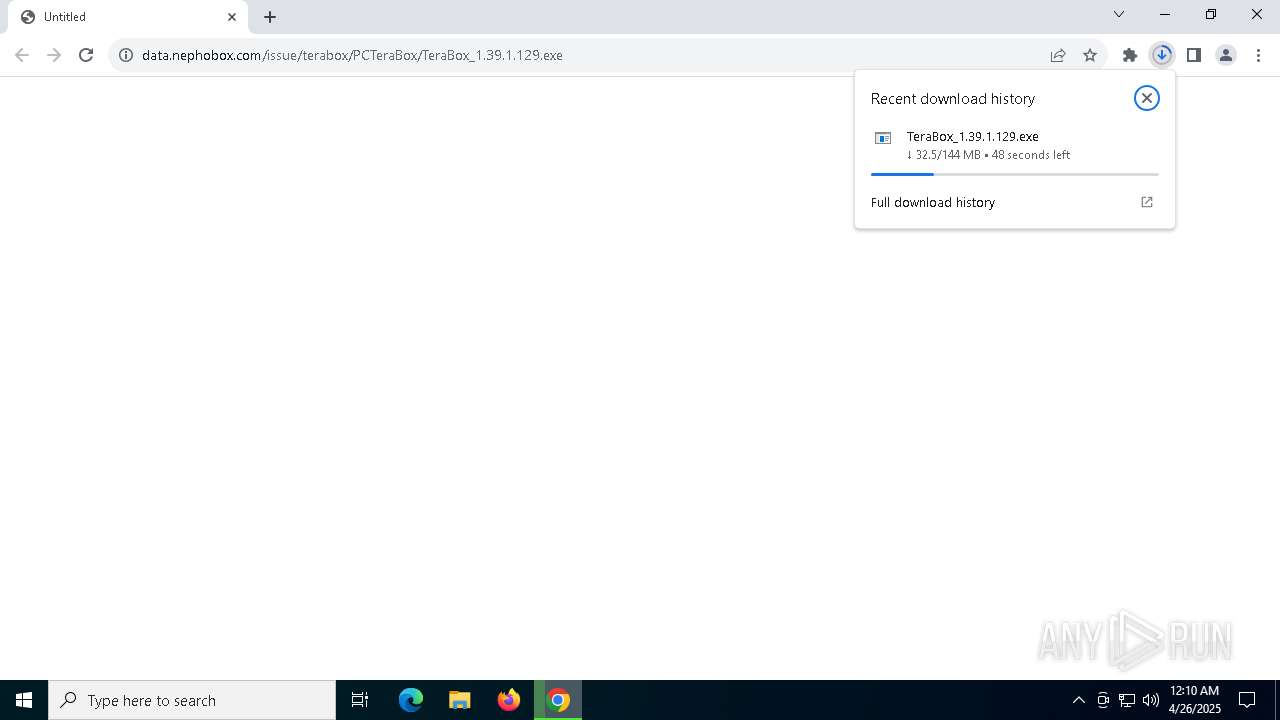
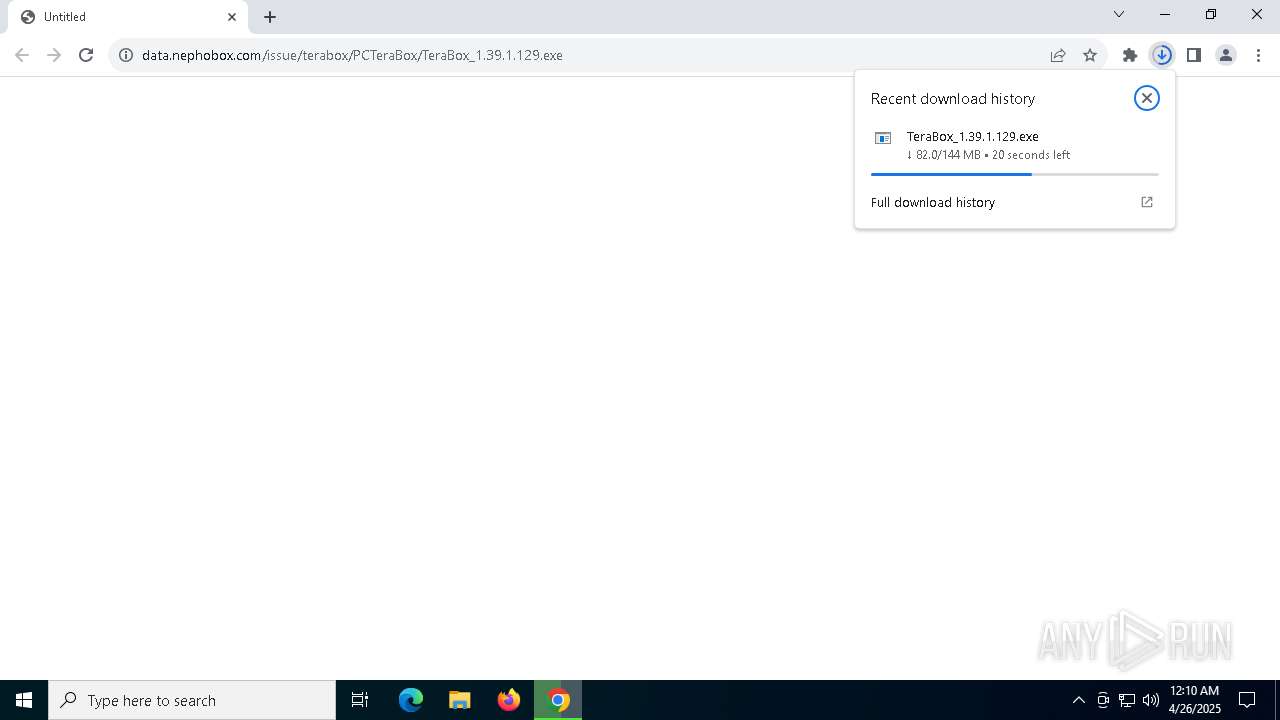
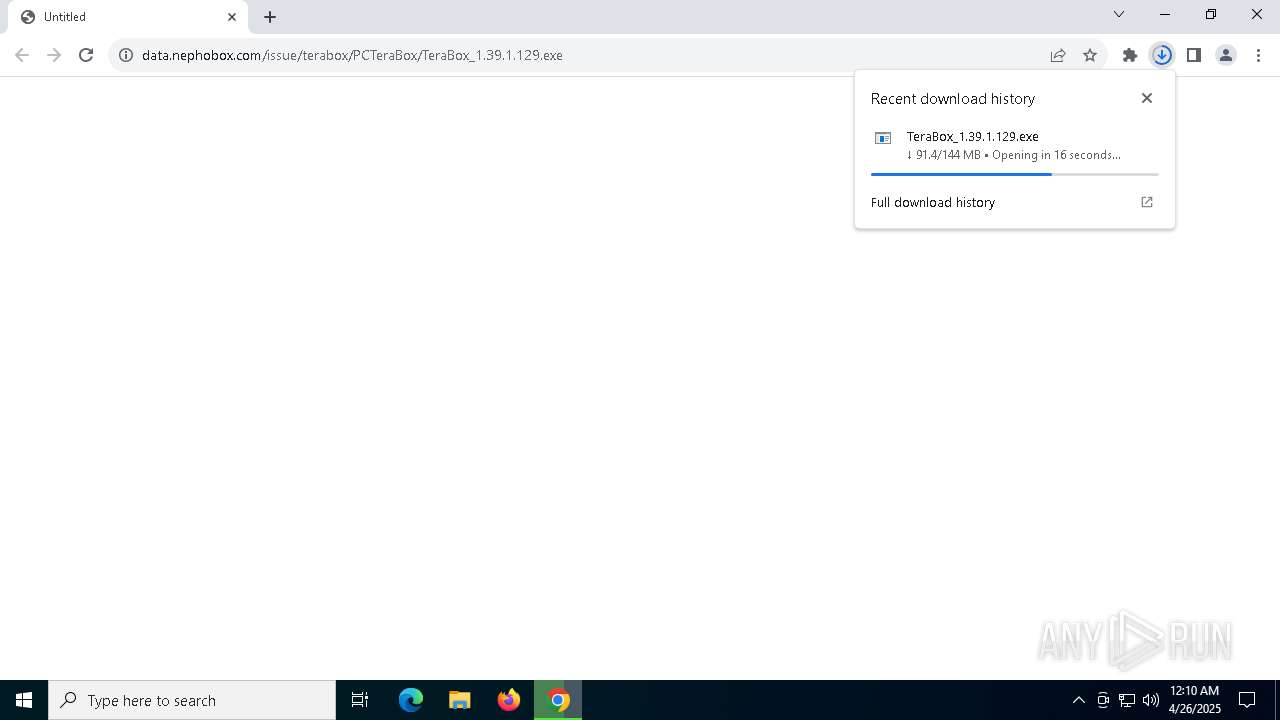
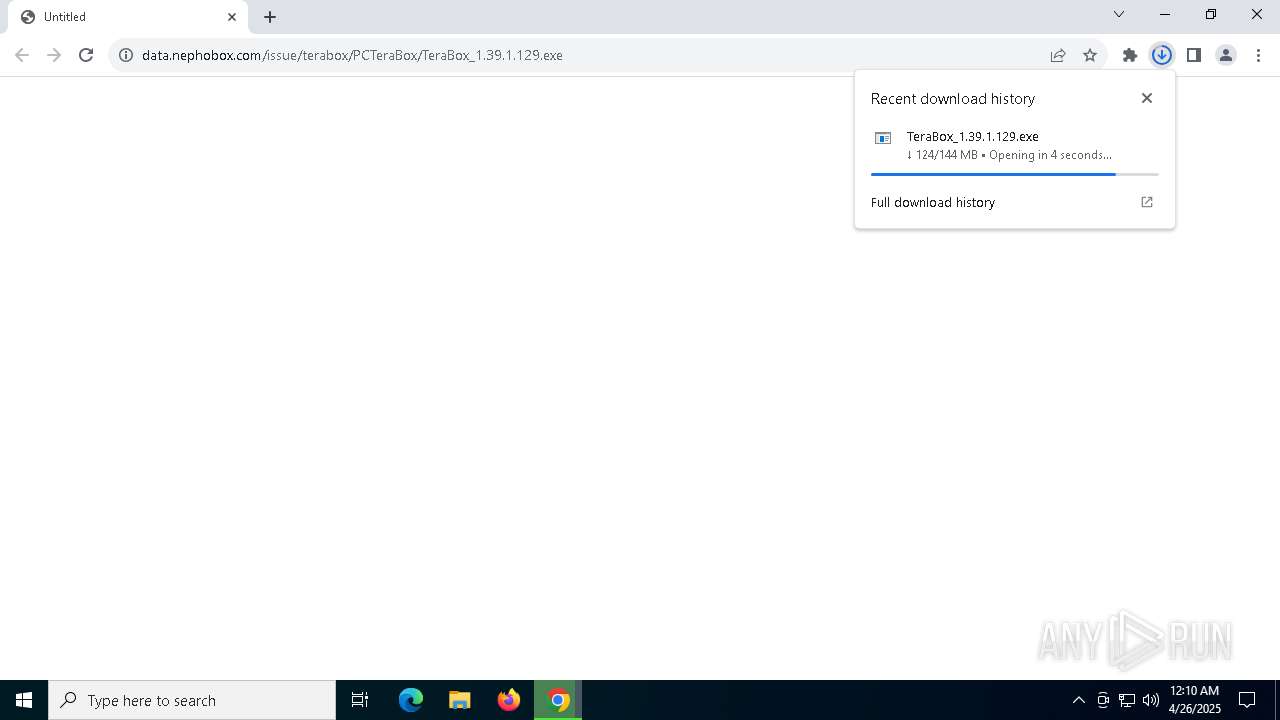
| URL: | https://data.nephobox.com/issue/terabox/PCTeraBox/TeraBox_1.39.1.129.exe |
| Full analysis: | https://app.any.run/tasks/21bce49f-b208-4c52-bbb5-729d31383b1e |
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2025, 00:10:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 24B2925EBD17D020EAD80B4075B4736E |
| SHA1: | D22B67979E9D9E58576C7EA45A7FF66ECAAAC037 |
| SHA256: | 8F8BB08A6B9F5E4442CB2F5D41BF1F5FB935C611D50EA6AAEBD2960BF91026BB |
| SSDEEP: | 3:N8ci/AMK82JAVVAX7+KdHgS6Nn:2cHMbKAVVAX7+KdHgS6Nn |
MALICIOUS
Changes the autorun value in the registry
- TeraBox.exe (PID: 5408)
Registers / Runs the DLL via REGSVR32.EXE
- TeraBox_1.39.1.129.exe (PID: 6676)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- TeraBox_1.39.1.129.exe (PID: 6676)
The process creates files with name similar to system file names
- TeraBox_1.39.1.129.exe (PID: 6676)
Executable content was dropped or overwritten
- TeraBox_1.39.1.129.exe (PID: 6676)
- TeraBoxUnite.exe (PID: 732)
Process drops legitimate windows executable
- TeraBox_1.39.1.129.exe (PID: 6676)
The process drops C-runtime libraries
- TeraBox_1.39.1.129.exe (PID: 6676)
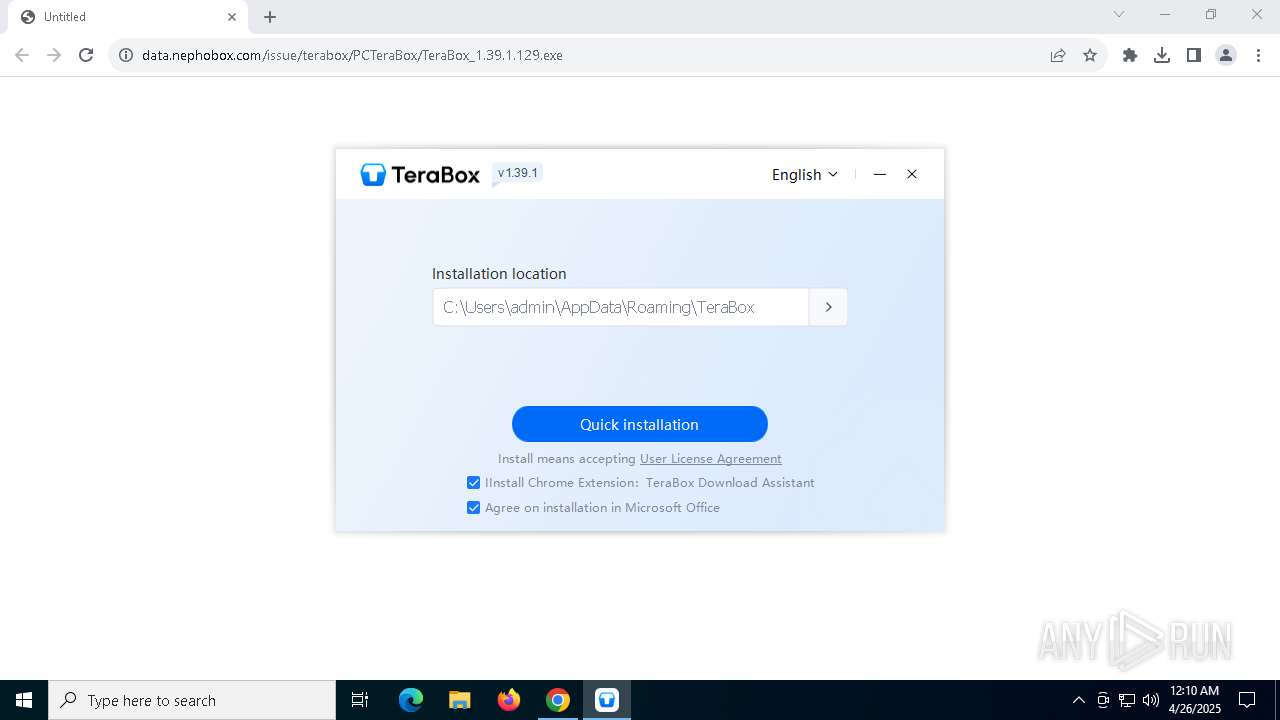
Creates a software uninstall entry
- TeraBox_1.39.1.129.exe (PID: 6676)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 5892)
- regsvr32.exe (PID: 5112)
- regsvr32.exe (PID: 672)
Reads security settings of Internet Explorer
- TeraBox_1.39.1.129.exe (PID: 6676)
- TeraBoxWebService.exe (PID: 5048)
- TeraBox.exe (PID: 4112)
Application launched itself
- TeraBoxUnite.exe (PID: 732)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 5072)
Checks supported languages
- TeraBox_1.39.1.129.exe (PID: 6676)
- TeraBox.exe (PID: 5408)
- TeraBoxWebService.exe (PID: 7928)
- YunUtilityService.exe (PID: 5344)
- TeraBoxWebService.exe (PID: 5048)
- TeraBox.exe (PID: 4112)
- TeraBoxUnite.exe (PID: 732)
- TeraBoxUnite.exe (PID: 5020)
- TeraBoxUnite.exe (PID: 7984)
- TeraBoxUnite.exe (PID: 1272)
- TeraBoxUnite.exe (PID: 7512)
- TeraBoxUnite.exe (PID: 7524)
Application launched itself
- chrome.exe (PID: 5072)
Reads the computer name
- TeraBox_1.39.1.129.exe (PID: 6676)
- TeraBox.exe (PID: 5408)
- YunUtilityService.exe (PID: 5344)
- TeraBoxWebService.exe (PID: 5048)
- TeraBox.exe (PID: 4112)
- TeraBoxUnite.exe (PID: 732)
- TeraBoxUnite.exe (PID: 7984)
- TeraBoxUnite.exe (PID: 5020)
Creates files or folders in the user directory
- TeraBox_1.39.1.129.exe (PID: 6676)
- TeraBox.exe (PID: 5408)
- TeraBox.exe (PID: 4112)
- TeraBoxWebService.exe (PID: 5048)
- TeraBoxUnite.exe (PID: 732)
The sample compiled with chinese language support
- TeraBox_1.39.1.129.exe (PID: 6676)
Create files in a temporary directory
- TeraBox_1.39.1.129.exe (PID: 6676)
- TeraBoxUnite.exe (PID: 732)
- TeraBoxUnite.exe (PID: 7984)
Reads the software policy settings
- slui.exe (PID: 7720)
- TeraBox.exe (PID: 4112)
- TeraBoxUnite.exe (PID: 732)
The sample compiled with english language support
- TeraBox_1.39.1.129.exe (PID: 6676)
Checks proxy server information
- TeraBox_1.39.1.129.exe (PID: 6676)
- TeraBoxWebService.exe (PID: 5048)
- TeraBox.exe (PID: 4112)
- TeraBoxUnite.exe (PID: 732)
Reads the machine GUID from the registry
- TeraBox.exe (PID: 4112)
- TeraBoxUnite.exe (PID: 732)
Process checks computer location settings
- TeraBoxUnite.exe (PID: 1272)
- TeraBoxUnite.exe (PID: 732)
- TeraBoxUnite.exe (PID: 7524)
- TeraBoxUnite.exe (PID: 7512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
171
Monitored processes
32
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "/s" "C:\Users\admin\AppData\Roaming\TeraBox\YunShellExt64.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxUnite.exe | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxUnite.exe | TeraBox.exe | ||||||||||||
User: admin Company: Flextech Integrity Level: MEDIUM Description: TeraBoxUnite Version: 1.39.1.129 Modules
| |||||||||||||||
| 1272 | "C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxUnite.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Local\Temp\TeraBox\cache" --app-path="C:\Users\admin\AppData\Roaming\TeraBox\resources\app.asar" --no-sandbox --no-zygote --node-integration-in-worker --first-renderer-process --no-sandbox --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=3008 --field-trial-handle=1520,i,3631426107065592080,6282538297084425161,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxUnite.exe | — | TeraBoxUnite.exe | |||||||||||
User: admin Company: Flextech Integrity Level: MEDIUM Description: TeraBoxUnite Version: 1.39.1.129 Modules
| |||||||||||||||
| 4112 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe | C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe | TeraBox_1.39.1.129.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Version: 1.39.1.129 Modules
| |||||||||||||||
| 5020 | "C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxUnite.exe" --type=gpu-process --no-sandbox --user-data-dir="C:\Users\admin\AppData\Roaming\TeraBox" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1784 --field-trial-handle=1520,i,3631426107065592080,6282538297084425161,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxUnite.exe | — | TeraBoxUnite.exe | |||||||||||
User: admin Company: Flextech Integrity Level: MEDIUM Description: TeraBoxUnite Version: 1.39.1.129 Modules
| |||||||||||||||
| 5048 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxWebService.exe | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxWebService.exe | TeraBox_1.39.1.129.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: TeraBoxWebService Version: 1.37.0.6 Modules
| |||||||||||||||
| 5072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://data.nephobox.com/issue/terabox/PCTeraBox/TeraBox_1.39.1.129.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5112 | "/s" "C:\Users\admin\AppData\Roaming\TeraBox\YunOfficeAddin64.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5344 | "C:\Users\admin\AppData\Roaming\TeraBox\YunUtilityService.exe" --install | C:\Users\admin\AppData\Roaming\TeraBox\YunUtilityService.exe | — | TeraBox_1.39.1.129.exe | |||||||||||
User: admin Company: Flextech Inc. Integrity Level: HIGH Description: TeraBox Service Used to Quickly Apply For Disk Space Exit code: 0 Version: 1.37.0.6 Modules
| |||||||||||||||
| 5384 | "C:\Users\admin\Downloads\TeraBox_1.39.1.129.exe" | C:\Users\admin\Downloads\TeraBox_1.39.1.129.exe | — | chrome.exe | |||||||||||
User: admin Company: Flextech Integrity Level: MEDIUM Description: TeraBox Installer Exit code: 3221226540 Version: 1.39.1.129 Modules
| |||||||||||||||
Total events
19 173
Read events
19 078
Write events
76
Delete events
19
Modification events
| (PID) Process: | (5072) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5072) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5072) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5072) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5072) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7844) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000001D9E87AC3FB6DB01 | |||
| (PID) Process: | (6676) TeraBox_1.39.1.129.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TeraBox |
| Operation: | write | Name: | Language |
Value: 1033 | |||
| (PID) Process: | (6676) TeraBox_1.39.1.129.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\TeraBox |
| Operation: | write | Name: | Language |
Value: 1033 | |||
| (PID) Process: | (5072) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (5072) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
Executable files
85
Suspicious files
227
Text files
55
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c3a0.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c3a0.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c3af.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c3a0.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c3af.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
816
DNS requests
43
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2088 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2088 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
7256 | chrome.exe | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5072 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7256 | chrome.exe | 98.98.225.244:443 | data.nephobox.com | — | US | unknown |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7256 | chrome.exe | 104.18.49.105:443 | issuepcdn.freeterabox.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
data.nephobox.com |
| unknown |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
issuepcdn.freeterabox.com |
| unknown |
www.google.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |
732 | TeraBoxUnite.exe | Misc activity | ET FILE_SHARING Observed File Sharing Domain (terabox .com in TLS SNI) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING DNS Query to File Sharing Domain (terabox .com) |