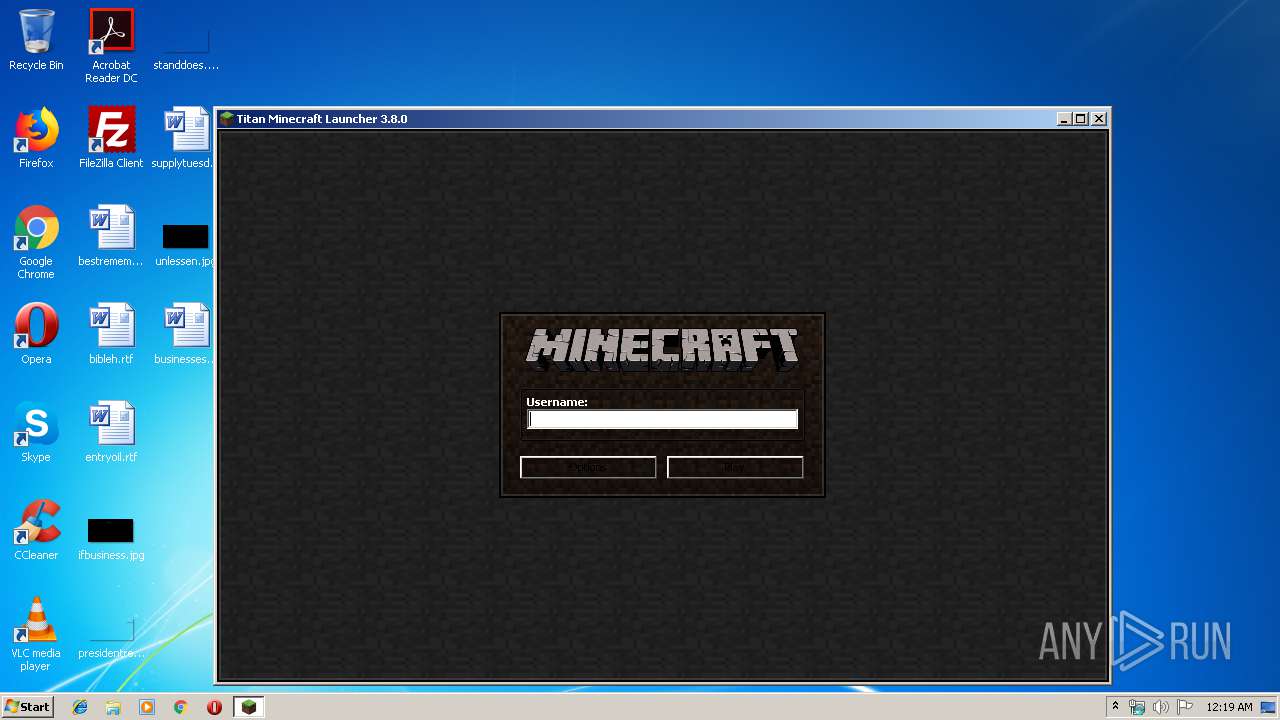
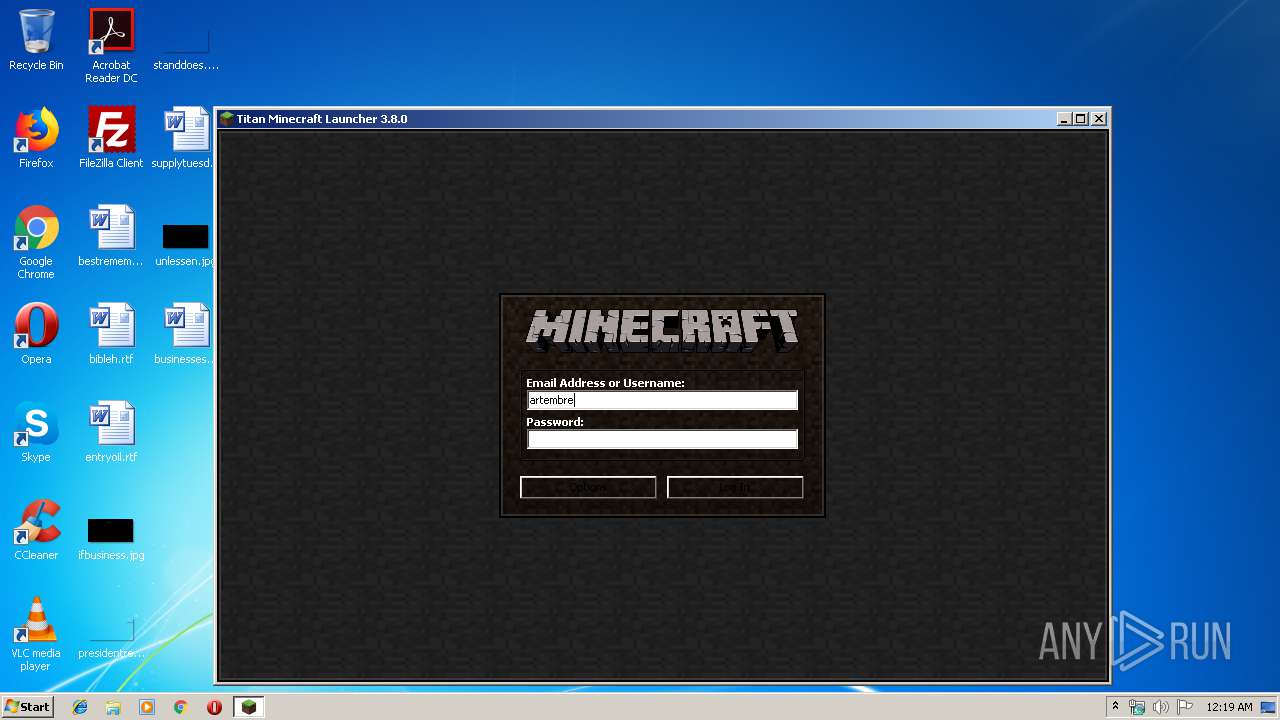
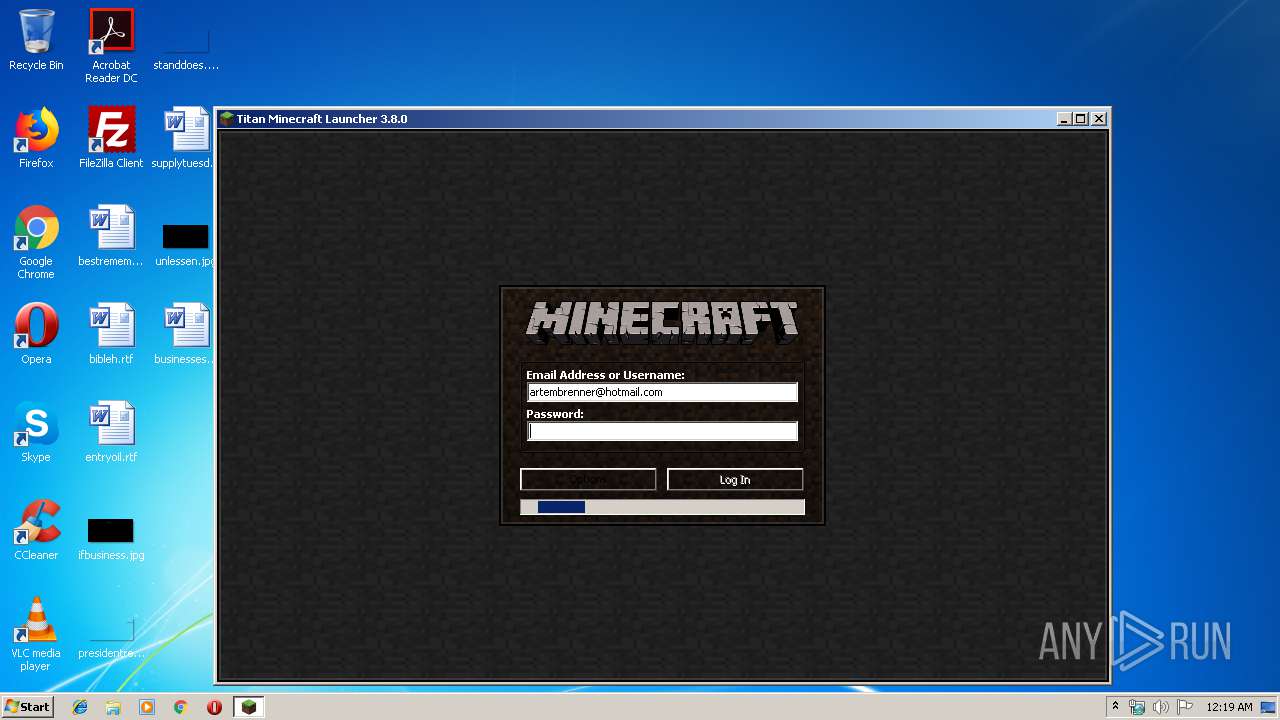
| File name: | minecraft-titan-launcher-3.7.0.exe |
| Full analysis: | https://app.any.run/tasks/2d6ef5c7-fafb-4383-aa9c-6d2bc05406ea |
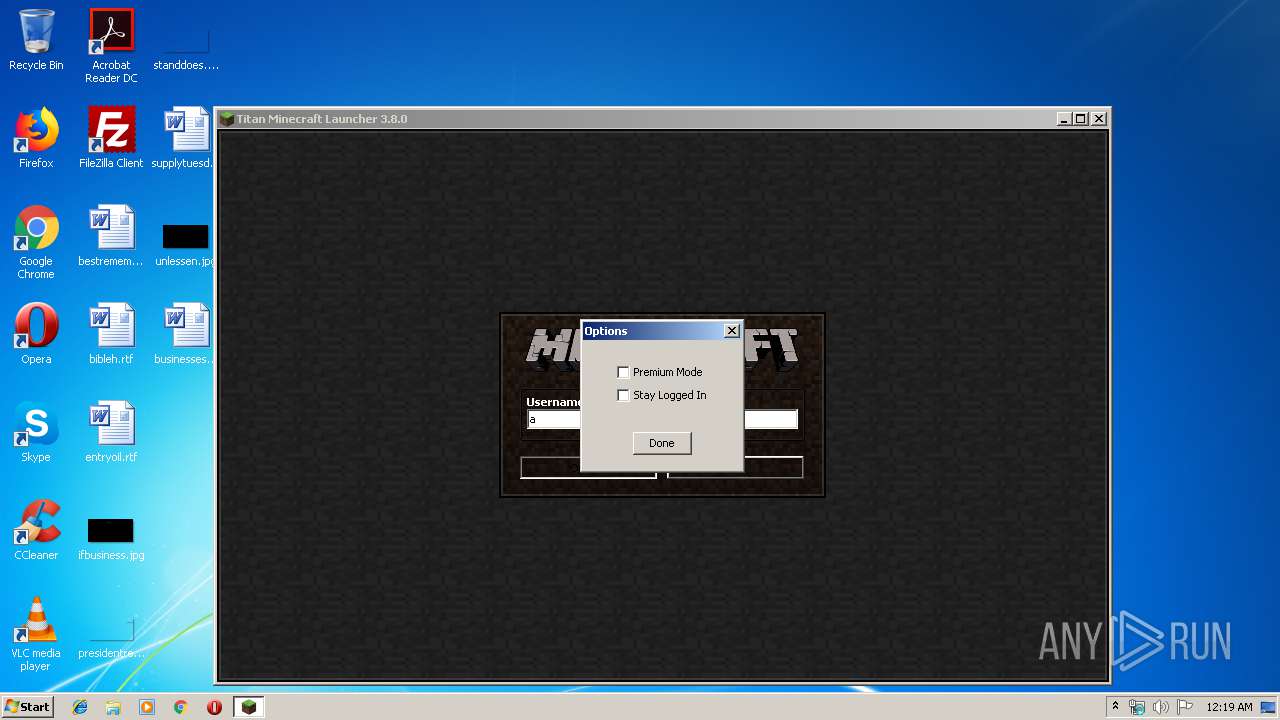
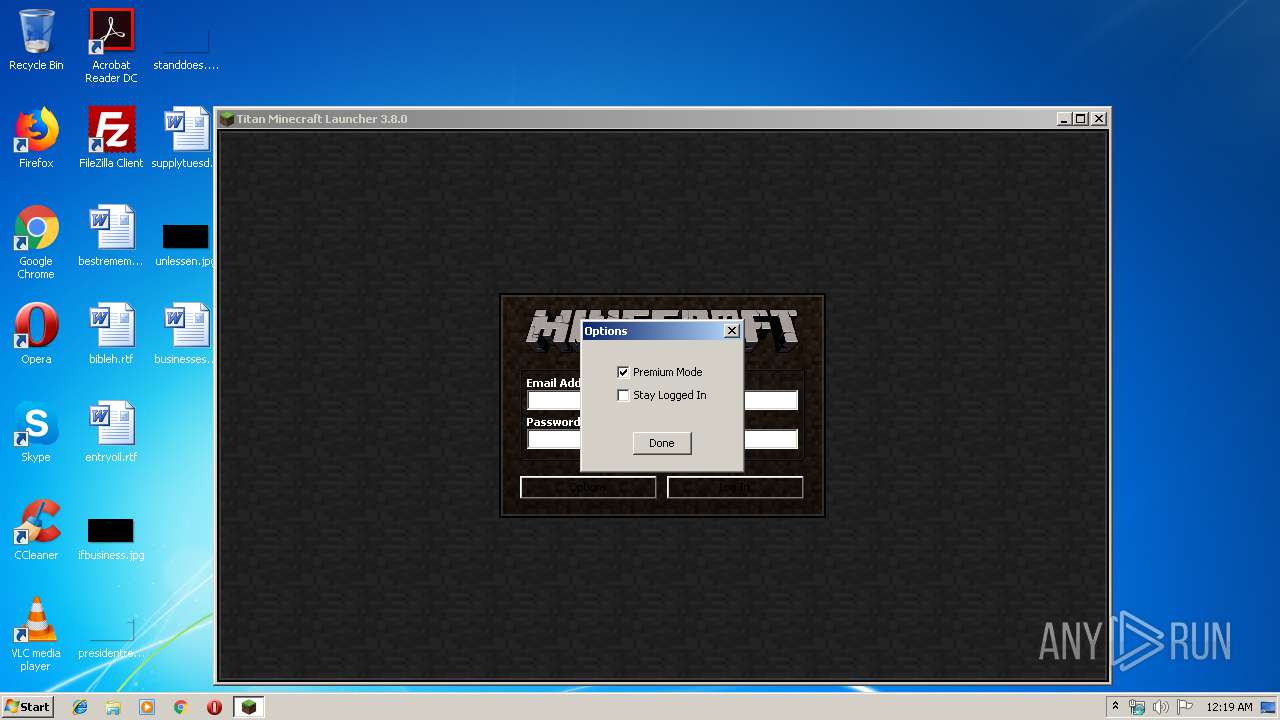
| Verdict: | Malicious activity |
| Analysis date: | December 17, 2019, 00:18:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 04C275F4DD49D860E3578D99ACCA2A7E |
| SHA1: | DD2C09F35DE2754B8757B5C977448E4AACB24E85 |
| SHA256: | 8EF6969EC02D4CDD5600E37E411FB030C196F3806EDFAECB3B279425927DAEC4 |
| SSDEEP: | 49152:cy8NZXlYv3NCMO1UgHrnRAST8XrhaRY0oaHaYLxNvjYDbOCBpVOOP4j:p8Xl7drn3T8hiVoaHa4vjap34j |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes JAVA applets
- minecraft-titan-launcher-3.7.0.exe (PID: 2712)
Creates files in the user directory
- javaw.exe (PID: 4004)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:17 03:18:54+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 18432 |
| InitializedDataSize: | 18432 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.8.0.0 |
| ProductVersionNumber: | 3.8.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Titan Launcher |
| FileDescription: | 1.13.1 Minecraft Launcher |
| FileVersion: | 3.8.0 |
| InternalName: | Minecraft Launcher |
| LegalCopyright: | Titan Launcher |
| OriginalFileName: | Minecraft Launcher.exe |
| ProductName: | Titan Launcher |
| ProductVersion: | 3.8.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Oct-2018 01:18:54 |
| Detected languages: |
|
| CompanyName: | Titan Launcher |
| FileDescription: | 1.13.1 Minecraft Launcher |
| FileVersion: | 3.8.0 |
| InternalName: | Minecraft Launcher |
| LegalCopyright: | Titan Launcher |
| OriginalFilename: | Minecraft Launcher.exe |
| ProductName: | Titan Launcher |
| ProductVersion: | 3.8.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 17-Oct-2018 01:18:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004728 | 0x00004800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.05951 |
.data | 0x00006000 | 0x000000E0 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.346693 |
.rdata | 0x00007000 | 0x00000500 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99808 |
.bss | 0x00008000 | 0x00008EF0 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000A94 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.61998 |
.rsrc | 0x00012000 | 0x00003238 | 0x00003400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.64567 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86519 | 1138 | UNKNOWN | Process Default Language | RT_MANIFEST |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 3.91327 | 25 | UNKNOWN | Process Default Language | RT_RCDATA |
25 | 2 | 4 | UNKNOWN | Process Default Language | RT_RCDATA |
27 | 2 | 4 | UNKNOWN | Process Default Language | RT_RCDATA |
30 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
101 | 4.04307 | 50 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2712 | "C:\Users\admin\AppData\Local\Temp\minecraft-titan-launcher-3.7.0.exe" | C:\Users\admin\AppData\Local\Temp\minecraft-titan-launcher-3.7.0.exe | — | explorer.exe | |||||||||||
User: admin Company: Titan Launcher Integrity Level: MEDIUM Description: 1.13.1 Minecraft Launcher Exit code: 0 Version: 3.8.0 Modules
| |||||||||||||||
| 4004 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -Xms256m -Xmx512m -jar "C:\Users\admin\AppData\Local\Temp\minecraft-titan-launcher-3.7.0.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | minecraft-titan-launcher-3.7.0.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
26
Read events
24
Write events
2
Delete events
0
Modification events
| (PID) Process: | (4004) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4004 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio4646325619576865858.tmp | — | |
MD5:— | SHA256:— | |||
| 4004 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio8217960480827486047.tmp | — | |
MD5:— | SHA256:— | |||
| 4004 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio232473809321260153.tmp | — | |
MD5:— | SHA256:— | |||
| 4004 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio6111260406981183929.tmp | — | |
MD5:— | SHA256:— | |||
| 4004 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio9062013884674131522.tmp | — | |
MD5:— | SHA256:— | |||
| 4004 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio8626507938240790480.tmp | — | |
MD5:— | SHA256:— | |||
| 4004 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\servers.dat | image | |
MD5:0111E815777DADD5E0CAA7861A2C7247 | SHA256:FB200F3866248E687DA64875CCA0CDD68D3001772BD7BAB7FF66EF88FFAB3E66 | |||
| 4004 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_profiles.json | text | |
MD5:832C0CBB036C9DA1F3D4909F0EAFD57B | SHA256:F12810AED8DAE228B1D5809CBF7AD12D86EFFCD139F2CF1C36A51F91AB748F1A | |||
| 4004 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\minecraft launcher\Minecraft Update News.htm | html | |
MD5:2514A956BBF5669D63DB699380ADECB1 | SHA256:D52876836C55B7E9E3AF5C153BB86377EC6D75D132286113FBB952C914216A0F | |||
| 4004 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
10
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4004 | javaw.exe | GET | 200 | 198.54.115.64:80 | http://teamextrememc.com/failsafe/failsafe.txt | US | text | 257 b | malicious |
4004 | javaw.exe | GET | 200 | 198.54.115.64:80 | http://teamextrememc.com/failsafe/Minecraft%20Update%20News.htm | US | html | 24.2 Kb | malicious |
4004 | javaw.exe | GET | 200 | 198.54.115.64:80 | http://teamextrememc.com/failsafe/Minecraft%20Update%20News.htm | US | html | 24.2 Kb | malicious |
4004 | javaw.exe | GET | 200 | 52.216.92.213:80 | http://assets.mojang.com/cobalt/cobalt_logo_150.PNG | US | image | 14.3 Kb | shared |
4004 | javaw.exe | GET | 200 | 52.216.92.213:80 | http://assets.mojang.com/scrolls/scrolls_logo_150.png | US | image | 15.1 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4004 | javaw.exe | 152.199.19.43:443 | 78.media.tumblr.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4004 | javaw.exe | 52.222.165.169:443 | authserver.mojang.com | Amazon.com, Inc. | US | unknown |
4004 | javaw.exe | 52.216.92.213:80 | assets.mojang.com | Amazon.com, Inc. | US | unknown |
4004 | javaw.exe | 198.54.115.64:80 | teamextrememc.com | Namecheap, Inc. | US | malicious |
4004 | javaw.exe | 152.199.21.147:443 | assets.tumblr.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | suspicious |
4004 | javaw.exe | 13.225.74.128:443 | launchermeta.mojang.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
titanindex.net |
| malicious |
teamextrememc.com |
| malicious |
launchermeta.mojang.com |
| whitelisted |
assets.tumblr.com |
| whitelisted |
78.media.tumblr.com |
| whitelisted |
assets.mojang.com |
| shared |
static.tumblr.com |
| whitelisted |
authserver.mojang.com |
| suspicious |