| download: | phBot%20Installer.exe |
| Full analysis: | https://app.any.run/tasks/c205bbe2-3981-4d51-914c-dc617b7b0316 |
| Verdict: | Malicious activity |
| Analysis date: | May 06, 2019, 12:28:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 85D6F0F52271E26F8663DDC6EB099690 |
| SHA1: | 7F3A3E716A1F61456F890D46E64D646CD35816E6 |
| SHA256: | 8F5F16D4915062EDACD320F59C614476110A874AD75E3A4B4F8A9B5CD195F37B |
| SSDEEP: | 1536:xQFX8F8D8mDd00By9uy9yonnQFOG34QUmeclU1Rghv:yFX8F8D8mxnY9uy9XQFOqUBYo6 |
MALICIOUS
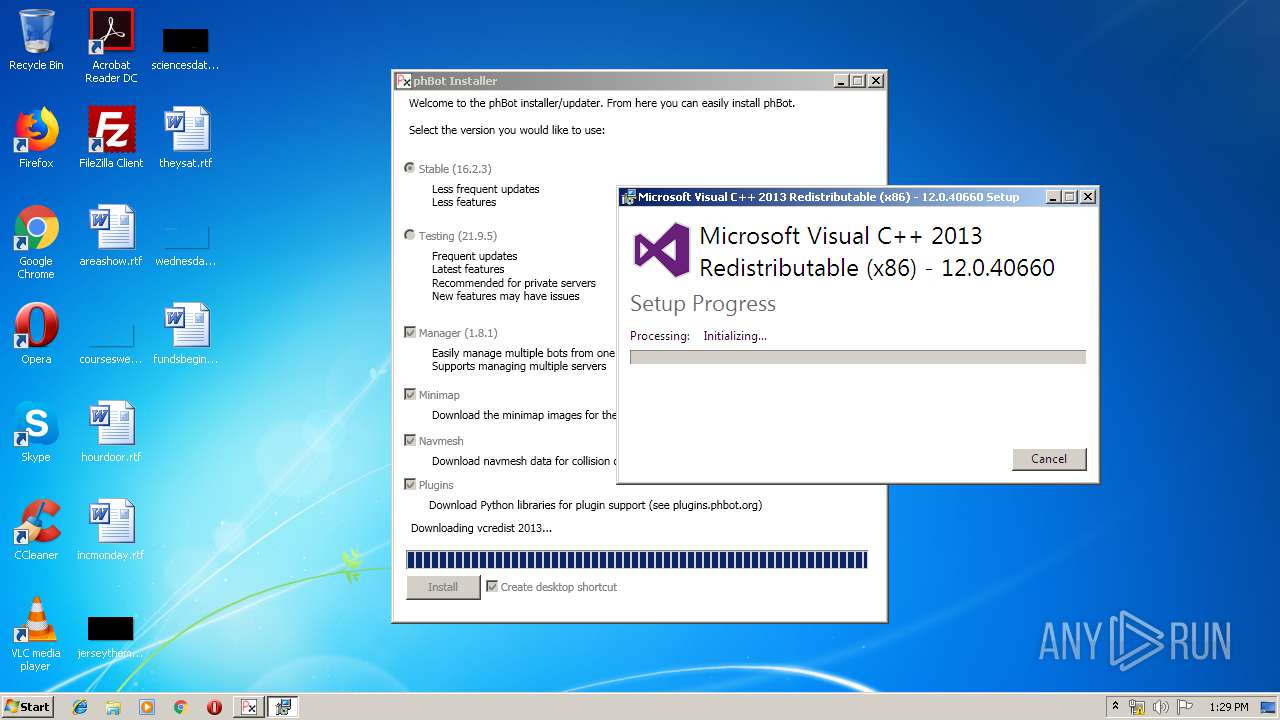
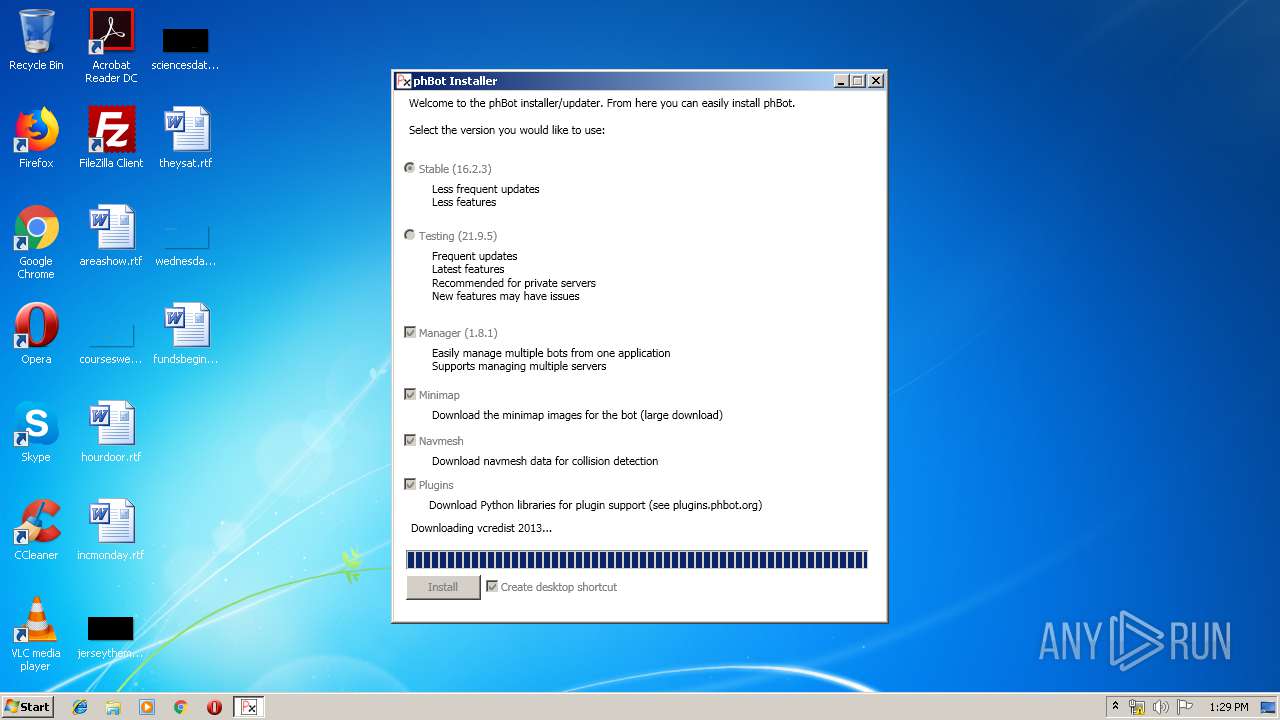
Loads dropped or rewritten executable
- vcredist_2013_x86.exe (PID: 1816)
Changes the autorun value in the registry
- vcredist_x86.exe (PID: 1792)
Application was dropped or rewritten from another process
- vcredist_x86.exe (PID: 1792)
- vcredist_2013_x86.exe (PID: 1816)
SUSPICIOUS
Reads Environment values
- f46980c6-afaa-4bf8-98f3-06290e26f613.exe (PID: 356)
Searches for installed software
- vcredist_x86.exe (PID: 1792)
Executable content was dropped or overwritten
- vcredist_x86.exe (PID: 1792)
- msiexec.exe (PID: 2640)
- vcredist_2013_x86.exe (PID: 1816)
- f46980c6-afaa-4bf8-98f3-06290e26f613.exe (PID: 356)
Creates files in the program directory
- vcredist_x86.exe (PID: 1792)
Creates a software uninstall entry
- vcredist_x86.exe (PID: 1792)
Creates files in the Windows directory
- msiexec.exe (PID: 2640)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 2828)
Changes settings of System certificates
- DrvInst.exe (PID: 2088)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 2088)
Searches for installed software
- msiexec.exe (PID: 2640)
Creates a software uninstall entry
- msiexec.exe (PID: 2640)
Reads settings of System Certificates
- f46980c6-afaa-4bf8-98f3-06290e26f613.exe (PID: 356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:29 09:37:22+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 41984 |
| InitializedDataSize: | 7168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc23e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.6.0 |
| ProductVersionNumber: | 1.0.6.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
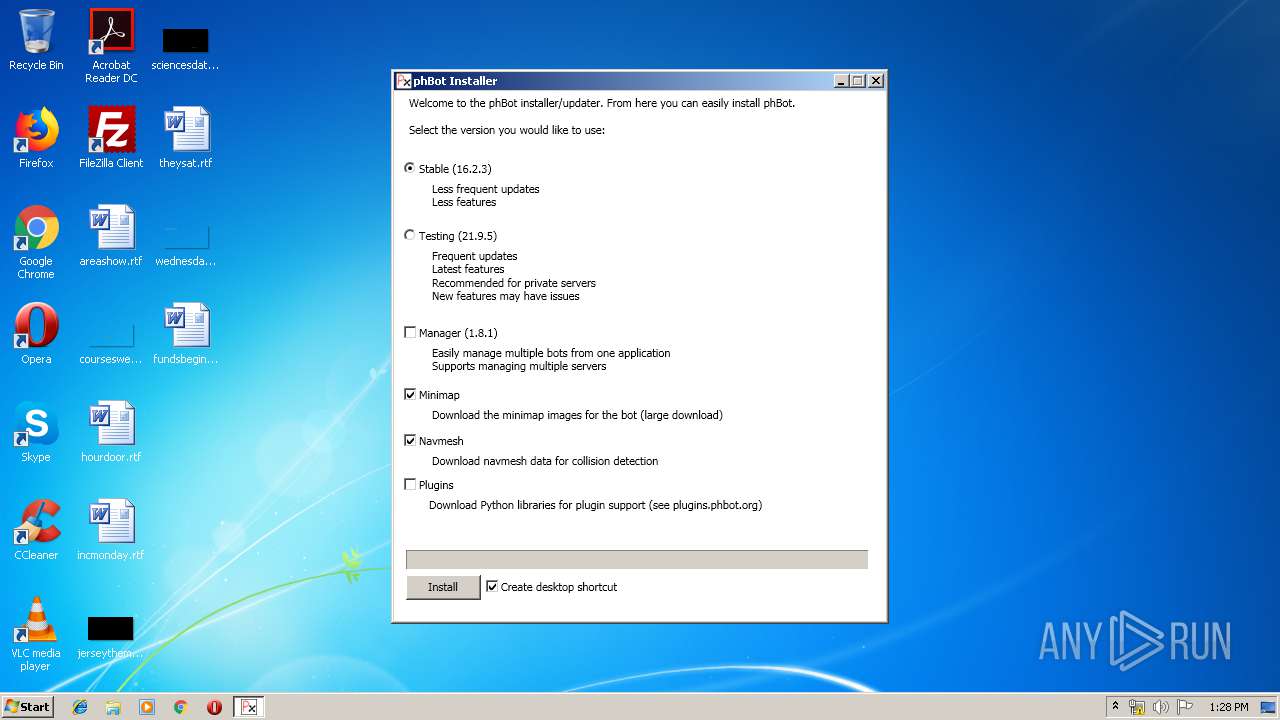
| Comments: | phBot Installer |
| CompanyName: | ProjectHax |
| FileDescription: | phBot Installer |
| FileVersion: | 1.0.6.0 |
| InternalName: | phBot Installer.exe |
| LegalCopyright: | Copyright © ProjectHax 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | phBot Installer.exe |
| ProductName: | phBot Installer |
| ProductVersion: | 1.0.6.0 |
| AssemblyVersion: | 1.0.6.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Mar-2019 08:37:22 |
| Debug artifacts: |
|
| Comments: | phBot Installer |
| CompanyName: | ProjectHax |
| FileDescription: | phBot Installer |
| FileVersion: | 1.0.6.0 |
| InternalName: | phBot Installer.exe |
| LegalCopyright: | Copyright © ProjectHax 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | phBot Installer.exe |
| ProductName: | phBot Installer |
| ProductVersion: | 1.0.6.0 |
| Assembly Version: | 1.0.6.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-Mar-2019 08:37:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0000A244 | 0x0000A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.64484 |
.rsrc | 0x0000E000 | 0x000019C4 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02731 |
.reloc | 0x00010000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00813 | 3137 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.81924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
41
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Users\admin\AppData\Local\Temp\f46980c6-afaa-4bf8-98f3-06290e26f613.exe" | C:\Users\admin\AppData\Local\Temp\f46980c6-afaa-4bf8-98f3-06290e26f613.exe | explorer.exe | ||||||||||||
User: admin Company: ProjectHax Integrity Level: MEDIUM Description: phBot Installer Exit code: 0 Version: 1.0.6.0 Modules
| |||||||||||||||
| 1792 | "C:\Users\admin\AppData\Local\Temp\{61087a79-ac85-455c-934d-1fa22cc64f36}\.be\vcredist_x86.exe" -q -burn.elevated BurnPipe.{4EE2FC90-71C6-41F7-9346-EA17EFD31475} {729C6144-B124-45EC-958F-C5E041FC00D9} 1816 | C:\Users\admin\AppData\Local\Temp\{61087a79-ac85-455c-934d-1fa22cc64f36}\.be\vcredist_x86.exe | vcredist_2013_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.40660 Exit code: 0 Version: 12.0.40660.0 Modules
| |||||||||||||||
| 1816 | "C:\Users\admin\AppData\Local\Temp\vcredist_2013_x86.exe" /install /passive /norestart | C:\Users\admin\AppData\Local\Temp\vcredist_2013_x86.exe | f46980c6-afaa-4bf8-98f3-06290e26f613.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.40660 Exit code: 0 Version: 12.0.40660.0 Modules
