| download: | Minecraft%20Launcher.exe |
| Full analysis: | https://app.any.run/tasks/ff22f7f9-3eef-4567-b7db-69b631c8c60e |
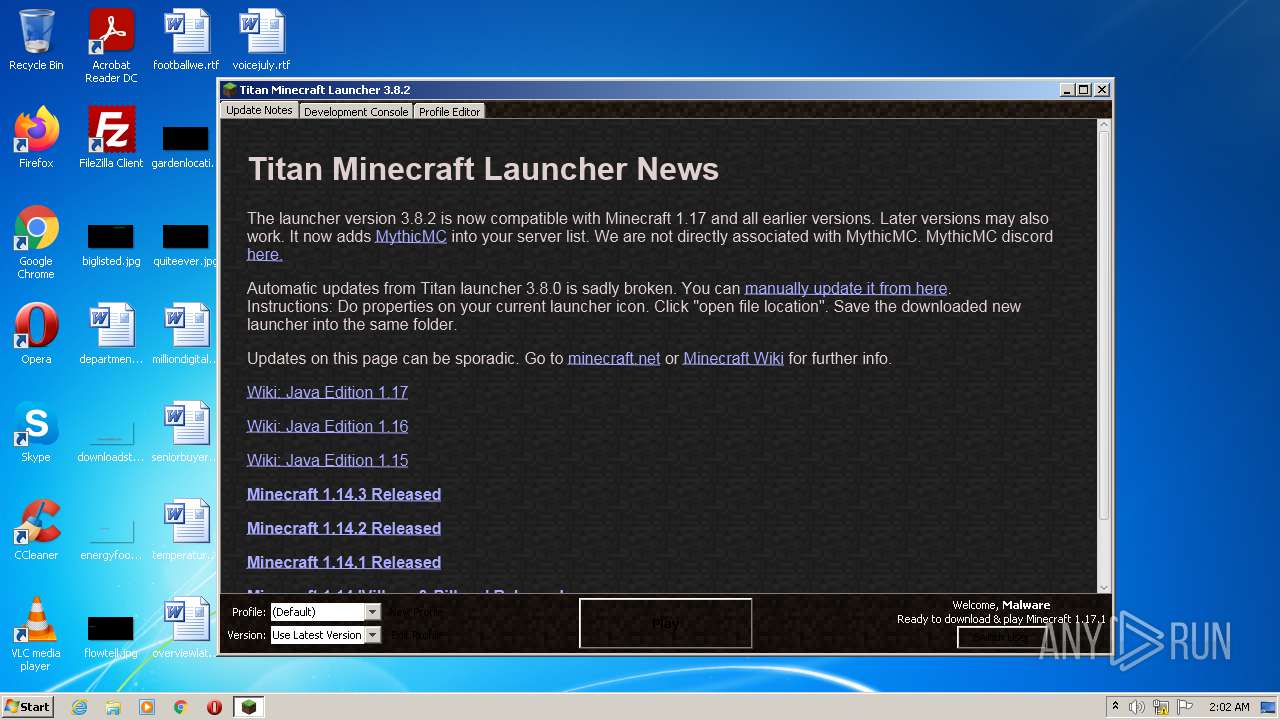
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2021, 01:01:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | C0F333E42E323F00CE7F98C5015898C2 |
| SHA1: | BE236E980BCE9287F105F9455D923482E2641DE0 |
| SHA256: | 8F5C385E556C34B006A5116691C489767AD3BA75604E0BE09146C4D7CAFD4314 |
| SSDEEP: | 98304:hxzL0s7PltQfNdNONNAX7Fvqkh/p1p8CTCjjOX4N:hRN9tQfNdyc7Fvqkdp8C2vp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Check for Java to be installed
- 0a11aaf0-ba91-4871-8928-9d7761b57bc0.exe (PID: 3920)
Checks supported languages
- javaw.exe (PID: 3868)
- 0a11aaf0-ba91-4871-8928-9d7761b57bc0.exe (PID: 3920)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 3868)
Creates files in the user directory
- javaw.exe (PID: 3868)
Creates files in the program directory
- javaw.exe (PID: 3868)
Executes JAVA applets
- 0a11aaf0-ba91-4871-8928-9d7761b57bc0.exe (PID: 3920)
Reads the computer name
- javaw.exe (PID: 3868)
INFO
Reads the computer name
- icacls.exe (PID: 336)
Checks supported languages
- icacls.exe (PID: 336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:08:20 18:31:12+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.26 |
| CodeSize: | 23040 |
| InitializedDataSize: | 25600 |
| UninitializedDataSize: | 36352 |
| EntryPoint: | 0x1590 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.8.2.0 |
| ProductVersionNumber: | 3.8.2.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
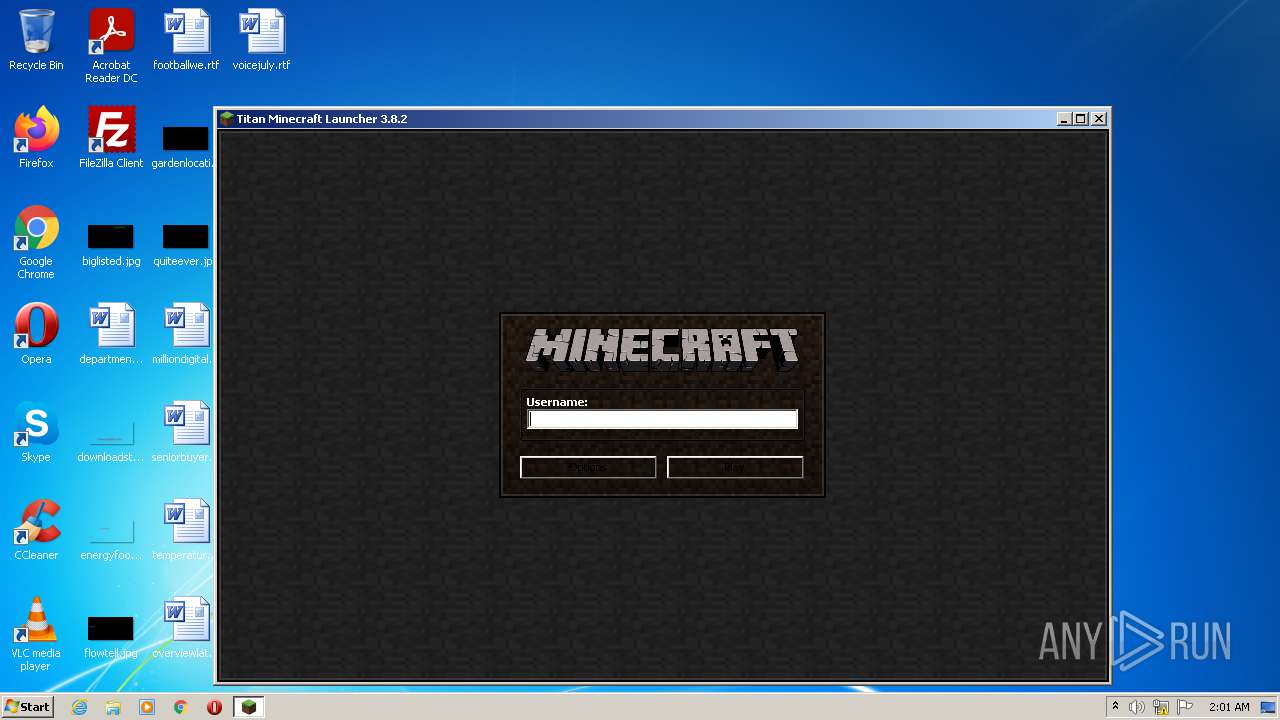
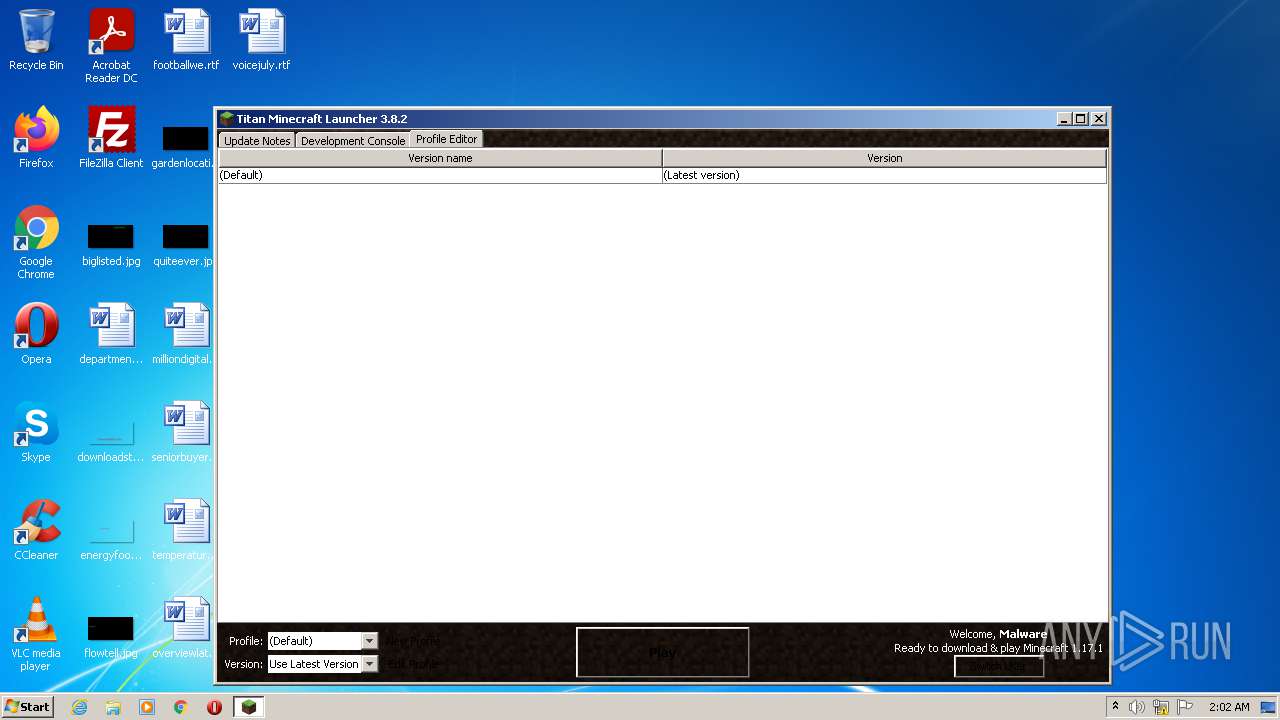
| CompanyName: | Titan Launcher |
| FileDescription: | 1.17 Minecraft Launcher |
| FileVersion: | 3.8.2 |
| InternalName: | Minecraft Launcher |
| LegalCopyright: | Titan Launcher |
| LegalTrademarks: | - |
| OriginalFileName: | Minecraft Launcher.exe |
| ProductName: | Titan Launcher |
| ProductVersion: | 3.8.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Aug-2021 16:31:12 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
| CompanyName: | Titan Launcher |
| FileDescription: | 1.17 Minecraft Launcher |
| FileVersion: | 3.8.2 |
| InternalName: | Minecraft Launcher |
| LegalCopyright: | Titan Launcher |
| LegalTrademarks: | - |
| OriginalFilename: | Minecraft Launcher.exe |
| ProductName: | Titan Launcher |
| ProductVersion: | 3.8.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 20-Aug-2021 16:31:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005970 | 0x00005A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.17662 |
.data | 0x00007000 | 0x00000010 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.11837 |
.rdata | 0x00008000 | 0x00000918 | 0x00000A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.27977 |
.eh_fram\x14\x11 | 0x00009000 | 0x00001114 | 0x00001200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.8242 |
.bss | 0x0000B000 | 0x00008DCC | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00014000 | 0x00000CC0 | 0x00000E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.91037 |
.CRT | 0x00015000 | 0x00000018 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.114463 |
.tls | 0x00016000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.231158 |
.rsrc | 0x00017000 | 0x00003270 | 0x00003400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.59048 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.81931 | 1114 | UNKNOWN | Process Default Language | RT_MANIFEST |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 3.78875 | 22 | UNKNOWN | Process Default Language | RT_RCDATA |
25 | 2 | 4 | UNKNOWN | Process Default Language | RT_RCDATA |
27 | 2 | 4 | UNKNOWN | Process Default Language | RT_RCDATA |
30 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
101 | 4.04307 | 50 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
advapi32.dll |
kernel32.dll |
msvcrt.dll |
shell32.dll |
user32.dll |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3868 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -Xms256m -Xmx512m -jar "C:\Users\admin\Downloads\0a11aaf0-ba91-4871-8928-9d7761b57bc0.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | 0a11aaf0-ba91-4871-8928-9d7761b57bc0.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3920 | "C:\Users\admin\Downloads\0a11aaf0-ba91-4871-8928-9d7761b57bc0.exe" | C:\Users\admin\Downloads\0a11aaf0-ba91-4871-8928-9d7761b57bc0.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Titan Launcher Integrity Level: MEDIUM Description: 1.17 Minecraft Launcher Exit code: 0 Version: 3.8.2 Modules
| |||||||||||||||
Total events
576
Read events
574
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3868) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
0
Suspicious files
0
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3868 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_profiles.json | text | |
MD5:— | SHA256:— | |||
| 3868 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 3868 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\servers.dat | image | |
MD5:009B730618EB922205FBB3E29BC81B9D | SHA256:517284D561F3B06BAE25F16C36B4FFDDDFC6C1234FBC4943C268EAF06D0F6403 | |||
| 3868 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio1859199886570990150.tmp | image | |
MD5:D141CC8E71A3351F1AACB88A74B45FA4 | SHA256:2788675E062E1111EAD50A9A05971A7C11FE6246A89F571CF9F59ED68C72BB17 | |||
| 3868 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio6660125406850927753.tmp | image | |
MD5:D141CC8E71A3351F1AACB88A74B45FA4 | SHA256:2788675E062E1111EAD50A9A05971A7C11FE6246A89F571CF9F59ED68C72BB17 | |||
| 3868 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\minecraft launcher\options.json | text | |
MD5:B9CF32949297936C8EDE369A16865831 | SHA256:4420CB57C8D4ADB8D867534F258D16D5BB7621D04A2C710CC94CBCA9F8D4E7C1 | |||
| 3868 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio8304223160446220073.tmp | image | |
MD5:E7E38B97A9FE7E0BB219AAF28BB750B7 | SHA256:99EDDE5742D3F824EB8F1EA03CCBDB969A04F94235CAE509644A442F8EBB039E | |||
| 3868 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio1999531417570275263.tmp | image | |
MD5:91D3708A258E5F789E2AE888CF68F66F | SHA256:0AD2672561C2BA4E86C38702682BD84D720351F3E5C4CA232F0043AAB7FA8B28 | |||
| 3868 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio3486625777763124480.tmp | image | |
MD5:D141CC8E71A3351F1AACB88A74B45FA4 | SHA256:2788675E062E1111EAD50A9A05971A7C11FE6246A89F571CF9F59ED68C72BB17 | |||
| 3868 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\minecraft launcher\Minecraft Update News.htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
7
DNS requests
5
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
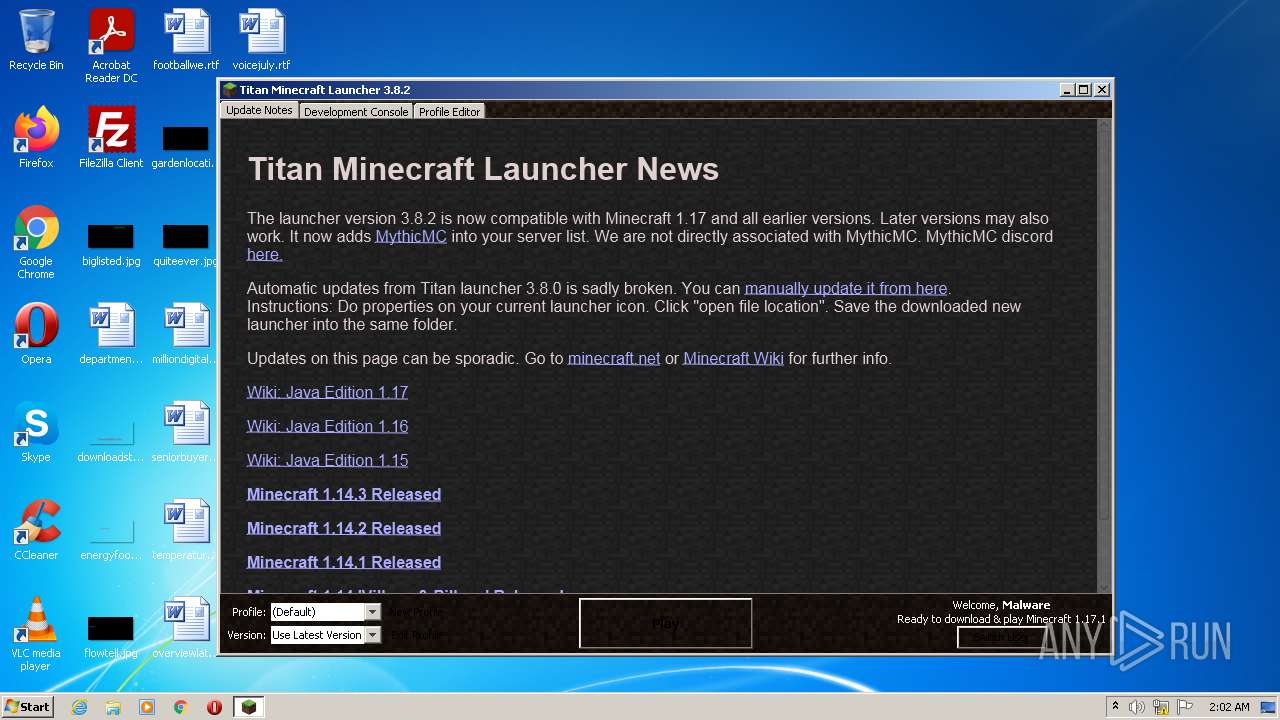
3868 | javaw.exe | GET | 404 | 104.21.50.65:80 | http://titan.mythicmc.org/LauncherUpdate/version.txt | US | html | 280 b | malicious |
3868 | javaw.exe | GET | 200 | 198.54.115.64:80 | http://teamextrememc.com/failsafe/failsafe.txt | US | text | 257 b | malicious |
3868 | javaw.exe | GET | 200 | 198.54.115.64:80 | http://teamextrememc.com/failsafe/Minecraft%20Update%20News.htm | US | html | 4.47 Kb | malicious |
3868 | javaw.exe | GET | 200 | 198.54.115.64:80 | http://teamextrememc.com/failsafe/Minecraft%20Update%20News.htm | US | html | 4.47 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | — | US | whitelisted |
3868 | javaw.exe | 104.21.50.65:80 | titan.mythicmc.org | Cloudflare Inc | US | suspicious |
3868 | javaw.exe | 198.54.115.64:80 | teamextrememc.com | Namecheap, Inc. | US | malicious |
3868 | javaw.exe | 192.0.77.40:443 | assets.tumblr.com | Automattic, Inc | US | suspicious |
3868 | javaw.exe | 143.204.93.135:443 | launchermeta.mojang.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
titan.mythicmc.org |
| malicious |
teamextrememc.com |
| malicious |
launchermeta.mojang.com |
| whitelisted |
assets.tumblr.com |
| whitelisted |
static.tumblr.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3868 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
3868 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |