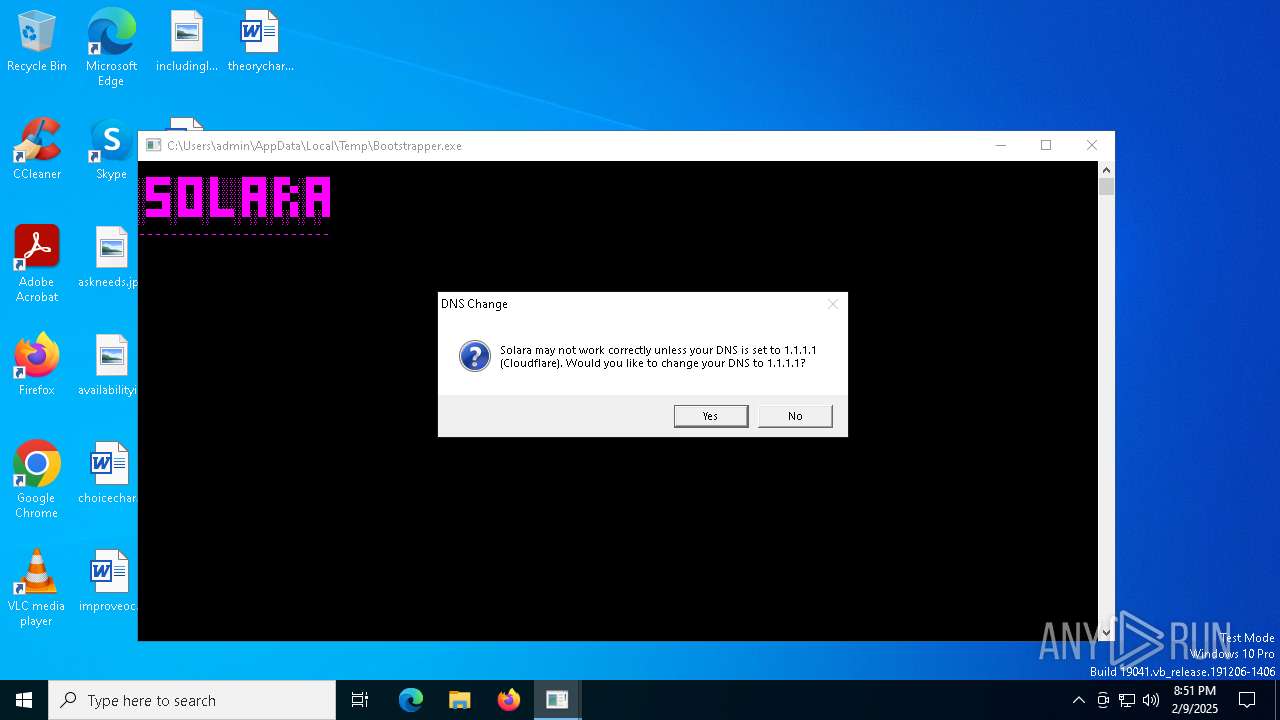
| File name: | Bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/adf285af-e133-41fc-869b-22c4eb50e001 |
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2025, 20:51:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 02C70D9D6696950C198DB93B7F6A835E |
| SHA1: | 30231A467A49CC37768EEA0F55F4BEA1CBFB48E2 |
| SHA256: | 8F2E28588F2303BD8D7A9B0C3FF6A9CB16FA93F8DDC9C5E0666A8C12D6880EE3 |
| SSDEEP: | 6144:tXxndGsQZDAvUHFLRSZ3e82Zavp/ijHrGEW1NhVhOQNaDffKTghOpDozwKdVuaQ:tf3gAvUlLvocaPhOmTghOpDkwKdw |
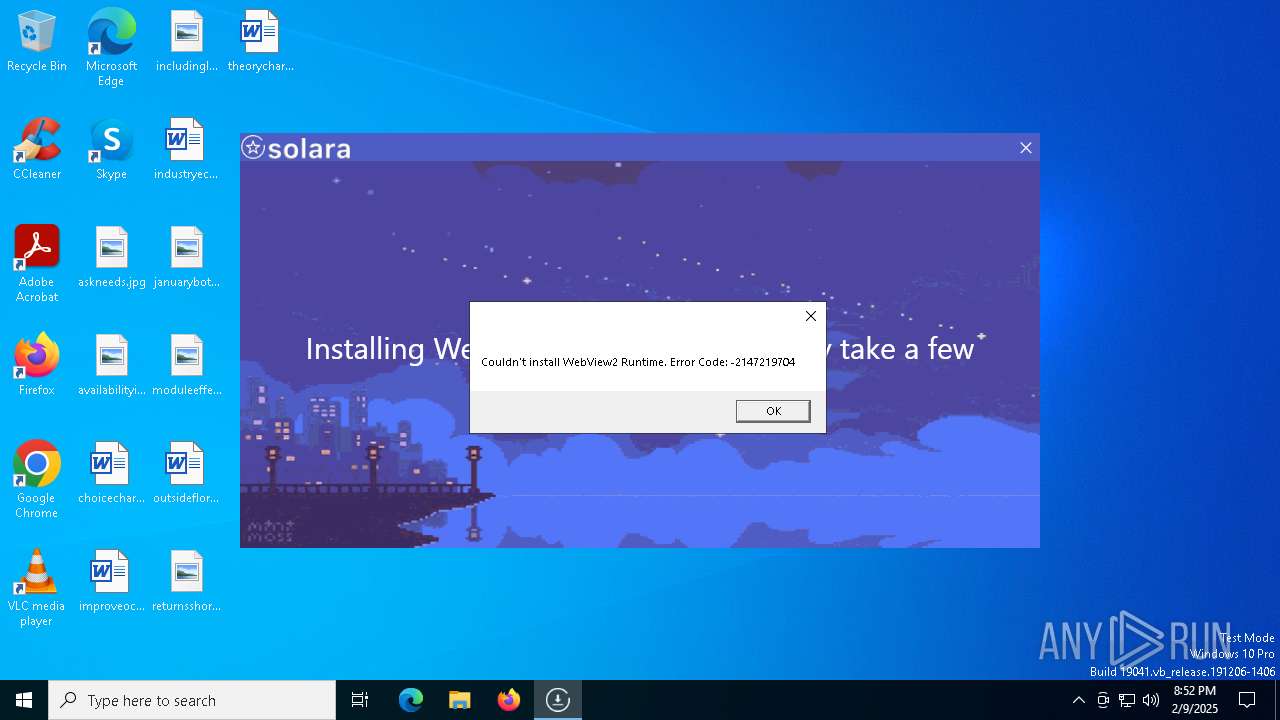
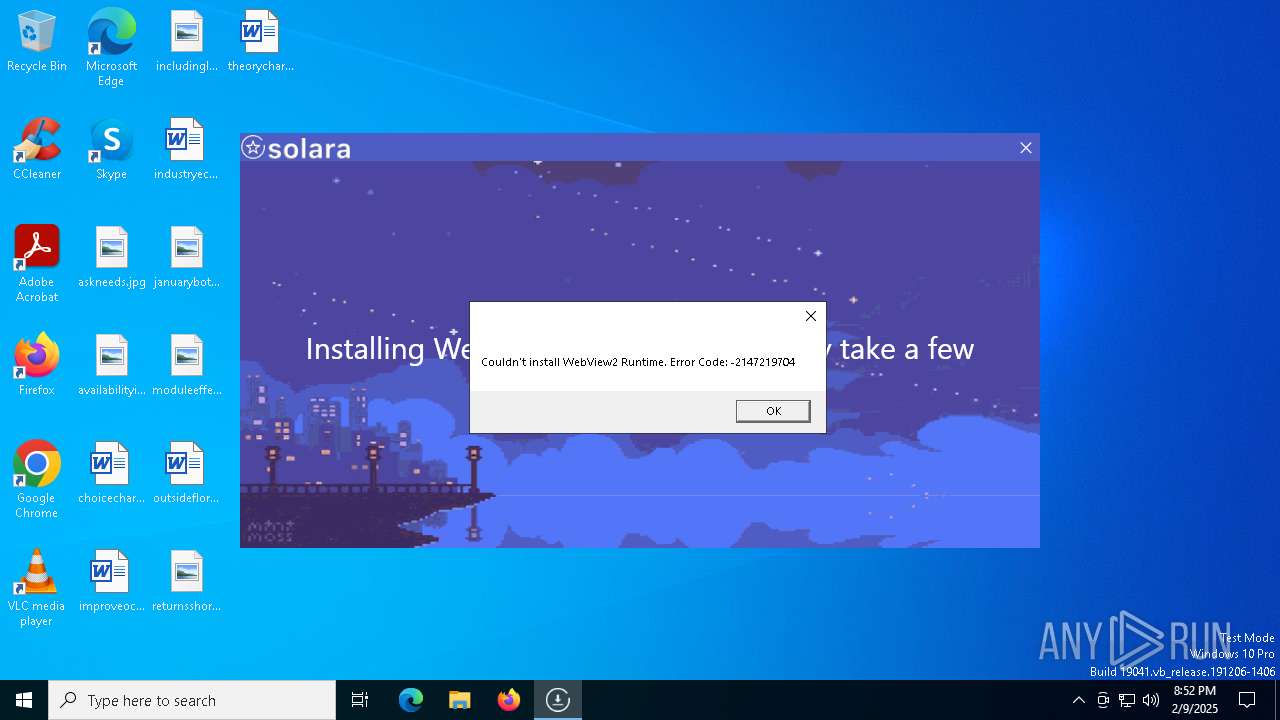
MALICIOUS
Adds path to the Windows Defender exclusion list
- BootstrapperV2.19.exe (PID: 4932)
SUSPICIOUS
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 6544)
Uses WMIC.EXE to obtain information about the network interface controller
- cmd.exe (PID: 6900)
Starts CMD.EXE for commands execution
- Bootstrapper.exe (PID: 6332)
Reads security settings of Internet Explorer
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
- MicrosoftEdgeUpdate.exe (PID: 6320)
- Solara.exe (PID: 5300)
Executable content was dropped or overwritten
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
- MicrosoftEdgeWebview2Setup.exe (PID: 1612)
Reads the date of Windows installation
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
Script adds exclusion path to Windows Defender
- BootstrapperV2.19.exe (PID: 4932)
Query Microsoft Defender preferences
- BootstrapperV2.19.exe (PID: 4932)
Starts POWERSHELL.EXE for commands execution
- BootstrapperV2.19.exe (PID: 4932)
Process drops legitimate windows executable
- BootstrapperV2.19.exe (PID: 4932)
- MicrosoftEdgeWebview2Setup.exe (PID: 1612)
- MicrosoftEdgeUpdate.exe (PID: 6320)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 1612)
- MicrosoftEdgeUpdate.exe (PID: 6320)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 6320)
The process drops C-runtime libraries
- BootstrapperV2.19.exe (PID: 4932)
Reads the BIOS version
- Solara.exe (PID: 5300)
INFO
Checks supported languages
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
- MicrosoftEdgeWebview2Setup.exe (PID: 1612)
- MicrosoftEdgeUpdate.exe (PID: 6320)
- Solara.exe (PID: 5300)
Reads the computer name
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
- MicrosoftEdgeUpdate.exe (PID: 6320)
- Solara.exe (PID: 5300)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6956)
Disables trace logs
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
- Solara.exe (PID: 5300)
Reads the machine GUID from the registry
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
- Solara.exe (PID: 5300)
Checks proxy server information
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
- MicrosoftEdgeUpdate.exe (PID: 6320)
- wermgr.exe (PID: 7080)
- Solara.exe (PID: 5300)
Reads Environment values
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
- MicrosoftEdgeUpdate.exe (PID: 6320)
- Solara.exe (PID: 5300)
Create files in a temporary directory
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
Reads the software policy settings
- Bootstrapper.exe (PID: 6332)
- BootstrapperV2.19.exe (PID: 4932)
- MicrosoftEdgeUpdate.exe (PID: 6320)
- wermgr.exe (PID: 7080)
- Solara.exe (PID: 5300)
Process checks computer location settings
- Bootstrapper.exe (PID: 6332)
- MicrosoftEdgeUpdate.exe (PID: 6320)
- BootstrapperV2.19.exe (PID: 4932)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2436)
- powershell.exe (PID: 6732)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6732)
The sample compiled with english language support
- BootstrapperV2.19.exe (PID: 4932)
- MicrosoftEdgeWebview2Setup.exe (PID: 1612)
- MicrosoftEdgeUpdate.exe (PID: 6320)
Creates files in the program directory
- BootstrapperV2.19.exe (PID: 4932)
- MicrosoftEdgeWebview2Setup.exe (PID: 1612)
Process checks whether UAC notifications are on
- Solara.exe (PID: 5300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:13 21:07:39+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 816640 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc948a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | SolaraBootstrapper |
| FileVersion: | 1.0.0.0 |
| InternalName: | SolaraBootstrapper.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | SolaraBootstrapper.exe |
| ProductName: | SolaraBootstrapper |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
150
Monitored processes
18
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1612 | "C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe" /silent /install | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | BootstrapperV2.19.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Setup Exit code: 2147747592 Version: 1.3.195.43 Modules
| |||||||||||||||
| 2436 | "powershell" -Command "Get-MpPreference | Select-Object -ExpandProperty ExclusionPath" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | BootstrapperV2.19.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4932 | "C:\Users\admin\AppData\Local\Temp\BootstrapperV2.19.exe" --oldBootstrapper "C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe" --isUpdate true | C:\Users\admin\AppData\Local\Temp\BootstrapperV2.19.exe | Bootstrapper.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Bootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
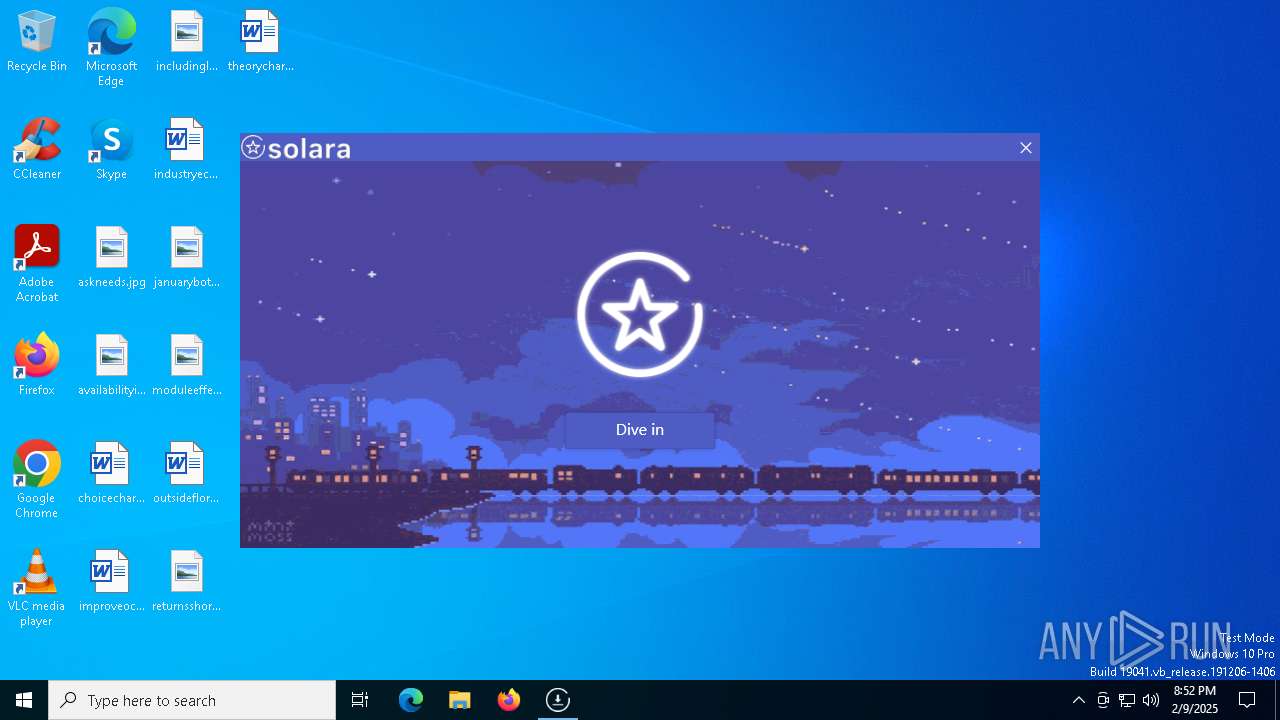
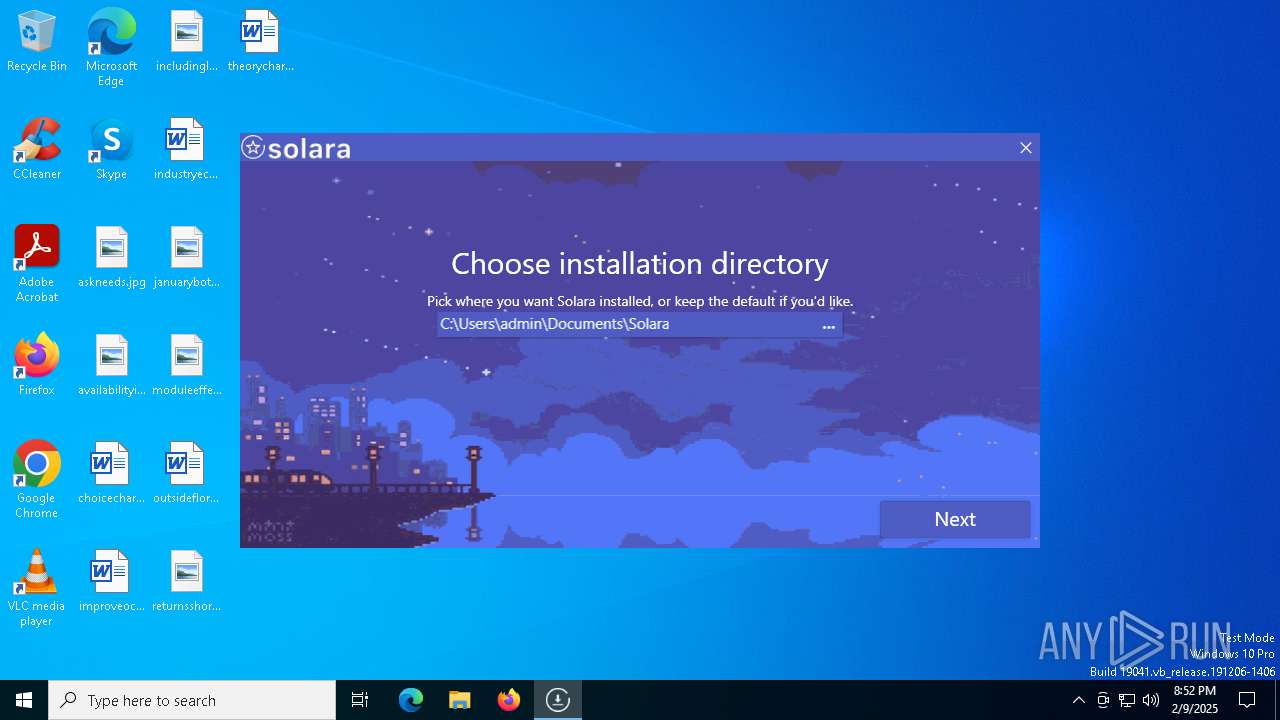
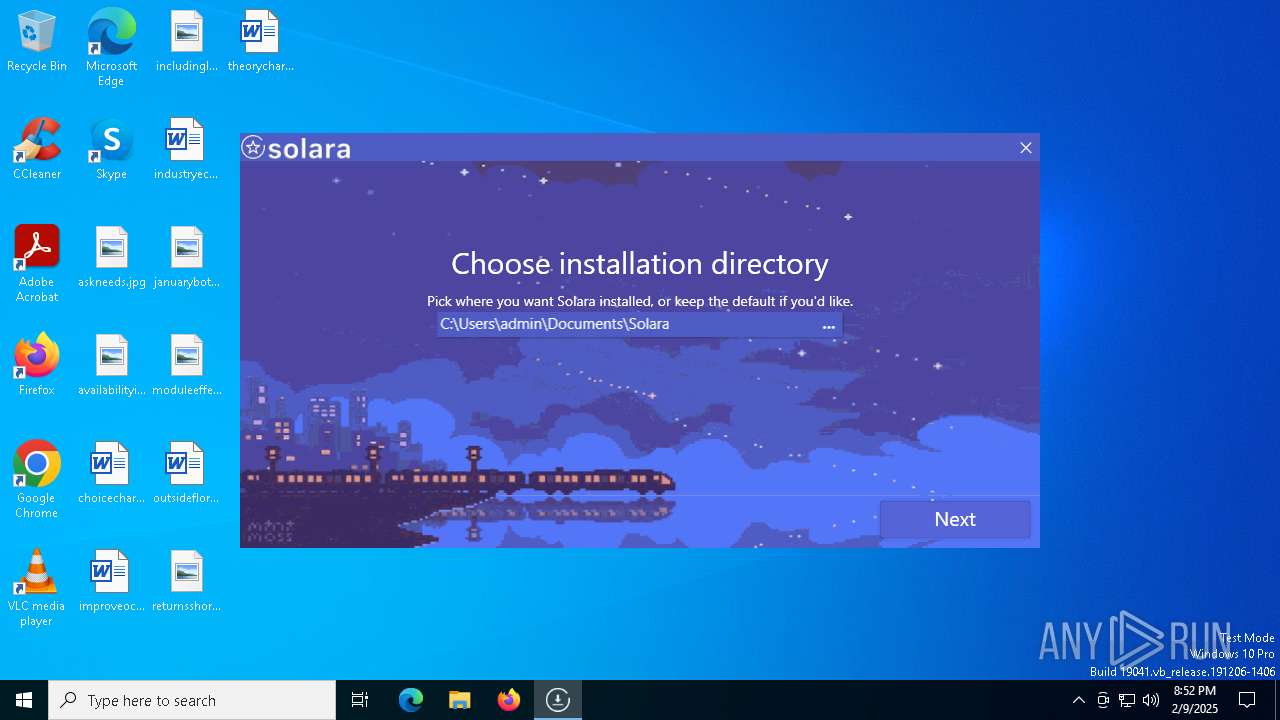
| 5300 | "C:\Users\admin\Documents\Solara\Solara.exe" --bootstrapperPath "C:\Users\admin\AppData\Local\Temp" | C:\Users\admin\Documents\Solara\Solara.exe | BootstrapperV2.19.exe | ||||||||||||
User: admin Company: CMD Softworks Integrity Level: HIGH Description: Solara V3 Version: 3.0.0.0 Modules
| |||||||||||||||
| 6160 | "C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SolaraBootstrapper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6320 | "C:\Program Files (x86)\Microsoft\Temp\EU156B.tmp\MicrosoftEdgeUpdate.exe" /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Program Files (x86)\Microsoft\Temp\EU156B.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Exit code: 2147747592 Version: 1.3.195.43 Modules
| |||||||||||||||
| 6332 | "C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SolaraBootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6344 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6544 | "cmd" /c ipconfig /all | C:\Windows\System32\cmd.exe | — | Bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 686
Read events
23 573
Write events
110
Delete events
3
Modification events
| (PID) Process: | (6332) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6332) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6332) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6332) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6332) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6332) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6332) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6332) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6332) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6332) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
212
Suspicious files
16
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6732 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nbu40lxn.5c1.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1612 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EU156B.tmp\MicrosoftEdgeComRegisterShellARM64.exe | executable | |
MD5:8F7C44E937ECC243D05EAB5BB218440B | SHA256:BC3CDD57A892CE1841787061E23E526AD46575460CD66C1DC6DCF0F811563D59 | |||
| 4932 | BootstrapperV2.19.exe | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | executable | |
MD5:B49D269A231BCF719D6DE10F6DCF0692 | SHA256:BDE514014B95C447301D9060A221EFB439C3C1F5DB53415F080D4419DB75B27E | |||
| 6332 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\DISCORD | binary | |
MD5:43151972F36B756BB89CE08B7B8E1023 | SHA256:ABE3C8428FA463FEF24F4BD5280910E5C2CCB7ABCCE86E9EBBD93C6538DC0479 | |||
| 1612 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EU156B.tmp\msedgeupdate.dll | executable | |
MD5:40CD707DD3011A9845FF9C42256EA7E3 | SHA256:9F4C7072716E0BE1BE08207A7024A5E41162E288E677D805BE8E5469A8BD4909 | |||
| 1612 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EU156B.tmp\MicrosoftEdgeUpdateBroker.exe | executable | |
MD5:E5DE2B67B2B629859949DB28D614FAAB | SHA256:8C86A415557DA686214675A02A94964F07C2166C811C61542776F4BF920555CA | |||
| 1612 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EU156B.tmp\psmachine_64.dll | executable | |
MD5:886D71AA7EA1C34644AA759FB5A09B5F | SHA256:95D1B924759B36FBD2A20682E919392D64DC8C1B153F909F921DA7E57825A04C | |||
| 2436 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_puc2jhhu.0eg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1612 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EU156B.tmp\MicrosoftEdgeUpdateComRegisterShell64.exe | executable | |
MD5:714C34FE6098B45A3303C611C4323EAE | SHA256:FBF495968C4A385FF0790E6B65D26610EF917A2B36A5387EFF7AE79D7A980AC5 | |||
| 1612 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EU156B.tmp\MicrosoftEdgeUpdateOnDemand.exe | executable | |
MD5:A8652F75AD0579D14FB45BB5A6C98D23 | SHA256:E41E92F37BFDE77799E947FCE1D6E9378B4C53FB4B86905F64622691C30AD1E5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
53
DNS requests
30
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2736 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2736 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
836 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
836 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6444 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7080 | wermgr.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2736 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2736 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.21.65.132:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1612 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
getsolara.dev |
| malicious |
819a7369.solaraweb-alj.pages.dev |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
6332 | Bootstrapper.exe | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |