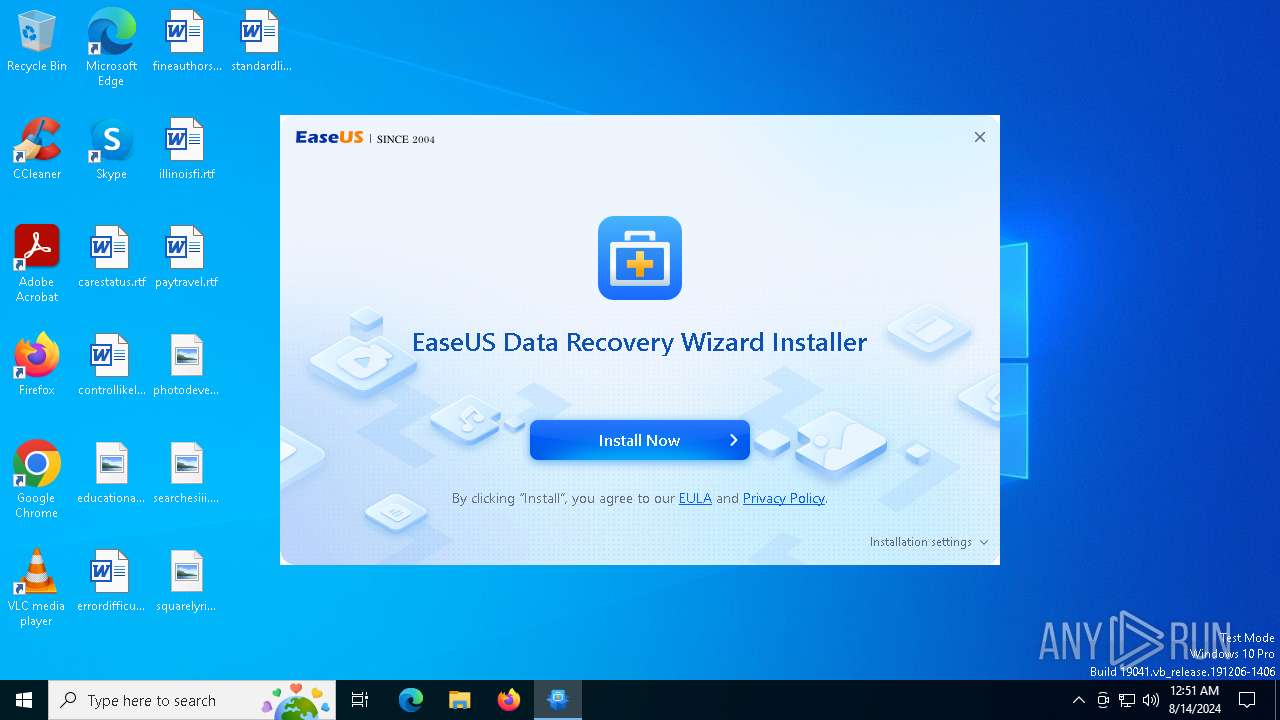
| File name: | drw_google_trial_installer.27584.exe |
| Full analysis: | https://app.any.run/tasks/3db3fede-947f-41b7-b075-af0a21ba01e0 |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2024, 00:51:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 789E380FB028EAE5575B11ABF440D4CD |
| SHA1: | B37E989E4F185D8606B6F66494F816A4278C5BEE |
| SHA256: | 8F6A60DBC178B95D6099FE381FA21E0F22F1EA4BB5EF77B2253848A2A191A44D |
| SSDEEP: | 98304:3R6kCNJtOBr9cFj83wAqNYoMmZGKHZ9/RoMt5Wr8ufGlzny2xwIw/NLS17e0z0tL:16Ny3 |
MALICIOUS
Scans artifacts that could help determine the target
- AliyunWrapExe.exe (PID: 6712)
- AliyunWrapExe.exe (PID: 7084)
SUSPICIOUS
Drops the executable file immediately after the start
- drw_google_trial_installer.27584.exe (PID: 6600)
- drw19.0.0.0_ad_google_trial.exe (PID: 7056)
- drw19.0.0.0_ad_google_trial.tmp (PID: 2608)
Reads security settings of Internet Explorer
- EDownloader.exe (PID: 6632)
- AliyunWrapExe.exe (PID: 6712)
- AliyunWrapExe.exe (PID: 7084)
Executable content was dropped or overwritten
- drw_google_trial_installer.27584.exe (PID: 6600)
- drw19.0.0.0_ad_google_trial.exe (PID: 7056)
- drw19.0.0.0_ad_google_trial.tmp (PID: 2608)
Reads Microsoft Outlook installation path
- EDownloader.exe (PID: 6632)
Reads Internet Explorer settings
- EDownloader.exe (PID: 6632)
Reads the Windows owner or organization settings
- drw19.0.0.0_ad_google_trial.tmp (PID: 2608)
Process drops legitimate windows executable
- drw19.0.0.0_ad_google_trial.tmp (PID: 2608)
The process drops C-runtime libraries
- drw19.0.0.0_ad_google_trial.tmp (PID: 2608)
INFO
Creates files or folders in the user directory
- AliyunWrapExe.exe (PID: 6712)
- AliyunWrapExe.exe (PID: 7084)
Checks supported languages
- drw_google_trial_installer.27584.exe (PID: 6600)
- InfoForSetup.exe (PID: 6784)
- InfoForSetup.exe (PID: 6656)
- InfoForSetup.exe (PID: 6776)
- AliyunWrapExe.exe (PID: 6712)
- InfoForSetup.exe (PID: 6692)
- EDownloader.exe (PID: 6632)
- InfoForSetup.exe (PID: 7044)
- InfoForSetup.exe (PID: 7032)
- InfoForSetup.exe (PID: 2476)
- InfoForSetup.exe (PID: 6832)
- drw19.0.0.0_ad_google_trial.exe (PID: 7056)
- drw19.0.0.0_ad_google_trial.tmp (PID: 2608)
- InfoForSetup.exe (PID: 4236)
- AliyunWrapExe.exe (PID: 7084)
- InfoForSetup.exe (PID: 6568)
- InfoForSetup.exe (PID: 7000)
- InfoForSetup.exe (PID: 6612)
Reads the computer name
- AliyunWrapExe.exe (PID: 6712)
- EDownloader.exe (PID: 6632)
- drw19.0.0.0_ad_google_trial.tmp (PID: 2608)
- AliyunWrapExe.exe (PID: 7084)
Create files in a temporary directory
- drw_google_trial_installer.27584.exe (PID: 6600)
- InfoForSetup.exe (PID: 6692)
- EDownloader.exe (PID: 6632)
- AliyunWrapExe.exe (PID: 6712)
- drw19.0.0.0_ad_google_trial.exe (PID: 7056)
- drw19.0.0.0_ad_google_trial.tmp (PID: 2608)
- AliyunWrapExe.exe (PID: 7084)
Checks proxy server information
- AliyunWrapExe.exe (PID: 6712)
- EDownloader.exe (PID: 6632)
- AliyunWrapExe.exe (PID: 7084)
Reads the machine GUID from the registry
- EDownloader.exe (PID: 6632)
Process checks Internet Explorer phishing filters
- EDownloader.exe (PID: 6632)
Creates files in the program directory
- drw19.0.0.0_ad_google_trial.tmp (PID: 2608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 03:57:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
151
Monitored processes
19
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2476 | /SendInfo Window "Downloading" Activity "Result_Download_Program" Attribute "{\"Average_Networkspeed\":\"1.60MB\",\"Cdn\":\"https://d1.easeus.com/drw/ad/drw19.0.0.0_ad_google_trial.exe\",\"Elapsedtime\":\"47\",\"Errorinfo\":\"0\",\"Result\":\"Success\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2608 | "C:\Users\admin\AppData\Local\Temp\is-E5G6K.tmp\drw19.0.0.0_ad_google_trial.tmp" /SL5="$601E2,78068482,192512,C:\Users\admin\AppData\Local\Temp\drw19.0.0.0_ad_google_trial.exe" /verysilent /DIR="C:\Program Files\EaseUS\EaseUS Data Recovery Wizard" /LANG=en agreeImprove= GUID=S-1-5-21-1693682860-607145093-2874071422-1001 xurlID=27584 TestID=AG190_2024729newcert-07245 | C:\Users\admin\AppData\Local\Temp\is-E5G6K.tmp\drw19.0.0.0_ad_google_trial.tmp | drw19.0.0.0_ad_google_trial.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
| 4236 | "C:\Users\admin\AppData\Local\Temp\is-6RDSA.tmp\InfoForSetup.exe" /SendInfo "Window" "Langsel" "Activity" "Click_Confirm" "Attribute" "{\"Language\":\"en\"}" | C:\Users\admin\AppData\Local\Temp\is-6RDSA.tmp\InfoForSetup.exe | — | drw19.0.0.0_ad_google_trial.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6552 | "C:\Users\admin\AppData\Local\Temp\drw_google_trial_installer.27584.exe" | C:\Users\admin\AppData\Local\Temp\drw_google_trial_installer.27584.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6568 | "C:\Users\admin\AppData\Local\Temp\is-6RDSA.tmp\InfoForSetup.exe" /SendInfo "Window" "Selectdestinationlocation" "Activity" "Click_Confirm" "Attribute" "{\"Path\":\"C:/Program Files/EaseUS/EaseUS Data Recovery Wizard\"}" | C:\Users\admin\AppData\Local\Temp\is-6RDSA.tmp\InfoForSetup.exe | — | drw19.0.0.0_ad_google_trial.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6600 | "C:\Users\admin\AppData\Local\Temp\drw_google_trial_installer.27584.exe" | C:\Users\admin\AppData\Local\Temp\drw_google_trial_installer.27584.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6612 | "C:\Users\admin\AppData\Local\Temp\is-6RDSA.tmp\InfoForSetup.exe" /SendInfo "Window" "Selectadditionaltasks" "Activity" "Click_Install" "Attribute" "{\"Test_id\":\"AG190_2024729newcert-07245\",\"Version\":\"Ad_Google_Trial_trial\",\"Num\":\"19.0.0.0\",\"Language\":\"en\"}" | C:\Users\admin\AppData\Local\Temp\is-6RDSA.tmp\InfoForSetup.exe | — | drw19.0.0.0_ad_google_trial.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6632 | "C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\EDownloader.exe" EXEDIR=C:\Users\admin\AppData\Local\Temp ||| EXENAME=drw_google_trial_installer.27584.exe ||| DOWNLOAD_VERSION=ad_google_trial ||| PRODUCT_VERSION=2.0.0 ||| INSTALL_TYPE=0 | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\EDownloader.exe | drw_google_trial_installer.27584.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6656 | /Uid "S-1-5-21-1693682860-607145093-2874071422-1001" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 6692 | /SendInfo Window "Web_Installer" Activity "Result_Run_Installer" Attribute "{\"Country\":\"United States\",\"Pageid\":\"27584\",\"Timezone\":\"GMT-00:00\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
8 356
Read events
8 316
Write events
40
Delete events
0
Modification events
| (PID) Process: | (6712) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6712) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6712) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6712) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6712) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6712) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6712) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6632) EDownloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6632) EDownloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6632) EDownloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
164
Suspicious files
95
Text files
4 134
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6600 | drw_google_trial_installer.27584.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\ChineseTrad.ini | text | |
MD5:FE7AD6D1DD07AEAFEECE921ECB23F3E7 | SHA256:7EF907A793D9087AA804A688BDDDECF33A76011E4D820E7332533C070277507F | |||
| 6600 | drw_google_trial_installer.27584.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\skin.zip | compressed | |
MD5:784C6F9B53521F4CB115532F49B67A36 | SHA256:A0951464134E2AF94ECD389EA9C0F3D784BAE909F60EB2F45D7764B4DBDE7A73 | |||
| 6600 | drw_google_trial_installer.27584.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\EDownloader.exe | executable | |
MD5:8A250A75859FE52116E706A640E6D77C | SHA256:823AB6955052EF34218559B53D4F15224B5A850B532672FA33A7634DC74981DC | |||
| 6600 | drw_google_trial_installer.27584.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\Chinese.ini | text | |
MD5:FD6CA501ED9A613A5094EB4C92C1A847 | SHA256:4637C9C3FF511C3F15CB482C5A3EE42A3237D26AD002B2FCC3FF467E7A10B99F | |||
| 6600 | drw_google_trial_installer.27584.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\French.ini | text | |
MD5:1737B0DE1DA74E1D45285479CE66E556 | SHA256:201229433F78F5CB87A9357921F34CAA2820B2917FF572E82A57D31DB5774E46 | |||
| 6600 | drw_google_trial_installer.27584.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\Arabic.ini | text | |
MD5:B334764EB0A1069F6BA04C8E1F088CD0 | SHA256:D9A87257F203A80489756B8B31628FFF8D10AAB229D20A637A083059233DC54C | |||
| 6600 | drw_google_trial_installer.27584.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\Mungarian.ini | text | |
MD5:35331ED66C059568C54865EF7D41087C | SHA256:F55A35E6D3CCC944D4C264E34244A127BCE54079621CAB25D9E8E53CC1F9AC07 | |||
| 6600 | drw_google_trial_installer.27584.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\Polish.ini | text | |
MD5:DEF85351F7FDA76B962D6DE5F86F5FE5 | SHA256:E833E96EA0E4568FDDF90386AFDFF3F9BED6EA643FAF9EE6BC0938BE71344294 | |||
| 6600 | drw_google_trial_installer.27584.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\Italian.ini | text | |
MD5:AF930A64DA61B99CB120C8A3222456EB | SHA256:1287CD9E6626EC2081379694A309578C1D83BCA25B2C621D1A5D4608CD7AF9BF | |||
| 6600 | drw_google_trial_installer.27584.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2ad_google_trial\Dutch.ini | text | |
MD5:E4E098A3E165FC5ECB4CB806B7E6E9D8 | SHA256:3FE882930B7C5299290AE6C0C20AE065BD915984B381436B1C3D1D1CBFC67127 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
65
DNS requests
21
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6712 | AliyunWrapExe.exe | GET | 200 | 163.171.156.15:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=2 | unknown | — | — | unknown |
6712 | AliyunWrapExe.exe | POST | 200 | 47.252.97.9:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
6712 | AliyunWrapExe.exe | POST | 200 | 47.252.97.9:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
6712 | AliyunWrapExe.exe | POST | 200 | 47.252.97.9:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
6712 | AliyunWrapExe.exe | POST | 200 | 47.252.97.9:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
6632 | EDownloader.exe | POST | 200 | 18.172.112.107:80 | http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/ | unknown | — | — | unknown |
6712 | AliyunWrapExe.exe | POST | 200 | 47.252.97.9:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4436 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2872 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4208 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3036 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6712 | AliyunWrapExe.exe | 163.171.156.15:80 | track.easeus.com | QUANTILNETWORKS | DE | unknown |
6712 | AliyunWrapExe.exe | 47.252.97.9:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba US Technology Co., Ltd. | US | unknown |
6632 | EDownloader.exe | 18.172.112.107:80 | download.easeus.com | — | US | unknown |
3036 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6632 | EDownloader.exe | 18.66.112.111:443 | d1.easeus.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
track.easeus.com |
| unknown |
easeusinfo.us-east-1.log.aliyuncs.com |
| unknown |
download.easeus.com |
| unknown |
d1.easeus.com |
| unknown |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6712 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6712 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6712 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6712 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6712 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6712 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6712 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
7084 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
7084 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
Process | Message |
|---|---|
EDownloader.exe | [6636]-00:51:39:161 ParseCmdLine param=EXEDIR=C:\Users\admin\AppData\Local\Temp ||| EXENAME=drw_google_trial_installer.27584.exe ||| DOWNLOAD_VERSION=ad_google_trial ||| PRODUCT_VERSION=2.0.0 ||| INSTALL_TYPE=0
|
EDownloader.exe | [6636]-00:51:39:208 Install recomand return=259
|
EDownloader.exe | [6636]-00:51:39:895 Install recomand return=259
|
EDownloader.exe | [6636]-00:51:44:423 Install recomand return=259
|
EDownloader.exe | [6636]-00:51:44:439 Install recomand return=259
|
EDownloader.exe | [6804]-00:51:44:439 PostData Start download url=http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/?exeNumber=27584&lang=English&pcVersion=home&pid=2&tid=1&version=ad_google_trial
|
EDownloader.exe | [6804]-00:51:47:001 PostData end
|
EDownloader.exe | [6804]-00:51:47:001 Json parse Data Start
|
EDownloader.exe | [6804]-00:51:47:001 Json parse Data end
|
EDownloader.exe | [6636]-00:51:47:001 CHttpHelper::GetDownloadInfo 45 download info code:0
|