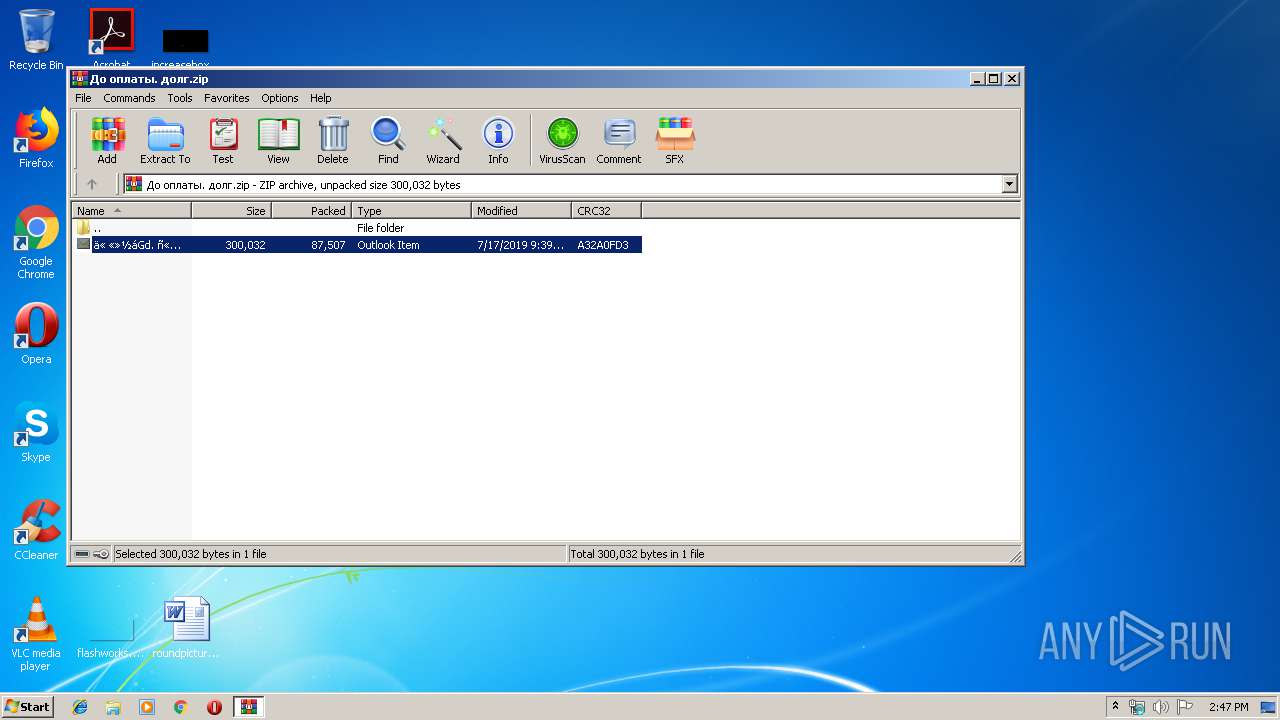
| File name: | До оплаты. долг.zip |
| Full analysis: | https://app.any.run/tasks/a70f3374-936f-4bb2-a315-4205e2470b57 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 13:46:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 31E46C8C515A11F6932E9A98A9FF732C |
| SHA1: | FA2EA04851466D729A849A700F05EE83FE26504F |
| SHA256: | 8F96028D7AB0073B153031A0ED585EB7B1FE75E7FB80260F128E8584785939A1 |
| SSDEEP: | 1536:T2PRAU6aH7VxatQ0vD8hibudW01EXpn+3lT0L+RxaQL56oXmd6fFlFLyoENRUV/w:T2JAU6OyQ0v/u3EXpn+Vokx0ge6fFlsh |
MALICIOUS
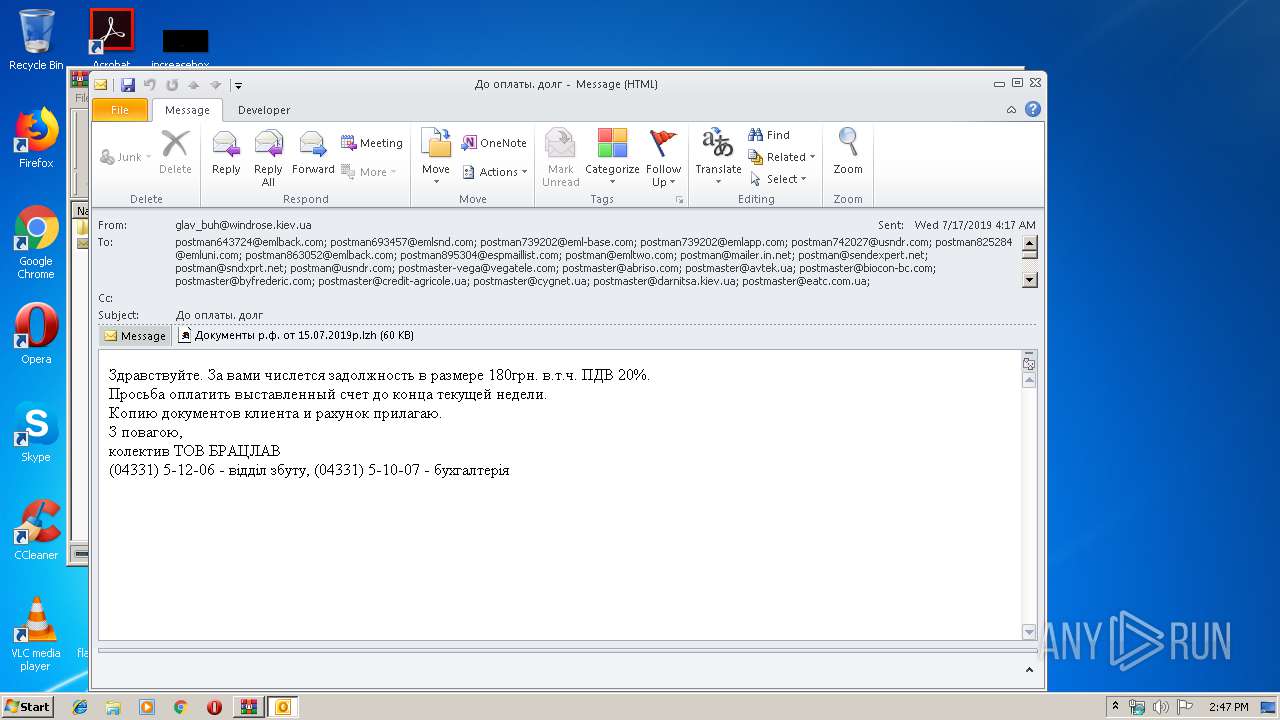
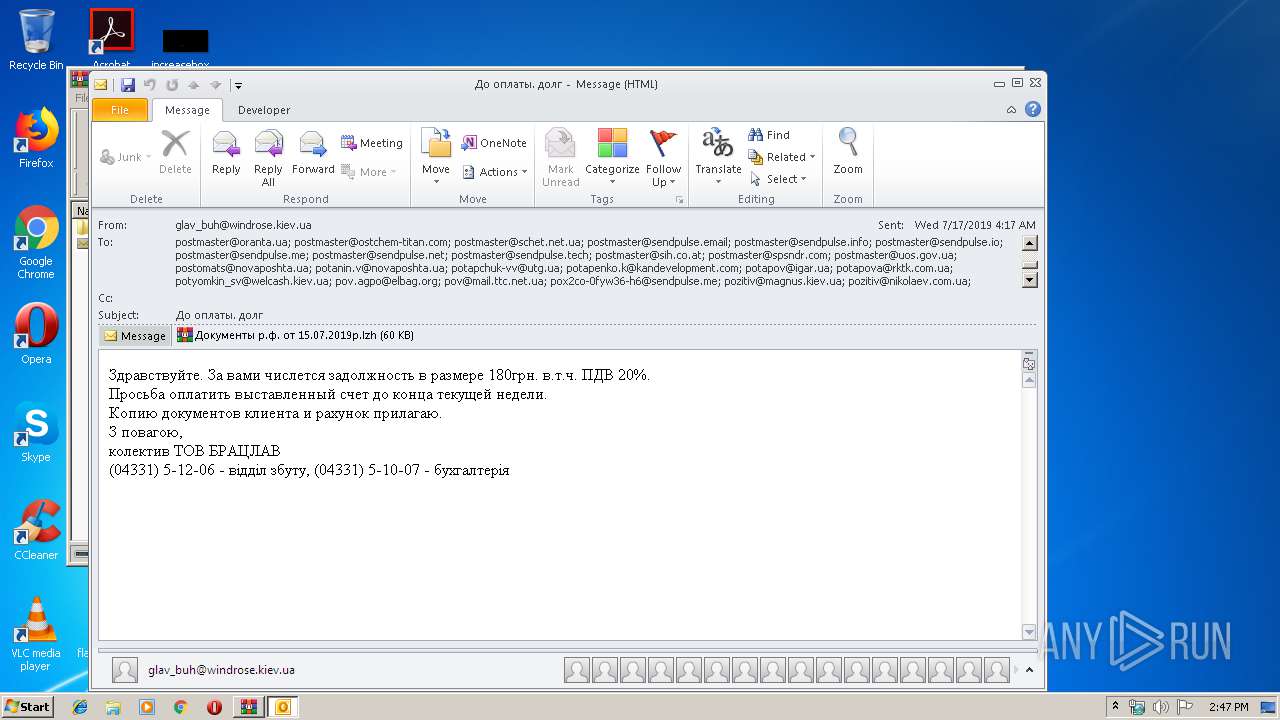
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3548)
Application was dropped or rewritten from another process
- 230659.exe (PID: 2616)
- 163453.exe (PID: 2596)
Downloads executable files from the Internet
- WScript.exe (PID: 2936)
- WScript.exe (PID: 3568)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3548)
- WScript.exe (PID: 2936)
- WScript.exe (PID: 3568)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3548)
Reads internet explorer settings
- OUTLOOK.EXE (PID: 3548)
Executed via COM
- DllHost.exe (PID: 2500)
Executable content was dropped or overwritten
- WScript.exe (PID: 2936)
- WScript.exe (PID: 3568)
- 163453.exe (PID: 2596)
Executes scripts
- WinRAR.exe (PID: 2940)
Starts Microsoft Office Application
- WinRAR.exe (PID: 2840)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3548)
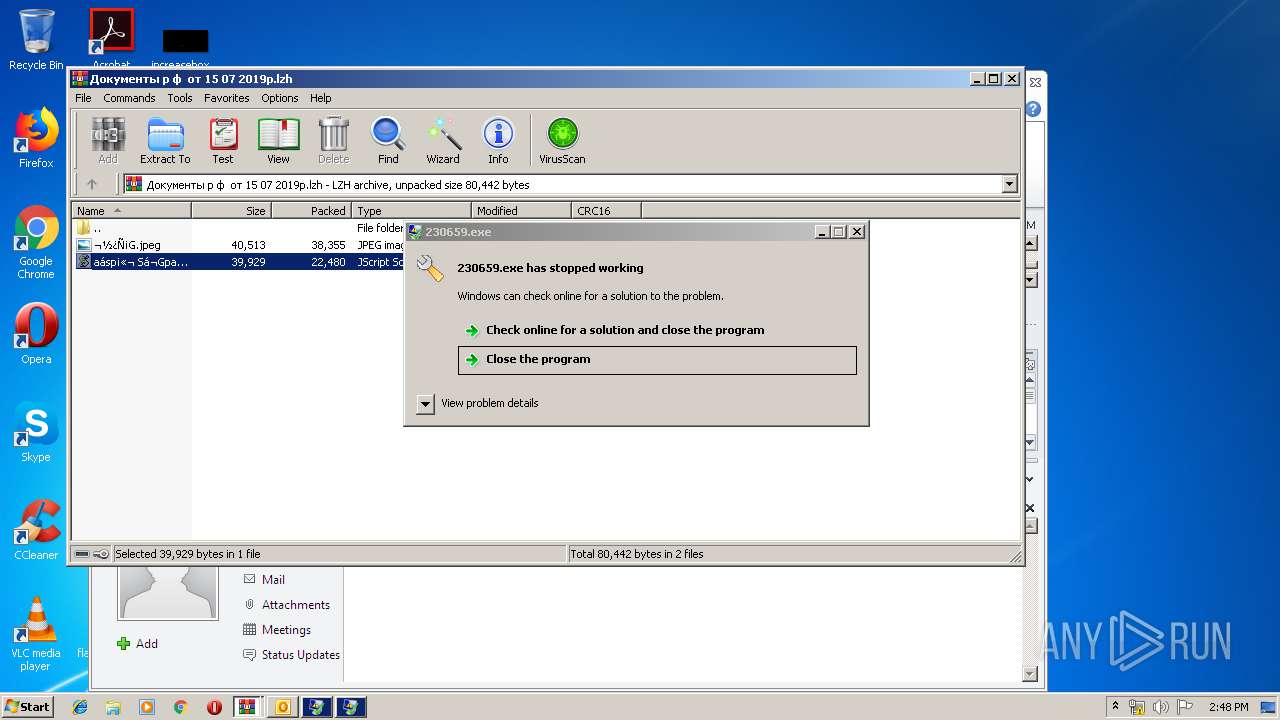
Application was crashed
- 163453.exe (PID: 2596)
- 230659.exe (PID: 2616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
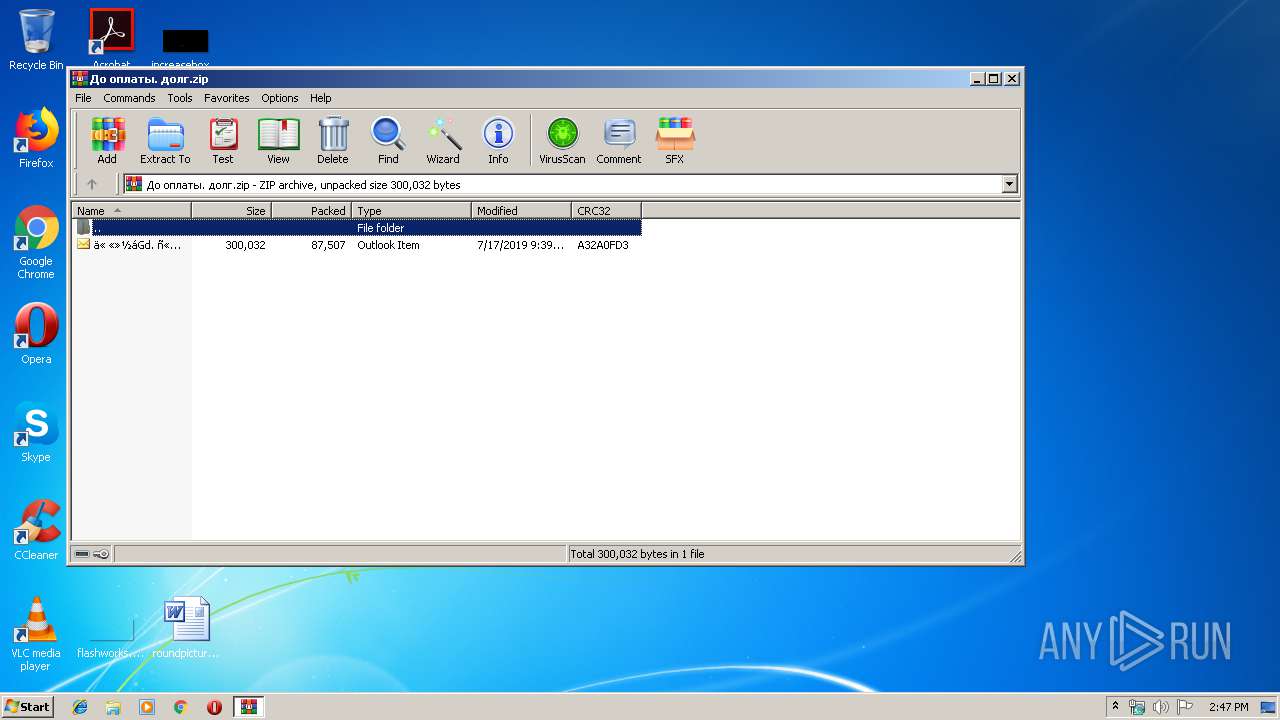
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:07:17 09:39:00 |
| ZipCRC: | 0xa32a0fd3 |
| ZipCompressedSize: | 87507 |
| ZipUncompressedSize: | 300032 |
| ZipFileName: | ?? ??????. ????.msg |
Total processes
44
Monitored processes
8
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2500 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2596 | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\163453.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\163453.exe | WScript.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2616 | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\230659.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\230659.exe | WScript.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
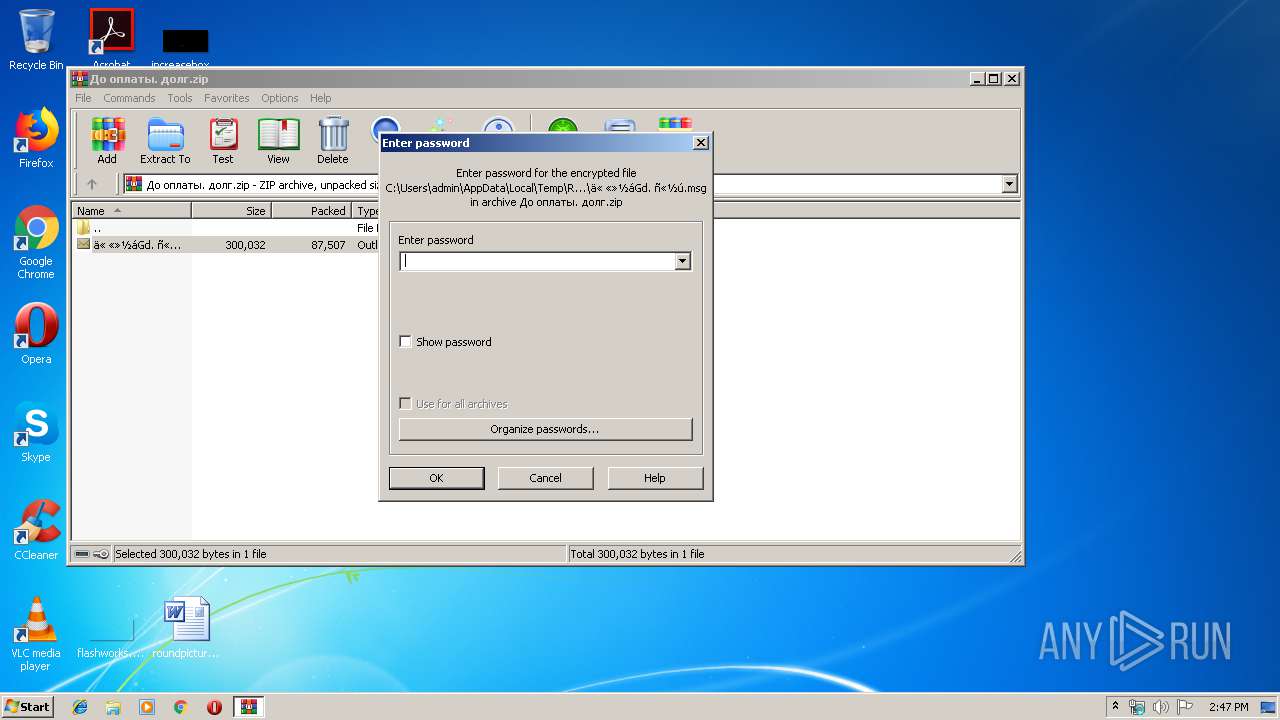
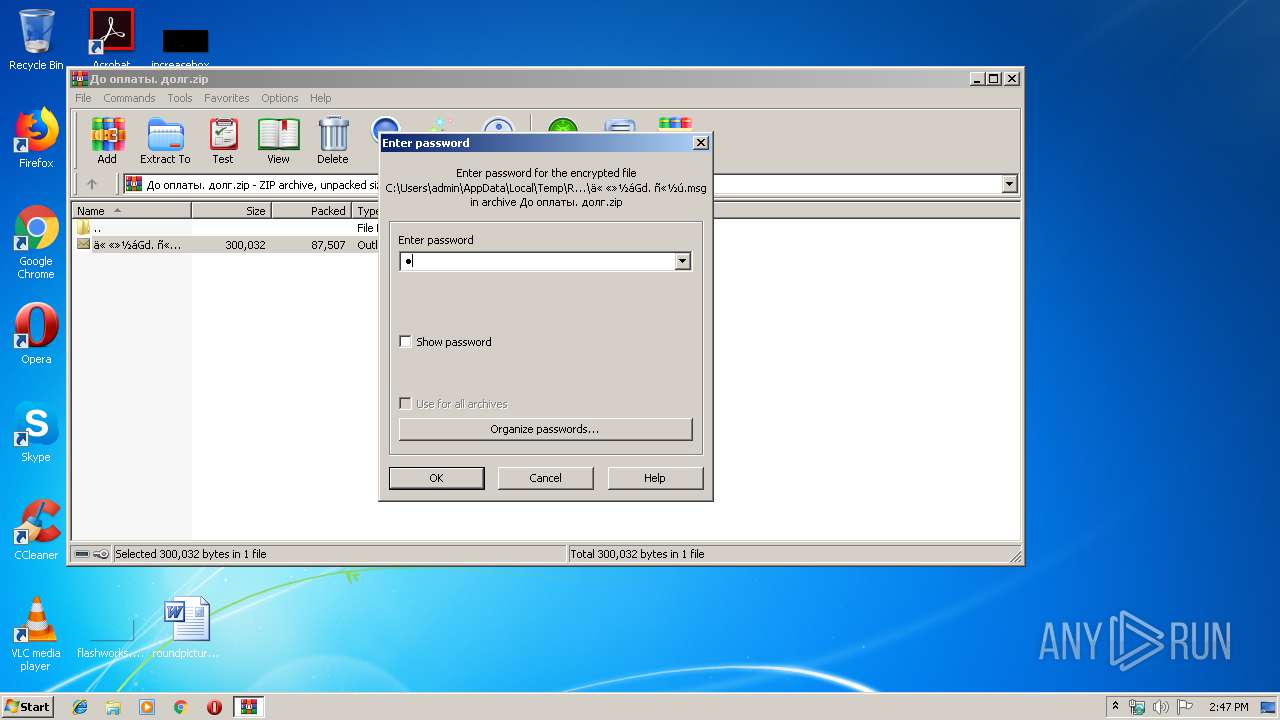
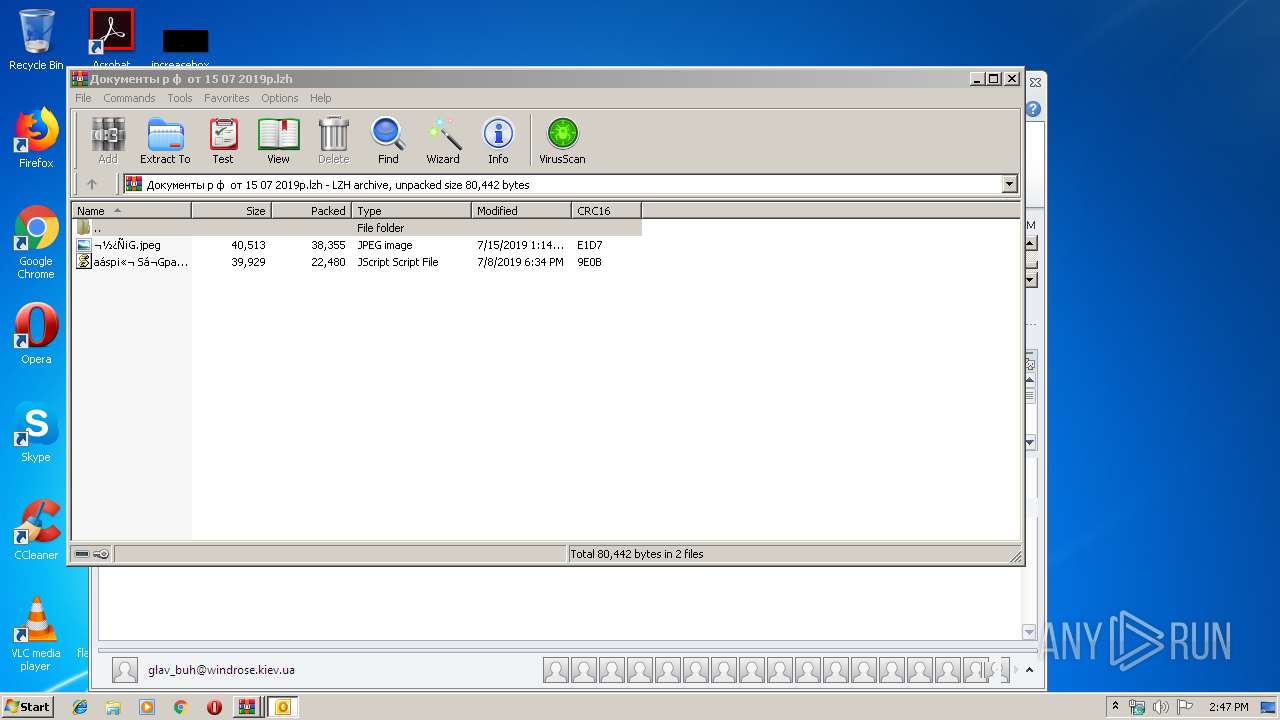
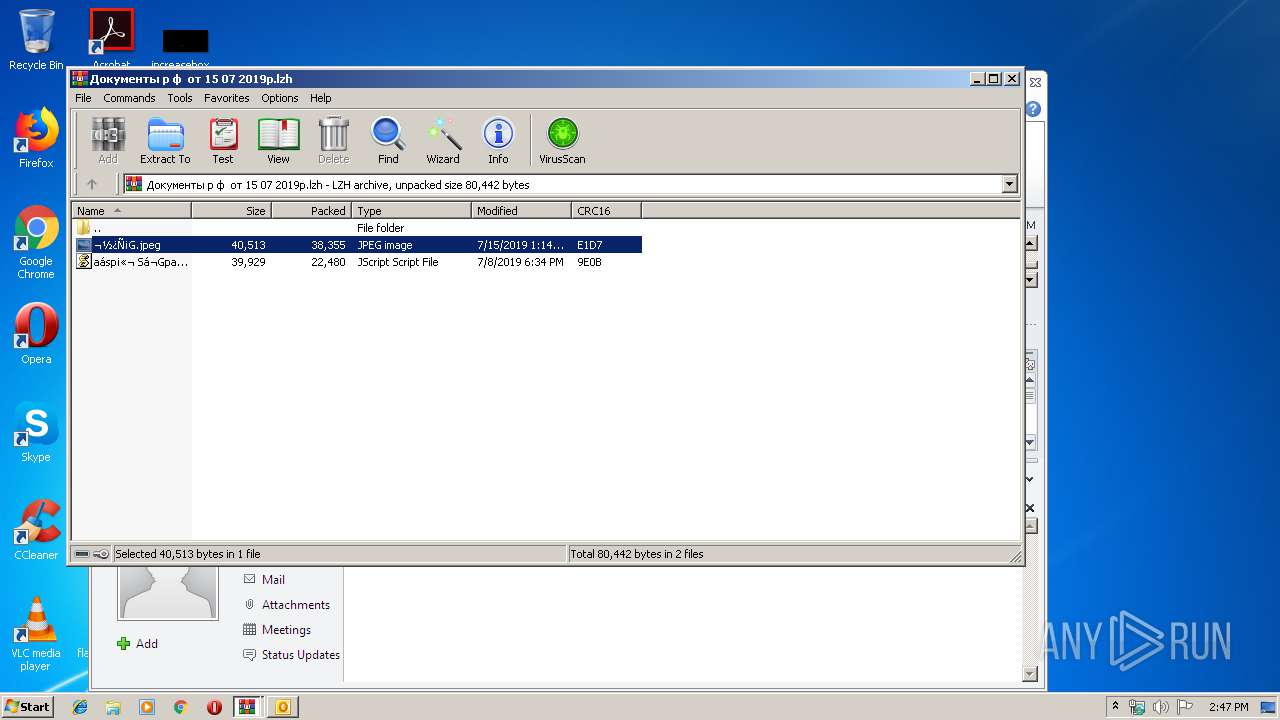
| 2840 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\До оплаты. долг.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
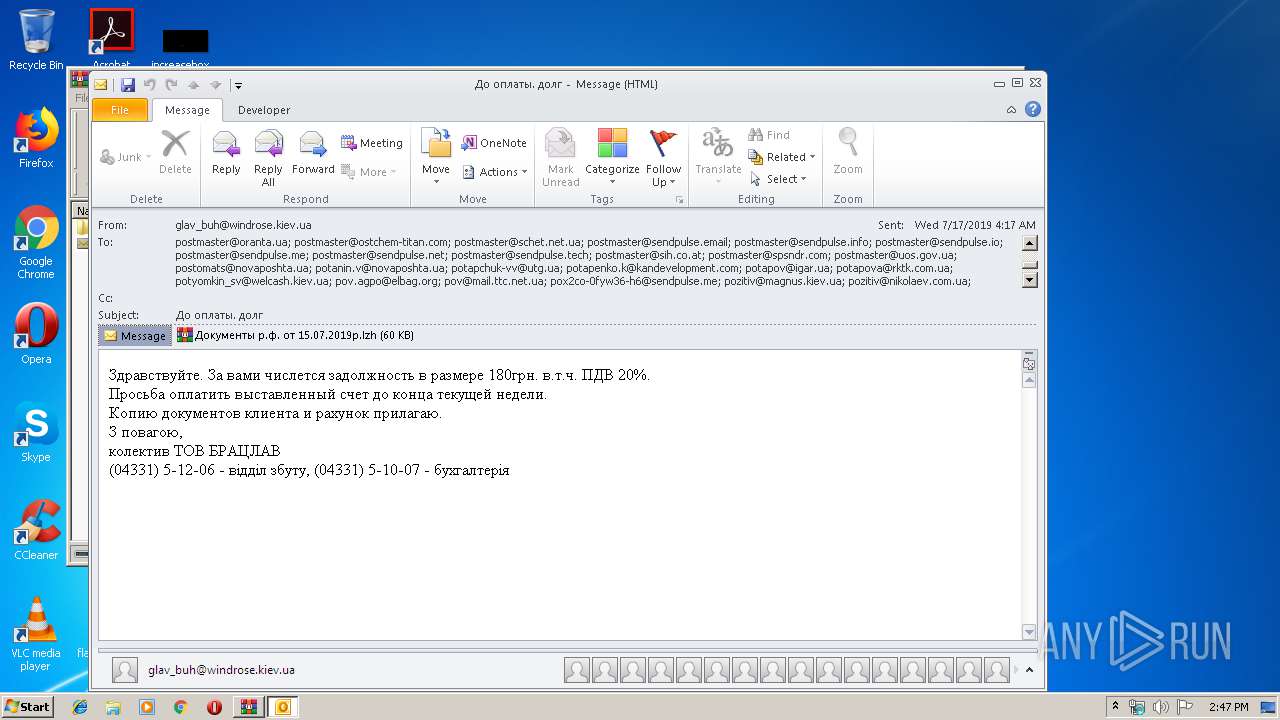
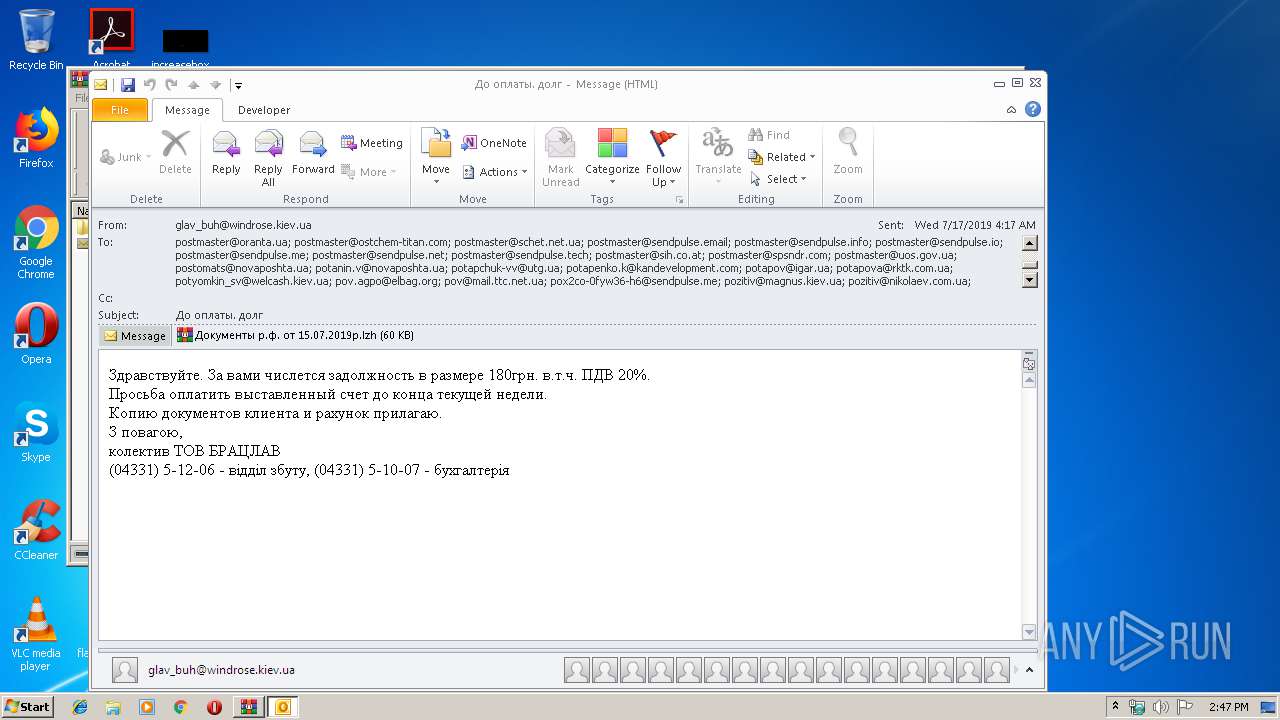
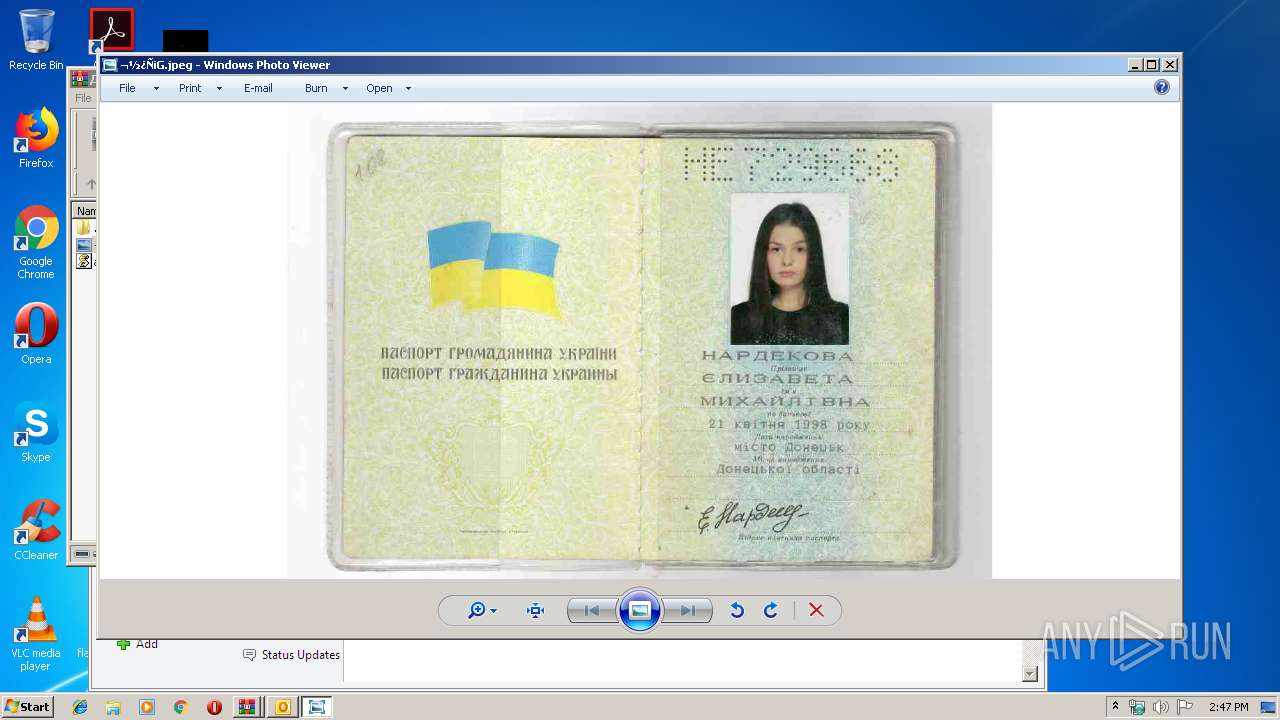
| 2936 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2940.28125\aásp¡«¬ Sá¬Gpaá n 127 «G 15.07.2019a..js" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
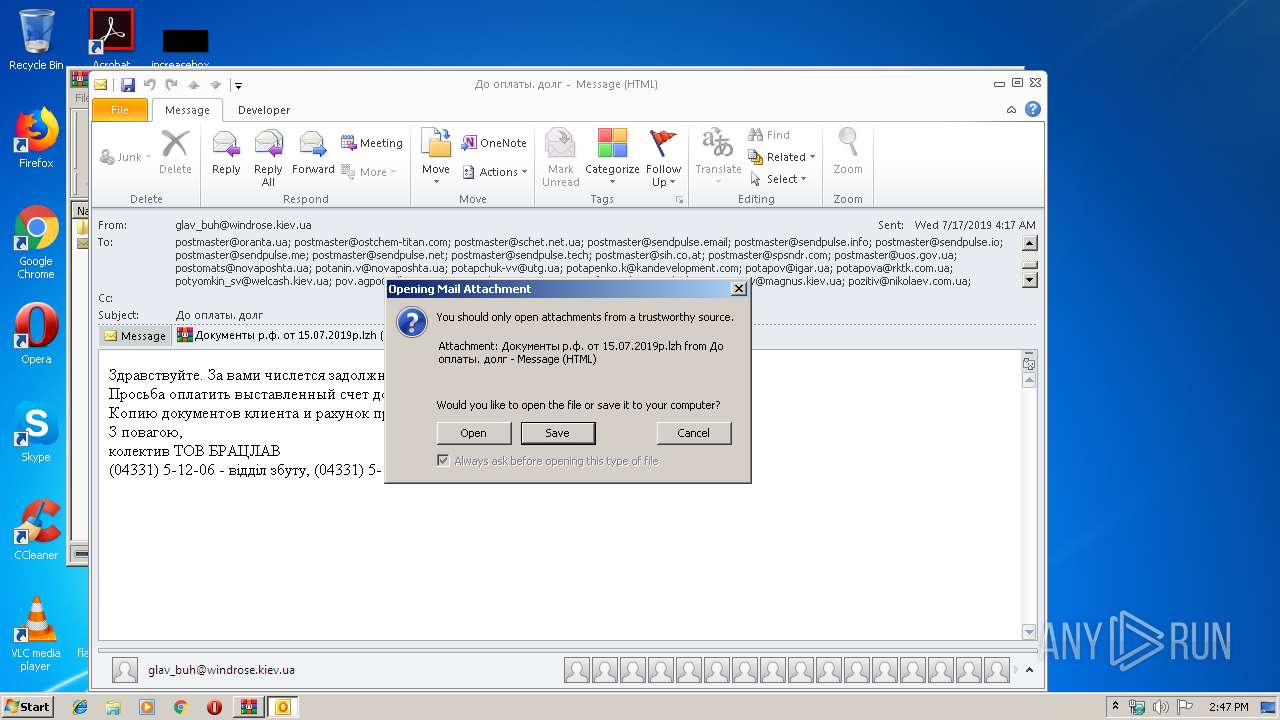
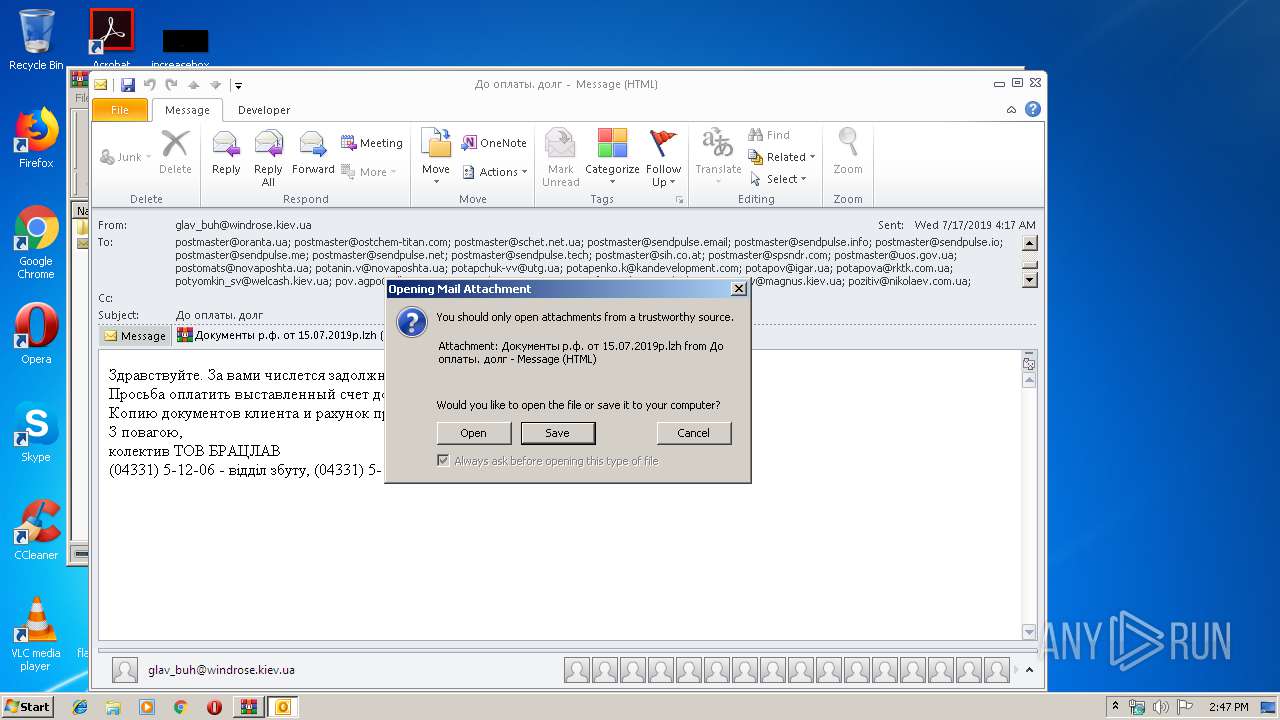
| 2940 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0FDEG9LU\Документы р ф от 15 07 2019р.lzh" | C:\Program Files\WinRAR\WinRAR.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3548 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIb2840.23834\ä« «»½áGd. ñ«½ú.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3568 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2940.28264\aásp¡«¬ Sá¬Gpaá n 127 «G 15.07.2019a..js" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
2 781
Read events
2 305
Write events
456
Delete events
20
Modification events
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\До оплаты. долг.zip | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214FA-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000004A257723A63CD501 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214EB-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000584C7E23A63CD501 | |||
Executable files
5
Suspicious files
0
Text files
29
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR3238.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0FDEG9LU\Документы р ф от 15 07 2019р (2).lzh\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2840.23834\ä« «»½áGd. ñ«½ú.msg | msg | |
MD5:— | SHA256:— | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0FDEG9LU\Документы р ф от 15 07 2019р (2).lzh | lzh | |
MD5:— | SHA256:— | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{75172CDF-28BF-41B1-9EB7-50E7C058CE10}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_6BEB8C1CC620A540AAFD9CDD7BB1CA8E.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0FDEG9LU\Документы р ф от 15 07 2019р.lzh | lzh | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2940.28264\aásp¡«¬ Sá¬Gpaá n 127 «G 15.07.2019a..js | text | |
MD5:— | SHA256:— | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_78B2FED0EB11D3498083B13322DB2DC7.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3568 | WScript.exe | GET | 200 | 47.254.69.179:80 | http://informatioshopname.ru/partiya/malashop.exe | US | executable | 268 Kb | malicious |
3548 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2936 | WScript.exe | GET | 200 | 47.254.69.179:80 | http://informatioshopname.ru/partiya/malashop.exe | US | executable | 268 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3568 | WScript.exe | 47.254.69.179:80 | informatioshopname.ru | Alibaba (China) Technology Co., Ltd. | US | suspicious |
2936 | WScript.exe | 47.254.69.179:80 | informatioshopname.ru | Alibaba (China) Technology Co., Ltd. | US | suspicious |
3548 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
informatioshopname.ru |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2936 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3568 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |