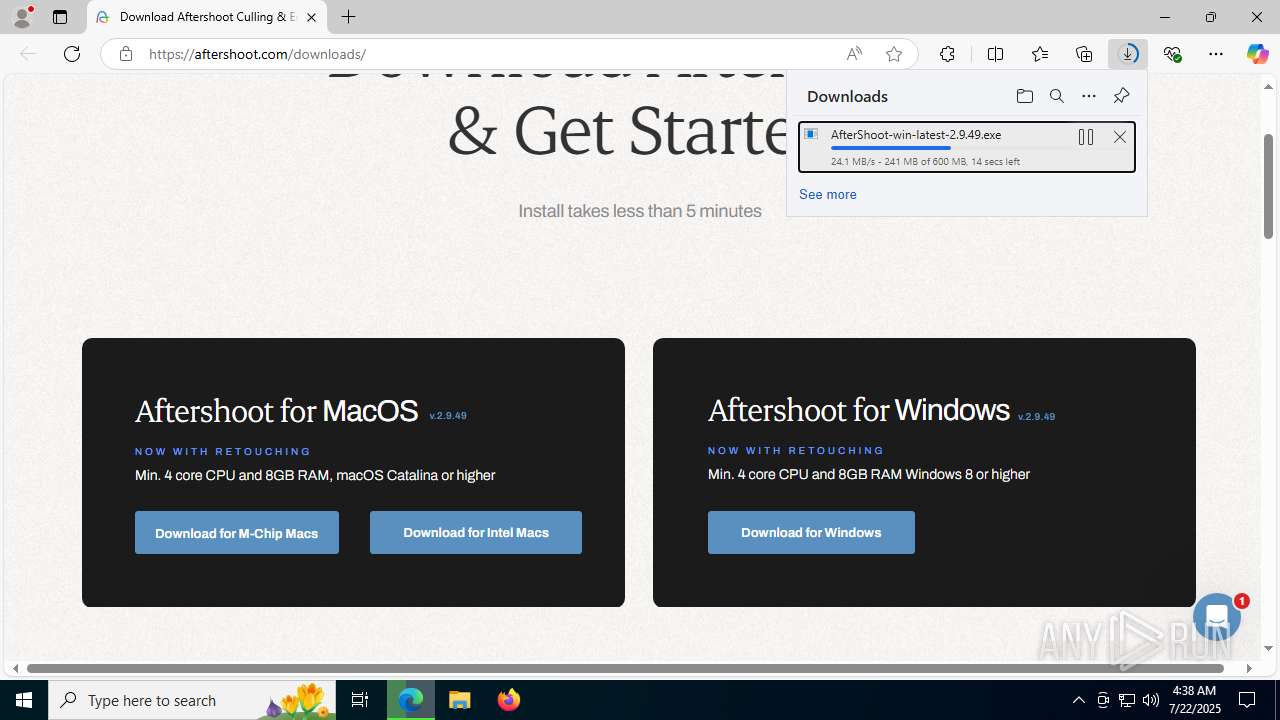
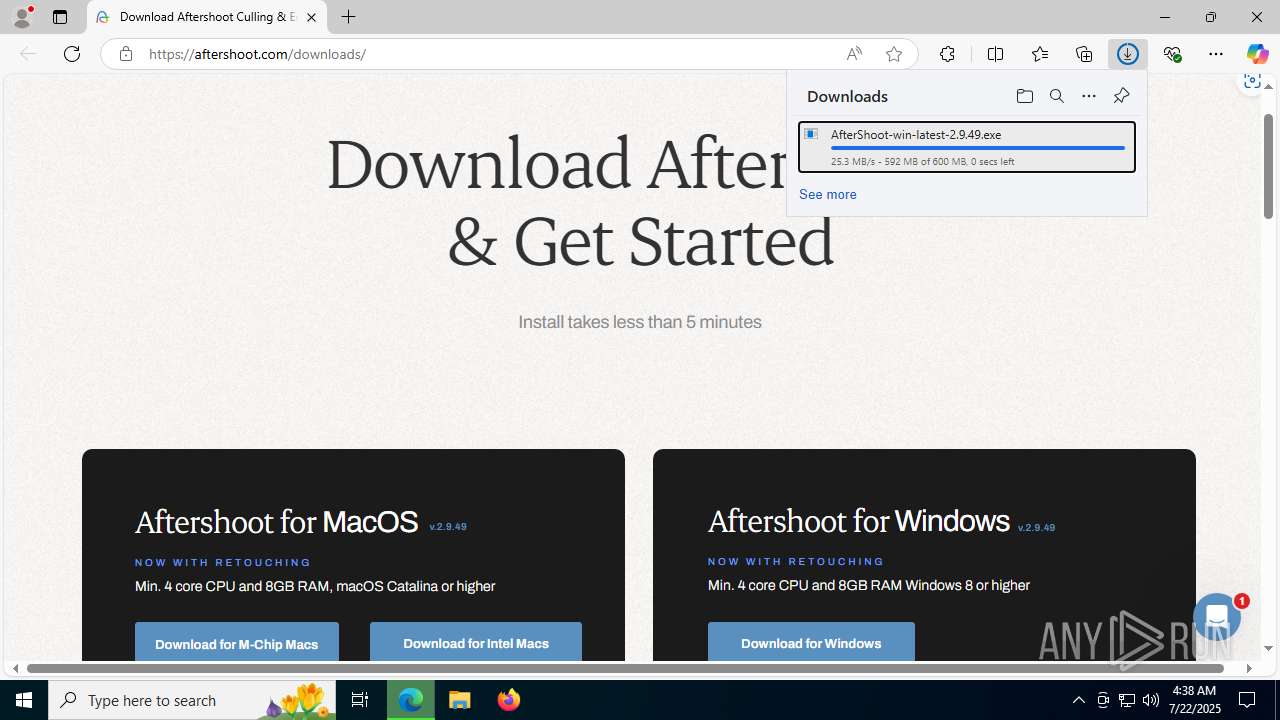
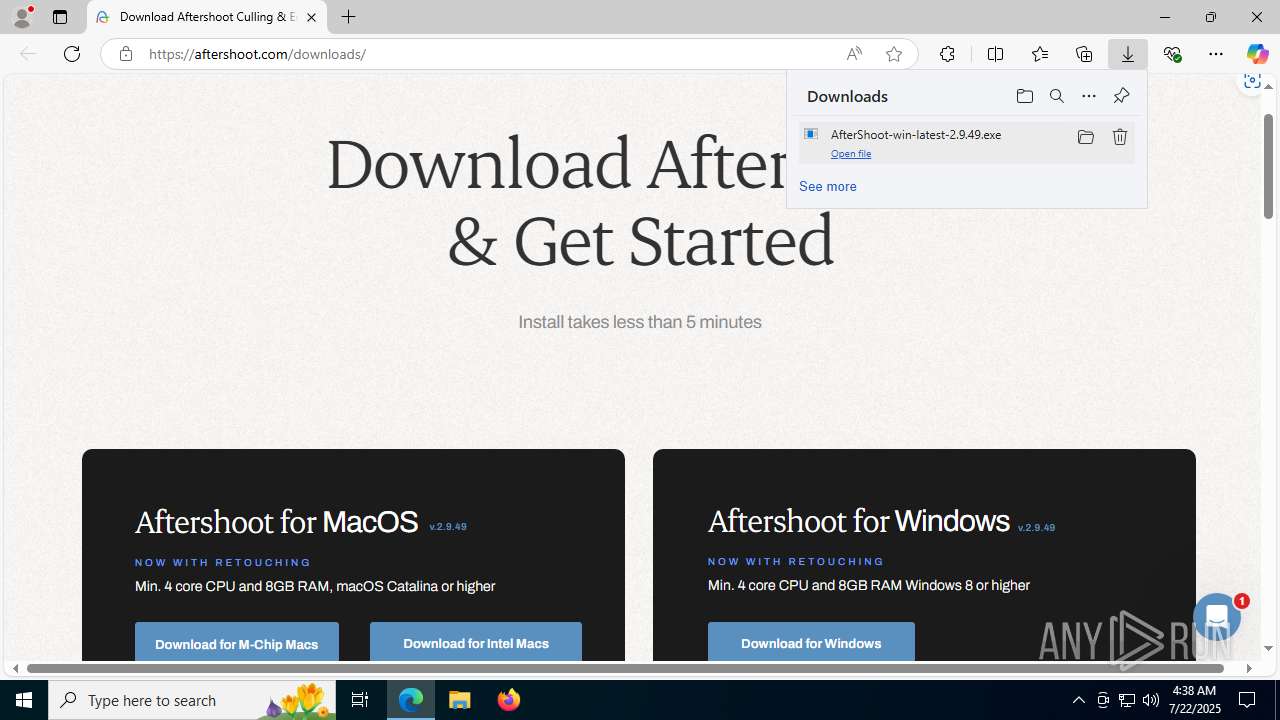
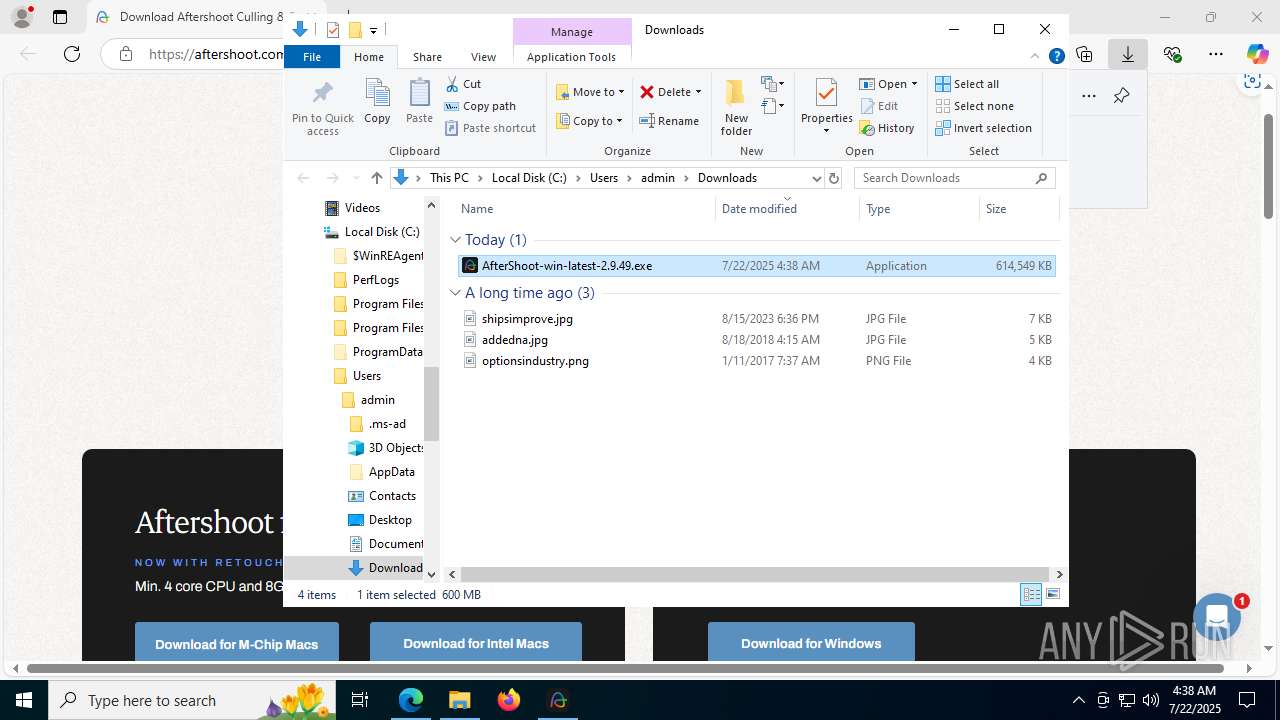
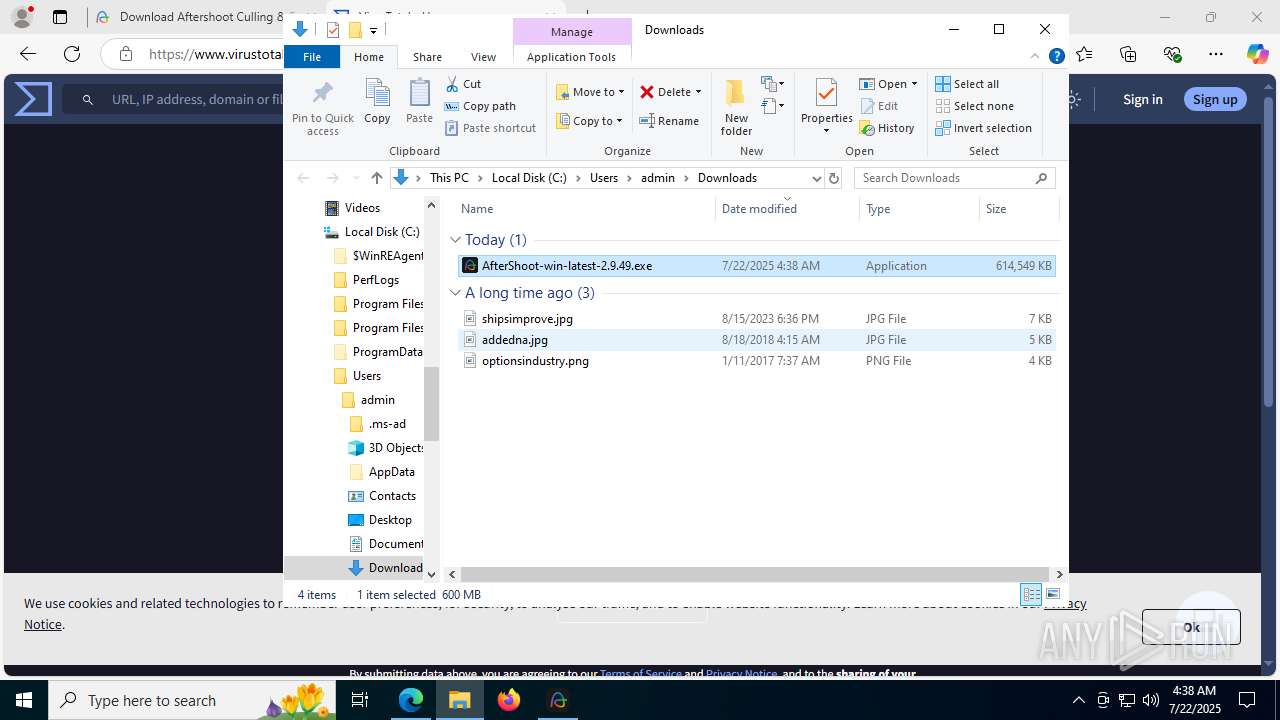
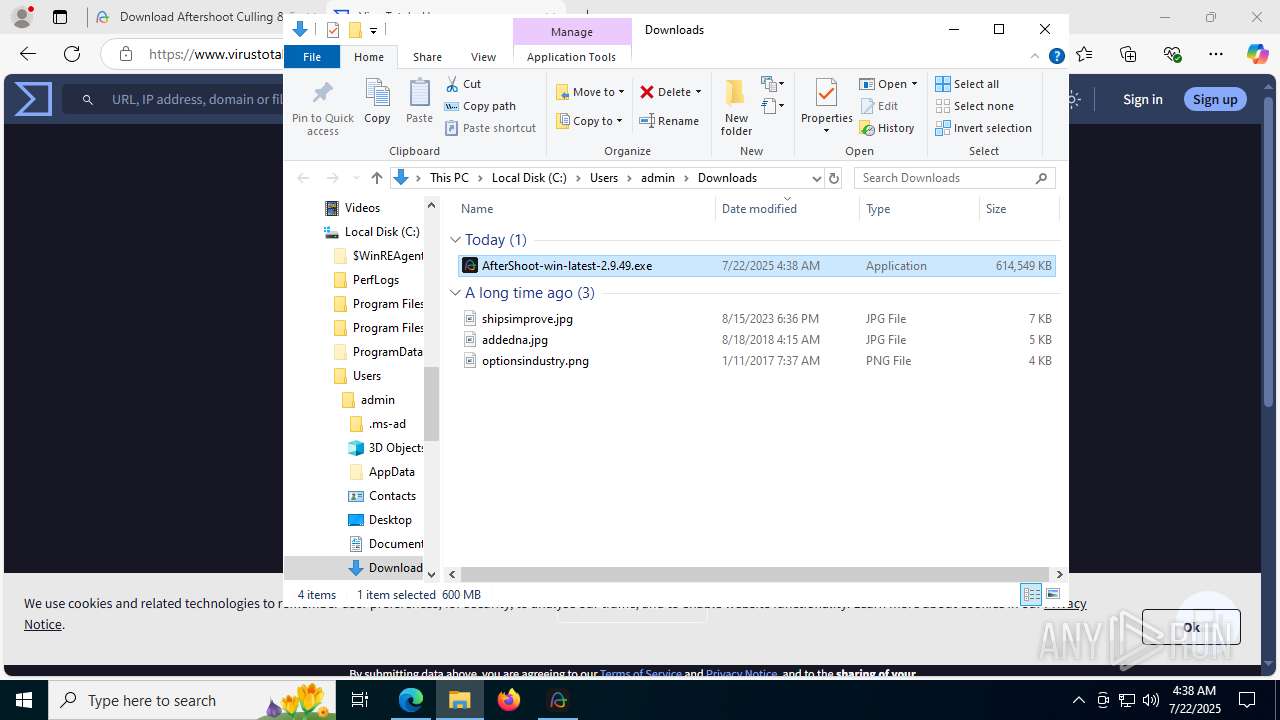
| URL: | https://aftershoot.com/downloads/ |
| Full analysis: | https://app.any.run/tasks/fe4e994d-52b2-4084-b345-0bd8628c2000 |
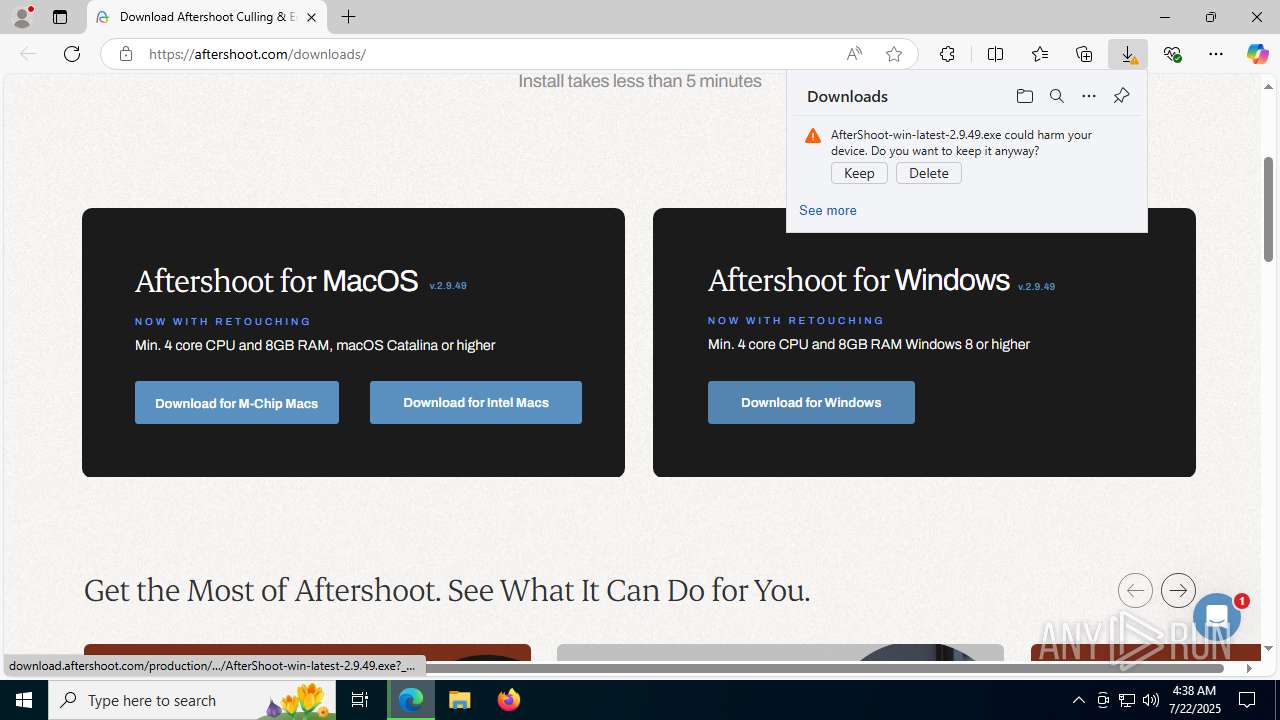
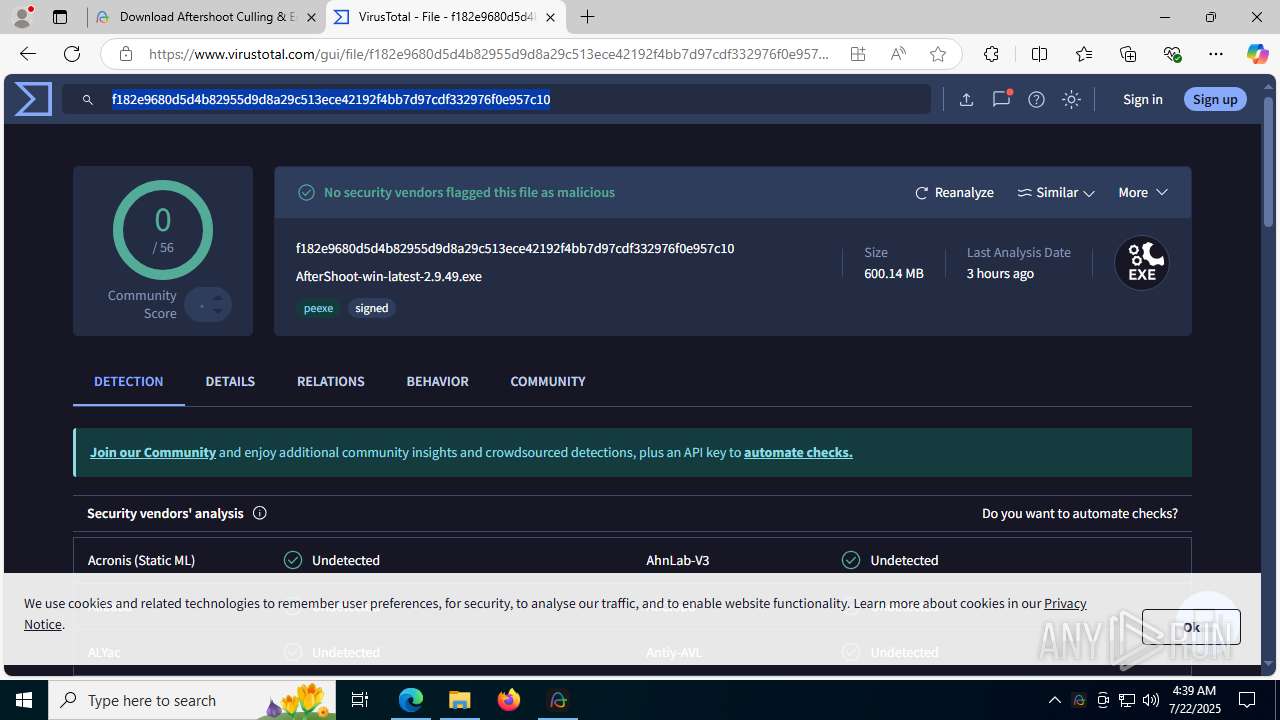
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2025, 04:37:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
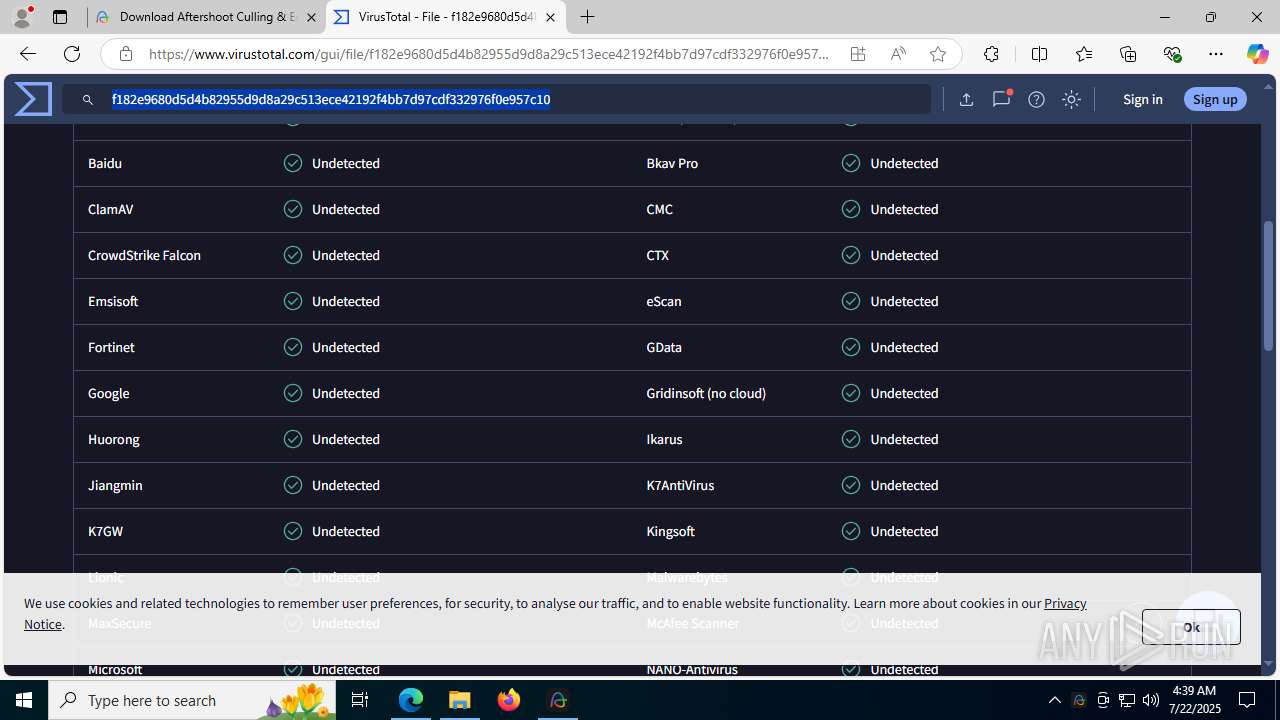
| MD5: | 53D428CC76FD7EB4B6BA3E8FFDA4E2FF |
| SHA1: | 0084346BFDA97B8D831158069A10030ABAFF37B5 |
| SHA256: | 8FE0EC71A98EC19EF6B3ED990E0BB745CEB3F57B445750200A4BAC53F1E4A91E |
| SSDEEP: | 3:N8RwmXKn:2qman |
MALICIOUS
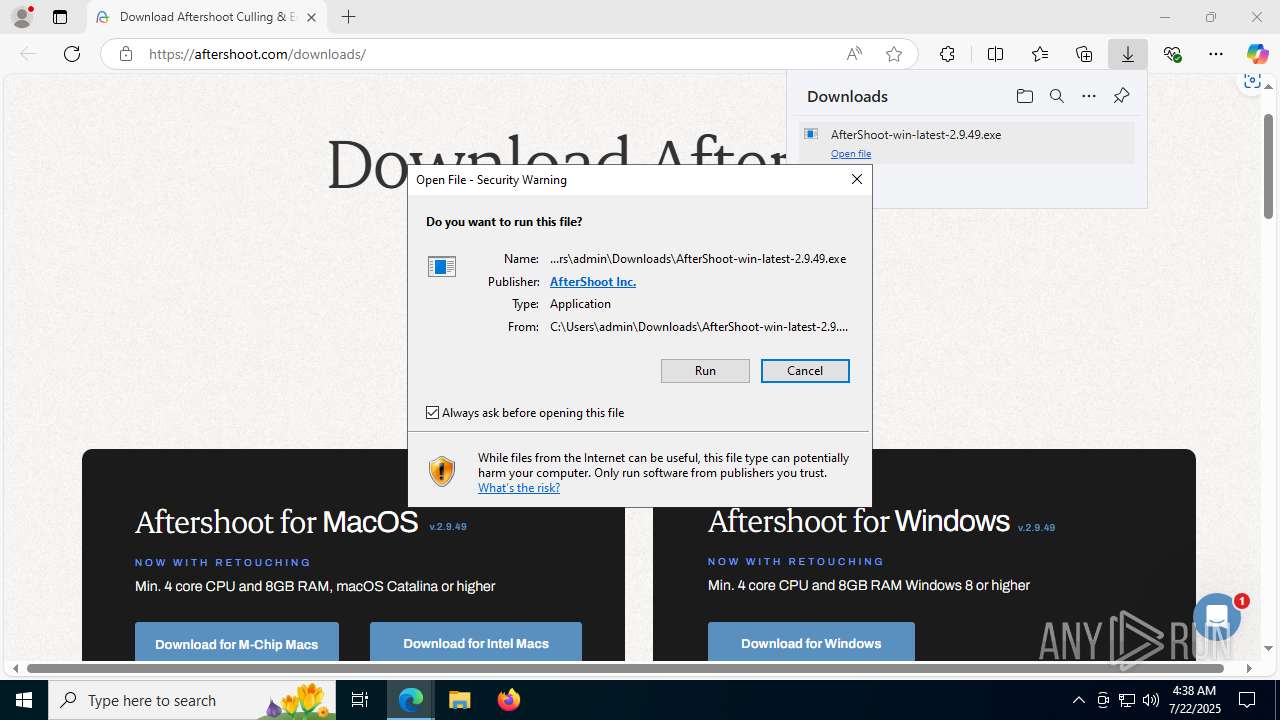
Executing a file with an untrusted certificate
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
- aftershoot-backend.exe (PID: 9072)
Changes powershell execution policy (Unrestricted)
- AfterShoot.exe (PID: 1512)
Run PowerShell with an invisible window
- powershell.exe (PID: 10060)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
Drops 7-zip archiver for unpacking
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
There is functionality for taking screenshot (YARA)
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
The process creates files with name similar to system file names
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
Reads security settings of Internet Explorer
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
