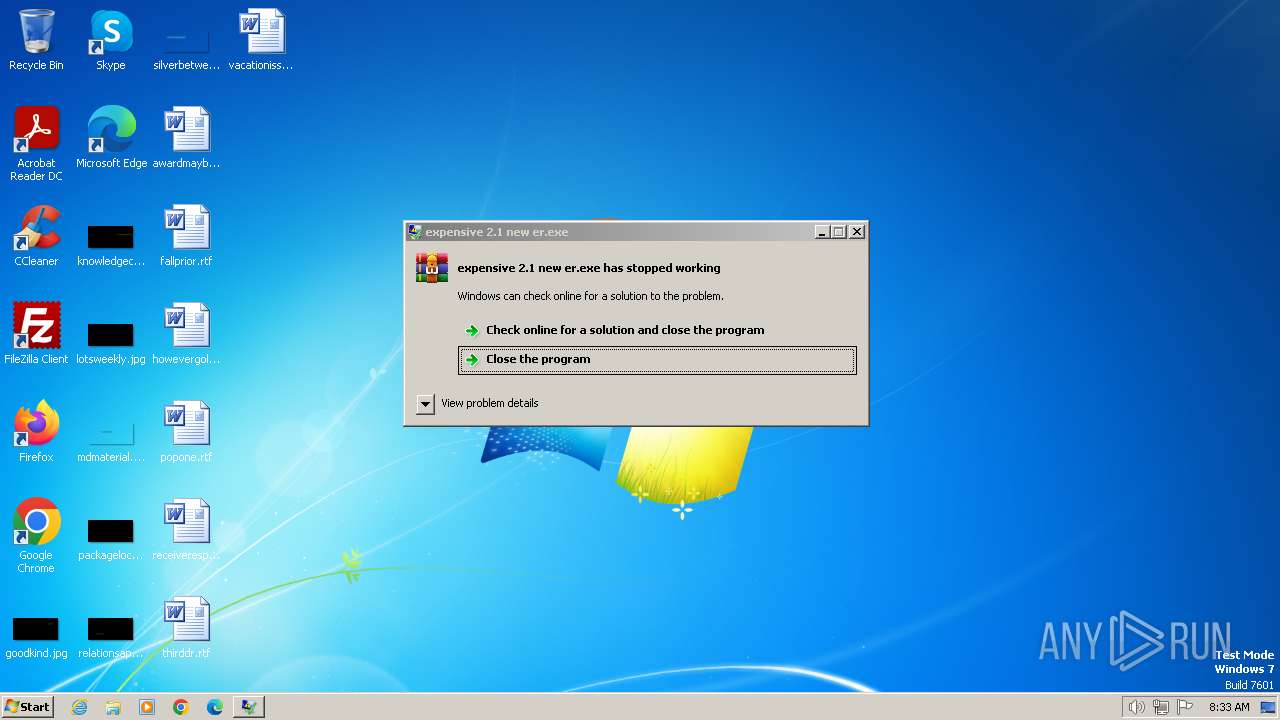
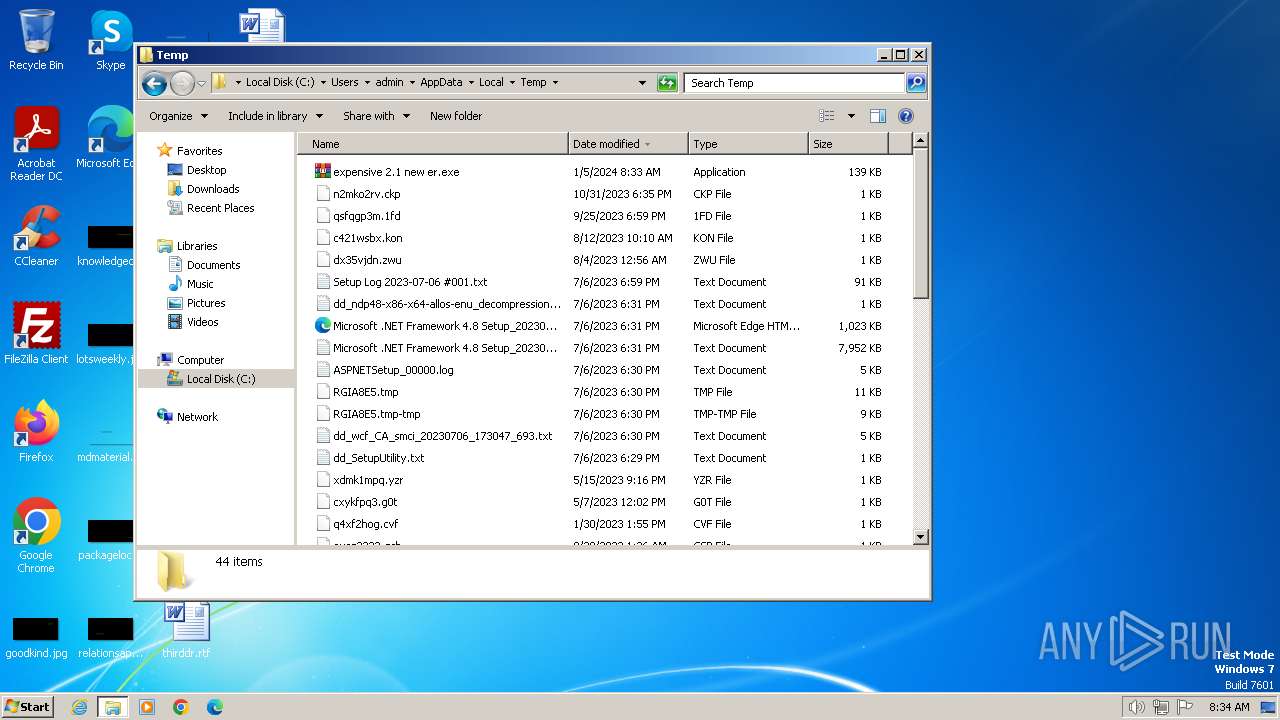
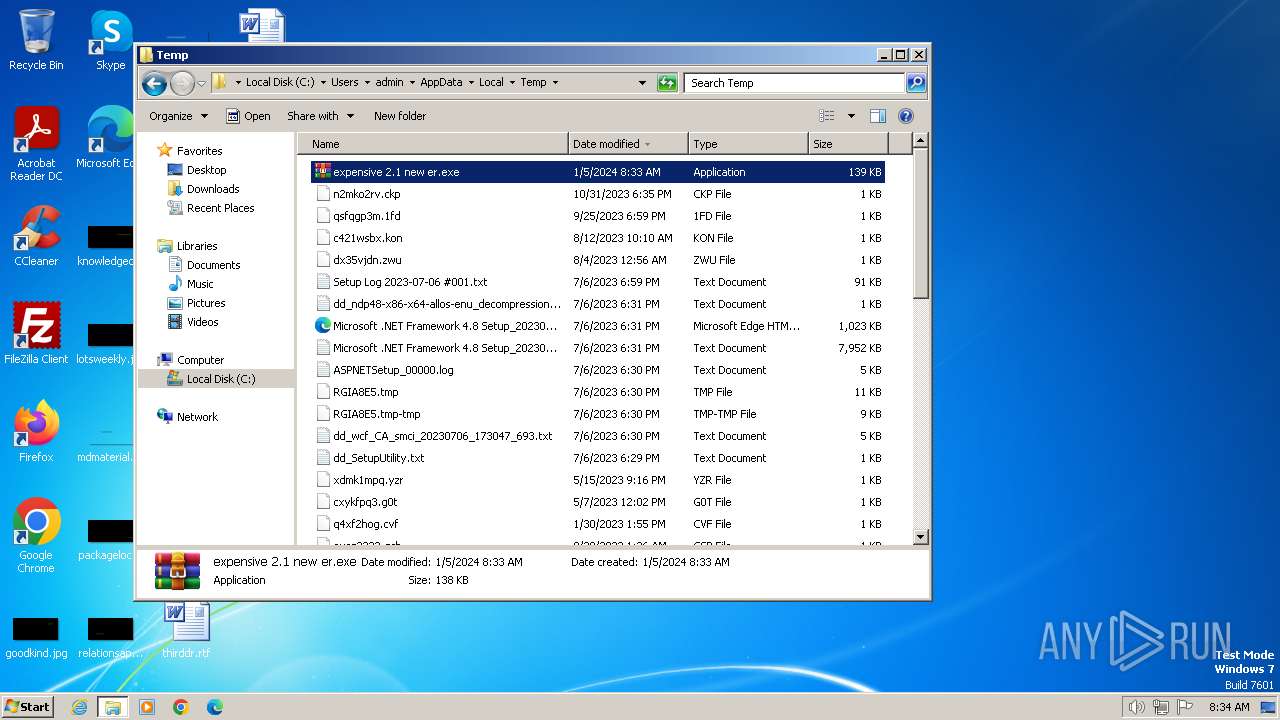
| File name: | expensive 2.1 new er.exe |
| Full analysis: | https://app.any.run/tasks/ce60958b-62a6-4be6-a96e-af3910a424da |
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2024, 08:33:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0FF18F9CEA25627C0DD74AF7EBEBB525 |
| SHA1: | 5FEC351D0C8E0D0B4442A5F0E1200BD8ACACED94 |
| SHA256: | 8FFC5DAFEF7B5348AF92E909CB3FFCF67B1CBC313D557D1EDFE6B3A61B6B5888 |
| SSDEEP: | 3072:H+JeZaFI9U/9OfWCNVSXWq4CdvUMfq3zs2UFX9Ud/ld9CfwSew6Nl:eJeZcI9sWaWkawq3zTOXY9C+w6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- expensive 2.1 new er.exe (PID: 2044)
