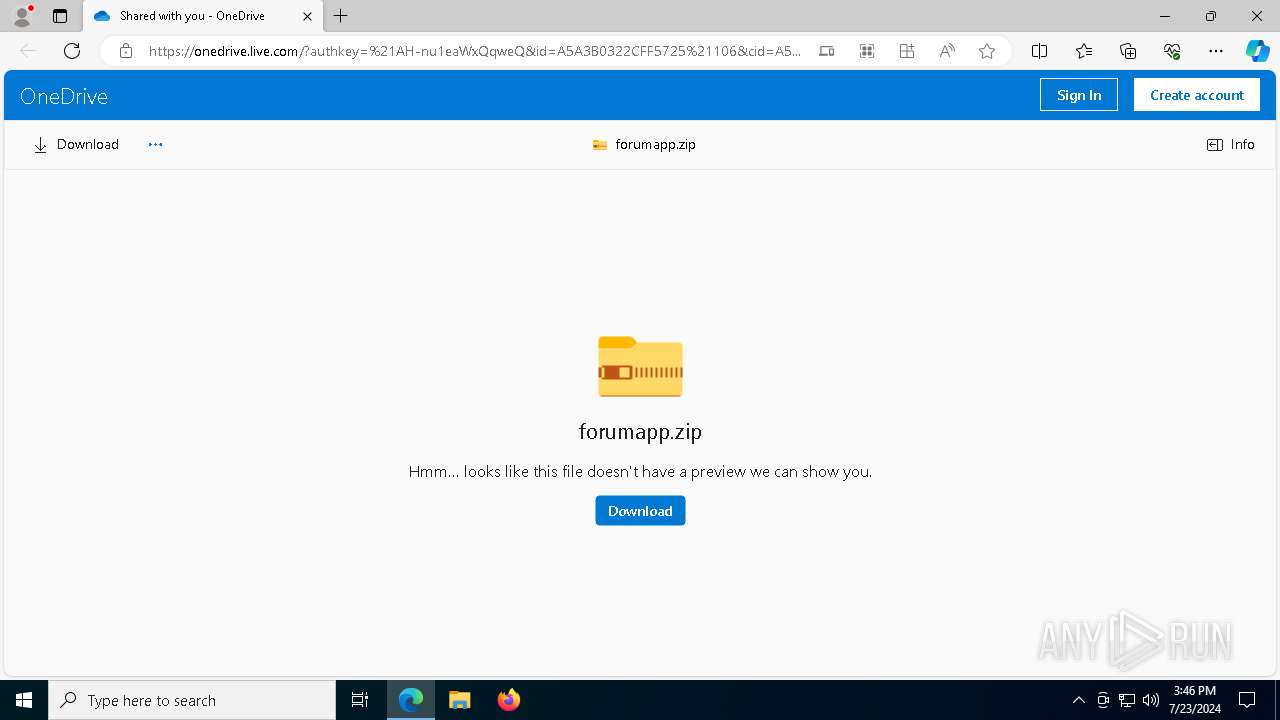
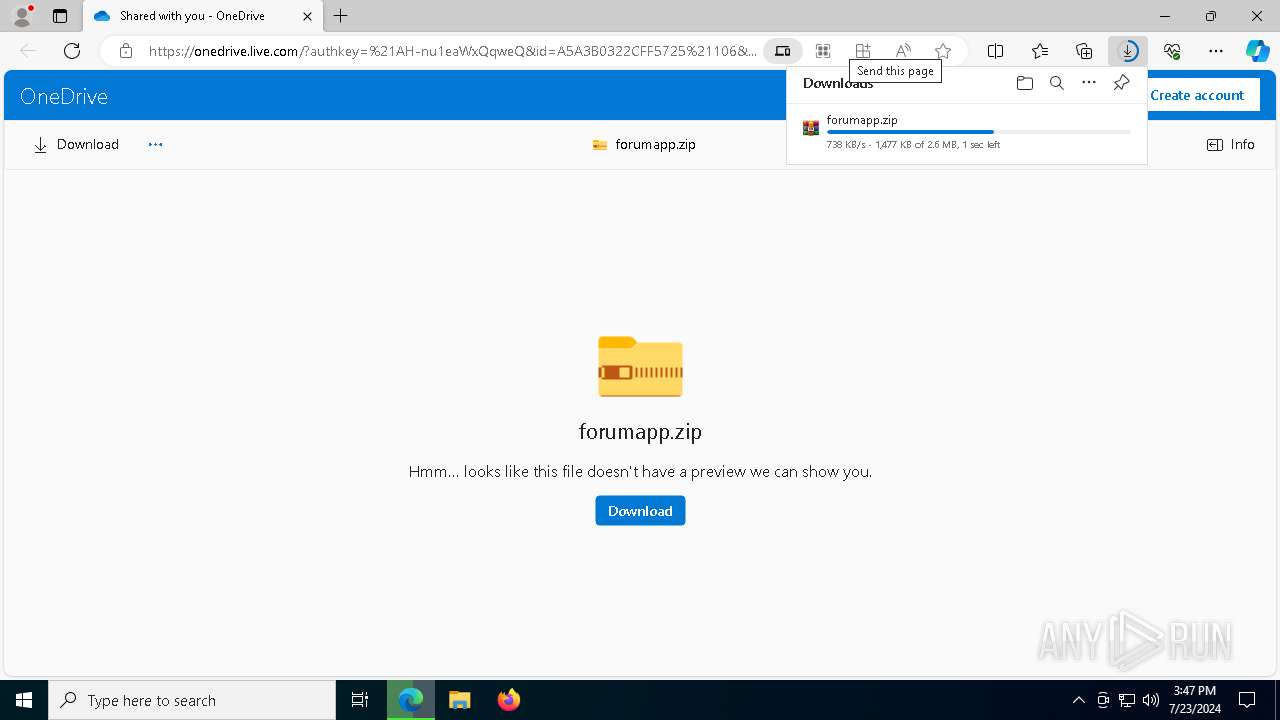
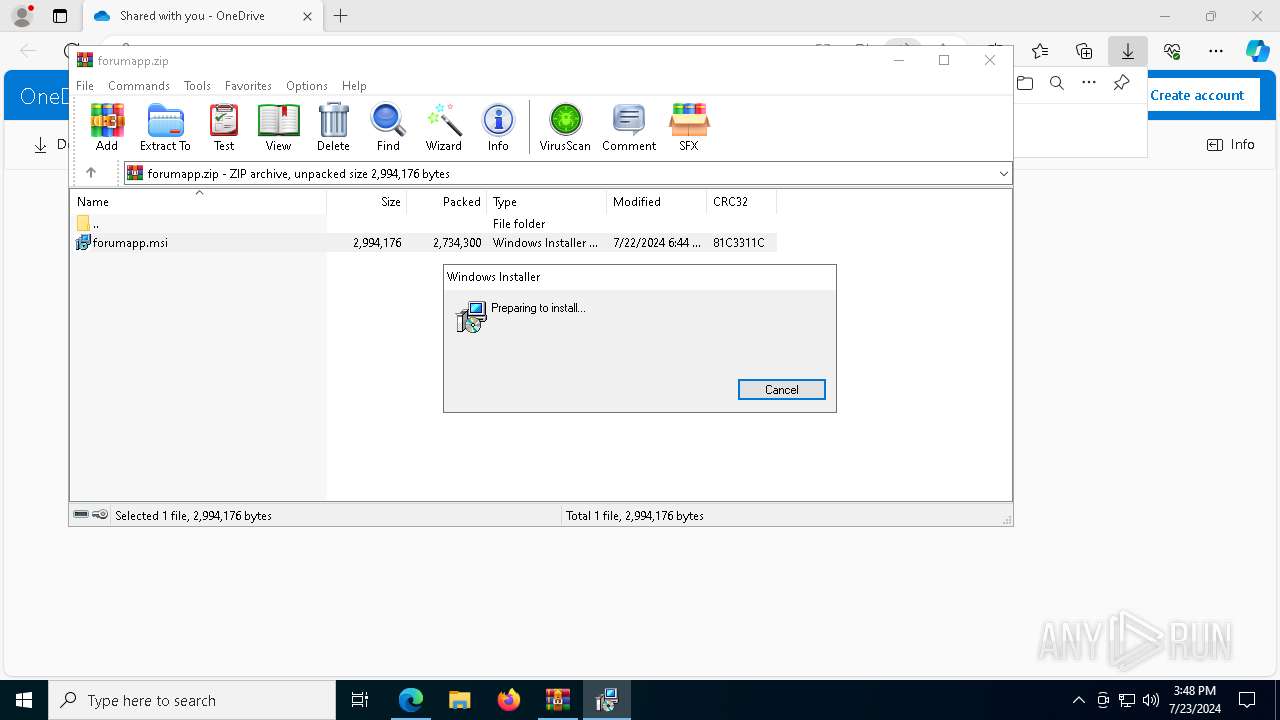
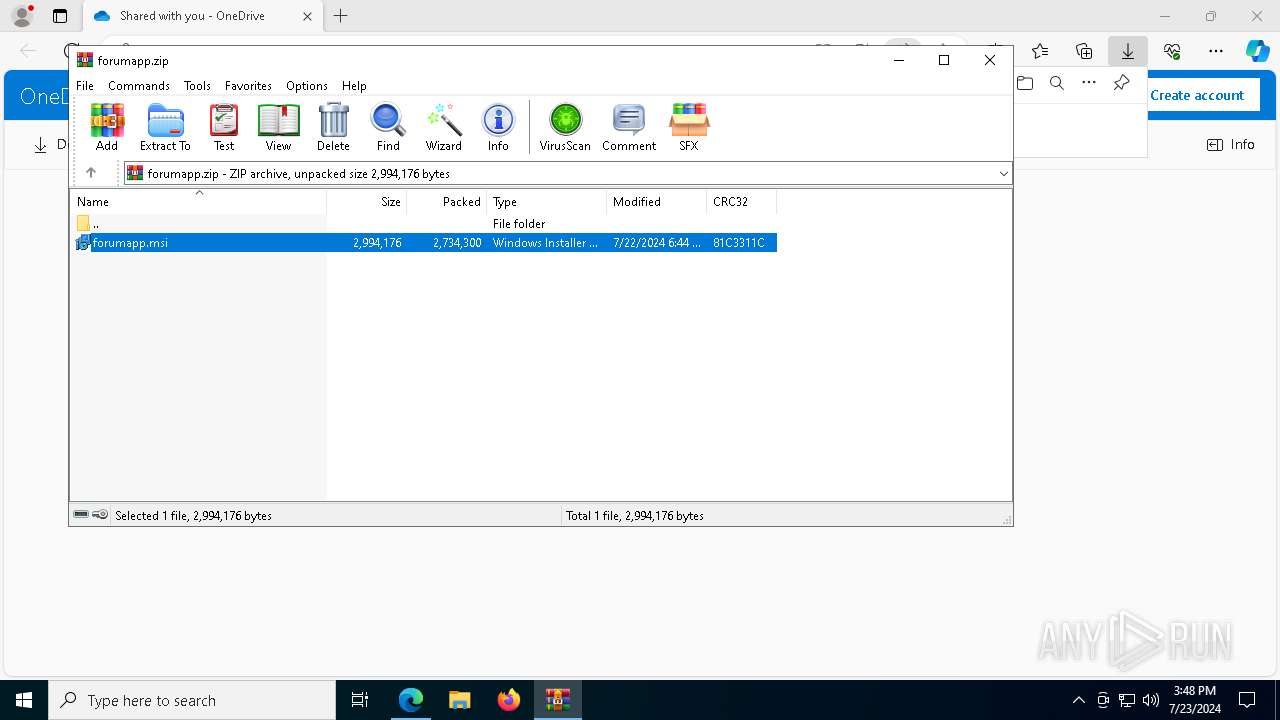
| URL: | https://1drv.ms/u/s!AiVX_ywysKOlan-nu1eaWxQqweQ?e=3DXaVbFg |
| Full analysis: | https://app.any.run/tasks/a452250a-7b9f-4211-a257-2559192cf91a |
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2024, 15:44:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C7AE53317B00ECC2DBAF7355120954D8 |
| SHA1: | 88FFDDE2A248E065FB438C9F53AD21E687E1A373 |
| SHA256: | 8FDDC486C04DDC120E35AEEBE95901A18DB5AC3ABEE592246C8A5A80E5F418A3 |
| SSDEEP: | 3:N8qDLIWKfXSuXajyzSAYhsC:2qXyXSIaO+PsC |
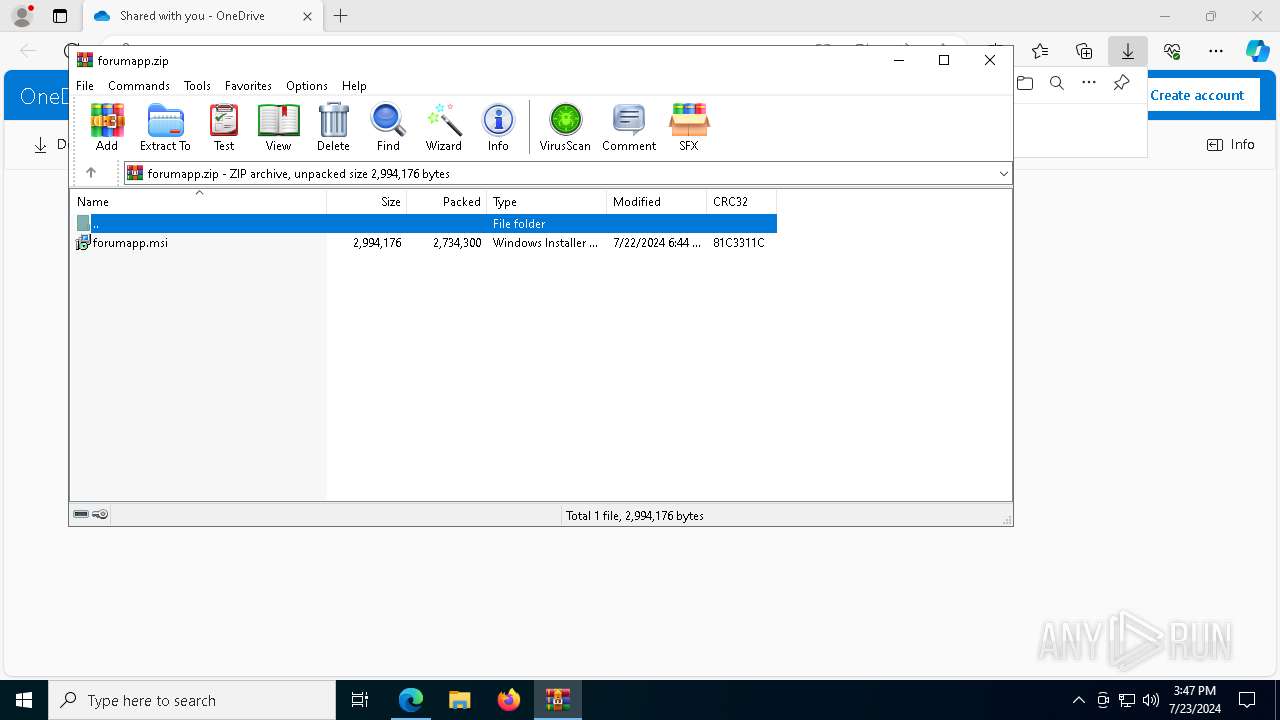
MALICIOUS
ATERAAGENT has been detected (YARA)
- msiexec.exe (PID: 3044)
- msiexec.exe (PID: 4288)
Drops the executable file immediately after the start
- msiexec.exe (PID: 3044)
- AteraAgent.exe (PID: 3048)
Starts NET.EXE for service management
- msiexec.exe (PID: 3840)
- net.exe (PID: 7124)
SUSPICIOUS
Process drops legitimate windows executable
- msedge.exe (PID: 4860)
- msedge.exe (PID: 1132)
- WinRAR.exe (PID: 7196)
- msiexec.exe (PID: 3044)
- rundll32.exe (PID: 6376)
- rundll32.exe (PID: 5808)
- rundll32.exe (PID: 7888)
- rundll32.exe (PID: 3008)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7196)
- AteraAgent.exe (PID: 6084)
- AteraAgent.exe (PID: 3048)
Executes as Windows Service
- VSSVC.exe (PID: 1552)
- AteraAgent.exe (PID: 3048)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3044)
Checks Windows Trust Settings
- msiexec.exe (PID: 3044)
- AteraAgent.exe (PID: 6084)
Executable content was dropped or overwritten
- rundll32.exe (PID: 6376)
- rundll32.exe (PID: 5808)
- rundll32.exe (PID: 7888)
- rundll32.exe (PID: 3008)
- AteraAgent.exe (PID: 3048)
Uses TASKKILL.EXE to kill process
- msiexec.exe (PID: 3840)
Starts SC.EXE for service management
- AteraAgent.exe (PID: 3048)
Reads the date of Windows installation
- AteraAgent.exe (PID: 3048)
Potential Corporate Privacy Violation
- rundll32.exe (PID: 5808)
- AteraAgent.exe (PID: 3048)
- rundll32.exe (PID: 3008)
- AgentPackageAgentInformation.exe (PID: 6316)
- AgentPackageAgentInformation.exe (PID: 888)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 1132)
- WinRAR.exe (PID: 7196)
Application launched itself
- msedge.exe (PID: 1132)
Checks supported languages
- identity_helper.exe (PID: 2068)
- TextInputHost.exe (PID: 7376)
- msiexec.exe (PID: 3044)
- msiexec.exe (PID: 2888)
- msiexec.exe (PID: 3840)
- AteraAgent.exe (PID: 6084)
- AteraAgent.exe (PID: 3048)
- AgentPackageAgentInformation.exe (PID: 6316)
- AgentPackageAgentInformation.exe (PID: 888)
Reads the computer name
- identity_helper.exe (PID: 2068)
- TextInputHost.exe (PID: 7376)
- msiexec.exe (PID: 3044)
- msiexec.exe (PID: 2888)
- msiexec.exe (PID: 3840)
- AteraAgent.exe (PID: 6084)
- AteraAgent.exe (PID: 3048)
- AgentPackageAgentInformation.exe (PID: 6316)
- AgentPackageAgentInformation.exe (PID: 888)
Reads Environment values
- identity_helper.exe (PID: 2068)
- AteraAgent.exe (PID: 6084)
- AteraAgent.exe (PID: 3048)
- AgentPackageAgentInformation.exe (PID: 888)
- AgentPackageAgentInformation.exe (PID: 6316)
Drops the executable file immediately after the start
- msedge.exe (PID: 4860)
- msedge.exe (PID: 1132)
- WinRAR.exe (PID: 7196)
- rundll32.exe (PID: 6376)
- rundll32.exe (PID: 5808)
- rundll32.exe (PID: 7888)
- rundll32.exe (PID: 3008)
The process uses the downloaded file
- msedge.exe (PID: 7752)
- WinRAR.exe (PID: 7196)
- msedge.exe (PID: 1132)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 4288)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7196)
- msiexec.exe (PID: 3044)
Reads the software policy settings
- msiexec.exe (PID: 4288)
- msiexec.exe (PID: 3044)
- rundll32.exe (PID: 5808)
- AteraAgent.exe (PID: 6084)
- AteraAgent.exe (PID: 3048)
- AgentPackageAgentInformation.exe (PID: 888)
- AgentPackageAgentInformation.exe (PID: 6316)
- rundll32.exe (PID: 3008)
Creates files or folders in the user directory
- msiexec.exe (PID: 4288)
Checks proxy server information
- msiexec.exe (PID: 4288)
- rundll32.exe (PID: 5808)
- rundll32.exe (PID: 3008)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3044)
- AteraAgent.exe (PID: 6084)
- AteraAgent.exe (PID: 3048)
- AgentPackageAgentInformation.exe (PID: 888)
- AgentPackageAgentInformation.exe (PID: 6316)
Create files in a temporary directory
- rundll32.exe (PID: 6376)
- rundll32.exe (PID: 5808)
- rundll32.exe (PID: 7888)
- rundll32.exe (PID: 3008)
Disables trace logs
- rundll32.exe (PID: 5808)
- rundll32.exe (PID: 3008)
- AteraAgent.exe (PID: 3048)
- AgentPackageAgentInformation.exe (PID: 6316)
- AgentPackageAgentInformation.exe (PID: 888)
Creates a software uninstall entry
- msiexec.exe (PID: 3044)
Creates files in the program directory
- AteraAgent.exe (PID: 6084)
- AteraAgent.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
225
Monitored processes
78
Malicious processes
5
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe" 99ed0b54-0a9e-445e-b237-9c7a0deb8e11 "00c0a643-e0db-4ba1-a7d6-bde364ec1156" agent-api.atera.com/Production 443 or8ixLi90Mf "minimalIdentification" 001Q300000KToluIAD | C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe | AteraAgent.exe | ||||||||||||
User: SYSTEM Company: Atera Networks Integrity Level: SYSTEM Description: AgentPackageAgentInformation Exit code: 0 Version: 37.2.0.0 Modules
| |||||||||||||||
| 1000 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3676 --field-trial-handle=2348,i,14949936612146306395,12843790626537172314,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://1drv.ms/u/s!AiVX_ywysKOlan-nu1eaWxQqweQ?e=3DXaVbFg" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1552 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2068 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5572 --field-trial-handle=2348,i,14949936612146306395,12843790626537172314,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2872 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2884 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=1540 --field-trial-handle=2348,i,14949936612146306395,12843790626537172314,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2888 | C:\Windows\syswow64\MsiExec.exe -Embedding 6C340240D314E834D679DD5189A1E8A4 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2912 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5128 --field-trial-handle=2348,i,14949936612146306395,12843790626537172314,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
40 706
Read events
40 286
Write events
396
Delete events
24
Modification events
| (PID) Process: | (1132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (1132) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1132) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
37
Suspicious files
377
Text files
120
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe266f.TMP | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe267f.TMP | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe267f.TMP | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe266f.TMP | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe26cd.TMP | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
115
DNS requests
95
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5528 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6e6d05a2-47e8-42b8-85a0-e8b7ee48333a?P1=1722295790&P2=404&P3=2&P4=llOGHK5T7U87EY7jdQu3YID%2fYznqiRu1QGy811rKpUnO1rM8Nc5xzWHzaF%2fLQLMQixEU9B3u9dXCcGxi5rdPDA%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6e6d05a2-47e8-42b8-85a0-e8b7ee48333a?P1=1722295790&P2=404&P3=2&P4=llOGHK5T7U87EY7jdQu3YID%2fYznqiRu1QGy811rKpUnO1rM8Nc5xzWHzaF%2fLQLMQixEU9B3u9dXCcGxi5rdPDA%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6e6d05a2-47e8-42b8-85a0-e8b7ee48333a?P1=1722295790&P2=404&P3=2&P4=llOGHK5T7U87EY7jdQu3YID%2fYznqiRu1QGy811rKpUnO1rM8Nc5xzWHzaF%2fLQLMQixEU9B3u9dXCcGxi5rdPDA%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d1341e55-98c5-4092-9eed-9f565b77bd81?P1=1722325934&P2=404&P3=2&P4=EXMoghE2Q5p0zo%2btAeU13sH0A%2biigoKpeSMsyn6tw%2bFRP3sfD8bK06ZYk%2fADe9pRexkP7W%2fuaDnZQRvSQJ9Gqw%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6e6d05a2-47e8-42b8-85a0-e8b7ee48333a?P1=1722295790&P2=404&P3=2&P4=llOGHK5T7U87EY7jdQu3YID%2fYznqiRu1QGy811rKpUnO1rM8Nc5xzWHzaF%2fLQLMQixEU9B3u9dXCcGxi5rdPDA%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d1341e55-98c5-4092-9eed-9f565b77bd81?P1=1722325934&P2=404&P3=2&P4=EXMoghE2Q5p0zo%2btAeU13sH0A%2biigoKpeSMsyn6tw%2bFRP3sfD8bK06ZYk%2fADe9pRexkP7W%2fuaDnZQRvSQJ9Gqw%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d1341e55-98c5-4092-9eed-9f565b77bd81?P1=1722325934&P2=404&P3=2&P4=EXMoghE2Q5p0zo%2btAeU13sH0A%2biigoKpeSMsyn6tw%2bFRP3sfD8bK06ZYk%2fADe9pRexkP7W%2fuaDnZQRvSQJ9Gqw%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d1341e55-98c5-4092-9eed-9f565b77bd81?P1=1722325934&P2=404&P3=2&P4=EXMoghE2Q5p0zo%2btAeU13sH0A%2biigoKpeSMsyn6tw%2bFRP3sfD8bK06ZYk%2fADe9pRexkP7W%2fuaDnZQRvSQJ9Gqw%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d1341e55-98c5-4092-9eed-9f565b77bd81?P1=1722325934&P2=404&P3=2&P4=EXMoghE2Q5p0zo%2btAeU13sH0A%2biigoKpeSMsyn6tw%2bFRP3sfD8bK06ZYk%2fADe9pRexkP7W%2fuaDnZQRvSQJ9Gqw%3d%3d | unknown | — | — | whitelisted |
5528 | svchost.exe | GET | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/81c945d1-1834-4d97-ab56-9ed86990a128?P1=1722301245&P2=404&P3=2&P4=kvmNKe82flNCGAhB0FZBcO8WuZiaUap6GFzYa0%2bBZUZ98AdP5DUS%2b9dWnvBfuppCluKt1FPQHXtujQkS5YBezQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6012 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4040 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3056 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 184.86.251.4:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5272 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1132 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4860 | msedge.exe | 13.107.42.12:443 | 1drv.ms | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
1drv.ms |
| shared |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
go.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
onedrive.live.com |
| shared |
Threats
8 ETPRO signatures available at the full report