- AfterShoot.exe (PID: 9268)
Process drops legitimate windows executable
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
Executable content was dropped or overwritten
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
The process drops C-runtime libraries
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
Process drops SQLite DLL files
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
Creates a software uninstall entry
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
Starts application with an unusual extension
- cmd.exe (PID: 4820)
- cmd.exe (PID: 8808)
Starts CMD.EXE for commands execution
- AfterShoot.exe (PID: 1512)
- NETSTAT.EXE (PID: 8848)
- NETSTAT.EXE (PID: 1932)
- AfterShoot.exe (PID: 12064)
- NETSTAT.EXE (PID: 11936)
Application launched itself
- AfterShoot.exe (PID: 1512)
- AfterShoot.exe (PID: 12064)
Starts POWERSHELL.EXE for commands execution
- AfterShoot.exe (PID: 1512)
- aftershoot-backend.exe (PID: 9072)
The process bypasses the loading of PowerShell profile settings
- AfterShoot.exe (PID: 1512)
The process hides Powershell's copyright startup banner
- AfterShoot.exe (PID: 1512)
Likely accesses (executes) a file from the Public directory
- aftershoot-backend.exe (PID: 9072)
Lists computer manufacturer and model
- aftershoot-backend.exe (PID: 9072)
The process checks if it is being run in the virtual environment
- aftershoot-backend.exe (PID: 9072)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 7580)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 11184)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8624)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 11168)
