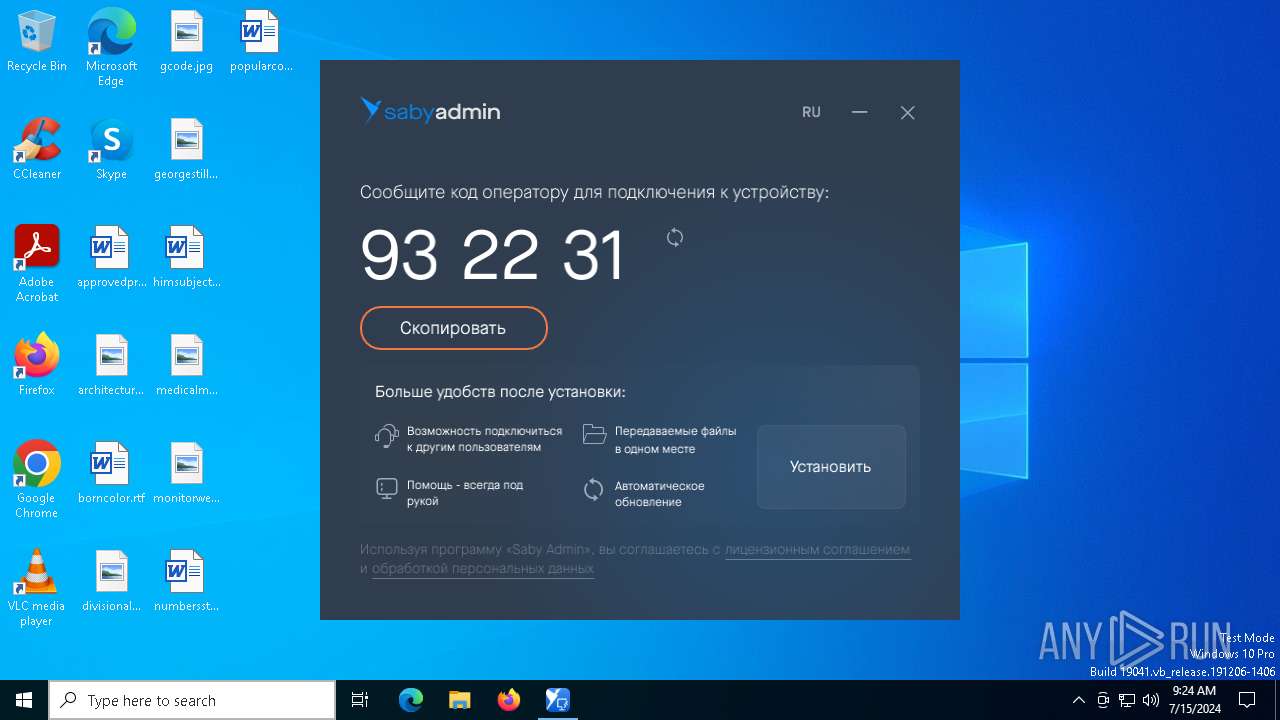
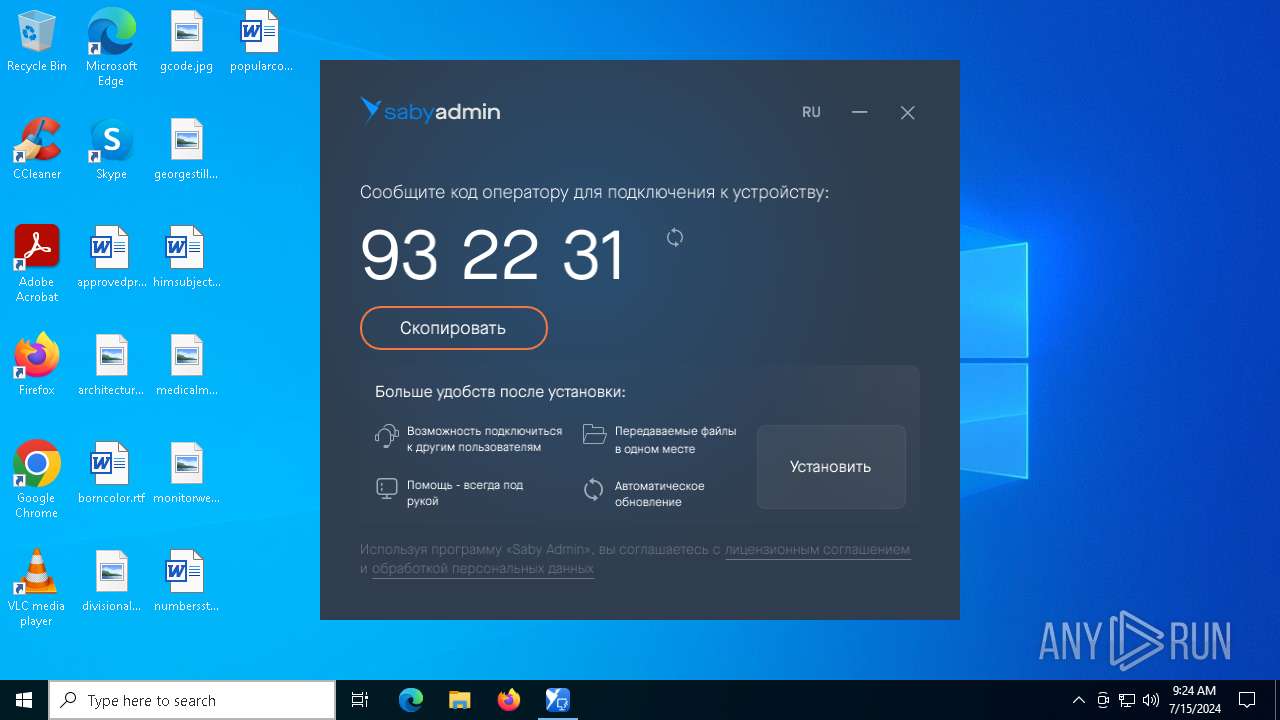
| File name: | SabyAdmin_1035490543.exe |
| Full analysis: | https://app.any.run/tasks/25bb4b89-5cd3-4f8b-9a43-3dbe6bc31599 |
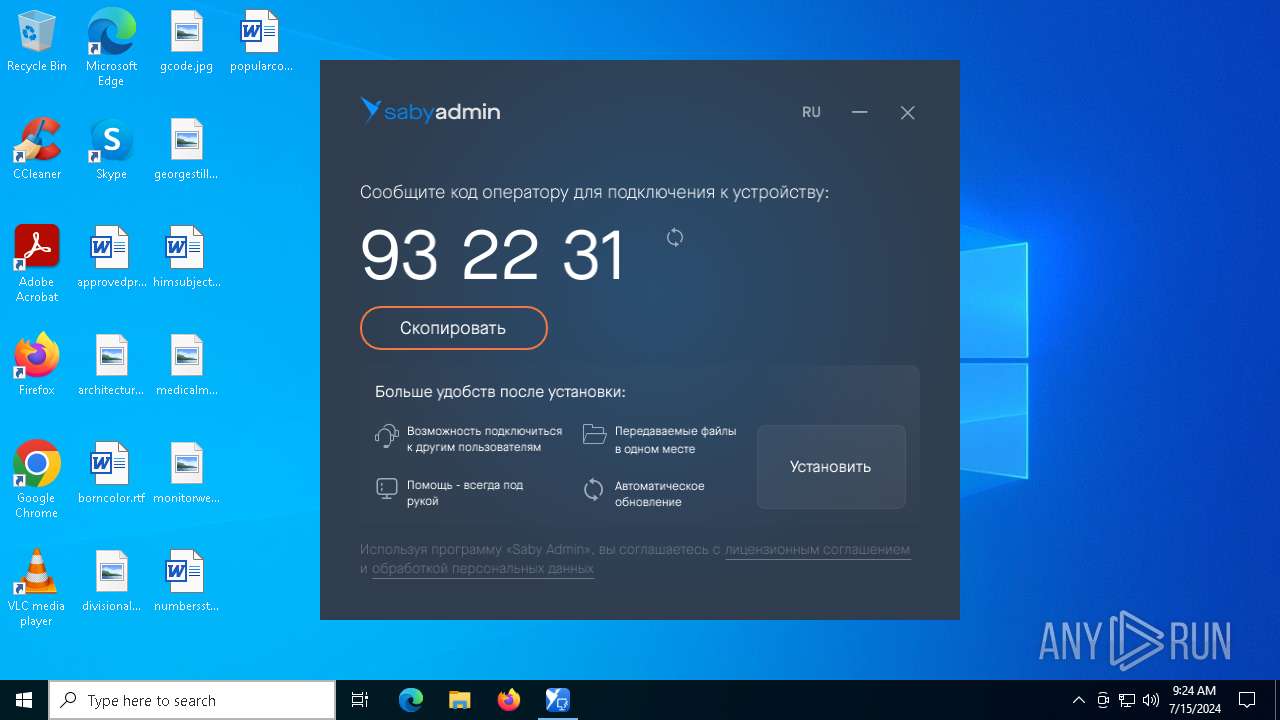
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2024, 09:23:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 3DD848872E1107F9F91577C412C17B4C |
| SHA1: | 9A9BB823E327EFDD4BAC72077578BE19A8876FDC |
| SHA256: | 8F1F6E381E415975DACEE000A6E12A35AE24B0FE7B56E2204D13048CF377ECBC |
| SSDEEP: | 98304:/86eKIRU0qx0eLcUaY/LlNtoOdKIqK/YNXXZkjxiL3BMesdg2+AS2C5wntl6meFd:HD//ehzqNLhf7UQsEFCyATZas6wZt3b |
MALICIOUS
Drops the executable file immediately after the start
- SabyAdmin_1035490543.exe (PID: 3168)
SUSPICIOUS
Application launched itself
- SabyAdmin_1035490543.exe (PID: 3168)
- SabyAdmin_1035490543.exe (PID: 6500)
- SabyAdmin_1035490543.exe (PID: 6612)
Reads security settings of Internet Explorer
- SabyAdmin_1035490543.exe (PID: 6500)
Reads the date of Windows installation
- SabyAdmin_1035490543.exe (PID: 6500)
Executes as Windows Service
- SabyAdmin_1035490543.exe (PID: 6612)
INFO
Checks supported languages
- SabyAdmin_1035490543.exe (PID: 3168)
- SabyAdmin_1035490543.exe (PID: 6500)
- SabyAdmin_1035490543.exe (PID: 6576)
- SabyAdmin_1035490543.exe (PID: 6612)
- SabyAdmin_1035490543.exe (PID: 6632)
Reads CPU info
- SabyAdmin_1035490543.exe (PID: 3168)
- SabyAdmin_1035490543.exe (PID: 6632)
Creates files in the program directory
- SabyAdmin_1035490543.exe (PID: 3168)
- SabyAdmin_1035490543.exe (PID: 6632)
Reads the machine GUID from the registry
- SabyAdmin_1035490543.exe (PID: 3168)
- SabyAdmin_1035490543.exe (PID: 6500)
- SabyAdmin_1035490543.exe (PID: 6576)
- SabyAdmin_1035490543.exe (PID: 6612)
- SabyAdmin_1035490543.exe (PID: 6632)
Reads the computer name
- SabyAdmin_1035490543.exe (PID: 3168)
- SabyAdmin_1035490543.exe (PID: 6500)
- SabyAdmin_1035490543.exe (PID: 6576)
- SabyAdmin_1035490543.exe (PID: 6612)
- SabyAdmin_1035490543.exe (PID: 6632)
Process checks computer location settings
- SabyAdmin_1035490543.exe (PID: 6500)
UPX packer has been detected
- SabyAdmin_1035490543.exe (PID: 6632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1981:04:02 21:14:20+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 13365248 |
| InitializedDataSize: | 352256 |
| UninitializedDataSize: | 51298304 |
| EntryPoint: | 0x3daa0e0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 24.3207.1.0 |
| ProductVersionNumber: | 24.3207.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Tensor |
| FileDescription: | SabyAdminInstaller |
| FileVersion: | 24.3207.1.0 |
| InternalName: | SabyAdminInstaller.exe |
| LegalCopyright: | TENSOR (c). All rights reserved. |
| OriginalFileName: | SabyAdminInstaller.exe |
| ProductName: | SabyAdminInstaller |
| ProductVersion: | 24.3207.1.0 |
Total processes
143
Monitored processes
7
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3168 | "C:\Users\admin\AppData\Local\Temp\SabyAdmin_1035490543.exe" | C:\Users\admin\AppData\Local\Temp\SabyAdmin_1035490543.exe | explorer.exe | ||||||||||||
User: admin Company: Tensor Integrity Level: MEDIUM Description: SabyAdminInstaller Exit code: 0 Version: 24.3207.1.0 Modules
| |||||||||||||||
| 6500 | C:\Users\admin\AppData\Local\Temp\SabyAdmin_1035490543.exe --log_file 09-23-56_SabyAdminInstaller --mode 10 --app_version 24.3207.1.0 --installer_mode_version 3 --no-silent --log_file_path C:\ProgramData\SabyAdmin --language en --raw_arguments AQAAADsAAABDOlxVc2Vyc1xhZG1pblxBcHBEYXRhXExvY2FsXFRlbXBcU2FieUFkbWluXzEwMzU0OTA1NDMuZXhlAA== | C:\Users\admin\AppData\Local\Temp\SabyAdmin_1035490543.exe | — | SabyAdmin_1035490543.exe | |||||||||||
User: admin Company: Tensor Integrity Level: MEDIUM Description: SabyAdminInstaller Exit code: 0 Version: 24.3207.1.0 Modules
| |||||||||||||||
| 6576 | "C:\Users\admin\AppData\Local\Temp\SabyAdmin_1035490543.exe" --app_version "24.3207.1.0" --force_set_double_start --force_use_uac_privilege --installer_mode_version 3 --language "en" --log_file "09-23-56_SabyAdminInstaller" --log_file_path "C:\ProgramData\SabyAdmin" --mode 10 --multi_start --privilege_elevation_state 1 --raw_arguments "AQAAADsAAABDOlxVc2Vyc1xhZG1pblxBcHBEYXRhXExvY2FsXFRlbXBcU2FieUFkbWluXzEwMzU0OTA1NDMuZXhlAA==" --no-silent | C:\Users\admin\AppData\Local\Temp\SabyAdmin_1035490543.exe | SabyAdmin_1035490543.exe | ||||||||||||
User: admin Company: Tensor Integrity Level: HIGH Description: SabyAdminInstaller Exit code: 0 Version: 24.3207.1.0 Modules
| |||||||||||||||
| 6612 | "C:\Users\admin\AppData\Local\Temp\SabyAdmin_1035490543.exe" --sess_id 1 --app_version "24.3207.1.0" --force_set_double_start --force_use_uac_privilege --installer_mode_version 3 --language "en" --log_file "09-23-56_SabyAdminInstaller" --log_file_path "C:\ProgramData\SabyAdmin" --mode 10 --multi_start --privilege_elevation_state 2 --raw_arguments "AQAAADsAAABDOlxVc2Vyc1xhZG1pblxBcHBEYXRhXExvY2FsXFRlbXBcU2FieUFkbWluXzEwMzU0OTA1NDMuZXhlAA==" --no-silent | C:\Users\admin\AppData\Local\Temp\SabyAdmin_1035490543.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Tensor Integrity Level: SYSTEM Description: SabyAdminInstaller Exit code: 0 Version: 24.3207.1.0 Modules
| |||||||||||||||
| 6632 | "C:\Users\admin\AppData\Local\Temp\SabyAdmin_1035490543.exe" --app_version "24.3207.1.0" --force_set_double_start --force_use_uac_privilege --installer_mode_version 3 --language "en" --log_file "09-23-56_SabyAdminInstaller" --log_file_path "C:\ProgramData\SabyAdmin" --mode 10 --multi_start --privilege_elevation_state 3 --raw_arguments "AQAAADsAAABDOlxVc2Vyc1xhZG1pblxBcHBEYXRhXExvY2FsXFRlbXBcU2FieUFkbWluXzEwMzU0OTA1NDMuZXhlAA==" --sess_id 1 --no-silent --just_run | C:\Users\admin\AppData\Local\Temp\SabyAdmin_1035490543.exe | SabyAdmin_1035490543.exe | ||||||||||||
User: SYSTEM Company: Tensor Integrity Level: SYSTEM Description: SabyAdminInstaller Version: 24.3207.1.0 Modules
| |||||||||||||||
| 7032 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7064 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 189
Read events
14 169
Write events
20
Delete events
0
Modification events
| (PID) Process: | (6500) SabyAdmin_1035490543.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6500) SabyAdmin_1035490543.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6500) SabyAdmin_1035490543.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6500) SabyAdmin_1035490543.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6576) SabyAdmin_1035490543.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\SabyAdmin_1035490543.exe |
| Operation: | write | Name: | DumpFolder |
Value: C:\ProgramData\SabyAdmin\dumps | |||
| (PID) Process: | (6576) SabyAdmin_1035490543.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\SabyAdmin_1035490543.exe |
| Operation: | write | Name: | DumpCount |
Value: 10 | |||
| (PID) Process: | (6576) SabyAdmin_1035490543.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\SabyAdmin_1035490543.exe |
| Operation: | write | Name: | DumpType |
Value: 2 | |||
| (PID) Process: | (6576) SabyAdmin_1035490543.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | SoftwareSASGeneration |
Value: 3 | |||
| (PID) Process: | (6576) SabyAdmin_1035490543.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\UIPI\Clipboard\ExceptionFormats |
| Operation: | write | Name: | CF_HDROP |
Value: 15 | |||
| (PID) Process: | (6576) SabyAdmin_1035490543.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\LanmanServer\Parameters |
| Operation: | write | Name: | DisableStrictNameChecking |
Value: 1 | |||
Executable files
0
Suspicious files
10
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | SabyAdmin_1035490543.exe | C:\ProgramData\Tensor\device.id | text | |
MD5:9A44CA526BE2D0D70934B96680B4387B | SHA256:B784FD74BCF140E62C15265E8FA54CC88BA493CAC273786BB7543939D509BA81 | |||
| 3168 | SabyAdmin_1035490543.exe | C:\ProgramData\SabyAdmin\db\AuthService-shm | binary | |
MD5:30F315F78277FF641E22A5BBA6E40776 | SHA256:D5A1B880621CBD23C72FFB643A9211E4B0C56BCE10E941F0C978CFCFB025C1BE | |||
| 3168 | SabyAdmin_1035490543.exe | C:\ProgramData\SabyAdmin\db\UserService-wal | binary | |
MD5:05C6F9203D076EE5BB633391E96950CD | SHA256:F88B0F0A1DF651C878A2279D9A30D67A4AB67EA74671935209FD3BAE7C667177 | |||
| 3168 | SabyAdmin_1035490543.exe | C:\ProgramData\SabyAdmin\logs\20240715\2024-07-15_09-23-56_SabyAdminInstaller-events.log | text | |
MD5:7762D1ADA4D24A4E842457D61E652A2C | SHA256:8597E3E29100EEFC37FCE5691B59B9192884B318F104F28825BB7ADBFB22E4EC | |||
| 3168 | SabyAdmin_1035490543.exe | C:\ProgramData\SabyAdmin\db\AuthService-wal | binary | |
MD5:B52222A9B1B6626971B60945F153A2DC | SHA256:C3D4C9A4635A47D80D3C2C6BFF6601C0B3EE19D7123FB5EFDA3A99D96E28292B | |||
| 3168 | SabyAdmin_1035490543.exe | C:\ProgramData\SabyAdmin\db\DB_Status_saby-admin-installer | binary | |
MD5:2B5A30DCE6C0EE14A955EC2BD2198297 | SHA256:710E4603E8029440B4748F48D318BFD8F627F8F2909977C0E9828422243C5D14 | |||
| 6632 | SabyAdmin_1035490543.exe | C:\ProgramData\SabyAdmin\_settings | compressed | |
MD5:873F9015A020A1E61068B78A3B2CB53D | SHA256:3805AA21D7753BC4DEF6A461C2E8EAAD1599B049F13F1714D9FAF6198DCCBDD5 | |||
| 3168 | SabyAdmin_1035490543.exe | C:\ProgramData\SabyAdmin\db\AuthService | sqlite | |
MD5:A316359AAB06F59ABE55FC7ED2C56149 | SHA256:0287A06872ADF6194586DA9B8B7F8A9CFECC0E01CECC55347146C3556AFF1A34 | |||
| 3168 | SabyAdmin_1035490543.exe | C:\ProgramData\SabyAdmin\db\UserService | sqlite | |
MD5:A4B7BC65ACFB20728692B28BFF96D09F | SHA256:F05CE41E3461B5A802BC281B36B2B4435875A797F89A394FAA3614560D770BC1 | |||
| 3168 | SabyAdmin_1035490543.exe | C:\ProgramData\SabyAdmin\db\UserService-shm | binary | |
MD5:C7CA77B492D011CB275F029E97B61DF4 | SHA256:CE286C8C66A492F7DB91C8CBDC54883974007FC67CEF3D74B00F400B05AADC4F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
72
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2456 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4752 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4752 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2452 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1644 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4752 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
376 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2340 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.35:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4656 | SearchApp.exe | 92.123.104.35:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2456 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
rhm.sbis.ru |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |