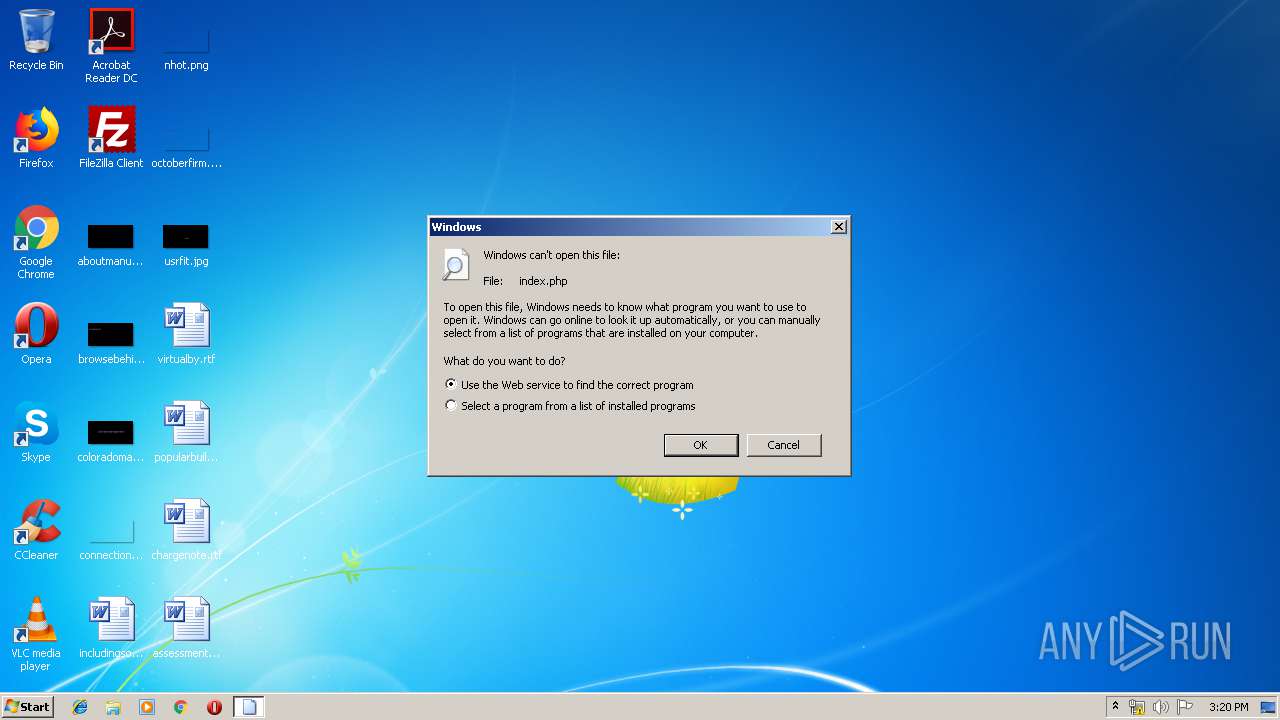
| download: | index.php |
| Full analysis: | https://app.any.run/tasks/4d4ef2c2-3c12-4e43-ba70-0c40be359301 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 14:20:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with CRLF line terminators |
| MD5: | D307300D0A74DC01B6F798FCBAAB3626 |
| SHA1: | AEA07CF2084DEC8322424E4118052733BBECFD1E |
| SHA256: | 8F44FE7BA0E0CE5E12BCC992661CC7A06ED55A5AAB0D64359B7A6E2145DA8C55 |
| SSDEEP: | 96:NvFzOSydpB7fibfyHmVcc9Vcc8ab/CBxnrwp:NkHNMfyHojVb/CBlrK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2716)
INFO
Application launched itself
- chrome.exe (PID: 2716)
Reads settings of System Certificates
- chrome.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=windows-1252 |
|---|---|
| Title: | DHL | Tracking System |
Total processes
49
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\index.php | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15471082926861265711 --mojo-platform-channel-handle=3600 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9545731533211567086 --mojo-platform-channel-handle=3508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f3a0f18,0x6f3a0f28,0x6f3a0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14863610732390458916 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14863610732390458916 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2612 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --service-pipe-token=13998788219825947019 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13998788219825947019 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2022053733350711005 --mojo-platform-channel-handle=976 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5001495908611839817 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5001495908611839817 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14470050418621999941 --mojo-platform-channel-handle=2628 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10010965388923036788 --mojo-platform-channel-handle=3604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
581
Read events
484
Write events
92
Delete events
5
Modification events
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2716-13199811678739750 |
Value: 259 | |||
| (PID) Process: | (2716) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
36
Text files
147
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a19155e7-7188-47d6-8478-79202dcfbc1e.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
29
DNS requests
13
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2556 | chrome.exe | GET | 301 | 104.108.68.232:80 | http://www.dhl.com/img/favicon.gif | NL | — | — | whitelisted |
2556 | chrome.exe | GET | 302 | 185.244.39.238:80 | http://cartoozmare.com/dhl/dhl/index.php | unknown | — | — | malicious |
2556 | chrome.exe | GET | 200 | 185.244.39.238:80 | http://cartoozmare.com/dhl/dhl/p2rgw0n6gbt53ls87jf5q47h.php?rand=13InboxLightaspxn.1774256418&fid.4.1252899642&fid=1&fav.1&rand.13InboxLight.aspxn.1774256418&fid.1252899642&fid.1&fav.1&email=&.rand=13InboxLight.aspx?n=1774256418&fid=4 | unknown | html | 4.71 Kb | malicious |
2556 | chrome.exe | POST | 302 | 185.244.39.238:80 | http://cartoozmare.com/dhl/dhl/post.php | unknown | — | — | malicious |
2556 | chrome.exe | POST | — | 185.244.39.238:80 | http://cartoozmare.com/dhl/dhl/post.php | unknown | — | — | malicious |
2556 | chrome.exe | POST | 302 | 185.244.39.238:80 | http://cartoozmare.com/dhl/dhl/post2.php | unknown | — | — | malicious |
2556 | chrome.exe | GET | 200 | 185.244.39.238:80 | http://cartoozmare.com/dhl/dhl/confirm.php | unknown | html | 5.74 Kb | malicious |
2556 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
2556 | chrome.exe | GET | 200 | 185.244.39.238:80 | http://cartoozmare.com/dhl/dhl/index2.php?email=avc@gmail.com | unknown | html | 4.83 Kb | malicious |
2556 | chrome.exe | GET | 200 | 185.244.39.238:80 | http://cartoozmare.com/dhl/dhl/images/alert-icon-red-md.png | unknown | image | 38.2 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2556 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.16.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 173.194.129.231:80 | r2---sn-q0c7rn76.gvt1.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.16.142:443 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
cartoozmare.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2556 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |
2556 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2556 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2556 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
9 ETPRO signatures available at the full report