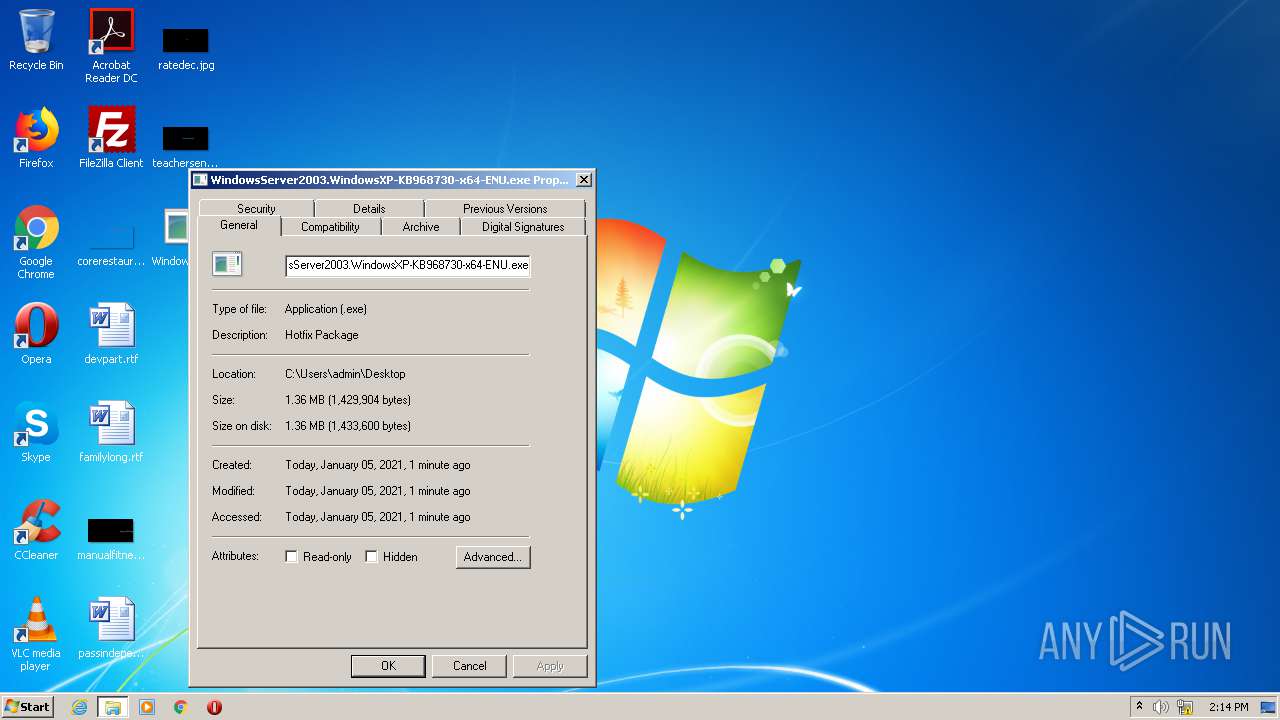
| File name: | WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe |
| Full analysis: | https://app.any.run/tasks/0974e848-4023-4520-a774-f81a742e47af |
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2021, 14:13:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 48186F6CA47DB6B9013D6D86144BE095 |
| SHA1: | F8680B4002CF5268B412A519ADE095995926054E |
| SHA256: | 8ECC8435B29C98FA3878FAE3423B6AA32820655FDE61E331FC590F07BE54977B |
| SSDEEP: | 24576:tI2QKsenHCIjGAoeWWpGPaNe/AgDKubdYgXa59btfsIr+/mu7dUC4:tI7CNJeogDKubduptfsK5uc |
MALICIOUS
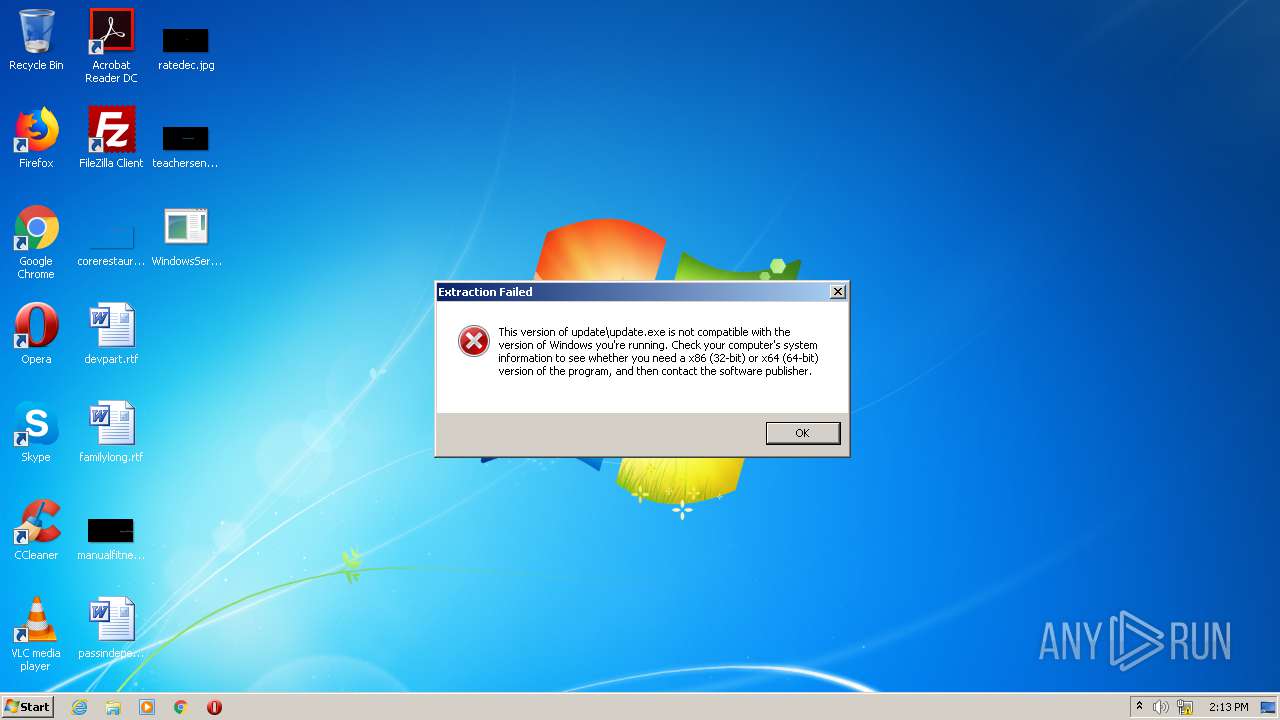
Drops executable file immediately after starts
- WinRAR.exe (PID: 1728)
SUSPICIOUS
Drops a file that was compiled in debug mode
- WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe (PID: 3272)
