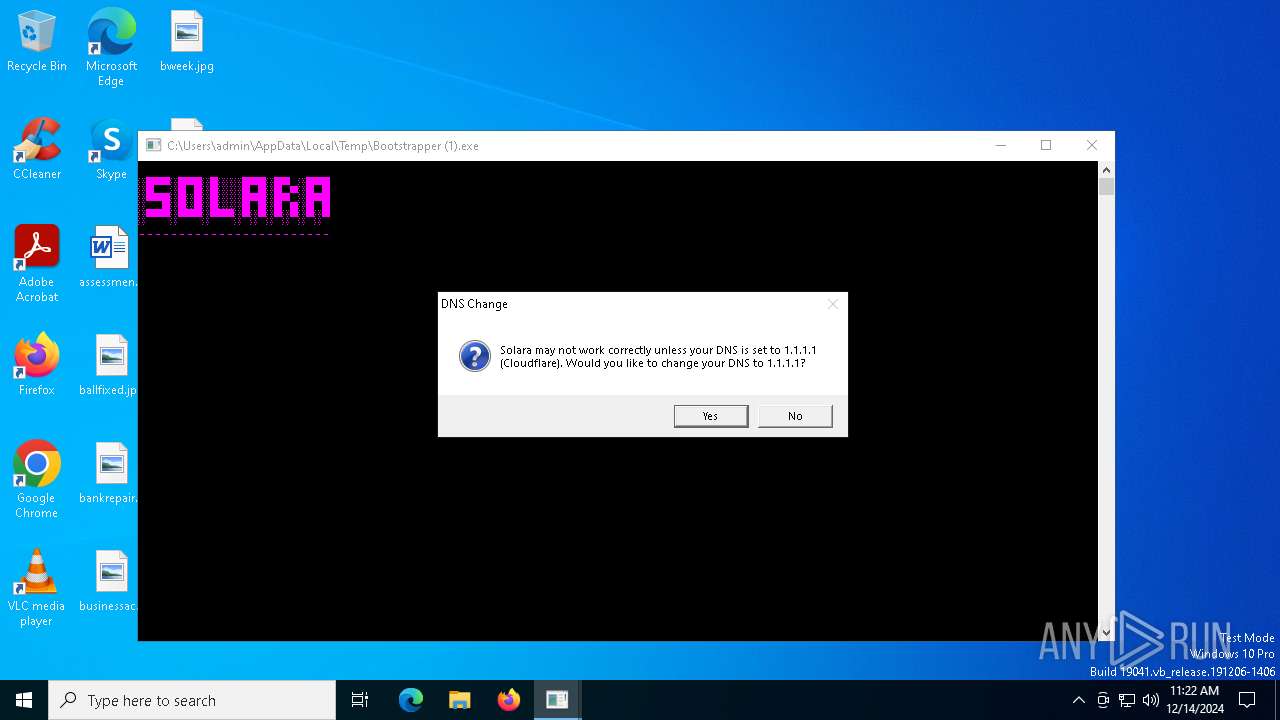
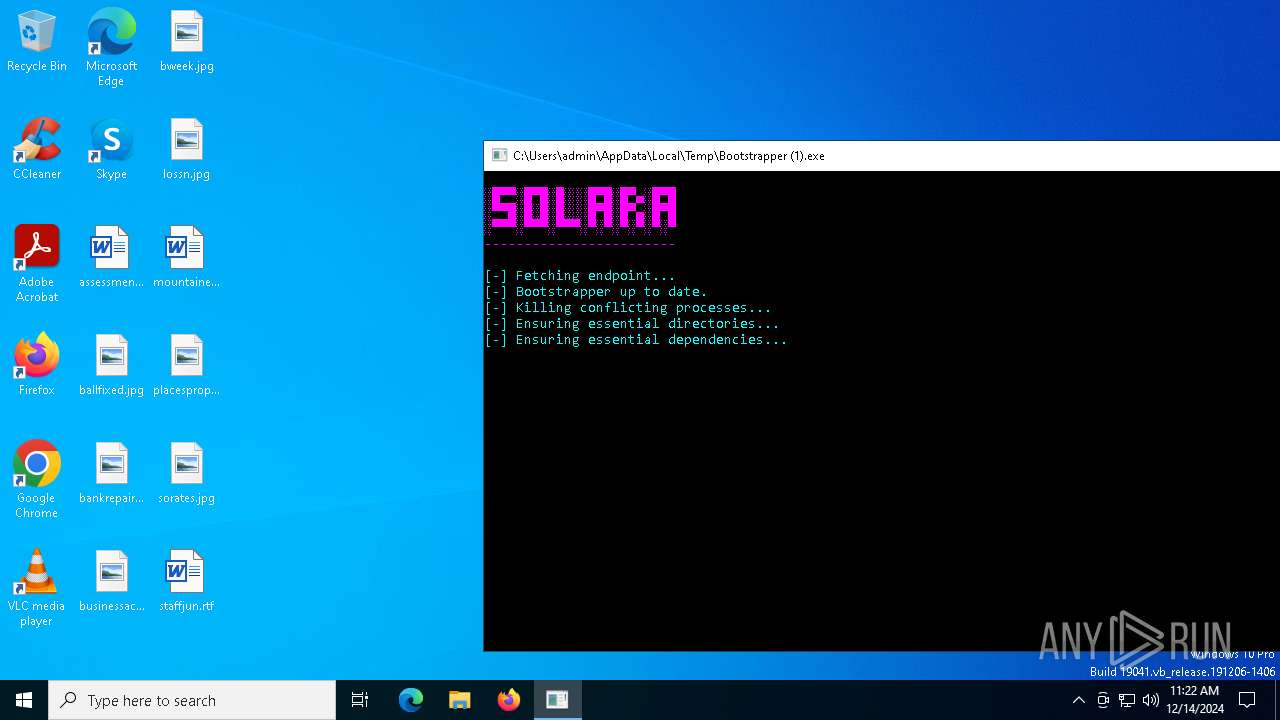
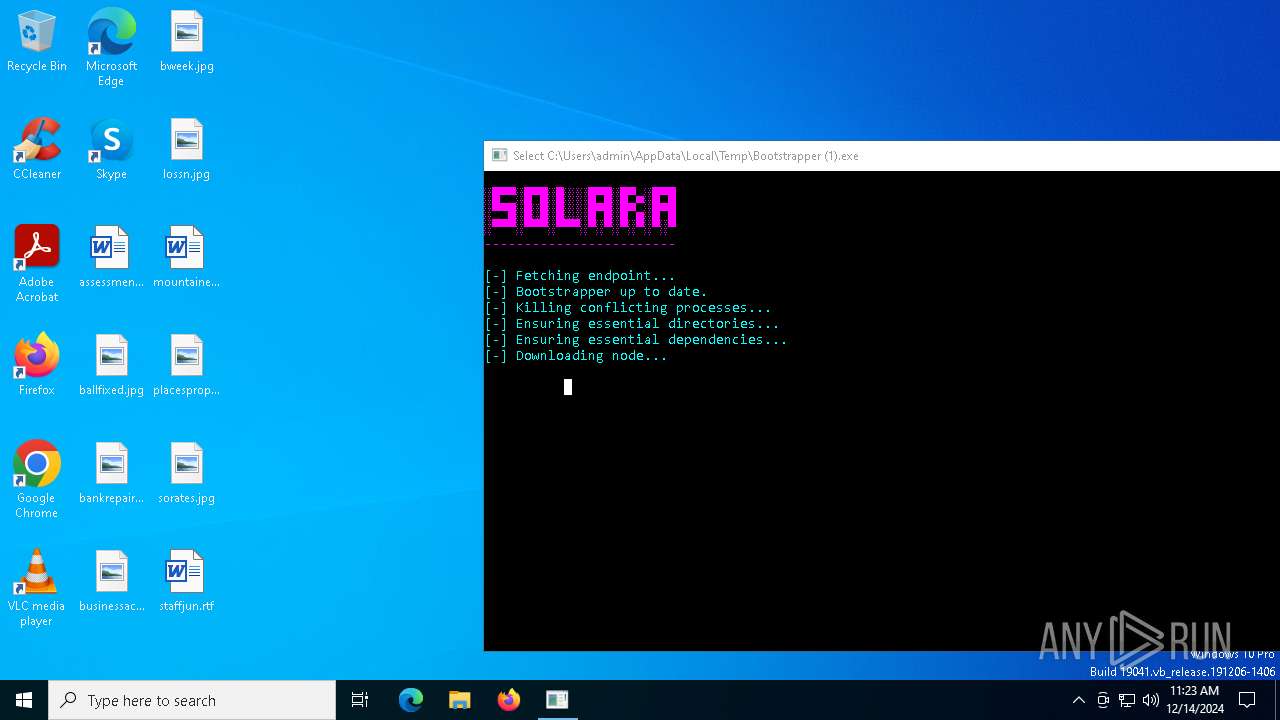
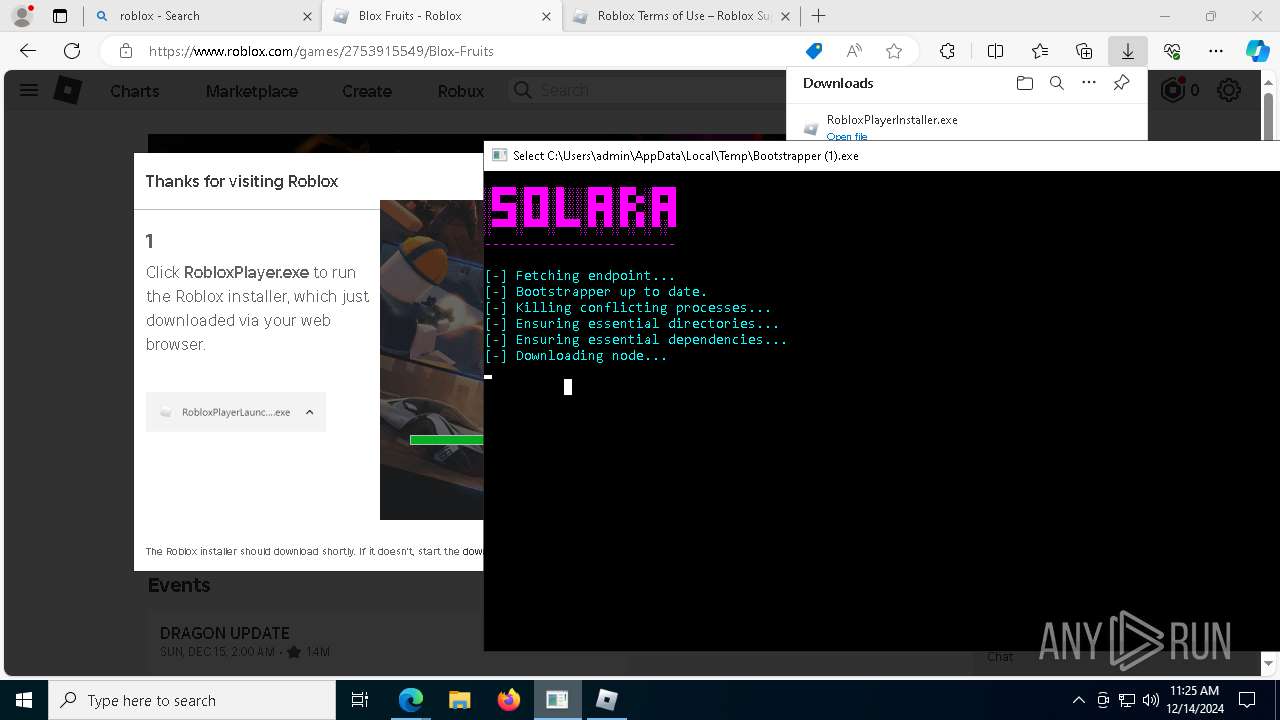
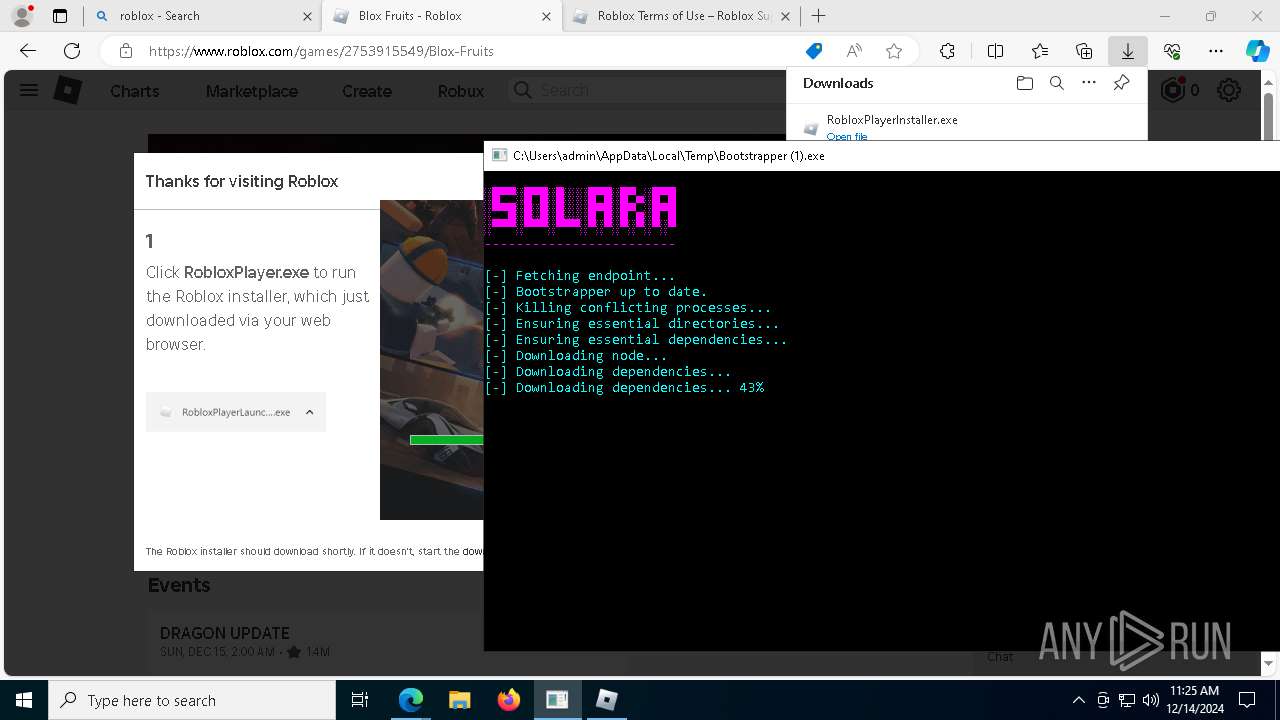
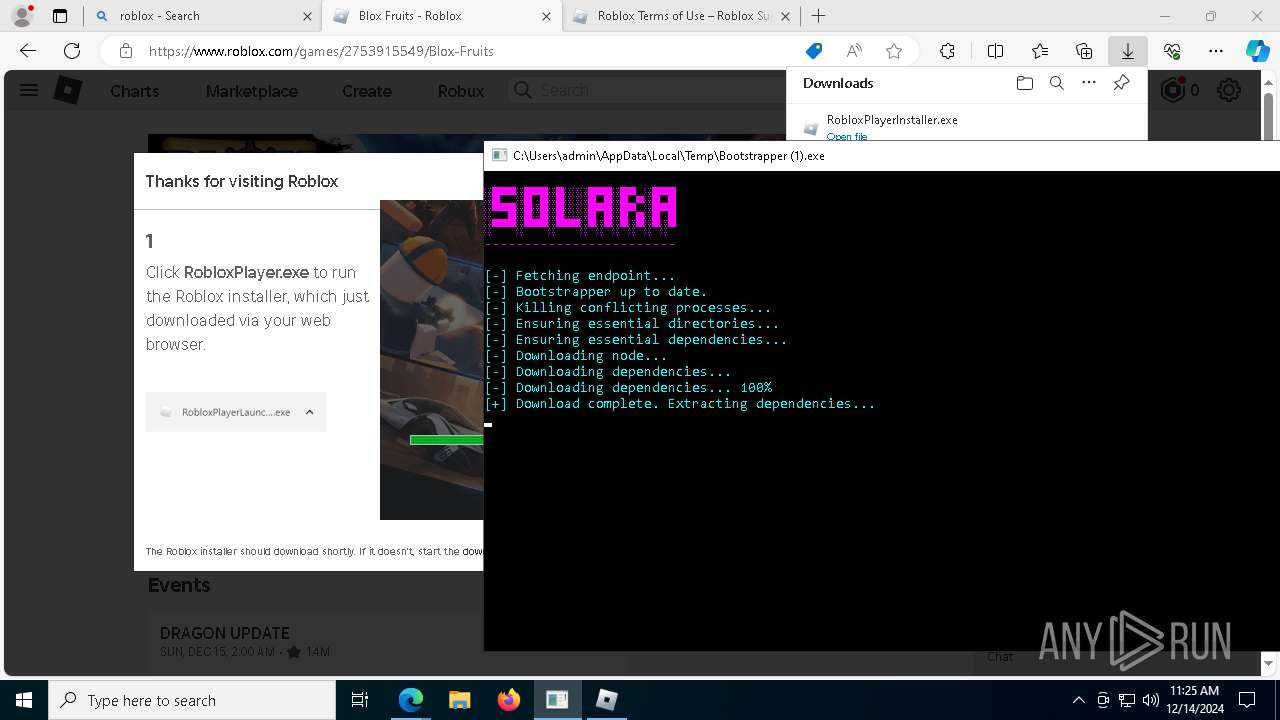
| File name: | Bootstrapper (1).exe |
| Full analysis: | https://app.any.run/tasks/3fd7d86c-27b7-45a4-a280-2e5d5c9335a2 |
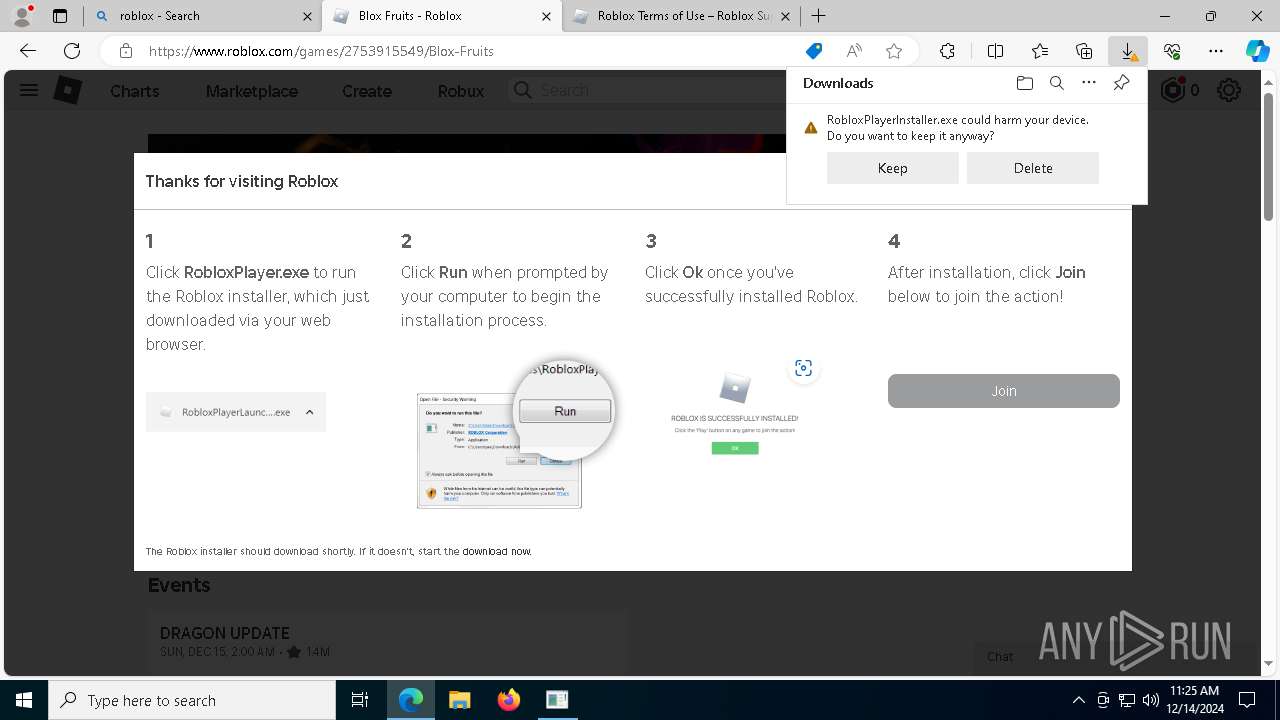
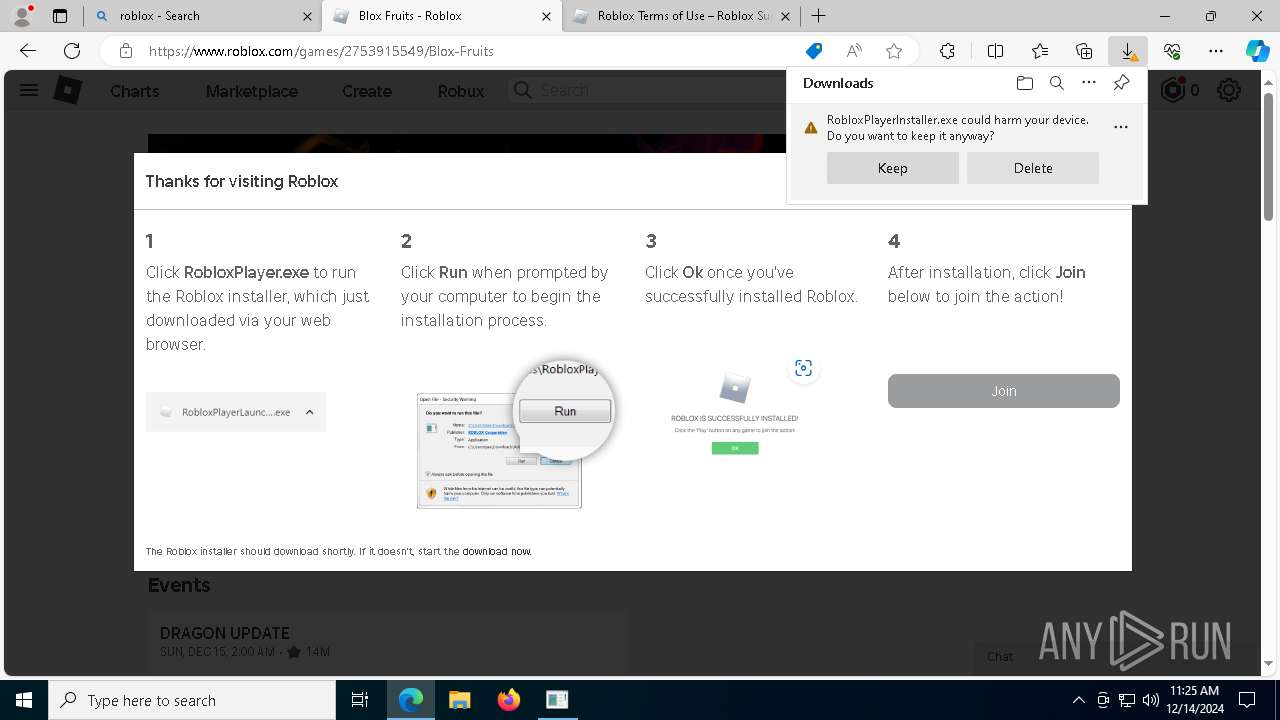
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 11:22:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 02C70D9D6696950C198DB93B7F6A835E |
| SHA1: | 30231A467A49CC37768EEA0F55F4BEA1CBFB48E2 |
| SHA256: | 8F2E28588F2303BD8D7A9B0C3FF6A9CB16FA93F8DDC9C5E0666A8C12D6880EE3 |
| SSDEEP: | 6144:tXxndGsQZDAvUHFLRSZ3e82Zavp/ijHrGEW1NhVhOQNaDffKTghOpDozwKdVuaQ:tf3gAvUlLvocaPhOmTghOpDkwKdw |
MALICIOUS
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 8064)
SUSPICIOUS
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 6556)
Uses WMIC.EXE to obtain information about the network interface controller
- cmd.exe (PID: 7088)
Starts CMD.EXE for commands execution
- Bootstrapper (1).exe (PID: 6464)
Reads security settings of Internet Explorer
- Bootstrapper (1).exe (PID: 6464)
- msiexec.exe (PID: 1228)
- msiexec.exe (PID: 7236)
- MicrosoftEdgeUpdate.exe (PID: 8064)
- MicrosoftEdgeUpdate.exe (PID: 6444)
Reads the date of Windows installation
- Bootstrapper (1).exe (PID: 6464)
Checks Windows Trust Settings
- msiexec.exe (PID: 6628)
- MicrosoftEdgeUpdate.exe (PID: 6444)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6628)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- msiexec.exe (PID: 7236)
- wevtutil.exe (PID: 7264)
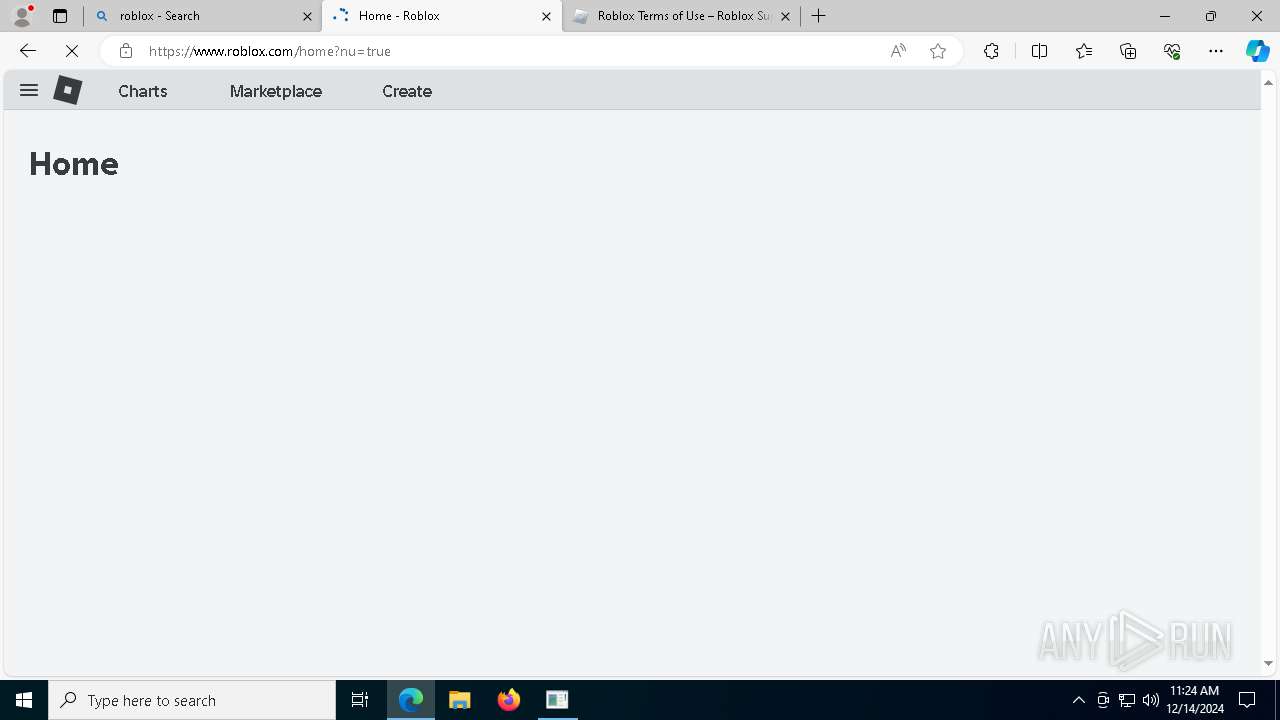
Changes default file association
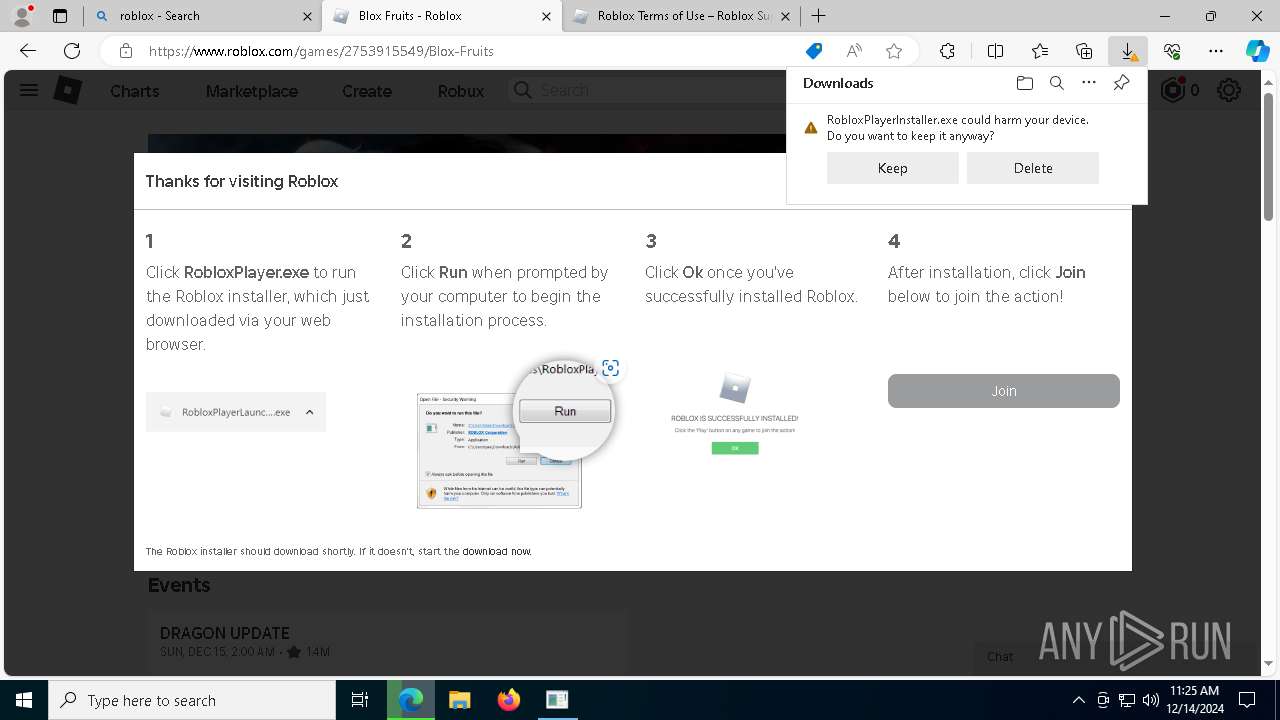
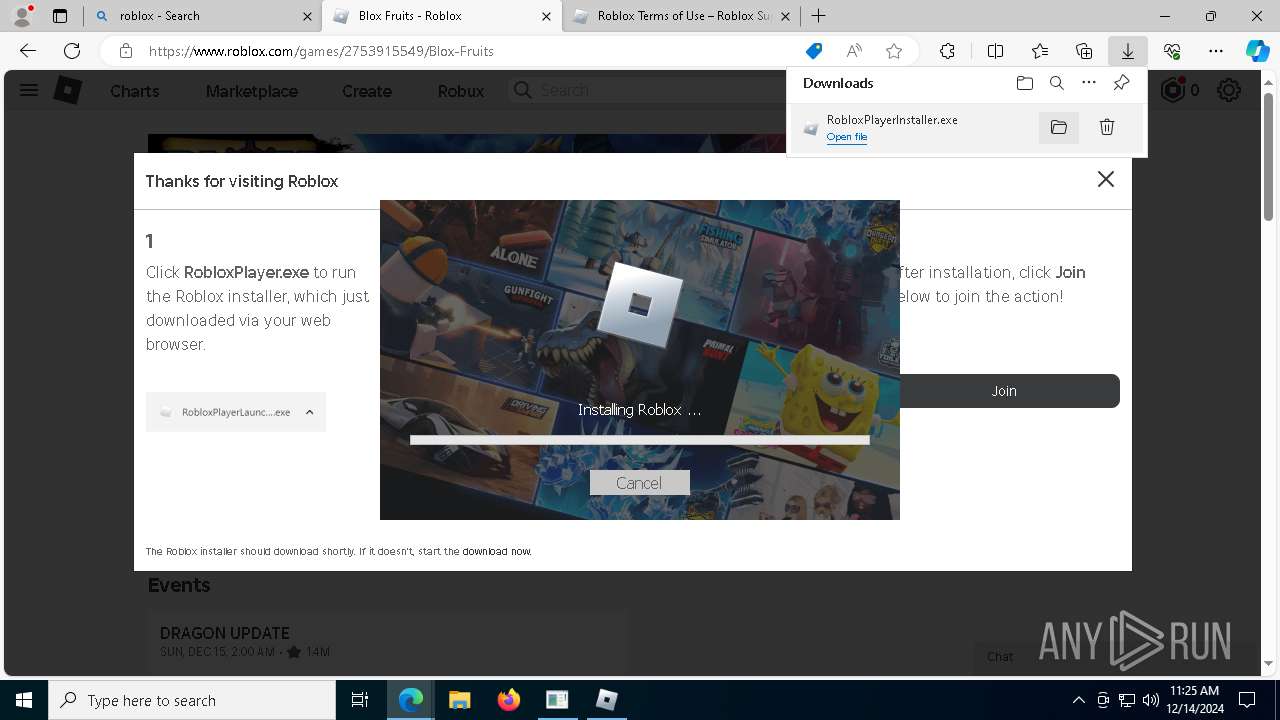
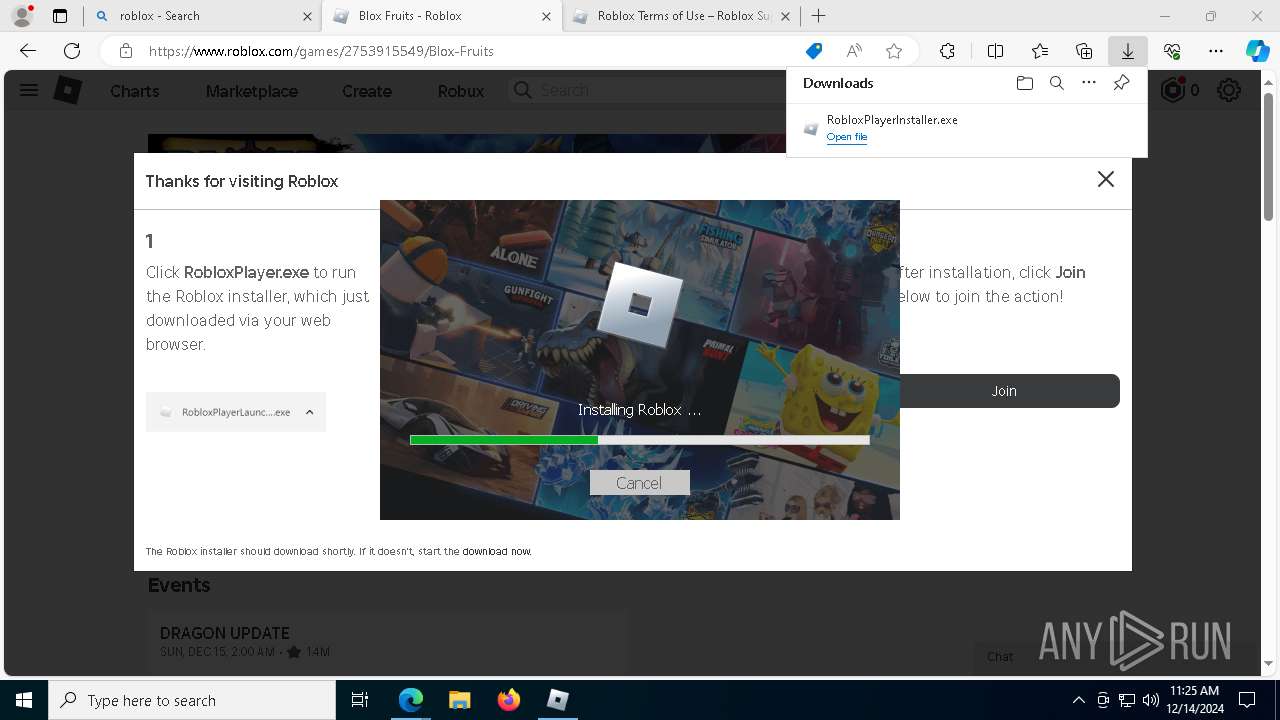
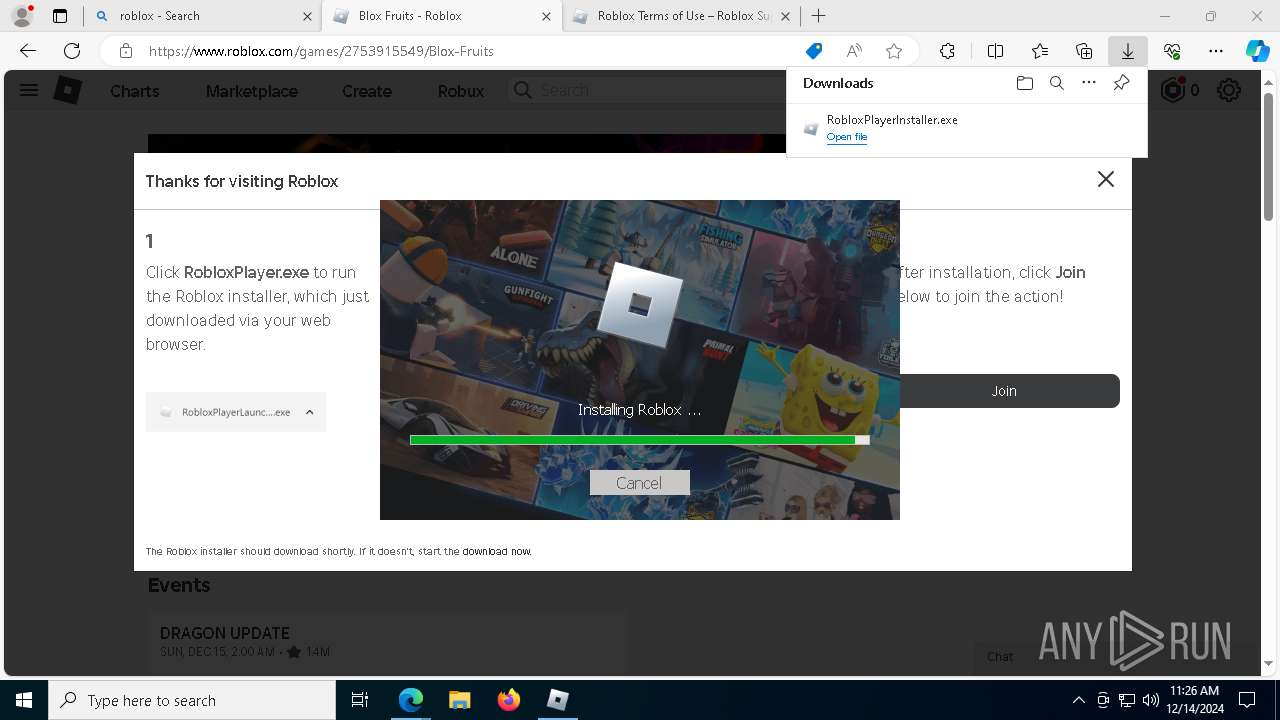
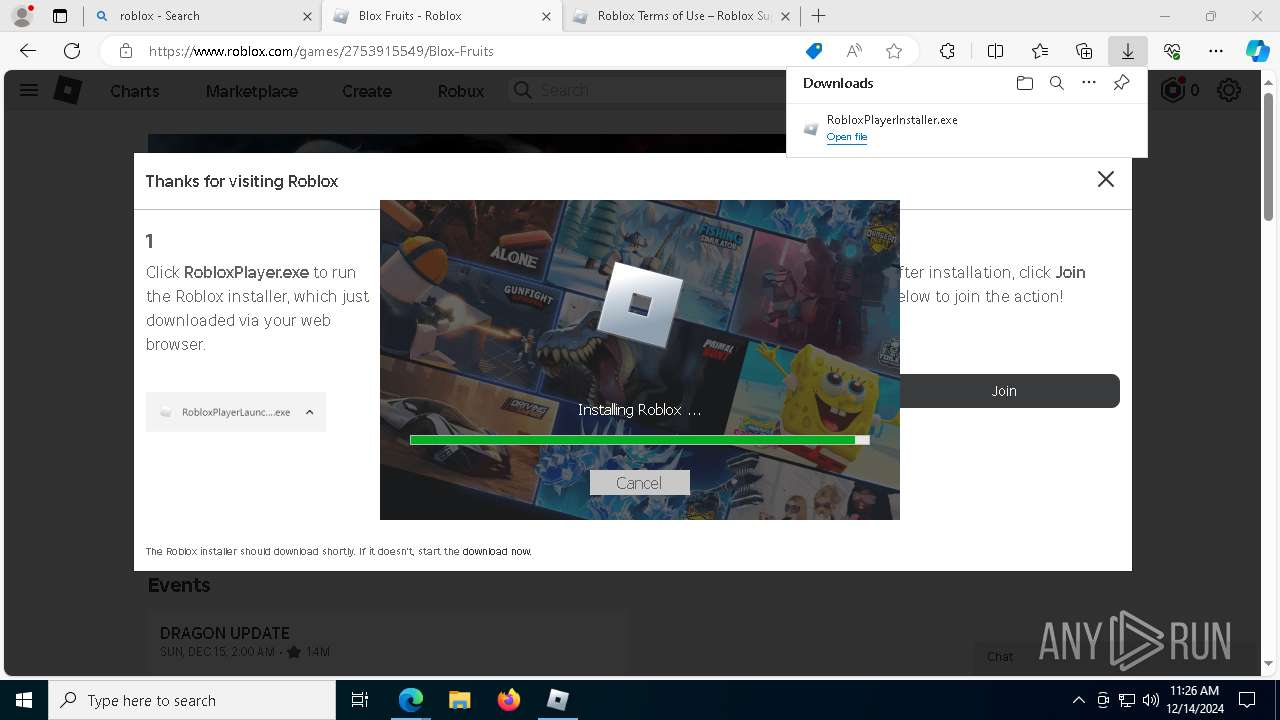
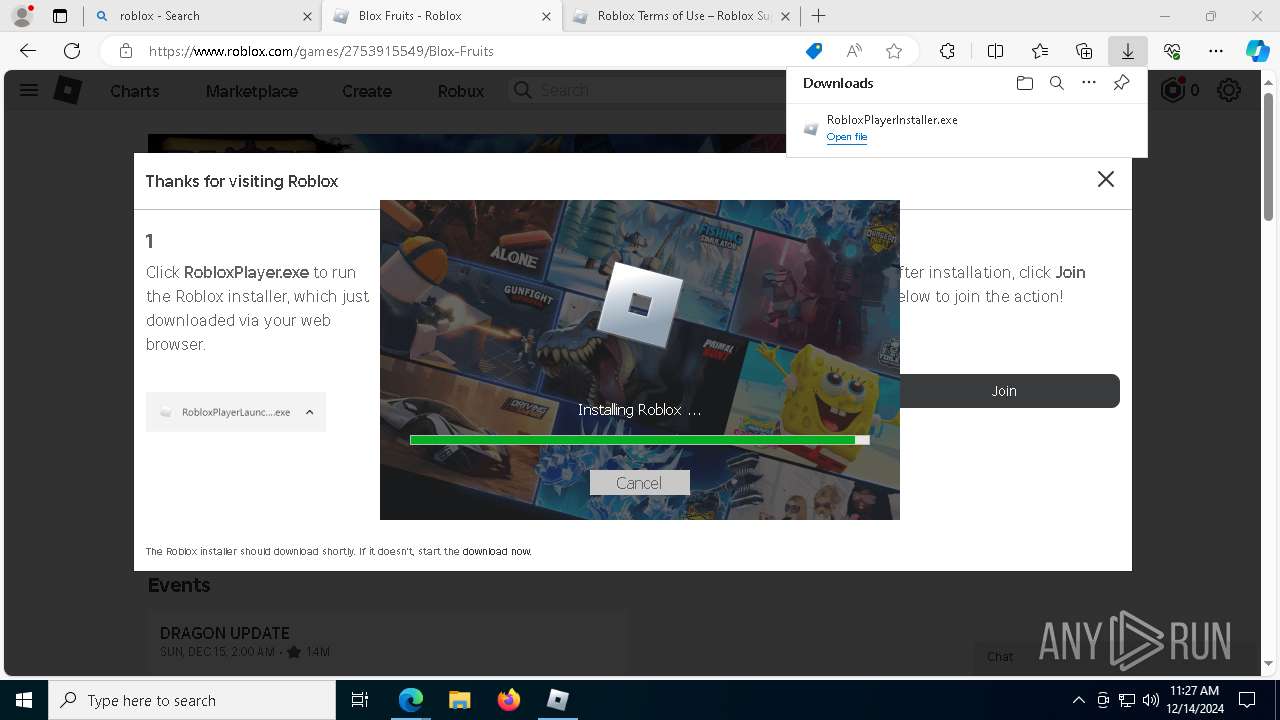
- RobloxPlayerInstaller.exe (PID: 7960)
Executable content was dropped or overwritten
- RobloxPlayerInstaller.exe (PID: 7960)
- Bootstrapper (1).exe (PID: 6464)
- MicrosoftEdgeWebview2Setup.exe (PID: 1400)
- MicrosoftEdgeUpdate.exe (PID: 8064)
- MicrosoftEdge_X64_131.0.2903.99.exe (PID: 3920)
Process drops legitimate windows executable
- RobloxPlayerInstaller.exe (PID: 7960)
- Bootstrapper (1).exe (PID: 6464)
- MicrosoftEdgeWebview2Setup.exe (PID: 1400)
- MicrosoftEdgeUpdate.exe (PID: 8064)
- MicrosoftEdge_X64_131.0.2903.99.exe (PID: 3920)
The process drops C-runtime libraries
- Bootstrapper (1).exe (PID: 6464)
- RobloxPlayerInstaller.exe (PID: 7960)
Executes application which crashes
- Solara.exe (PID: 1228)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 8064)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 8064)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2152)
- MicrosoftEdgeUpdate.exe (PID: 2484)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3820)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4944)
Potential Corporate Privacy Violation
- svchost.exe (PID: 7944)
Application launched itself
- setup.exe (PID: 1224)
INFO
Checks supported languages
- Bootstrapper (1).exe (PID: 6464)
- msiexec.exe (PID: 6628)
- msiexec.exe (PID: 1228)
- identity_helper.exe (PID: 4400)
- msiexec.exe (PID: 5564)
- msiexec.exe (PID: 7236)
- RobloxPlayerInstaller.exe (PID: 7960)
- Solara.exe (PID: 1228)
- MicrosoftEdgeWebview2Setup.exe (PID: 1400)
- MicrosoftEdgeUpdate.exe (PID: 2484)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2152)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3820)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4944)
- MicrosoftEdgeUpdate.exe (PID: 3080)
