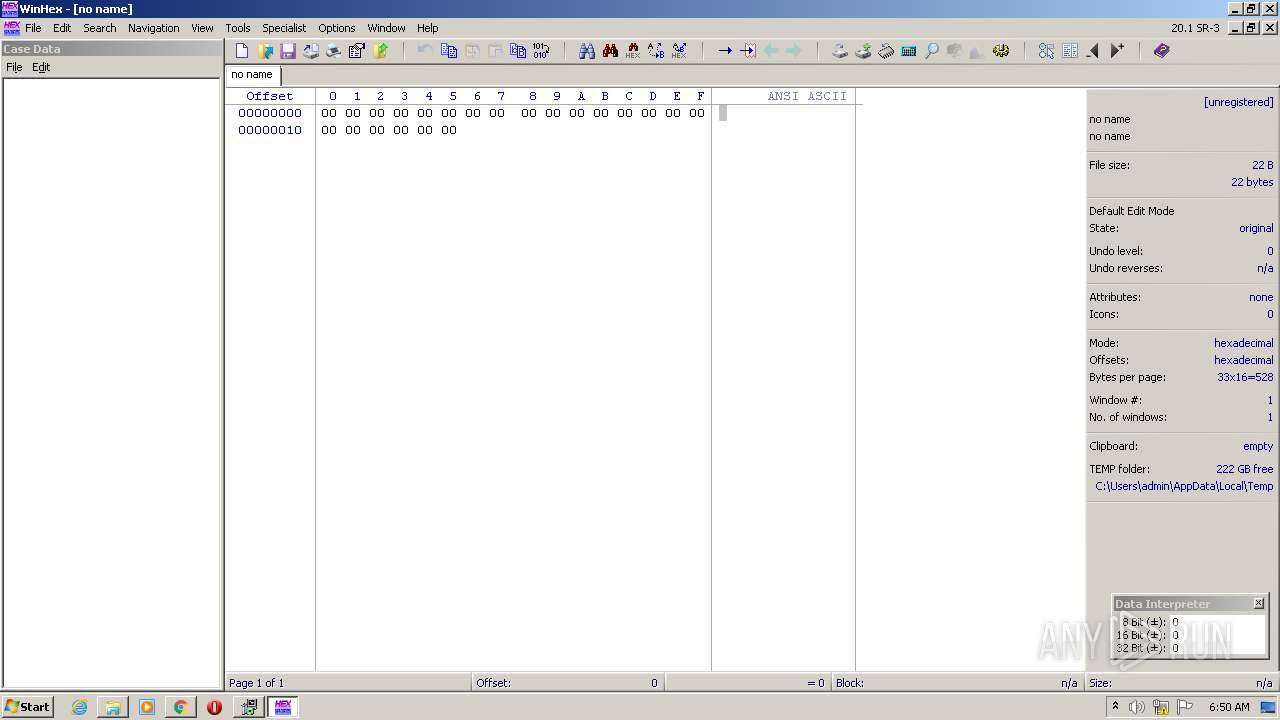
| URL: | http://www.winhex.com/winhex/hex-editor.html |
| Full analysis: | https://app.any.run/tasks/1d399295-09b2-417c-a34f-0cf87c0d60b9 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2021, 06:49:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 82C76085AC1D54C7565176725E237137 |
| SHA1: | 05ABC82AAC78078741401166DF791293551C19B1 |
| SHA256: | 8FEB8BD6CC170B972178F92983B1937532A56977D70925E15FA8EBF59B55A5A1 |
| SSDEEP: | 3:N1KJS4wdiMJg6MLUJ:Cc4w078 |
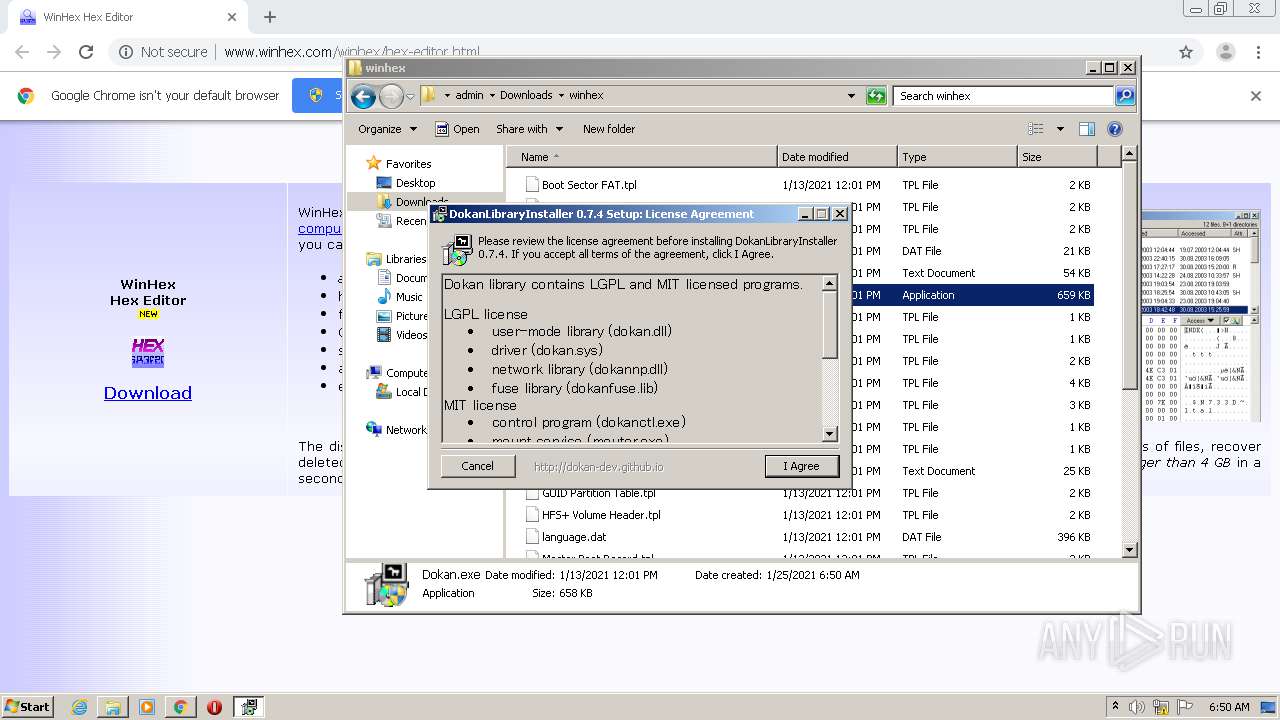
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 2600)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3352)
- Dokan.exe (PID: 1844)
- dokanctl.exe (PID: 2184)
- dokanctl.exe (PID: 1788)
- winhex.exe (PID: 3072)
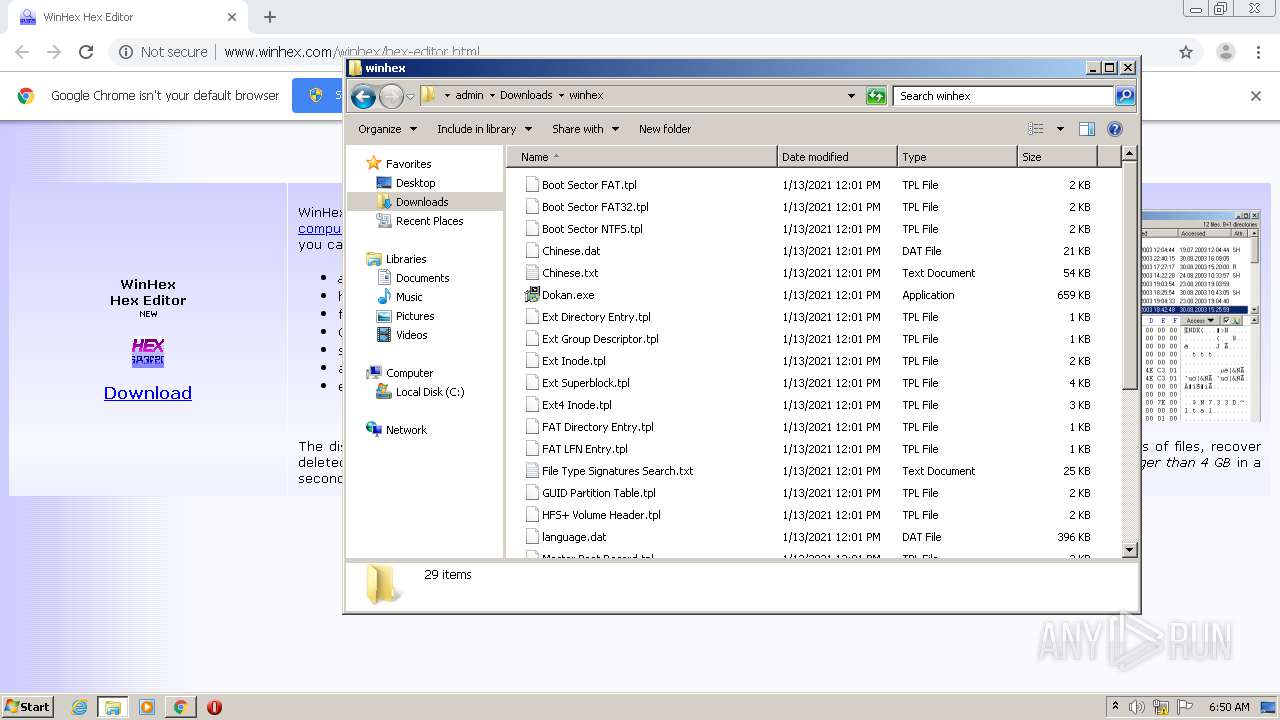
Application was dropped or rewritten from another process
- Dokan.exe (PID: 1144)
- Dokan.exe (PID: 1844)
- mounter.exe (PID: 672)
- dokanctl.exe (PID: 2184)
- dokanctl.exe (PID: 1788)
- winhex.exe (PID: 3072)
SUSPICIOUS
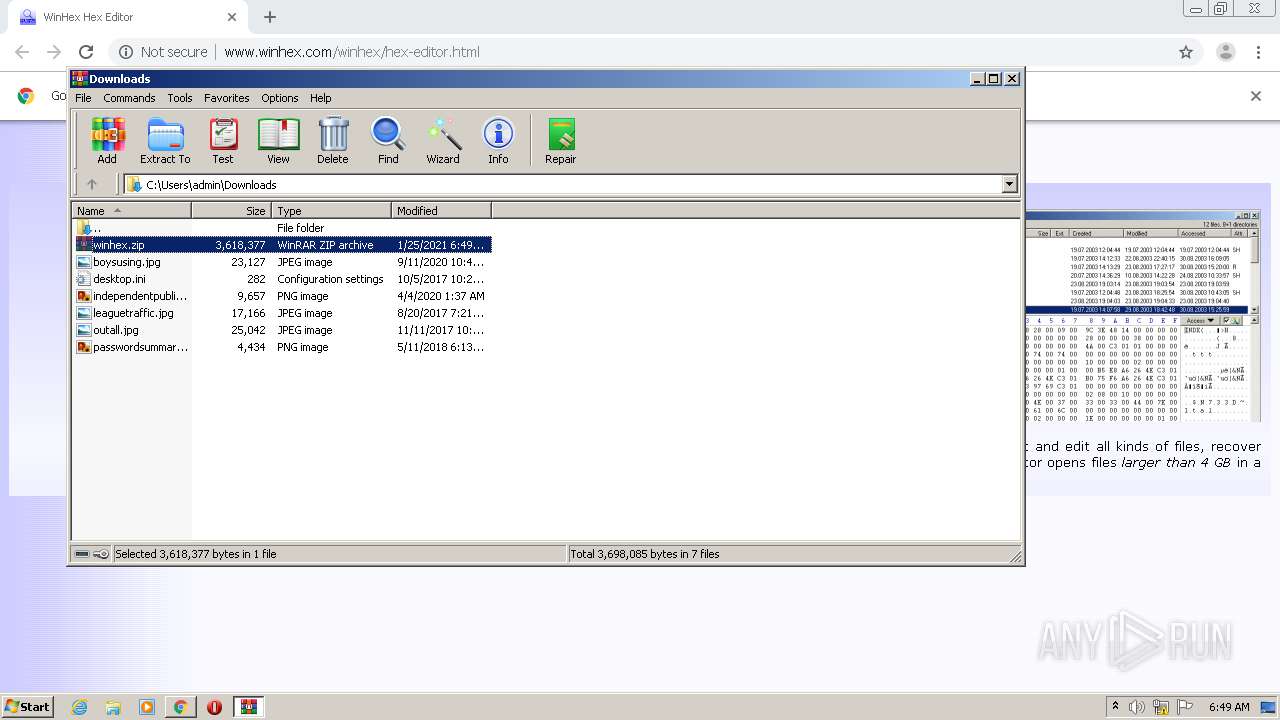
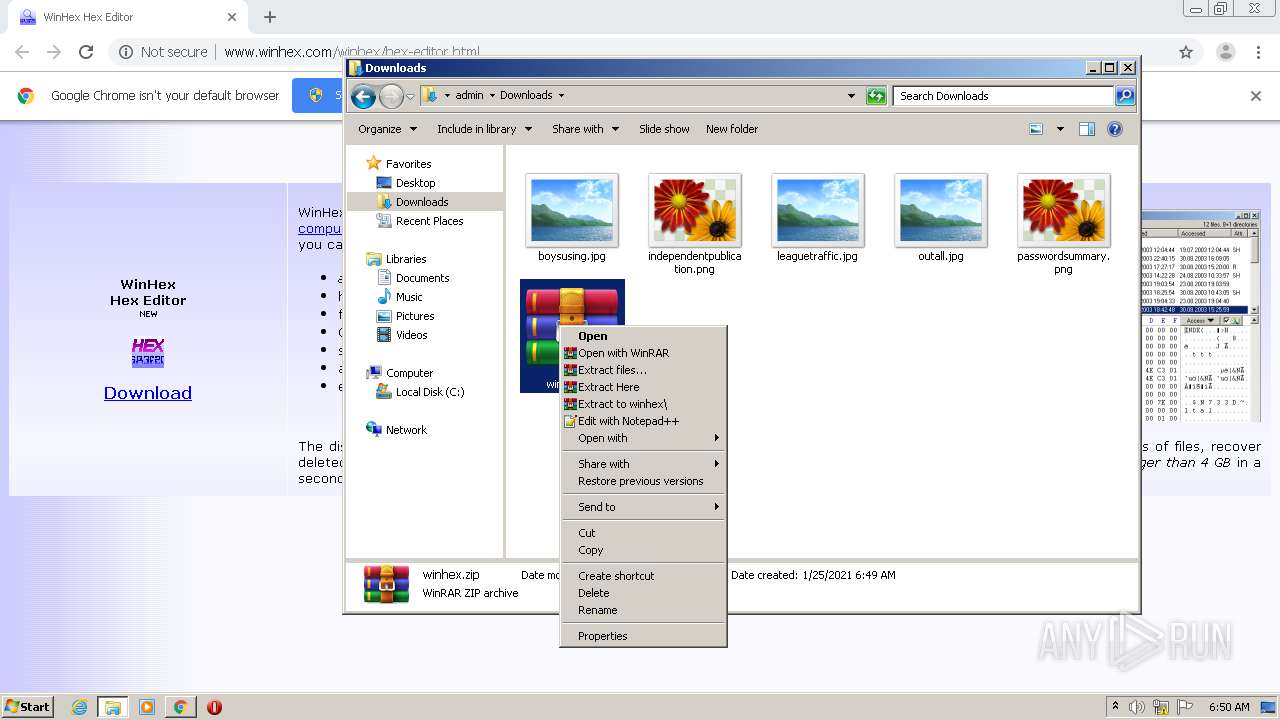
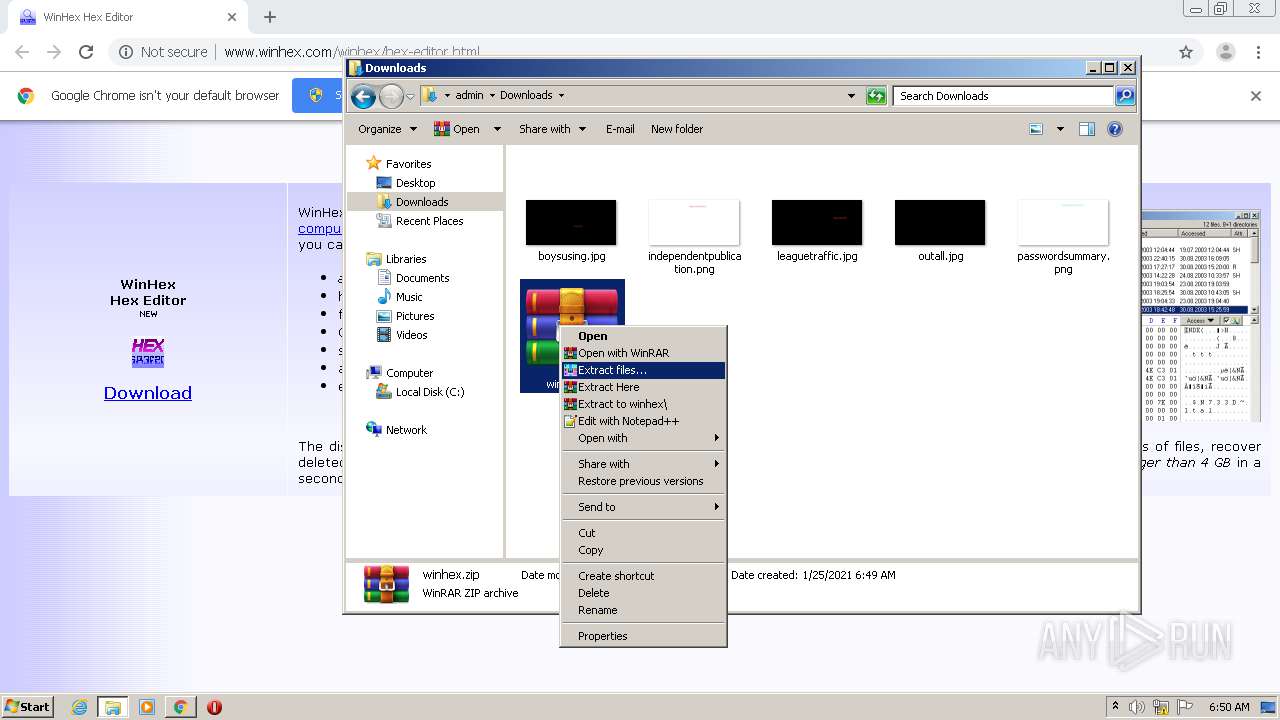
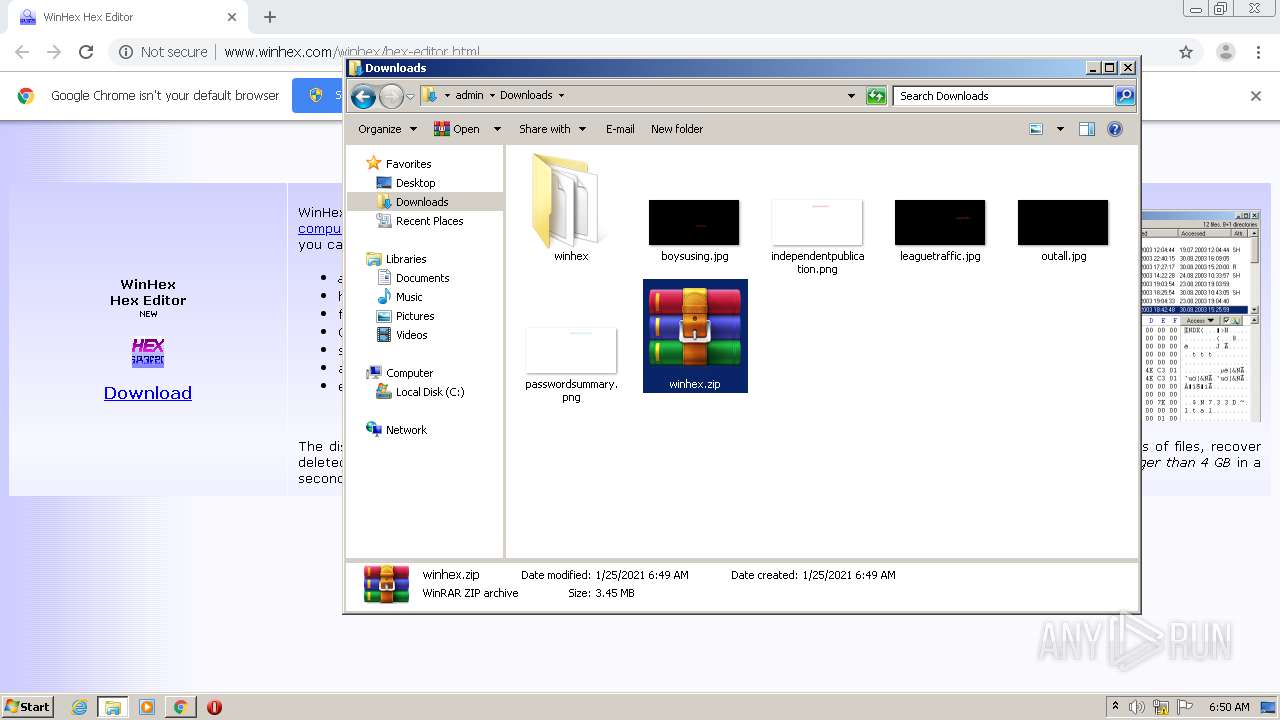
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2600)
- Dokan.exe (PID: 1844)
Drops a file with too old compile date
- WinRAR.exe (PID: 2600)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2600)
Drops a file that was compiled in debug mode
- Dokan.exe (PID: 1844)
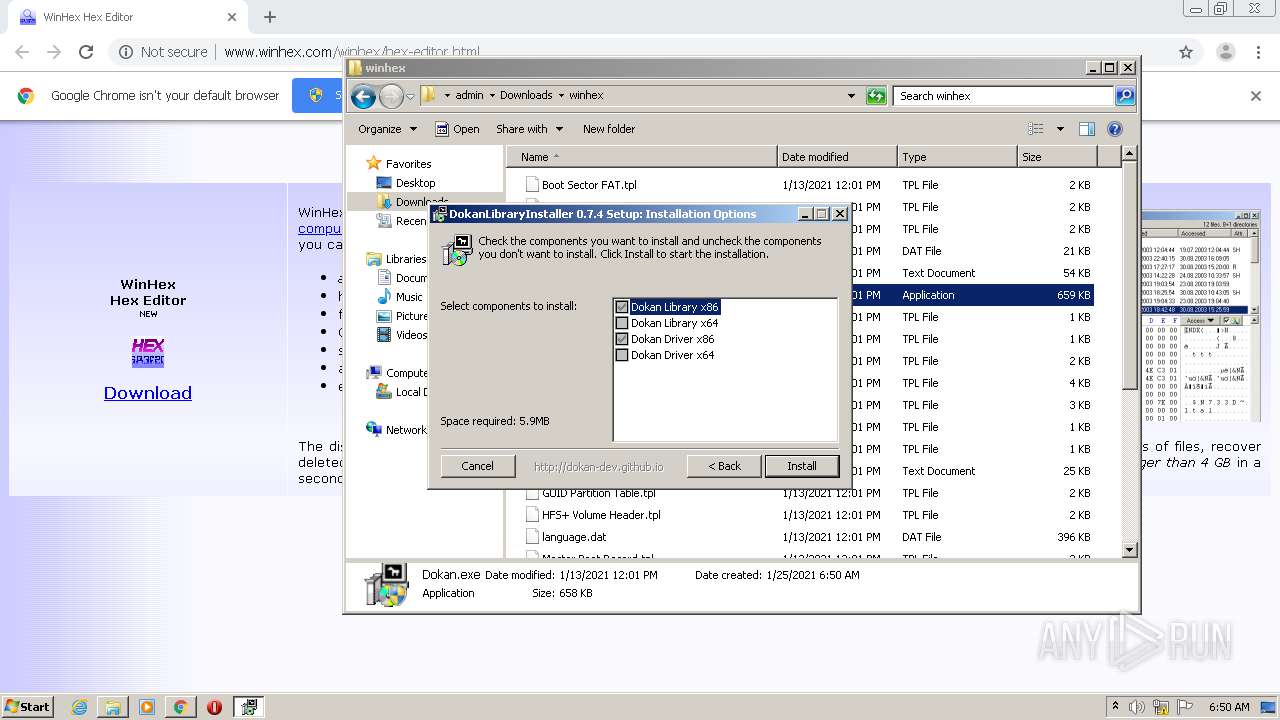
Creates a directory in Program Files
- Dokan.exe (PID: 1844)
Creates files in the program directory
- Dokan.exe (PID: 1844)
Creates files in the Windows directory
- Dokan.exe (PID: 1844)
Creates files in the driver directory
- Dokan.exe (PID: 1844)
Executed as Windows Service
- mounter.exe (PID: 672)
Creates a software uninstall entry
- Dokan.exe (PID: 1844)
INFO
Application launched itself
- chrome.exe (PID: 980)
Reads the hosts file
- chrome.exe (PID: 2232)
- chrome.exe (PID: 980)
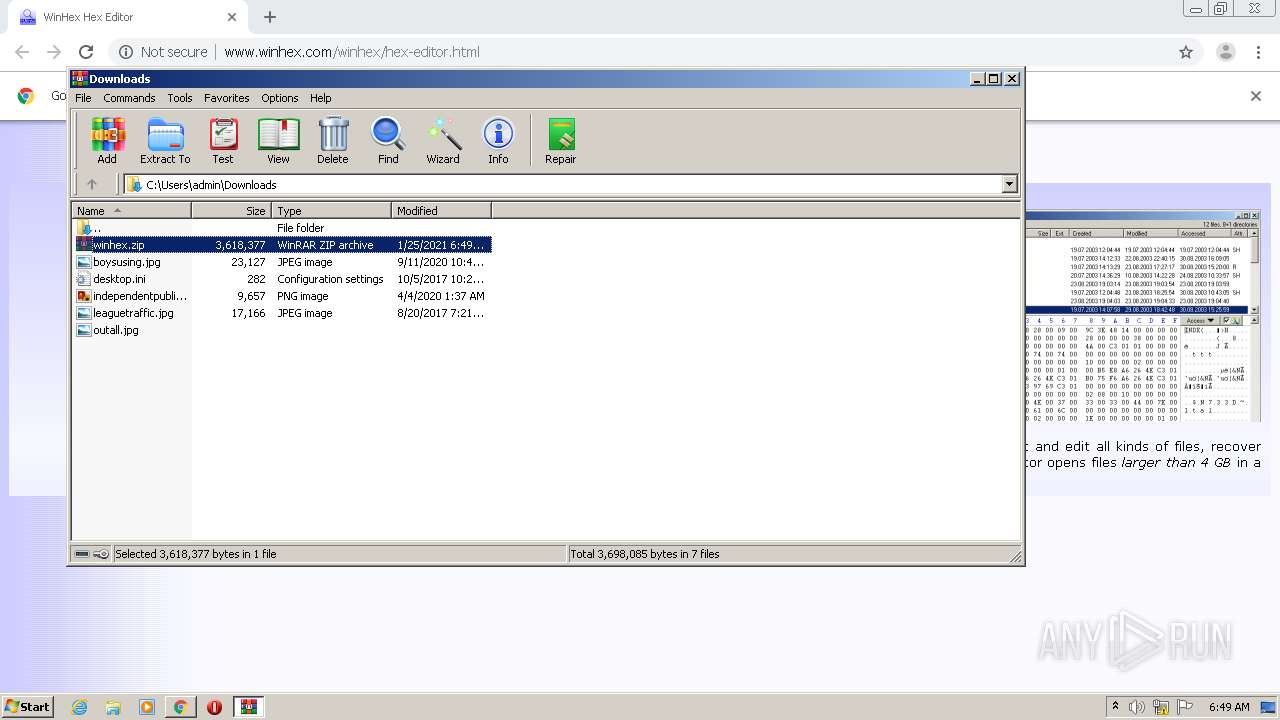
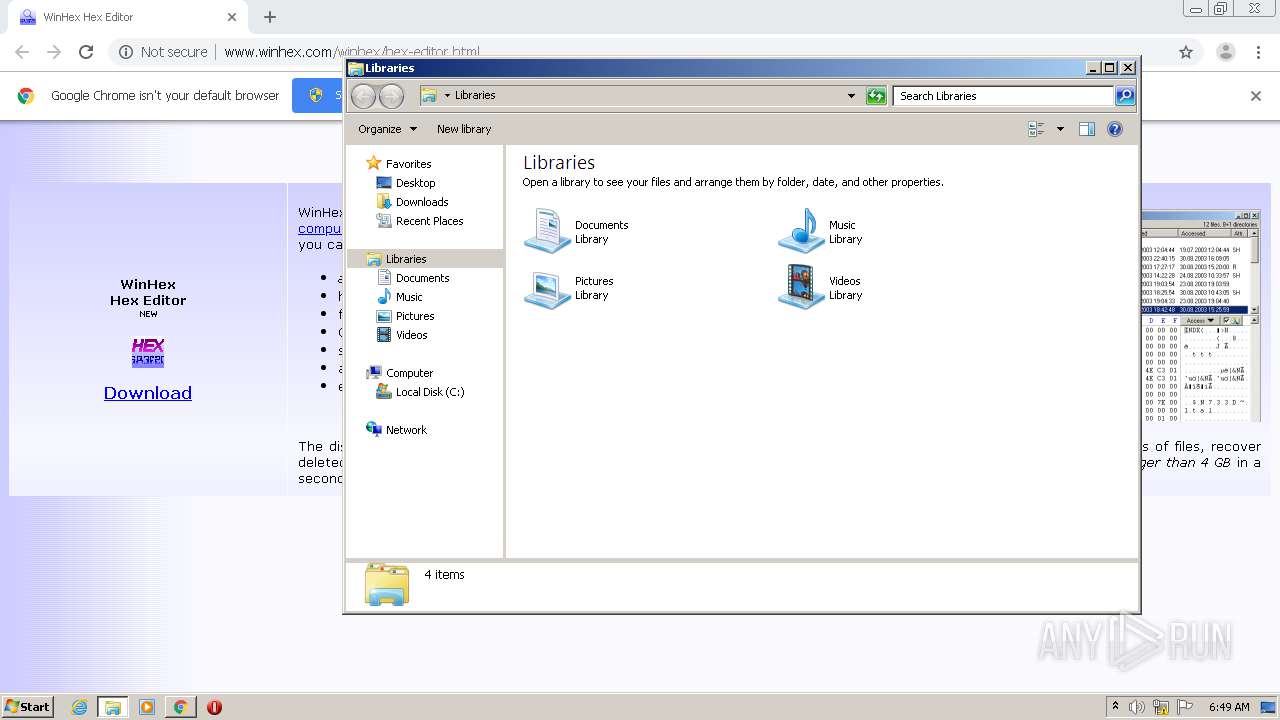
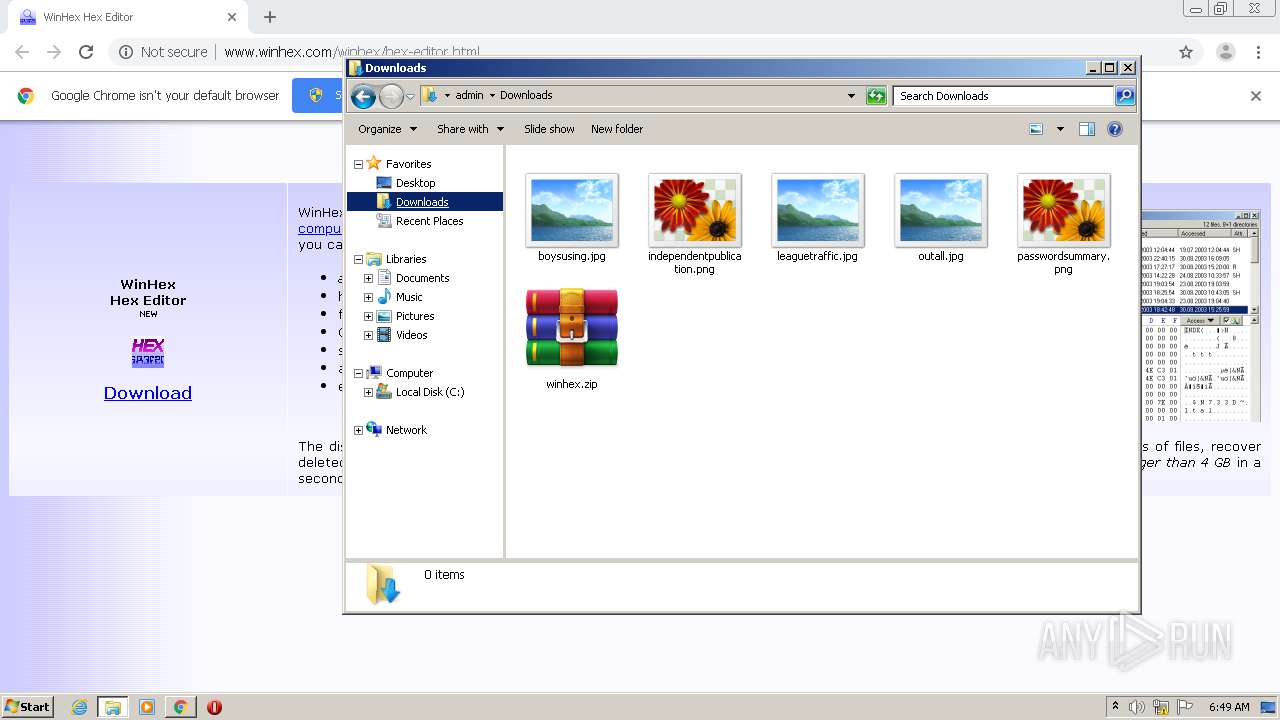
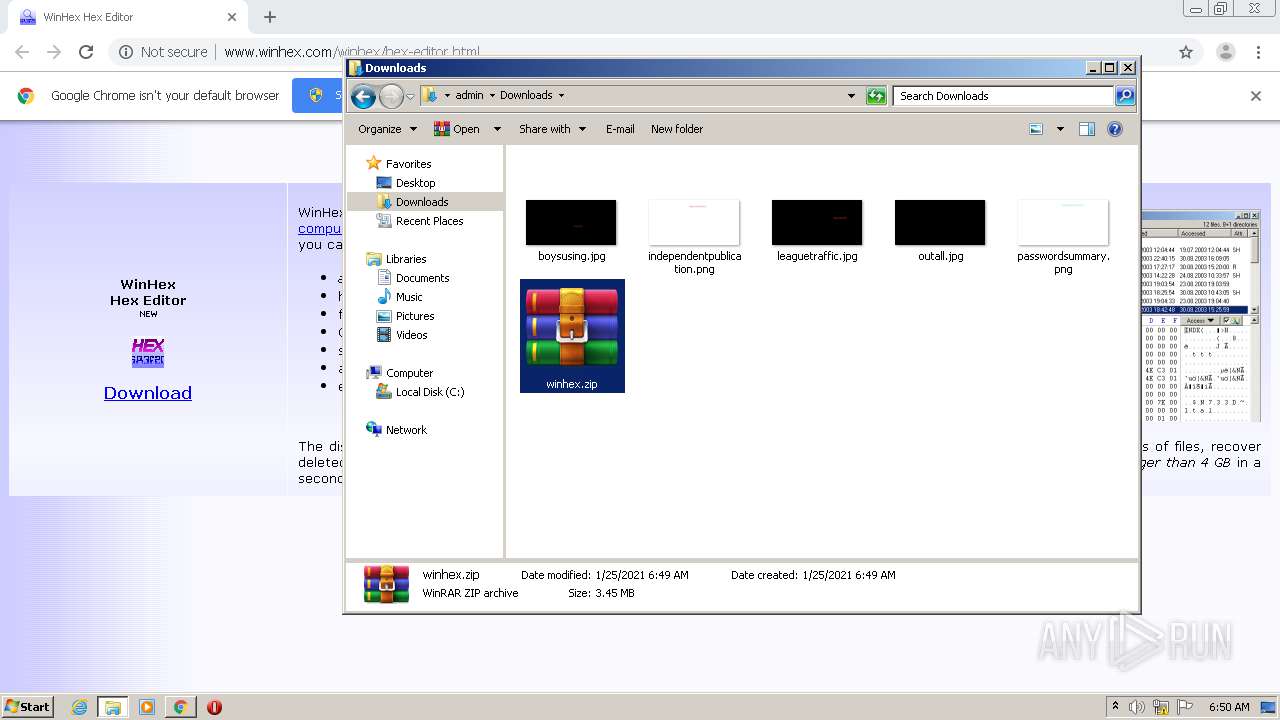
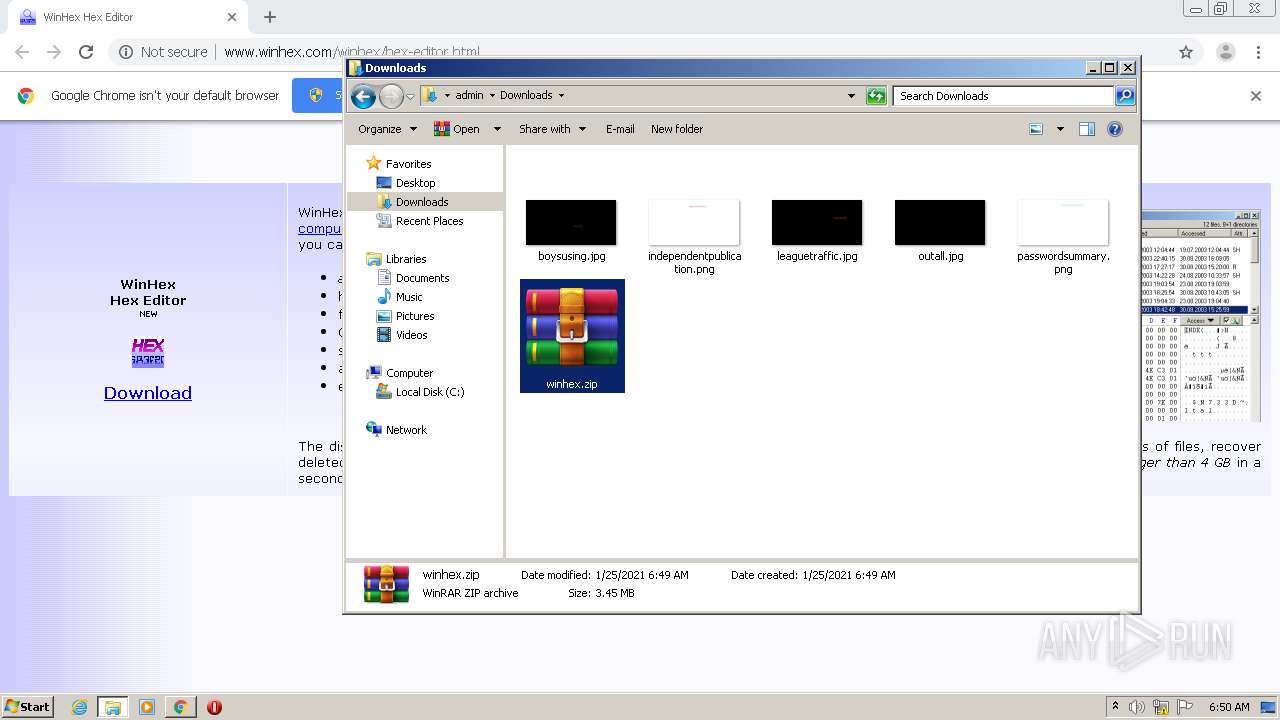
Manual execution by user
- explorer.exe (PID: 2036)
- WinRAR.exe (PID: 2600)
- Dokan.exe (PID: 1144)
- Dokan.exe (PID: 1844)
- winhex.exe (PID: 3072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
21
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
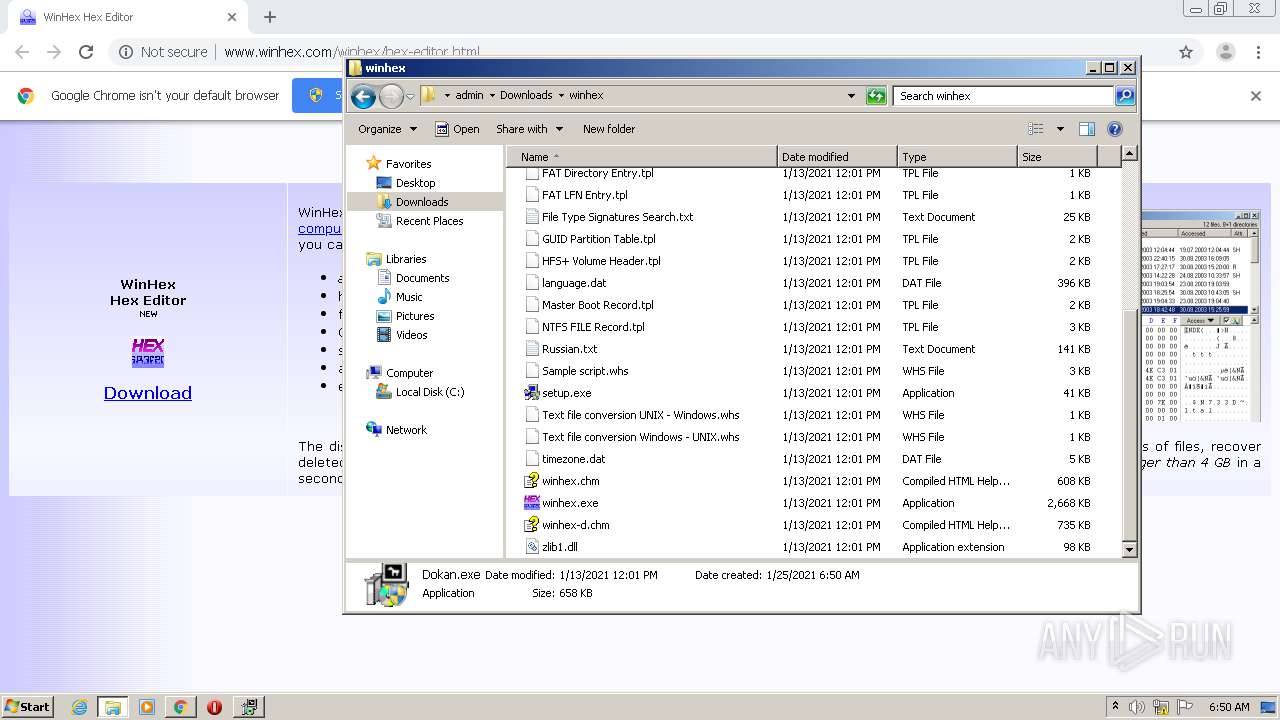
| 672 | "C:\Program Files\Dokan\DokanLibrary\mounter.exe" | C:\Program Files\Dokan\DokanLibrary\mounter.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://www.winhex.com/winhex/hex-editor.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | "C:\Users\admin\Downloads\winhex\Dokan.exe" | C:\Users\admin\Downloads\winhex\Dokan.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,5112202023172859284,10192765814199792984,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18167435843603898109 --mojo-platform-channel-handle=3576 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5112202023172859284,10192765814199792984,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15692718021078419041 --mojo-platform-channel-handle=2864 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5112202023172859284,10192765814199792984,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2023316320735013558 --mojo-platform-channel-handle=1088 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Dokan\DokanLibrary\dokanctl.exe" /i n | C:\Program Files\Dokan\DokanLibrary\dokanctl.exe | — | Dokan.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1844 | "C:\Users\admin\Downloads\winhex\Dokan.exe" | C:\Users\admin\Downloads\winhex\Dokan.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,5112202023172859284,10192765814199792984,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15386617675388108947 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2036 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 194
Read events
2 085
Write events
106
Delete events
3
Modification events
| (PID) Process: | (980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 980-13256030959087375 |
Value: 259 | |||
| (PID) Process: | (980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (980) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
13
Suspicious files
14
Text files
111
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-600E69EF-3D4.pma | — | |
MD5:— | SHA256:— | |||
| 980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e6b88d10-722b-4d9b-81ee-9fb0a69ea319.tmp | — | |
MD5:— | SHA256:— | |||
| 980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
| 980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
| 980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:67F45CAA18C889645F50CD6216C81E65 | SHA256:33ED82CDDDFFD55A5059C147C6CD20F66C6712314F890A39576D3C10914D0029 | |||
| 980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:F1220A80653B6B89B42DFD1B2E8155C3 | SHA256:36BBBC13CC1901CF269B4CE36E2EE08946806DFA58474AE88287CA8E9DA9725D | |||
| 980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1543c9.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
11
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
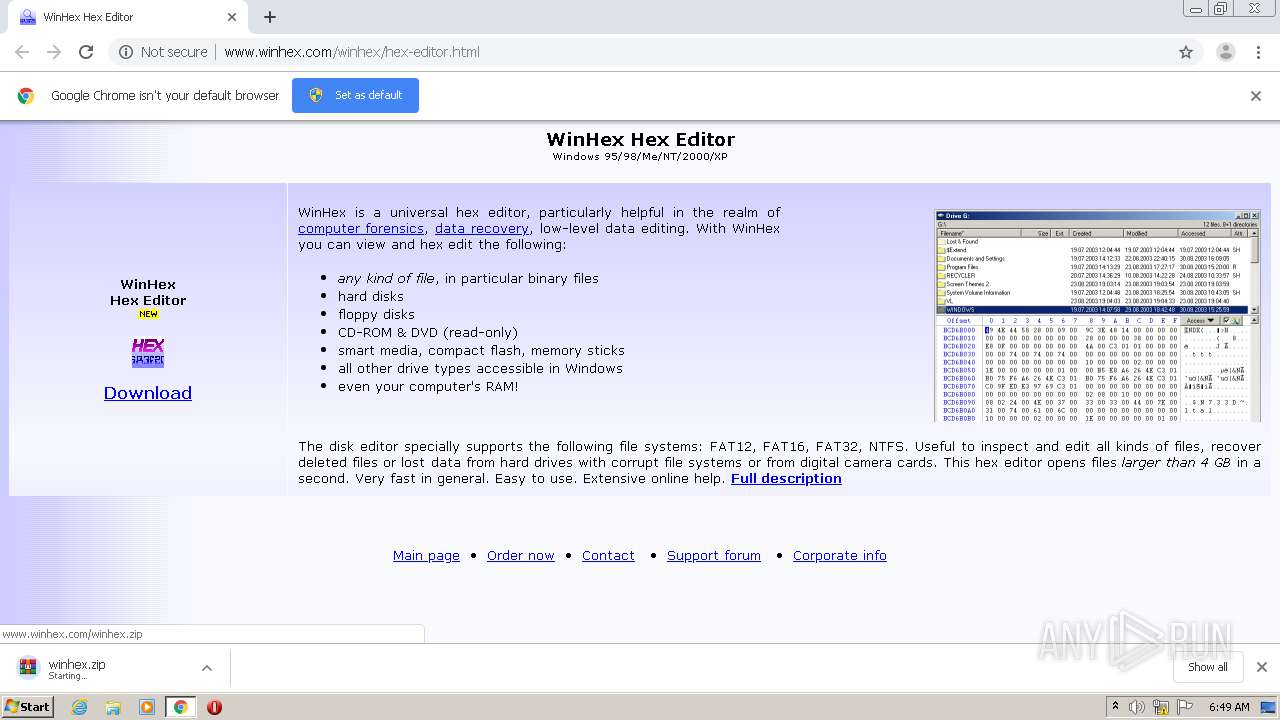
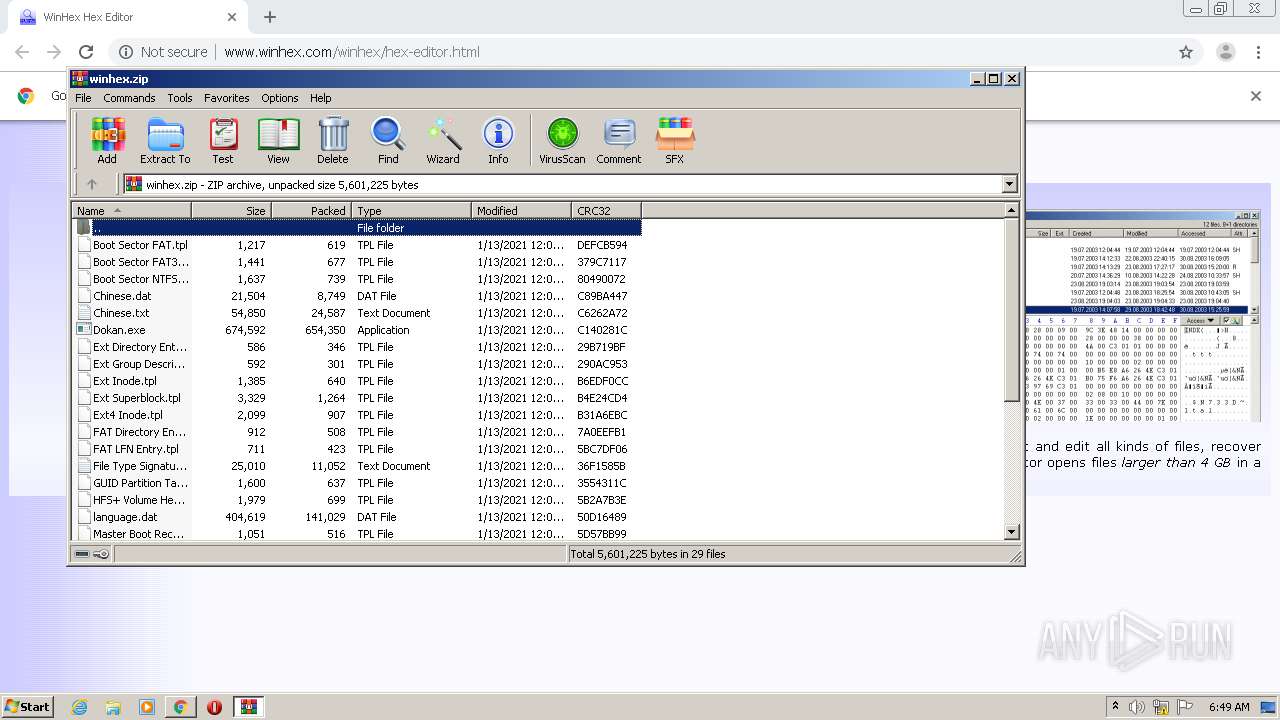
2232 | chrome.exe | GET | 200 | 217.160.0.81:80 | http://www.winhex.com/winhex.zip | DE | compressed | 3.45 Mb | malicious |
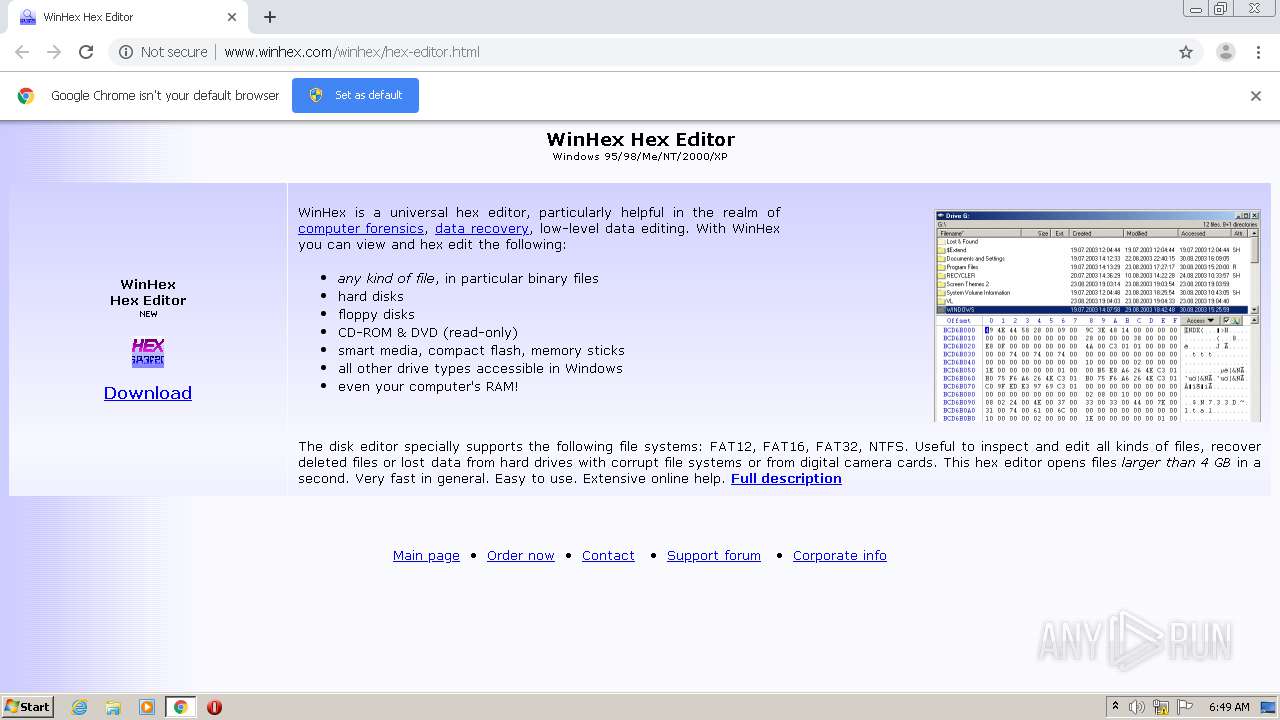
2232 | chrome.exe | GET | 200 | 217.160.0.81:80 | http://www.winhex.com/winhex/hex-editor.html | DE | html | 1.48 Kb | malicious |
2232 | chrome.exe | GET | 200 | 217.160.0.81:80 | http://www.winhex.com/pics/windows.gif | DE | image | 1.05 Kb | malicious |
2232 | chrome.exe | GET | 200 | 217.160.0.81:80 | http://www.winhex.com/pics/hex.gif | DE | image | 1.22 Kb | malicious |
2232 | chrome.exe | GET | 200 | 217.160.0.81:80 | http://www.winhex.com/pics/new.gif | DE | image | 1.74 Kb | malicious |
2232 | chrome.exe | GET | 200 | 217.160.0.81:80 | http://www.winhex.com/pics/hex-editor.gif | DE | image | 19.4 Kb | malicious |
2232 | chrome.exe | GET | 200 | 217.160.0.81:80 | http://www.winhex.com/pics/blue.gif | DE | image | 1.11 Kb | malicious |
2232 | chrome.exe | GET | 200 | 217.160.0.81:80 | http://www.winhex.com/pics/blue2.gif | DE | image | 1.21 Kb | malicious |
2232 | chrome.exe | GET | 200 | 217.160.0.81:80 | http://www.winhex.com/favicon.ico | DE | mpg | 1.37 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2232 | chrome.exe | 217.160.0.81:80 | www.winhex.com | 1&1 Internet SE | DE | malicious |
2232 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2232 | chrome.exe | 172.217.16.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3072 | winhex.exe | 142.250.184.131:443 | google.de | Google Inc. | US | whitelisted |
2232 | chrome.exe | 142.250.125.84:443 | accounts.google.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.winhex.com |
| malicious |
accounts.google.com |
| shared |
www.winhex.net |
| malicious |
www.x-ways.net |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
google.de |
| whitelisted |
Threats
Process | Message |
|---|---|
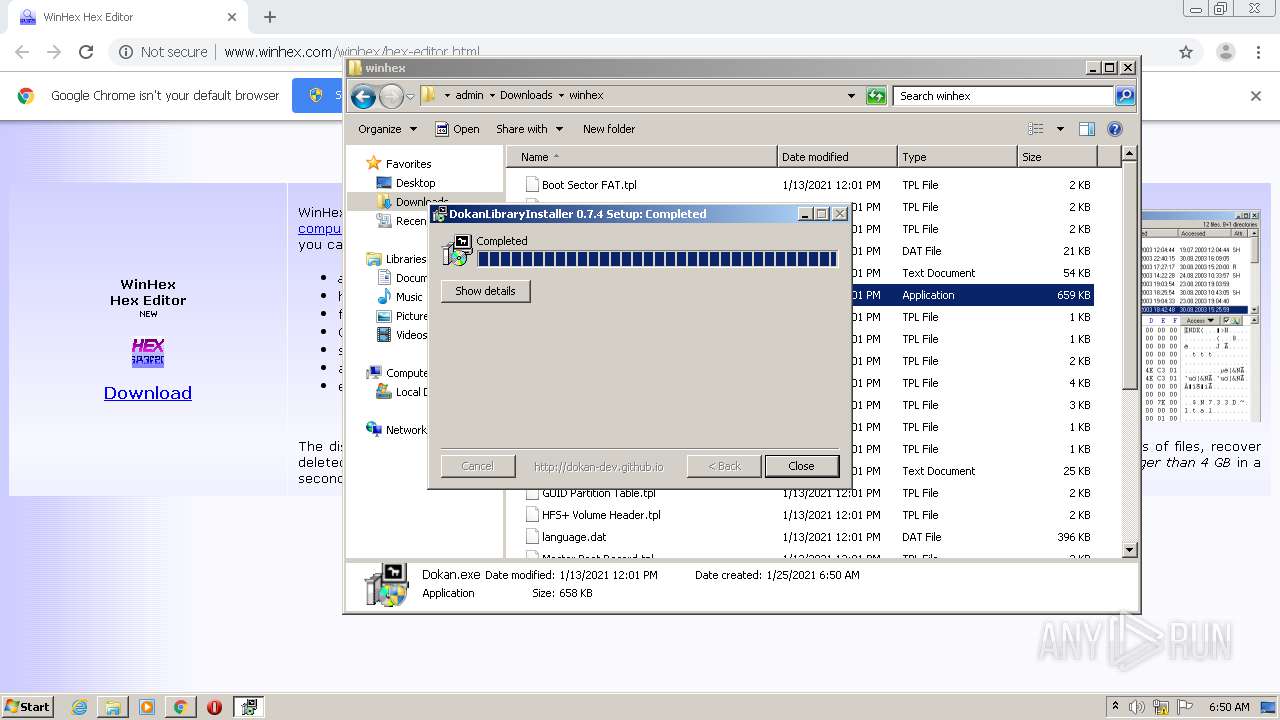
dokanctl.exe | Service (Dokan) installed
|
dokanctl.exe | Service (Dokan) started
|
dokanctl.exe | Service (Dokan) started
|
dokanctl.exe | Service (DokanMounter) installed
|
dokanctl.exe | Service (DokanMounter) started
|
dokanctl.exe | Service (DokanMounter) started
|