Executes as Windows Service
- WmiApSrv.exe (PID: 10936)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 8676)
INFO
Reads the computer name
- identity_helper.exe (PID: 7788)
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
- AfterShoot.exe (PID: 1512)
- AfterShoot.exe (PID: 7944)
- AfterShoot.exe (PID: 7784)
- aftershoot-backend.exe (PID: 9072)
- AfterShoot.exe (PID: 9268)
- AfterShoot.exe (PID: 12048)
- AfterShoot.exe (PID: 12064)
- AfterShoot.exe (PID: 7096)
- AfterShoot.exe (PID: 7284)
Checks supported languages
- identity_helper.exe (PID: 7788)
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
- AfterShoot.exe (PID: 1512)
- AfterShoot.exe (PID: 7944)
- chcp.com (PID: 8180)
- AfterShoot.exe (PID: 1480)
- AfterShoot.exe (PID: 9056)
- AfterShoot.exe (PID: 9044)
- AfterShoot.exe (PID: 9268)
- AfterShoot.exe (PID: 9280)
- AfterShoot.exe (PID: 7784)
- aftershoot-backend.exe (PID: 9072)
- AfterShoot.exe (PID: 12048)
- AfterShoot.exe (PID: 12064)
- AfterShoot.exe (PID: 7096)
- chcp.com (PID: 9028)
- AfterShoot.exe (PID: 9152)
- AfterShoot.exe (PID: 7284)
The sample compiled with english language support
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
Application launched itself
- msedge.exe (PID: 2804)
- msedge.exe (PID: 9080)
Executable content was dropped or overwritten
- msedge.exe (PID: 2804)
Reads Environment values
- identity_helper.exe (PID: 7788)
- AfterShoot.exe (PID: 1512)
- AfterShoot.exe (PID: 9280)
- aftershoot-backend.exe (PID: 9072)
- AfterShoot.exe (PID: 9268)
- AfterShoot.exe (PID: 12064)
- AfterShoot.exe (PID: 7944)
Create files in a temporary directory
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
- AfterShoot.exe (PID: 1512)
- powershell.exe (PID: 10060)
- aftershoot-backend.exe (PID: 9072)
Creates files or folders in the user directory
- AfterShoot-win-latest-2.9.49.exe (PID: 1964)
- AfterShoot.exe (PID: 1512)
- AfterShoot.exe (PID: 1480)
- AfterShoot.exe (PID: 7784)
- aftershoot-backend.exe (PID: 9072)
- AfterShoot.exe (PID: 9268)
- AfterShoot.exe (PID: 12048)
- AfterShoot.exe (PID: 9152)
- AfterShoot.exe (PID: 7284)
Manual execution by a user
- AfterShoot.exe (PID: 1512)
Changes the display of characters in the console
- cmd.exe (PID: 4820)
- cmd.exe (PID: 8808)
Process checks computer location settings
- AfterShoot.exe (PID: 1512)
- AfterShoot.exe (PID: 9056)
- AfterShoot.exe (PID: 9044)
- AfterShoot.exe (PID: 9280)
- AfterShoot.exe (PID: 9268)
- AfterShoot.exe (PID: 12064)
Reads CPU info
- AfterShoot.exe (PID: 1512)
- AfterShoot.exe (PID: 12064)
Checks proxy server information
- AfterShoot.exe (PID: 1512)
- aftershoot-backend.exe (PID: 9072)
- slui.exe (PID: 7604)
- AfterShoot.exe (PID: 12064)
Reads product name
- AfterShoot.exe (PID: 1512)
- AfterShoot.exe (PID: 9280)
- aftershoot-backend.exe (PID: 9072)
- AfterShoot.exe (PID: 9268)
- AfterShoot.exe (PID: 12064)
Reads the machine GUID from the registry
- AfterShoot.exe (PID: 1512)
- AfterShoot.exe (PID: 12048)
- AfterShoot.exe (PID: 12064)
- AfterShoot.exe (PID: 7944)
Reads the software policy settings
- powershell.exe (PID: 10060)
- slui.exe (PID: 7604)
- aftershoot-backend.exe (PID: 9072)
Reads security settings of Internet Explorer
- powershell.exe (PID: 10060)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7800)
- powershell.exe (PID: 6288)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7156)
Node.js compiler has been detected
- AfterShoot.exe (PID: 1512)
- AfterShoot.exe (PID: 1480)
Prints a route via ROUTE.EXE
- ROUTE.EXE (PID: 7632)
- ROUTE.EXE (PID: 4312)
- ROUTE.EXE (PID: 11012)
Creates files in the program directory
- aftershoot-backend.exe (PID: 9072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
389
Monitored processes
237
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 480 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | AfterShoot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --always-read-main-dll --field-trial-handle=8008,i,14456594687532952999,455527981207285951,262144 --variations-seed-version --mojo-platform-channel-handle=7940 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=38 --always-read-main-dll --field-trial-handle=9032,i,14456594687532952999,455527981207285951,262144 --variations-seed-version --mojo-platform-channel-handle=7772 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=45 --always-read-main-dll --field-trial-handle=9144,i,14456594687532952999,455527981207285951,262144 --variations-seed-version --mojo-platform-channel-handle=8464 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=64 --always-read-main-dll --field-trial-handle=11116,i,14456594687532952999,455527981207285951,262144 --variations-seed-version --mojo-platform-channel-handle=11092 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3640,i,14456594687532952999,455527981207285951,262144 --variations-seed-version --mojo-platform-channel-handle=3668 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1332 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | AfterShoot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | C:\WINDOWS\system32\cmd.exe /d /s /c "%windir%\System32\REG.exe QUERY HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography /v MachineGuid" | C:\Windows\System32\cmd.exe | — | AfterShoot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=61 --always-read-main-dll --field-trial-handle=10912,i,14456594687532952999,455527981207285951,262144 --variations-seed-version --mojo-platform-channel-handle=10308 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
149 186
Read events
149 015
Write events
117
Delete events
54
Modification events
| (PID) Process: | (2804) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2804) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2804) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2804) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2804) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2804) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393914 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {098F659A-228F-47F4-AA9D-8A58244B4220} | |||
| (PID) Process: | (2804) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2804) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E258047013992F00 | |||
| (PID) Process: | (2804) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393914 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {38426FDE-5C1C-43F9-92FD-F7608F2A6D2E} | |||
| (PID) Process: | (2804) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393914 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AD4A1DF4-918B-4568-8B19-C420281FA0A2} | |||
Executable files
135
Suspicious files
5 063
Text files
274
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d0d8.TMP | — | |
MD5:— | SHA256:— | |||
| 2804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d0d8.TMP | — | |
MD5:— | SHA256:— | |||
| 2804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18d0d8.TMP | — | |
MD5:— | SHA256:— | |||
| 2804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d0e7.TMP | — | |
MD5:— | SHA256:— | |||
| 2804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d0e7.TMP | — | |
MD5:— | SHA256:— | |||
| 2804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d0e7.TMP | — | |
MD5:— | SHA256:— | |||
| 2804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
783
DNS requests
987
Threats
57
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6176 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:QDgUBA12ZYkDVQ_1VBo1bBvyIOjqj3Lg6XlJxrR8LLo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
72 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7868 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7868 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2804 | msedge.exe | GET | 200 | 18.173.205.113:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQg3SSkKA74hABkhmlBtJTz8w3hlAQU%2BWC71OPVNPa49QaAJadz20ZpqJ4CEEJLalPOx2YUHCpjsaUcQQQ%3D | unknown | — | — | whitelisted |
2804 | msedge.exe | GET | 200 | 18.173.205.113:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSoEwb5tith0jIBy9frSyNGB1lsAAQUNr1J%2FzEs669qQP6ZwBbtuvxI3V8CEFig8iI3%2FfdnIGaJ1VA7sRA%3D | unknown | — | — | whitelisted |
188 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753247659&P2=404&P3=2&P4=caRBG2MAVeX9SGihEs5K8M%2fSzqBCN7tzxk6r%2fMVDpJTBGJh7xoNjVe33Lfq35bzFPBQgyU3053e7IefbVew7Yg%3d%3d | unknown | — | — | whitelisted |
188 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753247659&P2=404&P3=2&P4=caRBG2MAVeX9SGihEs5K8M%2fSzqBCN7tzxk6r%2fMVDpJTBGJh7xoNjVe33Lfq35bzFPBQgyU3053e7IefbVew7Yg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6732 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6176 | msedge.exe | 104.18.24.24:443 | aftershoot.com | CLOUDFLARENET | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6176 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6176 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6176 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6176 | msedge.exe | 104.126.37.136:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
aftershoot.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdn-cookieyes.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
a.omappapi.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6176 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
6176 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
6176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6176 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
6176 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
6176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6176 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |