| File name: | 6.bat |
| Full analysis: | https://app.any.run/tasks/1d2598b9-9041-4b44-8b4f-ec97dd124909 |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 05:31:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | EB93FE9227DAEF73E9D4EE9AA589BCE0 |
| SHA1: | A84F0B84FE2D32408C4B33C5DDA4A817110DBC20 |
| SHA256: | 8EFD51D4F94EEA731B86E8F434B884703A339164704724821EFCFB4651A0A838 |
| SSDEEP: | 48:dJZk7y4qK3TweGaTweGORTeCBrTJWeG5TJe+NGjWF4cf/Kk:dwZqKjkykORTX8llsjG8k |
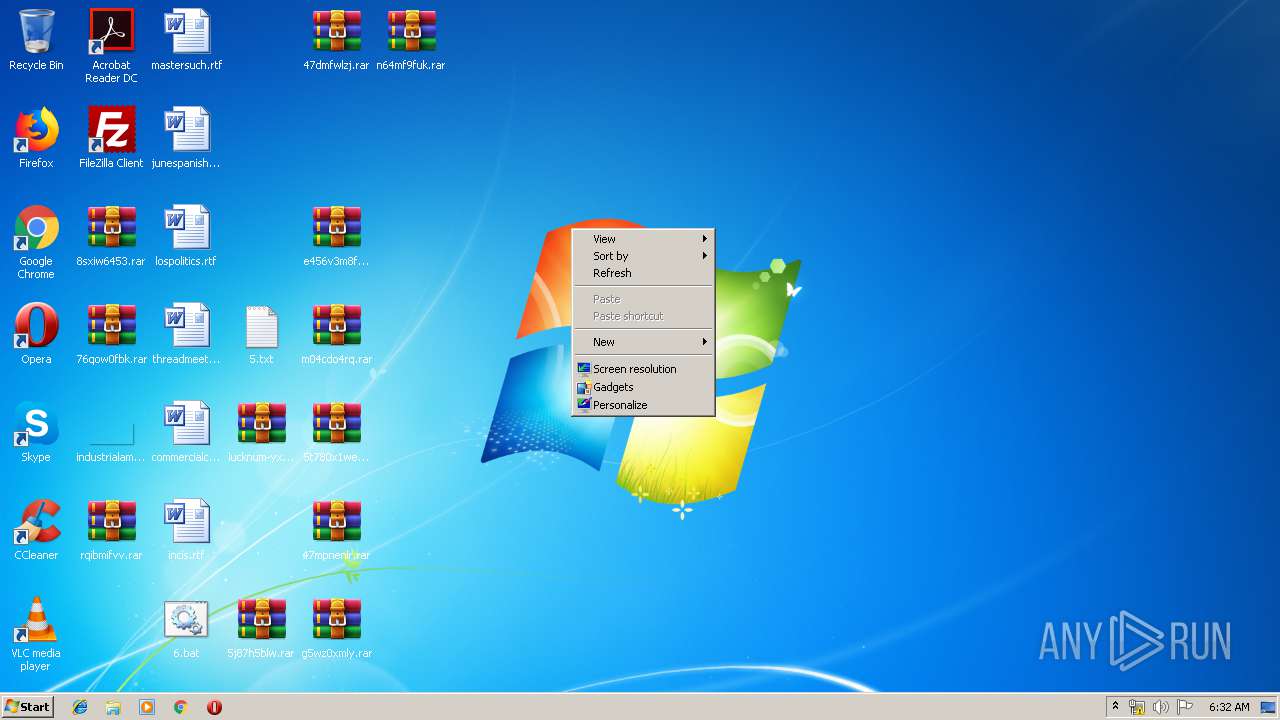
MALICIOUS
Application was dropped or rewritten from another process
- Rar.exe (PID: 3576)
- Rar.exe (PID: 3252)
- Rar.exe (PID: 2684)
- Rar.exe (PID: 3380)
- Rar.exe (PID: 3392)
- Rar.exe (PID: 3688)
- Rar.exe (PID: 4032)
- Rar.exe (PID: 2900)
- Rar.exe (PID: 2176)
- Rar.exe (PID: 2596)
- Rar.exe (PID: 928)
- Rar.exe (PID: 868)
SUSPICIOUS
Executable content was dropped or overwritten
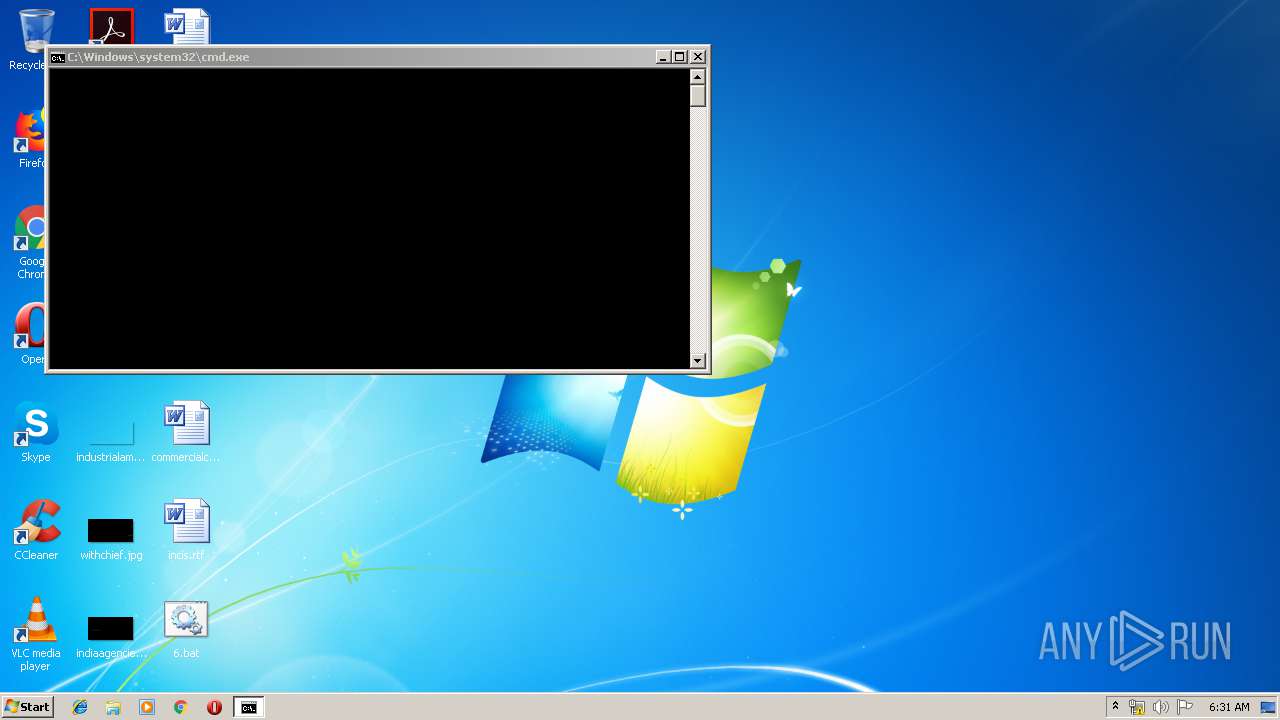
- cmd.exe (PID: 3204)
Starts MSHTA.EXE for opening HTA or HTMLS files
- cmd.exe (PID: 3296)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 2824)
- cmd.exe (PID: 3204)
Application launched itself
- cmd.exe (PID: 3204)
Starts application with an unusual extension
- cmd.exe (PID: 3204)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
50
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 772 | C:\Windows\system32\cmd.exe /c "dir /a/s/b/on *.exe *.jpg *.doc *.rtf" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 868 | rar.exe a -hpviaw369od "m04cdo4rq.rar" "C:\Users\admin\Desktop\healthcapacity.jpg " | C:\Users\admin\Desktop\Rar.exe | — | cmd.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: Command line RAR Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 928 | rar.exe a -hpiyn2ex66aqokgykouiw3vekhr5vizxcncbtqe6ta -df lucknum-yxnnzp.rar 4.txt | C:\Users\admin\Desktop\Rar.exe | — | cmd.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: Command line RAR Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1092 | more +1 1.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1180 | more +1 2.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1424 | more +1 3.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1480 | more +1 3.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1656 | more +1 1.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1752 | more +1 3.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1820 | more +1 2.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
424
Read events
420
Write events
4
Delete events
0
Modification events
| (PID) Process: | (2824) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2824) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
12
Text files
79
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | cmd.exe | C:\Users\admin\Desktop\a.tmp | — | |
MD5:— | SHA256:— | |||
| 3204 | cmd.exe | C:\Users\admin\Desktop\2.txt | text | |
MD5:— | SHA256:— | |||
| 928 | Rar.exe | C:\Users\admin\Desktop\lucknum-yxnnzp.rar | compressed | |
MD5:— | SHA256:— | |||
| 2596 | Rar.exe | C:\Users\admin\Desktop\5j87h5blw.rar | compressed | |
MD5:— | SHA256:— | |||
| 3204 | cmd.exe | C:\Users\admin\Desktop\commercialchat.rtf | text | |
MD5:— | SHA256:— | |||
| 3204 | cmd.exe | C:\Users\admin\Desktop\5.txt | text | |
MD5:— | SHA256:— | |||
| 3576 | Rar.exe | C:\Users\admin\Desktop\47dmfwlzj.rar | compressed | |
MD5:— | SHA256:— | |||
| 3204 | cmd.exe | C:\Users\admin\Desktop\healthcapacity.jpg | image | |
MD5:— | SHA256:— | |||
| 3204 | cmd.exe | C:\Users\admin\Desktop\incis.rtf | text | |
MD5:— | SHA256:— | |||
| 868 | Rar.exe | C:\Users\admin\Desktop\m04cdo4rq.rar | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report