- MicrosoftEdgeUpdate.exe (PID: 8064)
- MicrosoftEdgeUpdate.exe (PID: 5456)
- MicrosoftEdgeUpdate.exe (PID: 6444)
- MicrosoftEdge_X64_131.0.2903.99.exe (PID: 3920)
- setup.exe (PID: 1224)
- setup.exe (PID: 7144)
Reads the computer name
- Bootstrapper (1).exe (PID: 6464)
- msiexec.exe (PID: 6628)
- msiexec.exe (PID: 5564)
- msiexec.exe (PID: 1228)
- identity_helper.exe (PID: 4400)
- msiexec.exe (PID: 7236)
- RobloxPlayerInstaller.exe (PID: 7960)
- Solara.exe (PID: 1228)
- MicrosoftEdgeUpdate.exe (PID: 8064)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2152)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3820)
- MicrosoftEdgeUpdate.exe (PID: 2484)
- MicrosoftEdgeUpdate.exe (PID: 3080)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4944)
- MicrosoftEdgeUpdate.exe (PID: 5456)
- MicrosoftEdgeUpdate.exe (PID: 6444)
- MicrosoftEdge_X64_131.0.2903.99.exe (PID: 3920)
- setup.exe (PID: 1224)
Reads the software policy settings
- Bootstrapper (1).exe (PID: 6464)
- msiexec.exe (PID: 6628)
- Solara.exe (PID: 1228)
- WerFault.exe (PID: 7364)
- MicrosoftEdgeUpdate.exe (PID: 3080)
- MicrosoftEdgeUpdate.exe (PID: 6444)
The process uses the downloaded file
- Bootstrapper (1).exe (PID: 6464)
- msedge.exe (PID: 6924)
- msedge.exe (PID: 6976)
- RobloxPlayerInstaller.exe (PID: 7960)
Process checks computer location settings
- Bootstrapper (1).exe (PID: 6464)
- MicrosoftEdgeUpdate.exe (PID: 8064)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6628)
- RobloxPlayerInstaller.exe (PID: 7960)
- Solara.exe (PID: 1228)
- Bootstrapper (1).exe (PID: 6464)
- MicrosoftEdgeUpdate.exe (PID: 6444)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6628)
- msedge.exe (PID: 4056)
- msedge.exe (PID: 6976)
- msedge.exe (PID: 372)
Creates files or folders in the user directory
- msiexec.exe (PID: 6628)
- RobloxPlayerInstaller.exe (PID: 7960)
- WerFault.exe (PID: 7364)
- MicrosoftEdgeUpdate.exe (PID: 8064)
- MicrosoftEdge_X64_131.0.2903.99.exe (PID: 3920)
- setup.exe (PID: 7144)
- setup.exe (PID: 1224)
Application launched itself
- msiexec.exe (PID: 6628)
- msedge.exe (PID: 6976)
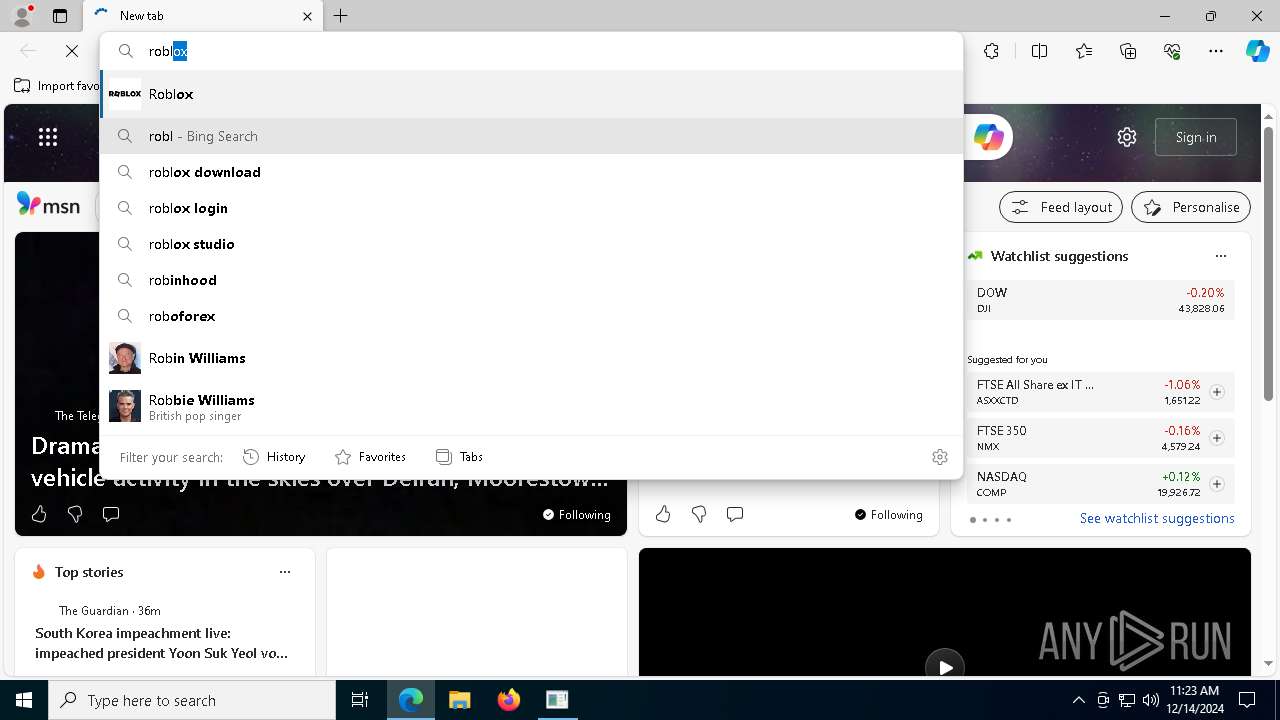
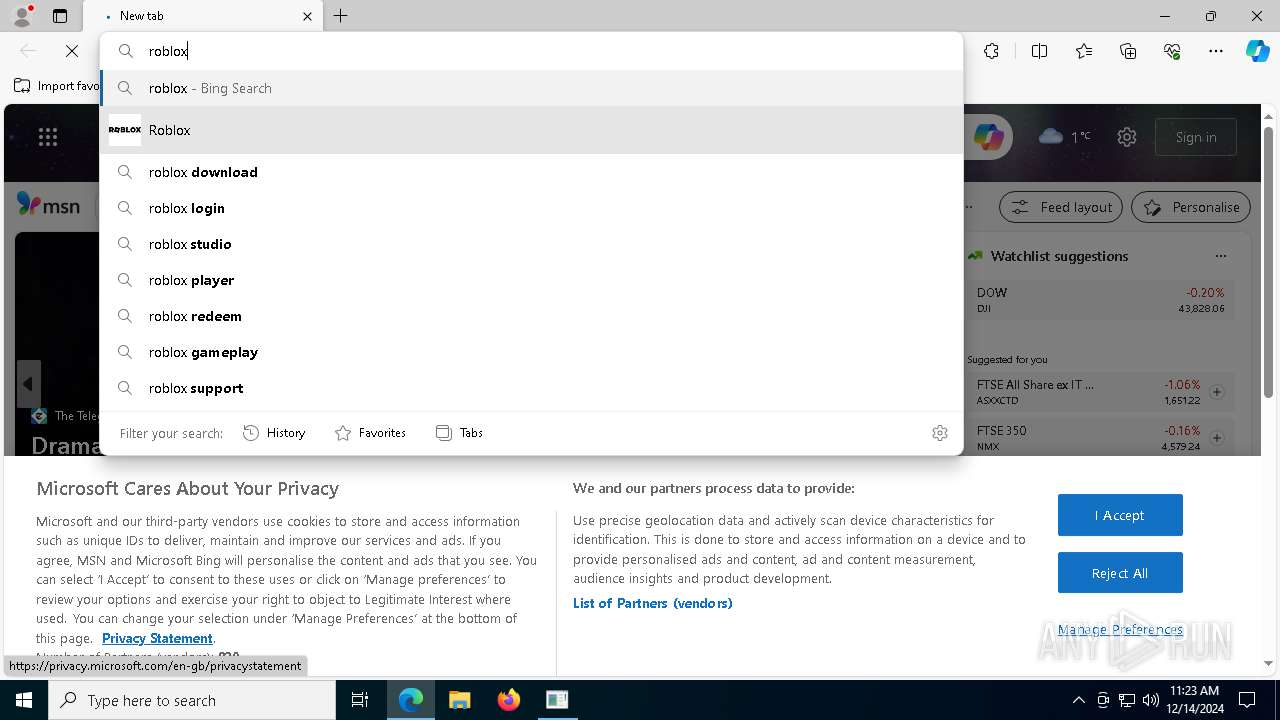
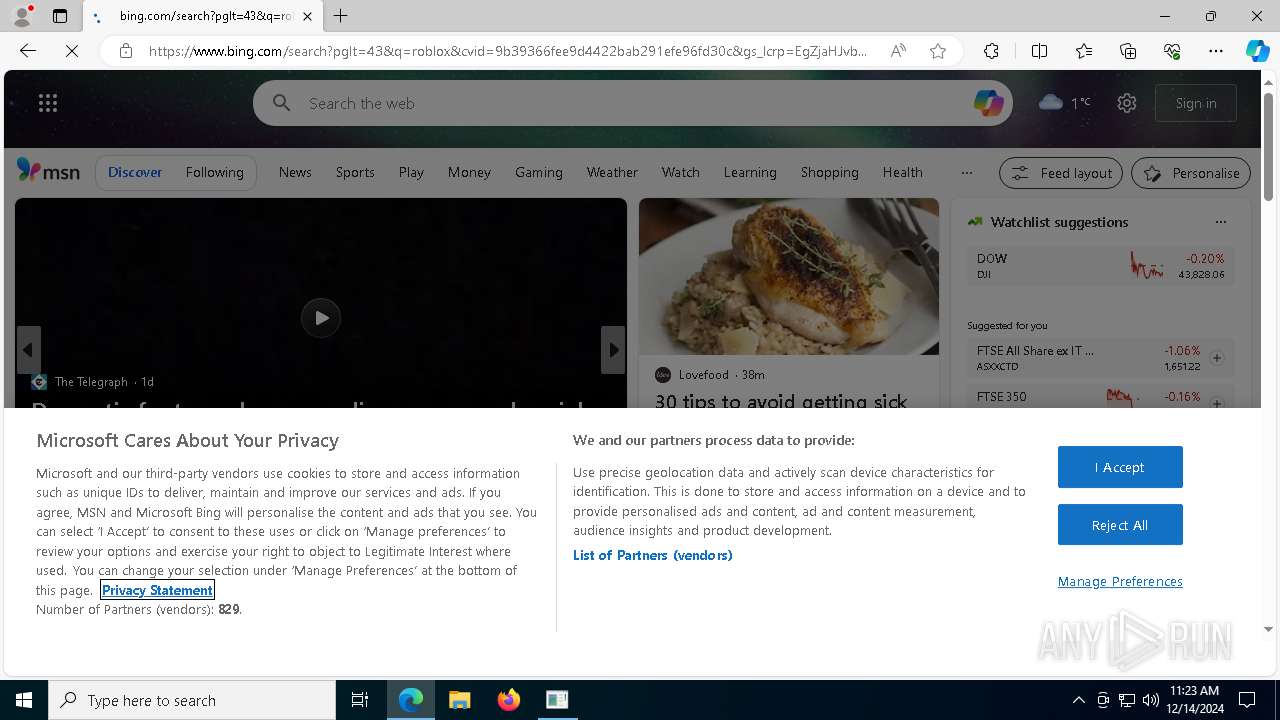
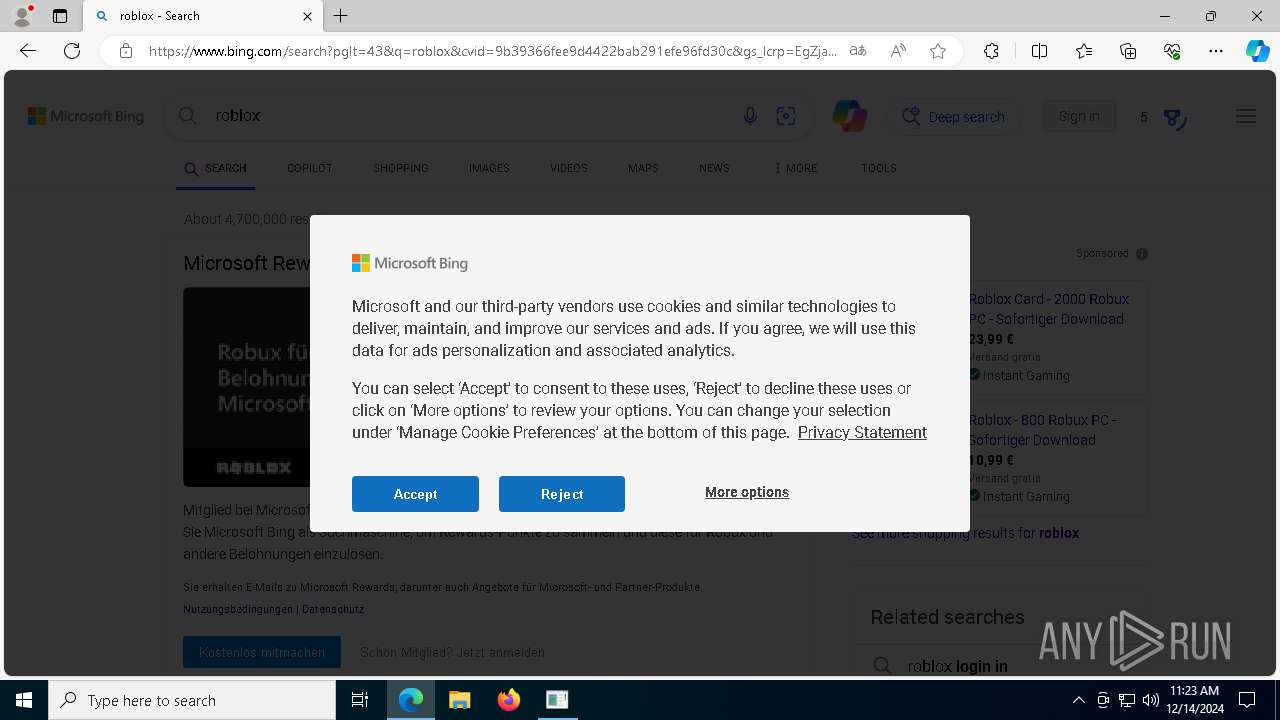
Manual execution by a user
- msedge.exe (PID: 6976)
Reads Environment values
- identity_helper.exe (PID: 4400)
- Solara.exe (PID: 1228)
- Bootstrapper (1).exe (PID: 6464)
- MicrosoftEdgeUpdate.exe (PID: 3080)
Create files in a temporary directory
- svchost.exe (PID: 7944)
- RobloxPlayerInstaller.exe (PID: 7960)
- MicrosoftEdgeWebview2Setup.exe (PID: 1400)
- Bootstrapper (1).exe (PID: 6464)
Creates a software uninstall entry
- msiexec.exe (PID: 6628)
The sample compiled with english language support
- msedge.exe (PID: 6976)
- msedge.exe (PID: 4056)
- msedge.exe (PID: 372)
- RobloxPlayerInstaller.exe (PID: 7960)
- Bootstrapper (1).exe (PID: 6464)
- MicrosoftEdgeWebview2Setup.exe (PID: 1400)
- MicrosoftEdgeUpdate.exe (PID: 8064)
- svchost.exe (PID: 7944)
- MicrosoftEdge_X64_131.0.2903.99.exe (PID: 3920)
Process checks whether UAC notifications are on
- RobloxPlayerInstaller.exe (PID: 7960)
Sends debugging messages
- RobloxPlayerInstaller.exe (PID: 7960)
Creates files in the program directory
- Bootstrapper (1).exe (PID: 6464)
Disables trace logs
- Solara.exe (PID: 1228)
- Bootstrapper (1).exe (PID: 6464)
Checks proxy server information
- Solara.exe (PID: 1228)
- WerFault.exe (PID: 7364)
- Bootstrapper (1).exe (PID: 6464)
- MicrosoftEdgeUpdate.exe (PID: 3080)
- MicrosoftEdgeUpdate.exe (PID: 6444)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:13 21:07:39+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 816640 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc948a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | SolaraBootstrapper |
| FileVersion: | 1.0.0.0 |
| InternalName: | SolaraBootstrapper.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | SolaraBootstrapper.exe |
| ProductName: | SolaraBootstrapper |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
240
Monitored processes
103
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --mojo-platform-channel-handle=7332 --field-trial-handle=2476,i,4449834689061813131,3306686945331299177,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2616 --field-trial-handle=2476,i,4449834689061813131,3306686945331299177,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --mojo-platform-channel-handle=5808 --field-trial-handle=2476,i,4449834689061813131,3306686945331299177,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2564 --field-trial-handle=2476,i,4449834689061813131,3306686945331299177,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=6212 --field-trial-handle=2476,i,4449834689061813131,3306686945331299177,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=4320 --field-trial-handle=2476,i,4449834689061813131,3306686945331299177,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5640 --field-trial-handle=2476,i,4449834689061813131,3306686945331299177,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1224 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{11872702-27ED-4599-AADB-D4EEF20B36A5}\EDGEMITMP_D34F3.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{11872702-27ED-4599-AADB-D4EEF20B36A5}\MicrosoftEdge_X64_131.0.2903.99.exe" --msedgewebview --verbose-logging --do-not-launch-msedge --user-level | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{11872702-27ED-4599-AADB-D4EEF20B36A5}\EDGEMITMP_D34F3.tmp\setup.exe | — | MicrosoftEdge_X64_131.0.2903.99.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Version: 131.0.2903.99 Modules
| |||||||||||||||
| 1228 | C:\Windows\syswow64\MsiExec.exe -Embedding 41D268A6ACB178E039A0B75DA6F7EAB7 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\ProgramData\Solara\Solara.exe" | C:\ProgramData\Solara\Solara.exe | Bootstrapper (1).exe | ||||||||||||
User: admin Company: CMD Softworks Integrity Level: HIGH Description: Solara V3 Exit code: 3762504530 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
38 388
Read events
33 791
Write events
4 521
Delete events
76
Modification events
| (PID) Process: | (6464) Bootstrapper (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper (1)_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6464) Bootstrapper (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper (1)_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6464) Bootstrapper (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper (1)_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6464) Bootstrapper (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper (1)_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6464) Bootstrapper (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper (1)_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6464) Bootstrapper (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper (1)_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6464) Bootstrapper (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper (1)_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6464) Bootstrapper (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper (1)_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6464) Bootstrapper (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper (1)_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6464) Bootstrapper (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper (1)_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
289
Suspicious files
2 954
Text files
1 261
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6464 | Bootstrapper (1).exe | C:\Users\admin\AppData\Local\Temp\node-v18.16.0-x64.msi | — | |
MD5:— | SHA256:— | |||
| 6628 | msiexec.exe | C:\Windows\Installer\139195.msi | — | |
MD5:— | SHA256:— | |||
| 6628 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\66AE3BFDF94A732B262342AD2154B86E_CEA48AEE703922244E2530F7A011BBC6 | binary | |
MD5:638A1420C2EA5978199890D585BBC828 | SHA256:AC6CA3550AFA69B4B4A1CB36DDA42DC2BECA9FD65712602D2CDDC082BD23C77B | |||
| 6628 | msiexec.exe | C:\Windows\Installer\MSI9E0C.tmp | executable | |
MD5:7A86CE1A899262DD3C1DF656BFF3FB2C | SHA256:B8F2D0909D7C2934285A8BE010D37C0609C7854A36562CBFCBCE547F4F4C7B0C | |||
| 6628 | msiexec.exe | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.log | text | |
MD5:D4FCAF7D679CA2F44403DE9782782D78 | SHA256:6B641DF91615424363EF41153B571284D9E2B2860D1AAC4D9416F0DCCF3790EC | |||
| 6628 | msiexec.exe | C:\Windows\Installer\MSI93C7.tmp | executable | |
MD5:9FE9B0ECAEA0324AD99036A91DB03EBB | SHA256:E2CCE64916E405976A1D0C522B44527D12B1CBA19DE25DA62121CF5F41D184C9 | |||
| 6628 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\42B9A473B4DAF01285A36B4D3C7B1662_178C086B699FD6C56B804AF3EF759CB5 | binary | |
MD5:DF34FC5D3C6EFCA920ADAE609D73EF4A | SHA256:0AD53D7BD54B36DF2A6133E1B253F4119AF596808AE84DFB7B836A45D82BF655 | |||
| 6464 | Bootstrapper (1).exe | C:\Users\admin\AppData\Local\Temp\DISCORD | binary | |
MD5:B016DAFCA051F817C6BA098C096CB450 | SHA256:B03C8C2D2429E9DBC7920113DEDF6FC09095AB39421EE0CC8819AD412E5D67B9 | |||
| 6628 | msiexec.exe | C:\Windows\Installer\MSI9426.tmp | executable | |
MD5:9FE9B0ECAEA0324AD99036A91DB03EBB | SHA256:E2CCE64916E405976A1D0C522B44527D12B1CBA19DE25DA62121CF5F41D184C9 | |||
| 6628 | msiexec.exe | C:\Windows\Installer\MSI9456.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
270
DNS requests
101
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.37.202.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7100 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7944 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734556399&P2=404&P3=2&P4=bfw9VwwHe3ix9p1YdS%2fnmsaIP5JHBIg1nS6U8aWLwizlReKS2v4fDHFHjefsDzsdb6JabVLzj7OmfmzVAKwdjA%3d%3d | unknown | — | — | whitelisted |
7944 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734556399&P2=404&P3=2&P4=bfw9VwwHe3ix9p1YdS%2fnmsaIP5JHBIg1nS6U8aWLwizlReKS2v4fDHFHjefsDzsdb6JabVLzj7OmfmzVAKwdjA%3d%3d | unknown | — | — | whitelisted |
6720 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6628 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAOO2y%2FG5AVzGnYPFRYUTIU%3D | unknown | — | — | whitelisted |
7944 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734556399&P2=404&P3=2&P4=bfw9VwwHe3ix9p1YdS%2fnmsaIP5JHBIg1nS6U8aWLwizlReKS2v4fDHFHjefsDzsdb6JabVLzj7OmfmzVAKwdjA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2548 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.32.238.112:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.37.202.100:80 | www.microsoft.com | Linknet-Fastnet ASN | ID | whitelisted |
5064 | SearchApp.exe | 2.21.110.146:443 | www.bing.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
getsolara.dev |
| malicious |
clientsettings.roblox.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
372 | msedge.exe | Misc activity | ET INFO Observed Cloudflare DNS over HTTPS Domain (cloudflare-dns .com in TLS SNI) |
2192 | svchost.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
— | — | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
7944 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
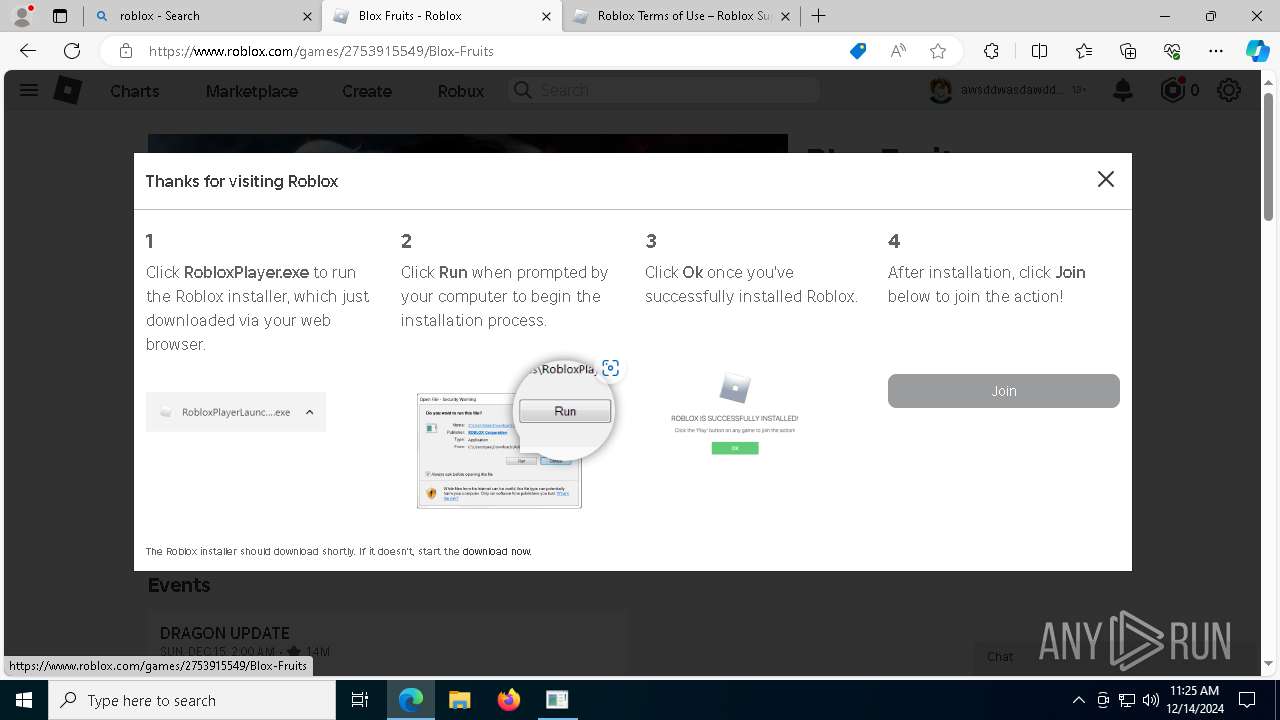
RobloxPlayerInstaller.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|