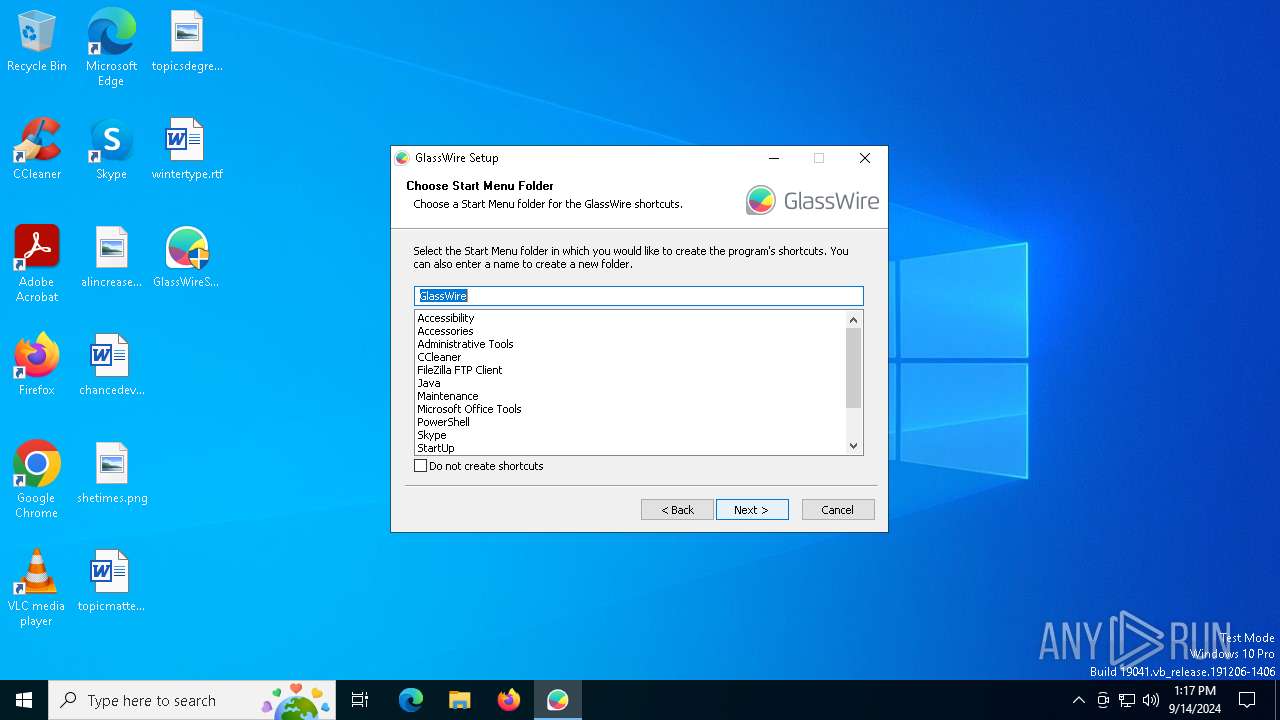
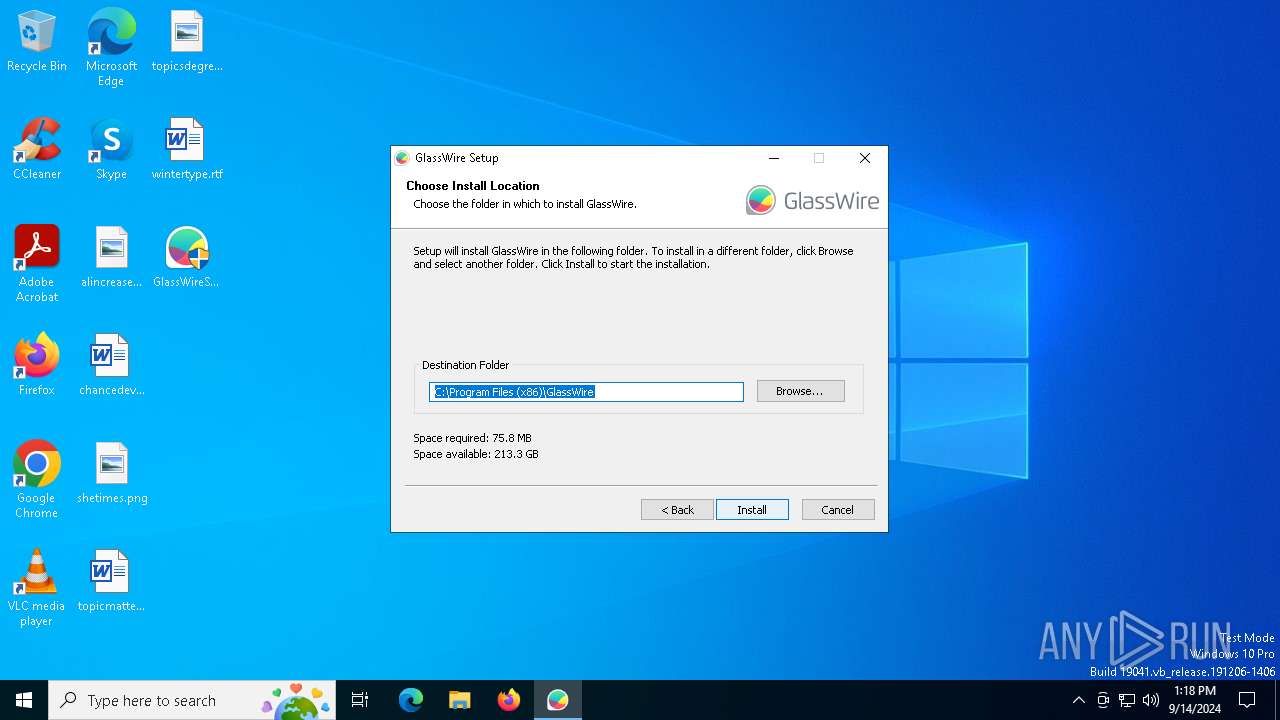
| File name: | GlassWireSetup.exe |
| Full analysis: | https://app.any.run/tasks/40a0e791-2f4f-4ebd-b9c3-0b72d3747898 |
| Verdict: | Malicious activity |
| Analysis date: | September 14, 2024, 13:16:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 334591F1044408785206F65F392115A6 |
| SHA1: | B5CE561415FEE016A40A7255C36837FB28D0A52B |
| SHA256: | 8FFF932C82DF6EB9E5C145C60045E988134948550A50405500A5F17911EE023C |
| SSDEEP: | 786432:M6/jIZT7Xedm9gt8HkQOk6iyO226ViqEnRTUC2dL4D0KH:McIZzedwgqHk5k6X6uiqEnx52FA |
MALICIOUS
Changes the autorun value in the registry
- rundll32.exe (PID: 6500)
- GlassWireSetup.exe (PID: 4008)
Starts NET.EXE for service management
- net.exe (PID: 6140)
- GlassWireSetup.exe (PID: 4008)
SUSPICIOUS
The process creates files with name similar to system file names
- GlassWireSetup.exe (PID: 4008)
Starts a Microsoft application from unusual location
- vc_redist.x86.exe (PID: 2132)
- vc_redist.x86.exe (PID: 2128)
Executable content was dropped or overwritten
- vc_redist.x86.exe (PID: 2132)
- vc_redist.x86.exe (PID: 2128)
- GlassWireSetup.exe (PID: 4008)
- rundll32.exe (PID: 6500)
Searches for installed software
- vc_redist.x86.exe (PID: 2128)
Reads the BIOS version
- GlassWireSetup.exe (PID: 4008)
- GWInstSt.exe (PID: 360)
- GWCtlSrv.exe (PID: 2112)
- GWCtlSrv.exe (PID: 7084)
- GWCtlSrv.exe (PID: 6488)
- GWIdlMon.exe (PID: 3208)
- GlassWire.exe (PID: 6236)
- GWIdlMon.exe (PID: 5540)
Drops a system driver (possible attempt to evade defenses)
- GlassWireSetup.exe (PID: 4008)
Creates files in the driver directory
- GlassWireSetup.exe (PID: 4008)
Reads security settings of Internet Explorer
- GlassWireSetup.exe (PID: 4008)
- GWInstSt.exe (PID: 360)
- GWCtlSrv.exe (PID: 6488)
Checks Windows Trust Settings
- GWInstSt.exe (PID: 360)
Uses RUNDLL32.EXE to load library
- GlassWireSetup.exe (PID: 4008)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- wevtutil.exe (PID: 936)
- GlassWireSetup.exe (PID: 4008)
Creates or modifies Windows services
- GWCtlSrv.exe (PID: 2112)
Executes as Windows Service
- GWCtlSrv.exe (PID: 6488)
Creates a software uninstall entry
- GlassWireSetup.exe (PID: 4008)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 6900)
INFO
Checks supported languages
- vc_redist.x86.exe (PID: 2128)
- GlassWireSetup.exe (PID: 4008)
- vc_redist.x86.exe (PID: 2132)
- GWInstSt.exe (PID: 360)
- GWCtlSrv.exe (PID: 2112)
- GWCtlSrv.exe (PID: 7084)
- GWCtlSrv.exe (PID: 6488)
- GlassWire.exe (PID: 6236)
- GWIdlMon.exe (PID: 5540)
- GWIdlMon.exe (PID: 3208)
Reads the computer name
- vc_redist.x86.exe (PID: 2128)
- GlassWireSetup.exe (PID: 4008)
- GWInstSt.exe (PID: 360)
- GWCtlSrv.exe (PID: 2112)
- GWCtlSrv.exe (PID: 7084)
- GWCtlSrv.exe (PID: 6488)
- GWIdlMon.exe (PID: 3208)
- GlassWire.exe (PID: 6236)
- GWIdlMon.exe (PID: 5540)
Create files in a temporary directory
- vc_redist.x86.exe (PID: 2128)
- GlassWireSetup.exe (PID: 4008)
Creates files in the program directory
- GlassWireSetup.exe (PID: 4008)
- GWCtlSrv.exe (PID: 6488)
Process checks whether UAC notifications are on
- GlassWireSetup.exe (PID: 4008)
- GWInstSt.exe (PID: 360)
- GWCtlSrv.exe (PID: 6488)
- GWCtlSrv.exe (PID: 2112)
- GWCtlSrv.exe (PID: 7084)
Process checks computer location settings
- GlassWireSetup.exe (PID: 4008)
- GWCtlSrv.exe (PID: 6488)
- GlassWire.exe (PID: 6236)
Themida protector has been detected
- GlassWireSetup.exe (PID: 4008)
- GWCtlSrv.exe (PID: 6488)
- GlassWire.exe (PID: 6236)
- GWIdlMon.exe (PID: 5540)
Checks proxy server information
- GWInstSt.exe (PID: 360)
Reads the time zone
- runonce.exe (PID: 2720)
Reads the machine GUID from the registry
- GWInstSt.exe (PID: 360)
- GWCtlSrv.exe (PID: 6488)
Reads the software policy settings
- GWInstSt.exe (PID: 360)
- GWCtlSrv.exe (PID: 6488)
Creates files or folders in the user directory
- GWInstSt.exe (PID: 360)
- GlassWireSetup.exe (PID: 4008)
- GlassWire.exe (PID: 6236)
Reads security settings of Internet Explorer
- runonce.exe (PID: 2720)
- explorer.exe (PID: 4980)
The process uses the downloaded file
- runonce.exe (PID: 2720)
- explorer.exe (PID: 4980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:30 16:55:15+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x351c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.694.0 |
| ProductVersionNumber: | 3.4.694.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | GlassWire |
| FileDescription: | GlassWire Setup |
| FileVersion: | 3,4,694,0 |
| LegalCopyright: | (c) 2024 GlassWire |
| OriginalFileName: | glasswire-setup-3.4.694.0-full.exe |
| ProductName: | GlassWire |
| ProductVersion: | 3,4,694,0 |
Total processes
138
Monitored processes
26
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Users\admin\AppData\Local\Temp\nsjFAE4.tmp\GWInstSt.exe" "https://www.glasswire.com/stat/install.php?v=3.4.694&build_type=full&os=Ten&platform=x64&update=0&install_id=4E445CF9A2FF9C6EBD0BE35E2E703529432868DE020975CE2820473AA700DB41" "nsis$.tmp" | C:\Users\admin\AppData\Local\Temp\nsjFAE4.tmp\GWInstSt.exe | GlassWireSetup.exe | ||||||||||||
User: admin Company: GlassWire Integrity Level: HIGH Description: GlassWire Installation Tools Exit code: 0 Version: 3.4.694.0 Modules
| |||||||||||||||
| 568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | GWIdlMon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | "C:\WINDOWS\system32\wevtutil.exe" im "C:\Users\admin\AppData\Local\Temp\nsjFAE4.tmp\eventlog.man" /rf:"C:\Program Files (x86)\GlassWire\GWEventLog.dll" /mf:"C:\Program Files (x86)\GlassWire\GWEventLog.dll" | C:\Windows\SysWOW64\wevtutil.exe | — | GlassWireSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Eventing Command Line Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | GWIdlMon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2056 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\Desktop\GlassWireSetup.exe" | C:\Users\admin\Desktop\GlassWireSetup.exe | — | explorer.exe | |||||||||||
User: admin Company: GlassWire Integrity Level: MEDIUM Description: GlassWire Setup Exit code: 3221226540 Version: 3,4,694,0 Modules
| |||||||||||||||
| 2112 | "C:\Program Files (x86)\GlassWire\GWCtlSrv.exe" "-i" | C:\Program Files (x86)\GlassWire\GWCtlSrv.exe | — | GlassWireSetup.exe | |||||||||||
User: admin Company: GlassWire Integrity Level: HIGH Description: GlassWire Control Service Exit code: 0 Version: 3.4.694.0 Modules
| |||||||||||||||
| 2128 | "C:\WINDOWS\Temp\{6F04E6E9-0E6E-4C2A-B91F-33AB5C75F8BC}\.cr\vc_redist.x86.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\nsjFAE4.tmp\vc_redist.x86.exe" -burn.filehandle.attached=668 -burn.filehandle.self=676 /install /quiet /norestart | C:\Windows\Temp\{6F04E6E9-0E6E-4C2A-B91F-33AB5C75F8BC}\.cr\vc_redist.x86.exe | vc_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.29.30139 Exit code: 1638 Version: 14.29.30139.0 Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\AppData\Local\Temp\nsjFAE4.tmp\vc_redist.x86.exe" /install /quiet /norestart | C:\Users\admin\AppData\Local\Temp\nsjFAE4.tmp\vc_redist.x86.exe | GlassWireSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.29.30139 Exit code: 1638 Version: 14.29.30139.0 Modules
| |||||||||||||||
| 2264 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | wevtutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 739
Read events
21 615
Write events
100
Delete events
24
Modification events
| (PID) Process: | (4008) GlassWireSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\GlassWire.exe |
| Operation: | write | Name: | DumpFolder |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (4008) GlassWireSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\GlassWire.exe |
| Operation: | write | Name: | DumpType |
Value: 2 | |||
| (PID) Process: | (4008) GlassWireSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\GWCtlSrv.exe |
| Operation: | write | Name: | DumpFolder |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (4008) GlassWireSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\GWCtlSrv.exe |
| Operation: | write | Name: | DumpType |
Value: 2 | |||
| (PID) Process: | (4008) GlassWireSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\GWIdlMon.exe |
| Operation: | write | Name: | DumpFolder |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (4008) GlassWireSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\GWIdlMon.exe |
| Operation: | write | Name: | DumpType |
Value: 2 | |||
| (PID) Process: | (4008) GlassWireSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GlassWire\full |
| Operation: | write | Name: | InstallID |
Value: 4E445CF9A2FF9C6EBD0BE35E2E703529432868DE020975CE2820473AA700DB41 | |||
| (PID) Process: | (4008) GlassWireSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GlassWire\full |
| Operation: | write | Name: | CloudDeviceId |
Value: | |||
| (PID) Process: | (360) GWInstSt.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (360) GWInstSt.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
33
Suspicious files
22
Text files
55
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | GlassWireSetup.exe | C:\Users\admin\AppData\Local\Temp\nsjFAE4.tmp\System.dll | executable | |
MD5:192639861E3DC2DC5C08BB8F8C7260D5 | SHA256:23D618A0293C78CE00F7C6E6DD8B8923621DA7DD1F63A070163EF4C0EC3033D6 | |||
| 2132 | vc_redist.x86.exe | C:\Windows\Temp\{6F04E6E9-0E6E-4C2A-B91F-33AB5C75F8BC}\.cr\vc_redist.x86.exe | executable | |
MD5:29C7A21BAE42889B08137C25AAE8E55C | SHA256:82612A2FA05D62929833052CE76788B98701F0C19DCA313923452AFEC44EDEC5 | |||
| 2128 | vc_redist.x86.exe | C:\Windows\Temp\{C4BB9EC0-136A-4A57-B658-C19F67C12A6F}\.ba\license.rtf | text | |
MD5:2EABBB391ACB89942396DF5C1CA2BAD8 | SHA256:E3156D170014CED8D17A02B3C4FF63237615E5C2A8983B100A78CB1F881D6F38 | |||
| 4008 | GlassWireSetup.exe | C:\Users\admin\AppData\Local\Temp\nsjFAE4.tmp\GWInstSt.exe | executable | |
MD5:63DC9E4A693261F14924D8692D2EB442 | SHA256:83861D09519D18D5050B996CF1E7D99577EA0E5D9D34F1BC4AC90CD985DA8969 | |||
| 2128 | vc_redist.x86.exe | C:\Windows\Temp\{C4BB9EC0-136A-4A57-B658-C19F67C12A6F}\.ba\logo.png | image | |
MD5:D6BD210F227442B3362493D046CEA233 | SHA256:335A256D4779EC5DCF283D007FB56FD8211BBCAF47DCD70FE60DED6A112744EF | |||
| 2128 | vc_redist.x86.exe | C:\Windows\Temp\{C4BB9EC0-136A-4A57-B658-C19F67C12A6F}\.ba\thm.xml | xml | |
MD5:F62729C6D2540015E072514226C121C7 | SHA256:F13BAE0EC08C91B4A315BB2D86EE48FADE597E7A5440DCE6F751F98A3A4D6916 | |||
| 4008 | GlassWireSetup.exe | C:\Users\admin\AppData\Local\Temp\nsjFAE4.tmp\nsihelper.dll | executable | |
MD5:E66D698421B463011B570FDF253478FF | SHA256:03FB90CA99BF6CF9808DA0E473897F7D8DCDDDEBB1CB1515B8BBBB090AEE39CD | |||
| 2128 | vc_redist.x86.exe | C:\Windows\Temp\{C4BB9EC0-136A-4A57-B658-C19F67C12A6F}\.ba\thm.wxl | xml | |
MD5:FBFCBC4DACC566A3C426F43CE10907B6 | SHA256:70400F181D00E1769774FF36BCD8B1AB5FBC431418067D31B876D18CC04EF4CE | |||
| 2128 | vc_redist.x86.exe | C:\Windows\Temp\{C4BB9EC0-136A-4A57-B658-C19F67C12A6F}\.ba\1028\thm.wxl | xml | |
MD5:472ABBEDCBAD24DBA5B5F5E8D02C340F | SHA256:8E2E660DFB66CB453E17F1B6991799678B1C8B350A55F9EBE2BA0028018A15AD | |||
| 2128 | vc_redist.x86.exe | C:\Windows\Temp\{C4BB9EC0-136A-4A57-B658-C19F67C12A6F}\.ba\1028\license.rtf | text | |
MD5:B7F65A3A169484D21FA075CCA79083ED | SHA256:32585B93E69272B6D42DAC718E04D954769FE31AC9217C6431510E9EEAD78C49 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
37
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
568 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 65.9.95.11:443 | https://www.glasswire.com/stat/install.php?v=3.4.694&build_type=full&os=Ten&platform=x64&update=0&install_id=4E445CF9A2FF9C6EBD0BE35E2E703529432868DE020975CE2820473AA700DB41 | unknown | — | — | unknown |
— | — | POST | 204 | 18.116.193.64:443 | https://api-us-east-2.protect.glasswire.com/endpoint-api/v1/endpoint/448637d5-8bd0-4c07-b0ae-cedcbd330565/heartbeat/3.4.694?s=3&l=Free&c=&i=IWu1h9&p=wELnsf&a= | unknown | — | — | unknown |
— | — | GET | 302 | 65.9.95.27:443 | https://www.glasswire.com/suspicious/update/?v=0&gzip=1 | unknown | — | — | unknown |
— | — | POST | 200 | 3.135.4.85:443 | https://api-us-east-2.protect.glasswire.com/api/v1.1/agent/detect/batch | unknown | binary | 1.07 Kb | unknown |
— | — | POST | 200 | 3.135.4.85:443 | https://api-us-east-2.protect.glasswire.com/api/v1.1/agent/device/register | unknown | binary | 45 b | unknown |
— | — | POST | 401 | 3.128.117.159:443 | https://api-us-east-2.protect.glasswire.com/endpoint-api/v1/endpoint/448637d5-8bd0-4c07-b0ae-cedcbd330565/heartbeat/3.4.694?s=1&l=Free&c=&i=LGw1ab&p=De7ajf&a= | unknown | binary | 63 b | unknown |
— | — | GET | 200 | 3.135.4.85:443 | https://api-us-east-2.protect.glasswire.com/api/v1.1/unauthenticated-token/448637d5-8bd0-4c07-b0ae-cedcbd330565 | unknown | binary | 872 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
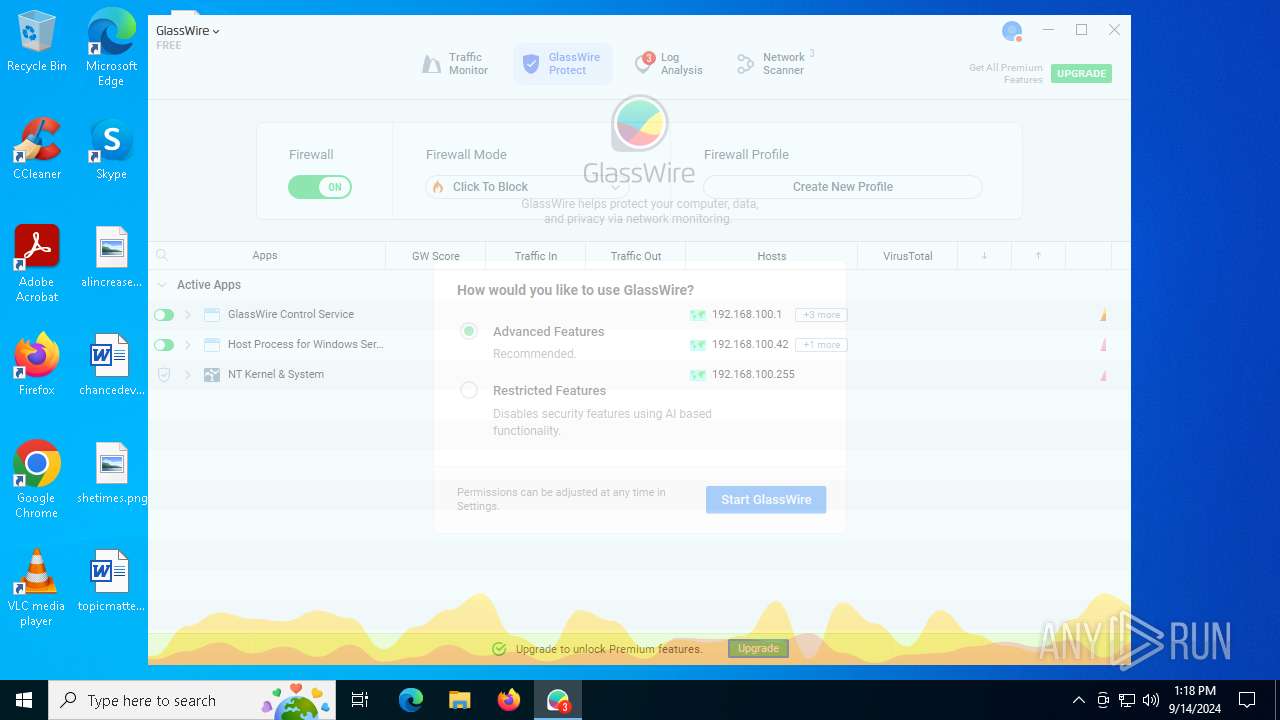
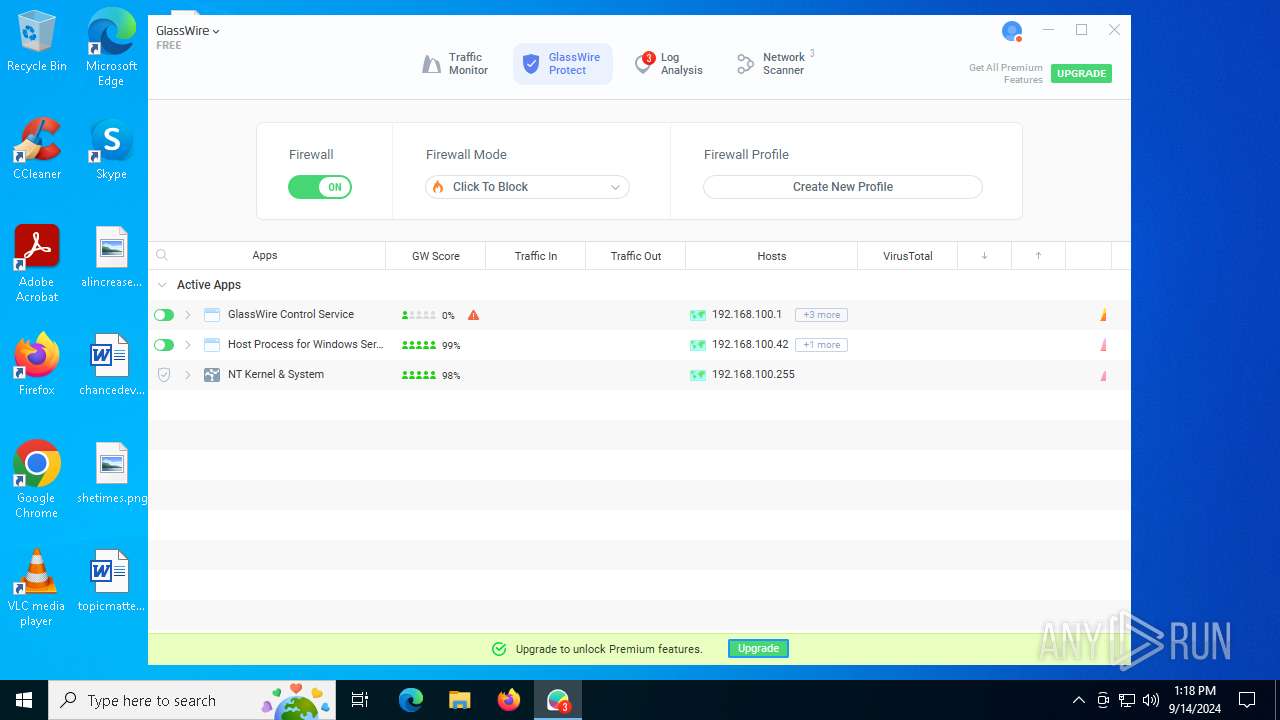
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
568 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4008 | GlassWireSetup.exe | 13.50.173.160:443 | pivot.protect.glasswire.com | AMAZON-02 | SE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
pivot.protect.glasswire.com |
| unknown |
www.glasswire.com |
| whitelisted |
api-us-east-2.protect.glasswire.com |
| unknown |
s3.amazonaws.com |
| shared |
geoip-database.protect.glasswire.com |
| unknown |