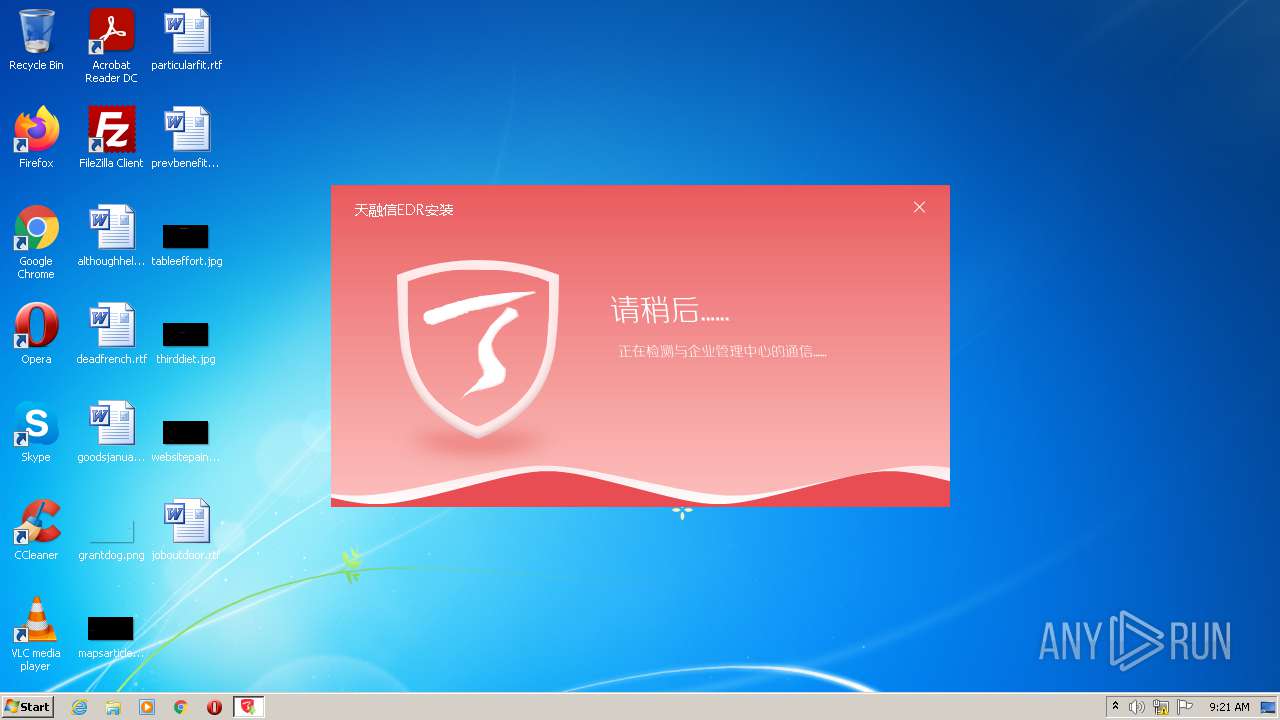
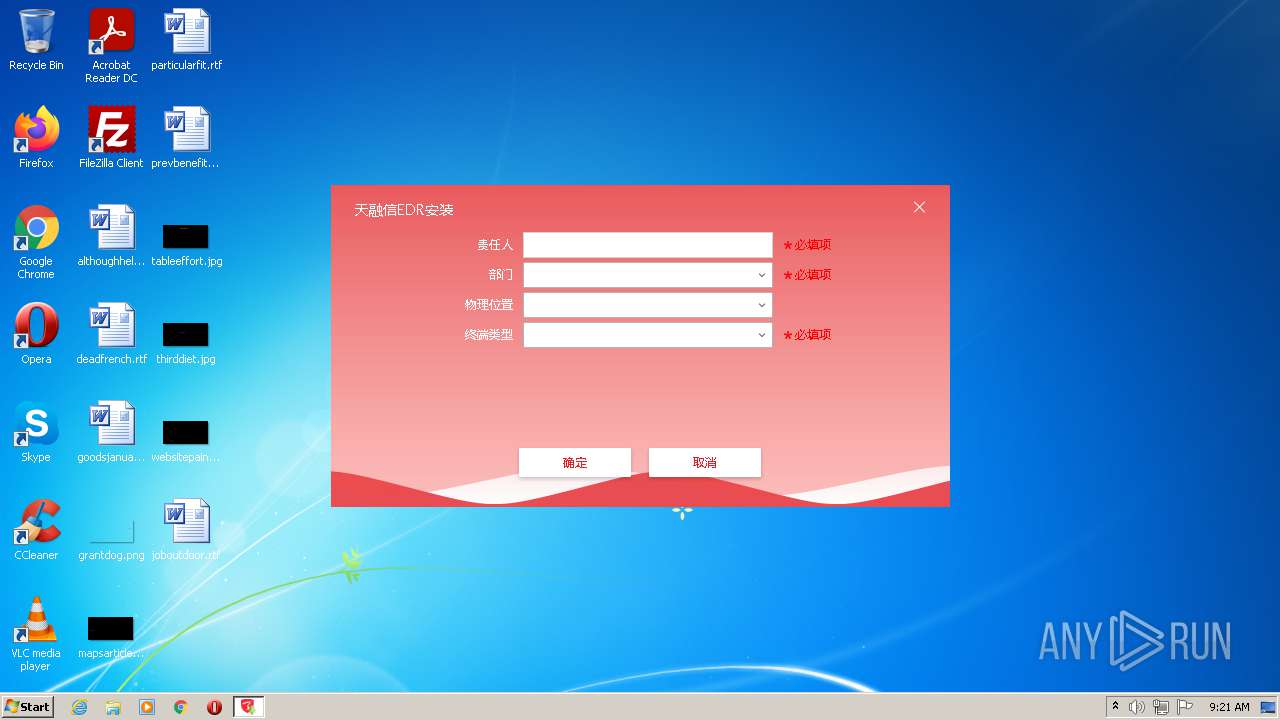
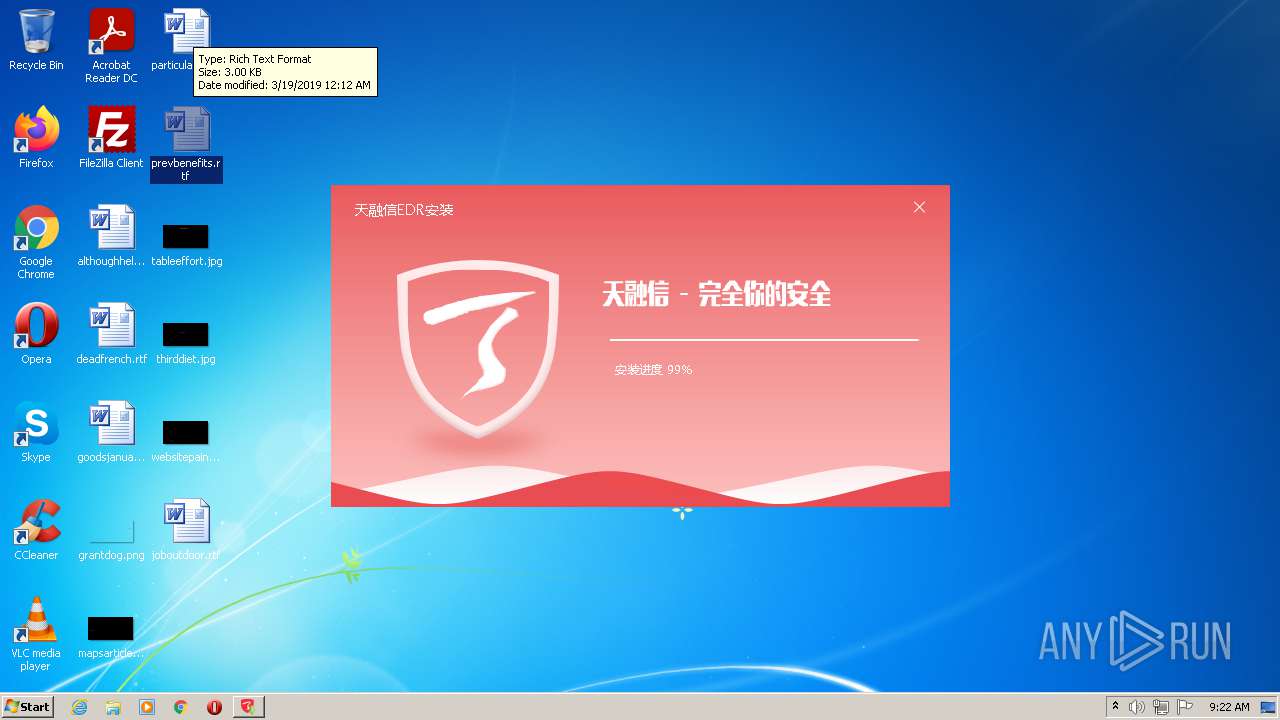
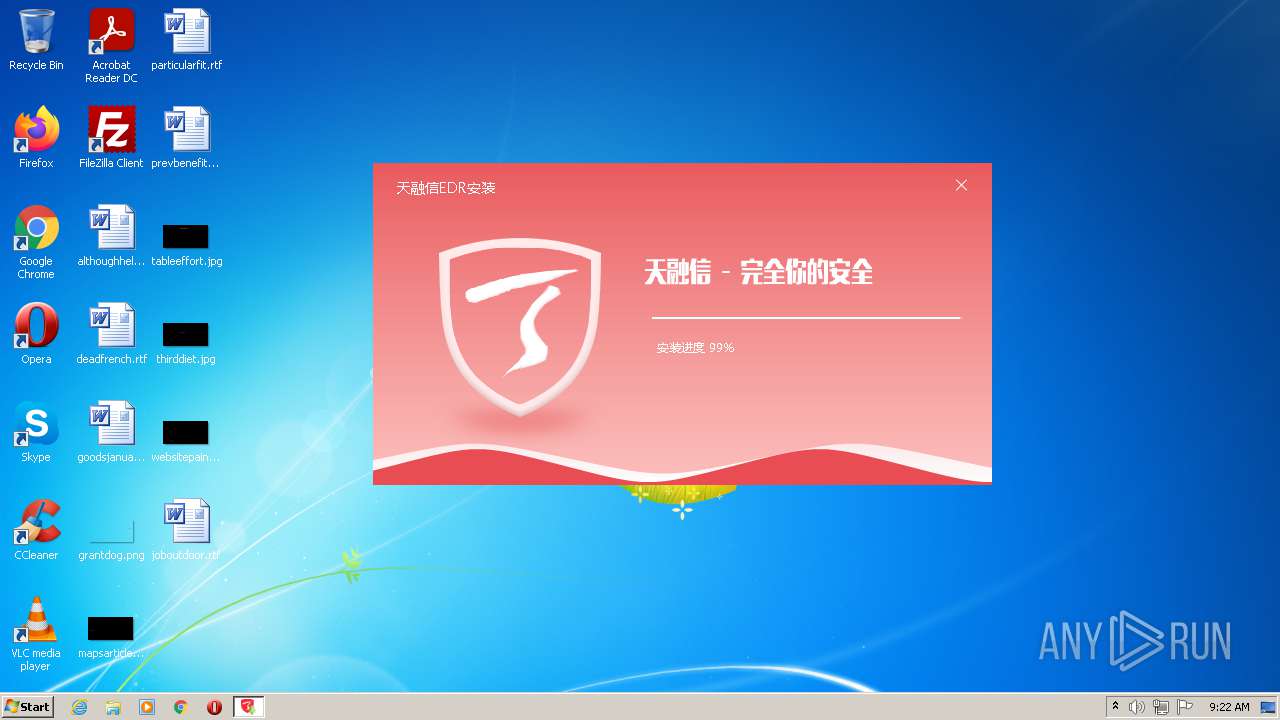
| File name: | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe |
| Full analysis: | https://app.any.run/tasks/cb5dcee8-26cc-4d3b-a3eb-cadf2b5692b8 |
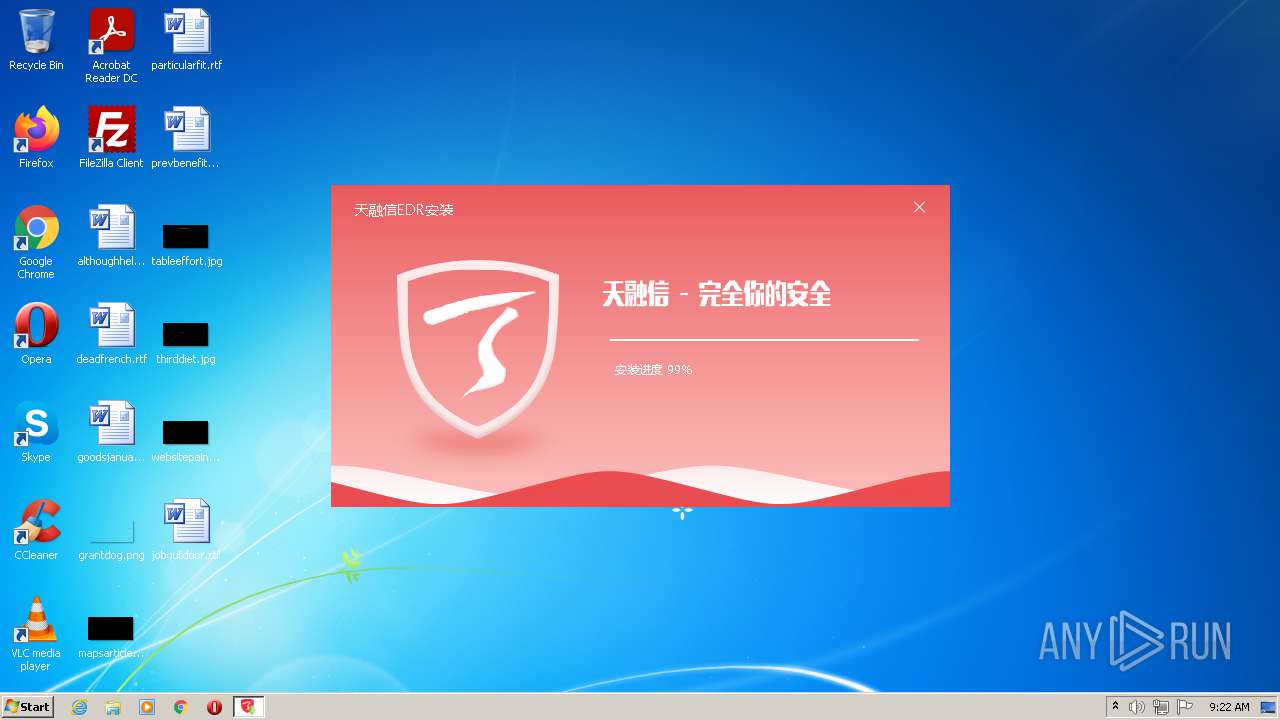
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2021, 08:21:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E12EEF5C3BC4938008ED084C925B81E6 |
| SHA1: | D73E7E41CCD7C1150F634CE210E16AB5B7C110CA |
| SHA256: | 8FD91B64F49AA33E299D426D3C6C212002AB1F5057E3EF6EB20F2B31E686F9A1 |
| SSDEEP: | 49152:QHW9IFpuj4Cm8A4Iv0TOCn7dpA92wwNKTYY:Qk2A4C/AD8T5n7PA92H8r |
MALICIOUS
Loads dropped or rewritten executable
- installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe (PID: 3260)
Starts NET.EXE for service management
- nsE573.tmp (PID: 1728)
- nsE4F5.tmp (PID: 3844)
Drops executable file immediately after starts
- installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe (PID: 3260)
SUSPICIOUS
Drops a file that was compiled in debug mode
- installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe (PID: 3260)
Executable content was dropped or overwritten
- installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe (PID: 3260)
Reads the computer name
- installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe (PID: 3260)
Checks supported languages
- installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe (PID: 3260)
- nsE4F5.tmp (PID: 3844)
- nsE573.tmp (PID: 1728)
Starts application with an unusual extension
- installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe (PID: 3260)
Executed via COM
- DllHost.exe (PID: 2504)
INFO
Checks supported languages
- net.exe (PID: 1348)
- net1.exe (PID: 1416)
- net1.exe (PID: 2316)
- DllHost.exe (PID: 2504)
- net.exe (PID: 3496)
Reads the computer name
- net1.exe (PID: 2316)
- DllHost.exe (PID: 2504)
- net1.exe (PID: 1416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 1.0.0.0 |
|---|---|
| ProductName: | Topsec Enterprise Security |
| LegalCopyright: | Beijing Topsec Network Security Technology Co., Ltd. |
| FileVersion: | 1.0.15.0 |
| FileDescription: | Topsec Enterprise Security |
| CompanyName: | Beijing Topsec Network Security Technology Co., Ltd. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.0.15.0 |
| FileVersionNumber: | 1.0.15.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x34a5 |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 141824 |
| CodeSize: | 26112 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2018:12:15 23:24:36+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:36 |
| Detected languages: |
|
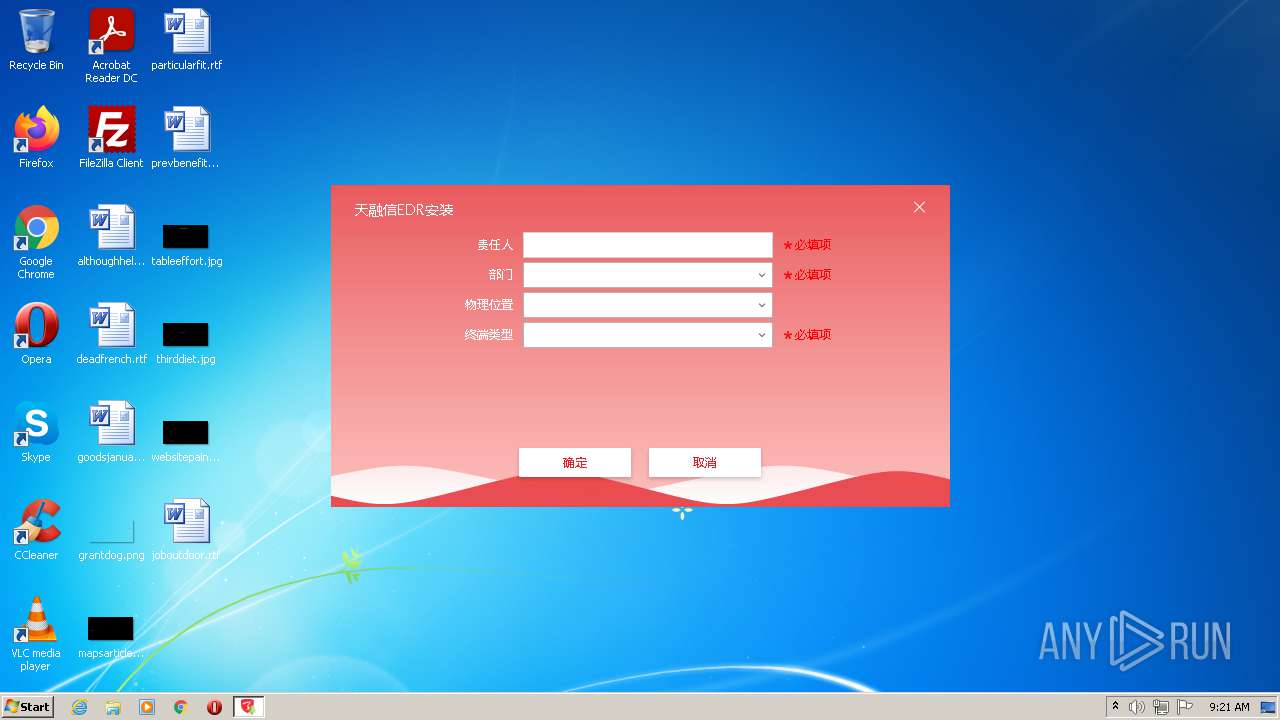
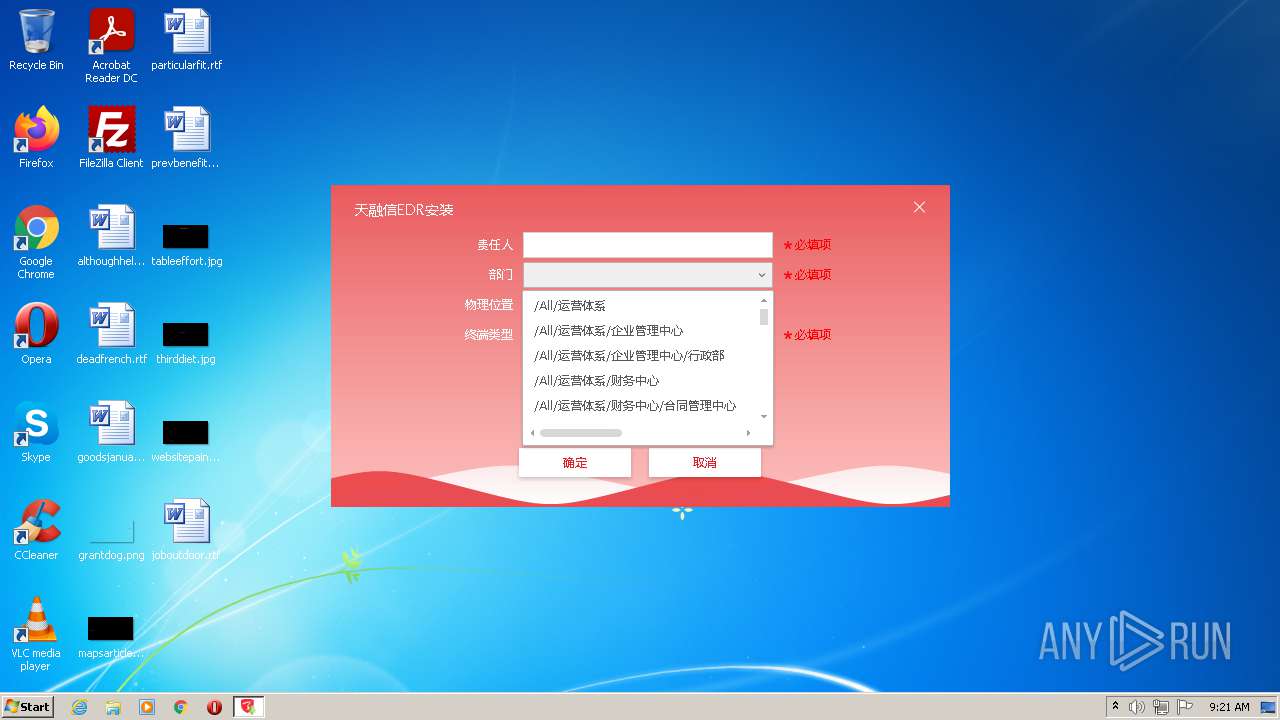
| CompanyName: | 北京天融信科技股份有限公司 |
| FileDescription: | 天融信企业安全软件 |
| FileVersion: | 1.0.15.0 |
| LegalCopyright: | 北京天融信科技股份有限公司 |
| ProductName: | 天融信企业安全软件 |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006409 | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41619 |
.rdata | 0x00008000 | 0x00001396 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15491 |
.data | 0x0000A000 | 0x00020358 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.0044 |
.ndata | 0x0002B000 | 0x00014000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003F000 | 0x00013BA8 | 0x00012E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.3716 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28733 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.68081 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.64819 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.55627 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 5.07542 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 6.00379 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 4.42841 | 1736 | UNKNOWN | English - United States | RT_ICON |
8 | 3.62304 | 1640 | UNKNOWN | English - United States | RT_ICON |
9 | 3.52553 | 1384 | UNKNOWN | English - United States | RT_ICON |
10 | 5.51801 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
47
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | net stop TopsecDaemon | C:\Windows\system32\net.exe | — | nsE4F5.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1416 | C:\Windows\system32\net1 stop TopsecClient | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1728 | "C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\nsE573.tmp" net stop TopsecClient | C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\nsE573.tmp | — | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 2316 | C:\Windows\system32\net1 stop TopsecDaemon | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2464 | "C:\Users\admin\AppData\Local\Temp\installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe" | C:\Users\admin\AppData\Local\Temp\installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Beijing Topsec Network Security Technology Co., Ltd. Integrity Level: MEDIUM Description: Topsec Enterprise Security Exit code: 3221226540 Version: 1.0.15.0 Modules
| |||||||||||||||
| 2504 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe" | C:\Users\admin\AppData\Local\Temp\installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | Explorer.EXE | ||||||||||||
User: admin Company: Beijing Topsec Network Security Technology Co., Ltd. Integrity Level: HIGH Description: Topsec Enterprise Security Exit code: 0 Version: 1.0.15.0 Modules
| |||||||||||||||
| 3496 | net stop TopsecClient | C:\Windows\system32\net.exe | — | nsE573.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3844 | "C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\nsE4F5.tmp" net stop TopsecDaemon | C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\nsE4F5.tmp | — | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
Total events
1 057
Read events
1 052
Write events
5
Delete events
0
Modification events
| (PID) Process: | (3260) installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Topsec\ESEndpoint |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files\Topsec\ESEndpoint | |||
| (PID) Process: | (3260) installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Topsec\ESEndpoint\app |
| Operation: | write | Name: | DataPath |
Value: C:\ProgramData\Topsec\ESEndpoint\ | |||
| (PID) Process: | (3260) installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Topsec\ESEndpoint\app |
| Operation: | write | Name: | UpdateLink |
Value: https://edrcom.topsec.com.cn:8090 | |||
| (PID) Process: | (2504) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (2504) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
Executable files
11
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\libcurl.dll | executable | |
MD5:— | SHA256:— | |||
| 3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\libxsse.dll | executable | |
MD5:— | SHA256:— | |||
| 3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\jansson.dll | executable | |
MD5:— | SHA256:— | |||
| 3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | C:\Users\admin\AppData\Local\Temp\swapfs-2 | binary | |
MD5:— | SHA256:— | |||
| 3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\installer-helper.dll | executable | |
MD5:— | SHA256:— | |||
| 3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\DuiLib.dll | executable | |
MD5:EF87A0AA9385A51AE7366273B6892633 | SHA256:2E92E7DD02C6EC7CF5A3D4D46D37787B22E7CDB442000413E42C1C0DB9014F66 | |||
| 3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | C:\Users\admin\AppData\Local\Temp\swapfs-4 | binary | |
MD5:— | SHA256:— | |||
| 3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\inst.ui | compressed | |
MD5:— | SHA256:— | |||
| 3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | C:\Users\admin\AppData\Local\Temp\nsn6BEB.tmp\upgrade.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3260 | installer_1.0.15.0(https#edrcom.topsec.com.cn_8090)_32_chs.exe | 111.200.39.114:8090 | edrcom.topsec.com.cn | China Unicom Beijing Province Network | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
edrcom.topsec.com.cn |
| unknown |