| |||||||||||||||
| 2088 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000005A8" "000003C4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2640 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2828 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 324
Read events
1 226
Write events
865
Delete events
233
Modification events
| (PID) Process: | (356) f46980c6-afaa-4bf8-98f3-06290e26f613.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: f46980c6-afaa-4bf8-98f3-06290e26f613.exe | |||
| (PID) Process: | (356) f46980c6-afaa-4bf8-98f3-06290e26f613.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\f46980c6-afaa-4bf8-98f3-06290e26f613_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (356) f46980c6-afaa-4bf8-98f3-06290e26f613.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\f46980c6-afaa-4bf8-98f3-06290e26f613_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (356) f46980c6-afaa-4bf8-98f3-06290e26f613.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\f46980c6-afaa-4bf8-98f3-06290e26f613_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (356) f46980c6-afaa-4bf8-98f3-06290e26f613.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\f46980c6-afaa-4bf8-98f3-06290e26f613_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (356) f46980c6-afaa-4bf8-98f3-06290e26f613.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\f46980c6-afaa-4bf8-98f3-06290e26f613_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (356) f46980c6-afaa-4bf8-98f3-06290e26f613.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\f46980c6-afaa-4bf8-98f3-06290e26f613_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (356) f46980c6-afaa-4bf8-98f3-06290e26f613.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\f46980c6-afaa-4bf8-98f3-06290e26f613_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (356) f46980c6-afaa-4bf8-98f3-06290e26f613.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\f46980c6-afaa-4bf8-98f3-06290e26f613_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (356) f46980c6-afaa-4bf8-98f3-06290e26f613.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\f46980c6-afaa-4bf8-98f3-06290e26f613_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
70
Suspicious files
25
Text files
74
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1792 | vcredist_x86.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1816 | vcredist_2013_x86.exe | C:\Users\admin\AppData\Local\Temp\{61087a79-ac85-455c-934d-1fa22cc64f36}\vcRuntimeMinimum_x86 | — | |
MD5:— | SHA256:— | |||
| 1816 | vcredist_2013_x86.exe | C:\Users\admin\AppData\Local\Temp\{61087a79-ac85-455c-934d-1fa22cc64f36}\cabB3E1576D1FEFBB979E13B1A5379E0B16 | — | |
MD5:— | SHA256:— | |||
| 1792 | vcredist_x86.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5cb08ba9-5e91-435f-bd02-ee62b09a4a04}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 2088 | DrvInst.exe | C:\Windows\INF\setupapi.ev1 | binary | |
MD5:— | SHA256:— | |||
| 1792 | vcredist_x86.exe | C:\ProgramData\Package Cache\{61087a79-ac85-455c-934d-1fa22cc64f36}\state.rsm | smt | |
MD5:— | SHA256:— | |||
| 1792 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\Cab2A6.tmp | — | |
MD5:— | SHA256:— | |||
| 1792 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\Tar2B7.tmp | — | |
MD5:— | SHA256:— | |||
| 2088 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
| 1792 | vcredist_x86.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1792 | vcredist_x86.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | der | 1.11 Kb | whitelisted |
1792 | vcredist_x86.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 555 b | whitelisted |
1792 | vcredist_x86.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
1792 | vcredist_x86.exe | GET | 200 | 2.21.38.54:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | FR | der | 813 b | whitelisted |
1792 | vcredist_x86.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1792 | vcredist_x86.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
356 | f46980c6-afaa-4bf8-98f3-06290e26f613.exe | 104.111.214.189:443 | download.microsoft.com | Akamai International B.V. | NL | whitelisted |
1792 | vcredist_x86.exe | 2.21.38.54:80 | www.microsoft.com | GTT Communications Inc. | FR | malicious |
356 | f46980c6-afaa-4bf8-98f3-06290e26f613.exe | 104.27.150.58:443 | cdn.projecthax.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.projecthax.com |
| suspicious |
download.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |