| File name: | VLC media player 64 Bit - CHIP-Installer.exe |
| Full analysis: | https://app.any.run/tasks/b3d14aca-2687-48c6-b3e8-eebc7dbbd001 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 18:27:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 22722279712CE6E7896AB7D5AB1E6710 |
| SHA1: | 674FB44A79609F40681B9A9896A566FE231FE221 |
| SHA256: | 8F4E34A4150B4EDFA357A6DC9D3E7F5D8632E9B84B7082E52FDF71EBDB997E31 |
| SSDEEP: | 24576:fq5TfcdHj4fmbpD2qY24Hywe4CaeRzs1Ay6z5R03+dT3yozyg0:fUTsam9xgHywe4C/s10dTy |
MALICIOUS
Application was dropped or rewritten from another process
- dmr_72.exe (PID: 3532)
SUSPICIOUS
Executable content was dropped or overwritten
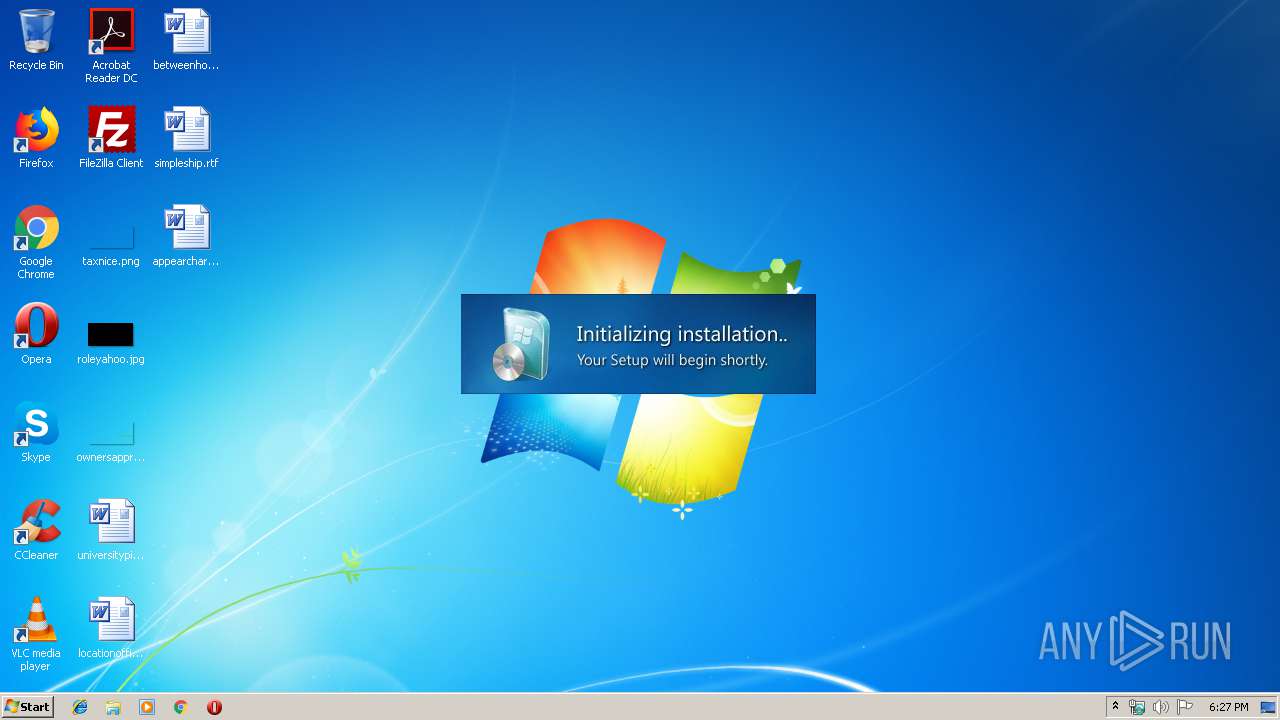
- VLC media player 64 Bit - CHIP-Installer.exe (PID: 748)
Creates files in the user directory
- dmr_72.exe (PID: 3532)
Starts Internet Explorer
- dmr_72.exe (PID: 3532)
INFO
Creates files in the user directory
- opera.exe (PID: 4068)
Changes internet zones settings
- iexplore.exe (PID: 2300)
Manual execution by user
- opera.exe (PID: 4068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (30.7) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (30.1) |
| .exe | | | Win32 EXE Yoda's Crypter (29.5) |
| .exe | | | Win32 Executable (generic) (5) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:12 13:13:10+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 344064 |
| InitializedDataSize: | 1007616 |
| UninitializedDataSize: | 1536000 |
| EntryPoint: | 0x1cb8d0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.11.0.3 |
| ProductVersionNumber: | 2.11.0.3 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | German |
| CharacterSet: | Unicode |
| FileVersion: | 2.11.0.3 |
| Comments: | CHIP Secured Installer |
| FileDescription: | CHIP Secured Installer |
| ProductVersion: | 2.11.0.3 |
| LegalCopyright: | Copyright © 2020 Chip Digital GmbH |
| CompanyName: | CHIP Digital GmbH |
| InternalName: | CHIP Secured Installer |
| ProductName: | CHIP Secured Installer |
| OriginalFileName: | CHIP Secured Installer |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Dec-2019 12:13:10 |
| Detected languages: |
|
| FileVersion: | 2.11.0.3 |
| Comments: | CHIP Secured Installer |
| FileDescription: | CHIP Secured Installer |
| ProductVersion: | 2.11.0.3 |
| LegalCopyright: | Copyright © 2020 Chip Digital GmbH |
| CompanyName: | CHIP Digital GmbH |
| InternalName: | CHIP Secured Installer |
| ProductName: | CHIP Secured Installer |
| OriginalFilename: | CHIP Secured Installer |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 12-Dec-2019 12:13:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00177000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00178000 | 0x00054000 | 0x00053C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93599 |
.rsrc | 0x001CC000 | 0x000F6000 | 0x000F6000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.405 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.32366 | 1444 | Latin 1 / Western European | German - Germany | RT_MANIFEST |
4 | 3.75291 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 3.26322 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
12 | 3.25812 | 1126 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
99 | 2.0815 | 20 | Latin 1 / Western European | English - United Kingdom | RT_GROUP_ICON |
166 | 2.68292 | 80 | Latin 1 / Western European | English - United Kingdom | RT_MENU |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
41
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | "C:\Users\admin\AppData\Local\Temp\VLC media player 64 Bit - CHIP-Installer.exe" | C:\Users\admin\AppData\Local\Temp\VLC media player 64 Bit - CHIP-Installer.exe | explorer.exe | ||||||||||||
User: admin Company: CHIP Digital GmbH Integrity Level: HIGH Description: CHIP Secured Installer Exit code: 0 Version: 2.11.0.3 Modules
| |||||||||||||||
| 1044 | "C:\Users\admin\AppData\Local\Temp\VLC media player 64 Bit - CHIP-Installer.exe" | C:\Users\admin\AppData\Local\Temp\VLC media player 64 Bit - CHIP-Installer.exe | — | explorer.exe | |||||||||||
User: admin Company: CHIP Digital GmbH Integrity Level: MEDIUM Description: CHIP Secured Installer Exit code: 3221226540 Version: 2.11.0.3 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | dmr_72.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3532 | "C:\Users\admin\AppData\Local\Temp\DMR\dmr_72.exe" -install -54504926 -chipderedesign -1348fada33d34b9486c1f60742a1a7b9 - -BLUB2 -vdonajkgqxzxmxkd -748 | C:\Users\admin\AppData\Local\Temp\DMR\dmr_72.exe | VLC media player 64 Bit - CHIP-Installer.exe | ||||||||||||
User: admin Company: Chip Digital GmbH Integrity Level: HIGH Description: CHIP Secured Installer Exit code: 0 Version: 2.11.0.3 Modules
| |||||||||||||||
| 3656 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2300 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4068 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
871
Read events
752
Write events
119
Delete events
0
Modification events
| (PID) Process: | (748) VLC media player 64 Bit - CHIP-Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (748) VLC media player 64 Bit - CHIP-Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3532) dmr_72.exe | Key: | HKEY_CURRENT_USER\Software\OCS |
| Operation: | write | Name: | CID |
Value: d7a76d48-7fdf-42a7-9eec-529d82c170e8 | |||
| (PID) Process: | (3532) dmr_72.exe | Key: | HKEY_CURRENT_USER\Software\OCS |
| Operation: | write | Name: | PID |
Value: chipderedesign | |||
| (PID) Process: | (3532) dmr_72.exe | Key: | HKEY_CURRENT_USER\Software\OCS |
| Operation: | write | Name: | lastPID |
Value: chipderedesign | |||
| (PID) Process: | (3532) dmr_72.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dmr_72_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3532) dmr_72.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dmr_72_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3532) dmr_72.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dmr_72_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3532) dmr_72.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dmr_72_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3532) dmr_72.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dmr_72_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
1
Suspicious files
33
Text files
11
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4068 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprF547.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprF587.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\W7Q46E3ZEC265WJHCT1O.temp | — | |
MD5:— | SHA256:— | |||
| 4068 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprFE81.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprFE82.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprFE83.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 748 | VLC media player 64 Bit - CHIP-Installer.exe | C:\Users\admin\AppData\Local\Temp\DMR\dmr_72.exe | executable | |
MD5:DFEA6E8D3B44F790ADB0C0FF067B5CB9 | SHA256:7F1D111345D073C98096EF34D373CD7080914616E749A3F043168F054C6D3FF2 | |||
| 4068 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opcacrt6.dat | binary | |
MD5:59761E989F564F76A3A4B778DB7ABCF1 | SHA256:AF879942D234D85C0CE75921DBDDA50E2F6D135BD961F259106131751359052B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
9
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3656 | iexplore.exe | GET | 301 | 2.16.181.41:80 | http://www.chip.de/secured-installer-support/feedback?t=&cid=&pid=&pg=57656C636F6D65&data=26536574757049443D26436C69656E7449443D26436F6E74656E7449443D26506172746E657249443D26536F7572636549443D267374724F533D3635373237323646373232303639364532303637363537343530363137323631364436353734363537323733343636463732344437333637343236463738323833303239264455423D26737472416E746976697275733D36353732373236463732323036393645323036373635373435303631373236313644363537343635373237333436364637323444373336373432364637383238333132392665784D73673D35353645363136323643363532303734364632303633364636453645363536333734323037343646323037343638363532303732363536443646373436353230373336353732373636353732264572726F72506C6163653D34373635373434383734373437303537363536323532363537313735363537333734 | unknown | — | — | whitelisted |
4068 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
2300 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3532 | dmr_72.exe | 148.251.213.132:80 | api2.chip-secured-download.de | Hetzner Online GmbH | DE | malicious |
4068 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
4068 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2300 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3656 | iexplore.exe | 2.16.181.41:80 | www.chip.de | Akamai International B.V. | — | whitelisted |
3656 | iexplore.exe | 2.16.181.41:443 | www.chip.de | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api2.chip-secured-download.de |
| unknown |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
www.chip.de |
| whitelisted |
www.bing.com |
| whitelisted |