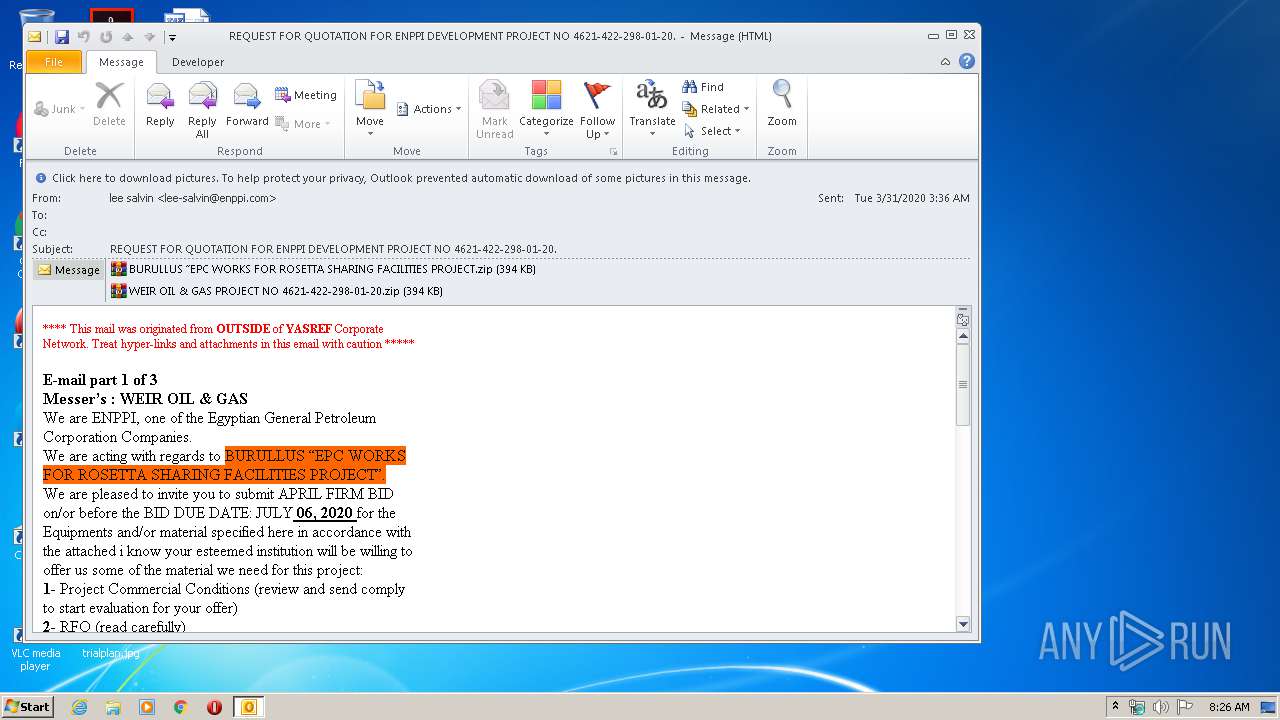
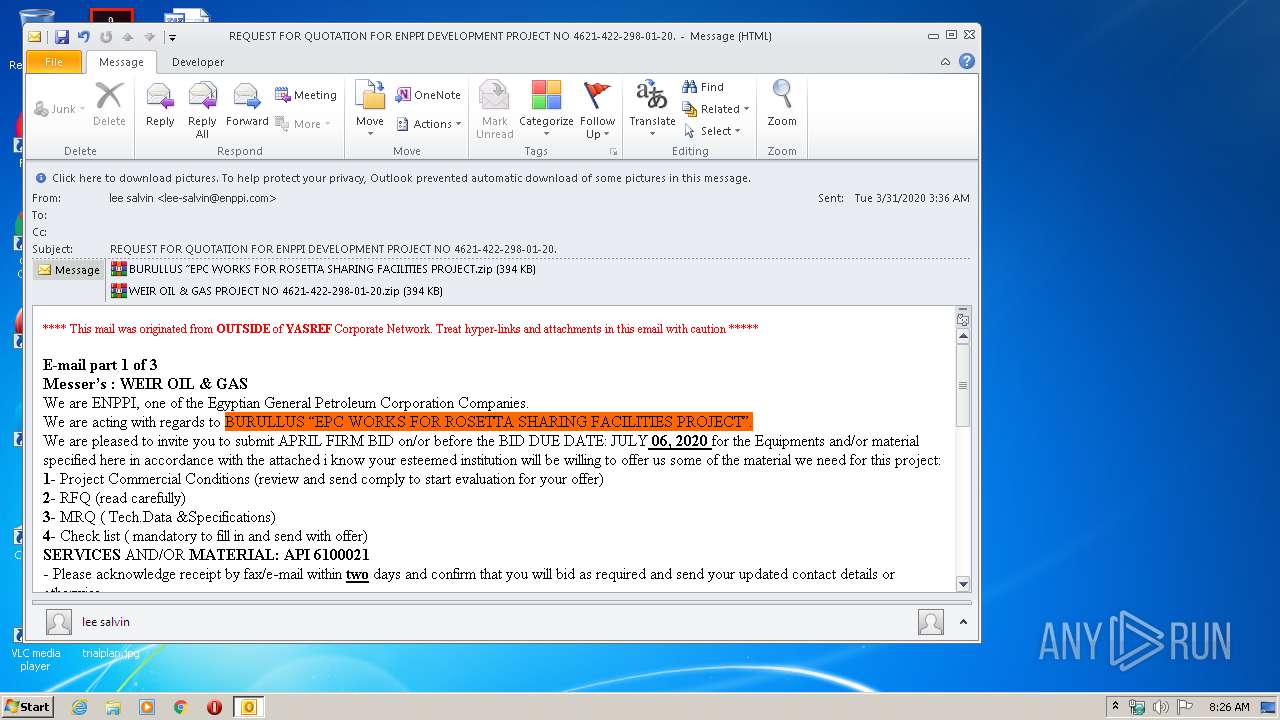
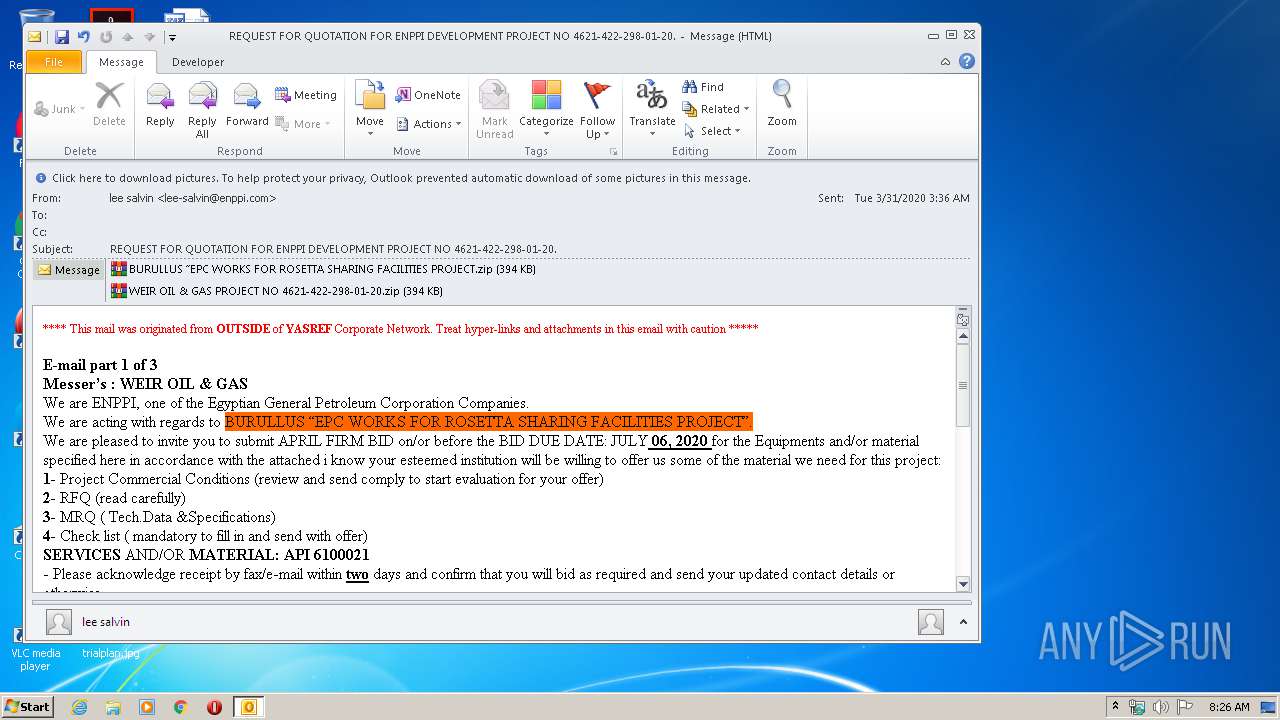
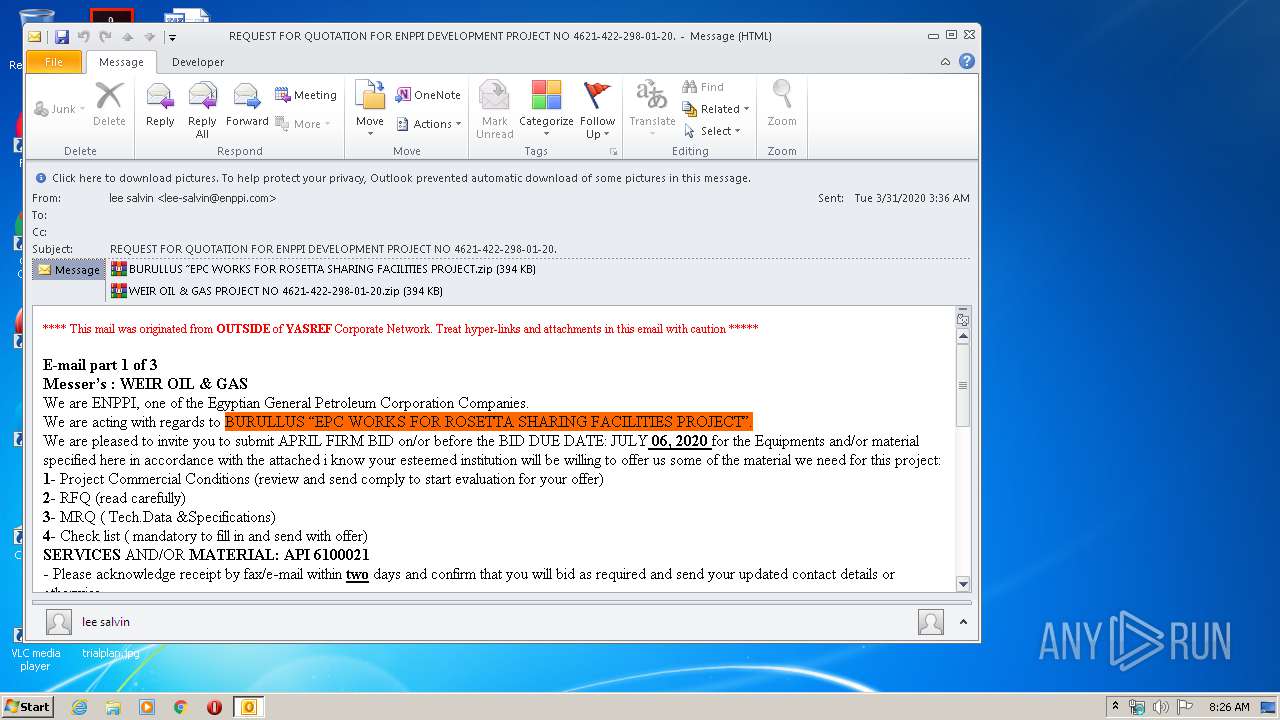
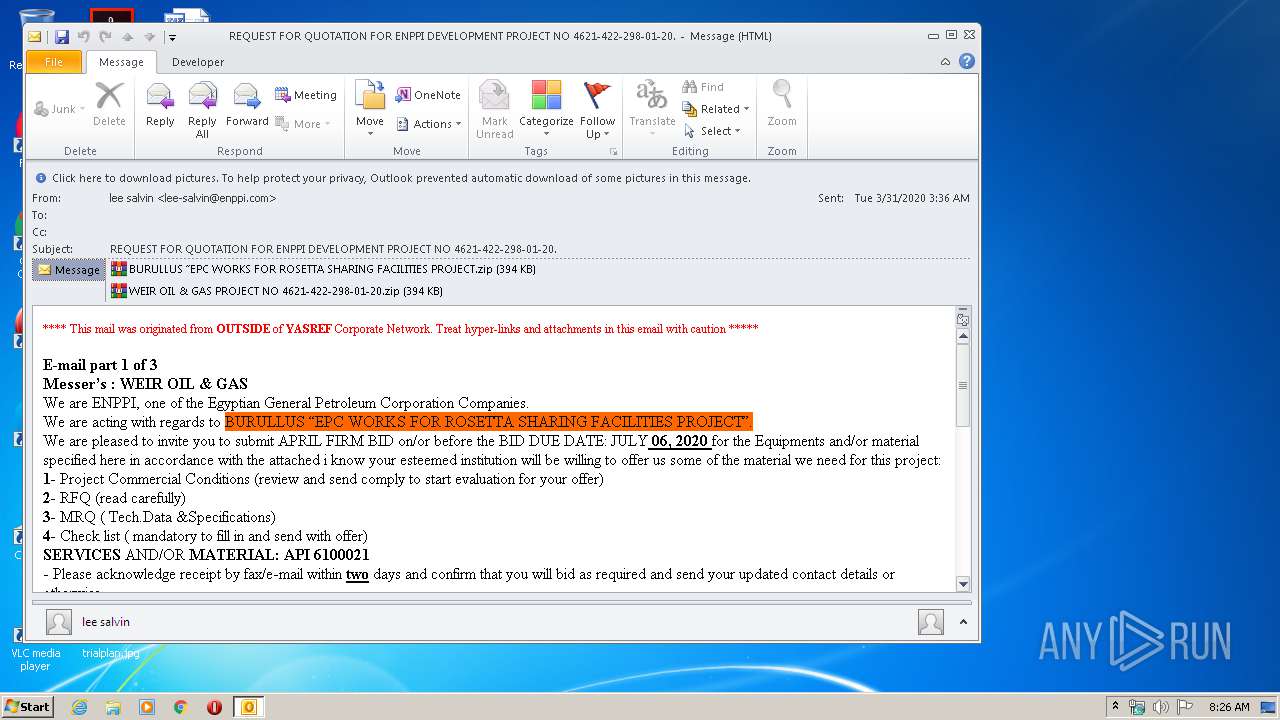
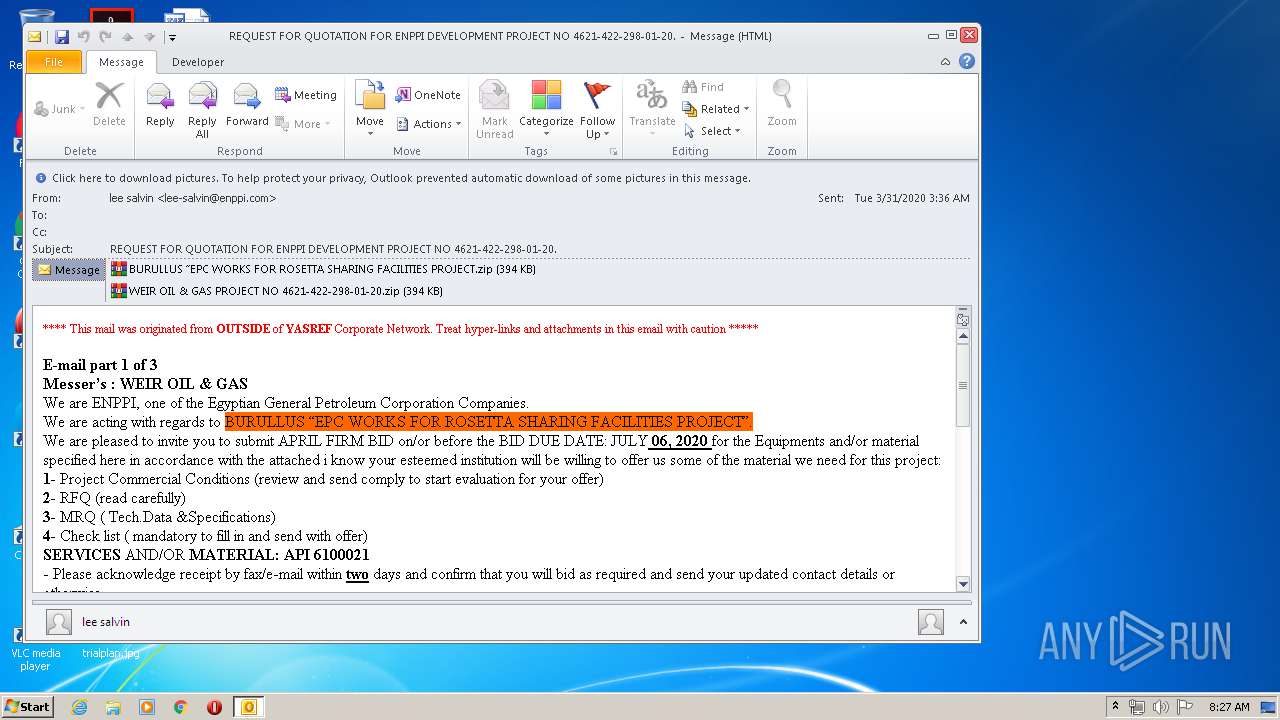
| File name: | REQUEST FOR QUOTATION FOR ENPPI DEVELOPMENT PROJECT NO 4621-422-298-01-20.msg |
| Full analysis: | https://app.any.run/tasks/883e0d43-0bbf-468f-a80a-997a0e13da07 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 07:25:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | D8BBD1BE0EEAB7DC0D2C0324A7ADFBE5 |
| SHA1: | D40269EEDDF285BF35A8EEFB1BD0762C17F34B4E |
| SHA256: | 8FF2FE68CD661ABB50FCEBB87AA5CC7A967111B1F5DDDBAF1E2F26E636A10327 |
| SSDEEP: | 24576:18luTjY58akm5smcLwmuTjY58akm5smcLwa:18C0su0s |
MALICIOUS
Application was dropped or rewritten from another process
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 2928)
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 912)
- BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe (PID: 4012)
- BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe (PID: 3680)
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2872)
Changes the autorun value in the registry
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 2928)
- BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe (PID: 3680)
Actions looks like stealing of personal data
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 2928)
- BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe (PID: 3680)
Changes settings of System certificates
- BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe (PID: 3680)
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 2928)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2872)
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 2928)
- BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe (PID: 3680)
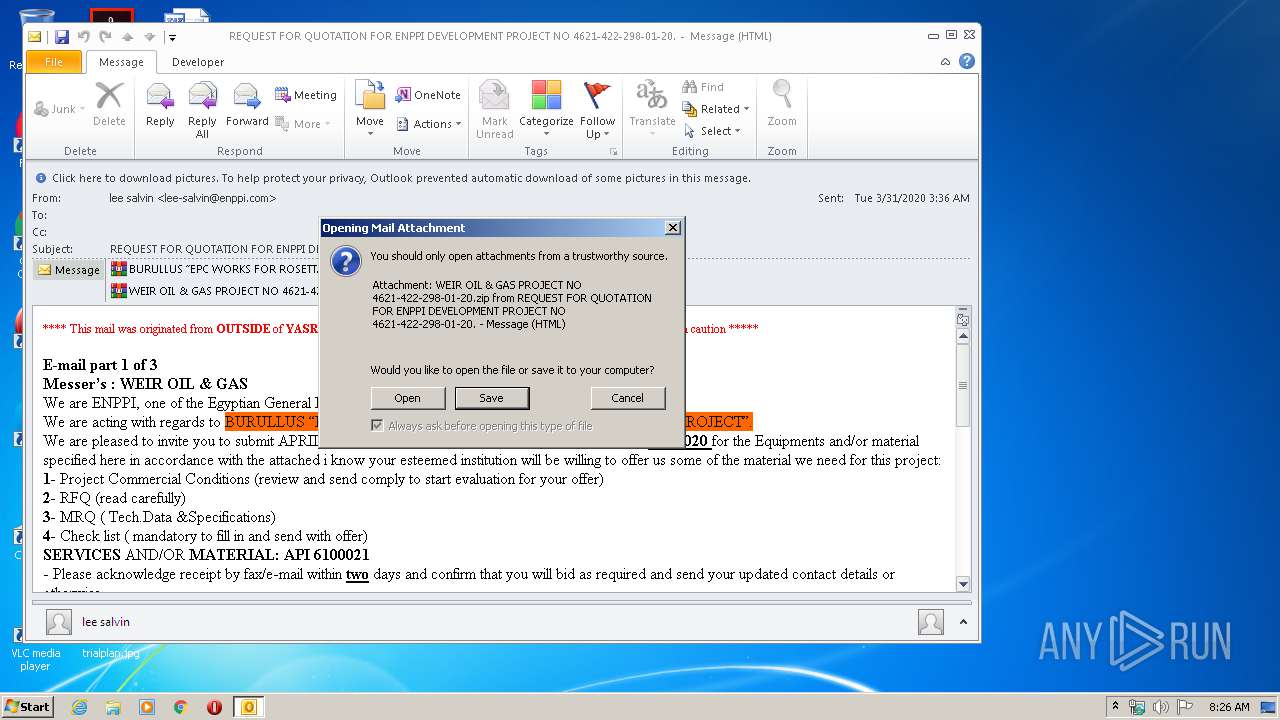
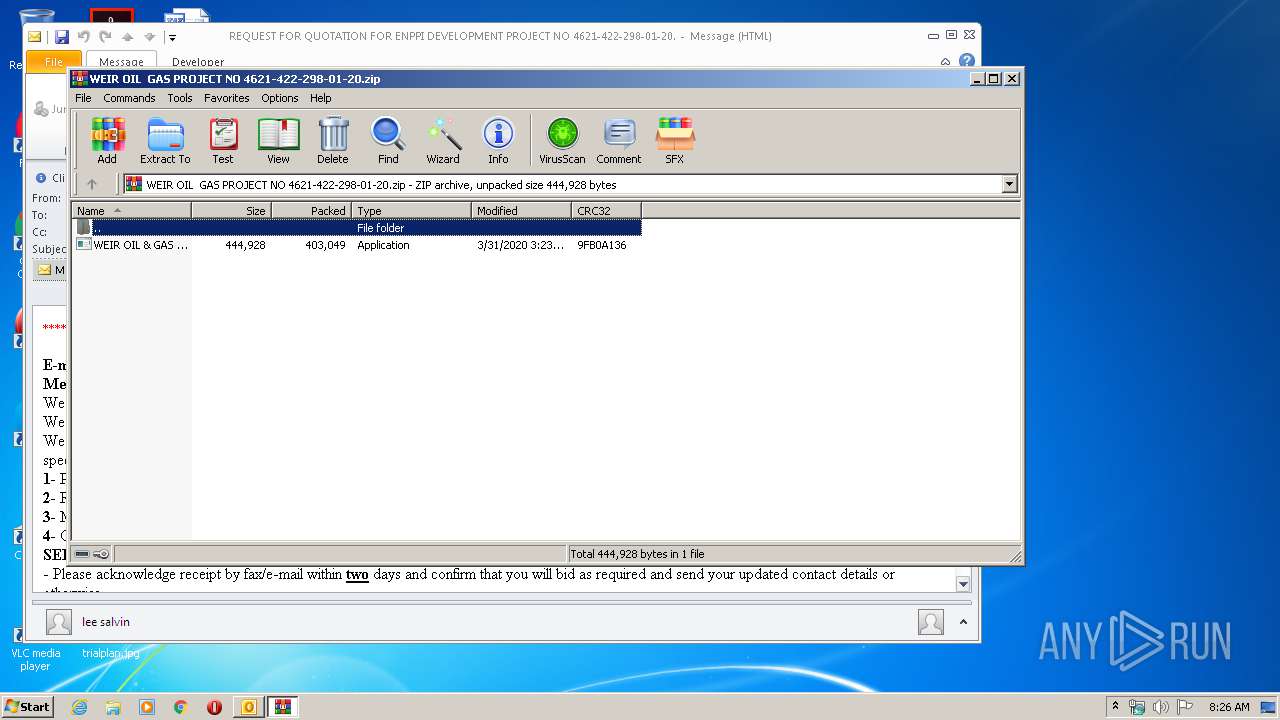
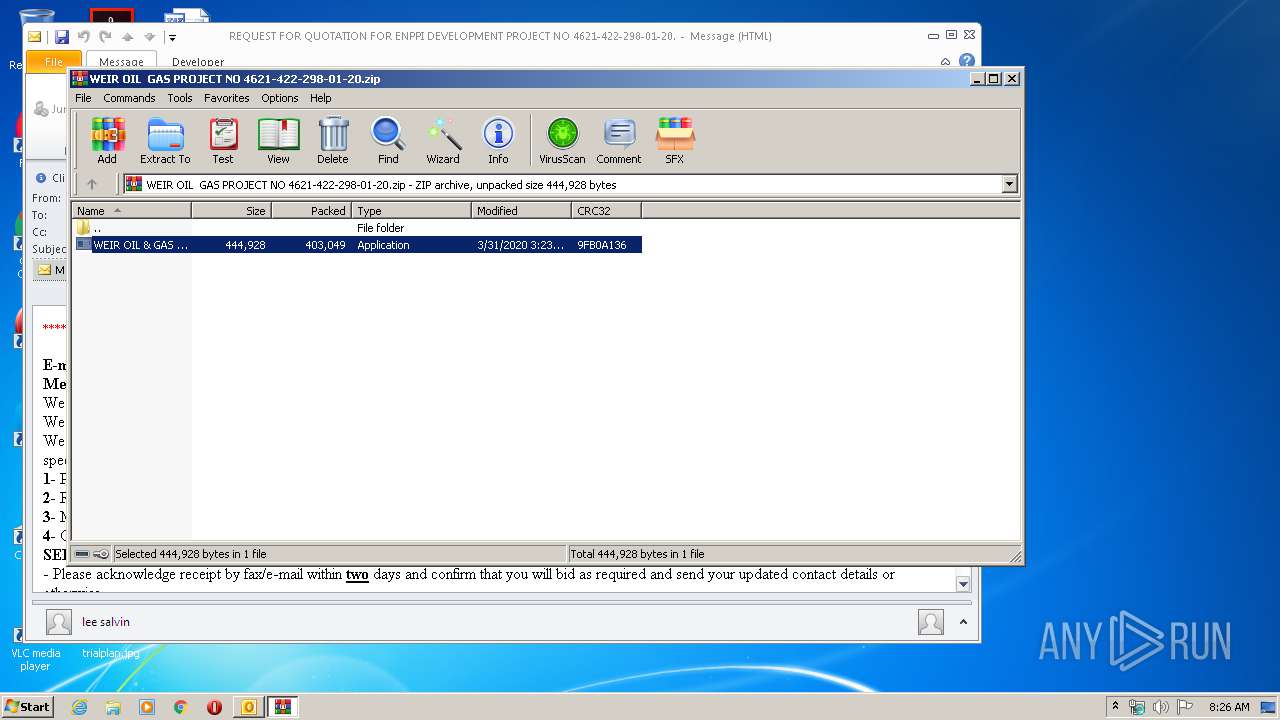
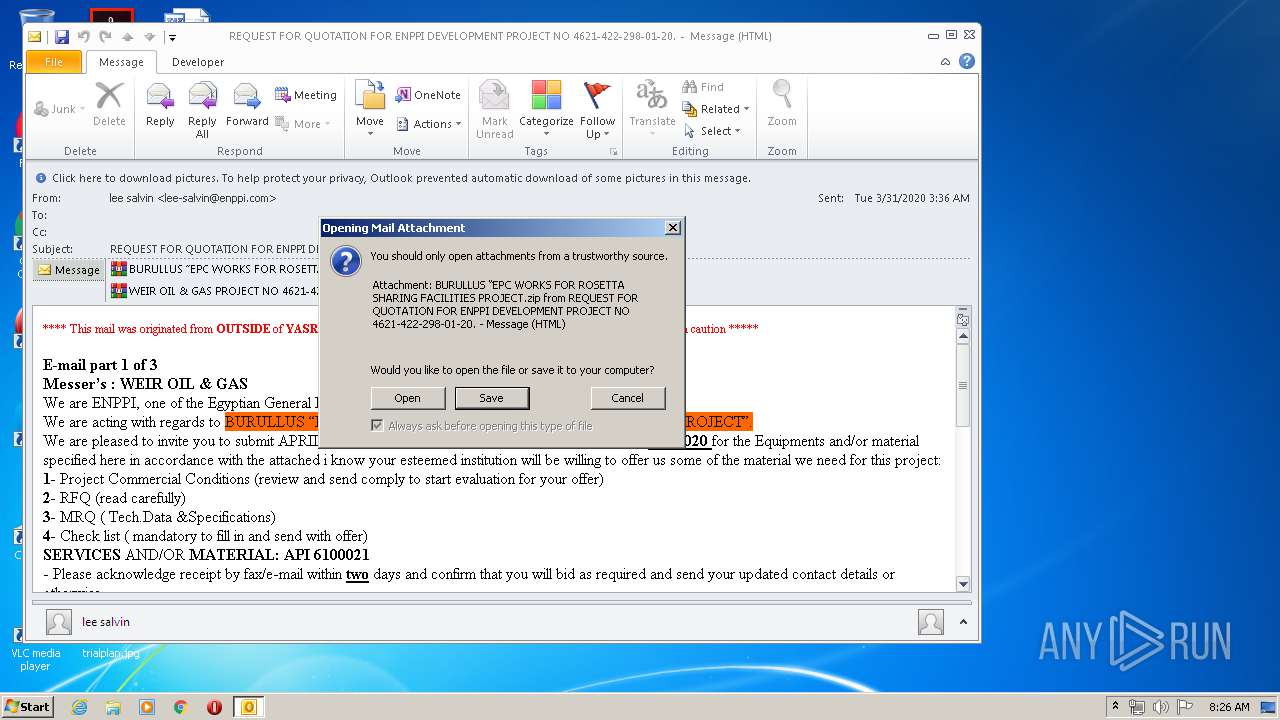
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2536)
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 2928)
- WinRAR.exe (PID: 3384)
- BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe (PID: 3680)
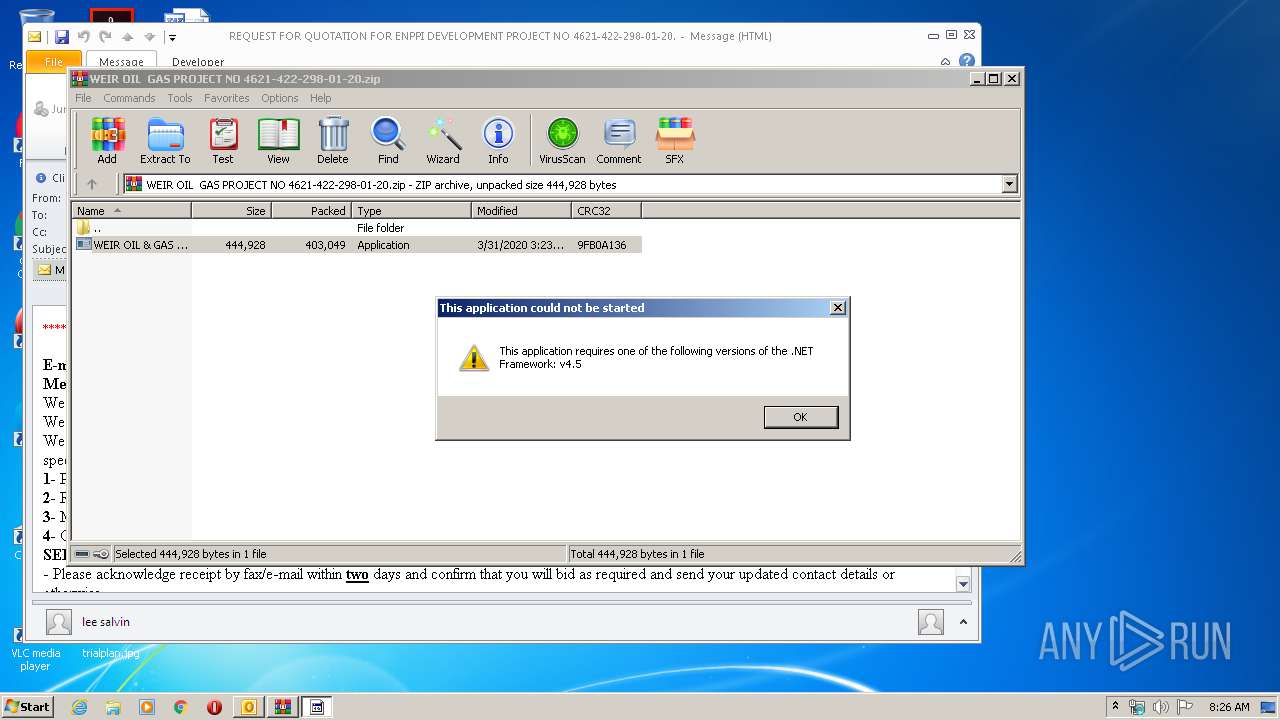
Application launched itself
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 912)
- BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe (PID: 4012)
Reads the cookies of Google Chrome
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 2928)
Reads the cookies of Mozilla Firefox
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 2928)
Adds / modifies Windows certificates
- BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe (PID: 3680)
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 2928)
INFO
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2872)
Reads settings of System Certificates
- WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe (PID: 2928)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
42
Monitored processes
7
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 912 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2536.41303\WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2536.41303\WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe | — | WinRAR.exe | |||||||||||
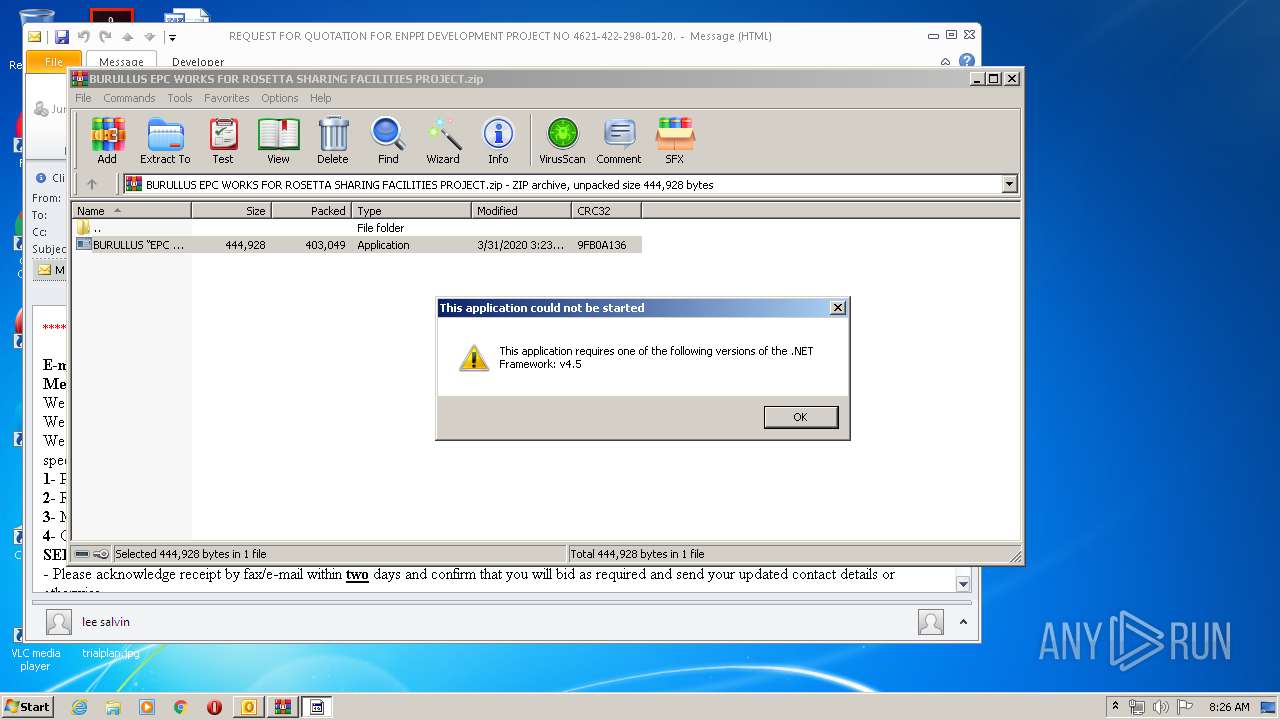
User: admin Integrity Level: MEDIUM Description: HighDpiDemo Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2536 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\H2TZ3TQH\WEIR OIL GAS PROJECT NO 4621-422-298-01-20.zip" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\REQUEST FOR QUOTATION FOR ENPPI DEVELOPMENT PROJECT NO 4621-422-298-01-20.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2928 | "{path}" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2536.41303\WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe | WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: HighDpiDemo Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
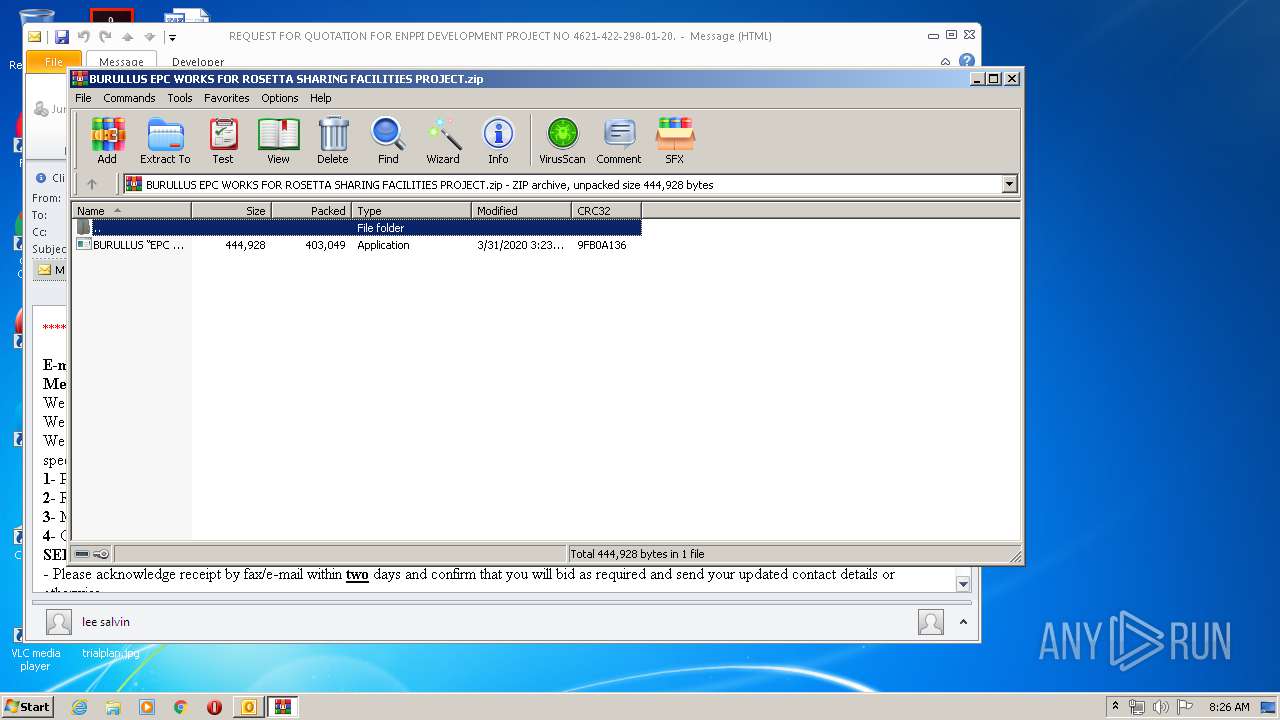
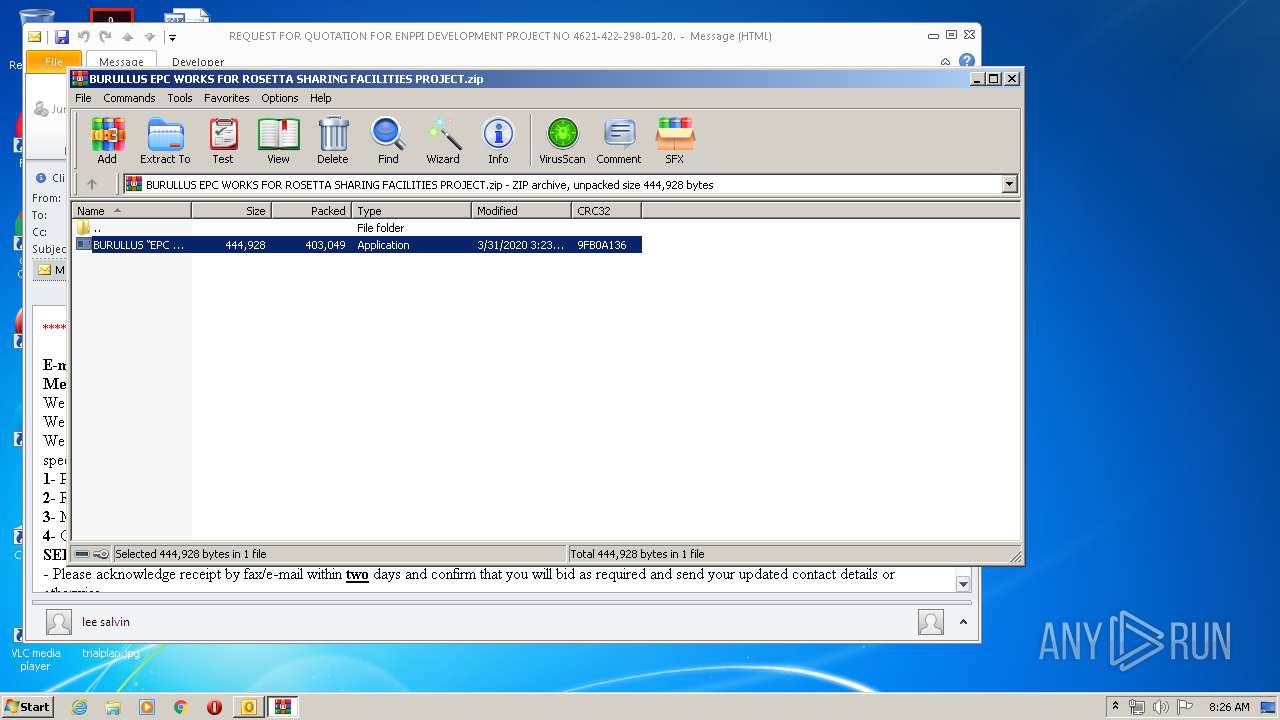
| 3384 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\H2TZ3TQH\BURULLUS EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.zip" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3680 | "{path}" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.44027\BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe | BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: HighDpiDemo Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4012 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.44027\BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3384.44027\BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: HighDpiDemo Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
6 038
Read events
2 226
Write events
2 724
Delete events
1 088
Modification events
| (PID) Process: | (2872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2872) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
4
Suspicious files
5
Text files
28
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6BA3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\H2TZ3TQH\WEIR OIL GAS PROJECT NO 4621-422-298-01-20 (2).zip\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\H2TZ3TQH\BURULLUS EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT (2).zip\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2928 | WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe | C:\Users\admin\AppData\Roaming\dhoosyji.rwr\Chrome\Default\Cookies | — | |
MD5:— | SHA256:— | |||
| 2928 | WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe | C:\Users\admin\AppData\Roaming\dhoosyji.rwr\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_B3B4629D1D0432439246312EBD792150.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_C71056DEF74B014BA1351B690B4A89AD.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 2536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2536.41303\WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2872 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2872 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3680 | BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe | 77.88.21.158:587 | smtp.yandex.com | YANDEX LLC | RU | whitelisted |
2928 | WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe | 77.88.21.158:587 | smtp.yandex.com | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
smtp.yandex.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2928 | WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2928 | WEIR OIL & GAS PROJECT NO 4621-422-298-01-20.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3680 | BURULLUS “EPC WORKS FOR ROSETTA SHARING FACILITIES PROJECT.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |