| File name: | 8fd02ff5ac9236bdef59109bb1ac54c51887a00928aa6181cd01af1440f37079 |
| Full analysis: | https://app.any.run/tasks/0b13e925-321a-4136-afaf-7aece7e24699 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 04:14:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
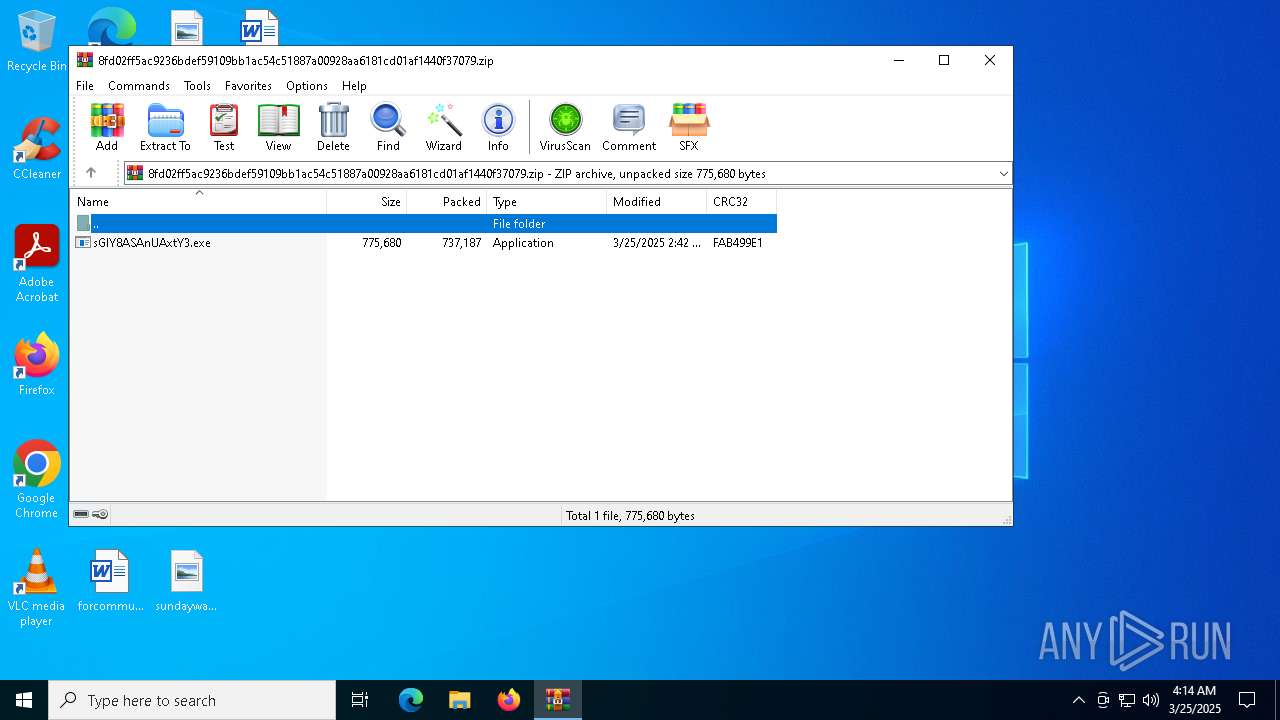
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 1A60963EC935360358E3DE9752BC51E4 |
| SHA1: | 1F86CEAA8C0B43CCE571824C809D060DB3DAF402 |
| SHA256: | 8FD02FF5AC9236BDEF59109BB1AC54C51887A00928AA6181CD01AF1440F37079 |
| SSDEEP: | 24576:x3h0TGP8btfwXSGhs8AO1ldhwP/fTKVX7AlDBwBZjAZAIbGCRKQHTg315:x3h0TGP8btfwiGh1AO1ldhwP/fTKVXkg |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6476)
Uses Task Scheduler to run other applications
- sGIY8ASAnUAxtY3.exe (PID: 1056)
SUSPICIOUS
Executable content was dropped or overwritten
- sGIY8ASAnUAxtY3.exe (PID: 1056)
Reads security settings of Internet Explorer
- sGIY8ASAnUAxtY3.exe (PID: 1056)
The process executes VB scripts
- sGIY8ASAnUAxtY3.exe (PID: 1056)
INFO
Process checks computer location settings
- sGIY8ASAnUAxtY3.exe (PID: 1056)
Create files in a temporary directory
- sGIY8ASAnUAxtY3.exe (PID: 1056)
Manual execution by a user
- sGIY8ASAnUAxtY3.exe (PID: 1056)
Checks supported languages
- sGIY8ASAnUAxtY3.exe (PID: 1056)
Reads the computer name
- sGIY8ASAnUAxtY3.exe (PID: 1056)
Reads the machine GUID from the registry
- sGIY8ASAnUAxtY3.exe (PID: 1056)
Creates files or folders in the user directory
- sGIY8ASAnUAxtY3.exe (PID: 1056)
Reads the software policy settings
- slui.exe (PID: 5256)
Checks proxy server information
- slui.exe (PID: 5256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:24 19:42:46 |
| ZipCRC: | 0xfab499e1 |
| ZipCompressedSize: | 737187 |
| ZipUncompressedSize: | 775680 |
| ZipFileName: | sGIY8ASAnUAxtY3.exe |
Total processes
135
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | sGIY8ASAnUAxtY3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 1056 | "C:\Users\admin\Desktop\sGIY8ASAnUAxtY3.exe" | C:\Users\admin\Desktop\sGIY8ASAnUAxtY3.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.4 Modules
| |||||||||||||||
| 1600 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\OcQFyyefoEr" /XML "C:\Users\admin\AppData\Local\Temp\tmp1B2.tmp" | C:\Windows\SysWOW64\schtasks.exe | — | sGIY8ASAnUAxtY3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4112 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | sGIY8ASAnUAxtY3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 5256 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5332 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | sGIY8ASAnUAxtY3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 6108 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | sGIY8ASAnUAxtY3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 14.8.9037.0 Modules
| |||||||||||||||
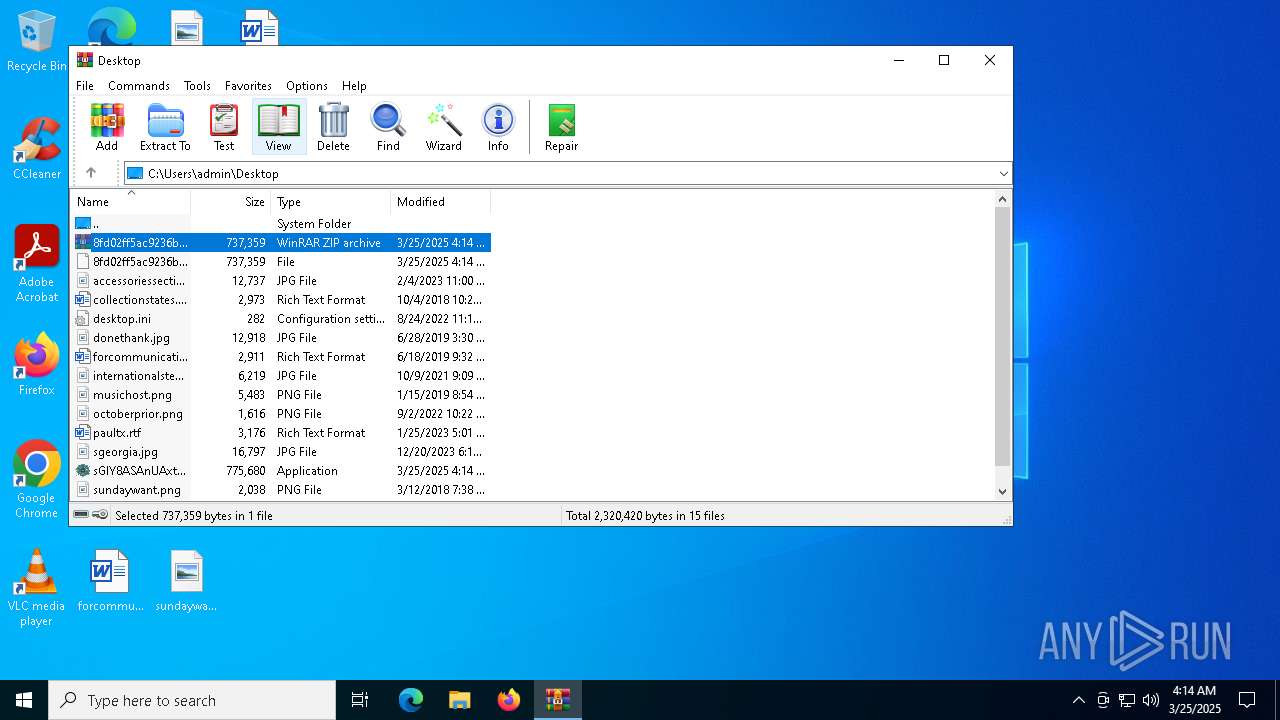
| 6476 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\8fd02ff5ac9236bdef59109bb1ac54c51887a00928aa6181cd01af1440f37079.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6652 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | sGIY8ASAnUAxtY3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 4294967295 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 7084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 360
Read events
5 343
Write events
17
Delete events
0
Modification events
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\8fd02ff5ac9236bdef59109bb1ac54c51887a00928aa6181cd01af1440f37079.zip | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (6476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
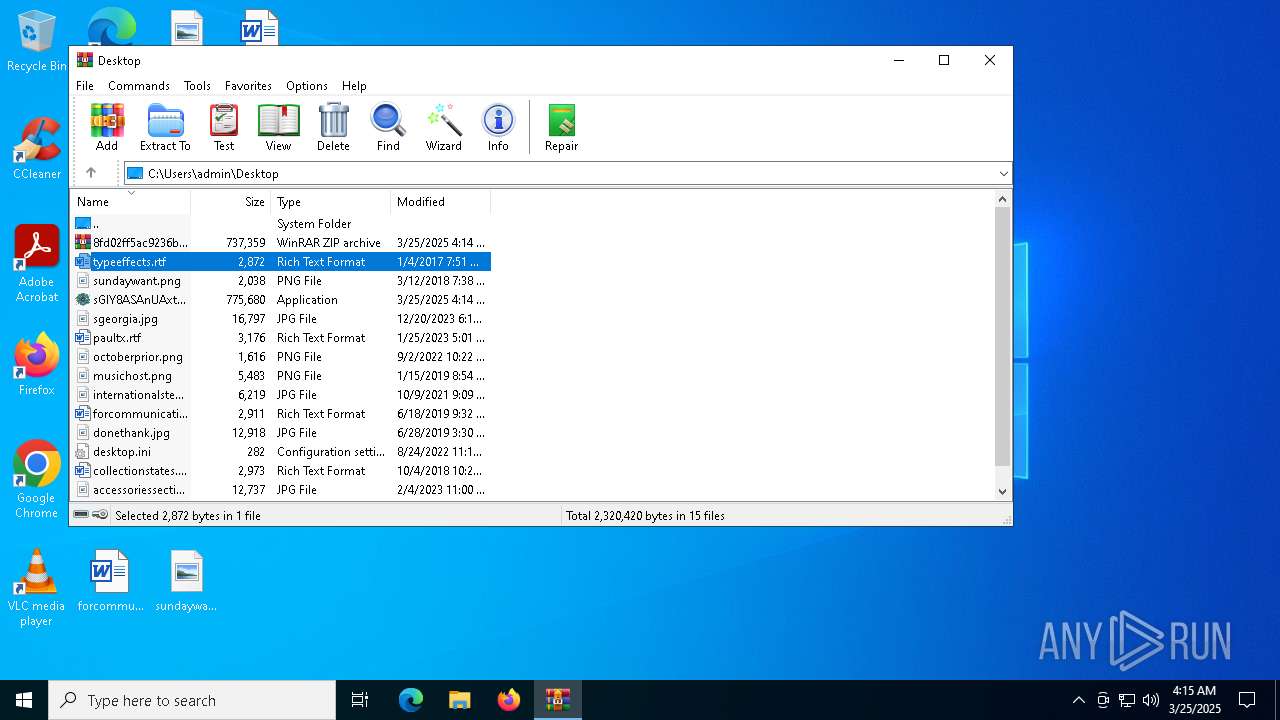
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1056 | sGIY8ASAnUAxtY3.exe | C:\Users\admin\AppData\Roaming\OcQFyyefoEr.exe | executable | |
MD5:63488C7230814CCE275D0F48187C0638 | SHA256:27AC9F0DBA8D7595BE661D32A76830765F142319ADB047A4BDF88842023E1EB7 | |||
| 1056 | sGIY8ASAnUAxtY3.exe | C:\Users\admin\AppData\Local\Temp\tmp1B2.tmp | xml | |
MD5:FA445C2CA6A02AF76C995AFCC5C61BE2 | SHA256:0E385CA7DFD9A276326F10F6E3D8EE0BD364CC3BAFAC97D26E9DF71A9F397234 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
22
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5960 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5256 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |