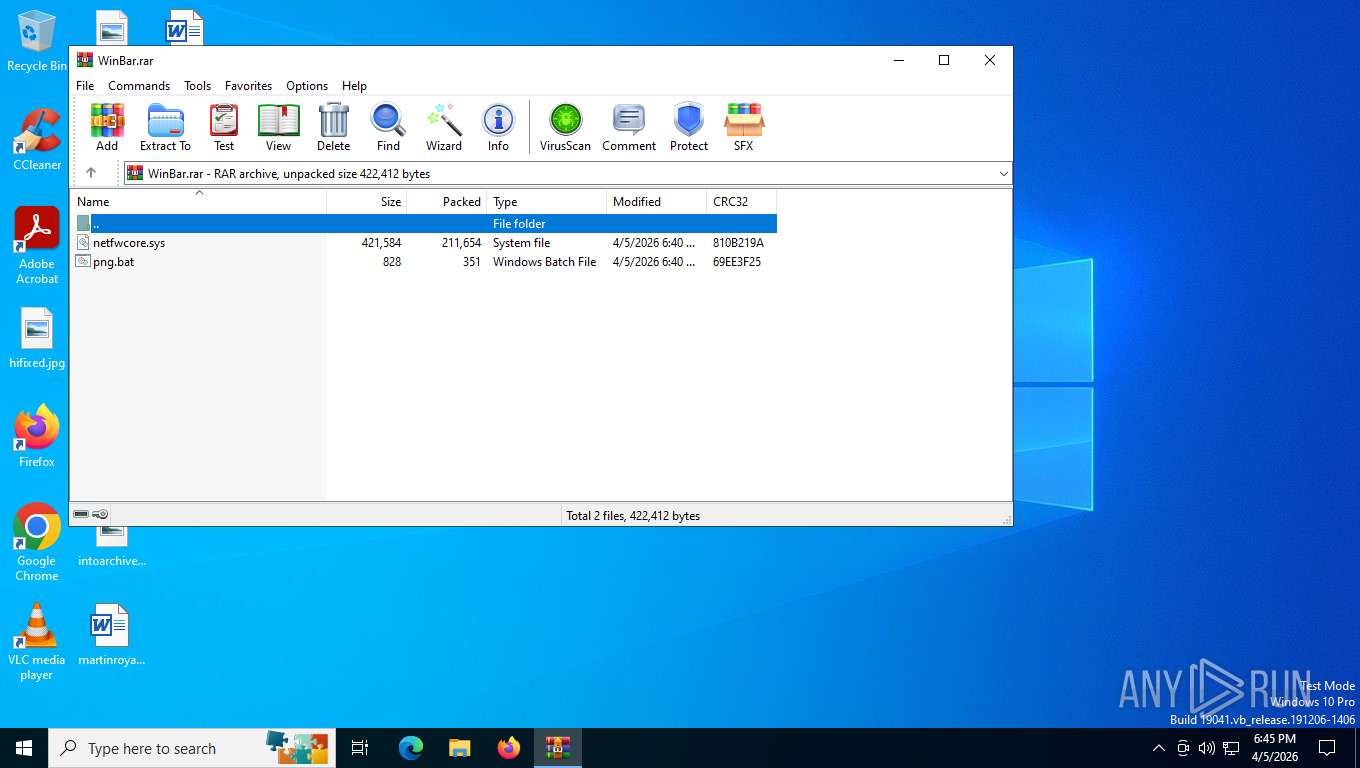
| File name: | WinBar.rar |
| Full analysis: | https://app.any.run/tasks/fe44ce1b-2e35-4fec-bcf9-10229cfe8fbe |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2026, 22:45:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 0FFA05EB951F67FE5FDC639ECE6532E8 |
| SHA1: | FE2B88BF6791163899D53153453AFF1971FD5FCD |
| SHA256: | 8EF9EAFDDF714F81ACC0033DD00D77D695C53F0E4CFA554DBEB5CE18CA38F33B |
| SSDEEP: | 6144:Pa9ws51WbGL0uW7SLAApWcXCFnPCDMlD53HPHiH9:6wSWbGHWOpWcXC9PNl13HPHid |
MALICIOUS
No malicious indicators.SUSPICIOUS
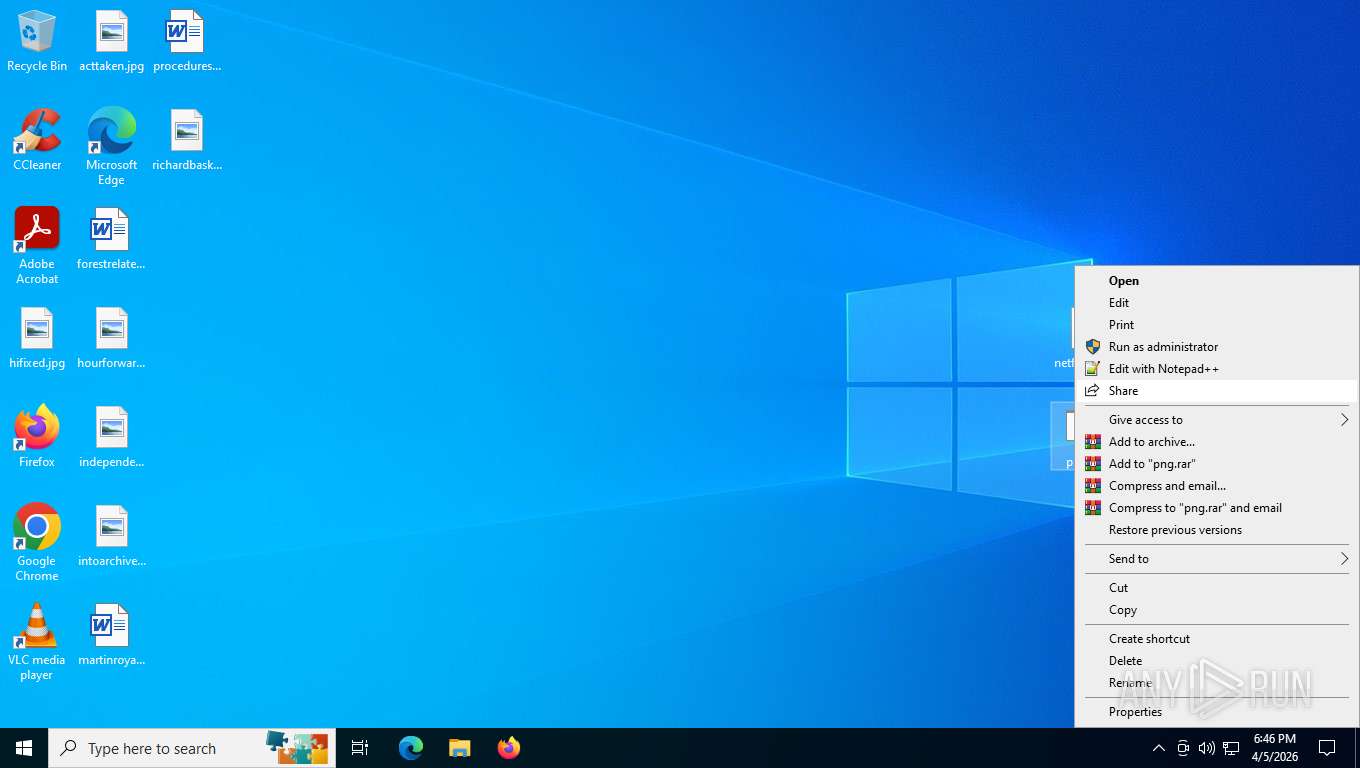
Starts CMD.EXE for commands execution
- cmd.exe (PID: 144)
Drops a system driver (possible attempt to evade defenses)
- cmd.exe (PID: 144)
- WinRAR.exe (PID: 2528)
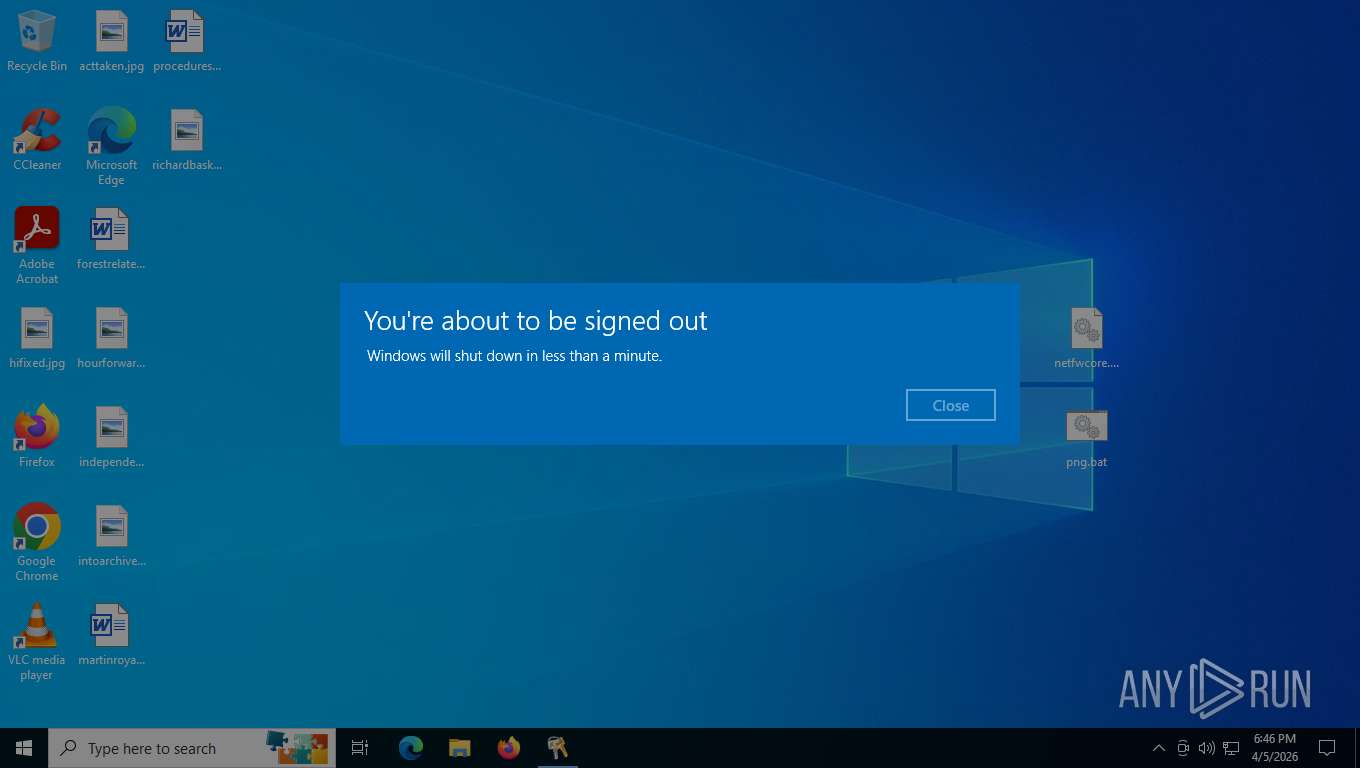
The system shut down or reboot
- cmd.exe (PID: 144)
Creates a new Windows service
- sc.exe (PID: 2156)
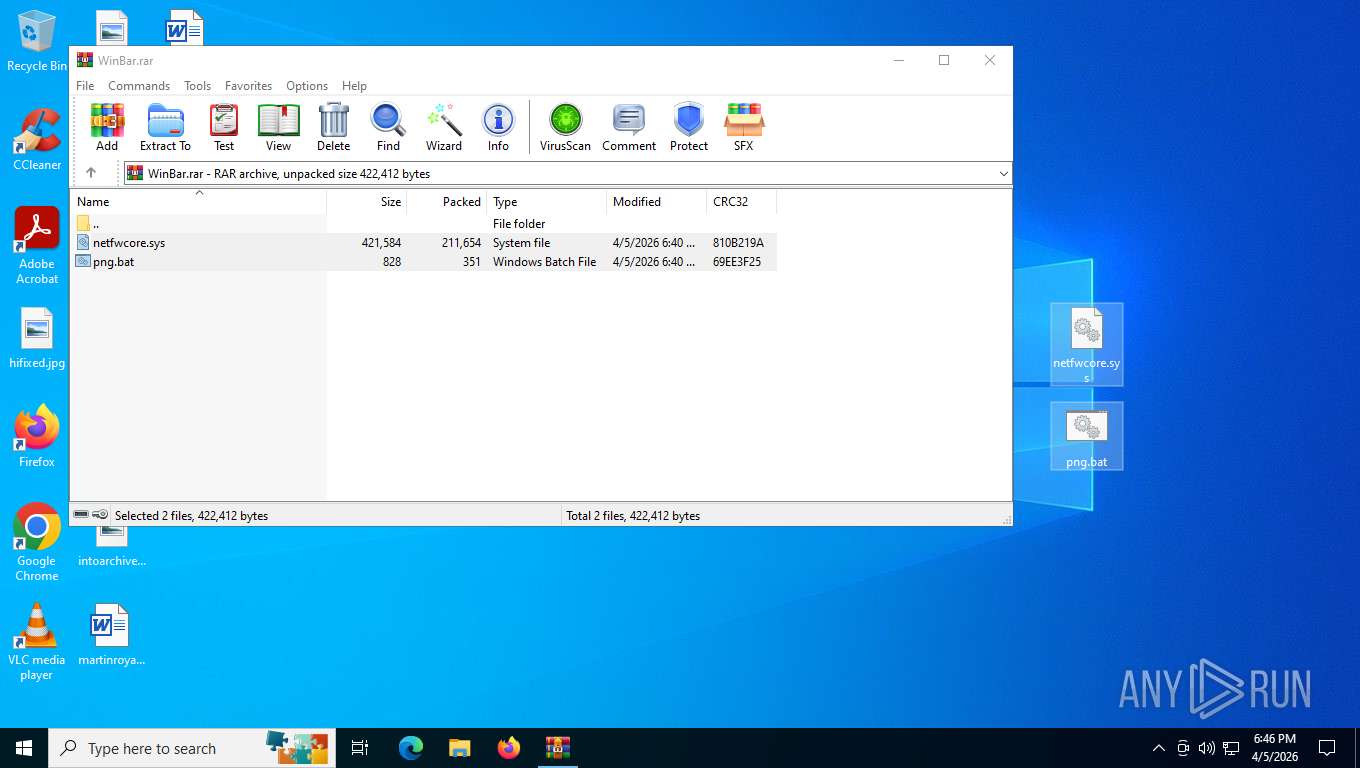
Executable content was dropped or overwritten
- cmd.exe (PID: 144)
INFO
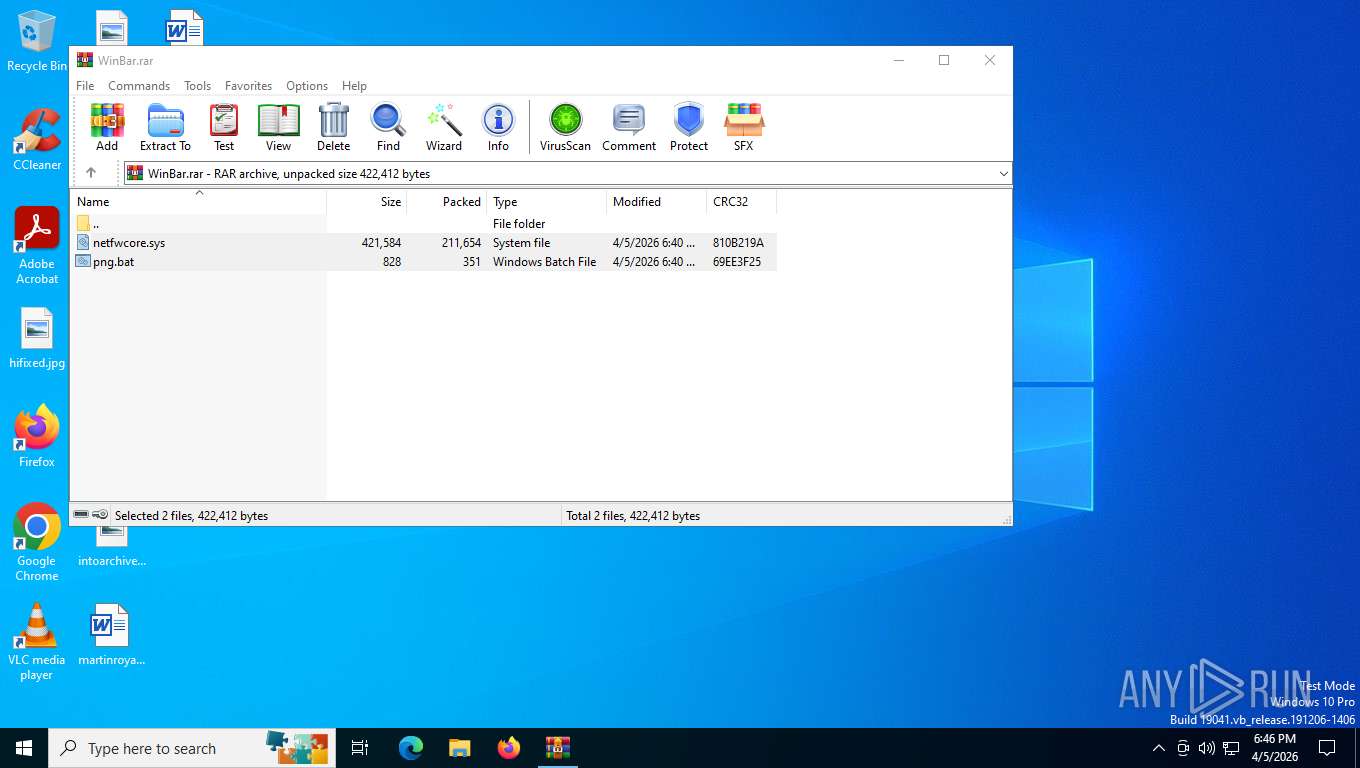
Generic archive extractor
- WinRAR.exe (PID: 2528)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2528)
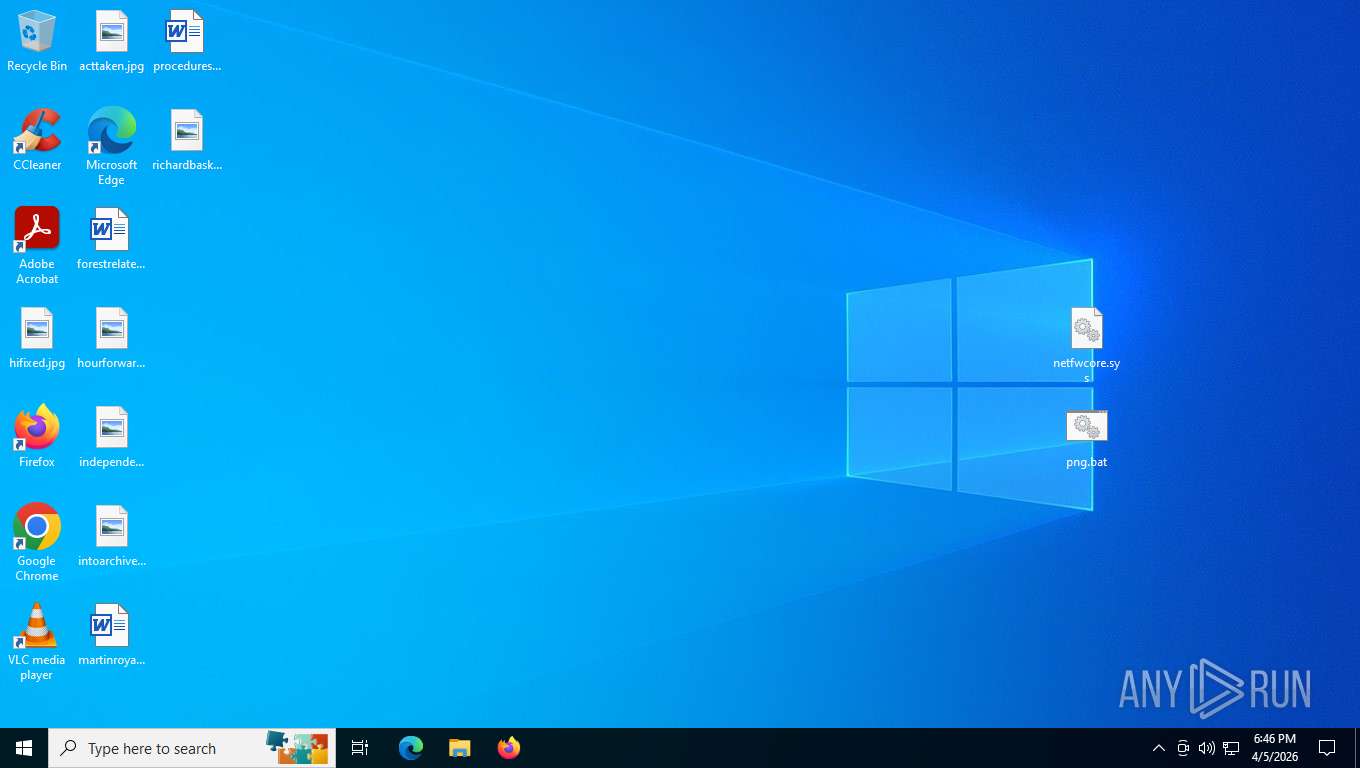
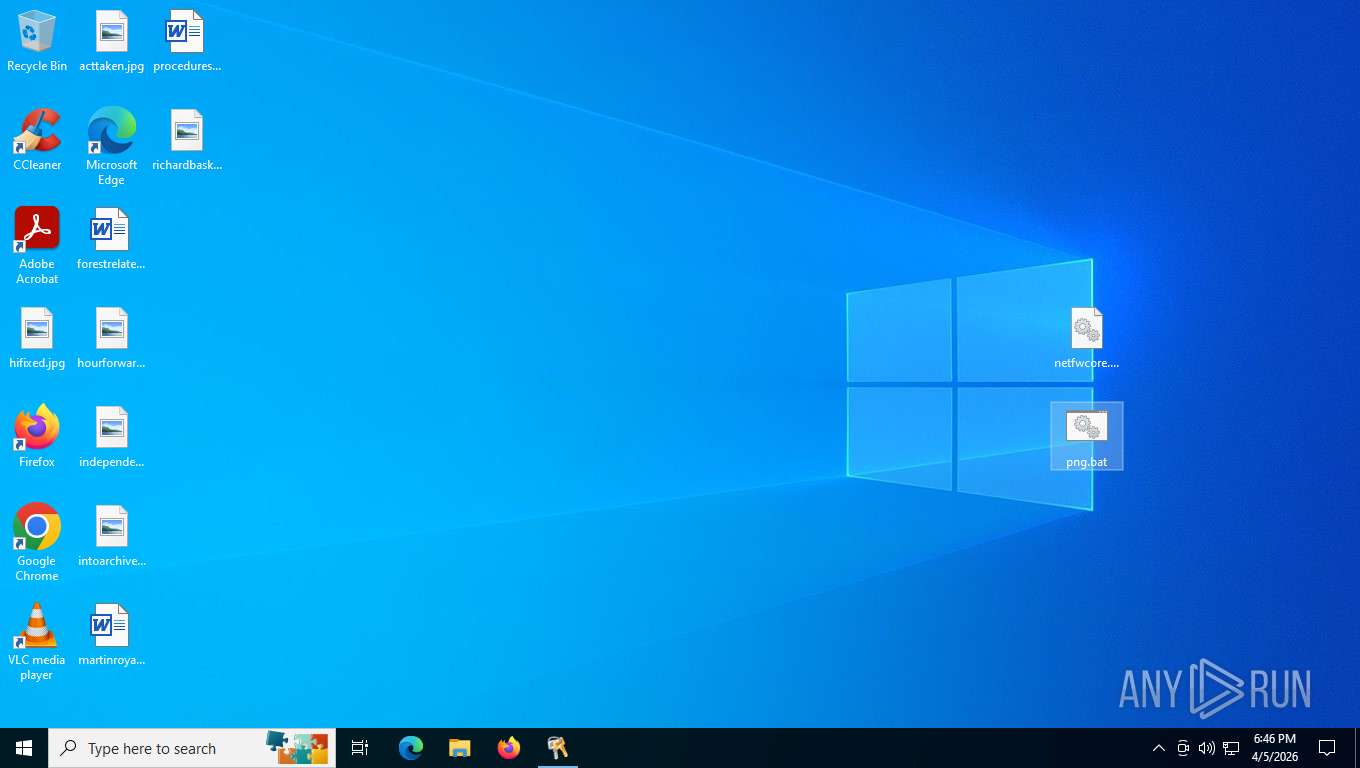
Manual execution by a user
- cmd.exe (PID: 144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 211654 |
| UncompressedSize: | 421584 |
| OperatingSystem: | Win32 |
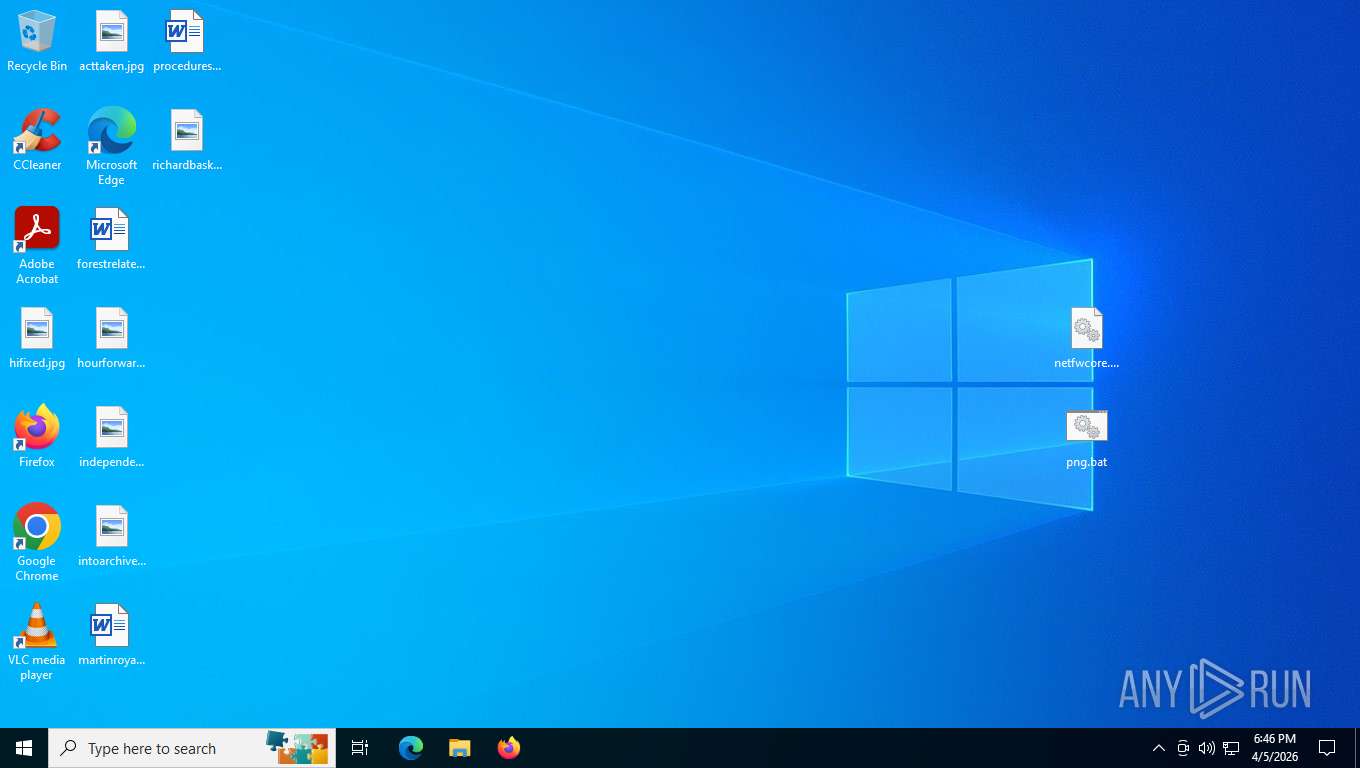
| ArchivedFileName: | netfwcore.sys |
Total processes
264
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\png.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1176 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2156 | sc create system2 binPath= "C:\Windows\System32\netfwcore.sys" DisplayName= "ca2" start= boot tag= 2 type= kernel group= "System Reserved" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2528 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\WinBar.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 8060 | shutdown /r /t 3 /f | C:\Windows\System32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 270
Read events
3 249
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (2528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\WinBar.rar | |||
| (PID) Process: | (2528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2528) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 144 | cmd.exe | C:\Windows\System32\netfwcore.sys | executable | |
MD5:8D2692C5A0915C19FE65F298D7100DA3 | SHA256:A4D3D3C794C6FD0C238B8E99D7480BD7255DF7F7C8F159E1A588E7A1A1D582AE | |||
| 2528 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2528.30003\netfwcore.sys | executable | |
MD5:8D2692C5A0915C19FE65F298D7100DA3 | SHA256:A4D3D3C794C6FD0C238B8E99D7480BD7255DF7F7C8F159E1A588E7A1A1D582AE | |||
| 2528 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2528.30003\png.bat | text | |
MD5:CB3EE7F3EA95A29337746A129A54976B | SHA256:1928BB504F621D6C16E08F16879AE9A3DB57C553CBA7B2CC953A030B464E4812 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
88
TCP/UDP connections
48
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6260 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
3088 | OfficeClickToRun.exe | GET | 200 | 52.123.243.207:443 | https://ecs.office.com/config/v2/Office/officeclicktorun/16.0.16026.20140/Production/CC?&Clientid=%7b48BA7FDF-353C-4FE5-8D8F-9E31911A3891%7d&Application=officeclicktorun&Platform=win32&Version=16.0.16026.20140&MsoVersion=16.0.16026.20140&ProcessName=officeclicktorun.exe&Audience=Production&Build=ship&Architecture=x64&OsVersion=10.0&OsBuild=19045&Channel=CC&InstallType=C2R&SessionId=%7b75E96B78-B409-461A-9734-1DE5EFAFC588%7d&LabMachine=false | US | — | — | whitelisted |
5504 | SearchApp.exe | GET | 304 | 92.123.104.33:443 | https://www.bing.com/rp/ANzUnPnVY0oL0XWxs0RLJxjJLUo.br.js | NL | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5316 | svchost.exe | POST | 200 | 20.190.159.75:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.75:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
5316 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.75:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.75:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | — | 203 b | whitelisted |
3088 | OfficeClickToRun.exe | GET | 200 | 52.110.17.73:443 | https://officeclient.microsoft.com/config16/?syslcid=1033&build=16.0.16026&crev=3 | US | xml | 187 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6260 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3428 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5316 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5316 | svchost.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6260 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |