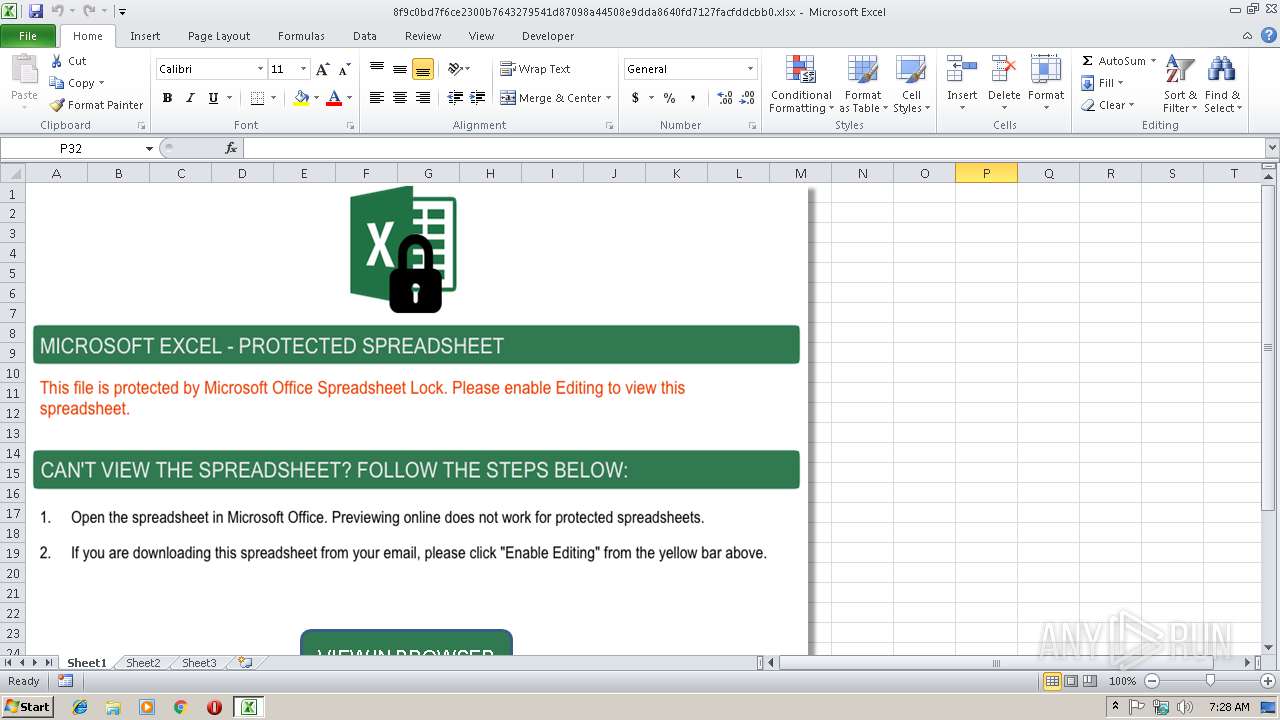
| File name: | 8f9c0bd7f6ce2300b7643279541d87098a44508e9dda8640fd7127facfddcbb0.xlsx |
| Full analysis: | https://app.any.run/tasks/8aba98eb-ad4f-48b7-81af-2775a68016a6 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 07:27:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 11EABE3F61399E1250E9A0043F493909 |
| SHA1: | 68F0596C8655001684E5644DA46E20FCB372C837 |
| SHA256: | 8F9C0BD7F6CE2300B7643279541D87098A44508E9DDA8640FD7127FACFDDCBB0 |
| SSDEEP: | 3072:yuSTkbFb15YByCEU2HHo0pVNZjcHyFRFunifMFFYMhnUJFyOKnIq2EsykT:5lFbDYrEUbkVNVcEFua+UJFpqu |
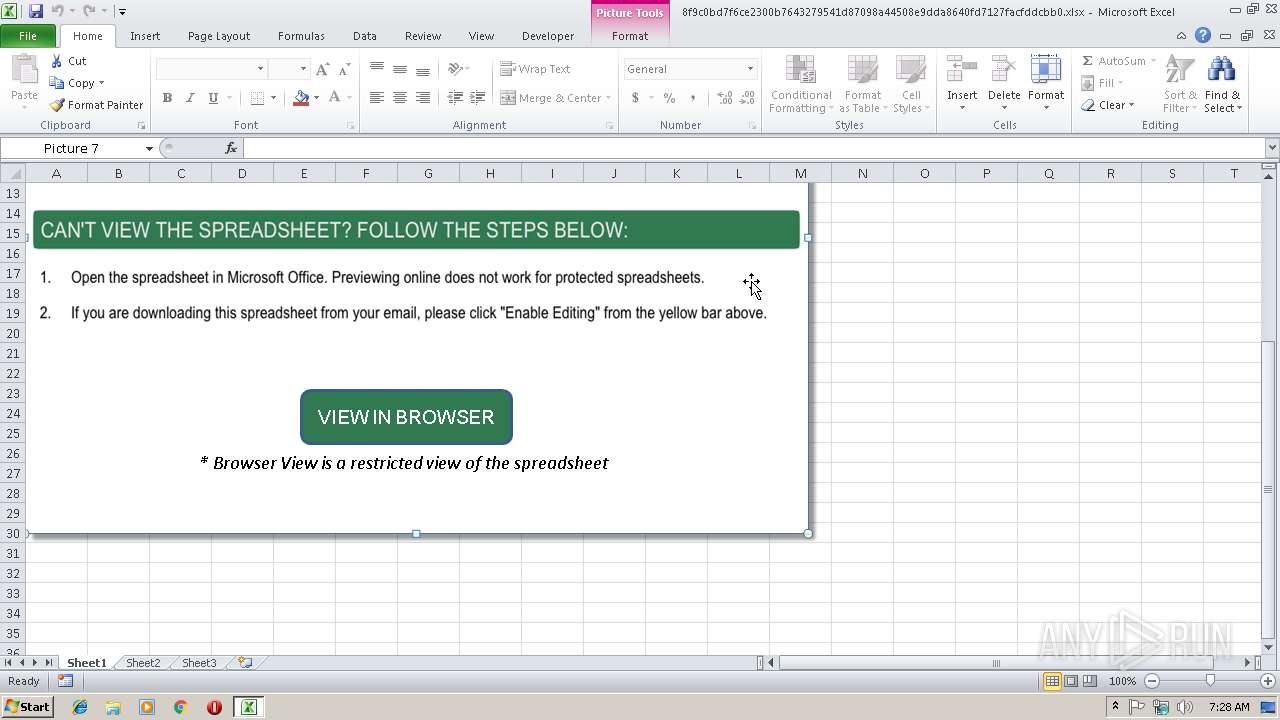
MALICIOUS
No malicious indicators.SUSPICIOUS
Unusual connect from Microsoft Office
- EXCEL.EXE (PID: 2728)
Reads internet explorer settings
- EXCEL.EXE (PID: 2728)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2728)
Reads internet explorer settings
- iexplore.exe (PID: 3564)
Reads Internet Cache Settings
- iexplore.exe (PID: 3564)
Creates files in the user directory
- EXCEL.EXE (PID: 2728)
- iexplore.exe (PID: 3564)
Changes internet zones settings
- iexplore.exe (PID: 3336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:01:31 15:10:18 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | docProps/ |
XML
| Application: | Microsoft Macintosh Excel |
|---|---|
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.03 |
| LastModifiedBy: | KB4 |
| CreateDate: | 2014:07:08 19:37:28Z |
| ModifyDate: | 2018:06:21 06:47:40Z |
XMP
| Creator: | brian |
|---|
Total processes
34
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2728 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3336 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3564 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3336 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 001
Read events
938
Write events
55
Delete events
8
Modification events
| (PID) Process: | (2728) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | ;2$ |
Value: 3B322400A80A0000010000000000000000000000 | |||
| (PID) Process: | (2728) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2728) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2728) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: A80A0000845E1C7337DAD40100000000 | |||
| (PID) Process: | (2728) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | ;2$ |
Value: 3B322400A80A0000010000000000000000000000 | |||
| (PID) Process: | (2728) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2728) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2728) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2728) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2728) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\198CD6 |
| Operation: | write | Name: | 198CD6 |
Value: 04000000A80A00006700000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0038006600390063003000620064003700660036006300650032003300300030006200370036003400330032003700390035003400310064003800370030003900380061003400340035003000380065003900640064006100380036003400300066006400370031003200370066006100630066006400640063006200620030002E0078006C0073007800000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000B037BB7437DAD401D68C1900D68C190000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
7
Text files
12
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR868B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3336 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2728 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFB371826116892484.TMP | — | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB433.tmp | — | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB434.tmp | — | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB444.tmp | — | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB445.tmp | — | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB512.tmp | — | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB513.tmp | — | |
MD5:— | SHA256:— | |||
| 3336 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF850A50DB59393B18.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
5
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
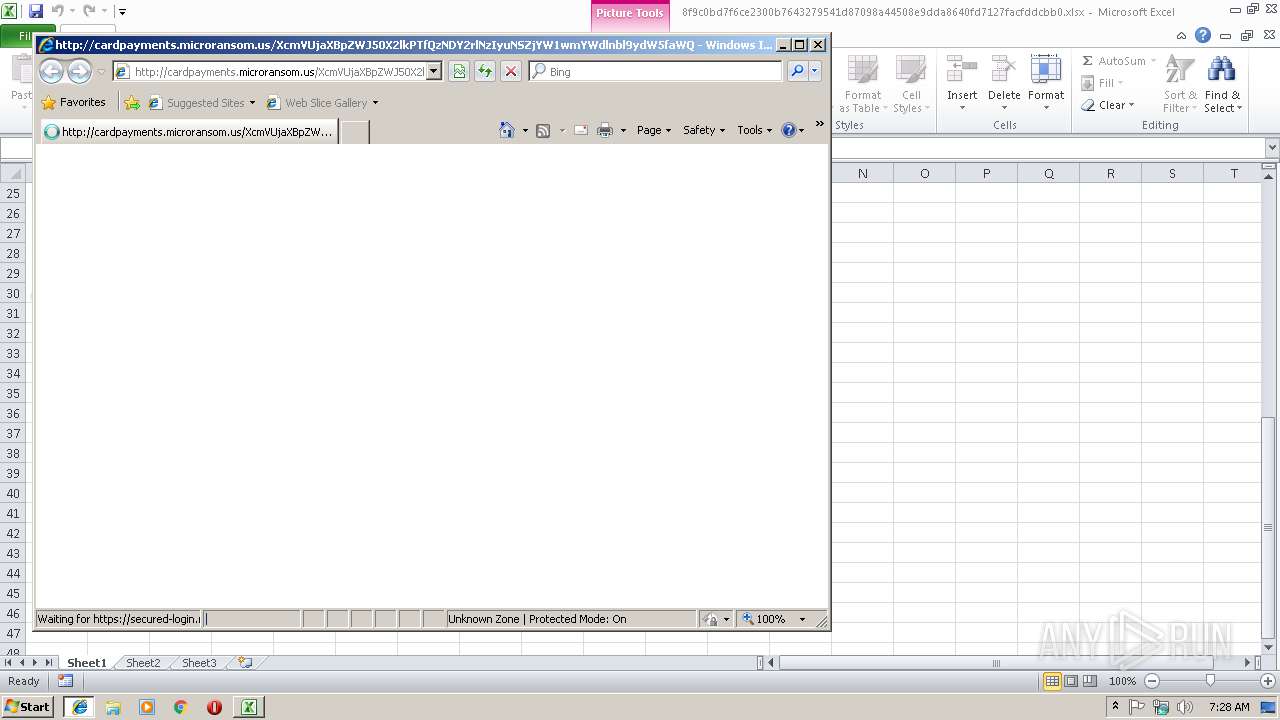
2728 | EXCEL.EXE | GET | 200 | 52.72.248.202:80 | http://cardpayments.microransom.us/XcmVKjaXBpZWZ50X2lkPTeQzNDY2QhNzIyjNSZjYW1wyYWclnbl9ydW5faWQ9MTg3mMjYxOCZhY3Rpb249YXR0YWNobWVudA== | US | — | — | suspicious |
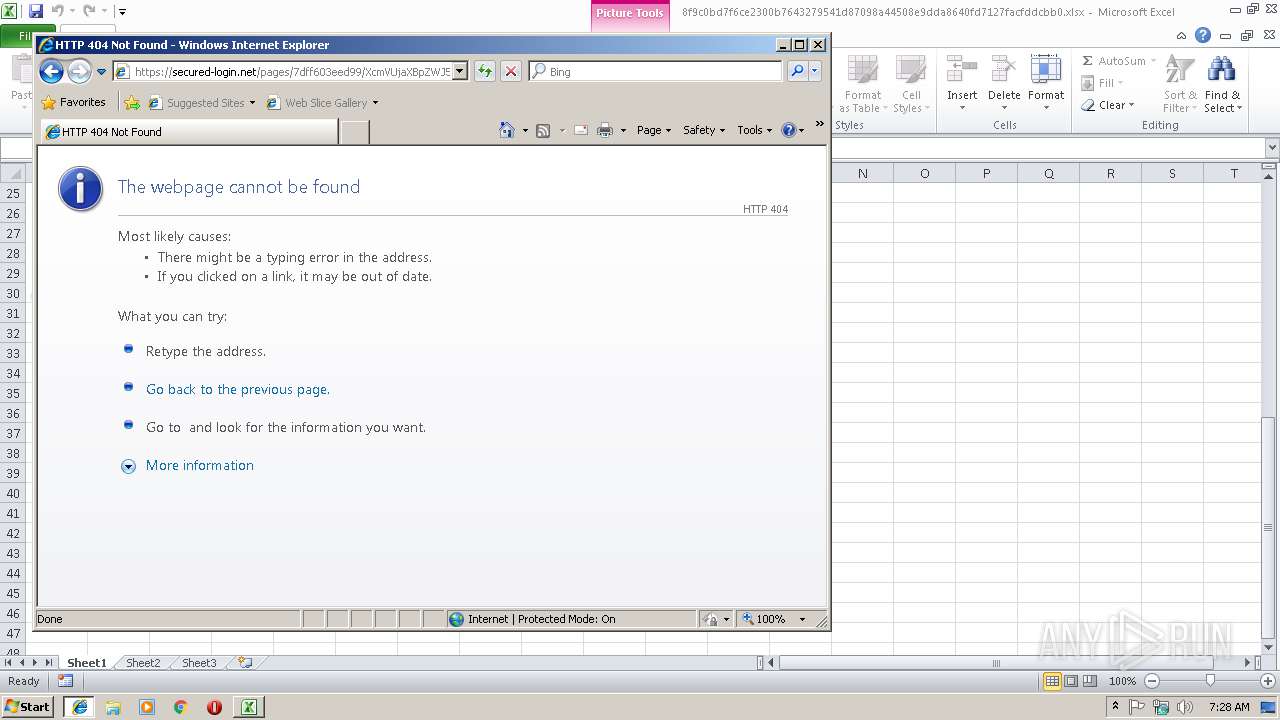
2728 | EXCEL.EXE | GET | 200 | 52.72.248.202:80 | http://cardpayments.microransom.us/XcmVUjaXBpZWJ50X2lkPTfQzNDY2rlNzIyuNSZjYW1wmYWdlnbl9ydW5faWQ9MTg3dMjYxOCZhY3Rpb249Y2xpY2smdXJsPWh0dHBzOi8vc2VjdXJlZC1sb2dpbi5uZXQvcGFnZXMvN2RmZjYwM2VlZDk5 | US | html | 334 b | suspicious |
3564 | iexplore.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3336 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3564 | iexplore.exe | GET | 200 | 52.222.146.58:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2728 | EXCEL.EXE | 52.72.248.202:80 | cardpayments.microransom.us | Amazon.com, Inc. | US | suspicious |
3336 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3564 | iexplore.exe | 52.222.146.58:80 | x.ss2.us | Amazon.com, Inc. | US | suspicious |
3564 | iexplore.exe | 54.164.242.137:443 | cardpayments.microransom.us | Amazon.com, Inc. | US | suspicious |
3564 | iexplore.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cardpayments.microransom.us |
| suspicious |
www.bing.com |
| whitelisted |
secured-login.net |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report