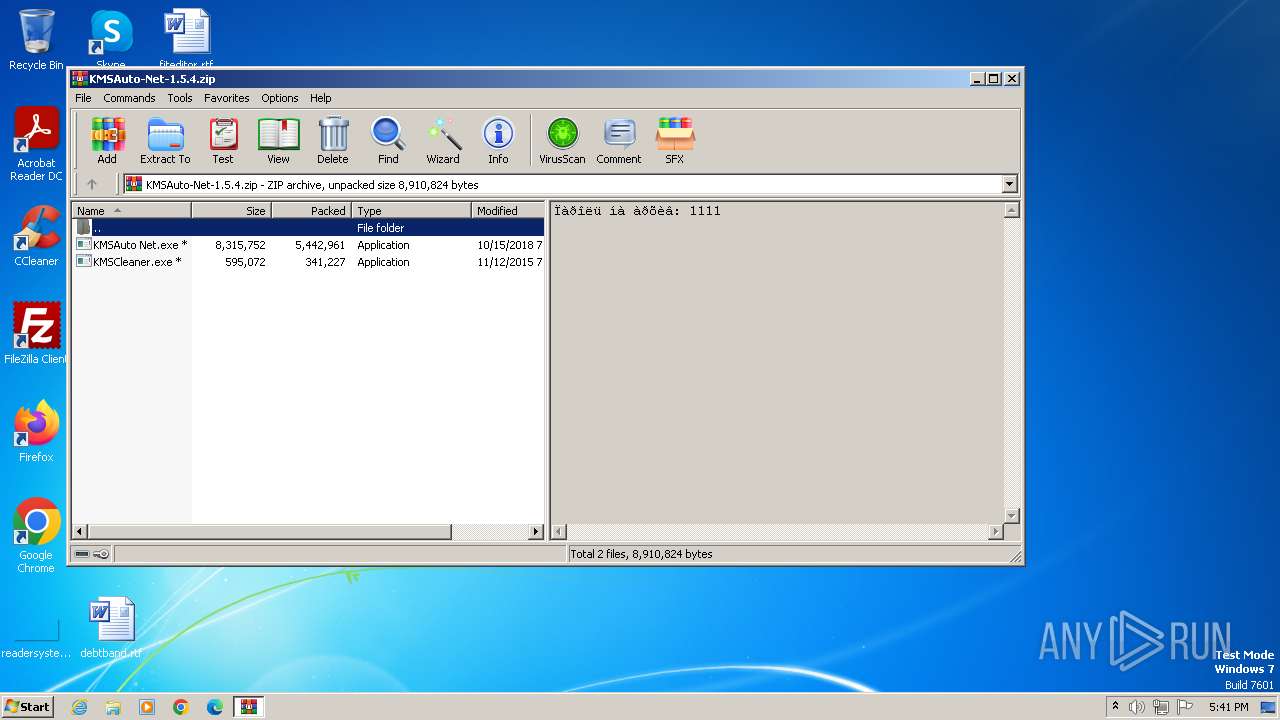
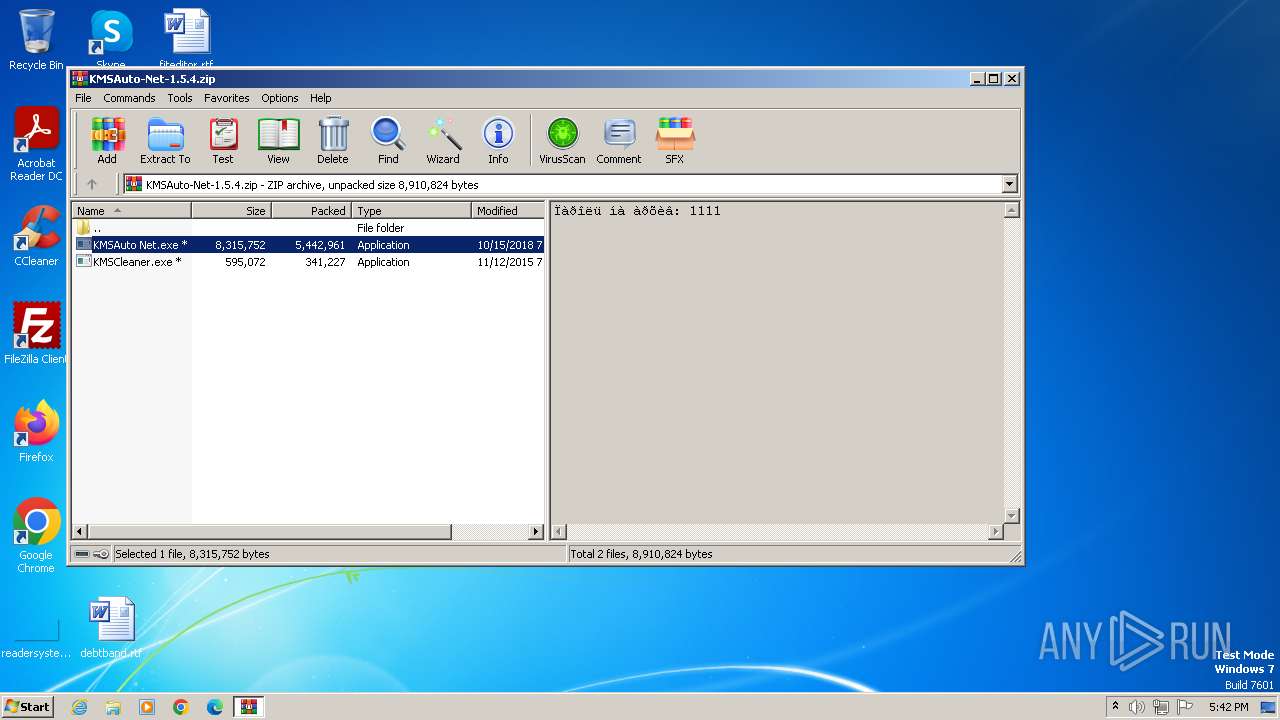
| File name: | KMSAuto-Net-1.5.4.zip |
| Full analysis: | https://app.any.run/tasks/1df28b76-a7d8-46b5-8cc8-75bcb75d44ab |
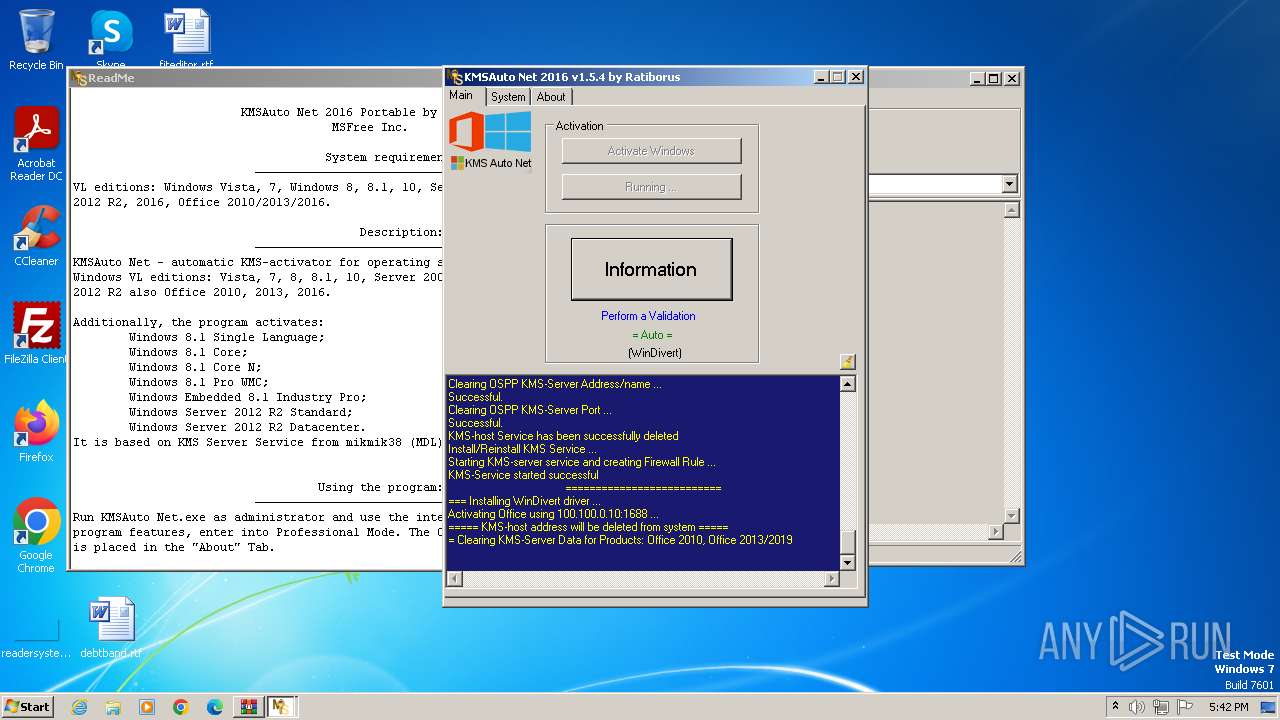
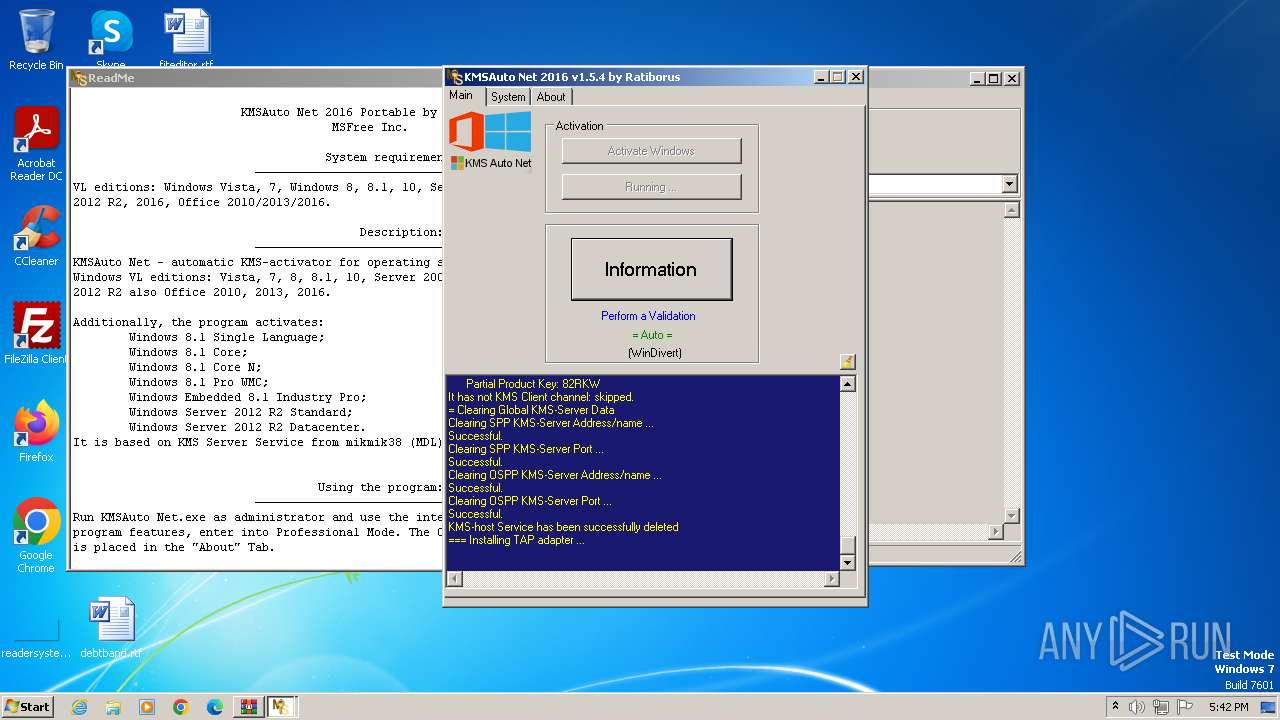
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2023, 16:41:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 97630B7C2AF0DB8685904A30258000B1 |
| SHA1: | 8F9286B1E0E8CF60B67D898AA8693486DDC2BD4E |
| SHA256: | 8F2CDF68836AE101E4D0857A7126D1911CEDB02CDA136EC9DD737D55FA15E51C |
| SSDEEP: | 98304:92YXkiY2d5CTaEsccPgAY7oKSgy74WArwRJoniKKUrnmioZDI7FJf4FhtXJYaz+e:y2taM8M9 |
MALICIOUS
Application was dropped or rewritten from another process
- KMSAuto Net.exe (PID: 3044)
- KMSAuto Net.exe (PID: 2288)
- wzt.dat (PID: 1912)
- certmgr.exe (PID: 2856)
- certmgr.exe (PID: 3448)
- bin.dat (PID: 2588)
- bin_x86.dat (PID: 3380)
- AESDecoder.exe (PID: 2456)
- KMSSS.exe (PID: 3656)
- wzt.dat (PID: 3168)
- certmgr.exe (PID: 3840)
- bin.dat (PID: 1836)
- certmgr.exe (PID: 2008)
- AESDecoder.exe (PID: 1488)
- bin_x86.dat (PID: 3400)
- KMSSS.exe (PID: 3824)
- bin_x86.dat (PID: 3816)
- FakeClient.exe (PID: 3400)
- certmgr.exe (PID: 2308)
- certmgr.exe (PID: 3560)
- AESDecoder.exe (PID: 128)
- bin_x86.dat (PID: 3084)
- bin.dat (PID: 2300)
- wzt.dat (PID: 3020)
Drops the executable file immediately after the start
- KMSAuto Net.exe (PID: 2288)
- AESDecoder.exe (PID: 2456)
- bin.dat (PID: 2588)
- wzt.dat (PID: 1912)
- bin_x86.dat (PID: 3380)
- wzt.dat (PID: 3168)
- bin.dat (PID: 1836)
- AESDecoder.exe (PID: 1488)
- bin_x86.dat (PID: 3400)
- bin_x86.dat (PID: 3816)
- bin.dat (PID: 2300)
- AESDecoder.exe (PID: 128)
- bin_x86.dat (PID: 3084)
- wzt.dat (PID: 3020)
SUSPICIOUS
Reads Internet Explorer settings
- KMSAuto Net.exe (PID: 2288)
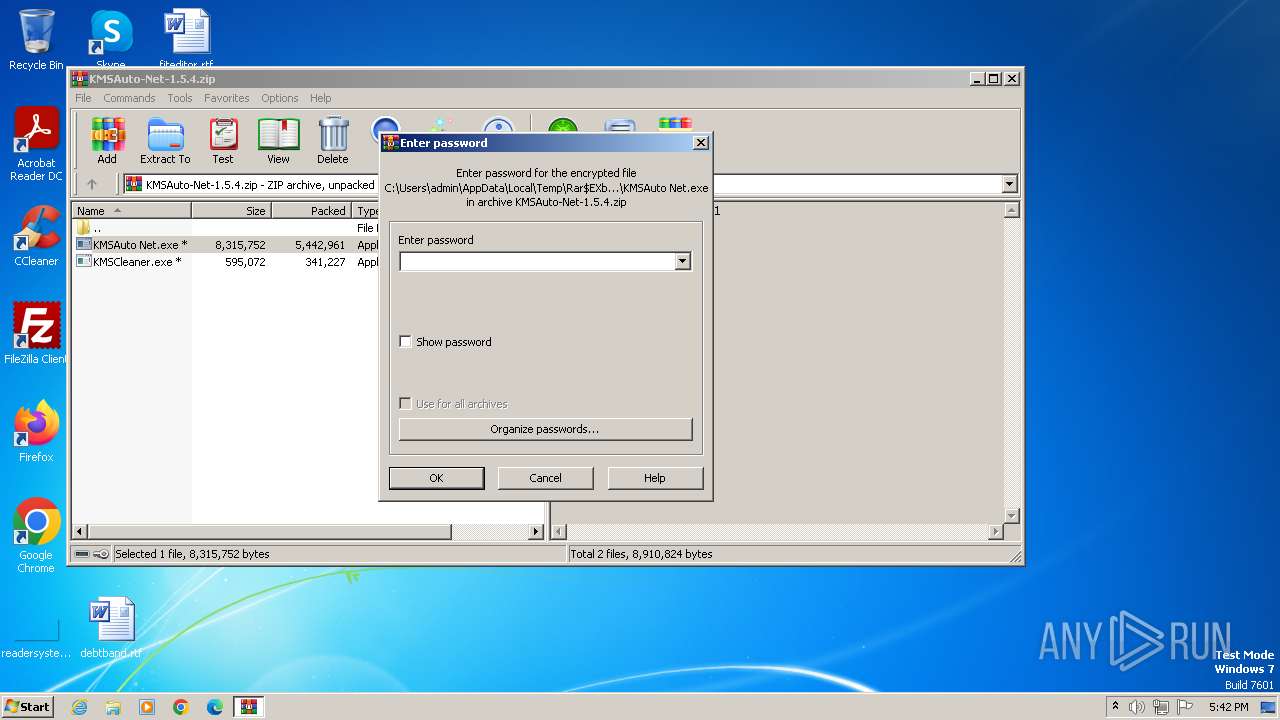
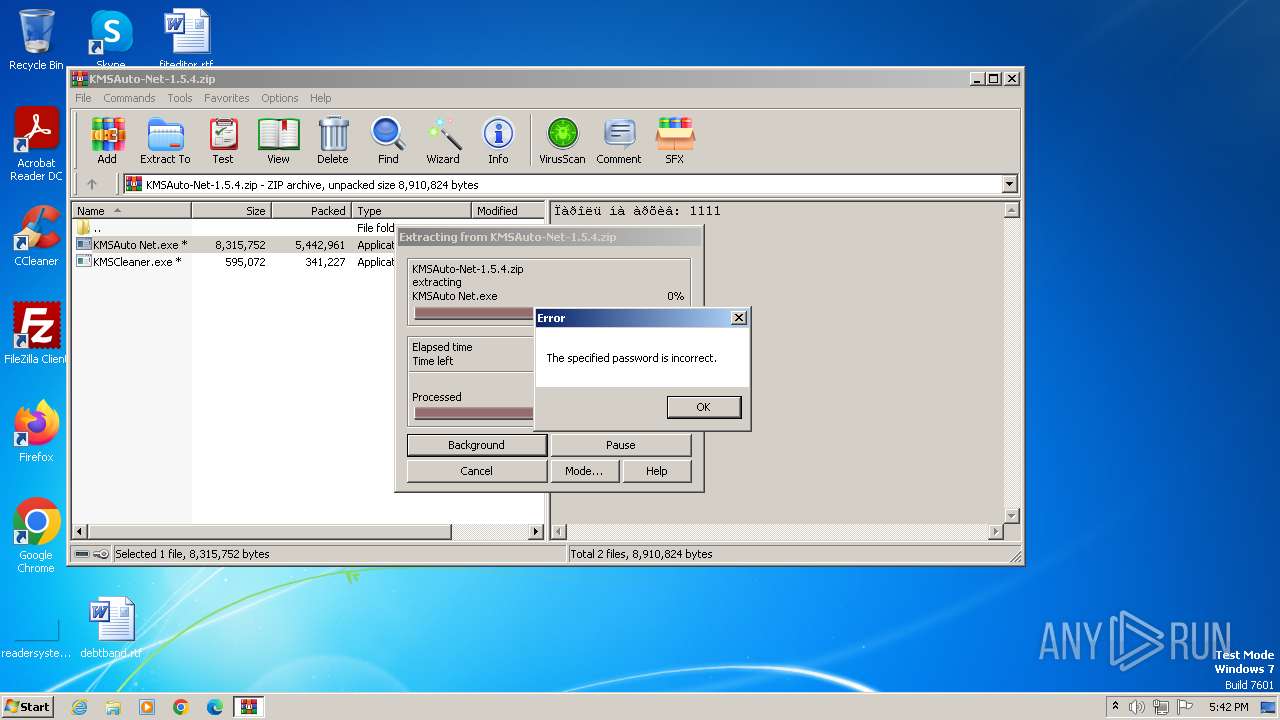
Drops 7-zip archiver for unpacking
- KMSAuto Net.exe (PID: 2288)
Starts application with an unusual extension
- cmd.exe (PID: 2128)
- cmd.exe (PID: 2344)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 1880)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 3256)
- cmd.exe (PID: 3564)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 2080)
- cmd.exe (PID: 1808)
Process drops legitimate windows executable
- wzt.dat (PID: 1912)
- bin_x86.dat (PID: 3380)
- wzt.dat (PID: 3168)
- bin_x86.dat (PID: 3400)
- bin_x86.dat (PID: 3816)
- wzt.dat (PID: 3020)
- bin_x86.dat (PID: 3084)
Application launched itself
- cmd.exe (PID: 3468)
- cmd.exe (PID: 3876)
Drops a system driver (possible attempt to evade defenses)
- bin_x86.dat (PID: 3380)
- bin_x86.dat (PID: 3400)
- bin_x86.dat (PID: 3816)
- bin_x86.dat (PID: 3084)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3468)
- KMSAuto Net.exe (PID: 2288)
- cmd.exe (PID: 3876)
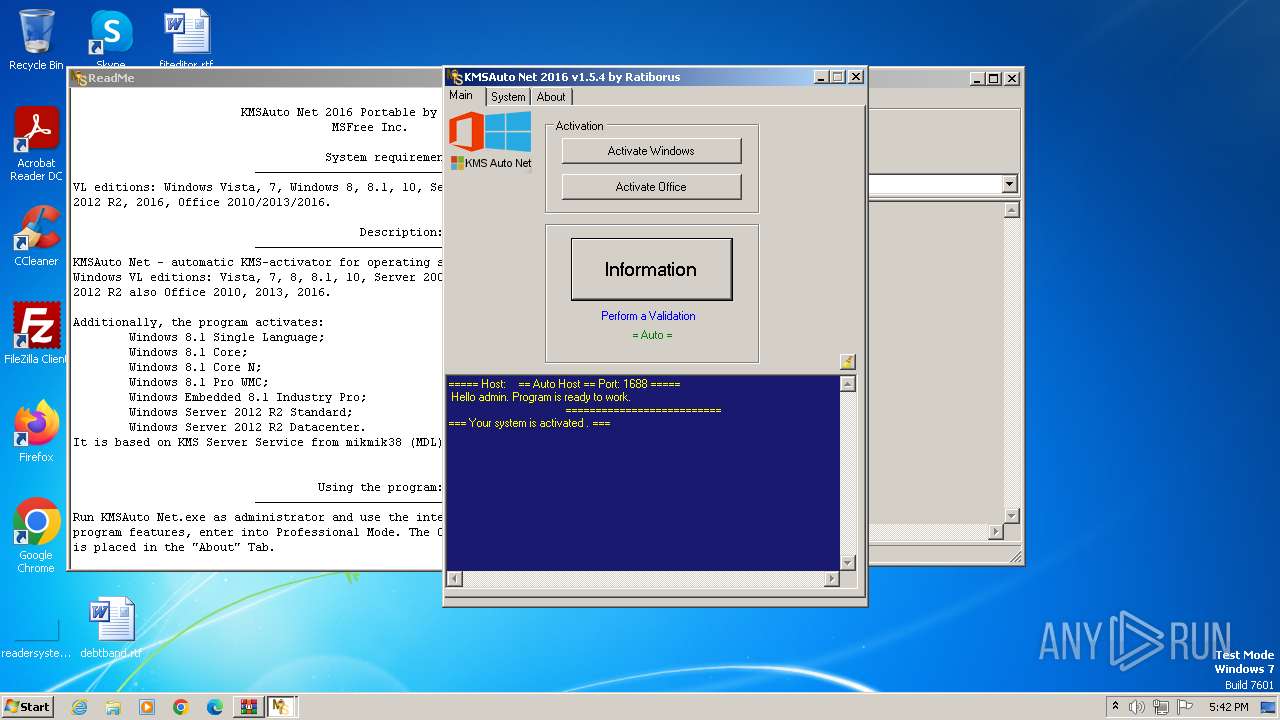
Uses NETSH.EXE to delete a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 2288)
Uses NETSH.EXE to add a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 2288)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 2288)
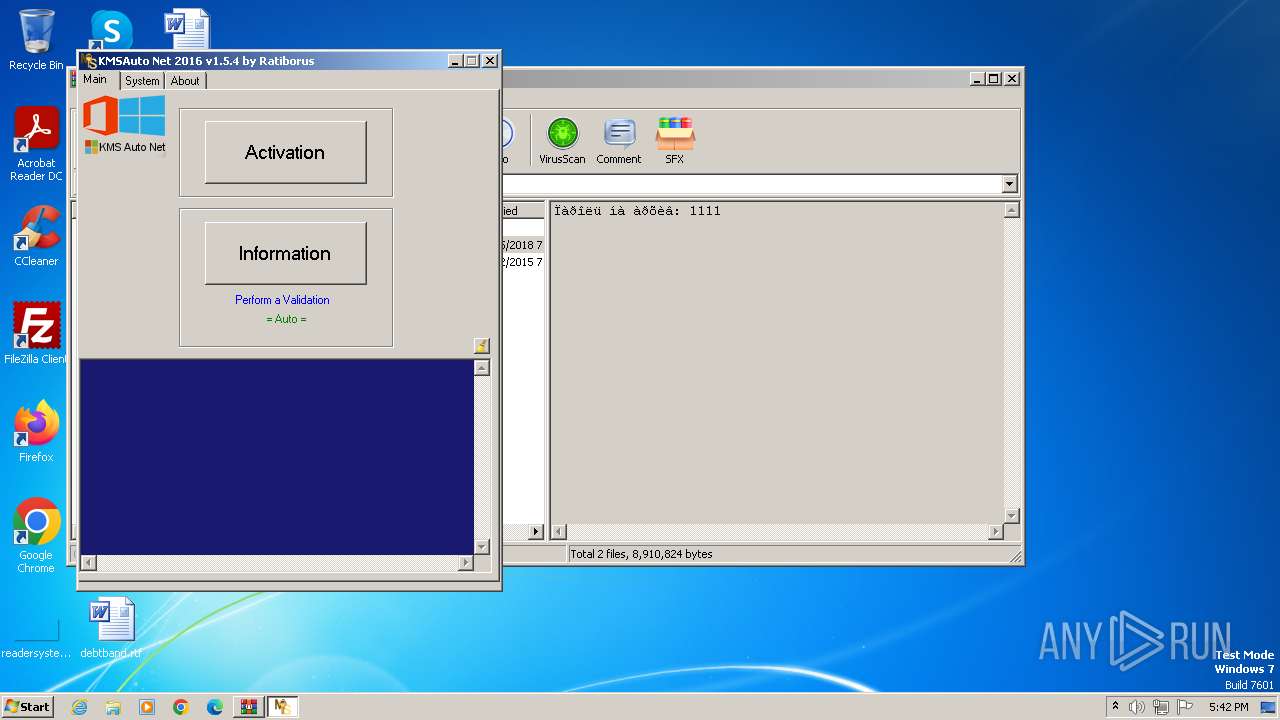
Creates or modifies Windows services
- KMSAuto Net.exe (PID: 2288)
Executes as Windows Service
- KMSSS.exe (PID: 3656)
- KMSSS.exe (PID: 3824)
Uses REG/REGEDIT.EXE to modify registry
- KMSAuto Net.exe (PID: 2288)
- cmd.exe (PID: 124)
- cmd.exe (PID: 2212)
Uses ROUTE.EXE to modify routing table
- cmd.exe (PID: 3112)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 2184)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3440)
Uses WMIC.EXE
- cmd.exe (PID: 4076)
- cmd.exe (PID: 328)
Reads the Internet Settings
- WMIC.exe (PID: 2300)
- WMIC.exe (PID: 3700)
INFO
Reads the computer name
- KMSAuto Net.exe (PID: 2288)
- KMSSS.exe (PID: 3656)
- KMSSS.exe (PID: 3824)
- FakeClient.exe (PID: 3400)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3640)
Creates files in the program directory
- cmd.exe (PID: 3288)
- wzt.dat (PID: 1912)
- KMSAuto Net.exe (PID: 2288)
- AESDecoder.exe (PID: 2456)
- bin.dat (PID: 2588)
- bin_x86.dat (PID: 3380)
- KMSSS.exe (PID: 3656)
- cmd.exe (PID: 2412)
- bin.dat (PID: 1836)
- AESDecoder.exe (PID: 1488)
- bin_x86.dat (PID: 3400)
- bin_x86.dat (PID: 3816)
- KMSSS.exe (PID: 3824)
- bin.dat (PID: 2300)
- wzt.dat (PID: 3168)
- cmd.exe (PID: 3528)
- AESDecoder.exe (PID: 128)
- bin_x86.dat (PID: 3084)
- wzt.dat (PID: 3020)
Reads product name
- KMSAuto Net.exe (PID: 2288)
Checks supported languages
- bin.dat (PID: 2588)
- AESDecoder.exe (PID: 2456)
- certmgr.exe (PID: 3448)
- certmgr.exe (PID: 2856)
- bin_x86.dat (PID: 3380)
- wzt.dat (PID: 3168)
- KMSSS.exe (PID: 3656)
- wzt.dat (PID: 1912)
- certmgr.exe (PID: 2008)
- certmgr.exe (PID: 3840)
- KMSAuto Net.exe (PID: 2288)
- bin.dat (PID: 1836)
- AESDecoder.exe (PID: 1488)
- bin_x86.dat (PID: 3400)
- KMSSS.exe (PID: 3824)
- bin_x86.dat (PID: 3816)
- FakeClient.exe (PID: 3400)
- bin.dat (PID: 2300)
- certmgr.exe (PID: 2308)
- certmgr.exe (PID: 3560)
- AESDecoder.exe (PID: 128)
- bin_x86.dat (PID: 3084)
- wzt.dat (PID: 3020)
Reads the machine GUID from the registry
- KMSAuto Net.exe (PID: 2288)
- KMSSS.exe (PID: 3656)
- KMSSS.exe (PID: 3824)
Creates files or folders in the user directory
- KMSAuto Net.exe (PID: 2288)
Reads Environment values
- KMSAuto Net.exe (PID: 2288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:10:15 09:59:34 |
| ZipCRC: | 0x0da1fbfe |
| ZipCompressedSize: | 5442961 |
| ZipUncompressedSize: | 8315752 |
| ZipFileName: | KMSAuto Net.exe |
Total processes
253
Monitored processes
125
Malicious processes
29
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | C:\Windows\System32\cmd.exe /D /c reg.exe DELETE HKLM\SYSTEM\CurrentControlSet\Services\KMSEmulator /f | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 128 | AESDecoder.exe | C:\ProgramData\KMSAuto\bin\AESDecoder.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 272 | C:\Windows\System32\cmd.exe /D /c del /F /Q "bin.dat" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 292 | C:\Windows\System32\Netsh Advfirewall Firewall delete rule name="0pen Port KMS" protocol=TCP | C:\Windows\System32\netsh.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | C:\Windows\System32\cmd.exe /D /c WMIC Path Win32_NetworkAdapter WHERE ServiceName="tapoas" get Manufacturer >"C:\Users\admin\AppData\Local\Temp\KMSSettmp95.tmp | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 576 | C:\Windows\System32\reg delete "HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 812 | "C:\Windows\System32\cmd.exe" /c rd "C:\ProgramData\KMSAuto" /S /Q | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 852 | "sc.exe" delete WinDivert1.1 | C:\Windows\System32\sc.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | route delete 100.100.0.10 0.0.0.0 | C:\Windows\System32\ROUTE.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | C:\Windows\System32\cmd.exe /D /c AESDecoder.exe | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
9 943
Read events
9 643
Write events
284
Delete events
16
Modification events
| (PID) Process: | (3640) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3640) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3640) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3640) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3640) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3640) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3640) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3640) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3640) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3640) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
57
Suspicious files
33
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3640 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3640.11070\KMSCleaner.exe | executable | |
MD5:13EA767A7BA607744EBEA7409B9F8649 | SHA256:A6E2CDC0E9426D50BD72D866BFC80E0FBA941EFB3AE6D1C564D409F57D1EB117 | |||
| 2288 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin.dat | executable | |
MD5:4D2E5AFFE6D1CCB42F6650FD57448A9B | SHA256:3CBF7C0231B3266B4A6946DCF9AAA39C2BF077F6E459CA9EAD39C516CBFCE74C | |||
| 2588 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror2.exe.aes | binary | |
MD5:A1A5AFA53B578DB6ABF400A88548F487 | SHA256:A9E76D637E0C0A65036D7F2D5C3D7B1C53218B94716554F4D9F6630DCFF8C75A | |||
| 3380 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\oas_sert.cer | binary | |
MD5:0041584E5F66762B1FA9BE8910D0B92B | SHA256:BB27684B569CBB72DEC63EA6FDEF8E5F410CDAEB73717EEE1B36478DBCFF94CC | |||
| 3380 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\x86TAP1\OemVista.inf | binary | |
MD5:41884571579F88540326252B81D0A9F8 | SHA256:A461B764E248D3E59A1A730FF94AF7E61121F5A02004E02B3B866AC8FD1689BE | |||
| 3380 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\x86TAP1\tap0901.cat | binary | |
MD5:AD8A5CBEC4F83AE4F850C793713EE770 | SHA256:878C1B205887B61906F6F4F8DA5783D2BB8756D0A39359288D09F65F983B27C2 | |||
| 2288 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\wzt.dat | executable | |
MD5:822DA2319294F2B768BFE9ED4EEBAC15 | SHA256:17B74D4EA905FAC0BA6857F78F47EE1E940675AF1BC27DED69FE2941318106EF | |||
| 2588 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror.exe | executable | |
MD5:2ED9C12A91E795804B1B770958C647AC | SHA256:CB56C248A38292C234D1AABE5E33A671FE8AE8AED28E0C8C4FBE767E4E7B82F5 | |||
| 2288 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin_x86.dat | executable | |
MD5:6C227B04F0605AF1A1B75F8FE16D1424 | SHA256:DCFDAB4ED4F5E5A821EB8FF9E85453A426AF3E725A0849CC4B0599746C879456 | |||
| 2456 | AESDecoder.exe | C:\ProgramData\KMSAuto\bin\KMSSS.exe | executable | |
MD5:01A80AAD5DABED1C1580F7E00213CF9D | SHA256:FD7499214ABAA13BF56D006AB7DE78EB8D6ADF17926C24ACE024D067049BC81D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Threats
Process | Message |
|---|---|
FakeClient.exe | WdfCoInstaller: [10/05/2023 17:42.48.748] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [10/05/2023 17:42.48.780] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [10/05/2023 17:42.48.780] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|