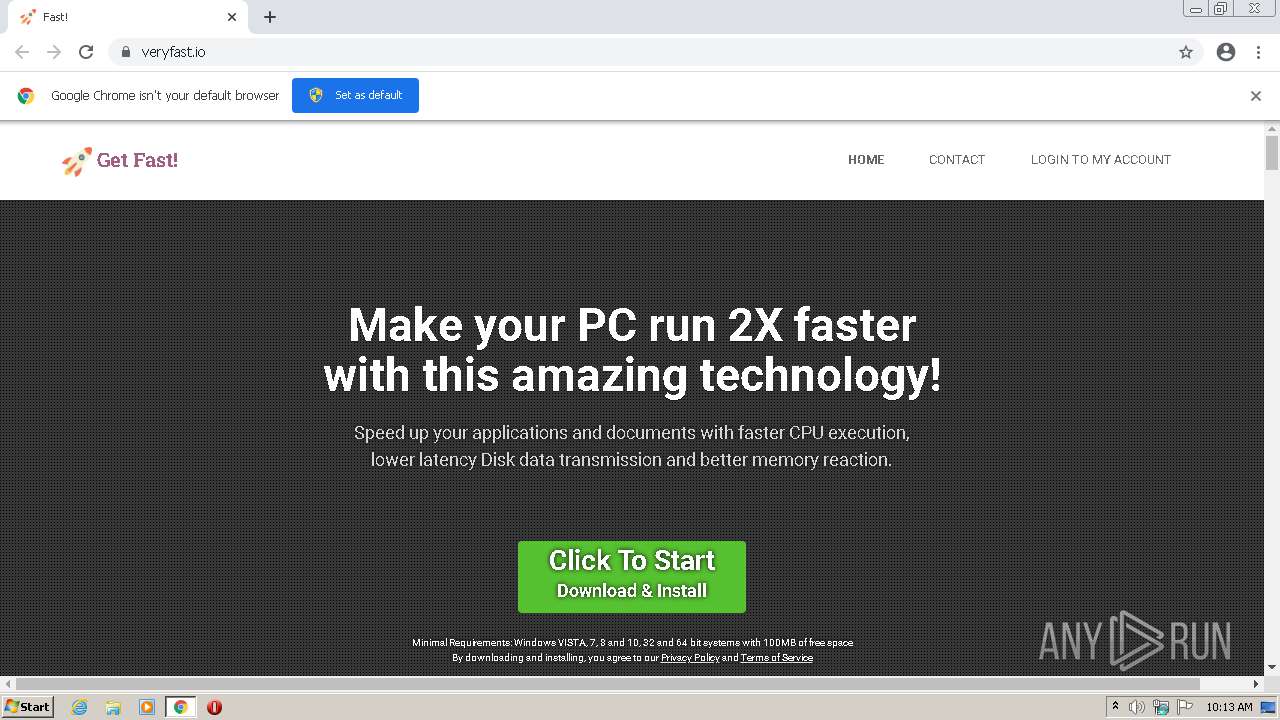
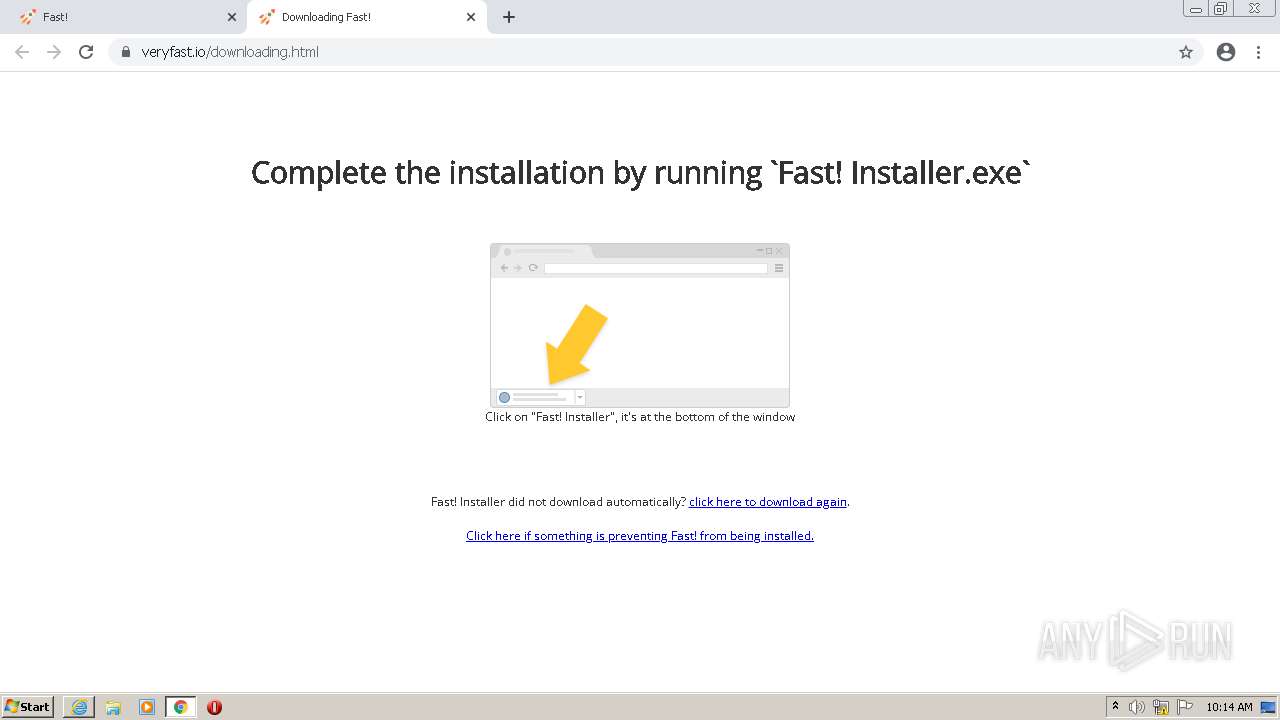
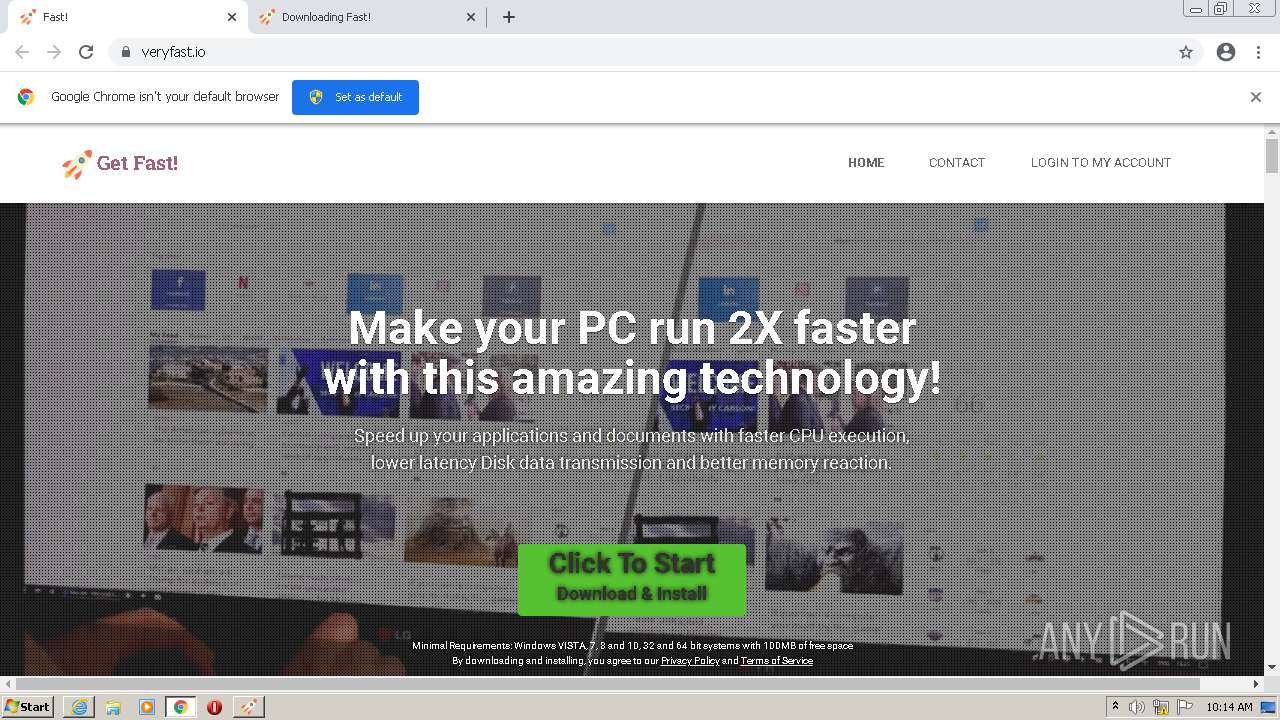
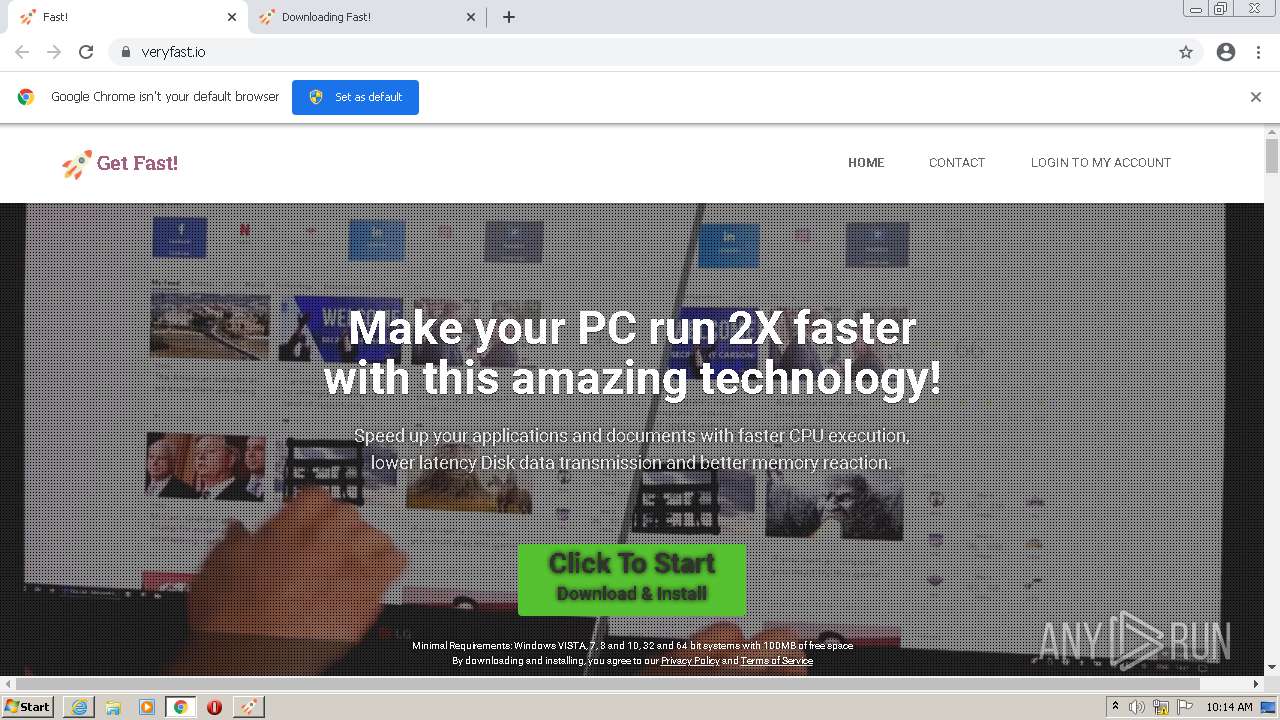
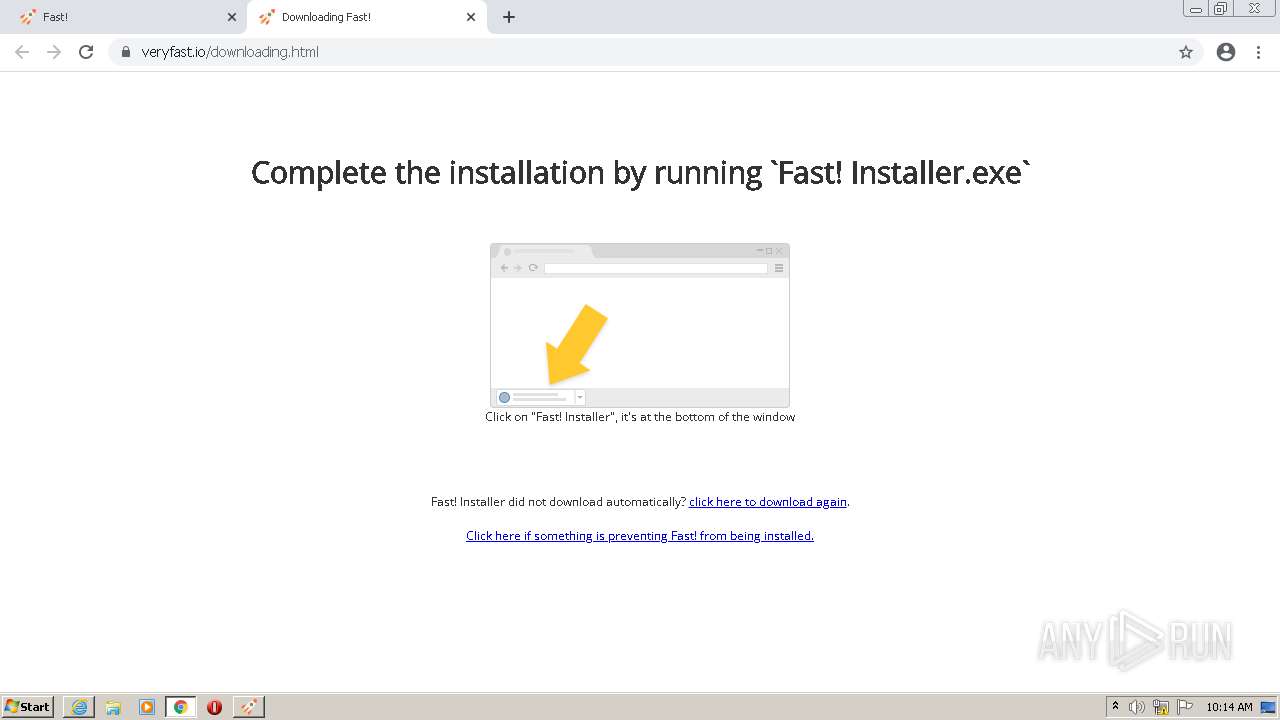
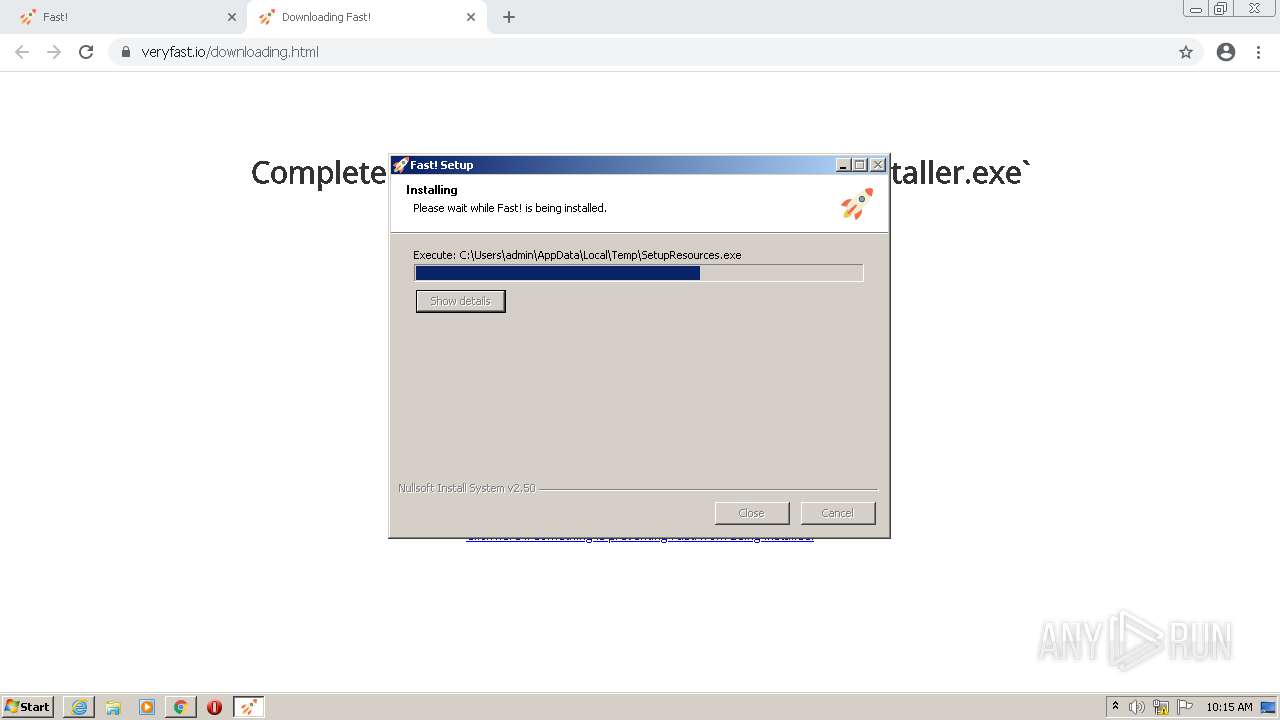
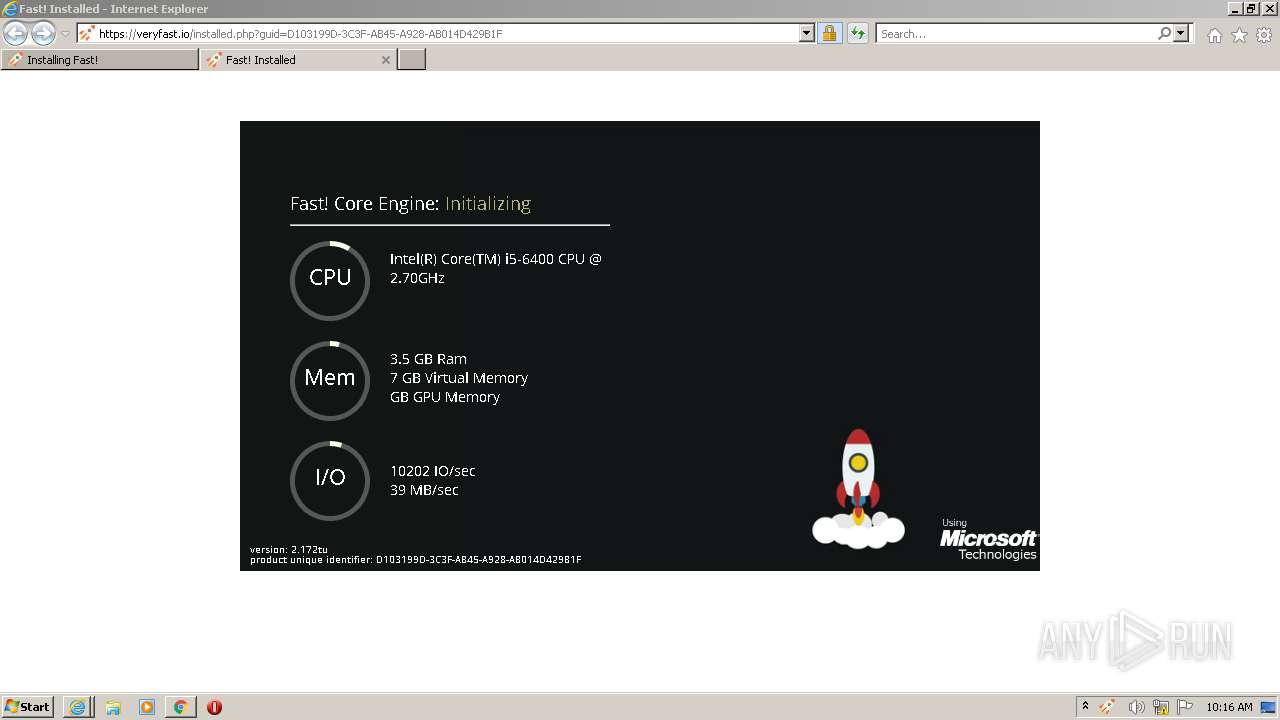
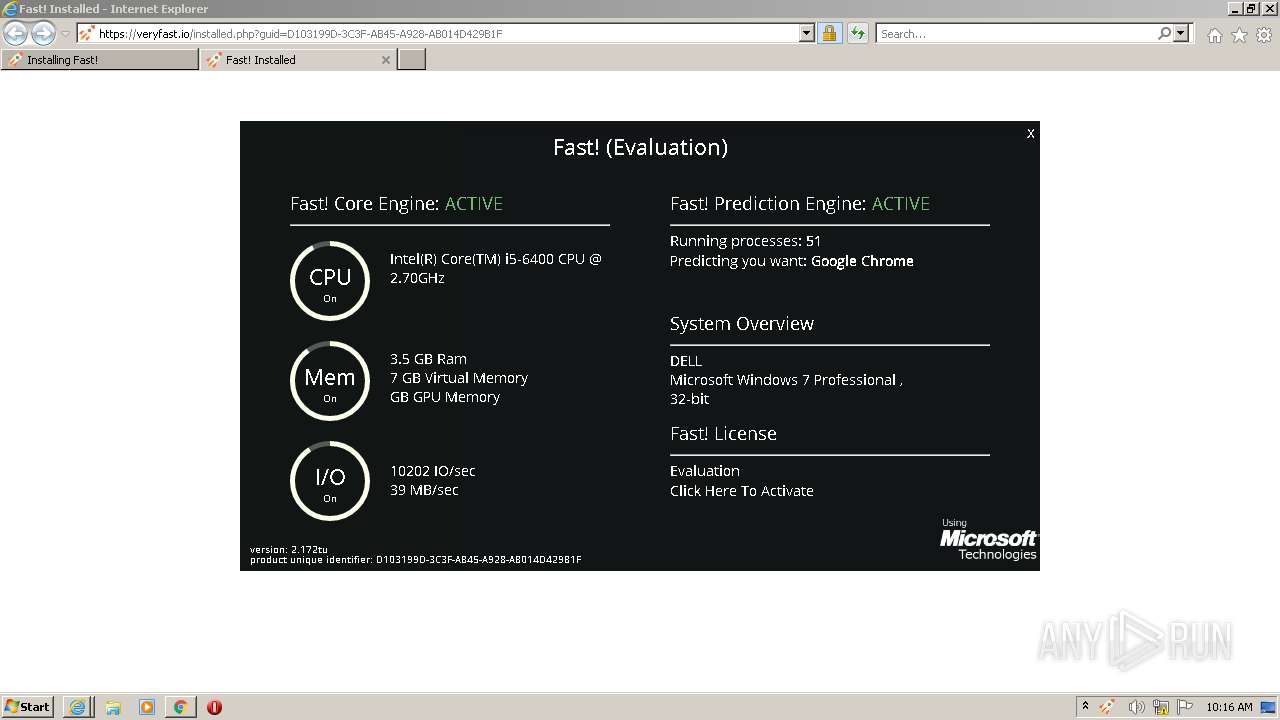
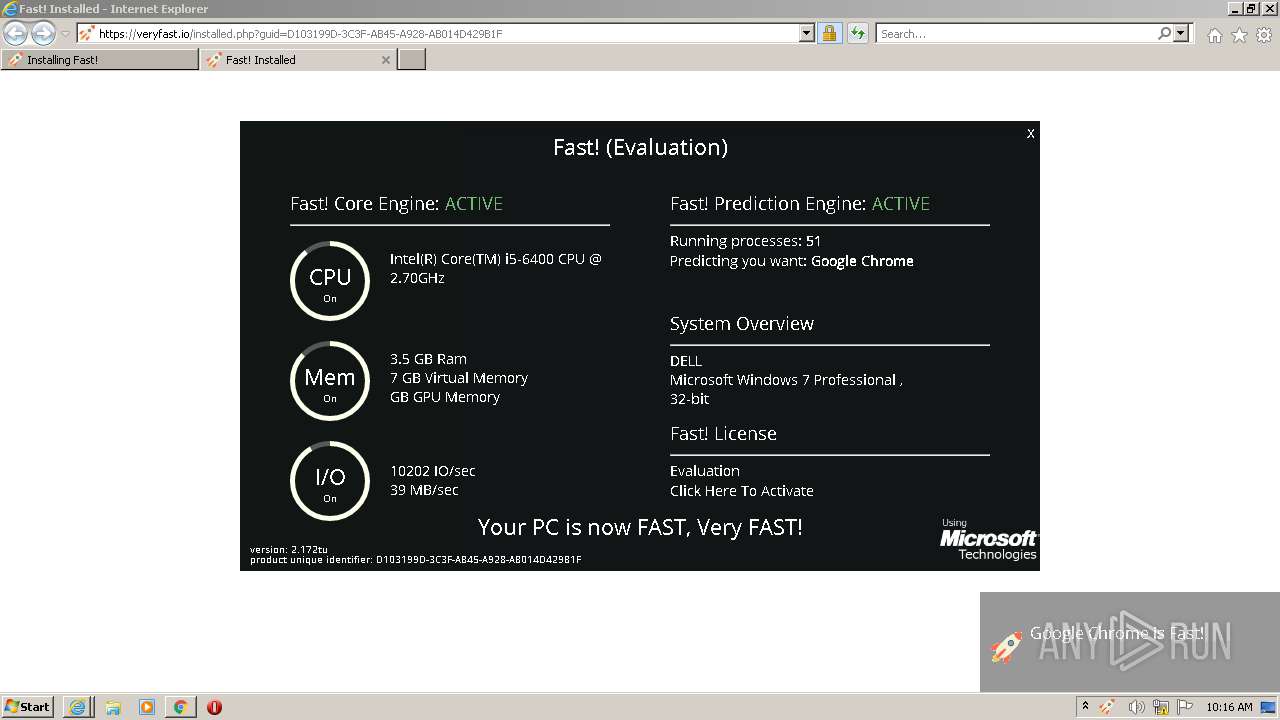
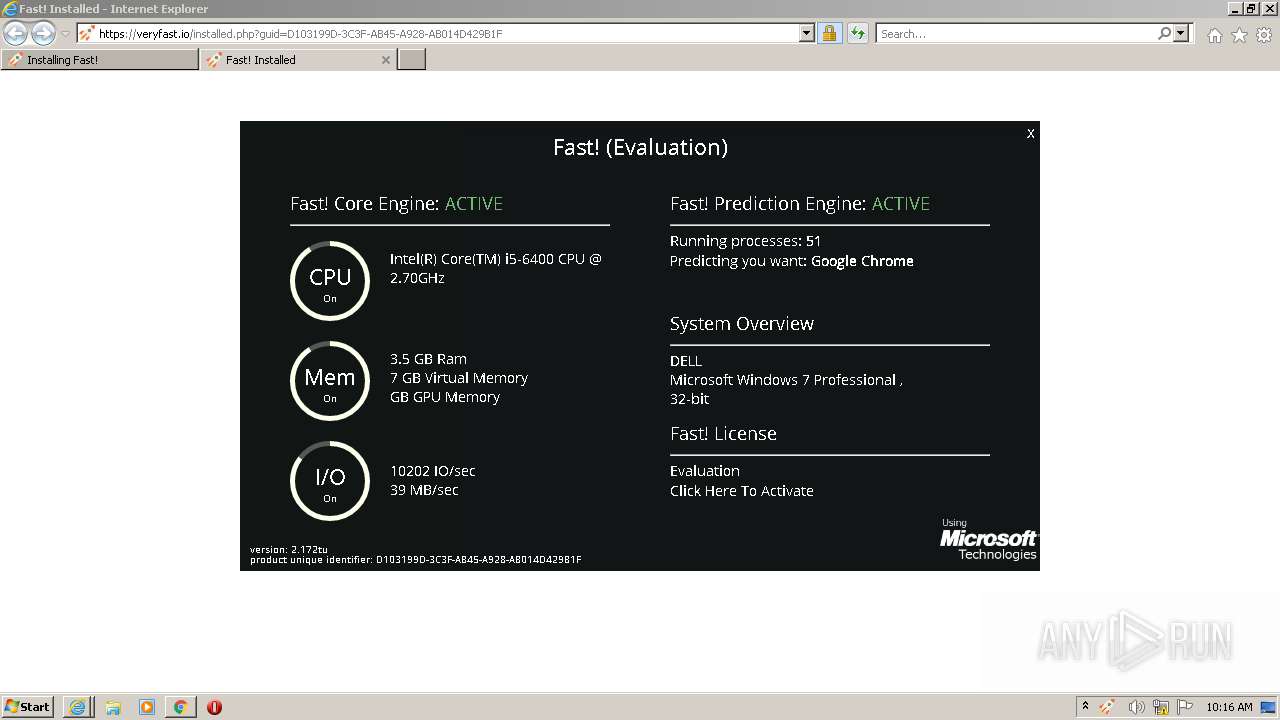
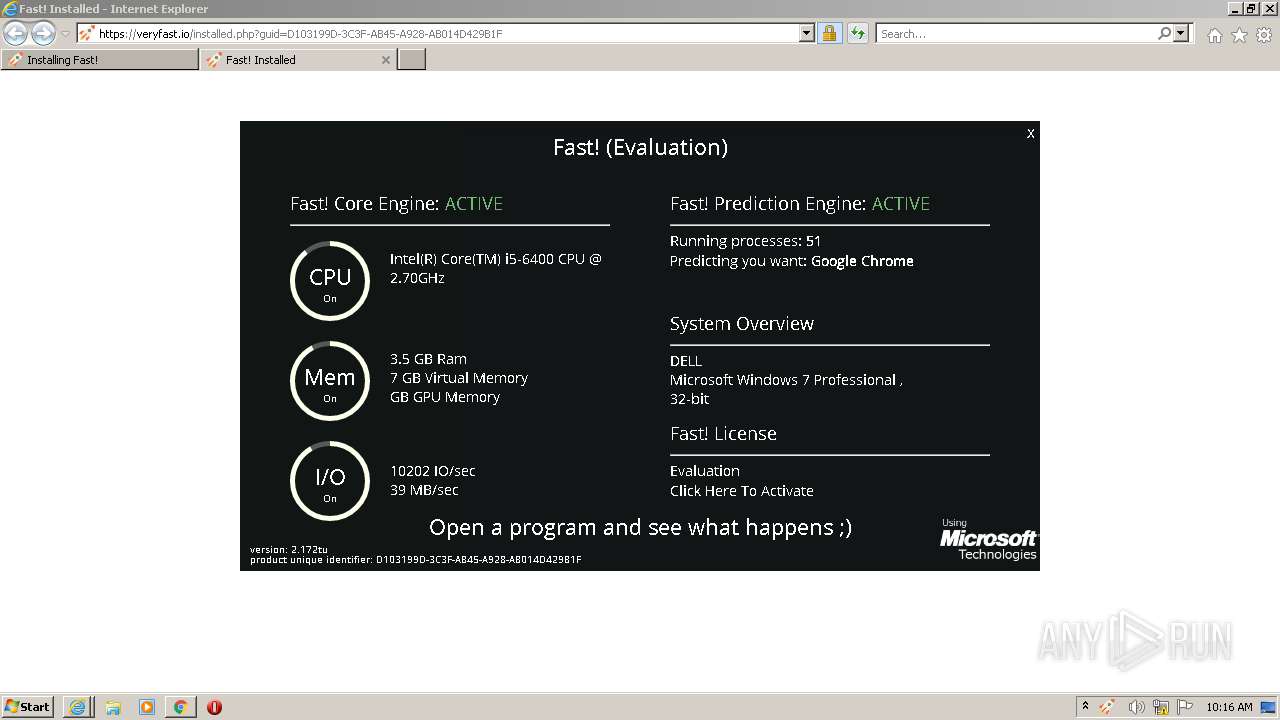
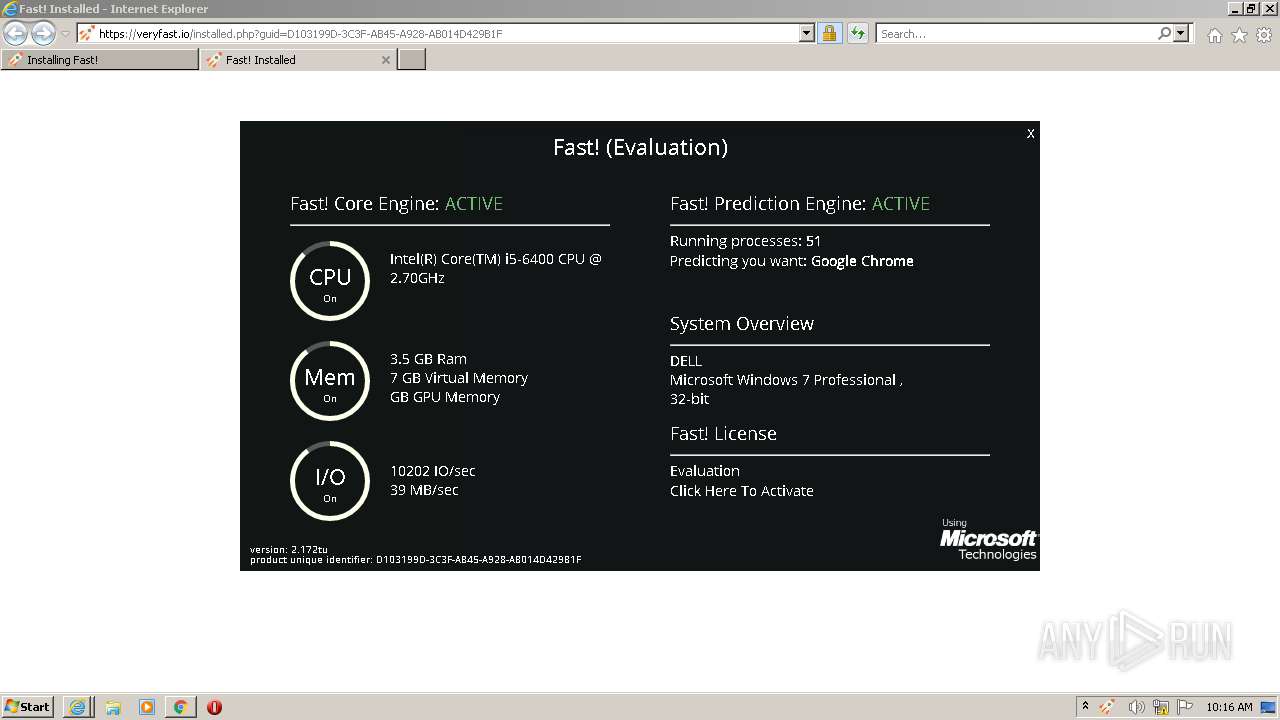
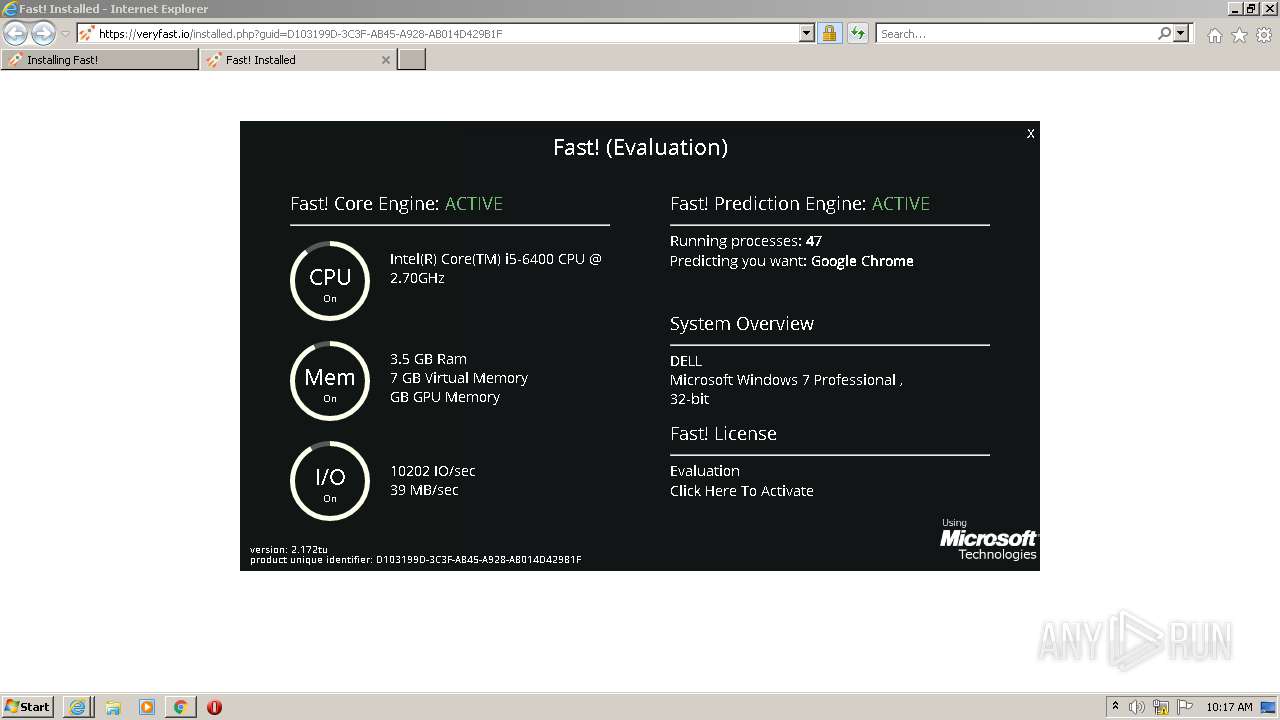
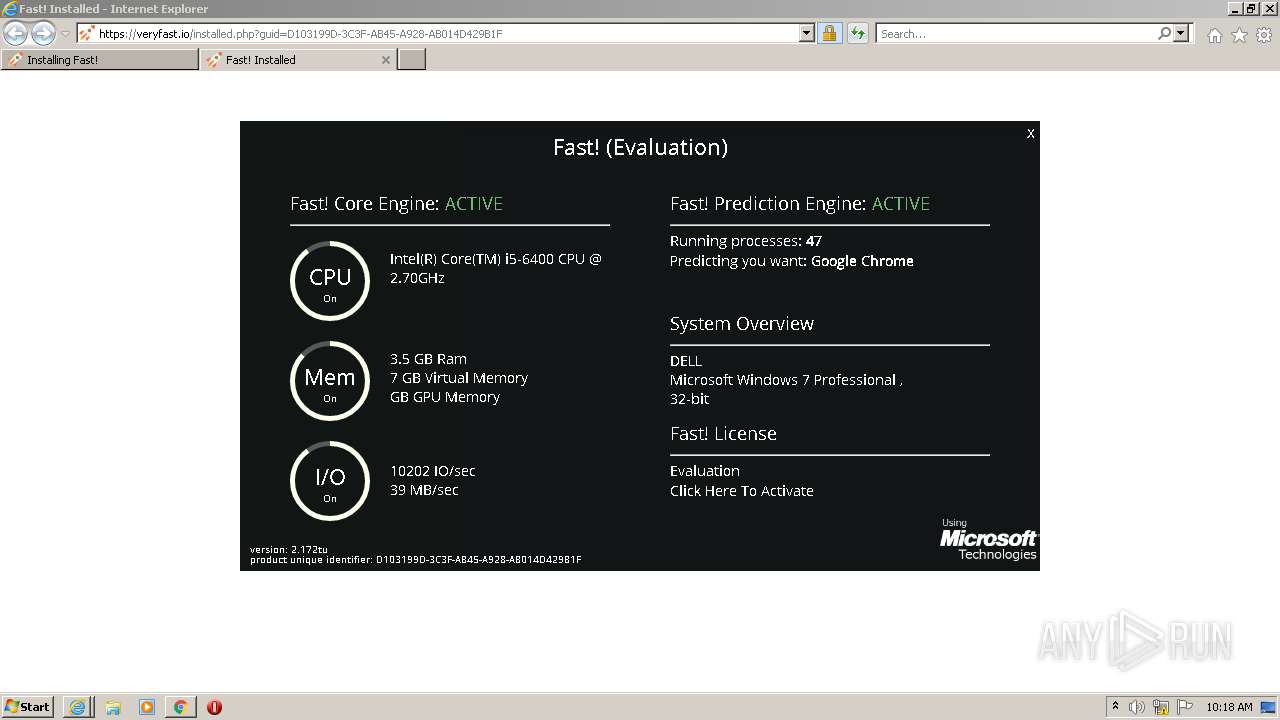
| URL: | https://veryfast.io/ |
| Full analysis: | https://app.any.run/tasks/bd70539f-d3a0-4389-98bb-a092e5abc2b8 |
| Verdict: | Malicious activity |
| Analysis date: | October 26, 2021, 09:12:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3AC99D5688250C29F9A9374F912B4212 |
| SHA1: | 2655E8CDE259E3DB84B7BDEBB17FFF0BB966018A |
| SHA256: | 8F7C592F6ACC950C956D6085F1B6B967C279B80370756407FE48CB69269B6994 |
| SSDEEP: | 3:N80chLK:2LK |
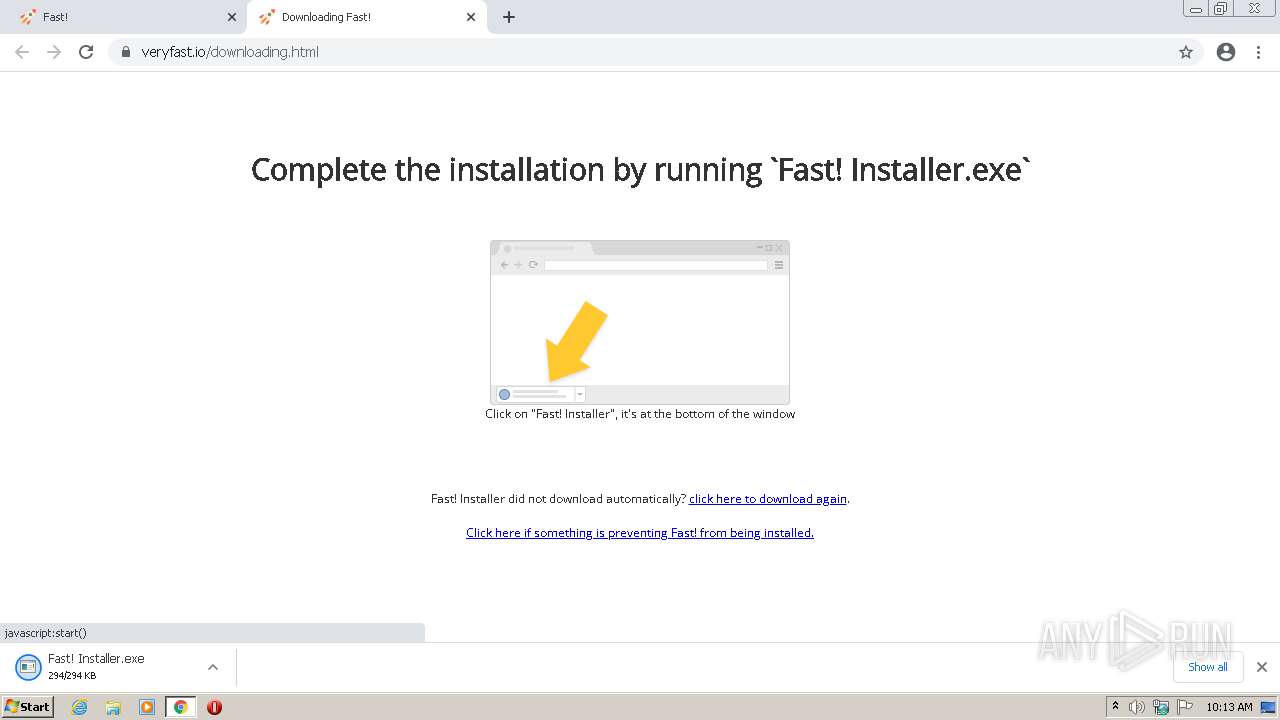
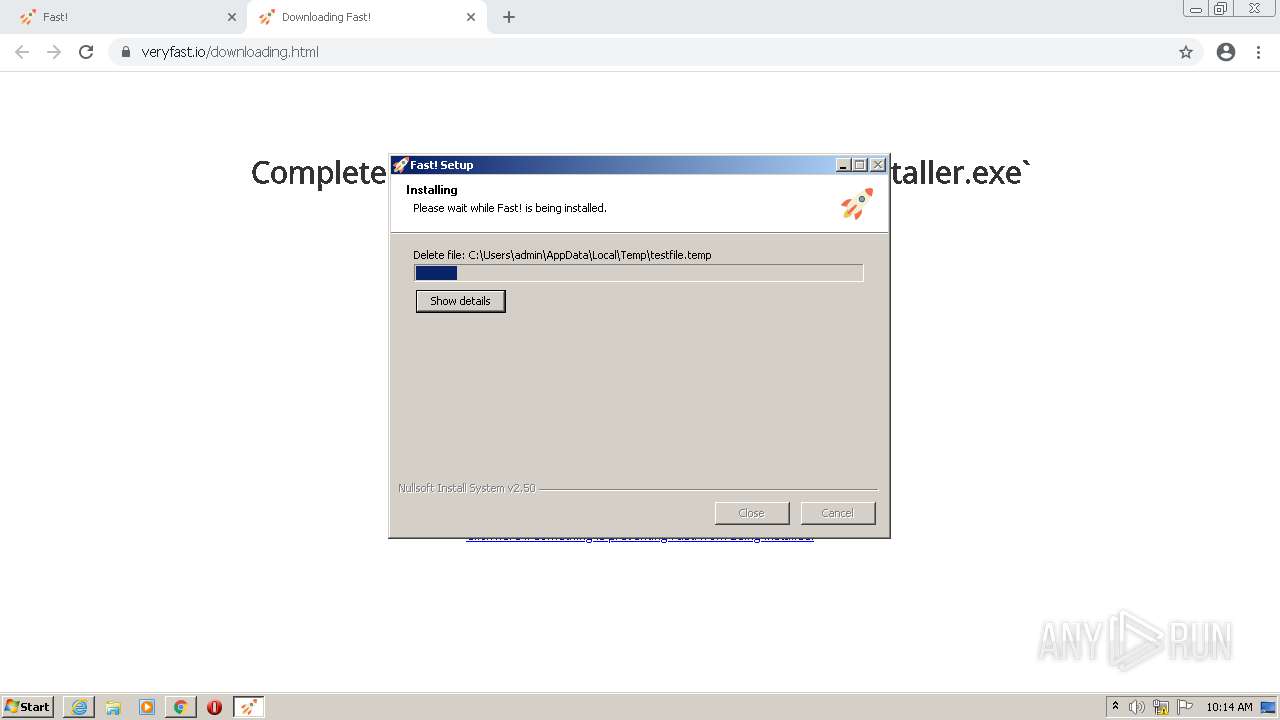
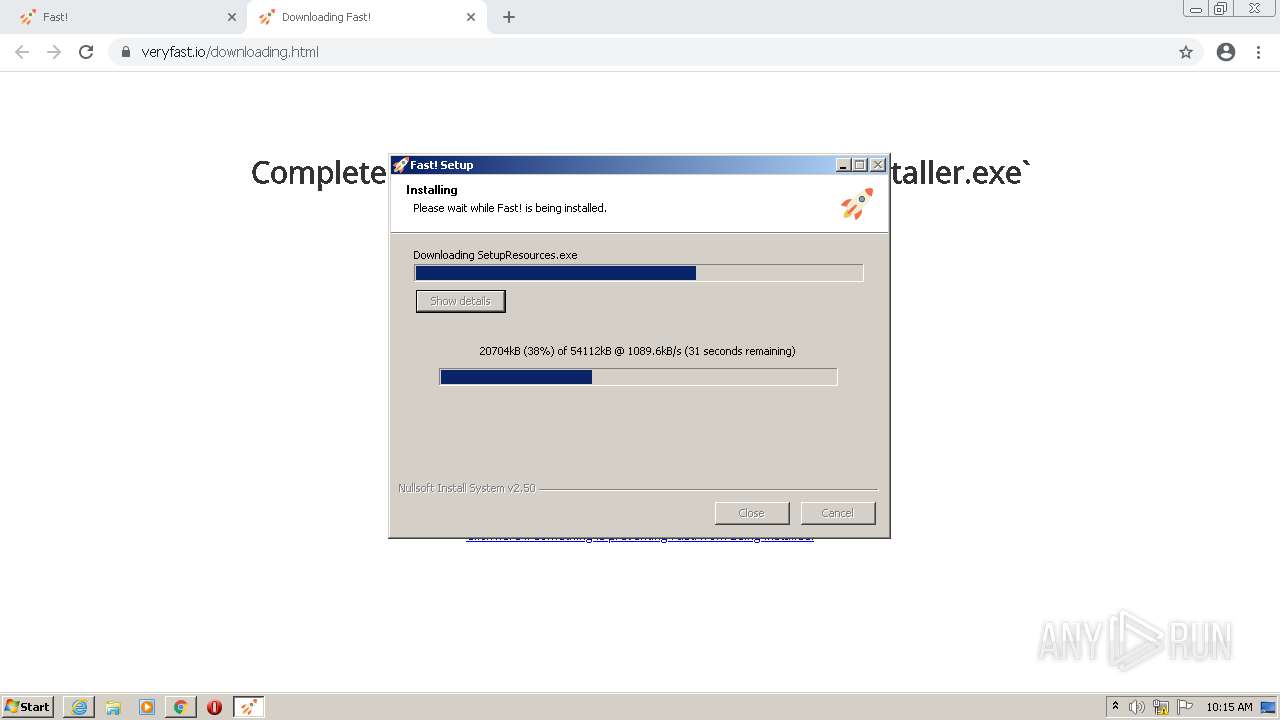
MALICIOUS
Application was dropped or rewritten from another process
- Fast! Installer.exe (PID: 3868)
- Fast! Installer.exe (PID: 2660)
- SetupEngine.exe (PID: 2528)
- diskspd.exe (PID: 596)
- SetupResources.exe (PID: 2096)
- nw.exe (PID: 3396)
- nw.exe (PID: 2768)
- fast!.exe (PID: 2292)
- FastSRV.exe (PID: 708)
- nw.exe (PID: 3480)
- nw.exe (PID: 3148)
- Fast!.exe (PID: 2112)
- fast!.exe (PID: 3368)
- nw.exe (PID: 2332)
- nw.exe (PID: 2440)
Changes settings of System certificates
- Fast! Installer.exe (PID: 3868)
Drops executable file immediately after starts
- SetupEngine.exe (PID: 2528)
- SetupResources.exe (PID: 2096)
- chrome.exe (PID: 3904)
Loads dropped or rewritten executable
- SetupEngine.exe (PID: 2528)
- nw.exe (PID: 2768)
- nw.exe (PID: 3396)
- nw.exe (PID: 3480)
- nw.exe (PID: 3148)
- nw.exe (PID: 2332)
- nw.exe (PID: 2440)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 320)
- Fast! Installer.exe (PID: 3868)
- SetupEngine.exe (PID: 2528)
- SetupResources.exe (PID: 2096)
- chrome.exe (PID: 3904)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 320)
- SetupEngine.exe (PID: 2528)
- SetupResources.exe (PID: 2096)
- chrome.exe (PID: 3904)
Reads the computer name
- Fast! Installer.exe (PID: 3868)
- SetupEngine.exe (PID: 2528)
- diskspd.exe (PID: 596)
- SetupResources.exe (PID: 2096)
- fast!.exe (PID: 2292)
- FastSRV.exe (PID: 708)
- nw.exe (PID: 3396)
- nw.exe (PID: 3480)
- nw.exe (PID: 2332)
Checks supported languages
- Fast! Installer.exe (PID: 3868)
- SetupEngine.exe (PID: 2528)
- ns3C3D.tmp (PID: 3208)
- cmd.exe (PID: 2824)
- diskspd.exe (PID: 596)
- SetupResources.exe (PID: 2096)
- fast!.exe (PID: 2292)
- FastSRV.exe (PID: 708)
- nw.exe (PID: 3396)
- nw.exe (PID: 2768)
- nw.exe (PID: 3480)
- nw.exe (PID: 3148)
- Fast!.exe (PID: 2112)
- fast!.exe (PID: 3368)
- nw.exe (PID: 2332)
- nw.exe (PID: 2440)
Adds / modifies Windows certificates
- Fast! Installer.exe (PID: 3868)
Searches for installed software
- Fast! Installer.exe (PID: 3868)
- fast!.exe (PID: 2292)
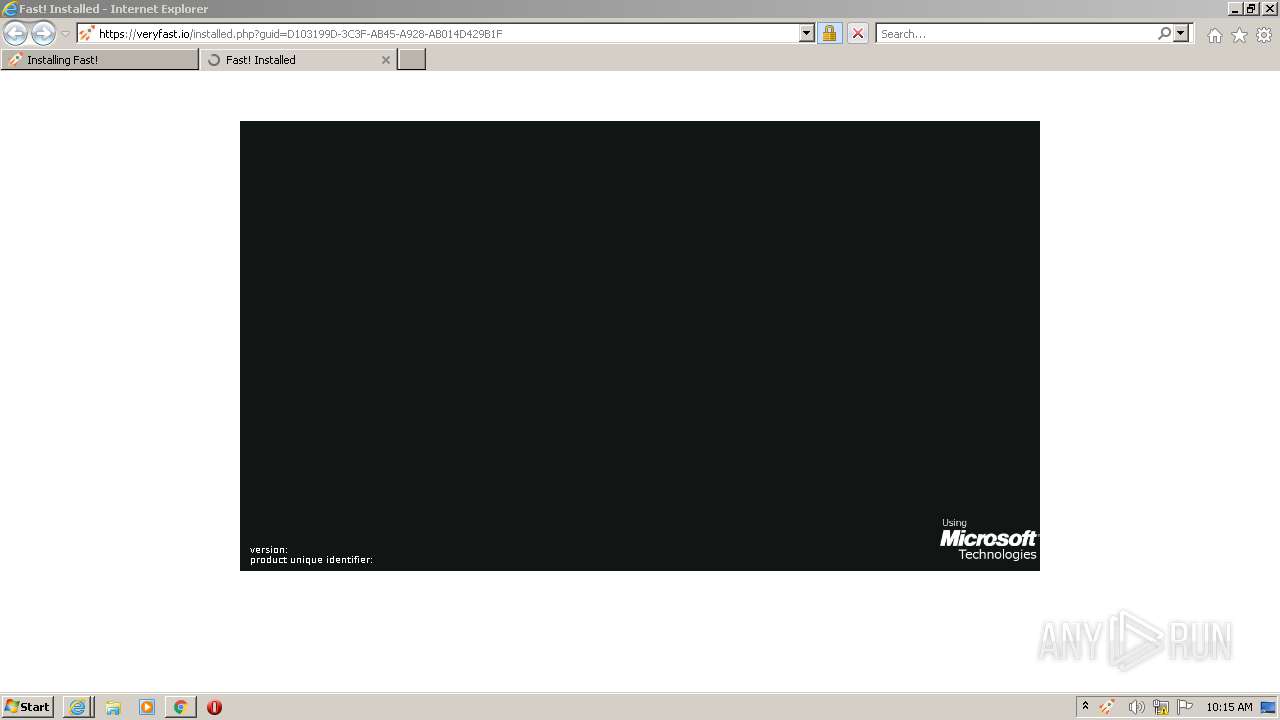
Starts Internet Explorer
- Fast! Installer.exe (PID: 3868)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2568)
Starts application with an unusual extension
- SetupEngine.exe (PID: 2528)
Creates a directory in Program Files
- SetupEngine.exe (PID: 2528)
- SetupResources.exe (PID: 2096)
Starts CMD.EXE for commands execution
- ns3C3D.tmp (PID: 3208)
Creates a software uninstall entry
- SetupEngine.exe (PID: 2528)
Creates files in the program directory
- SetupEngine.exe (PID: 2528)
- SetupResources.exe (PID: 2096)
Drops a file with too old compile date
- SetupEngine.exe (PID: 2528)
- SetupResources.exe (PID: 2096)
Creates files in the user directory
- SetupEngine.exe (PID: 2528)
Executed as Windows Service
- FastSRV.exe (PID: 708)
Application launched itself
- nw.exe (PID: 3396)
INFO
Checks supported languages
- chrome.exe (PID: 320)
- chrome.exe (PID: 2324)
- chrome.exe (PID: 3772)
- chrome.exe (PID: 1780)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 3480)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 924)
- chrome.exe (PID: 3900)
- iexplore.exe (PID: 2732)
- chrome.exe (PID: 2812)
- iexplore.exe (PID: 3264)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 2392)
- iexplore.exe (PID: 2568)
- chrome.exe (PID: 1400)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 3340)
Application launched itself
- chrome.exe (PID: 320)
- iexplore.exe (PID: 2732)
Reads the computer name
- chrome.exe (PID: 320)
- chrome.exe (PID: 3772)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 924)
- chrome.exe (PID: 2628)
- iexplore.exe (PID: 2732)
- chrome.exe (PID: 2812)
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2568)
Reads the hosts file
- chrome.exe (PID: 320)
- chrome.exe (PID: 3772)
- nw.exe (PID: 3396)
Reads settings of System Certificates
- chrome.exe (PID: 3772)
- chrome.exe (PID: 320)
- Fast! Installer.exe (PID: 3868)
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2732)
- SetupEngine.exe (PID: 2528)
- iexplore.exe (PID: 2568)
- nw.exe (PID: 3396)
Checks Windows Trust Settings
- Fast! Installer.exe (PID: 3868)
- chrome.exe (PID: 320)
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2732)
- SetupEngine.exe (PID: 2528)
- iexplore.exe (PID: 2568)
Reads the date of Windows installation
- chrome.exe (PID: 2628)
Changes internet zones settings
- iexplore.exe (PID: 2732)
Reads internet explorer settings
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2568)
Creates files in the user directory
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2732)
- iexplore.exe (PID: 2568)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2732)
Changes settings of System certificates
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2732)
Dropped object may contain Bitcoin addresses
- SetupResources.exe (PID: 2096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
49
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://veryfast.io/" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 596 | C:\Users\admin\AppData\Local\Temp\diskspd.exe -c100M -b4K -t1 -r -o32 -d10 -ag -h -Rxml C:\Users\admin\AppData\Local\Temp\testfile.temp | C:\Users\admin\AppData\Local\Temp\diskspd.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 708 | "C:\Program Files\Fast!\FastSRV.exe" | C:\Program Files\Fast!\FastSRV.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1056,7279545327550564058,16177430593093222120,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3108 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,7279545327550564058,16177430593093222120,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3076 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,7279545327550564058,16177430593093222120,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1812 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2096 | C:\Users\admin\AppData\Local\Temp\SetupResources.exe | C:\Users\admin\AppData\Local\Temp\SetupResources.exe | SetupEngine.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Fast!\Fast!.exe" | C:\Program Files\Fast!\Fast!.exe | — | SetupEngine.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,7279545327550564058,16177430593093222120,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3752 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\fast!\fast!.exe" | C:\Program Files\fast!\fast!.exe | — | FastSRV.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
58 825
Read events
58 327
Write events
490
Delete events
8
Modification events
| (PID) Process: | (320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (320) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
26
Suspicious files
80
Text files
270
Unknown types
99
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6177C6A5-140.pma | — | |
MD5:— | SHA256:— | |||
| 320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8b6bfdb4-f8c0-4017-a820-d81f18a6370f.tmp | text | |
MD5:— | SHA256:— | |||
| 320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1017a1.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF101781.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
91
TCP/UDP connections
122
DNS requests
65
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 209.85.226.104:80 | http://r3---sn-5hne6ns6.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=157.97.122.3&mm=28&mn=sn-5hne6ns6&ms=nvh&mt=1635239295&mv=m&mvi=3&pl=24&shardbypass=yes&smhost=r3---sn-5hne6n7e.gvt1.com | US | — | — | whitelisted |
— | — | HEAD | 302 | 142.250.185.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
2732 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3772 | chrome.exe | GET | 200 | 23.32.238.232:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?283268f405380832 | US | compressed | 59.7 Kb | whitelisted |
3868 | Fast! Installer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuqL92L3tjkN67RNFF%2FEdvT6NEzAQUwBKyKHRoRmfpcCV0GgBFWwZ9XEQCEAamqs%2Fo9%2Fik85Zcs%2BDaQ78%3D | US | der | 471 b | whitelisted |
3264 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3868 | Fast! Installer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAGC%2BAmOouYmuRo7J4Qfua8%3D | US | der | 1.47 Kb | whitelisted |
3264 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
— | — | GET | 206 | 209.85.226.104:80 | http://r3---sn-5hne6ns6.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=157.97.122.3&mm=28&mn=sn-5hne6ns6&ms=nvh&mt=1635239295&mv=m&mvi=3&pl=24&shardbypass=yes&smhost=r3---sn-5hne6n7e.gvt1.com | US | binary | 5.63 Kb | whitelisted |
3868 | Fast! Installer.exe | GET | 200 | 2.16.186.11:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgSD5dG8D5nNz0gsi0uESP2ZEA%3D%3D | unknown | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3772 | chrome.exe | 142.250.181.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 34.195.48.210:443 | veryfast.io | Amazon.com, Inc. | US | suspicious |
3772 | chrome.exe | 23.32.238.232:80 | ctldl.windowsupdate.com | XO Communications | US | unknown |
3772 | chrome.exe | 142.250.185.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3772 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 52.222.206.85:443 | d1uyoz7mfvzv4e.cloudfront.net | Amazon.com, Inc. | US | unknown |
— | — | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 74.125.71.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 142.250.185.99:443 | www.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
veryfast.io |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
d1uyoz7mfvzv4e.cloudfront.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |