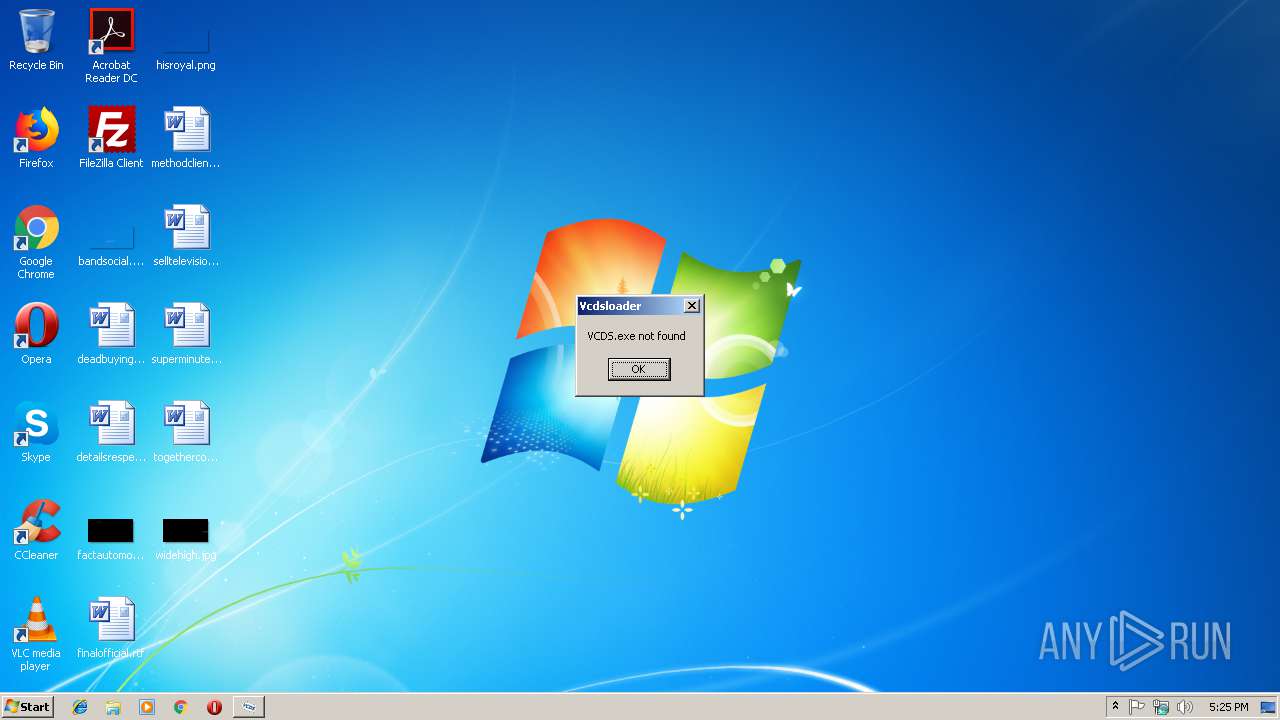
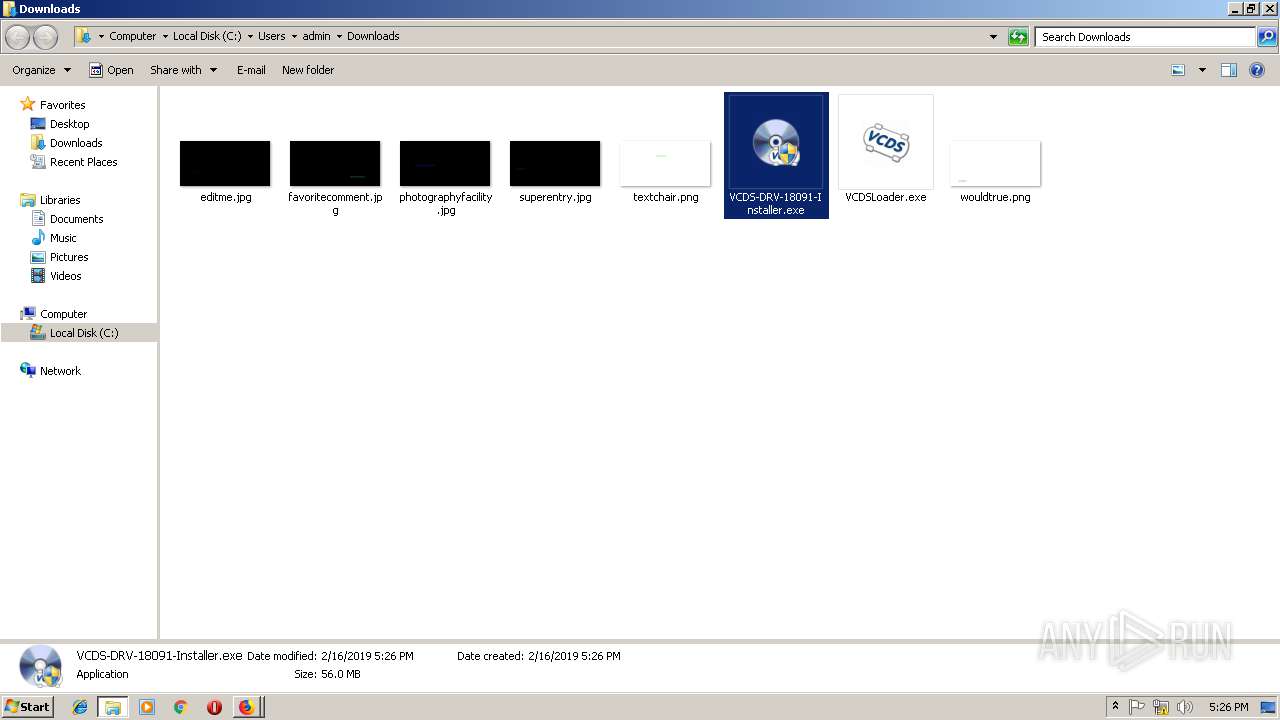
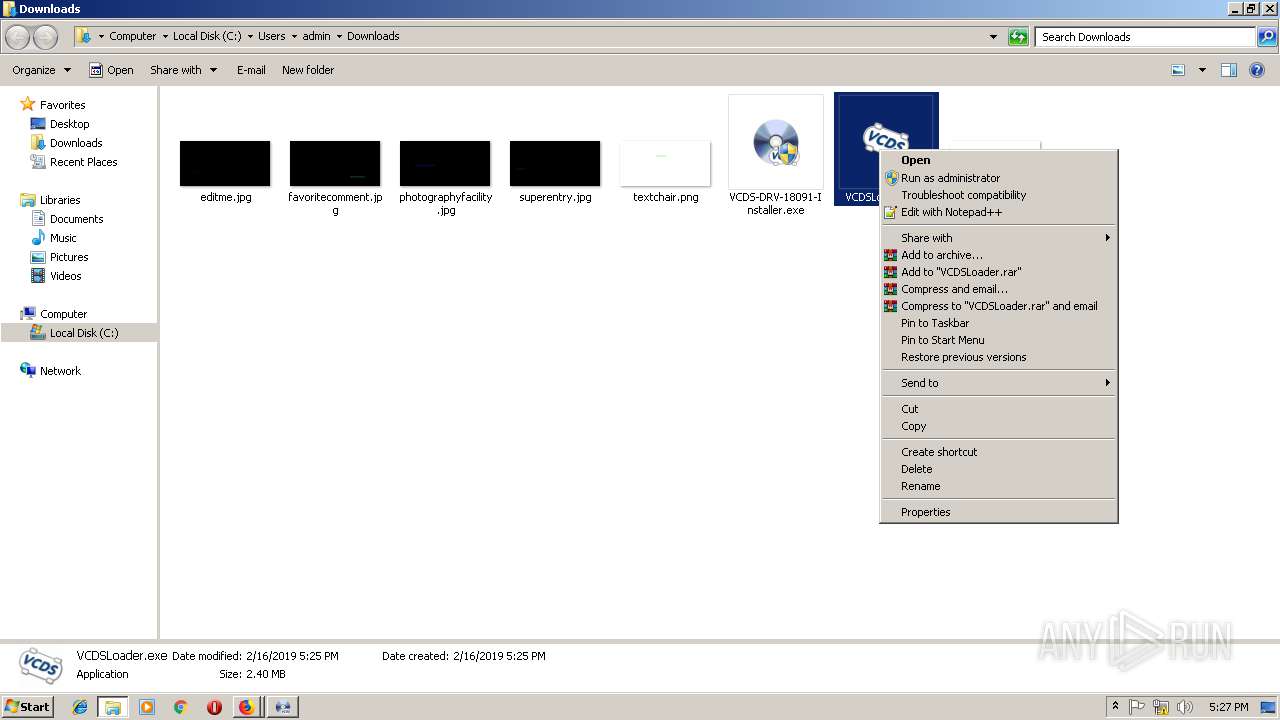
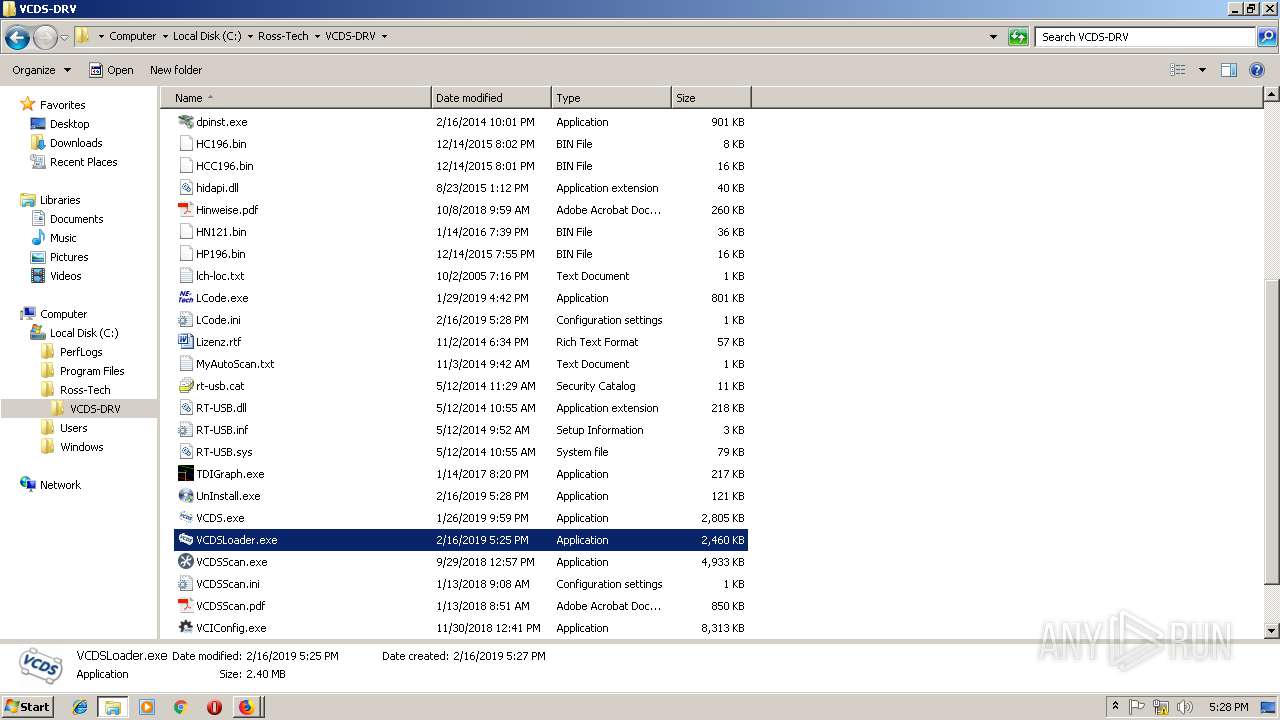
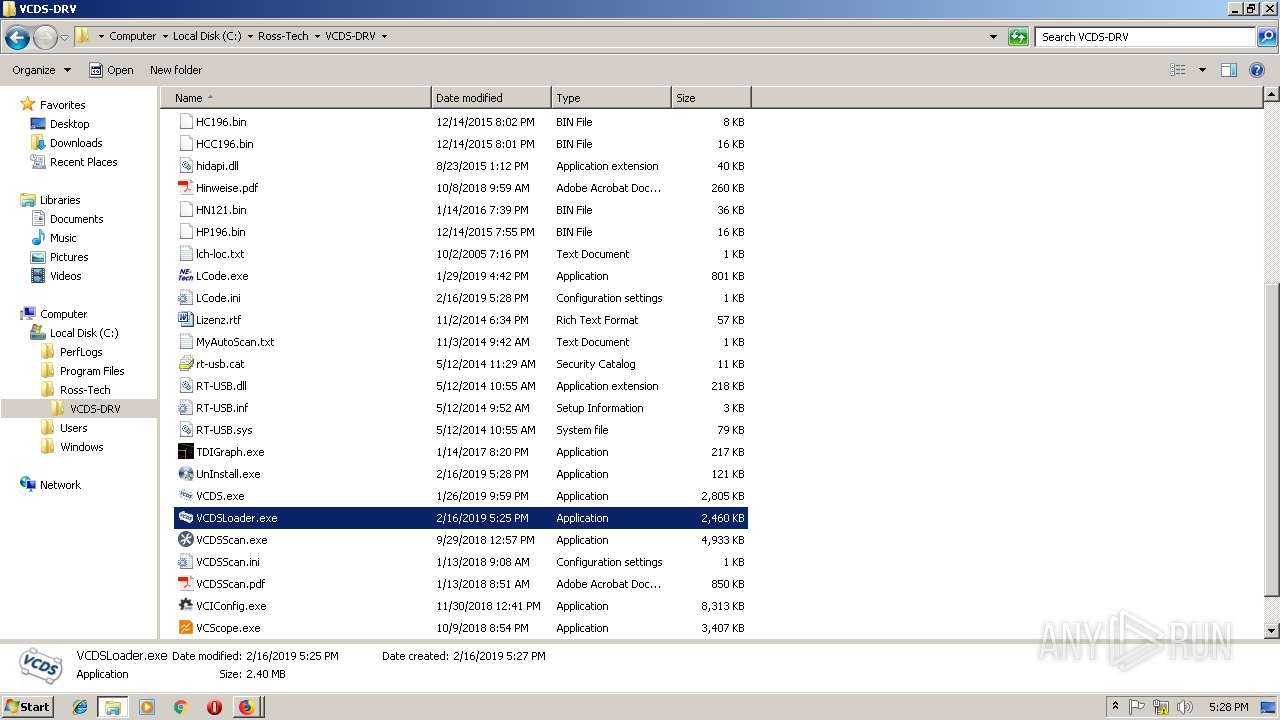
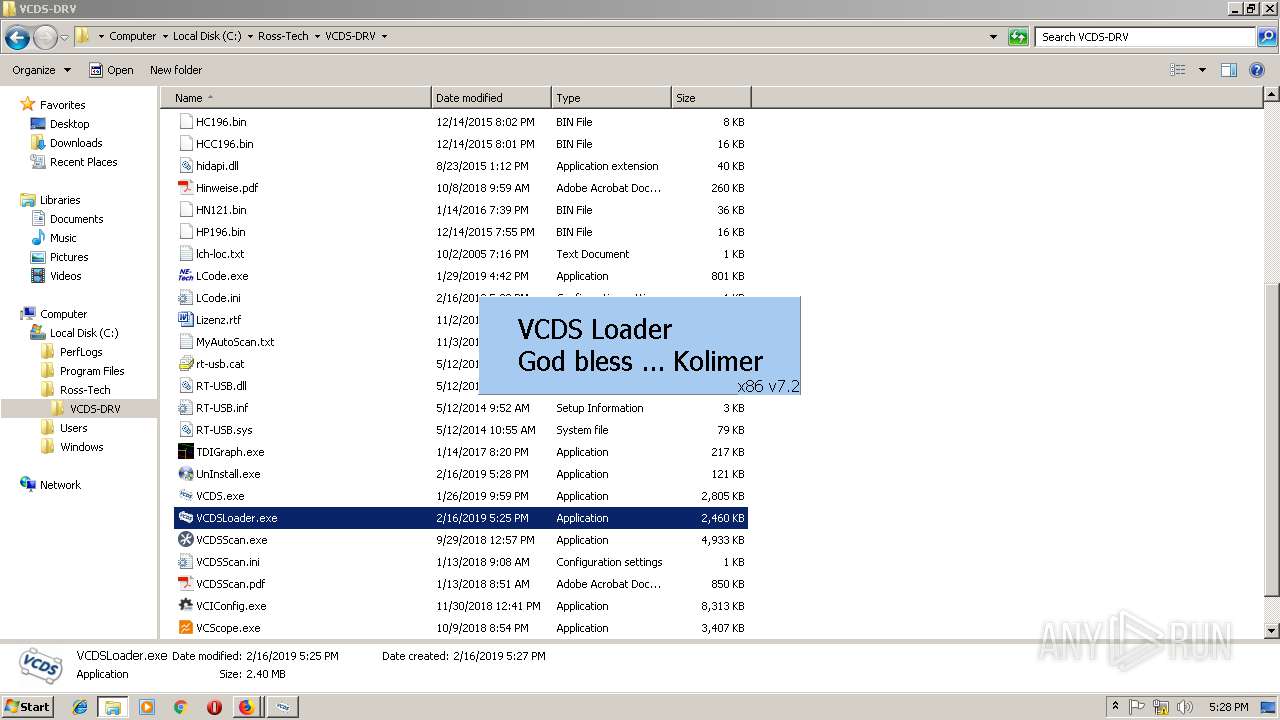
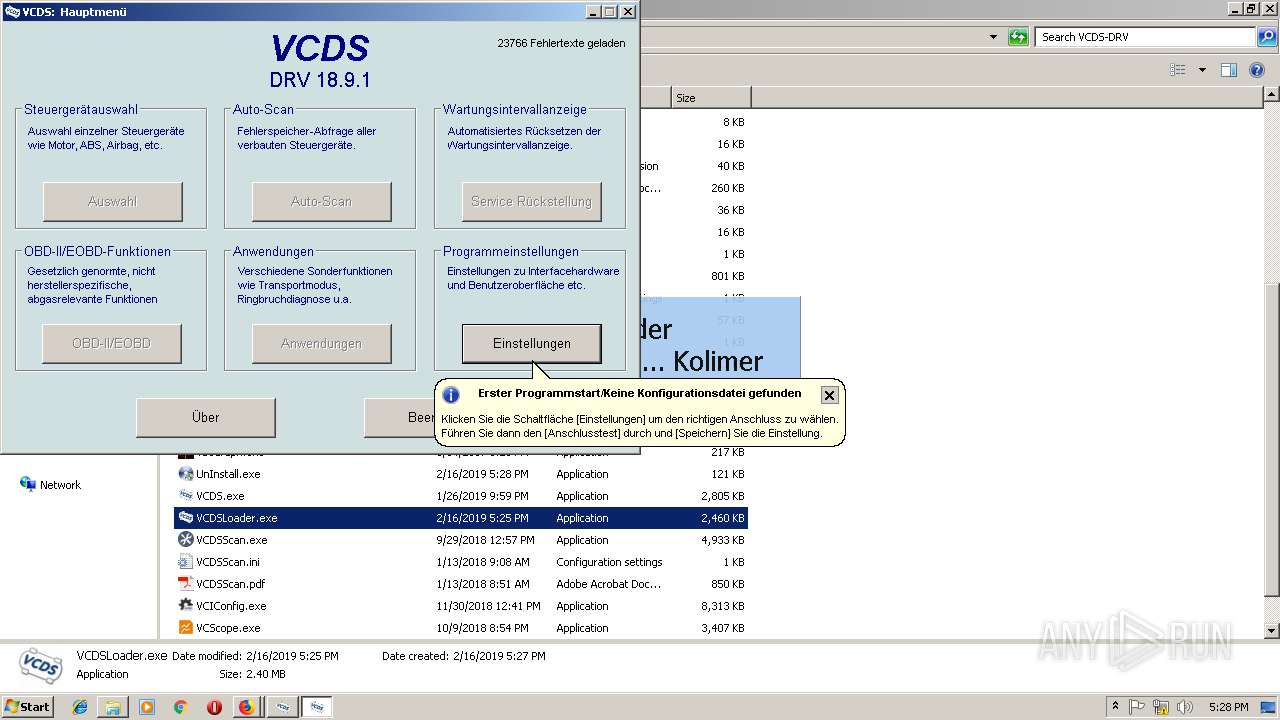
| File name: | VCDSLoader.exe |
| Full analysis: | https://app.any.run/tasks/fac86dd4-e2fb-46b4-923a-fc1a519fd04f |
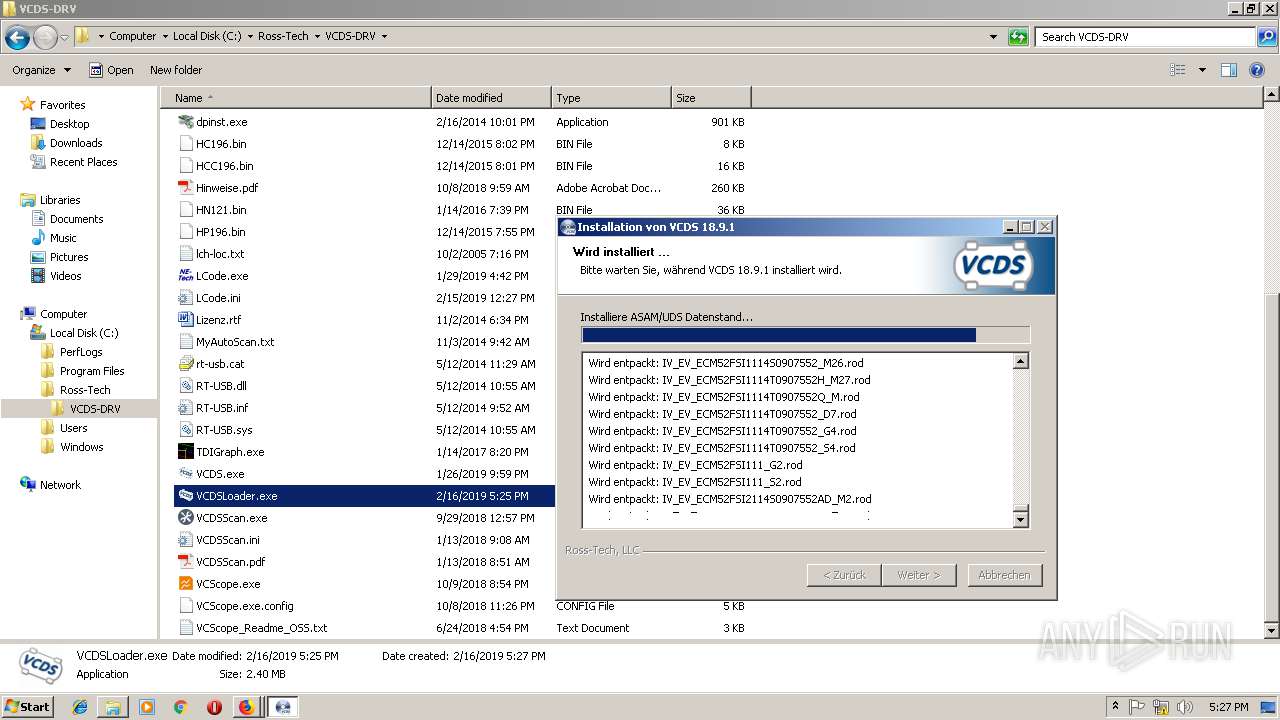
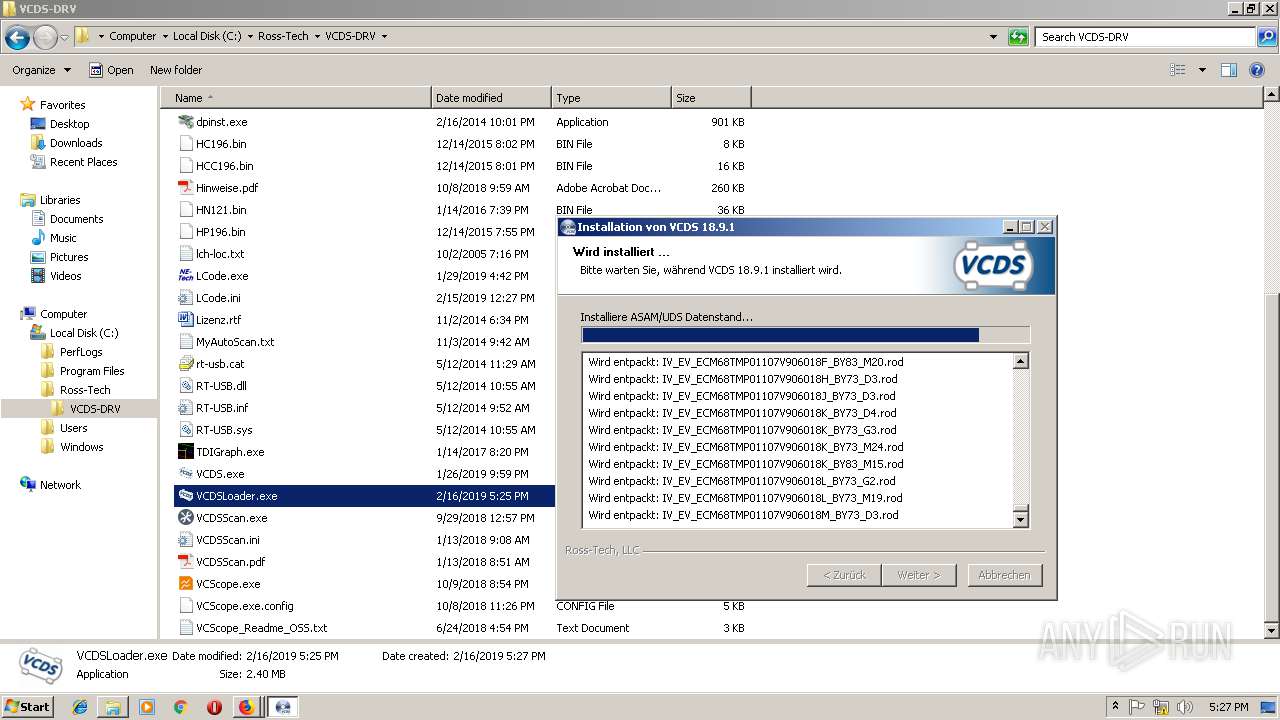
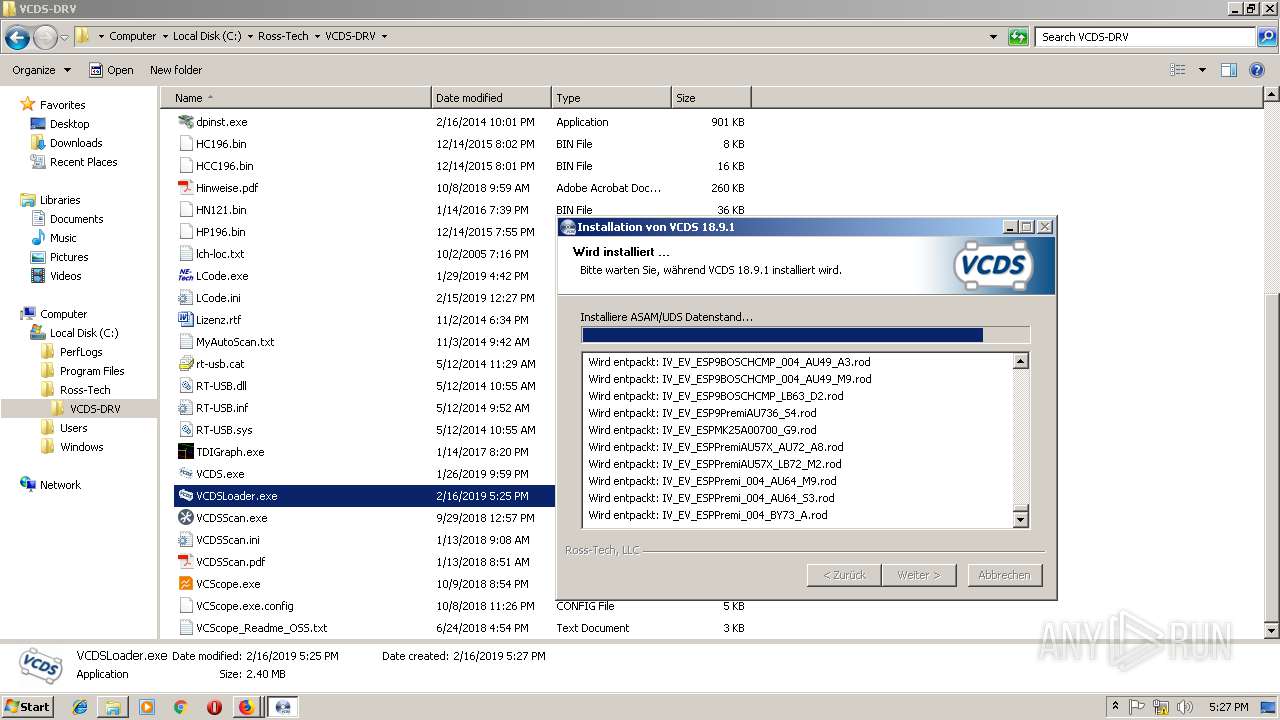
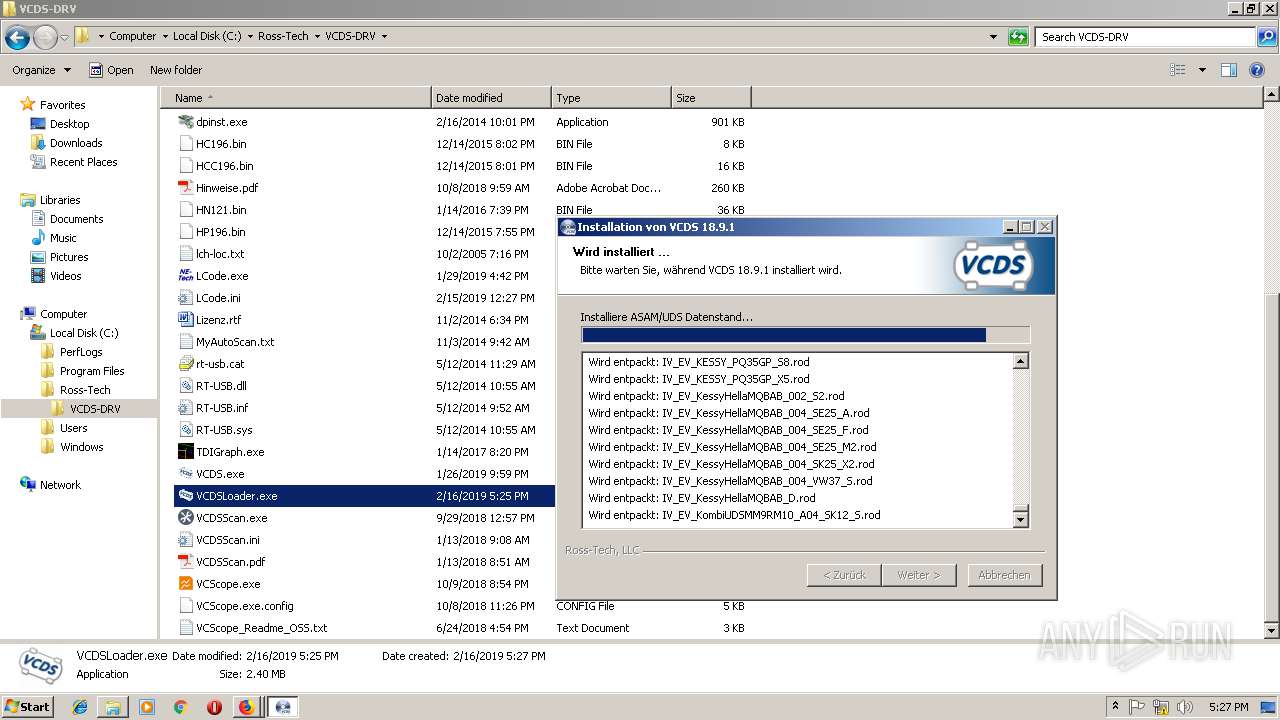
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2019, 17:25:04 |
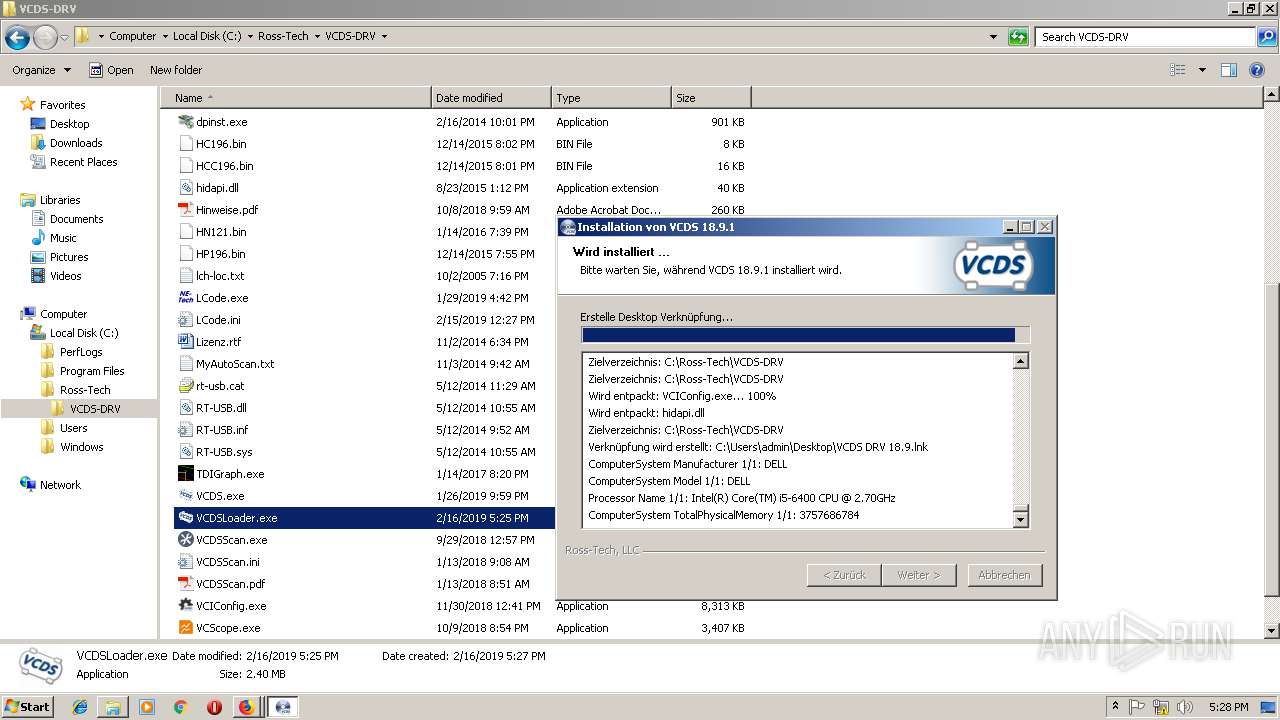
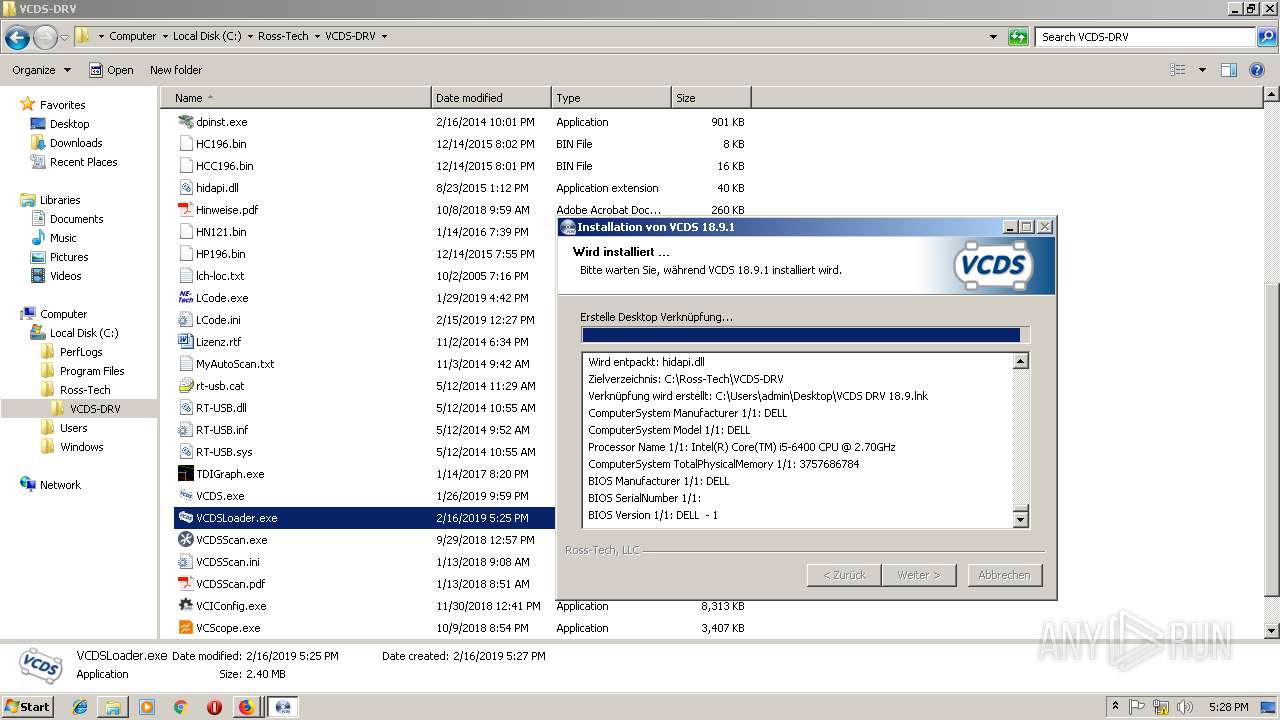
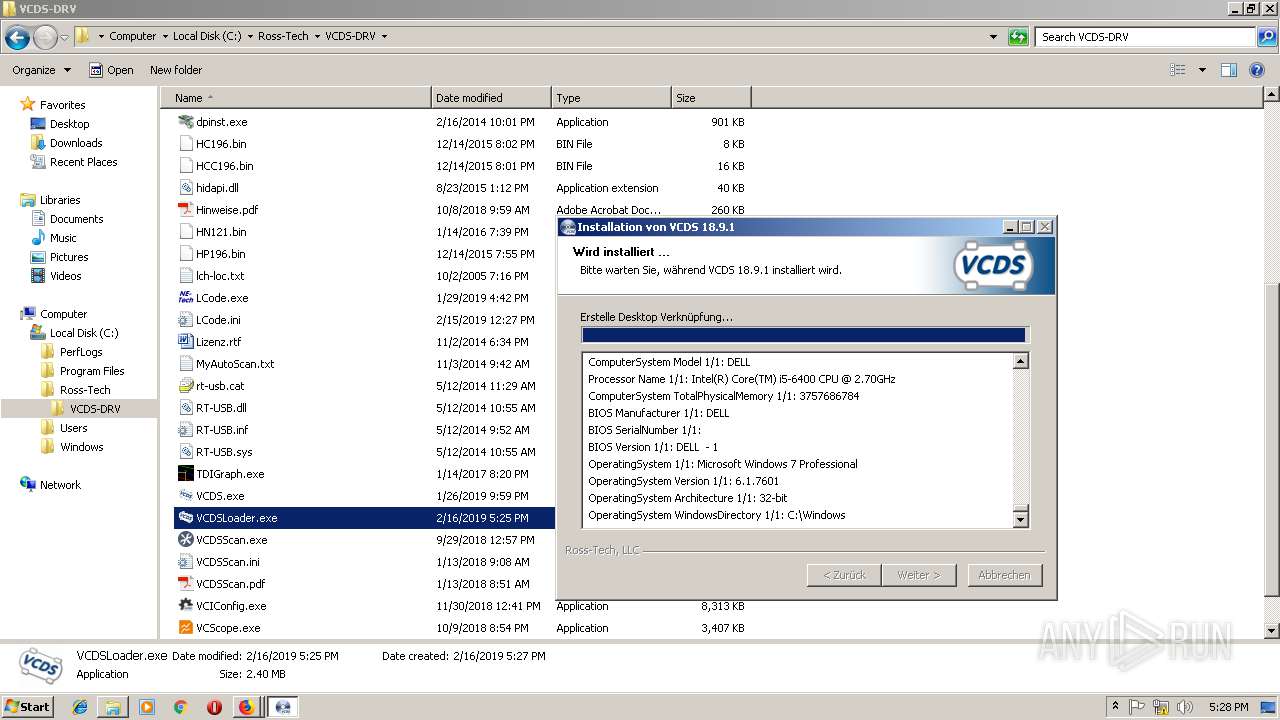
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9CD84ADA6E3715245BD1642674E12743 |
| SHA1: | 4526ABB9222EAEB85C1C64A9B0ED8A2A3939DD1C |
| SHA256: | 8FE0D314CC890B149031793D13FFCA85C72B928496A575D4DBE0CB719BC7542F |
| SSDEEP: | 49152:wE5ZT77/MV2mkrvNwvmq+kBitcIw23V7O2sRy04S138bJ4TY:LTzvmv3dAtVPwy04AO+Y |
MALICIOUS
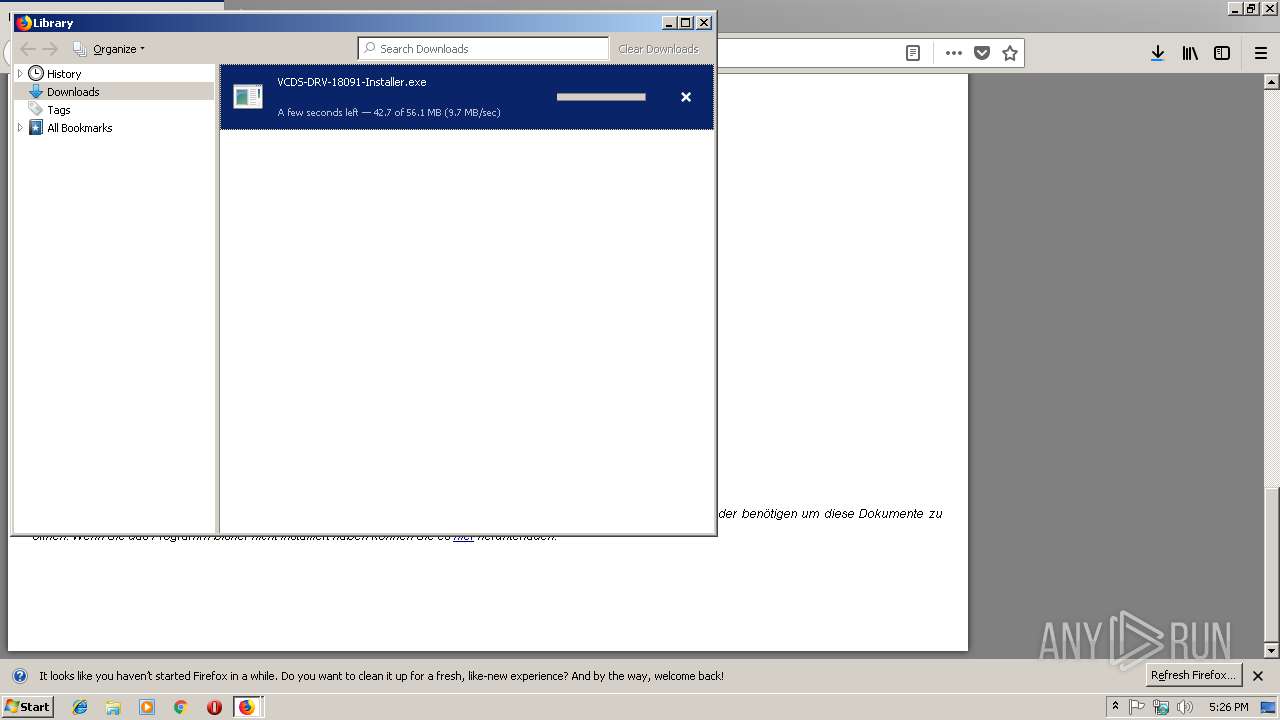
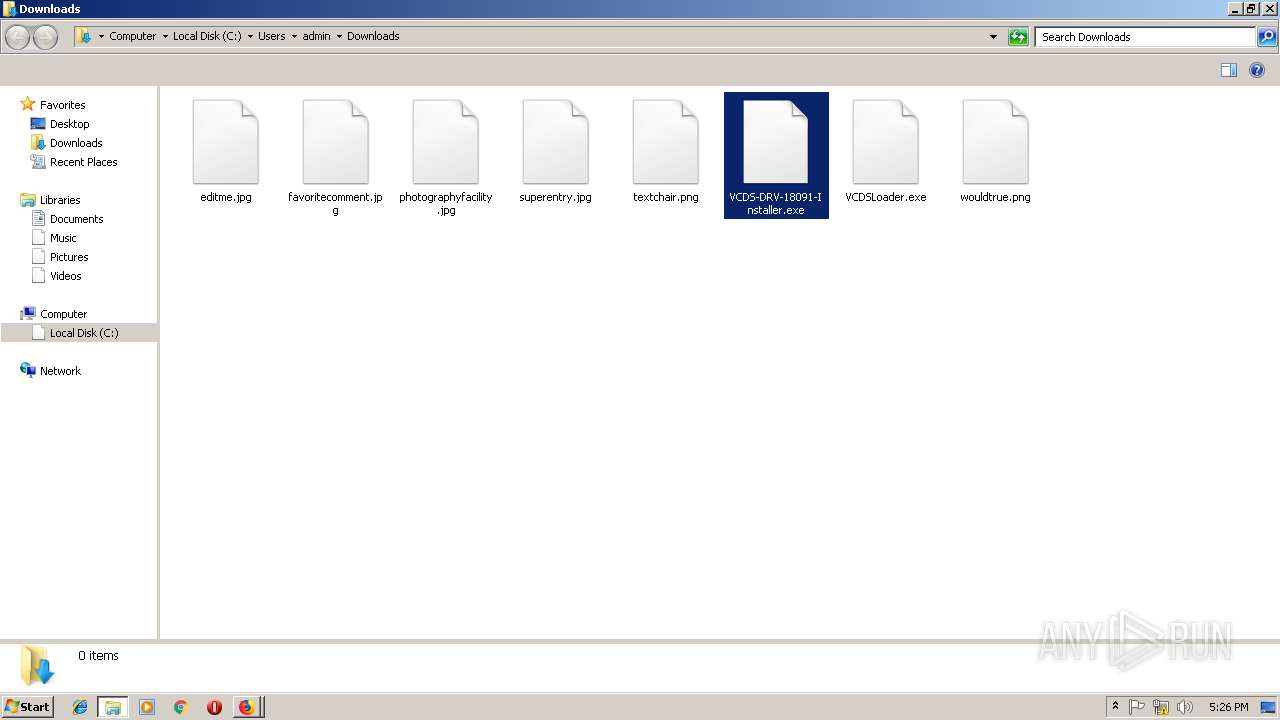
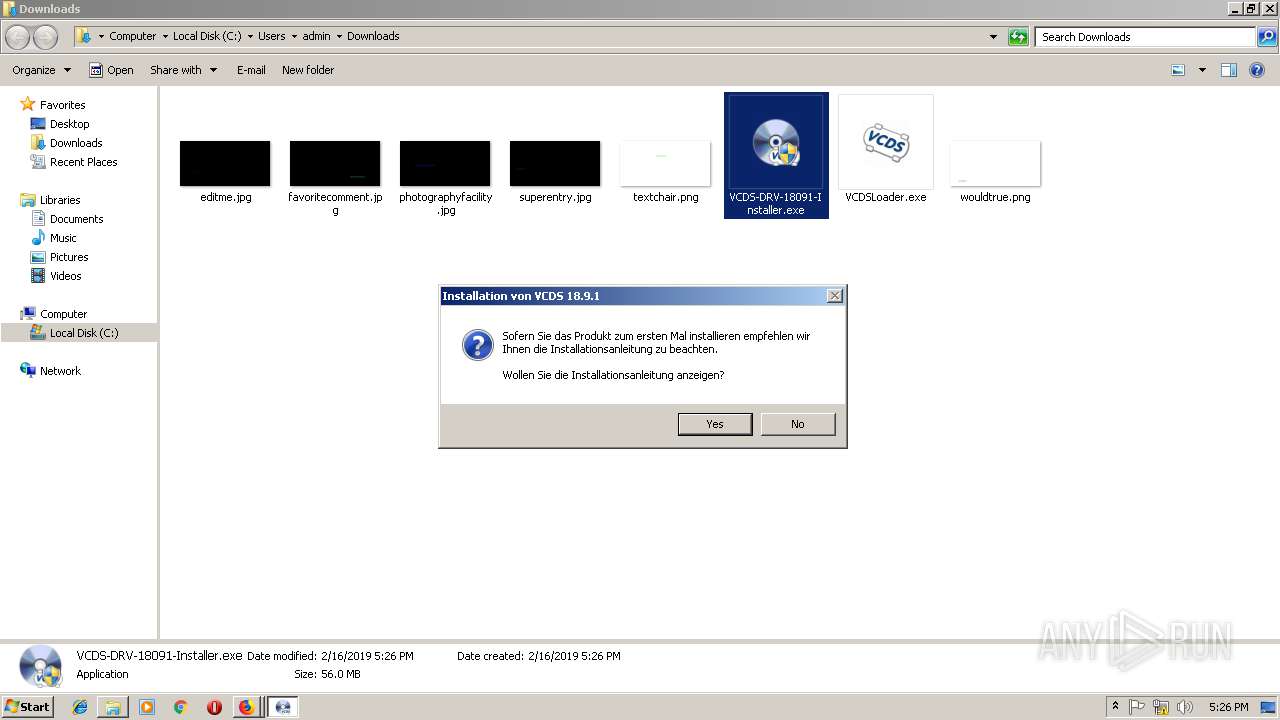
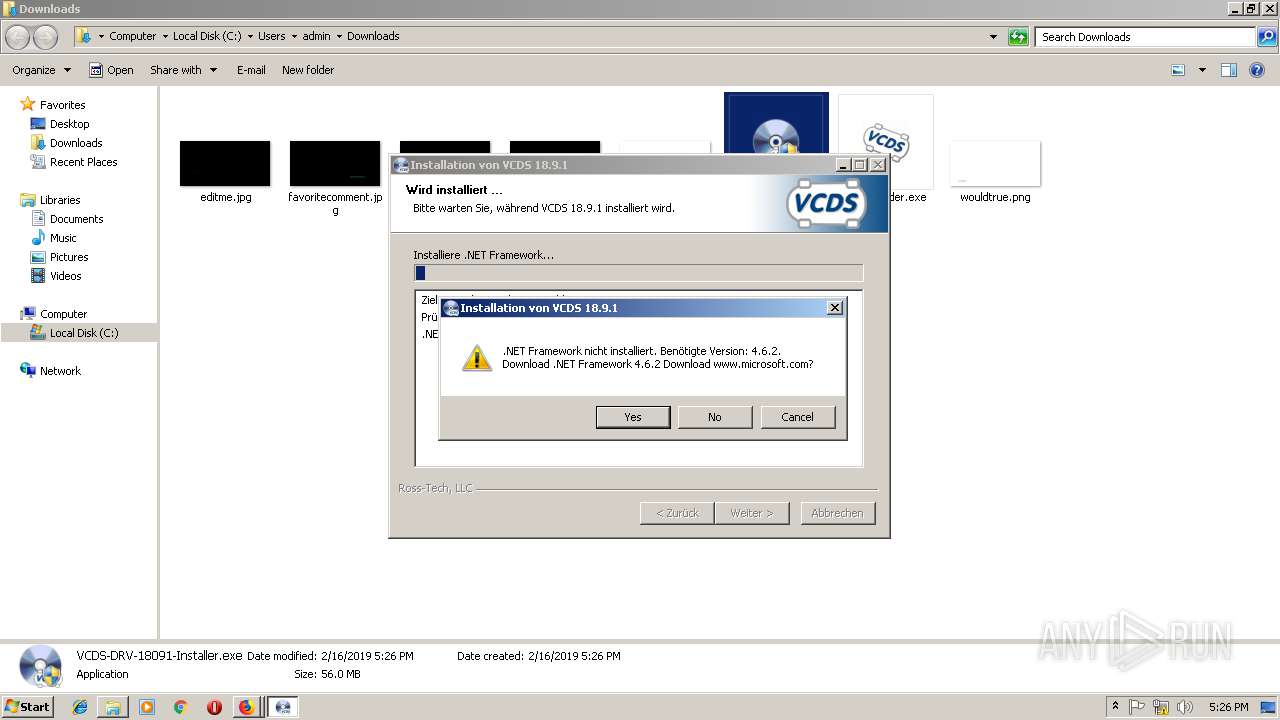
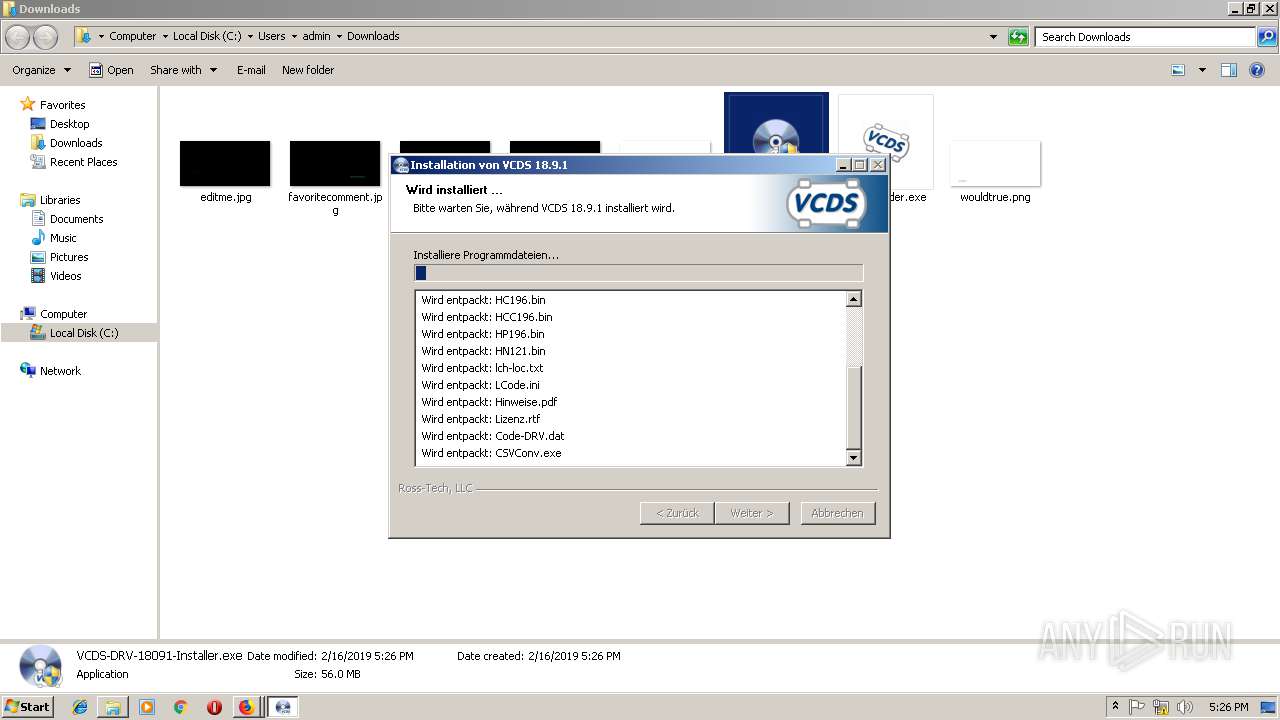
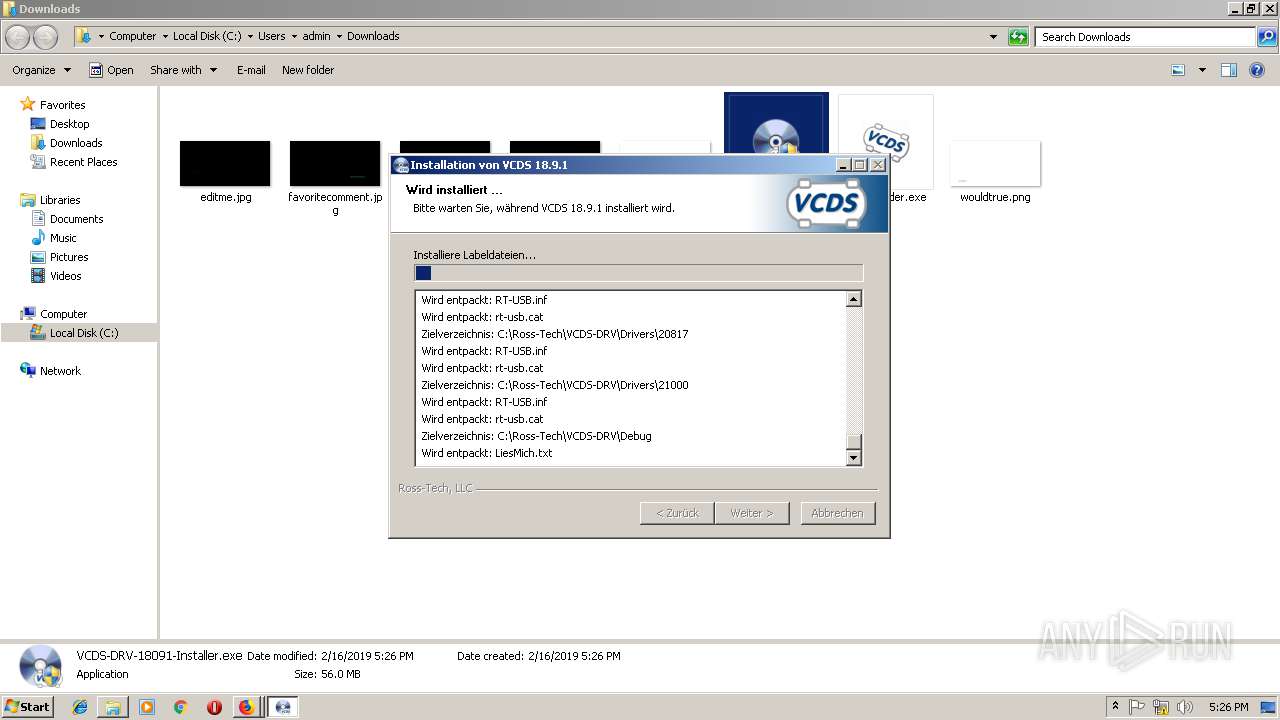
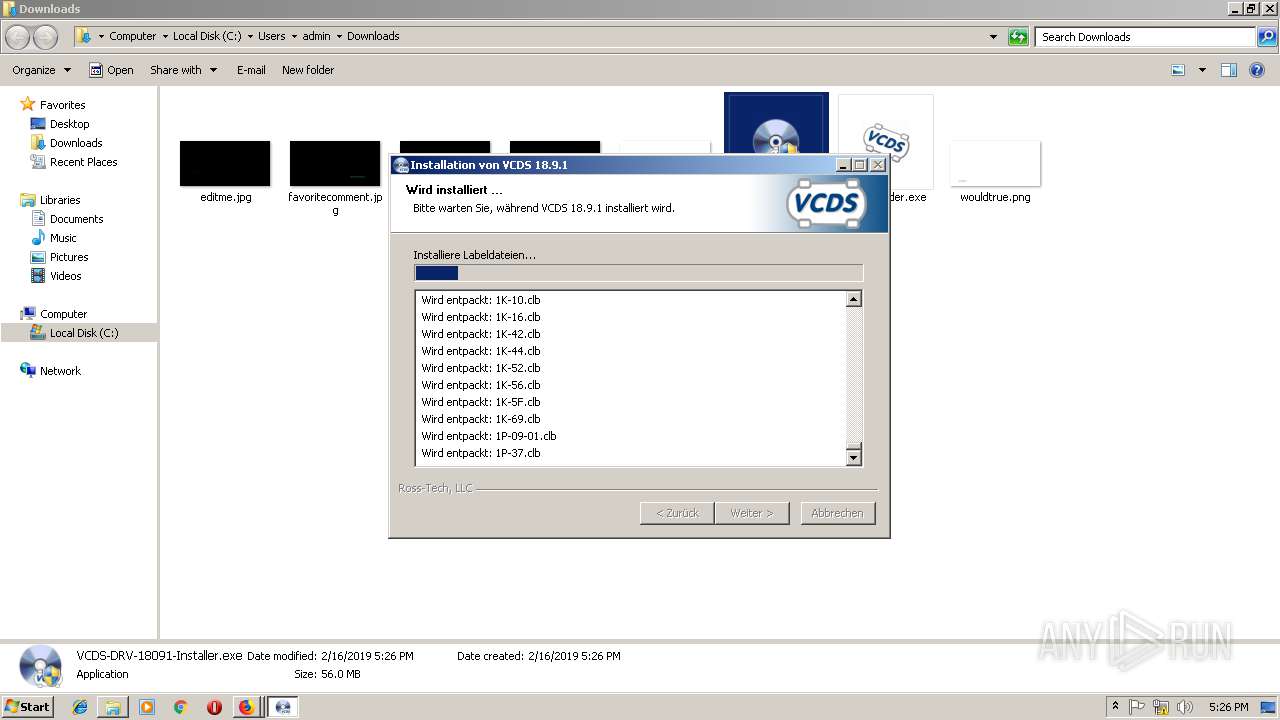
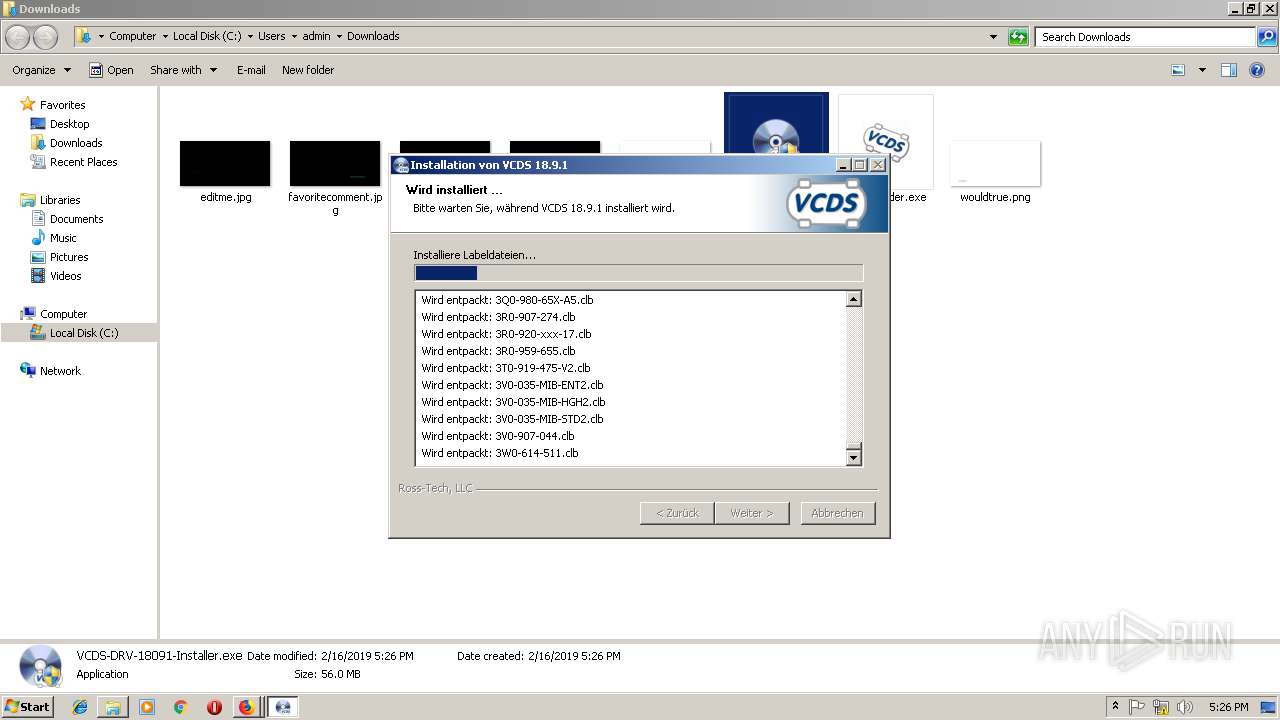
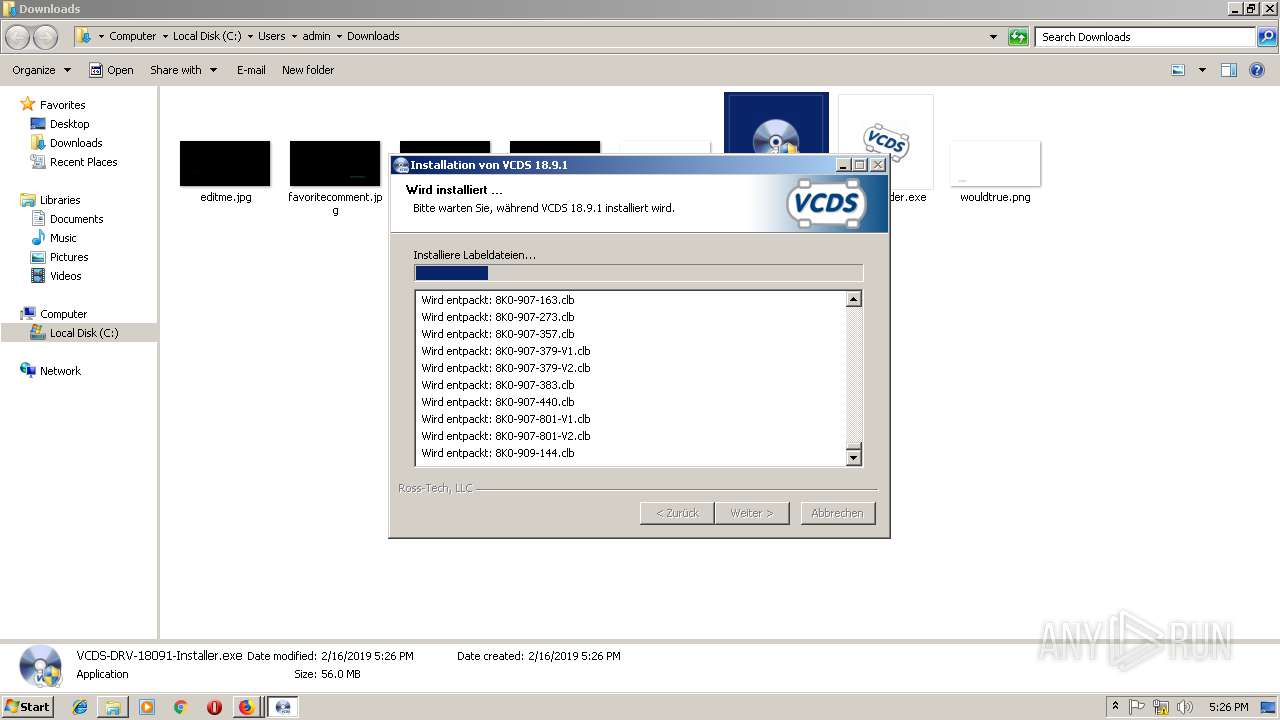
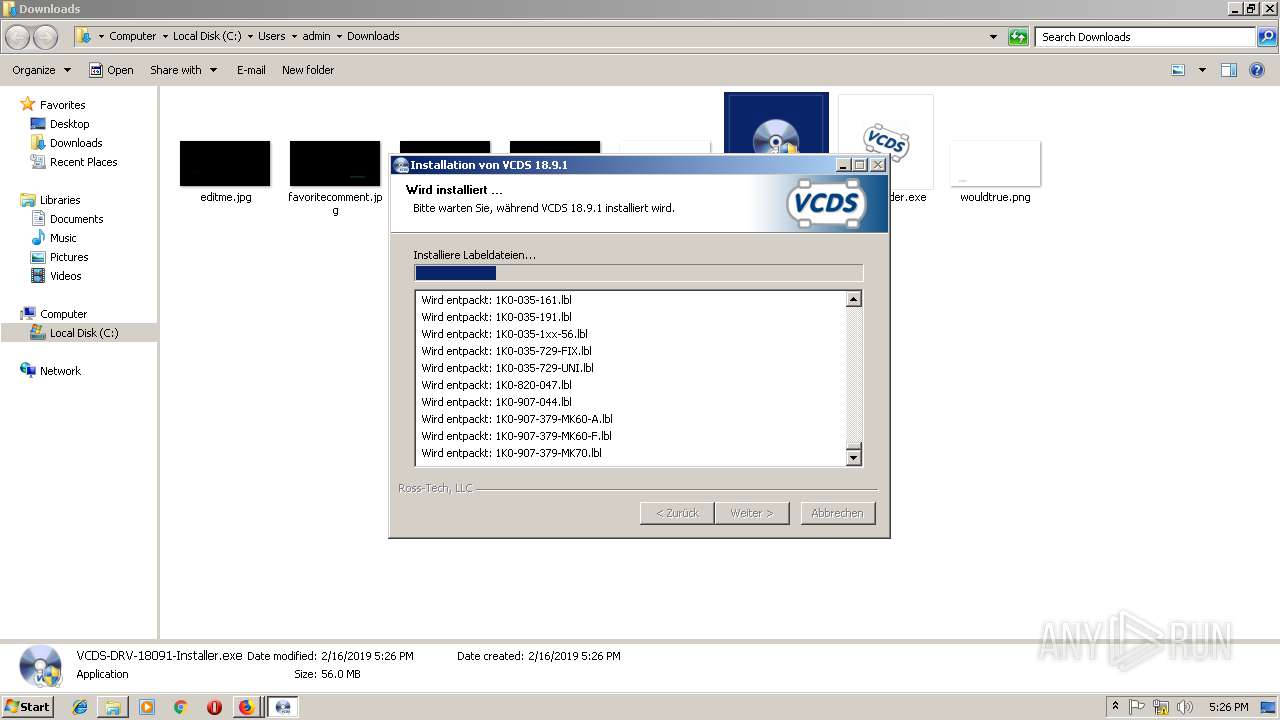
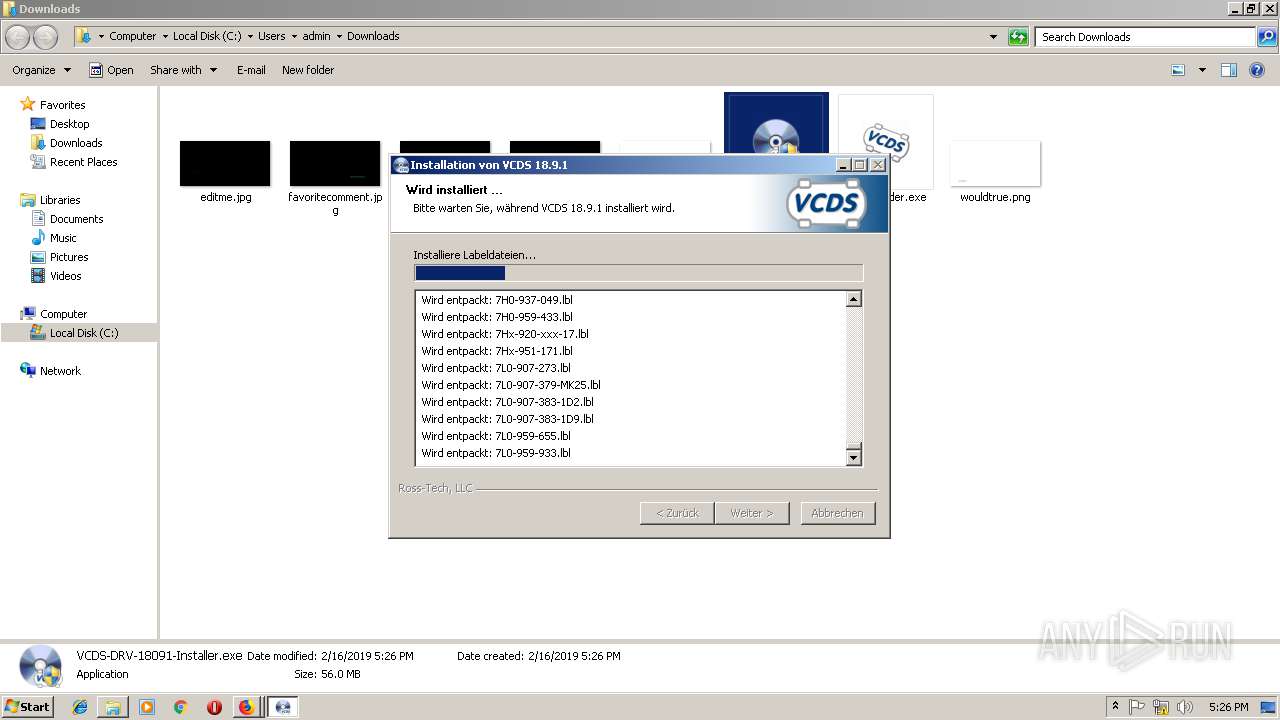
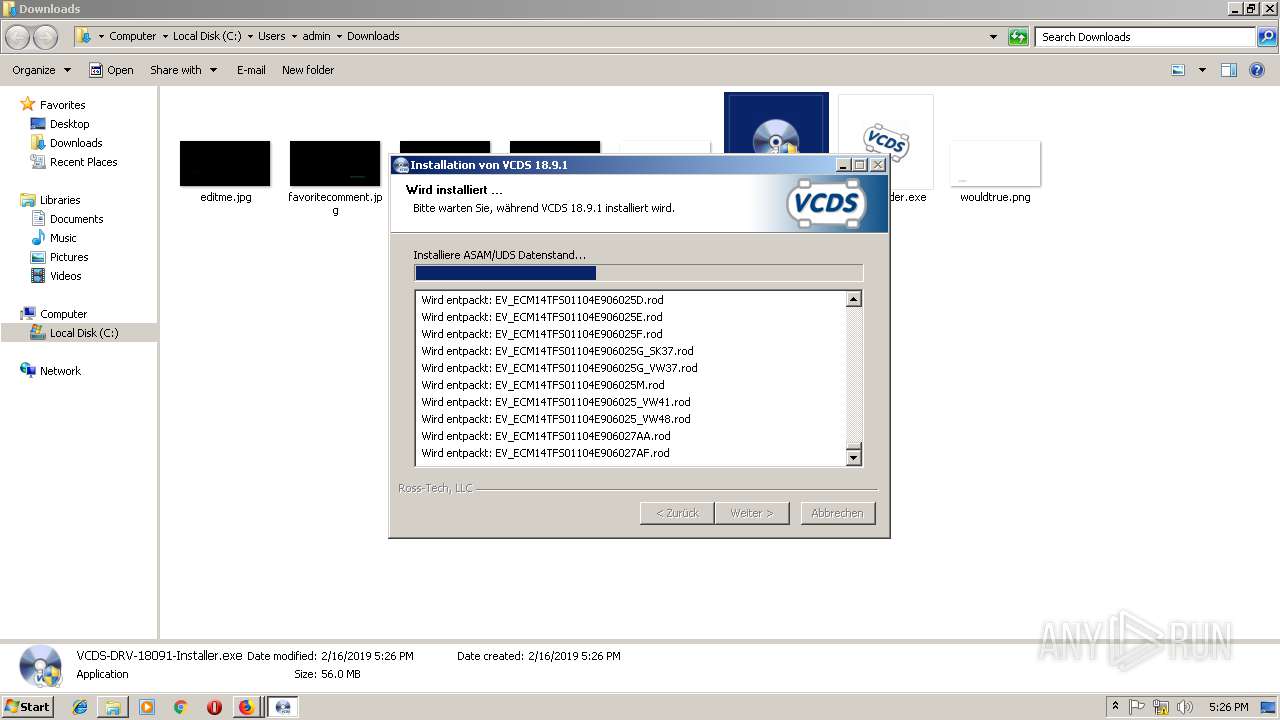
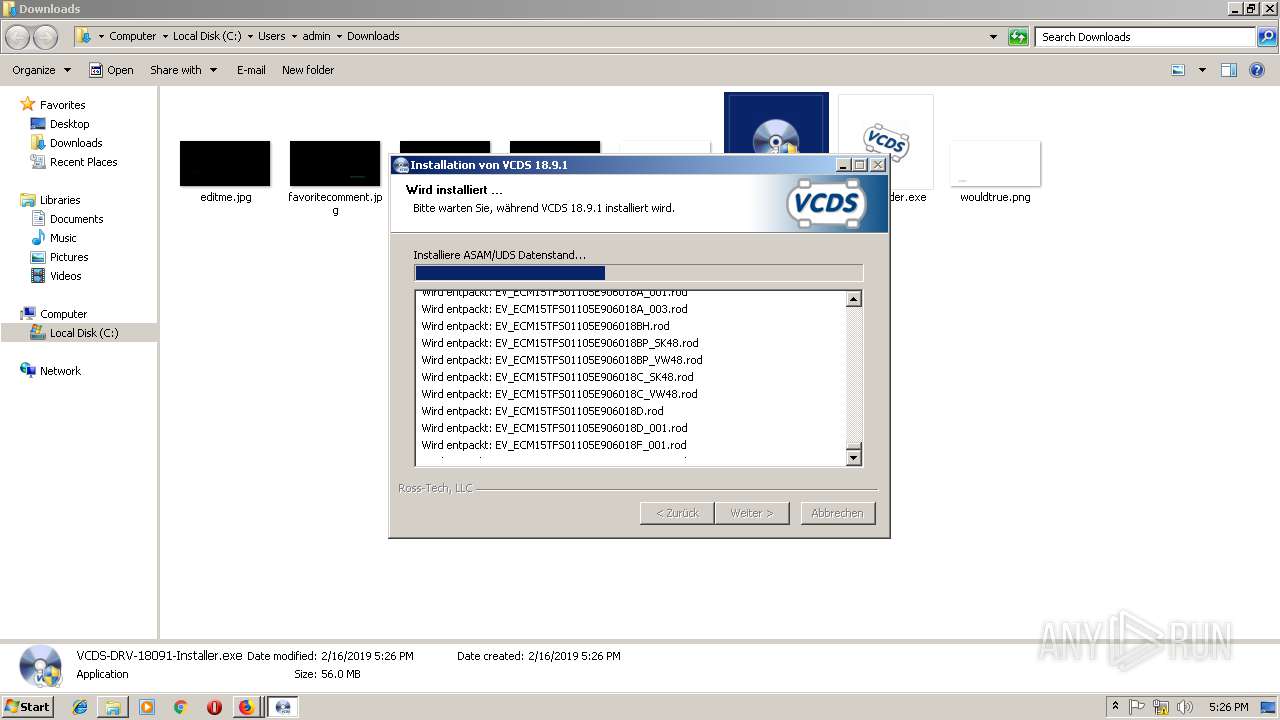
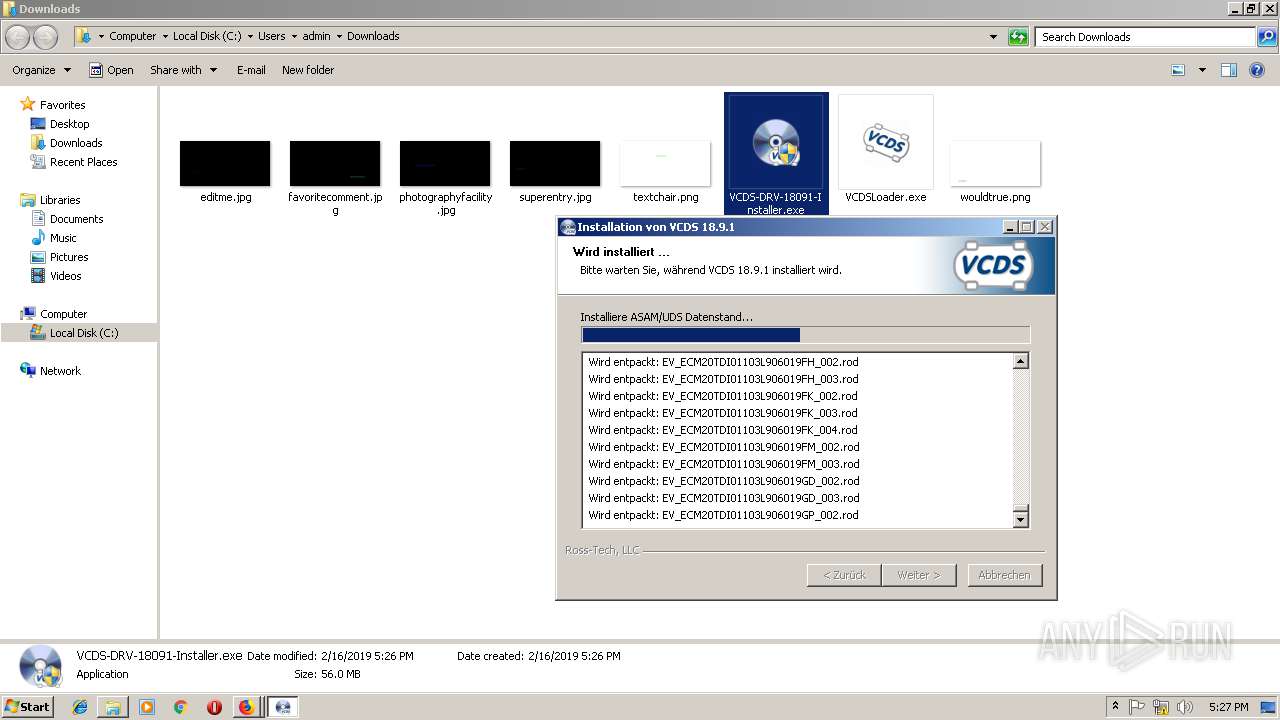
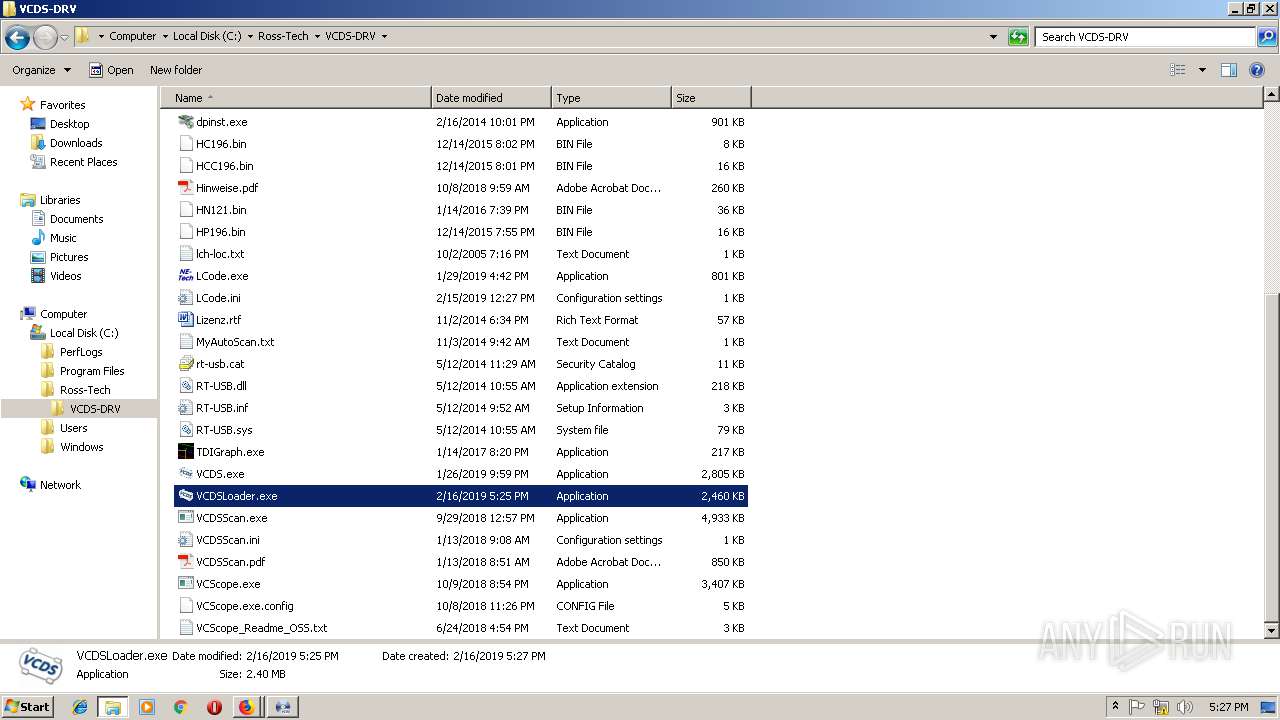
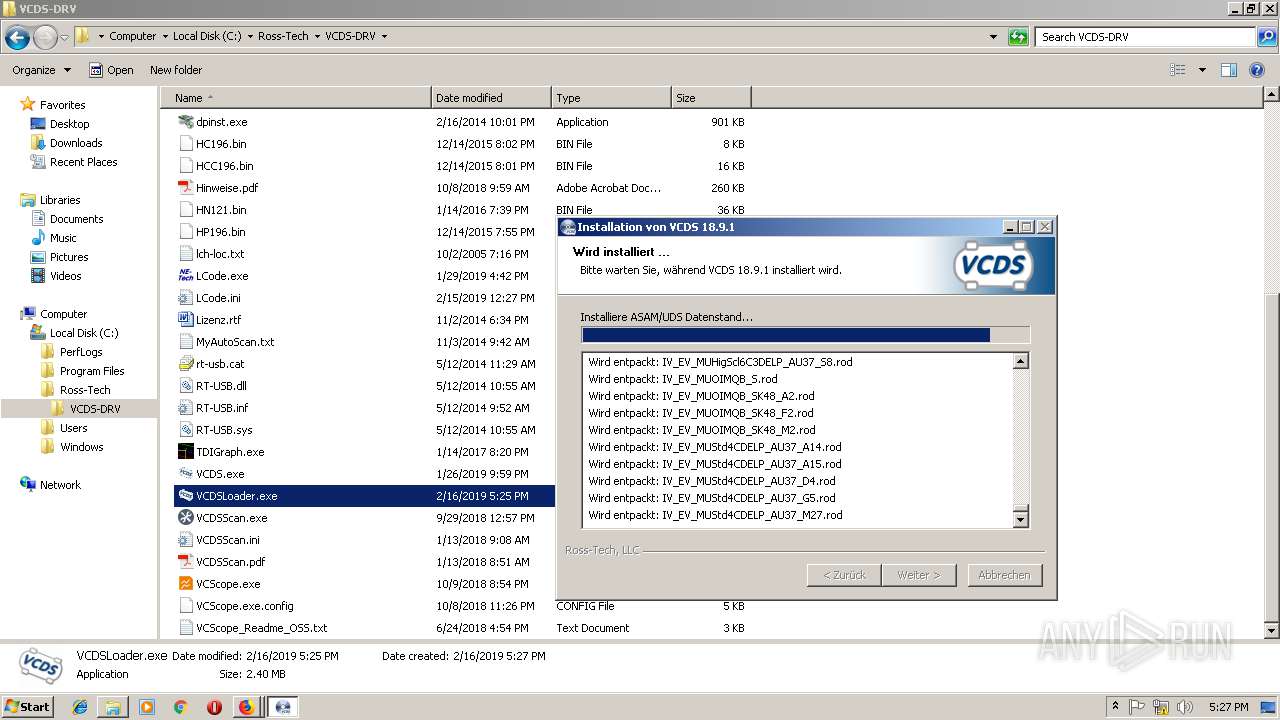
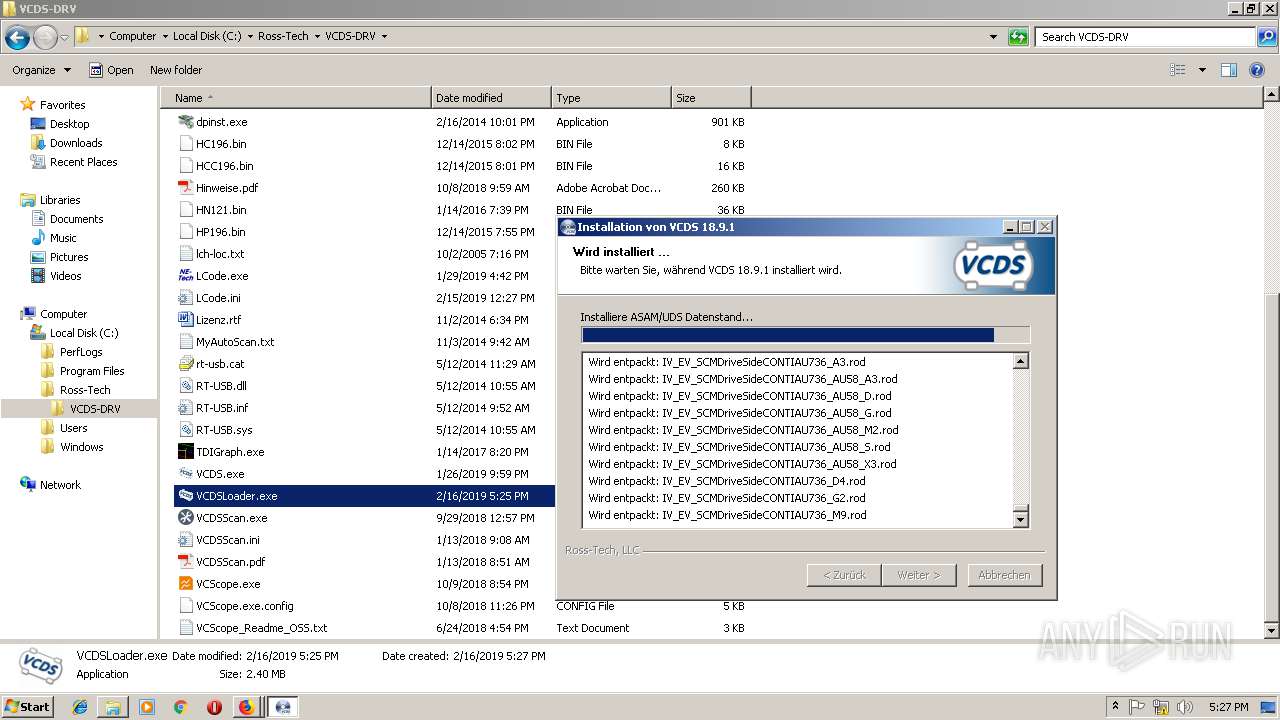
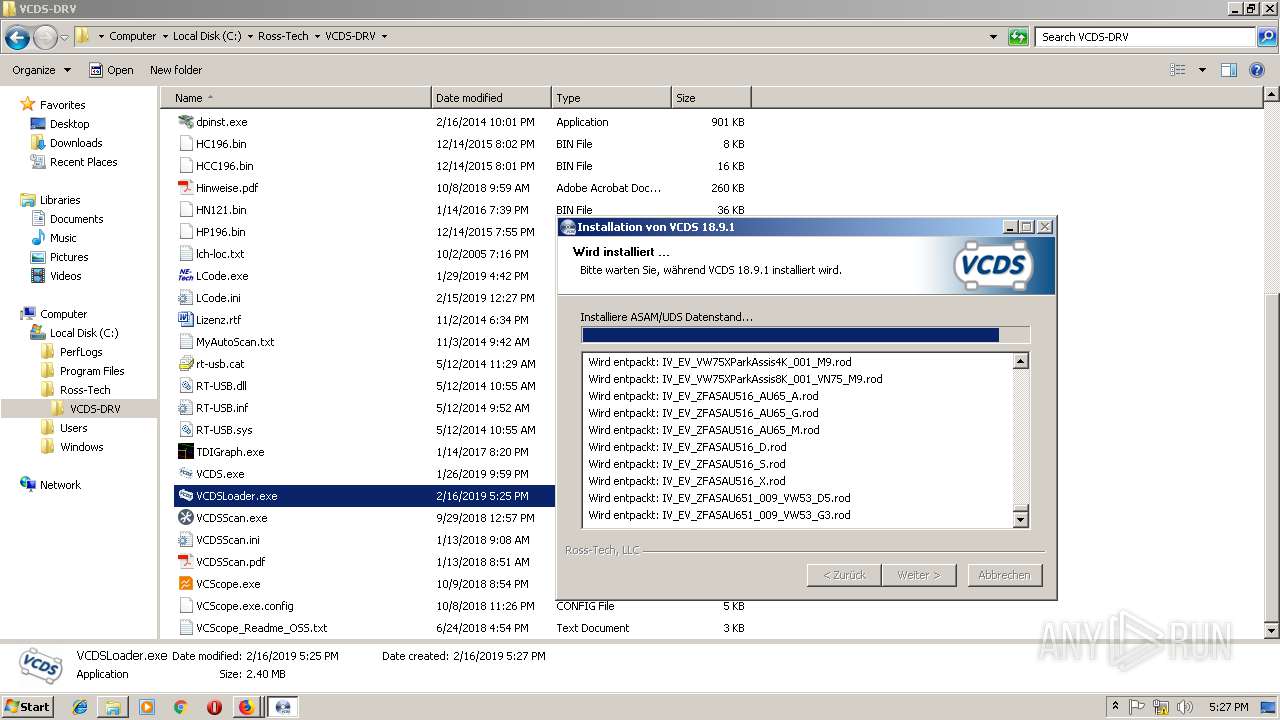
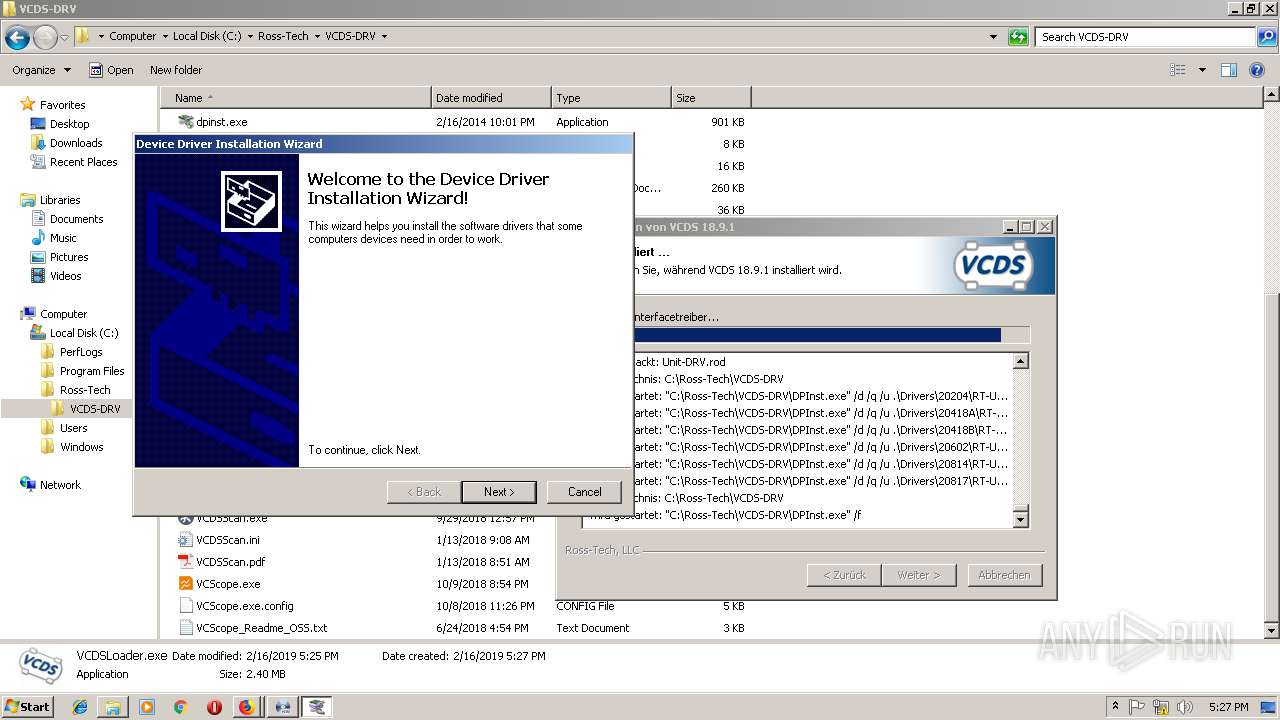
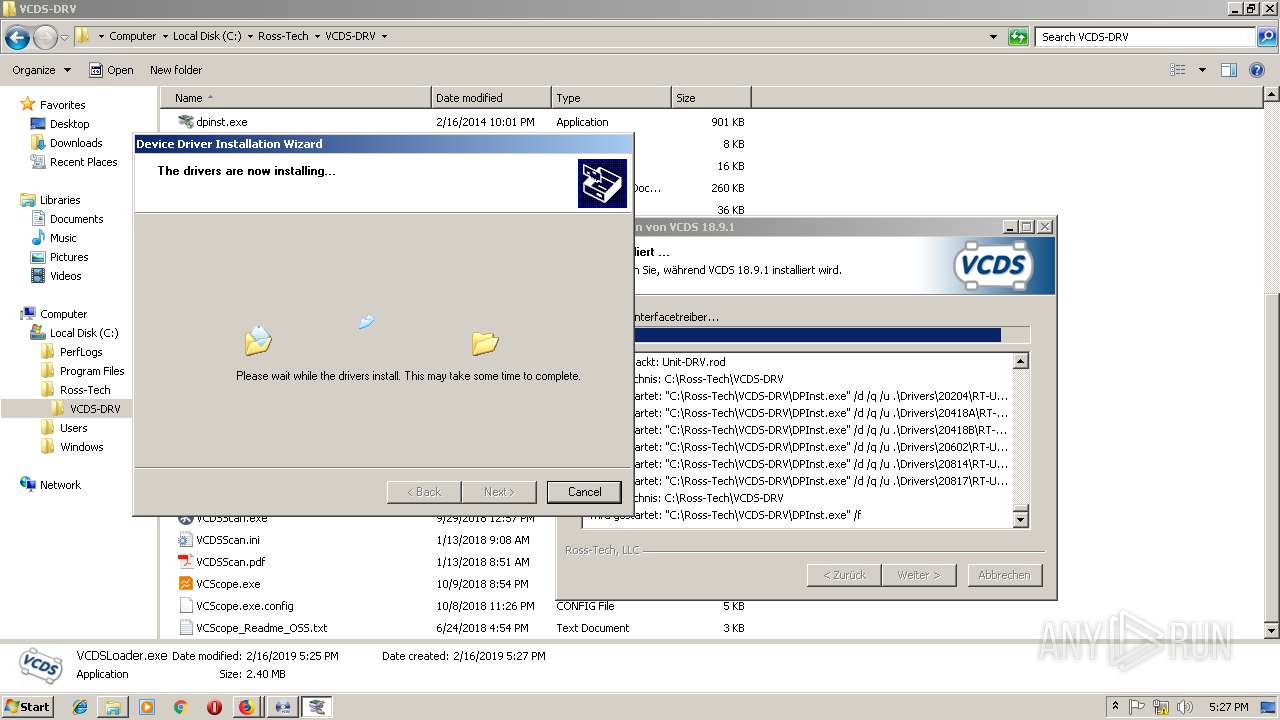
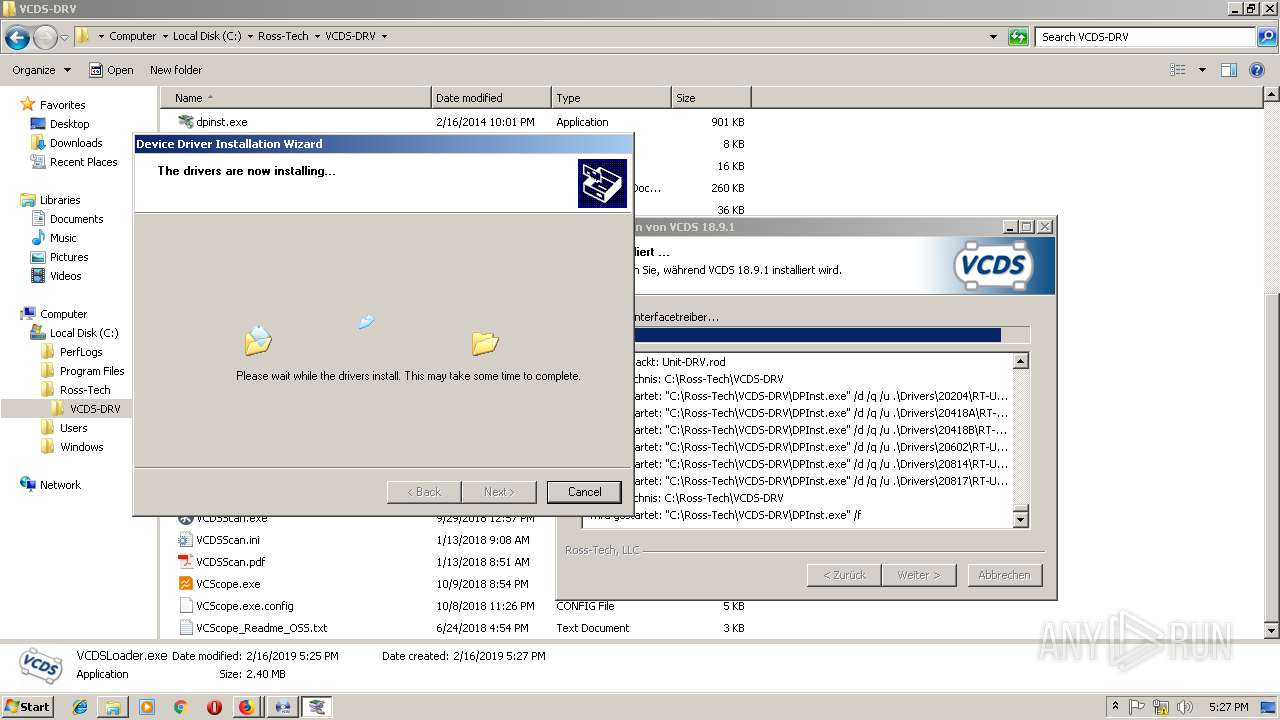
Application was dropped or rewritten from another process
- VCDS-DRV-18091-Installer.exe (PID: 3368)
- DPInst.exe (PID: 792)
- DPInst.exe (PID: 3264)
- VCDS-DRV-18091-Installer.exe (PID: 924)
- DPInst.exe (PID: 3376)
- DPInst.exe (PID: 1784)
- DPInst.exe (PID: 2284)
- DPInst.exe (PID: 2700)
- DPInst.exe (PID: 2840)
- nsF278.tmp (PID: 3000)
- nsFC4D.tmp (PID: 3044)
- ns27.tmp (PID: 3104)
- nsFE51.tmp (PID: 3252)
- ns3D3.tmp (PID: 2476)
- ns5A8.tmp (PID: 1964)
- ns944.tmp (PID: 3344)
- nsB1A.tmp (PID: 2832)
- nsCE0.tmp (PID: 2800)
- ns77E.tmp (PID: 2492)
- nsEB6.tmp (PID: 3748)
- ns1280.tmp (PID: 1720)
- ns20C.tmp (PID: 2664)
- VCDS.exe (PID: 3968)
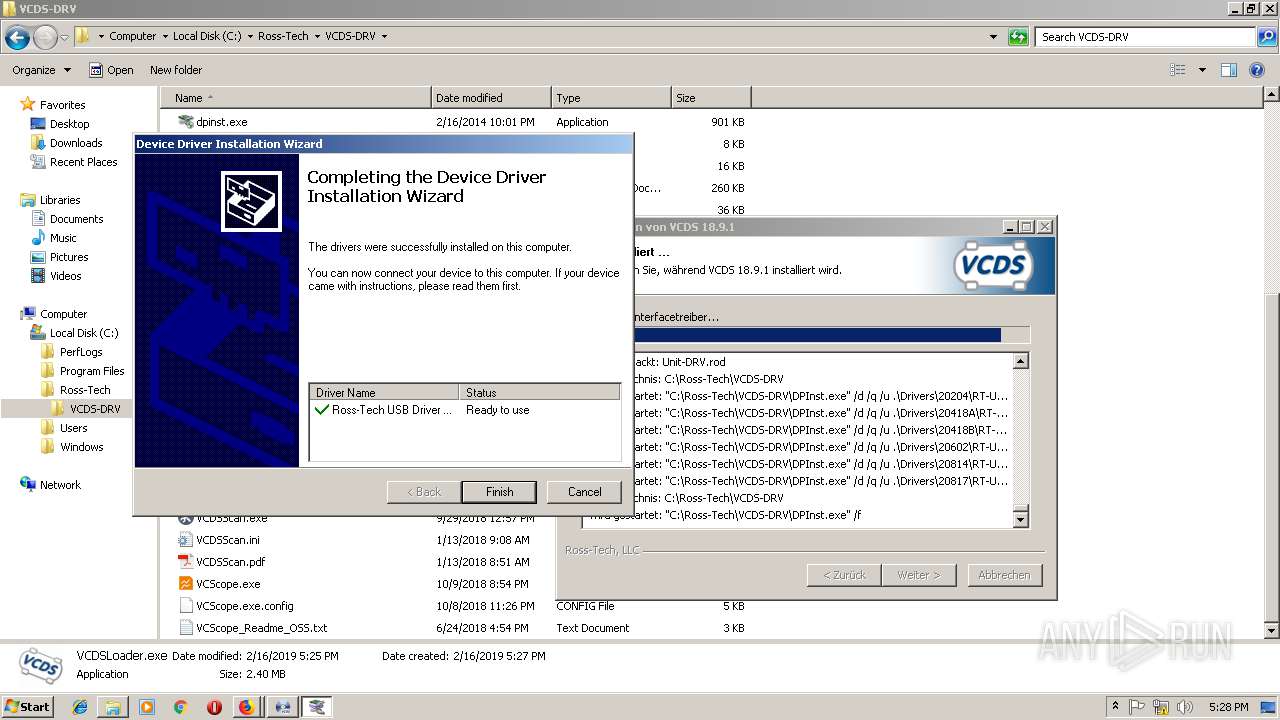
Loads dropped or rewritten executable
- VCDS-DRV-18091-Installer.exe (PID: 924)
- VCDS.exe (PID: 3968)
SUSPICIOUS
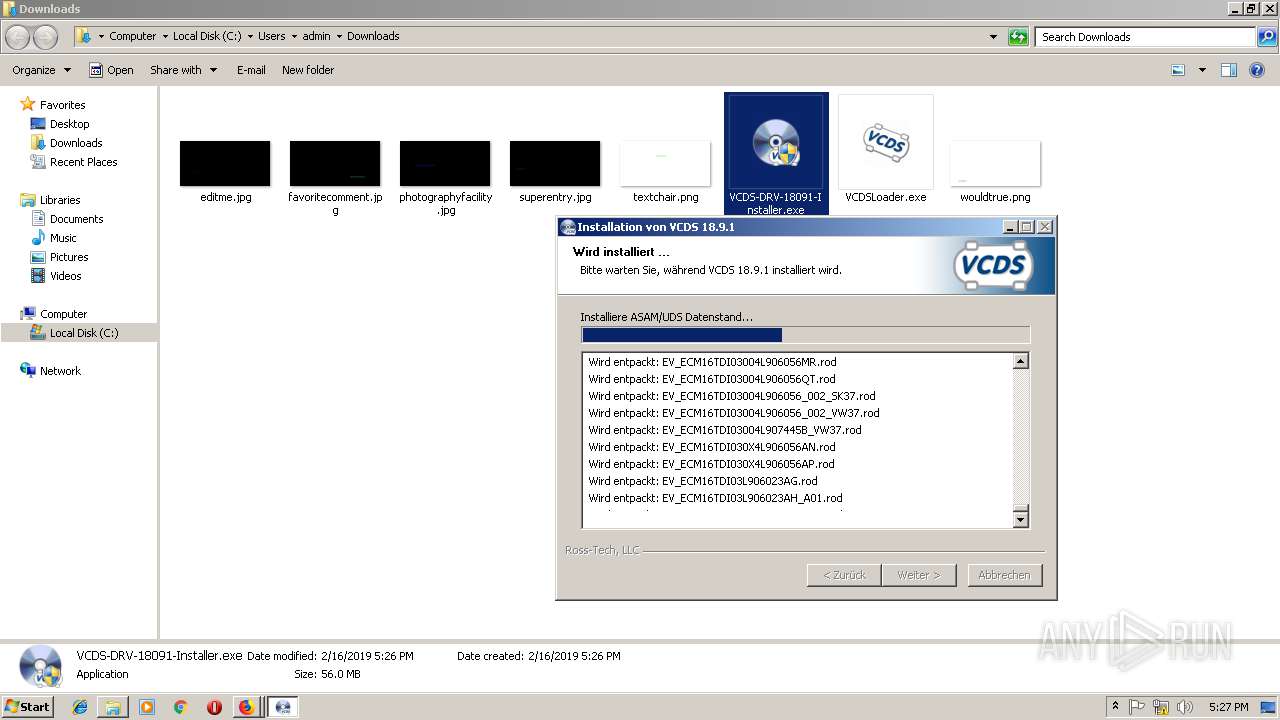
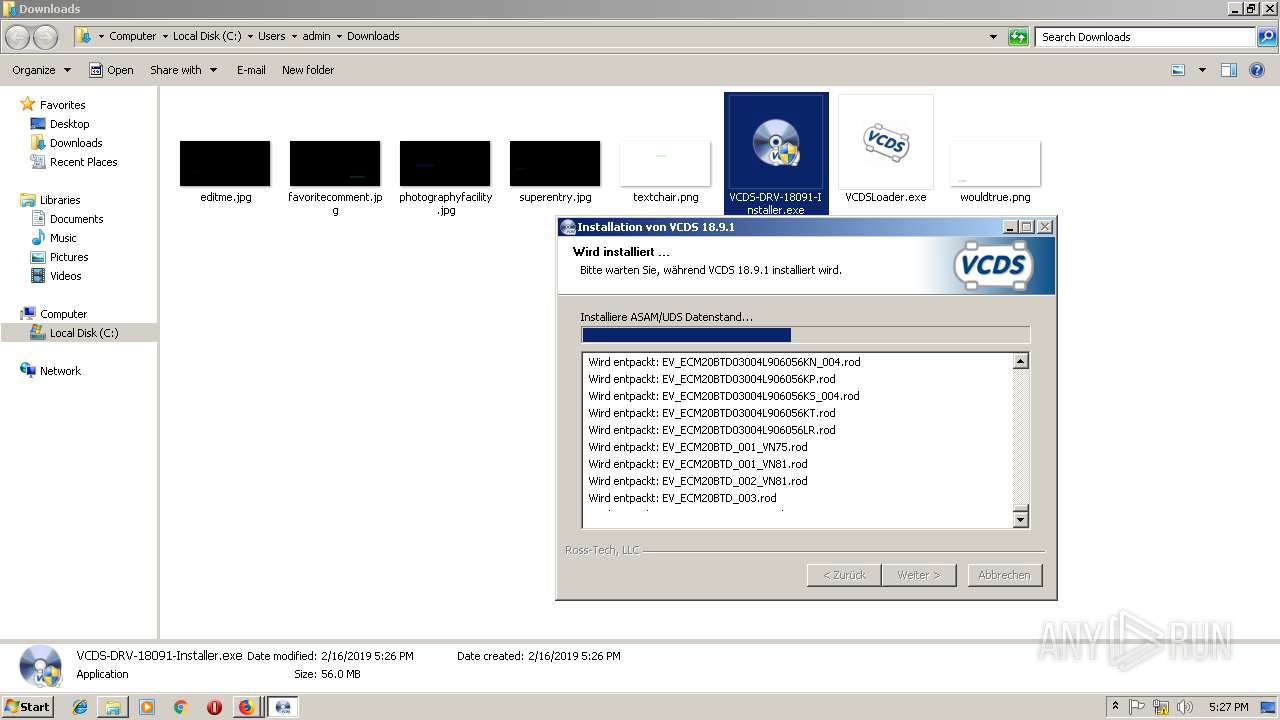
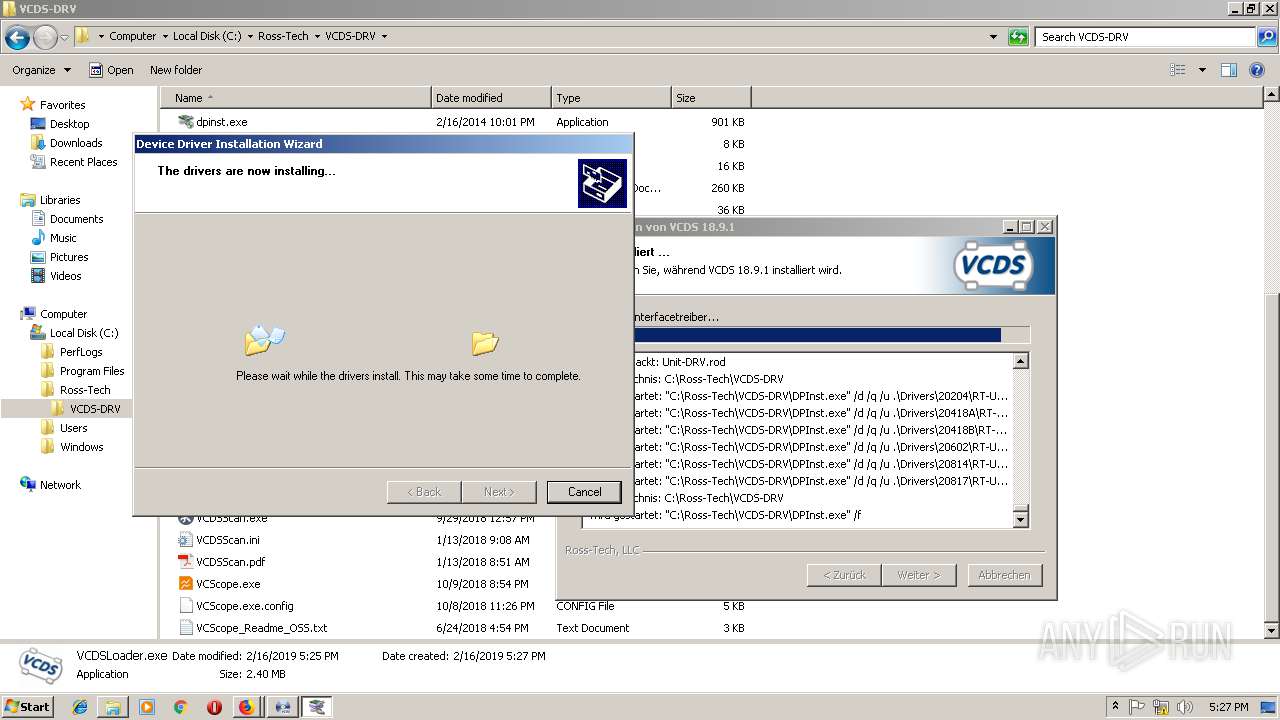
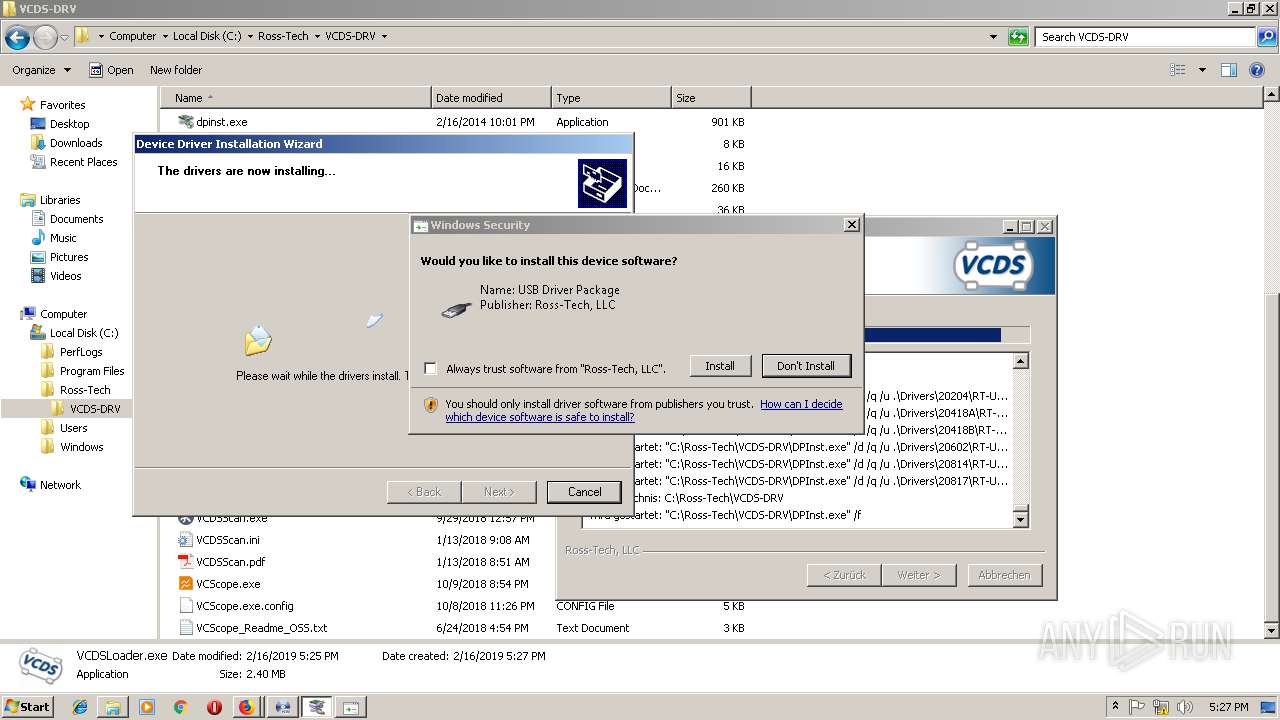
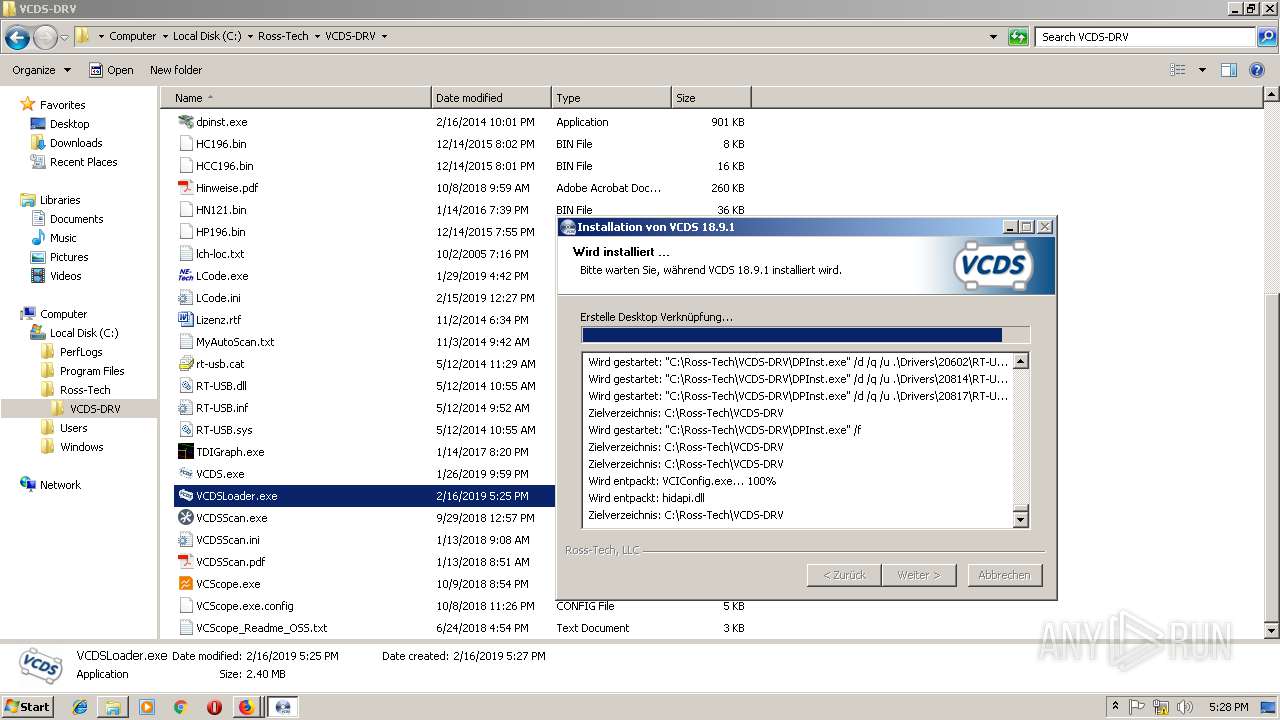
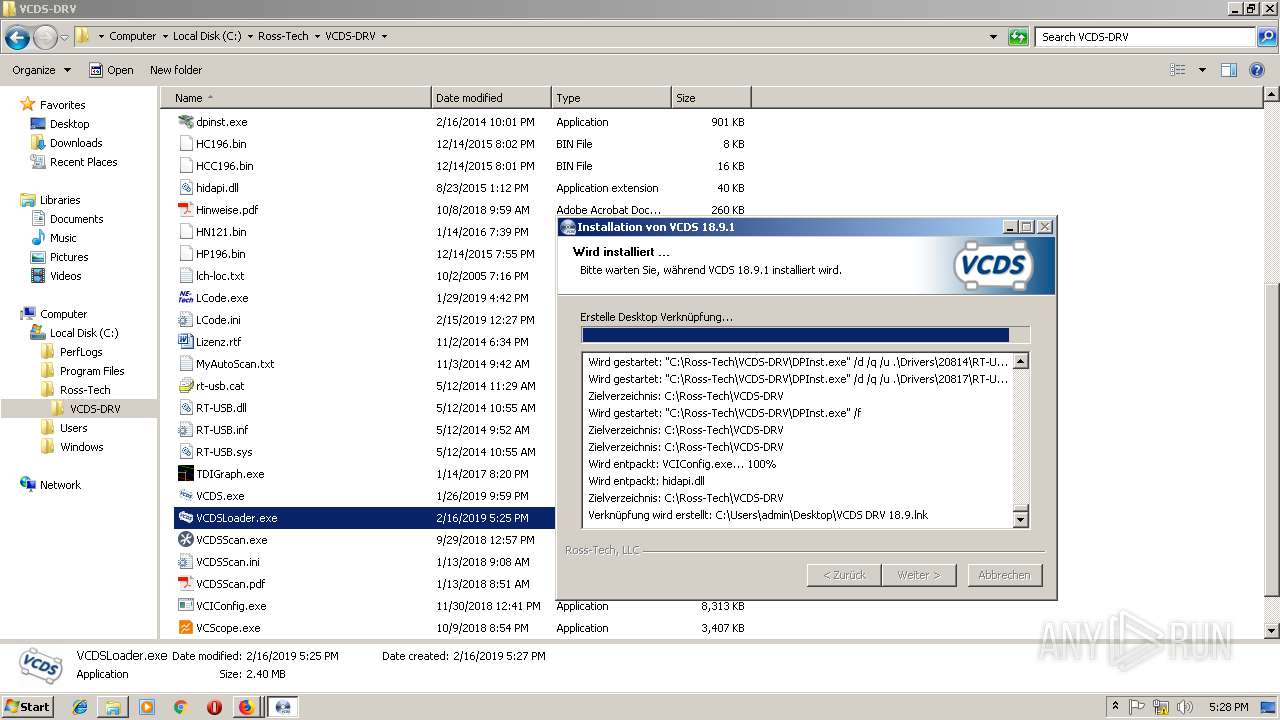
Executable content was dropped or overwritten
- firefox.exe (PID: 2308)
- VCDS-DRV-18091-Installer.exe (PID: 924)
- DPInst.exe (PID: 2700)
- DrvInst.exe (PID: 1520)
- VCDSLoader.exe (PID: 2184)
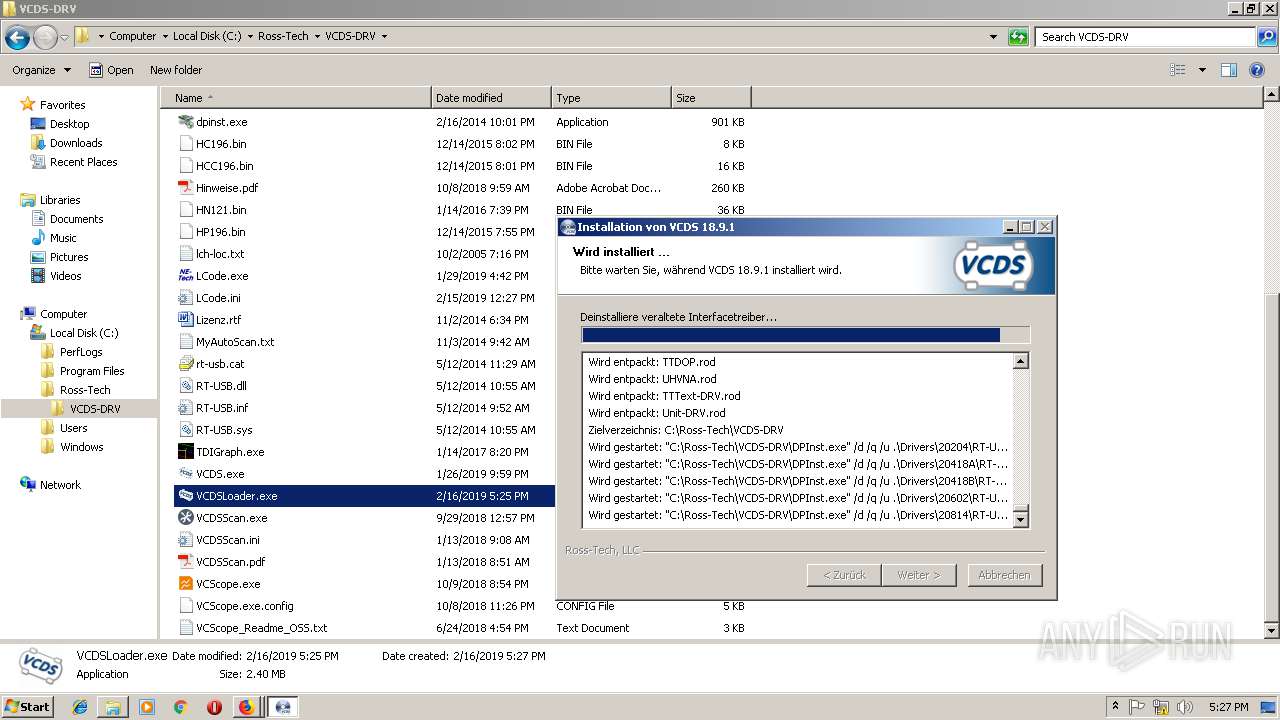
Creates files in the Windows directory
- DPInst.exe (PID: 3376)
- DrvInst.exe (PID: 1520)
Removes files from Windows directory
- DrvInst.exe (PID: 1520)
Creates files in the driver directory
- DrvInst.exe (PID: 1520)
Searches for installed software
- DrvInst.exe (PID: 1520)
Creates a software uninstall entry
- DPInst.exe (PID: 2700)
- VCDS-DRV-18091-Installer.exe (PID: 924)
Creates files in the program directory
- DPInst.exe (PID: 2700)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 1520)
Starts application with an unusual extension
- VCDS-DRV-18091-Installer.exe (PID: 924)
INFO
Reads CPU info
- firefox.exe (PID: 2308)
- firefox.exe (PID: 568)
- firefox.exe (PID: 3608)
- firefox.exe (PID: 3380)
Creates files in the user directory
- firefox.exe (PID: 2308)
Application launched itself
- firefox.exe (PID: 2308)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2308)
- VCDS-DRV-18091-Installer.exe (PID: 924)
Reads settings of System Certificates
- firefox.exe (PID: 2308)
Changes settings of System certificates
- DrvInst.exe (PID: 1520)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 1520)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:06 10:13:12+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2420736 |
| InitializedDataSize: | 98304 |
| UninitializedDataSize: | 6389760 |
| EntryPoint: | 0x867bb0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Dec-2018 09:13:12 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 06-Dec-2018 09:13:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
1111 | 0x00619000 | 0x0024F000 | 0x0024EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93422 |
0000 | 0x00001000 | 0x00618000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00868000 | 0x00018000 | 0x00017C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.64454 |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
netapi32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
100
Monitored processes
46
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | wmic /NAMESPACE:\\root\CIMV2 path Win32_Processor get Name | C:\Windows\System32\Wbem\wmic.exe | — | nsFE51.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 556 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000005F4" "000005F0" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2308.0.398259873\980185700" -childID 1 -isForBrowser -prefsHandle 1416 -prefsLen 8309 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2308 "\\.\pipe\gecko-crash-server-pipe.2308" 1296 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 792 | "C:\Ross-Tech\VCDS-DRV\DPInst.exe" /d /q /u .\Drivers\20418A\RT-USB.inf | C:\Ross-Tech\VCDS-DRV\DPInst.exe | — | VCDS-DRV-18091-Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 2147483648 Version: 2.1 Modules
| |||||||||||||||
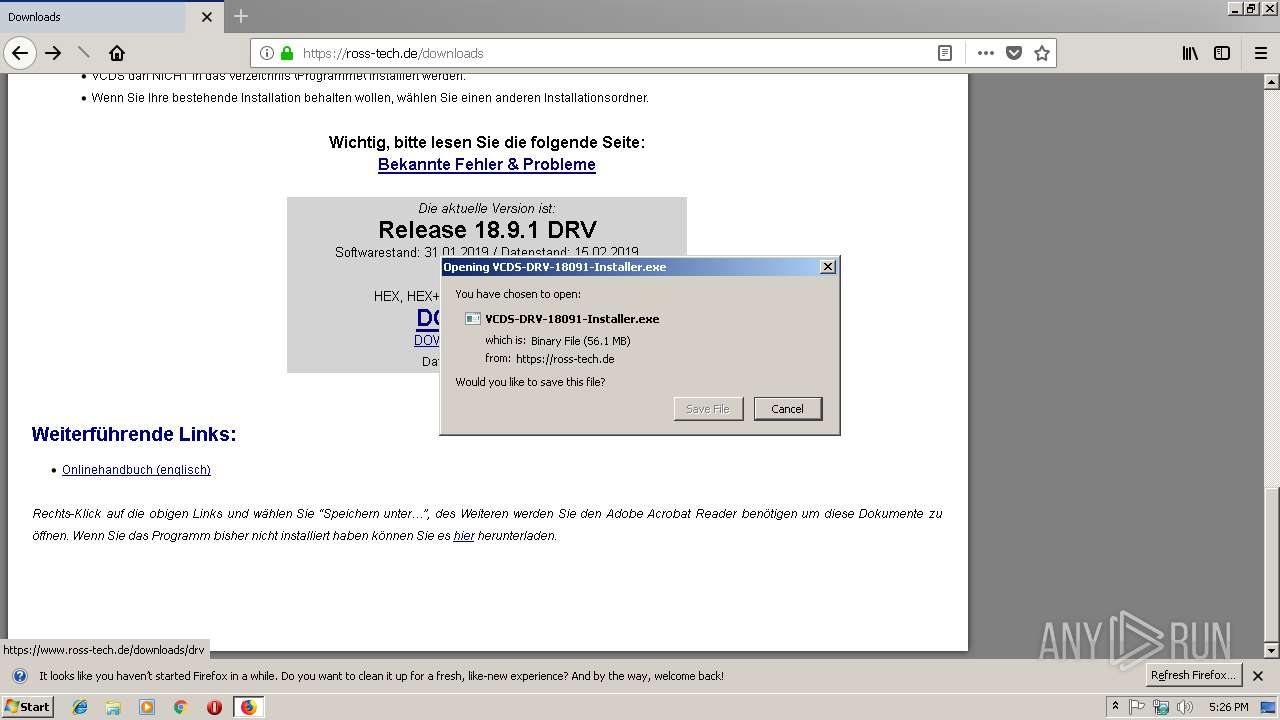
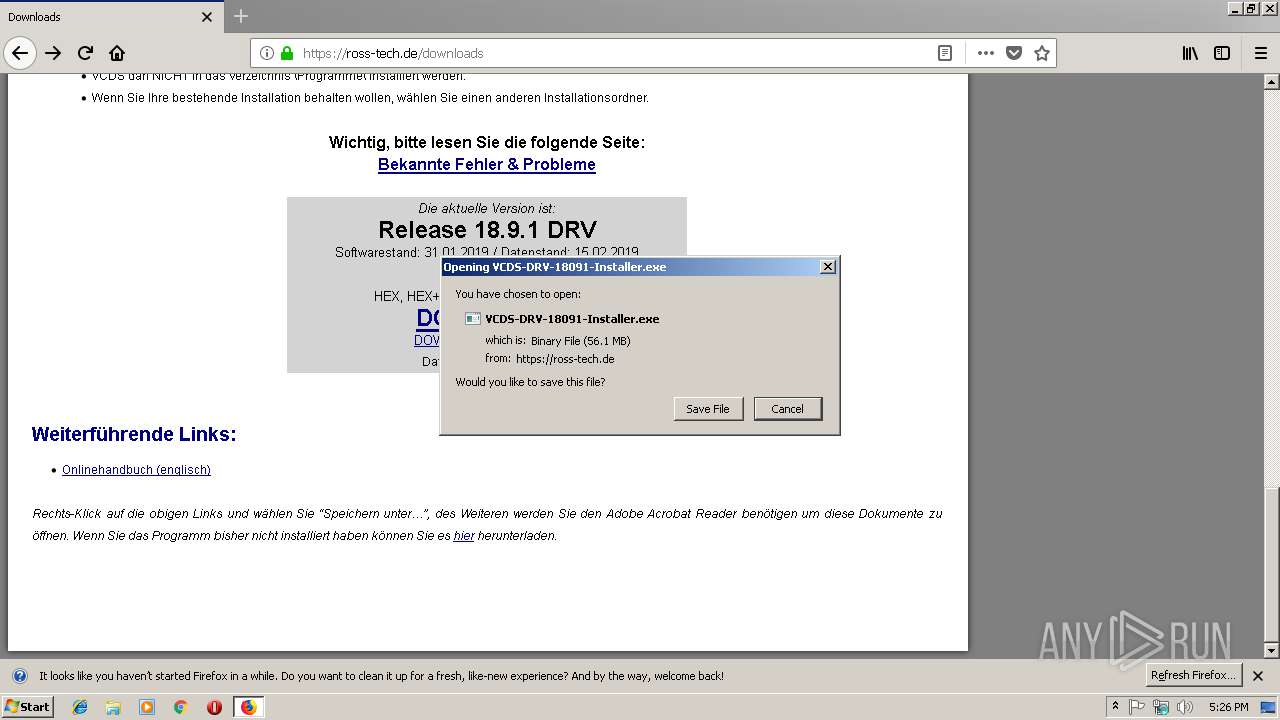
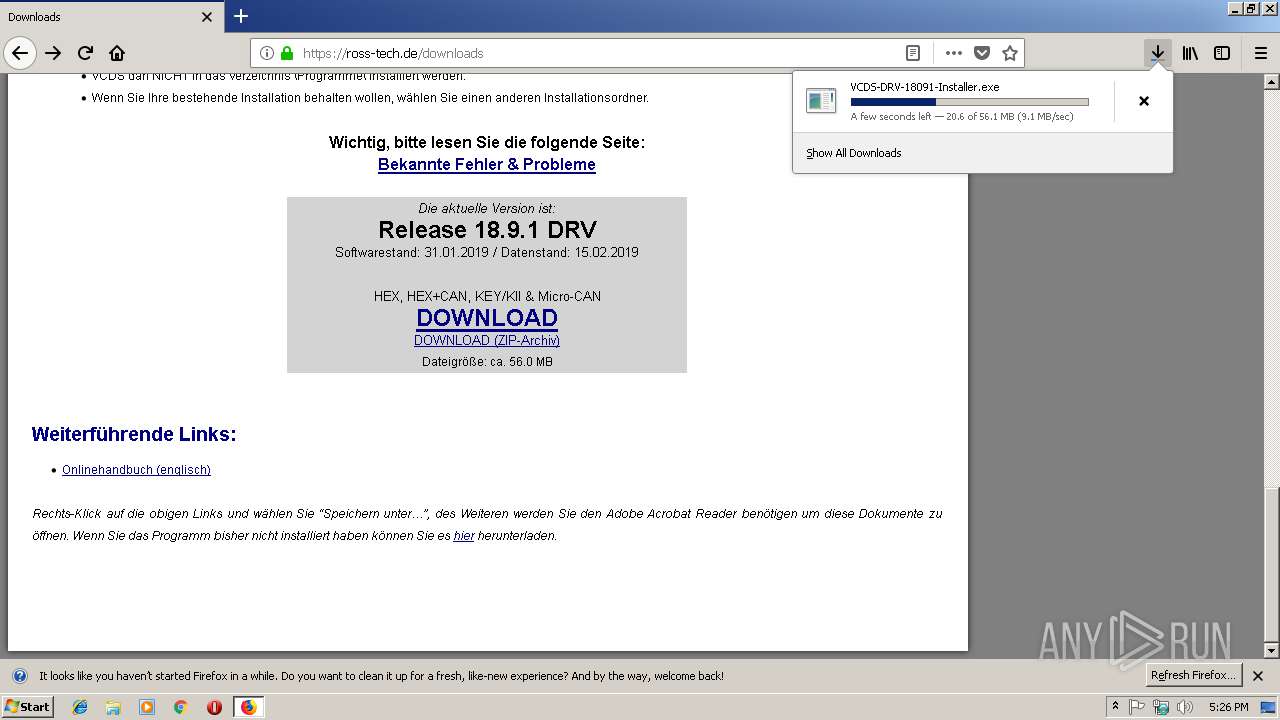
| 924 | "C:\Users\admin\Downloads\VCDS-DRV-18091-Installer.exe" | C:\Users\admin\Downloads\VCDS-DRV-18091-Installer.exe | explorer.exe | ||||||||||||
User: admin Company: Ross-Tech, LLC Integrity Level: HIGH Description: VCDS Installationsprogramm Exit code: 0 Version: 3.2.12.257 / v3.03 Modules
| |||||||||||||||
| 1356 | wmic /NAMESPACE:\\root\CIMV2 path Win32_BIOS get Version | C:\Windows\System32\Wbem\wmic.exe | — | ns5A8.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1420 | wmic /NAMESPACE:\\root\CIMV2 path Win32_NetworkAdapter get MACAddress | C:\Windows\System32\Wbem\wmic.exe | — | ns1280.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1520 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{704d8d18-b832-38d7-ddf4-db23fd4bc63a}\rt-usb.inf" "0" "6f6034a0b" "0000058C" "WinSta0\Default" "00000060" "208" "c:\ross-tech\vcds-drv" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1720 | "C:\Users\admin\AppData\Local\Temp\nsw4F08.tmp\ns1280.tmp" wmic /NAMESPACE:\\root\CIMV2 path Win32_NetworkAdapter get MACAddress | C:\Users\admin\AppData\Local\Temp\nsw4F08.tmp\ns1280.tmp | — | VCDS-DRV-18091-Installer.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1784 | "C:\Ross-Tech\VCDS-DRV\DPInst.exe" /d /q /u .\Drivers\20602\RT-USB.inf | C:\Ross-Tech\VCDS-DRV\DPInst.exe | — | VCDS-DRV-18091-Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 2147483648 Version: 2.1 Modules
| |||||||||||||||
Total events
2 334
Read events
2 036
Write events
298
Delete events
0
Modification events
| (PID) Process: | (2308) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2308) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2308) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2308) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2308) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (924) VCDS-DRV-18091-Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (924) VCDS-DRV-18091-Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3376) DPInst.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (792) DPInst.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2284) DPInst.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
53
Suspicious files
1 669
Text files
10 939
Unknown types
158
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2308 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2308 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\F4791798CB43F9FD04864DD2B921874B1CBCD11A | der | |
MD5:— | SHA256:— | |||
| 2308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2308 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.pset | cdxl | |
MD5:076933FF9904D1110D896E2C525E39E5 | SHA256:4CBBD8CA5215B8D161AEC181A74B694F4E24B001D5B081DC0030ED797A8973E0 | |||
| 2308 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.pset | cdxl | |
MD5:076933FF9904D1110D896E2C525E39E5 | SHA256:4CBBD8CA5215B8D161AEC181A74B694F4E24B001D5B081DC0030ED797A8973E0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
59
DNS requests
133
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2308 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
2308 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2308 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
2308 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
2308 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2308 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
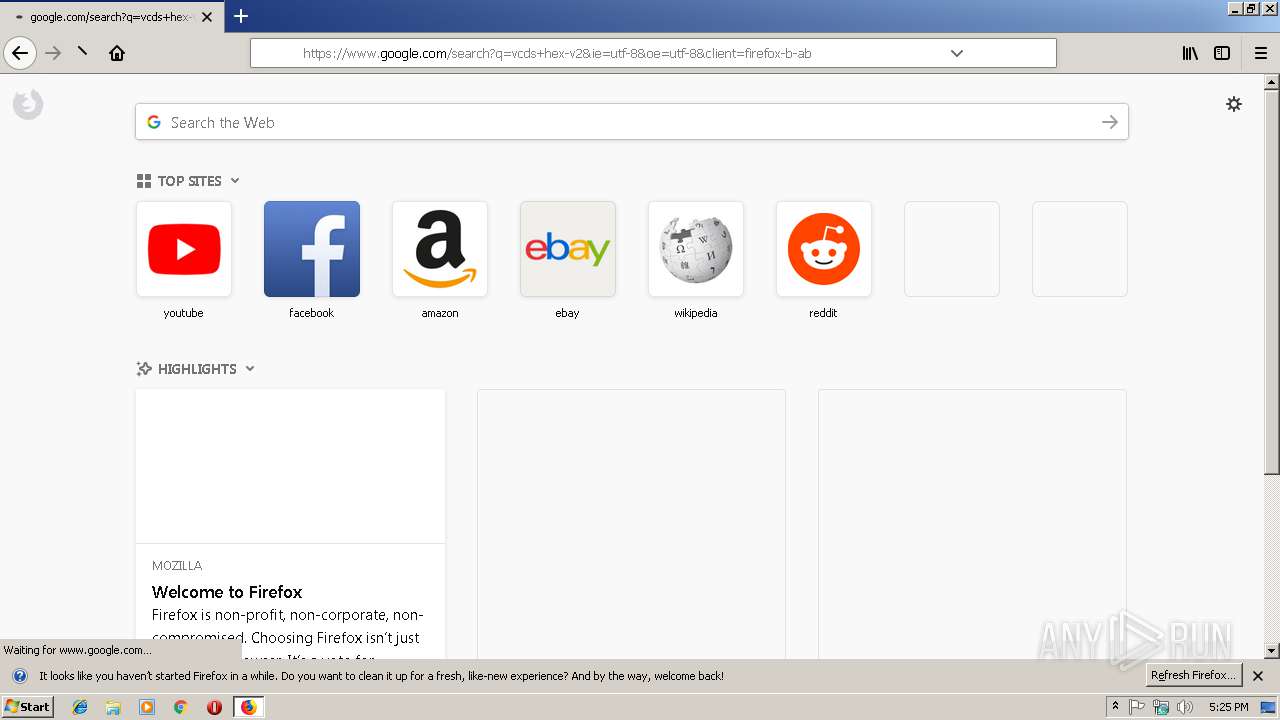
2308 | firefox.exe | GET | 200 | 207.58.189.11:80 | http://www.ross-tech.com/images/Flag-AR.jpg | US | image | 9.67 Kb | suspicious |
2308 | firefox.exe | GET | 200 | 207.58.189.11:80 | http://www.ross-tech.com/vcds/if-pics/IFP-HV2.jpg | US | image | 13.3 Kb | suspicious |
2308 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
2308 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2308 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2308 | firefox.exe | 52.27.184.151:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2308 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2308 | firefox.exe | 52.39.131.77:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2308 | firefox.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
2308 | firefox.exe | 52.222.150.25:443 | d1zkz3k4cclnv6.cloudfront.net | Amazon.com, Inc. | US | unknown |
2308 | firefox.exe | 172.217.16.206:443 | www.youtube.com | Google Inc. | US | whitelisted |
2308 | firefox.exe | 52.35.215.194:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2308 | firefox.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
2308 | firefox.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
drcwo519tnci7.cloudfront.net |
| shared |