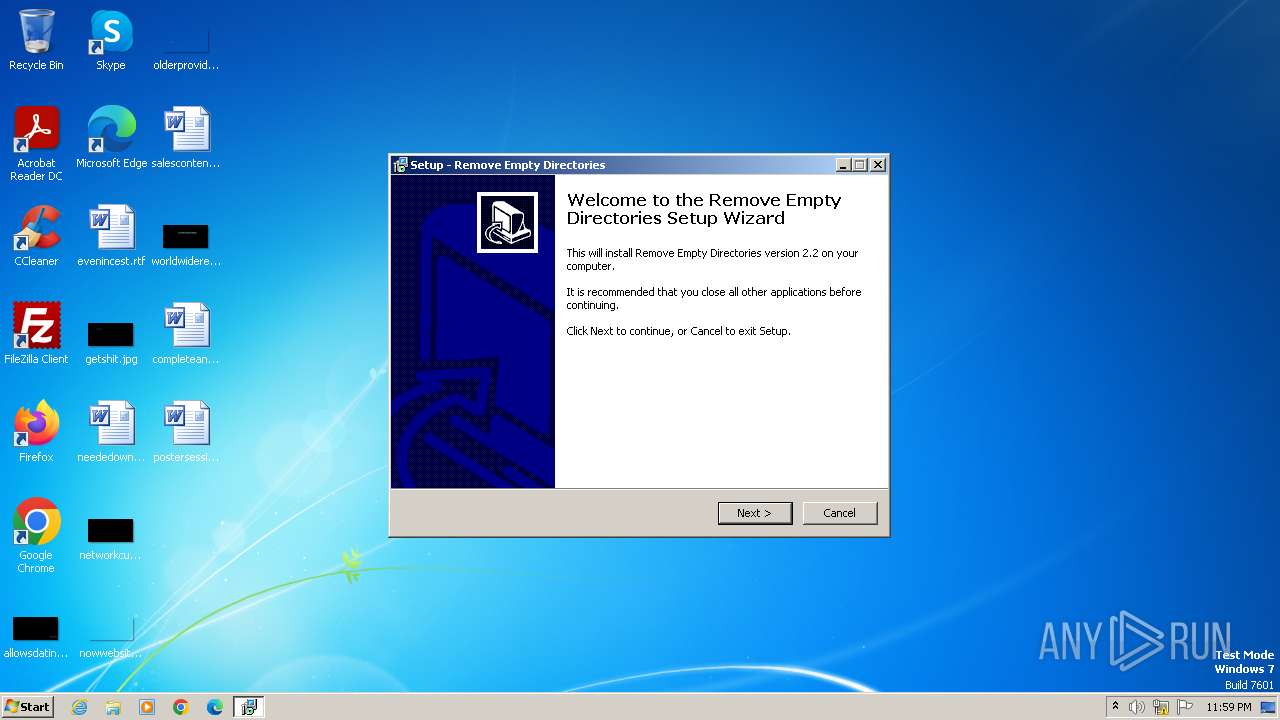
| File name: | red-v2.2-setup.exe |
| Full analysis: | https://app.any.run/tasks/31d95934-e5e6-4a6f-a010-dd122d406ac8 |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2023, 23:59:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0A0DD3ECD3A1A4202858D9C0884A540D |
| SHA1: | 60CB4399ABFEA5AA8BE713568A4E4D5CF4239586 |
| SHA256: | 8F163A667304E6D86C306CAB637B6F344AFDB166FB4ED66190CF10FCBB1B91D3 |
| SSDEEP: | 12288:CrGdJ1rsxXLI9xedaioIPvrTV0LS2dBVBXuZguAp7Tucl:CSdDrwXk9xAaioIPvrJiS2dBVBXuKuC9 |
MALICIOUS
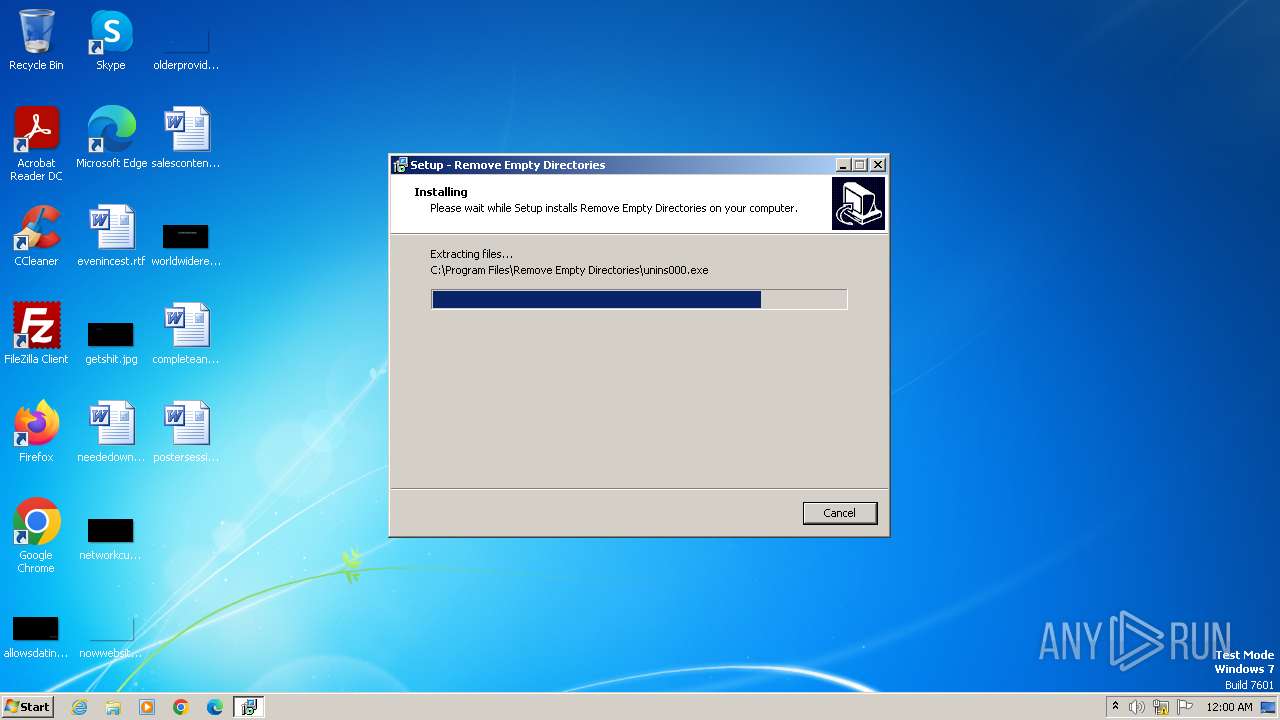
Drops the executable file immediately after the start
- red-v2.2-setup.exe (PID: 1996)
- red-v2.2-setup.exe (PID: 2928)
- red-v2.2-setup.tmp (PID: 1560)
Actions looks like stealing of personal data
- RED2.exe (PID: 600)
SUSPICIOUS
Reads the Windows owner or organization settings
- red-v2.2-setup.tmp (PID: 1560)
Process drops legitimate windows executable
- red-v2.2-setup.tmp (PID: 1560)
Reads the Internet Settings
- red-v2.2-setup.tmp (PID: 3264)
INFO
Create files in a temporary directory
- red-v2.2-setup.exe (PID: 1996)
- red-v2.2-setup.exe (PID: 2928)
- red-v2.2-setup.tmp (PID: 1560)
Checks supported languages
- red-v2.2-setup.exe (PID: 1996)
- red-v2.2-setup.tmp (PID: 3264)
- red-v2.2-setup.exe (PID: 2928)
- red-v2.2-setup.tmp (PID: 1560)
- RED2.exe (PID: 600)
Reads the computer name
- red-v2.2-setup.tmp (PID: 3264)
- red-v2.2-setup.tmp (PID: 1560)
- RED2.exe (PID: 600)
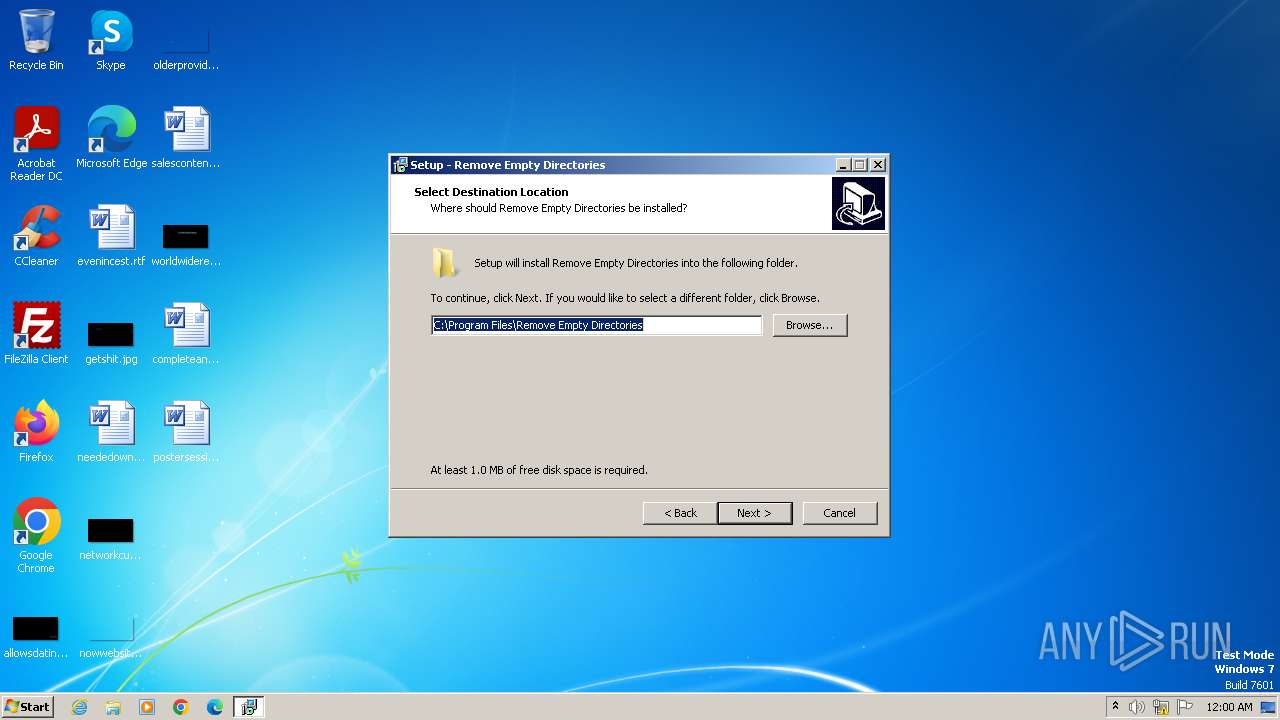
Creates files in the program directory
- red-v2.2-setup.tmp (PID: 1560)
Reads the machine GUID from the registry
- RED2.exe (PID: 600)
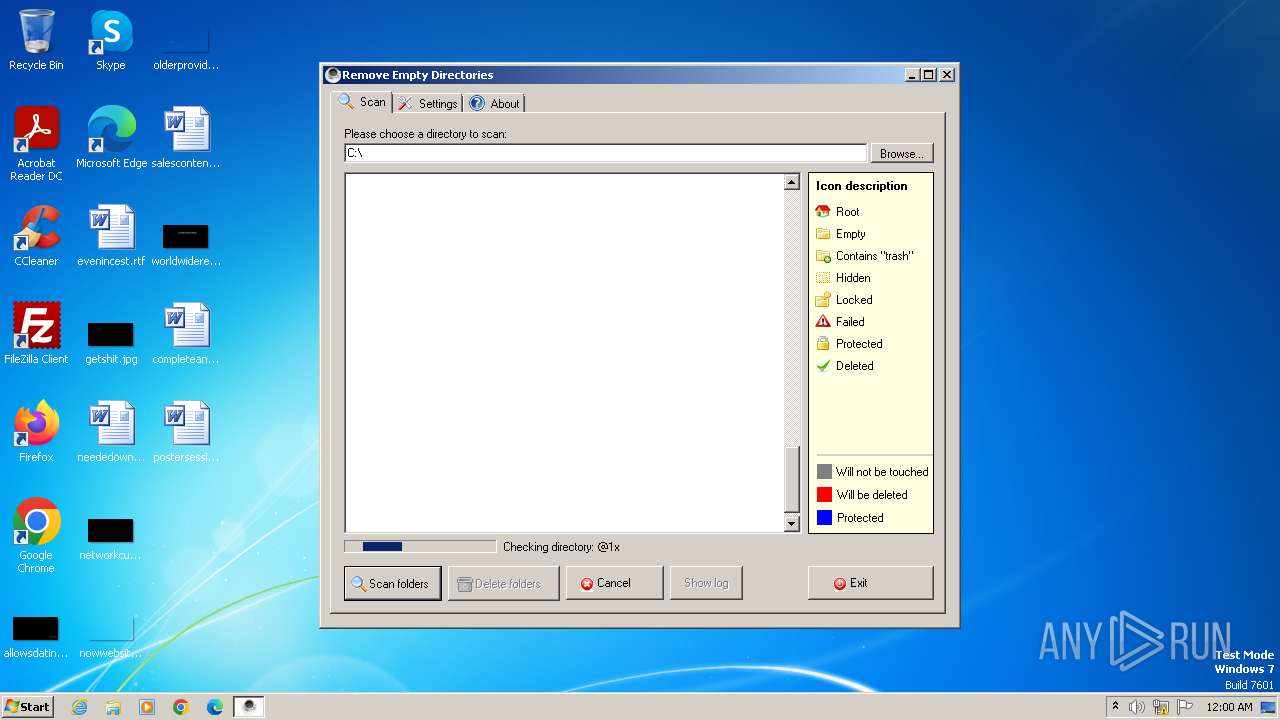
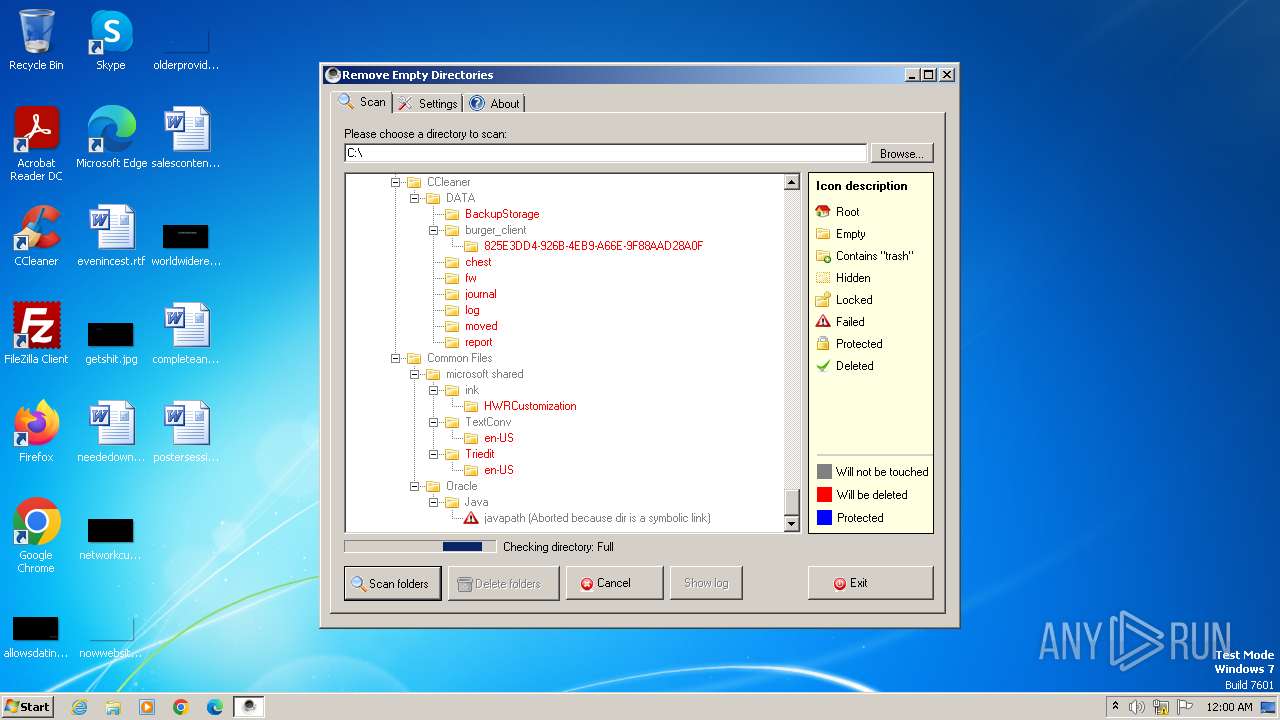
Checks transactions between databases Windows and Oracle
- RED2.exe (PID: 600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c40 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
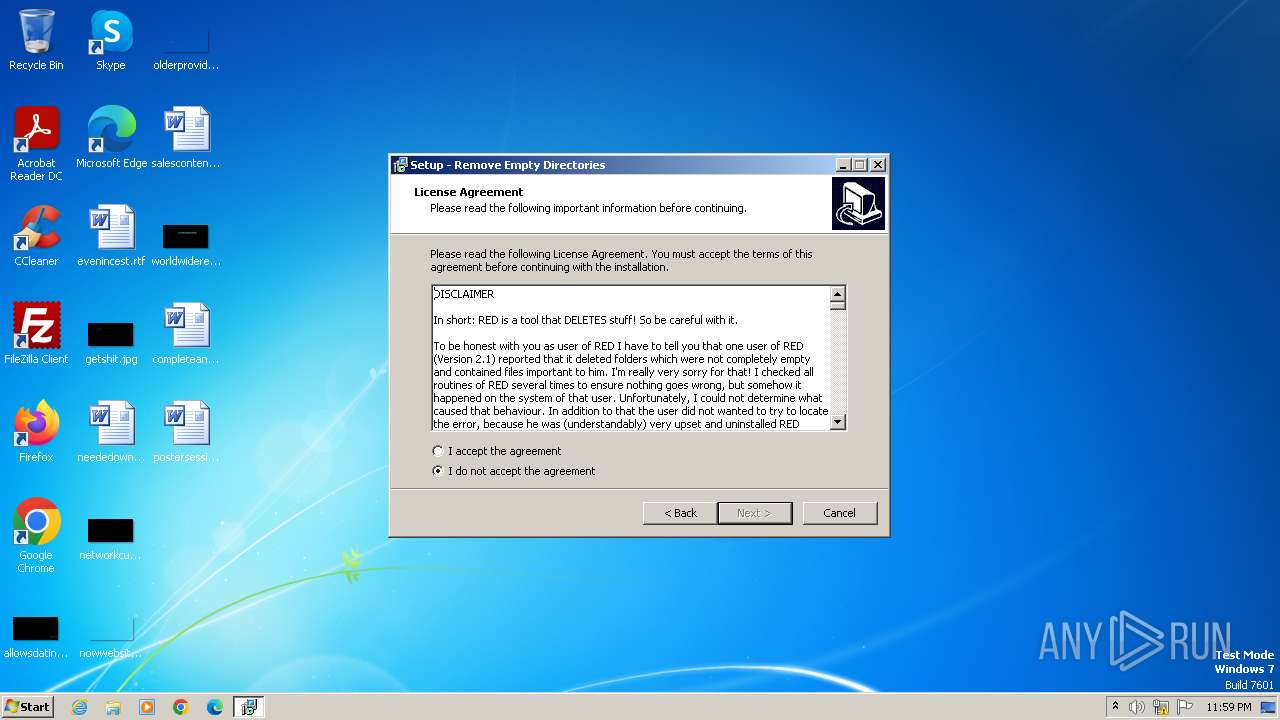
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Jonas John |
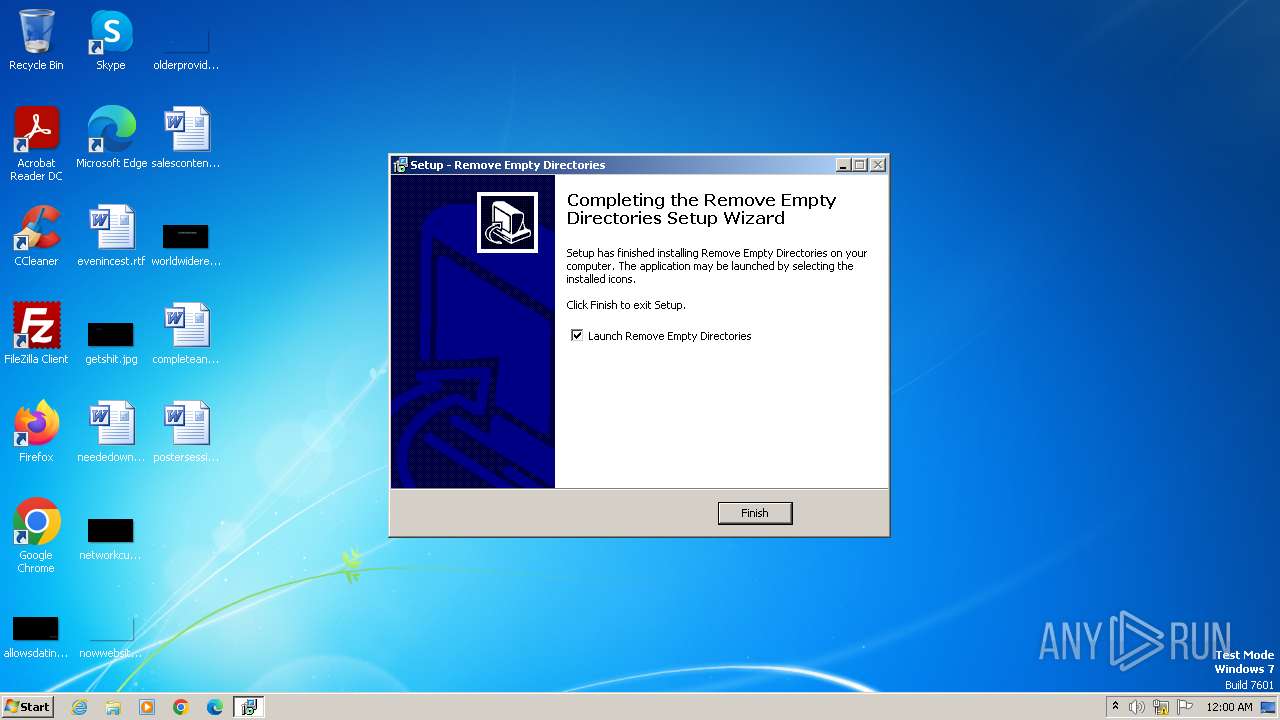
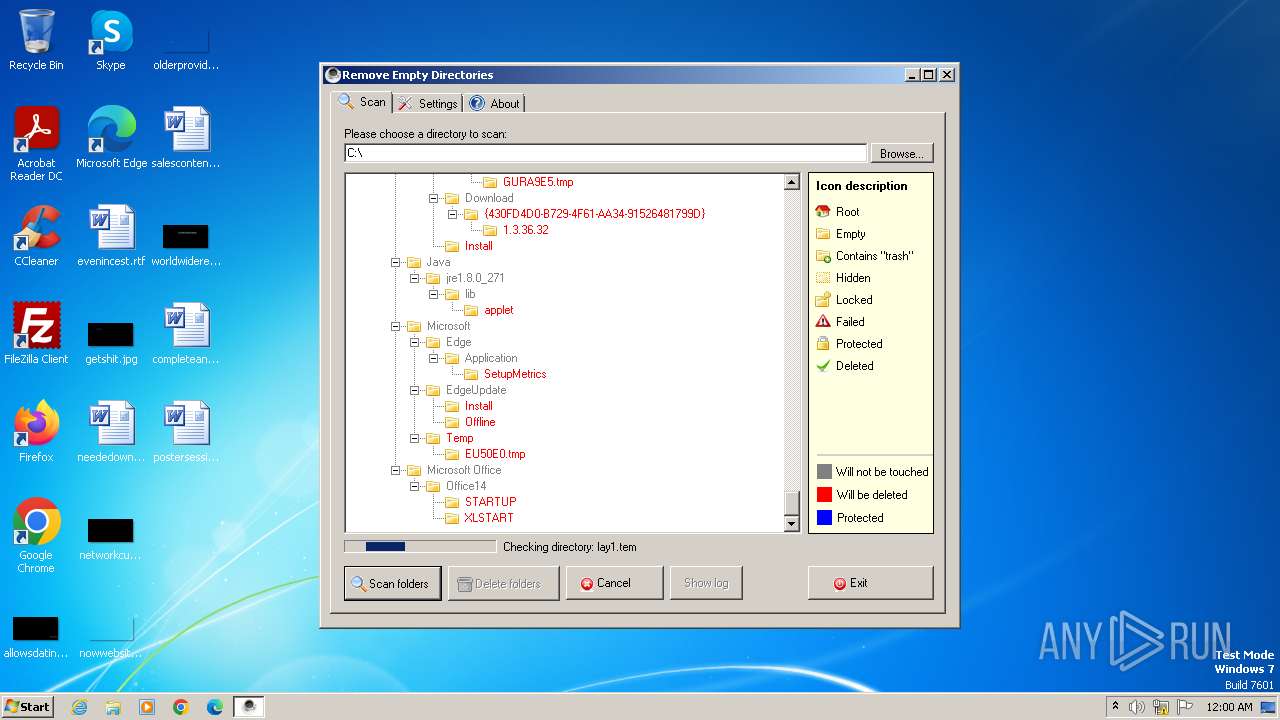
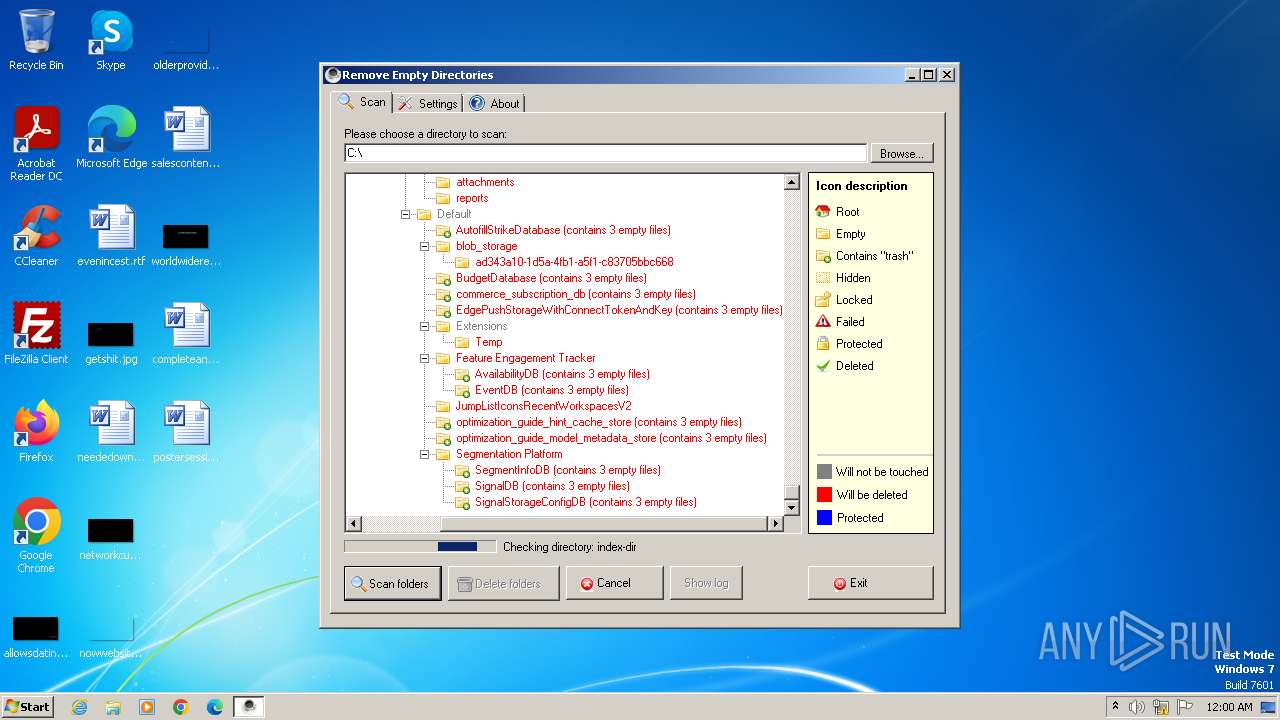
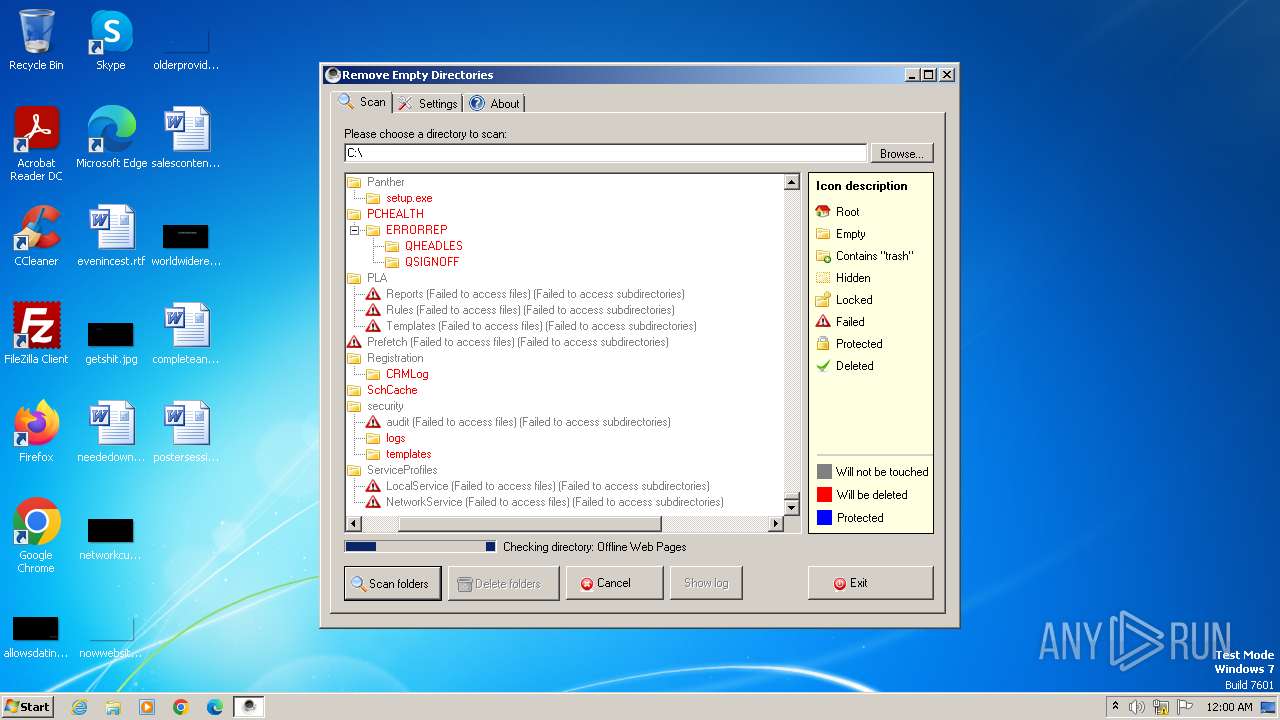
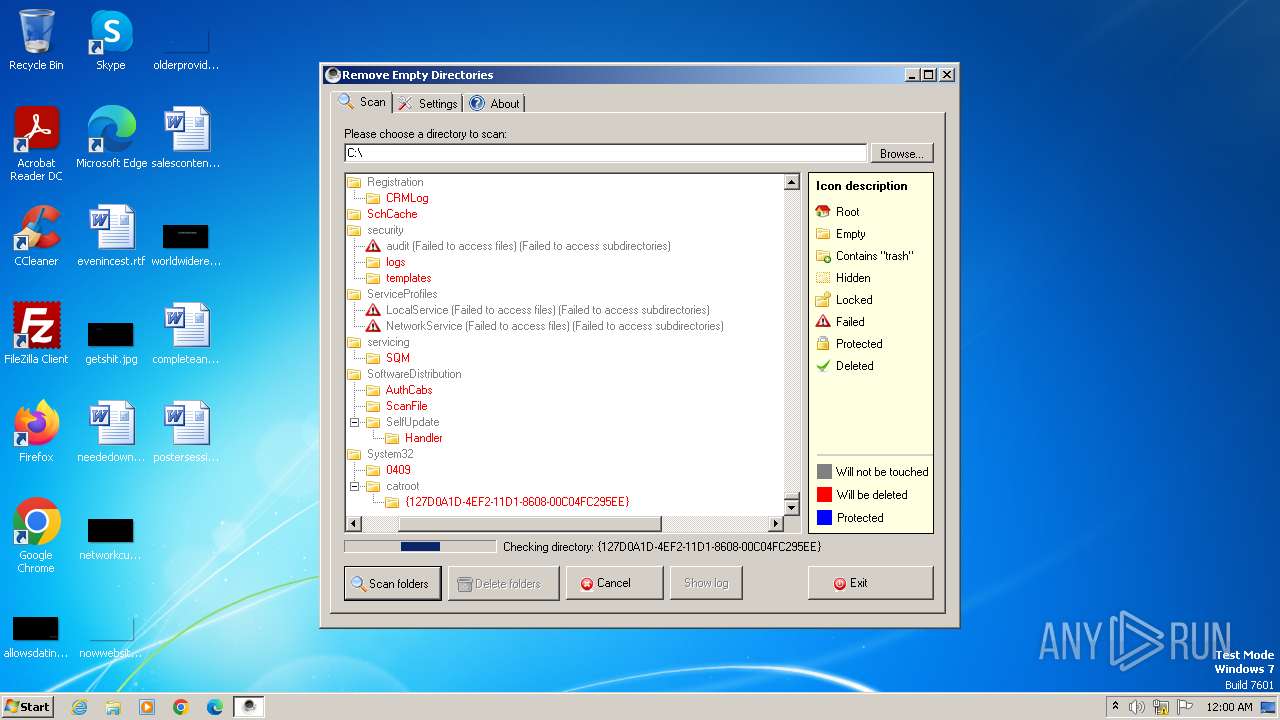
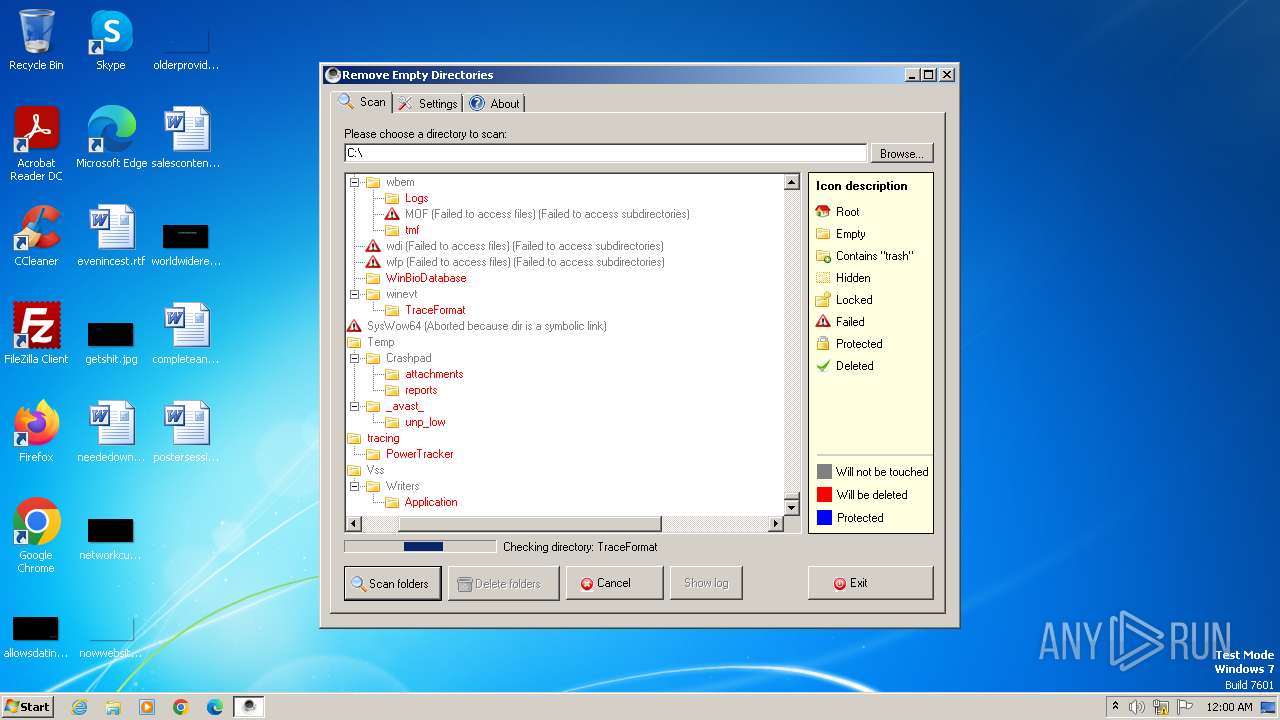
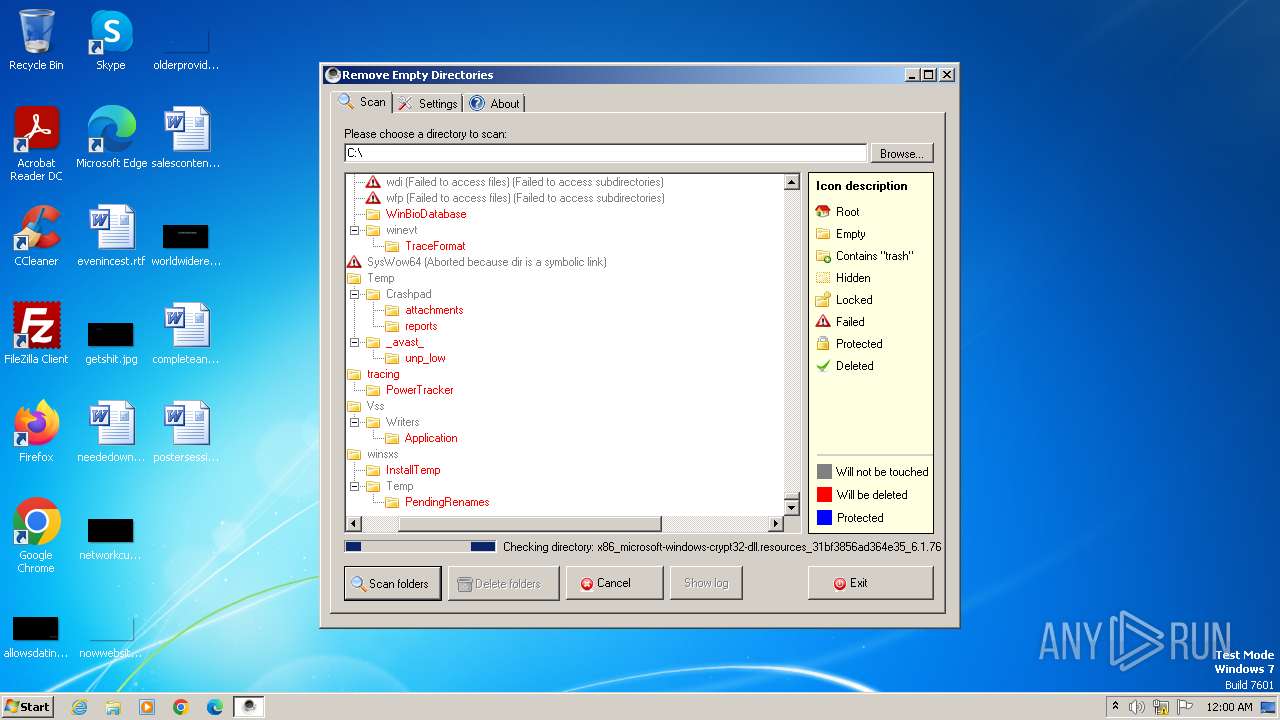
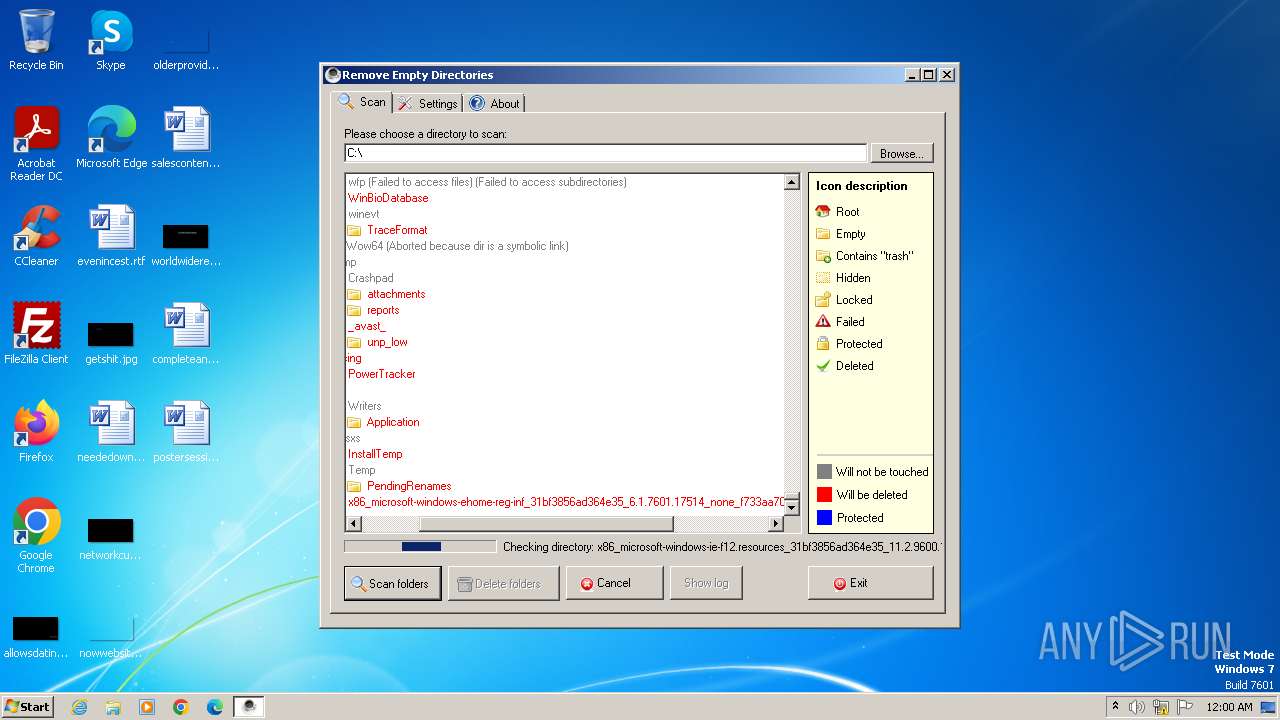
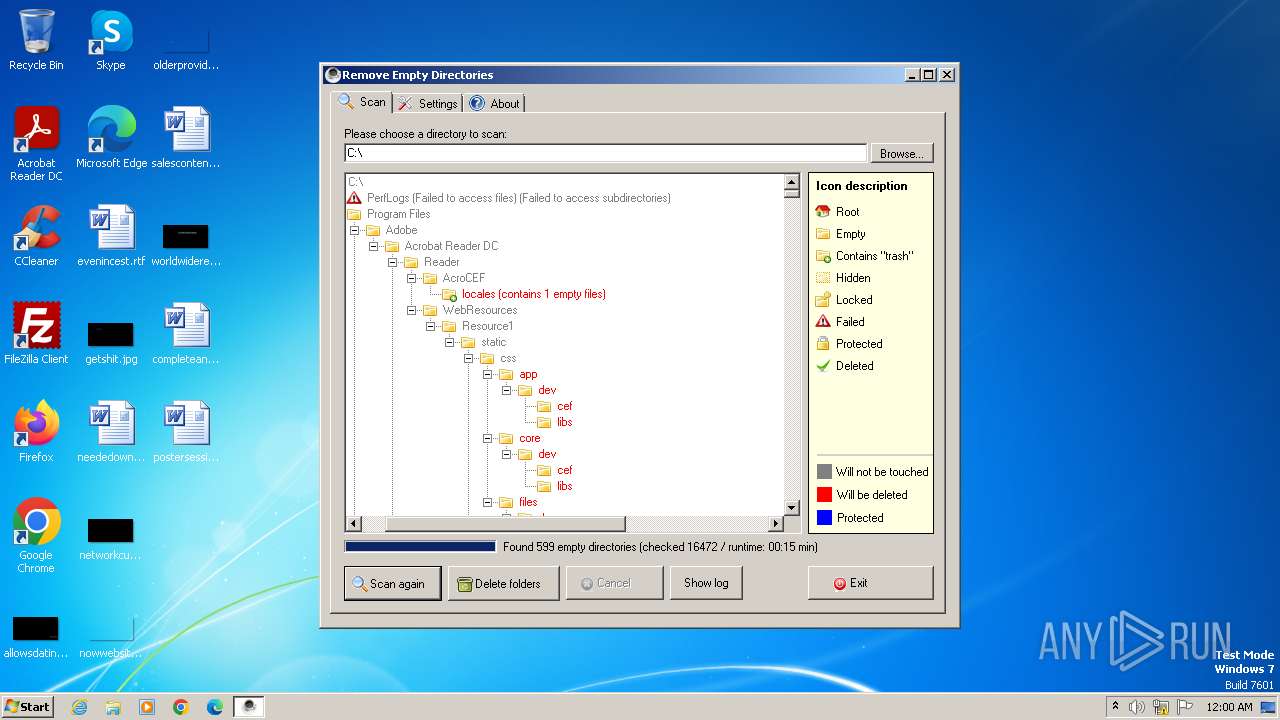
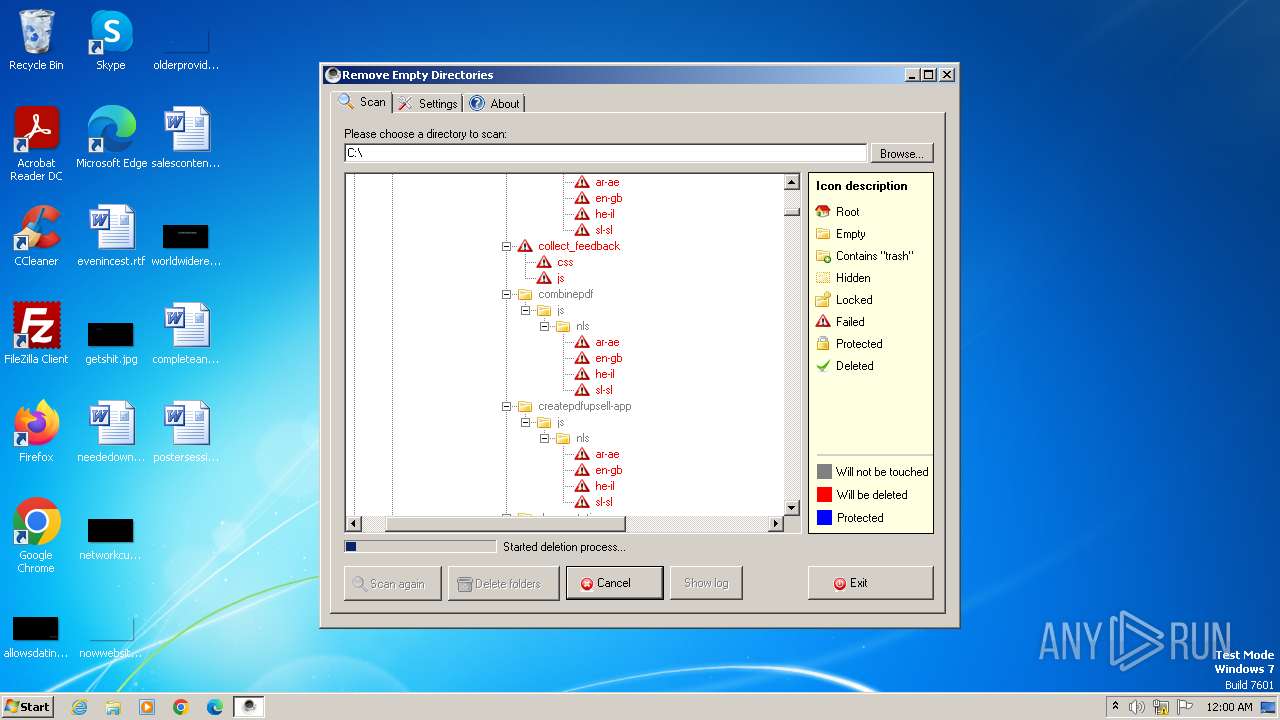
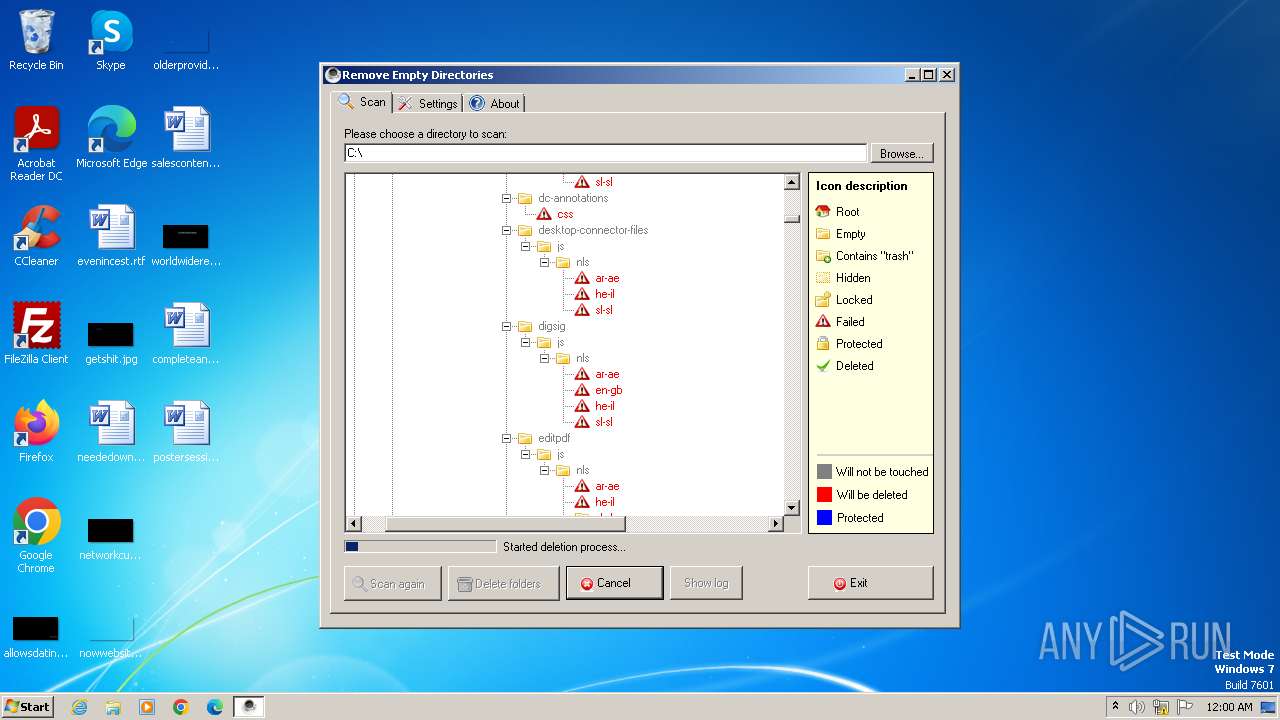
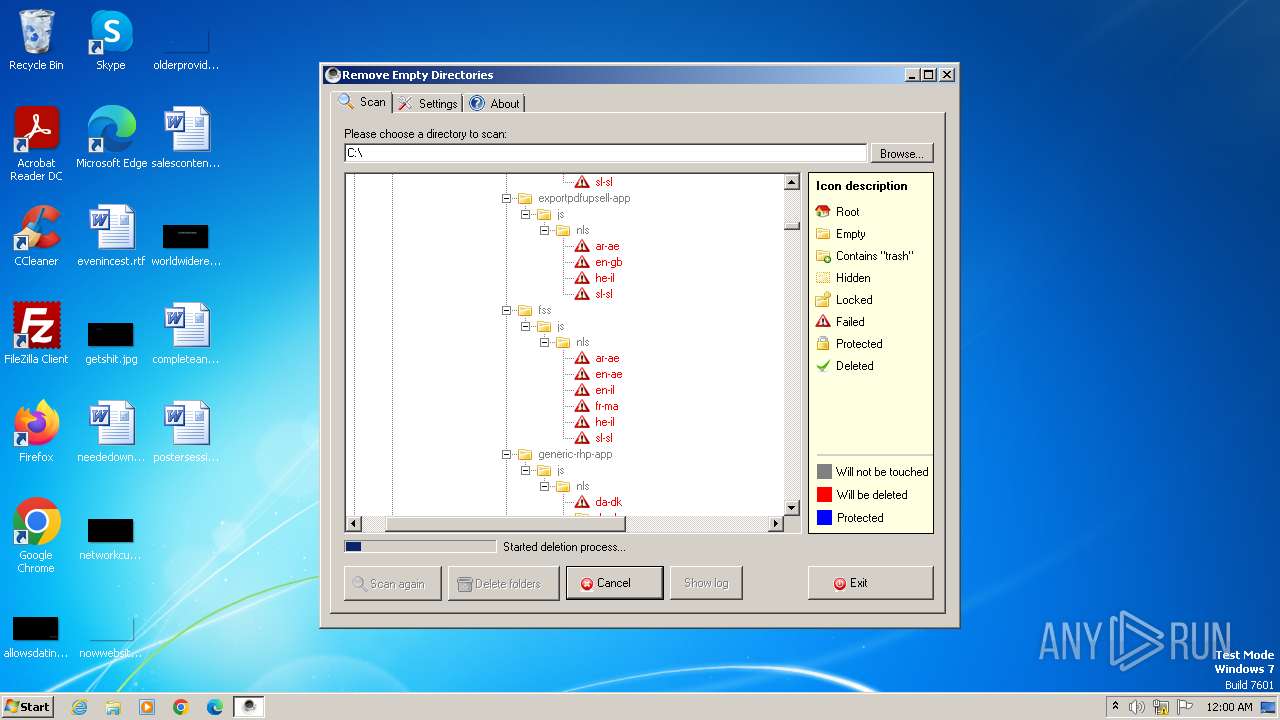
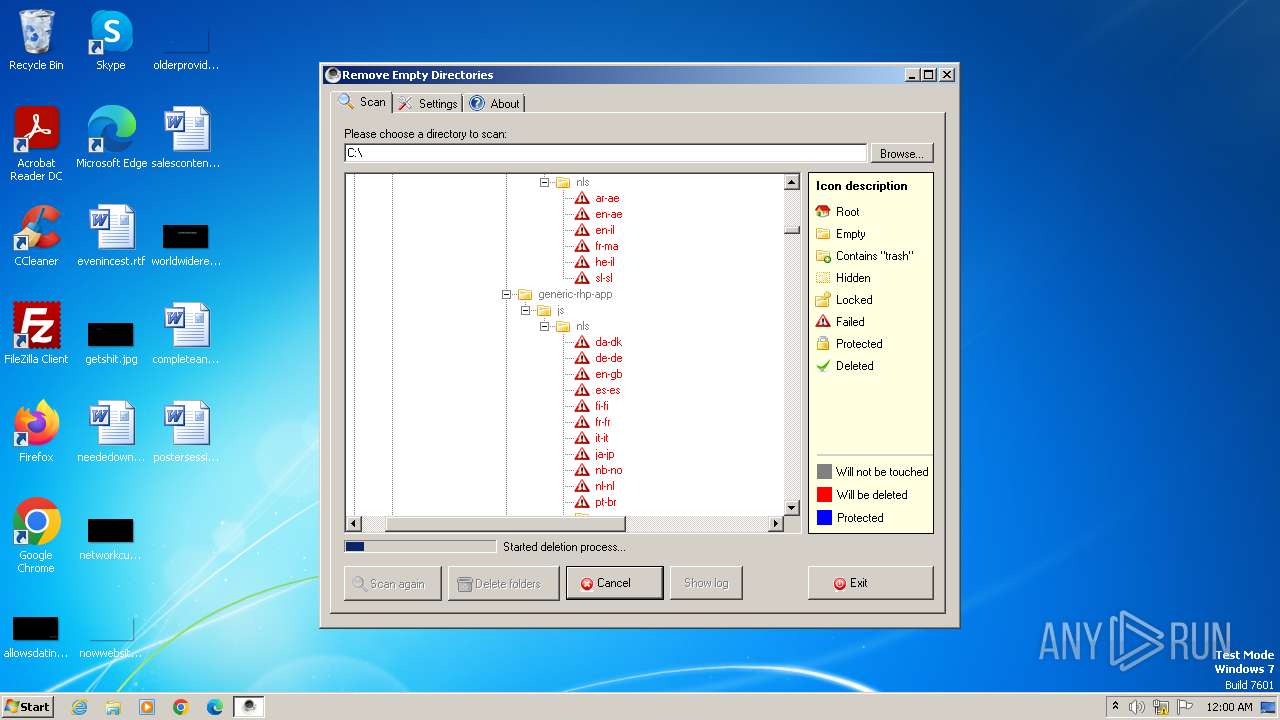
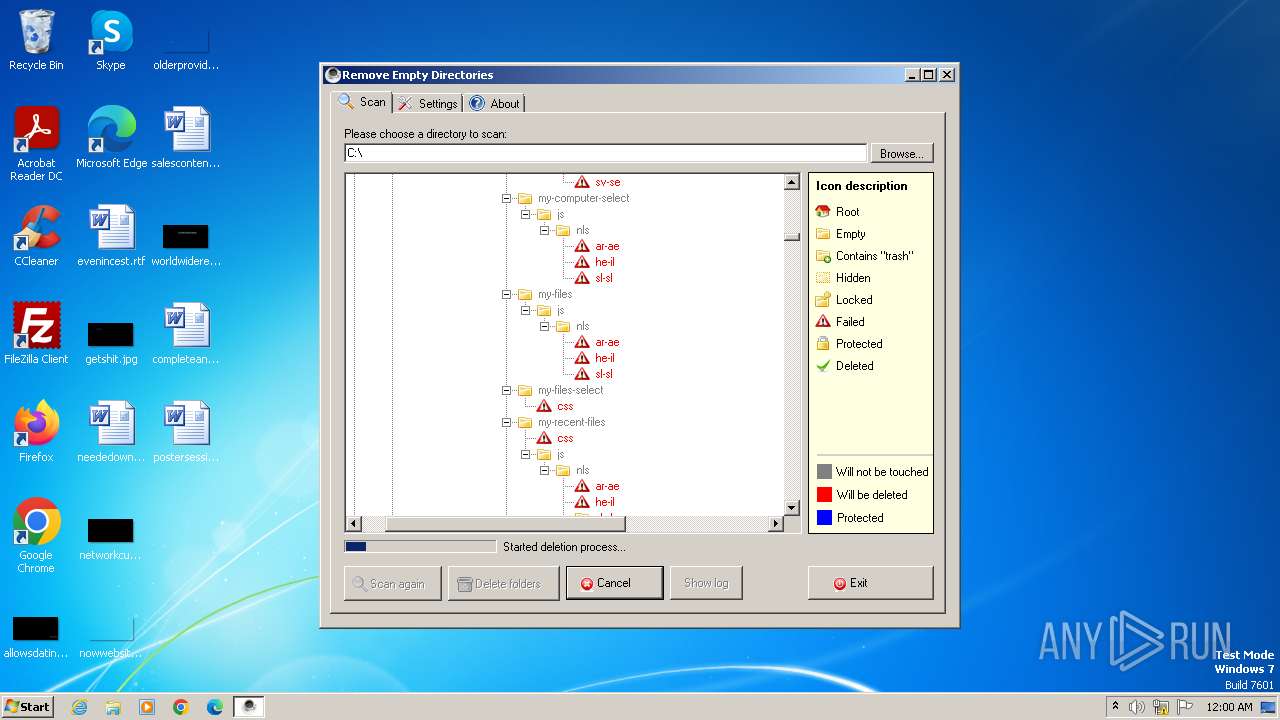
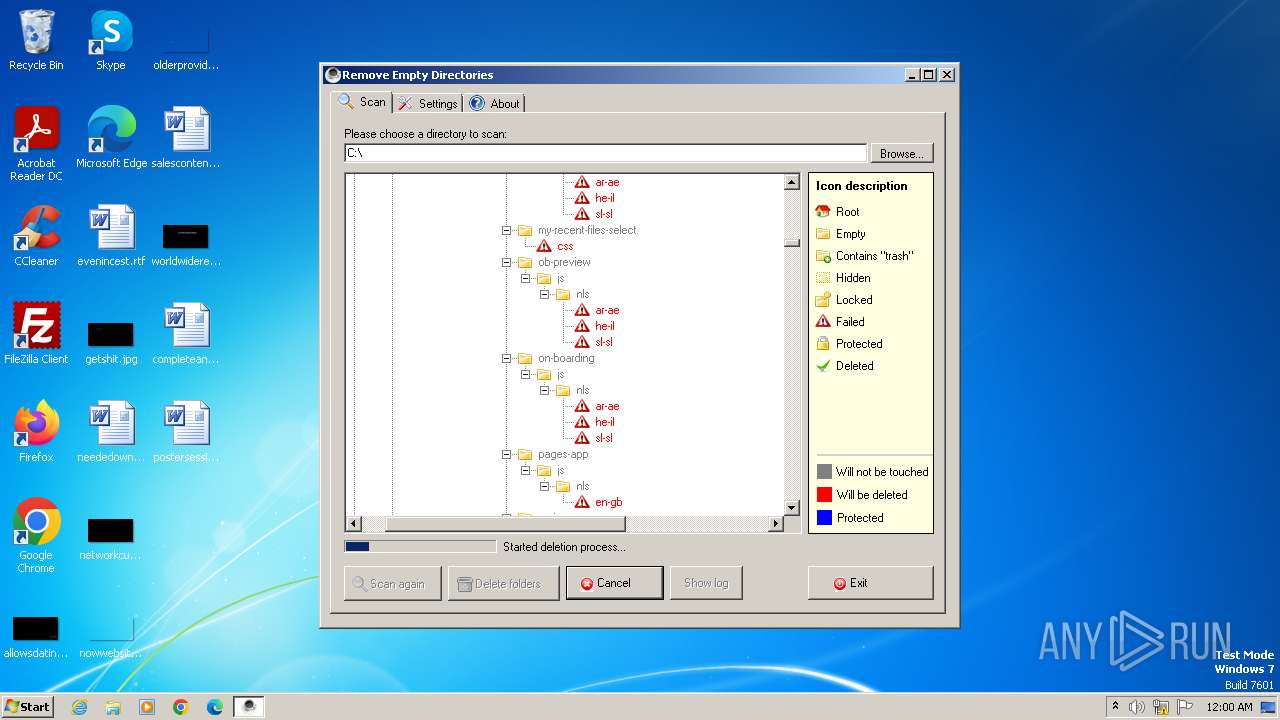
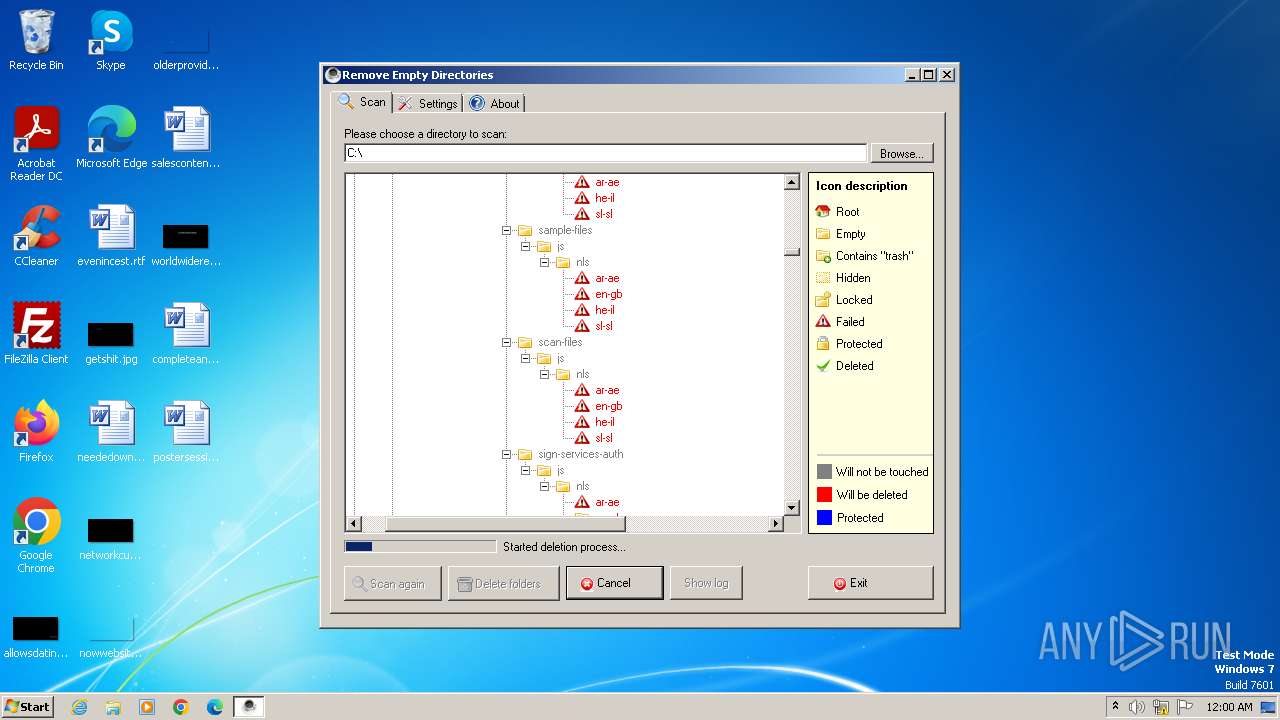
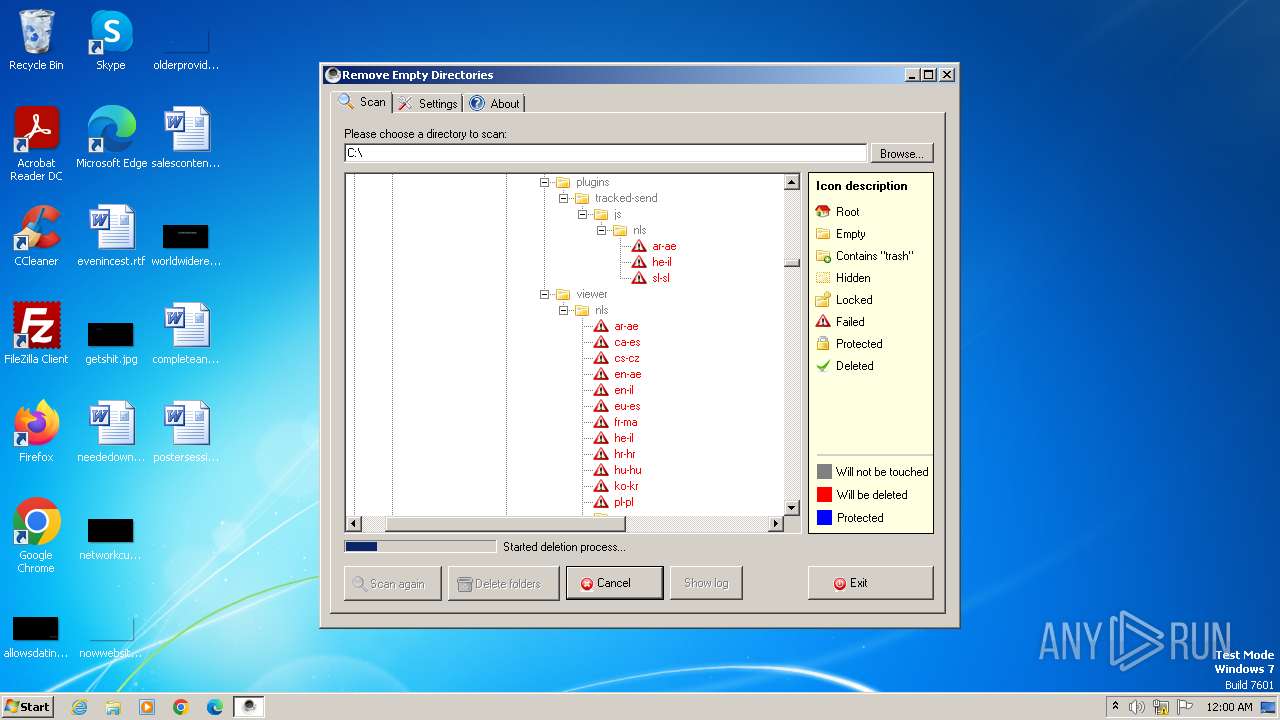
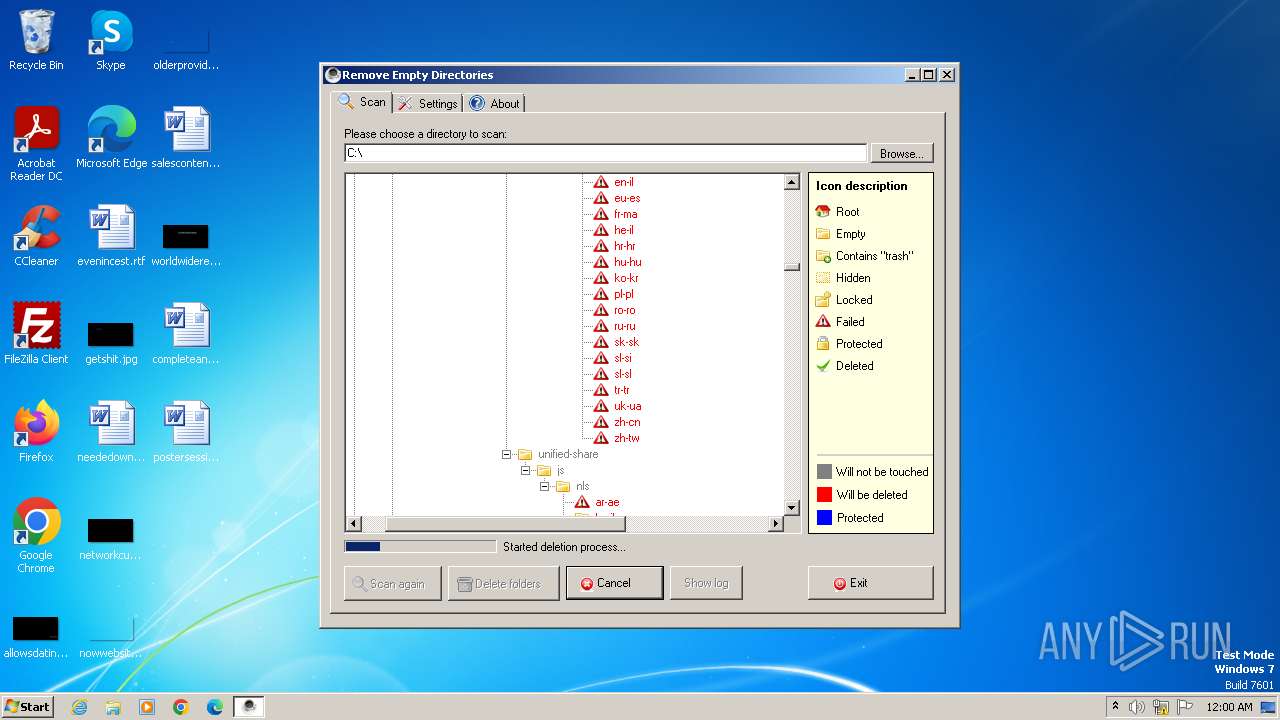
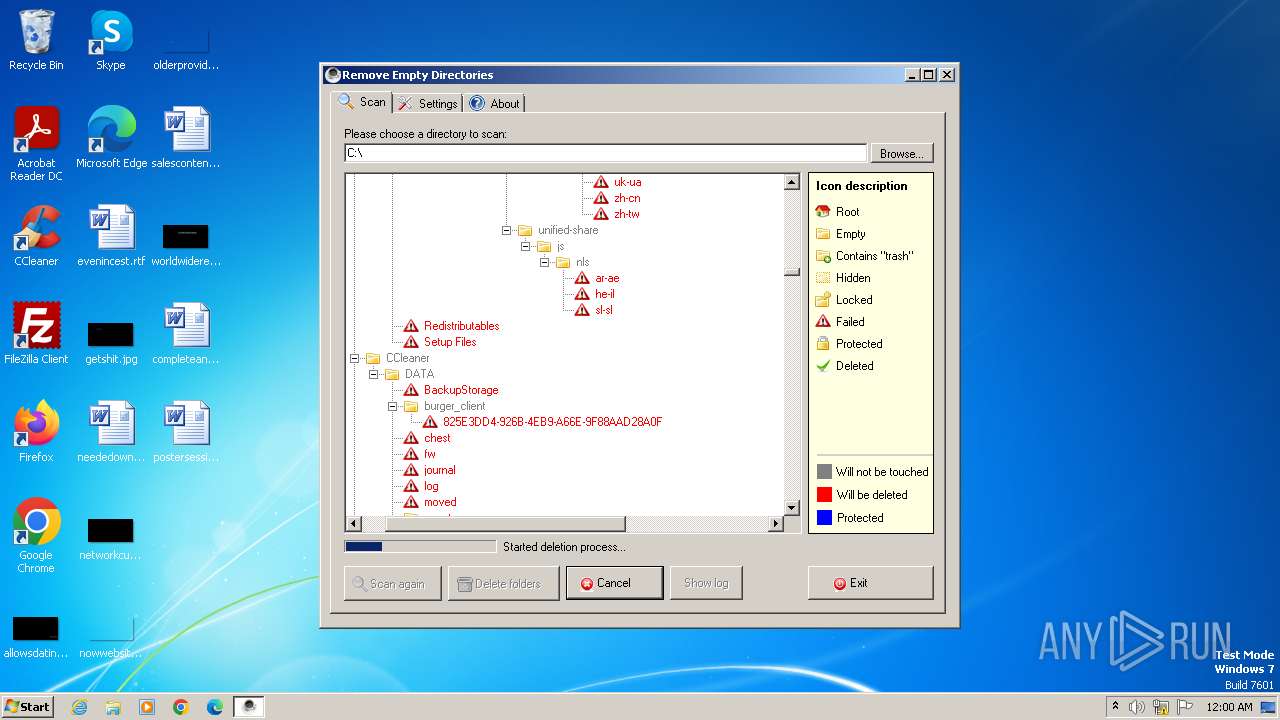
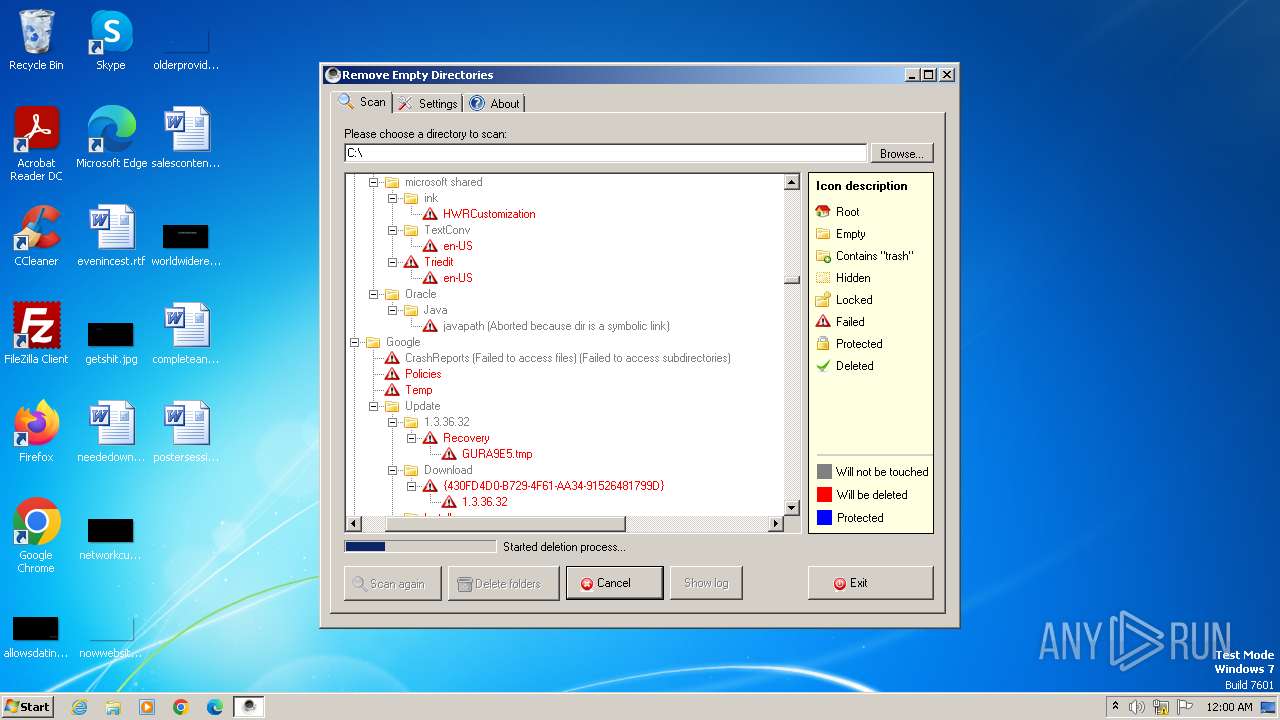
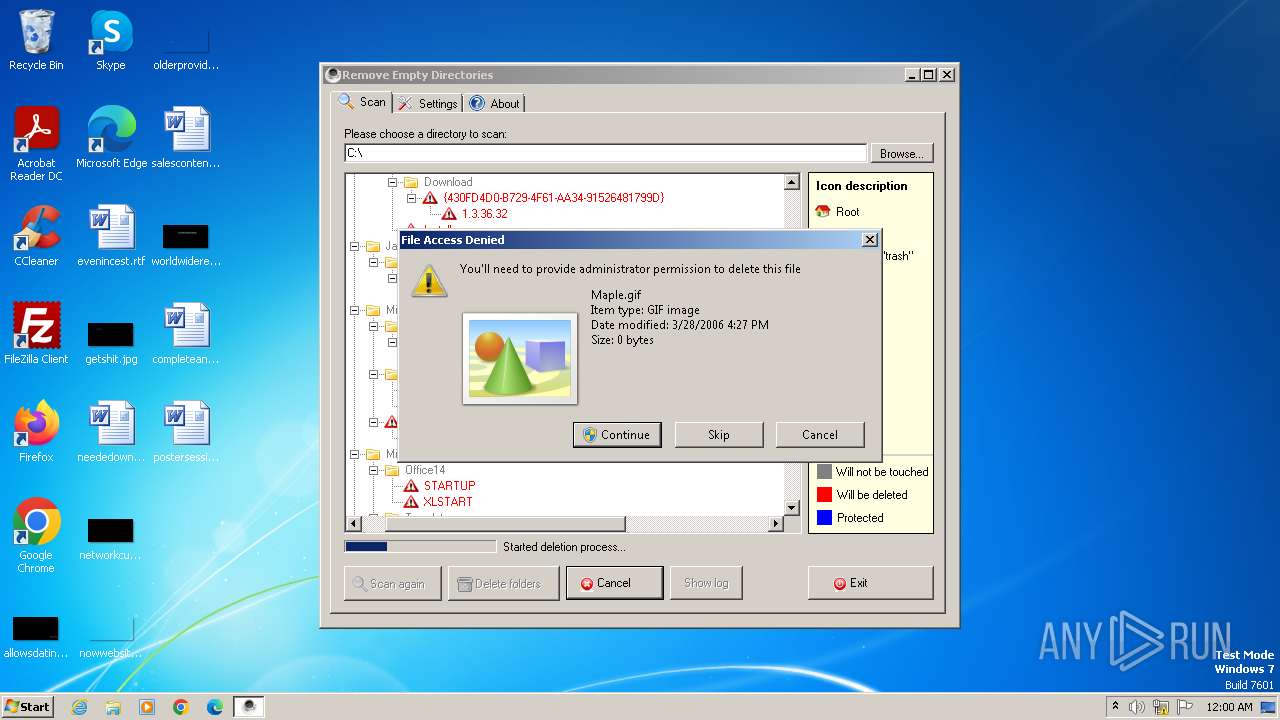
| FileDescription: | Remove Empty Directories Setup |
| FileVersion: | |
| LegalCopyright: | Remove Empty Directories © Jonas John 2006-2011 |
| ProductName: | Remove Empty Directories |
| ProductVersion: | 2.2 |
Total processes
46
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
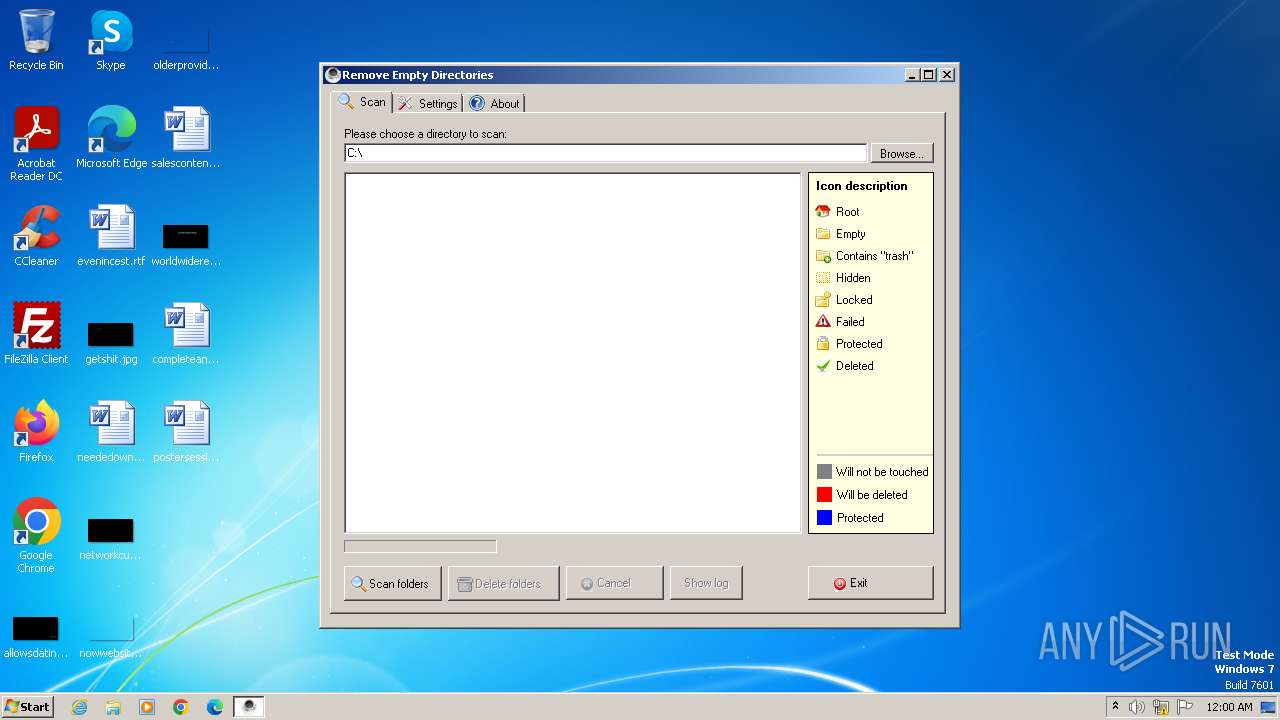
| 600 | "C:\Program Files\Remove Empty Directories\RED2.exe" | C:\Program Files\Remove Empty Directories\RED2.exe | red-v2.2-setup.tmp | ||||||||||||
User: admin Company: Remove Empty Directories Integrity Level: MEDIUM Description: Remove Empty Directories Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\Temp\is-DUQ9Q.tmp\red-v2.2-setup.tmp" /SL5="$1601E2,156490,54272,C:\Users\admin\AppData\Local\Temp\red-v2.2-setup.exe" /SPAWNWND=$190194 /NOTIFYWND=$1B0142 | C:\Users\admin\AppData\Local\Temp\is-DUQ9Q.tmp\red-v2.2-setup.tmp | — | red-v2.2-setup.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1996 | "C:\Users\admin\AppData\Local\Temp\red-v2.2-setup.exe" | C:\Users\admin\AppData\Local\Temp\red-v2.2-setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Jonas John Integrity Level: MEDIUM Description: Remove Empty Directories Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2928 | "C:\Users\admin\AppData\Local\Temp\red-v2.2-setup.exe" /SPAWNWND=$190194 /NOTIFYWND=$1B0142 | C:\Users\admin\AppData\Local\Temp\red-v2.2-setup.exe | red-v2.2-setup.tmp | ||||||||||||
User: admin Company: Jonas John Integrity Level: HIGH Description: Remove Empty Directories Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3264 | "C:\Users\admin\AppData\Local\Temp\is-B5D10.tmp\red-v2.2-setup.tmp" /SL5="$1B0142,156490,54272,C:\Users\admin\AppData\Local\Temp\red-v2.2-setup.exe" | C:\Users\admin\AppData\Local\Temp\is-B5D10.tmp\red-v2.2-setup.tmp | — | red-v2.2-setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3468 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 239
Read events
2 230
Write events
8
Delete events
1
Modification events
| (PID) Process: | (3264) red-v2.2-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3264) red-v2.2-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3264) red-v2.2-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3264) red-v2.2-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (600) RED2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{e1a82db4-a9f0-11e7-b142-806e6f6e6963} |
| Operation: | delete value | Name: | NeedToPurge |
Value: 1 | |||
Executable files
9
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | dllhost.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\$RGIEMH3.pak | — | |
MD5:— | SHA256:— | |||
| 1996 | red-v2.2-setup.exe | C:\Users\admin\AppData\Local\Temp\is-B5D10.tmp\red-v2.2-setup.tmp | executable | |
MD5:C080F73B1BDDE0853CB0258D9A02B0EC | SHA256:A0CFBC8DA39AD4A4D21C61D73873D225FFA5D7650FAE5938AB643F719D5F7363 | |||
| 1560 | red-v2.2-setup.tmp | C:\Program Files\Remove Empty Directories\is-2DMJJ.tmp | executable | |
MD5:2F96926F3FC75D780AB0451F0BE8BFA8 | SHA256:AC48374F409FAAF6644EEF448C844822D49426BA7AC747CC6AFC42554344D8F3 | |||
| 1560 | red-v2.2-setup.tmp | C:\Program Files\Remove Empty Directories\RED2.exe | executable | |
MD5:75F6CD0423C6ADB5640828FF7FBDAE19 | SHA256:1F778ACC4D56B96437A084B9D8FB2DBEC6CB8AFB67E9D29FFA3653591ABFAA48 | |||
| 1560 | red-v2.2-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-CBAHE.tmp\isxdl.dll | executable | |
MD5:48AD1A1C893CE7BF456277A0A085ED01 | SHA256:B0CC4697B2FD1B4163FDDCA2050FC62A9E7D221864F1BD11E739144C90B685B3 | |||
| 1560 | red-v2.2-setup.tmp | C:\Program Files\Remove Empty Directories\is-AQEON.tmp | executable | |
MD5:75F6CD0423C6ADB5640828FF7FBDAE19 | SHA256:1F778ACC4D56B96437A084B9D8FB2DBEC6CB8AFB67E9D29FFA3653591ABFAA48 | |||
| 1560 | red-v2.2-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-CBAHE.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1560 | red-v2.2-setup.tmp | C:\Program Files\Remove Empty Directories\unins000.exe | executable | |
MD5:2F96926F3FC75D780AB0451F0BE8BFA8 | SHA256:AC48374F409FAAF6644EEF448C844822D49426BA7AC747CC6AFC42554344D8F3 | |||
| 1560 | red-v2.2-setup.tmp | C:\Program Files\Remove Empty Directories\is-H0QLJ.tmp | text | |
MD5:B2710FCDE999160E97B4C25071897609 | SHA256:1FC67A34BF6EB0C7576C8AB493D73B4FCF0AA48ADE4EF3C37AB5A5456C104926 | |||
| 2928 | red-v2.2-setup.exe | C:\Users\admin\AppData\Local\Temp\is-DUQ9Q.tmp\red-v2.2-setup.tmp | executable | |
MD5:C080F73B1BDDE0853CB0258D9A02B0EC | SHA256:A0CFBC8DA39AD4A4D21C61D73873D225FFA5D7650FAE5938AB643F719D5F7363 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |