| File name: | PMT_1520528477_200054047_201112170000.xls |
| Full analysis: | https://app.any.run/tasks/e0dd8248-d3e6-46a7-a3a4-8c3fc7af5689 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 08:15:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Title: A, Subject: caP, Author: Atl, Last Saved By: Microsoft Office, Revision Number: 699, Name of Creating Application: Microsoft Excel, Total Editing Time: 09:05:00, Create Time/Date: Fri Aug 30 10:14:50 2019, Last Saved Time/Date: Tue Sep 10 11:38:59 2019, Number of Pages: 1, Number of Words: 4669, Number of Characters: 1838, Security: 0 |
| MD5: | 73E8D7D3213A4462EFC116E814904C69 |
| SHA1: | CD270E97760A1AC1BB06C03791EE3E54511173E6 |
| SHA256: | 8FBCC5E457C4E223148820CF4A1B6F760C819BF0BF0B5C61B92DCF8D5F8B5805 |
| SSDEEP: | 6144:F8mdr74qRlm5ibfVdLkUikJdGC1XcONnxusA2:F8UrDtdoUfPTfV |
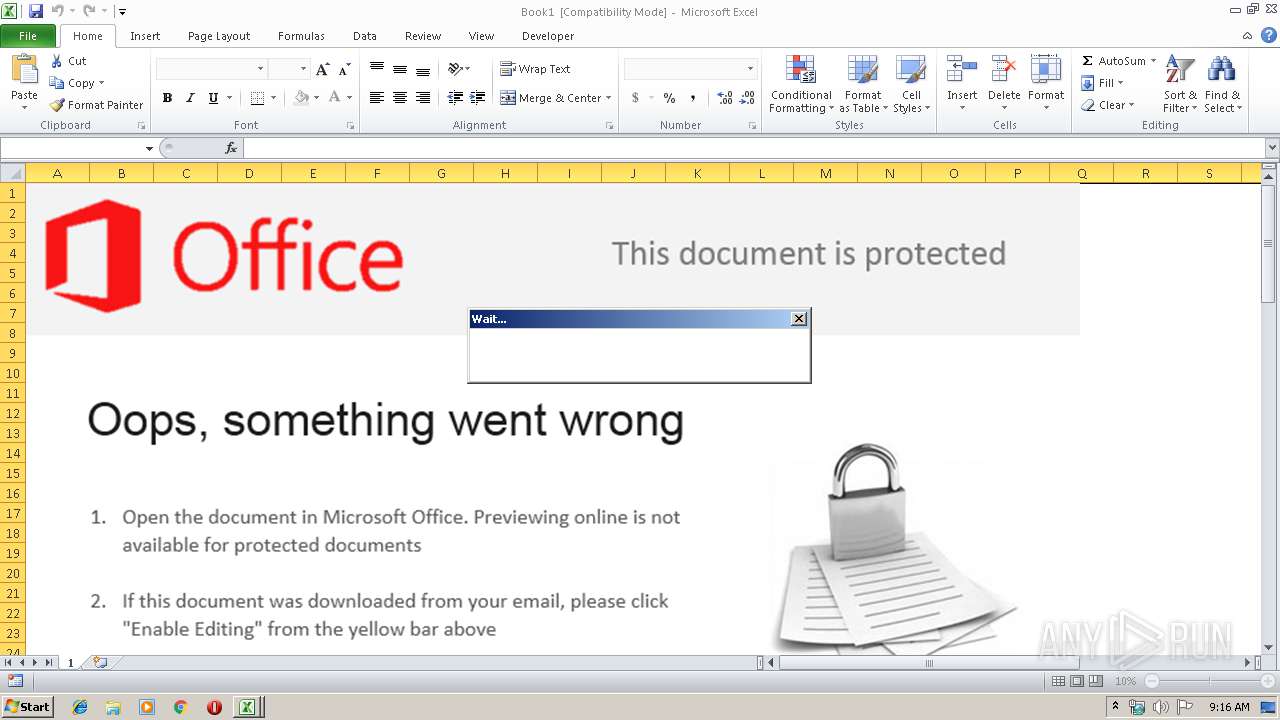
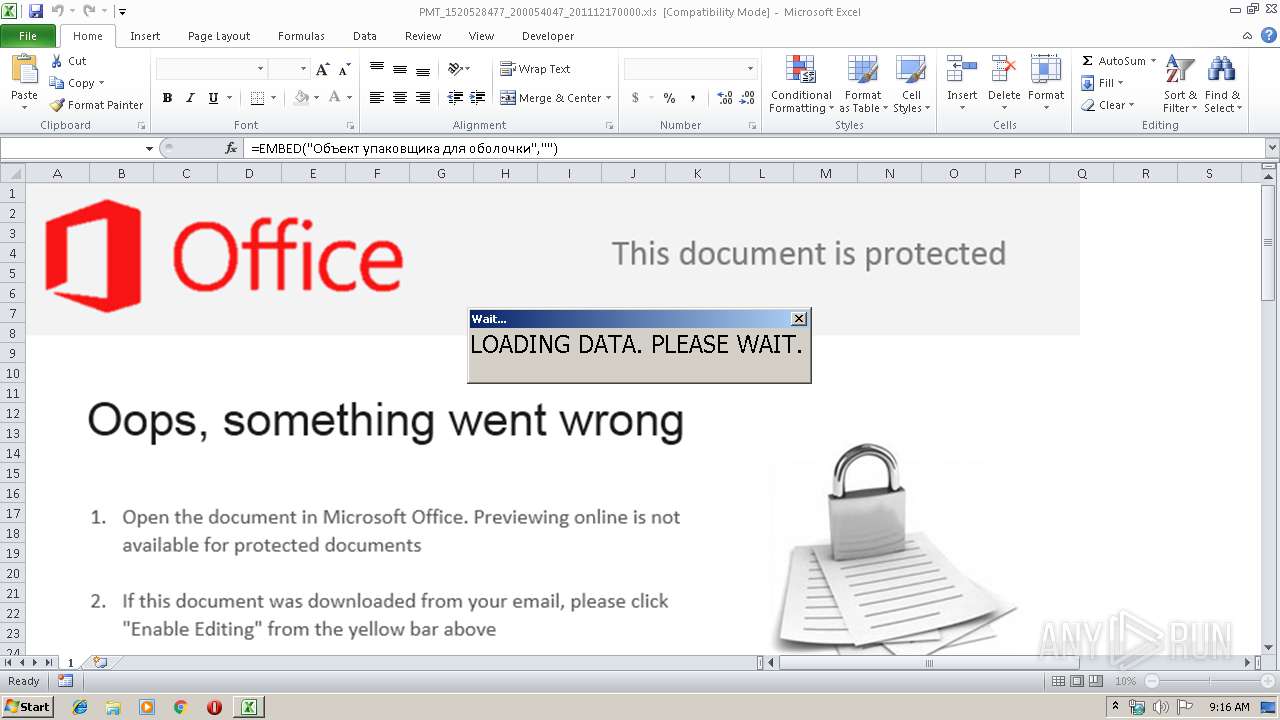
MALICIOUS
Loads dropped or rewritten executable
- EXCEL.EXE (PID: 3612)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 3612)
SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3612)
Creates files in the user directory
- EXCEL.EXE (PID: 3612)
Reads settings of System Certificates
- EXCEL.EXE (PID: 3612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 25 |
|---|---|
| CompObjUserType: | Microsoft Forms 2.0 Form |
| Title: | A |
| Subject: | caP |
| Author: | Atl |
| LastModifiedBy: | Microsoft Office |
| RevisionNumber: | 699 |
| Software: | Microsoft Excel |
| TotalEditTime: | 9.1 hours |
| CreateDate: | 2019:08:30 09:14:50 |
| ModifyDate: | 2019:09:10 10:38:59 |
| Pages: | 1 |
| Words: | 4669 |
| Characters: | 1838 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | - |
| Bytes: | 86400 |
| Lines: | 526 |
| Paragraphs: | 46 |
| AppVersion: | 11.9999 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | 1 |
| HeadingPairs: |
|
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3612 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
815
Read events
695
Write events
107
Delete events
13
Modification events
| (PID) Process: | (3612) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | j;$ |
Value: 6A3B24001C0E0000010000000000000000000000 | |||
| (PID) Process: | (3612) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3612) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3612) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 1C0E0000A062632C7968D50100000000 | |||
| (PID) Process: | (3612) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | j;$ |
Value: 6A3B24001C0E0000010000000000000000000000 | |||
| (PID) Process: | (3612) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3612) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3612) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3612) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3612) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\16A250 |
| Operation: | write | Name: | 16A250 |
Value: 040000001C0E00004000000043003A005C00550073006500720073005C00610064006D0069006E005C004400650073006B0074006F0070005C0050004D0054005F0031003500320030003500320038003400370037005F003200300030003000350034003000340037005F003200300031003100310032003100370030003000300030002E0078006C007300000000001700000043003A005C00550073006500720073005C00610064006D0069006E005C004400650073006B0074006F0070005C00010000000000000040B5BA2D7968D50150A2160050A2160000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
3
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3612 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9B6A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3612 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBA5BD.tmp | — | |
MD5:— | SHA256:— | |||
| 3612 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBA5BC.tmp | — | |
MD5:— | SHA256:— | |||
| 3612 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFD590875FC0E7BF7C.TMP | — | |
MD5:— | SHA256:— | |||
| 3612 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\36A61000 | — | |
MD5:— | SHA256:— | |||
| 3612 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFF6337BCFDD21AA52.TMP | — | |
MD5:— | SHA256:— | |||
| 3612 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~$13.xlsx | — | |
MD5:— | SHA256:— | |||
| 3612 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF3C9D3C34A4D4AD20.TMP | — | |
MD5:— | SHA256:— | |||
| 3612 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3612 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\13.xlsx.zip | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3612 | EXCEL.EXE | 95.216.147.100:443 | windows-update-02-en.com | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
windows-update-02-en.com |
| malicious |