- expensive 2.1 new er.exe (PID: 2176)
INFO
Reads the machine GUID from the registry
- expensive 2.1 new er.exe (PID: 2044)
- expensive 2.1 new er.exe (PID: 2176)
Reads the computer name
- expensive 2.1 new er.exe (PID: 2044)
- expensive 2.1 new er.exe (PID: 2176)
Drops the executable file immediately after the start
- expensive 2.1 new er.exe (PID: 2044)
Checks supported languages
- expensive 2.1 new er.exe (PID: 2044)
- expensive 2.1 new er.exe (PID: 2176)
Checks for external IP
- expensive 2.1 new er.exe (PID: 2044)
- expensive 2.1 new er.exe (PID: 2176)
Reads Environment values
- expensive 2.1 new er.exe (PID: 2044)
- expensive 2.1 new er.exe (PID: 2176)
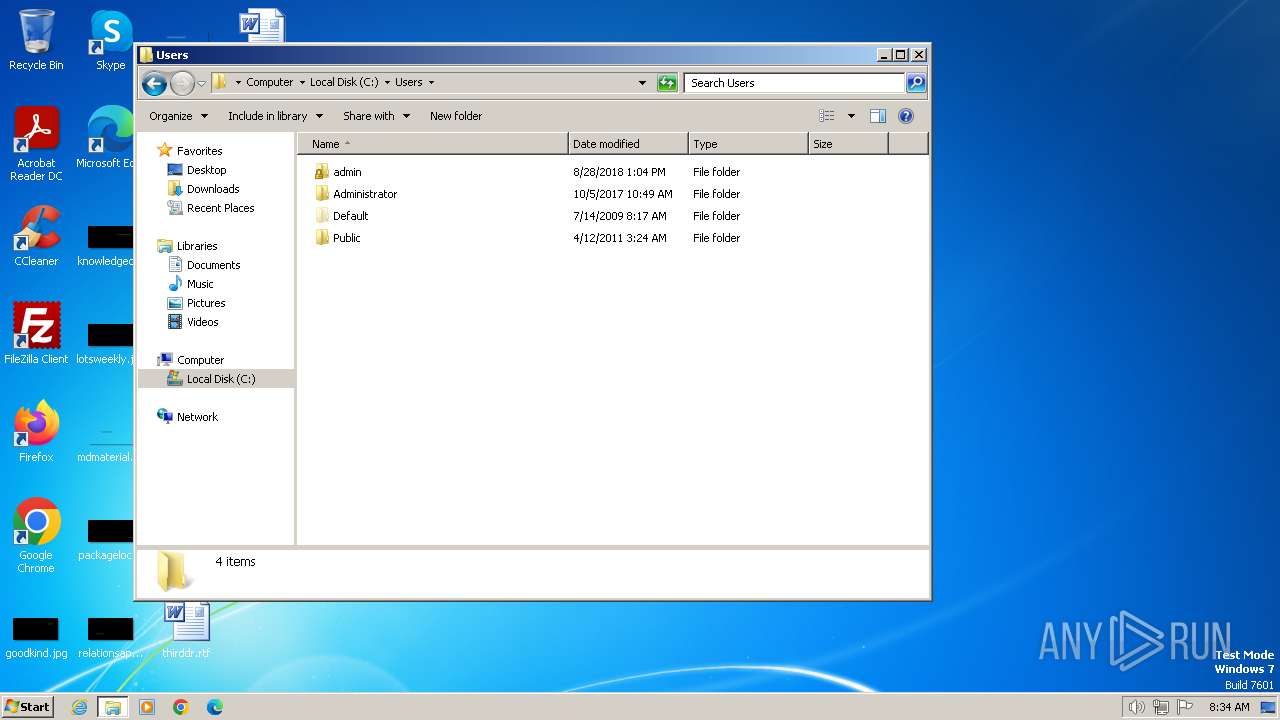
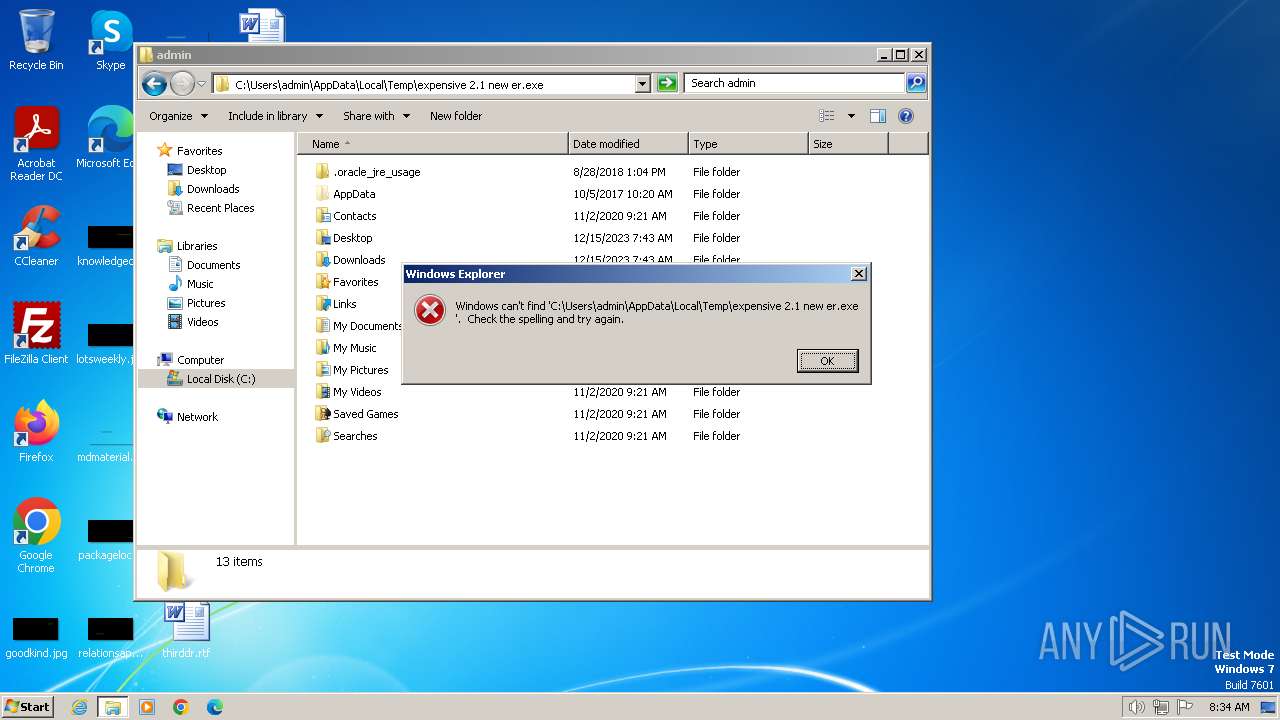
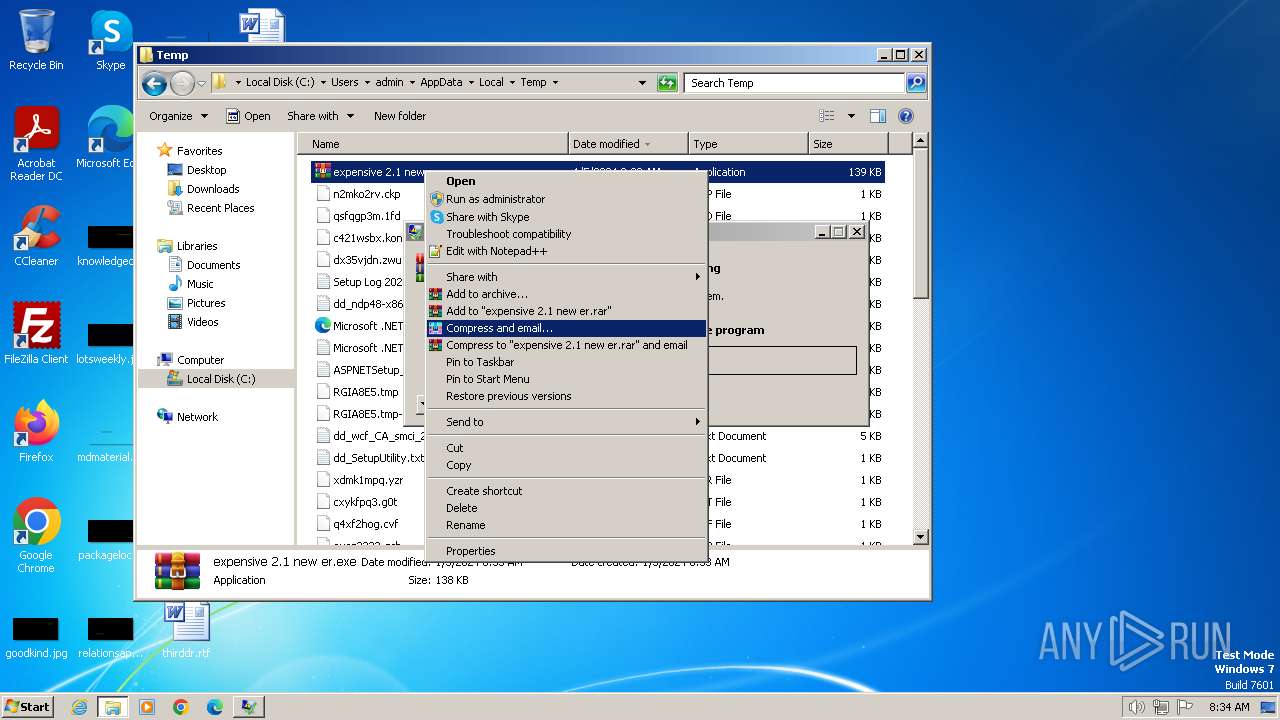
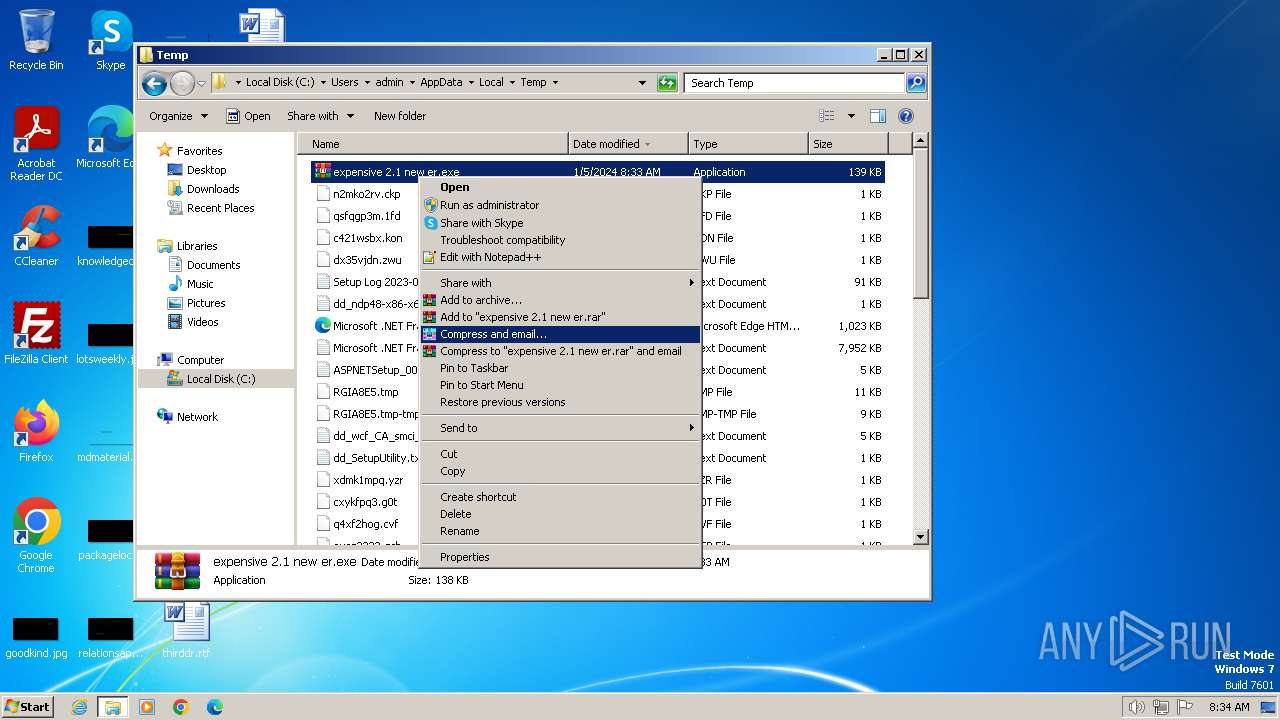
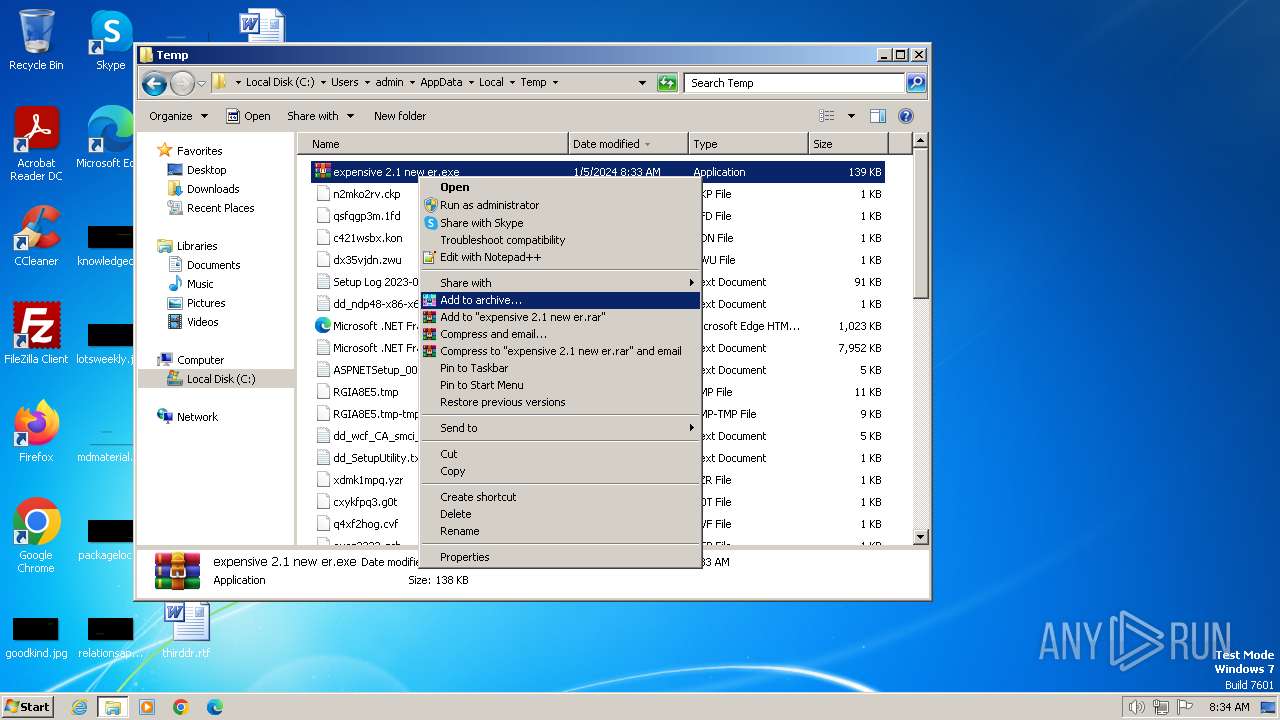
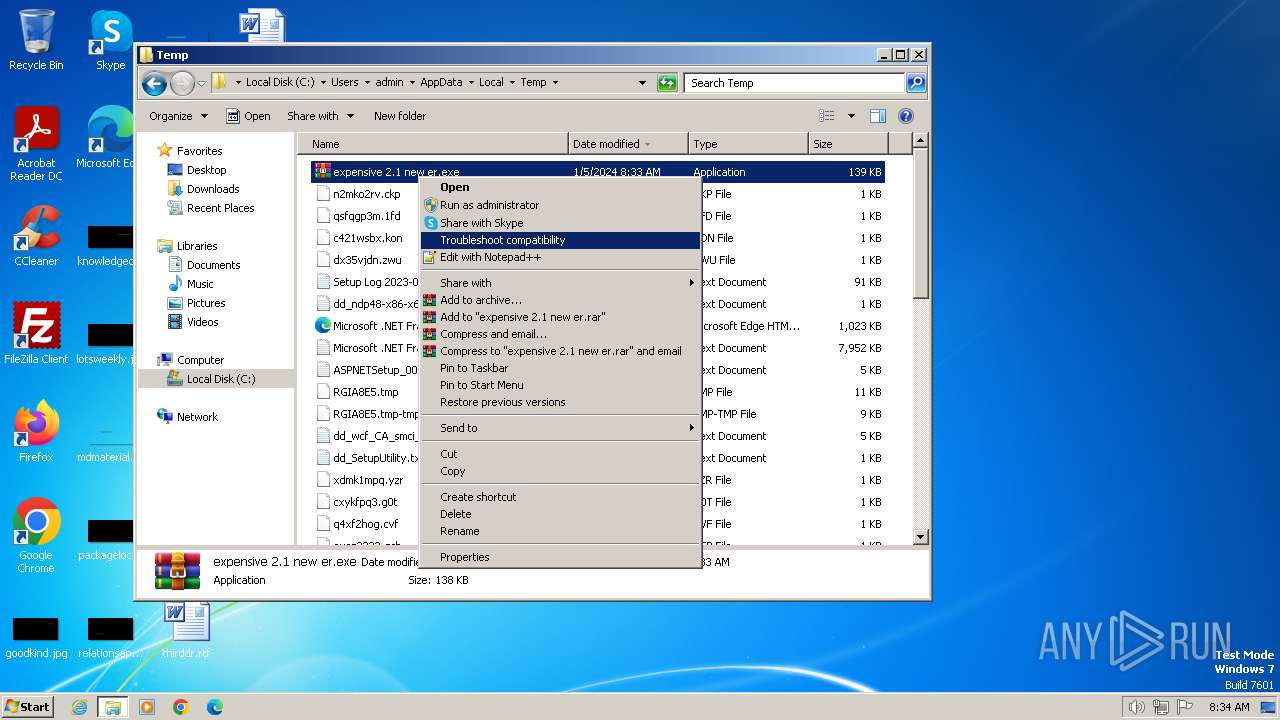
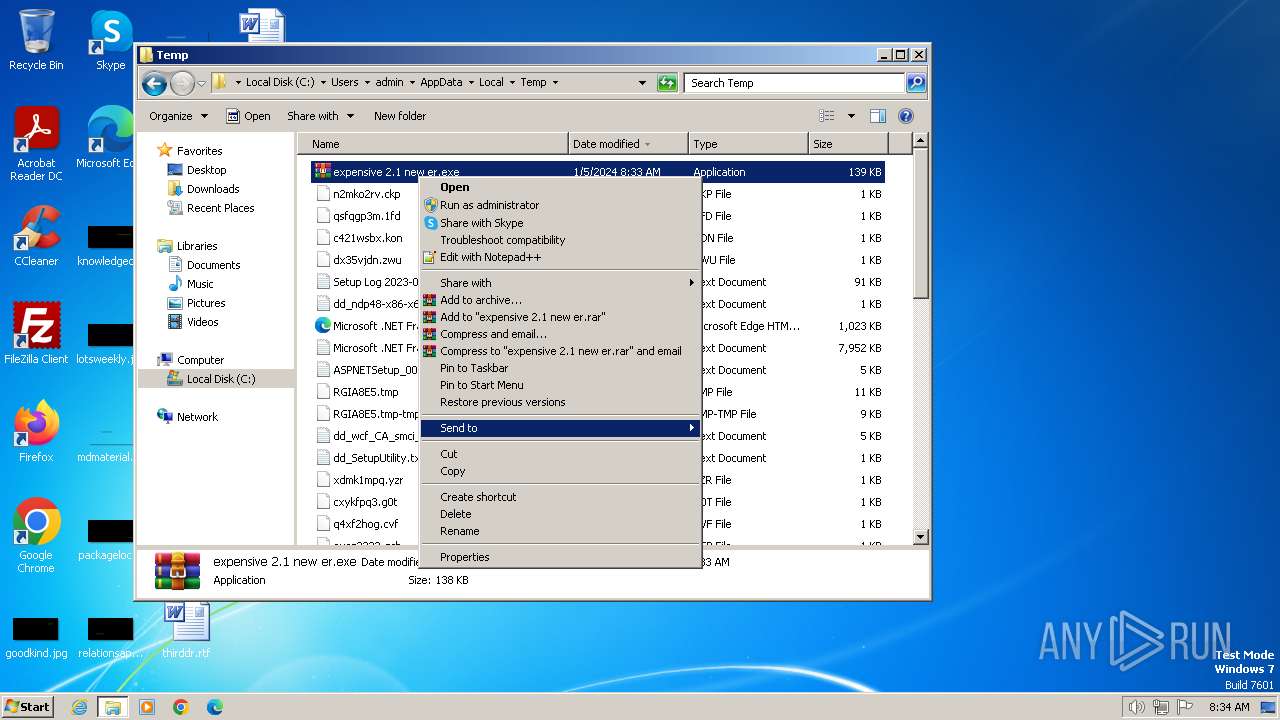
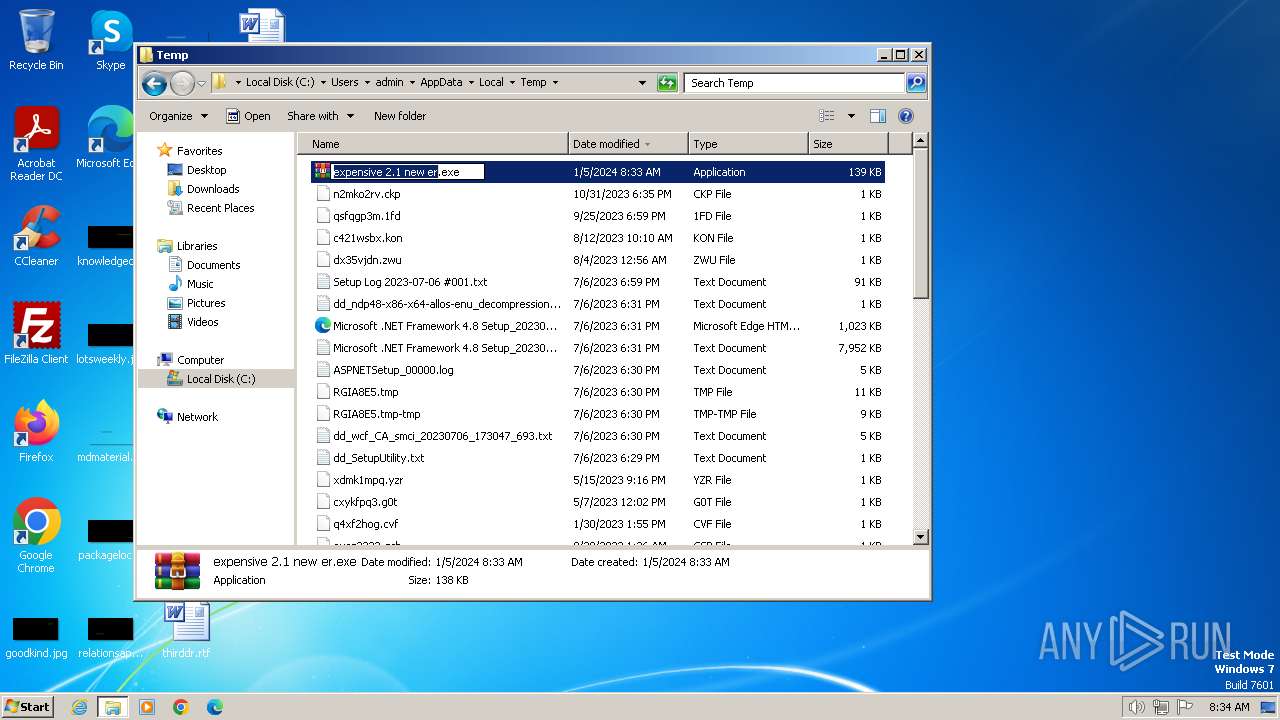
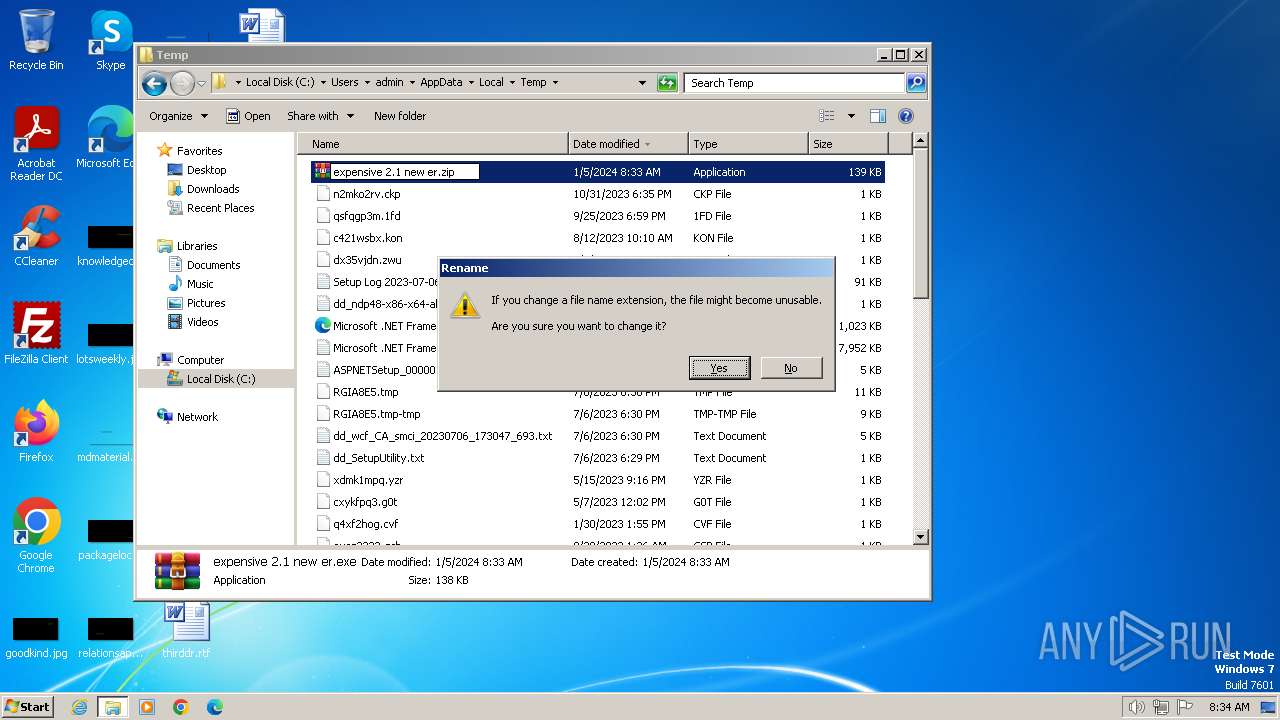
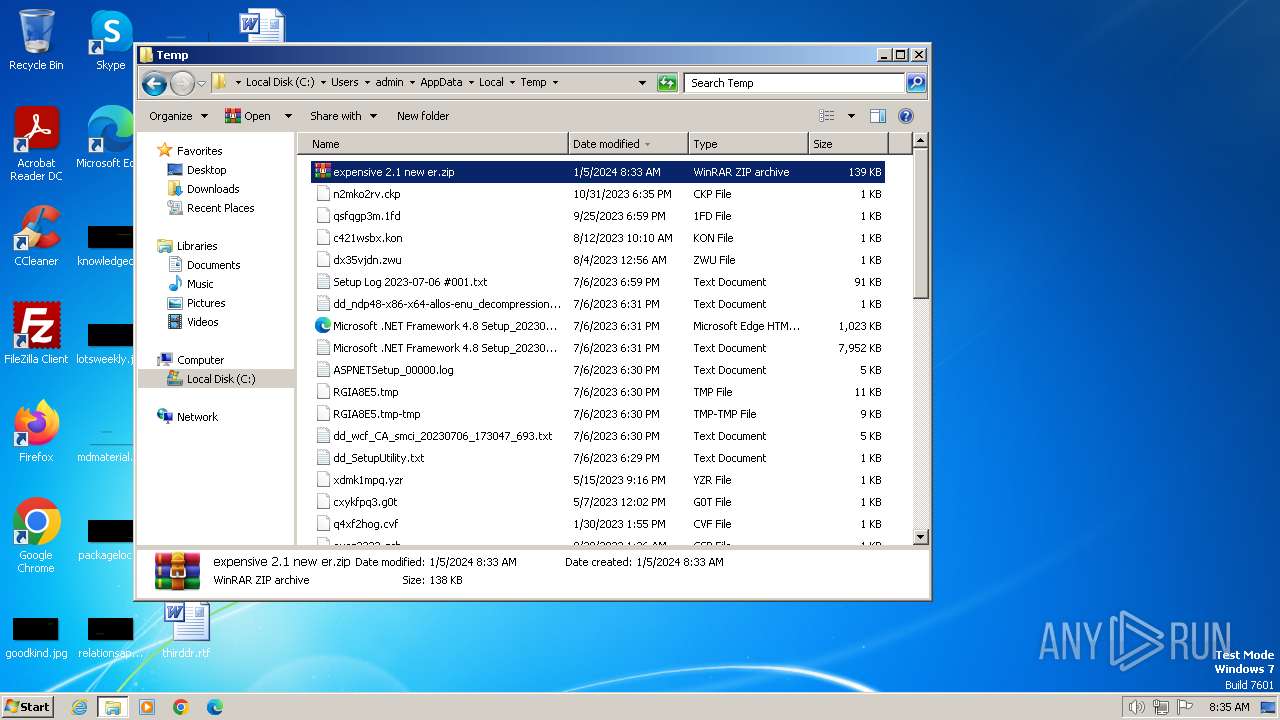
Manual execution by a user
- expensive 2.1 new er.exe (PID: 2176)
- explorer.exe (PID: 1772)
- WinRAR.exe (PID: 880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:01:05 08:38:40+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 39936 |
| InitializedDataSize: | 101376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xba8e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | XClient.exe |
| LegalCopyright: | |
| OriginalFileName: | XClient.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
44
Monitored processes
4
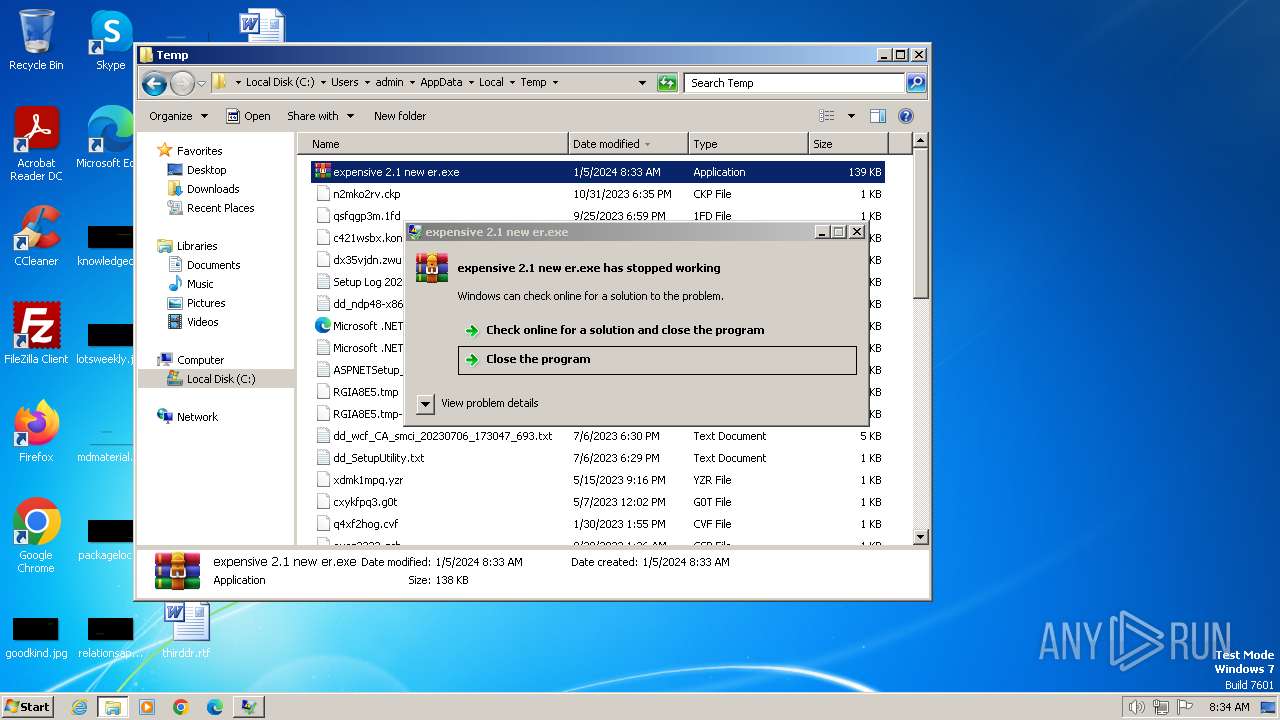
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
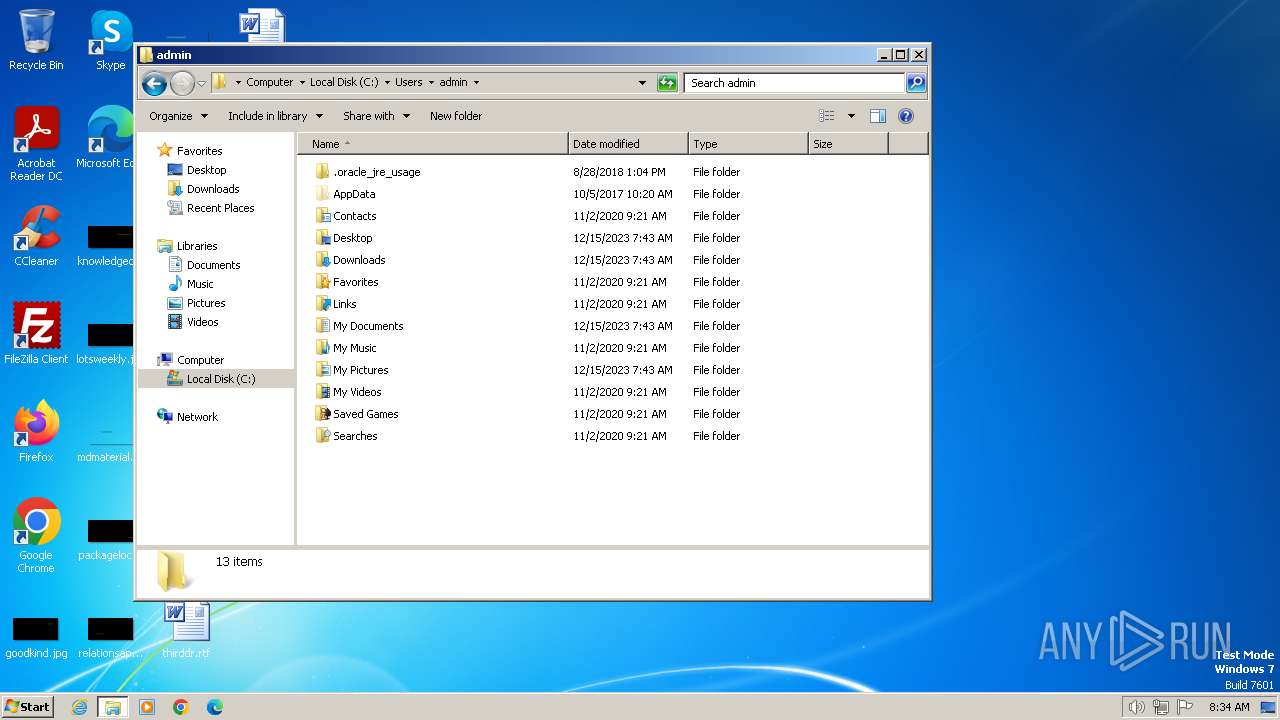
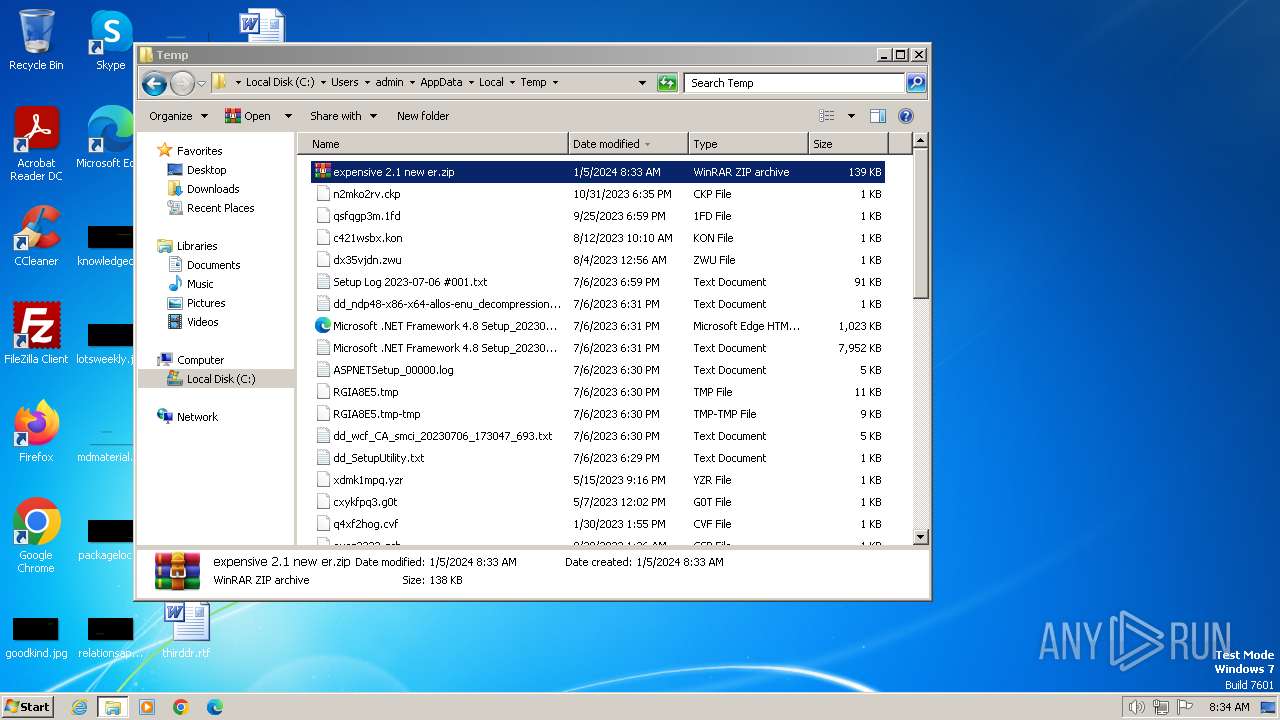
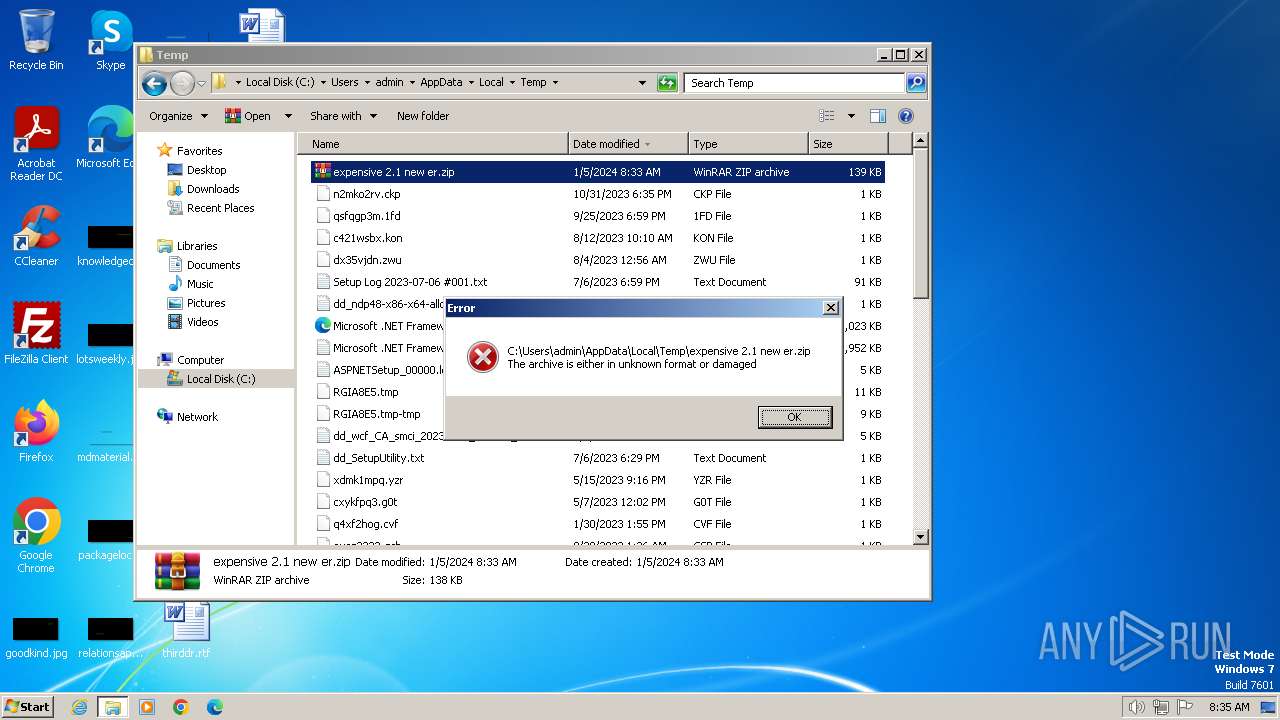
| 880 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\expensive 2.1 new er.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
| 1772 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2044 | "C:\Users\admin\AppData\Local\Temp\expensive 2.1 new er.exe" | C:\Users\admin\AppData\Local\Temp\expensive 2.1 new er.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 2148734499 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\Temp\expensive 2.1 new er.exe" | C:\Users\admin\AppData\Local\Temp\expensive 2.1 new er.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 2148734499 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 926
Read events
1 917
Write events
9
Delete events
0
Modification events
| (PID) Process: | (880) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band56_0 |
Value: 38000000730100000402000000000000D4D0C8000000000000000000000000005C0104000000000039000000B40200000000000001000000 | |||
| (PID) Process: | (880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band56_1 |
Value: 38000000730100000500000000000000D4D0C8000000000000000000000000008C010C0000000000160000002A0000000000000002000000 | |||
| (PID) Process: | (880) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band56_2 |
Value: 38000000730100000400000000000000D4D0C800000000000000000000000000AC0107000000000016000000640000000000000003000000 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2176 | expensive 2.1 new er.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | text | 5 b | unknown |
2044 | expensive 2.1 new er.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | text | 5 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2044 | expensive 2.1 new er.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
2176 | expensive 2.1 new er.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2044 | expensive 2.1 new er.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2044 | expensive 2.1 new er.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2044 | expensive 2.1 new er.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2176 | expensive 2.1 new er.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2176 | expensive 2.1 new er.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2176 | expensive 2.1 new er.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
Process | Message |
|---|---|
expensive 2.1 new er.exe | CLR: Managed code called FailFast without specifying a reason.
|
expensive 2.1 new er.exe | CLR: Managed code called FailFast without specifying a reason.
|