- WinRAR.exe (PID: 1728)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1728)
- WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe (PID: 3272)
Drops a file with too old compile date
- WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe (PID: 3272)
- WinRAR.exe (PID: 1728)
INFO
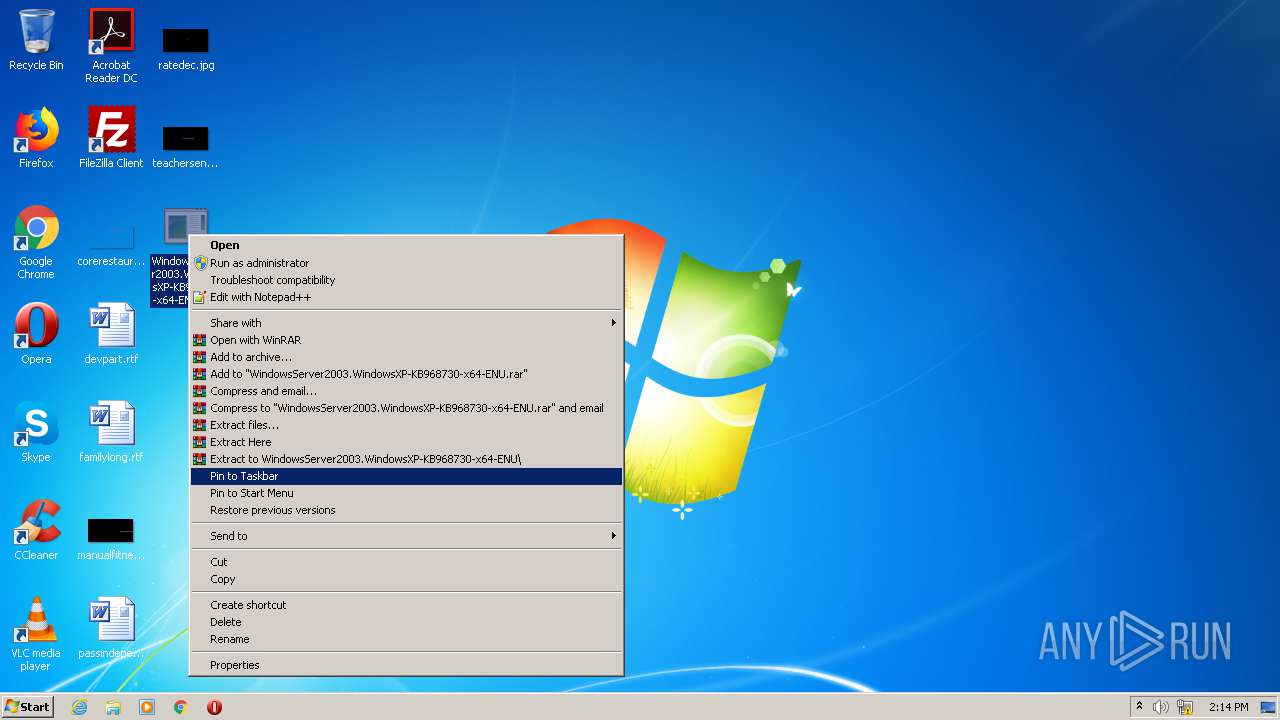
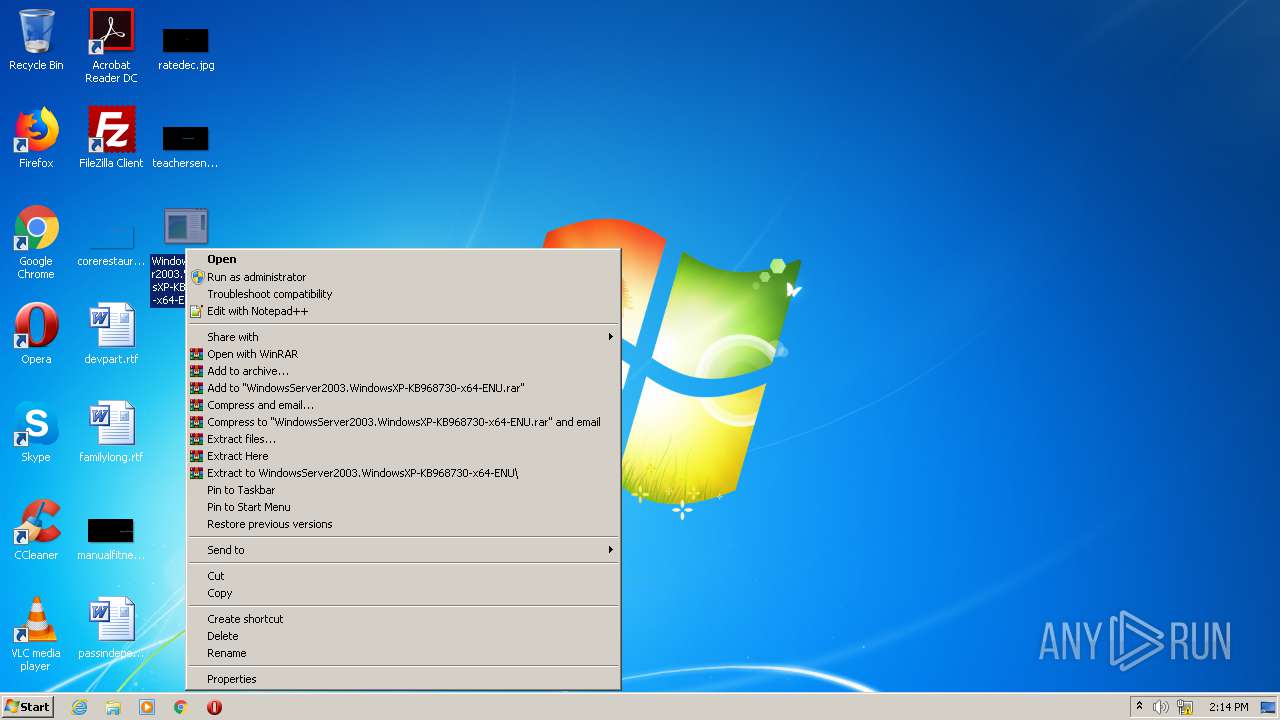
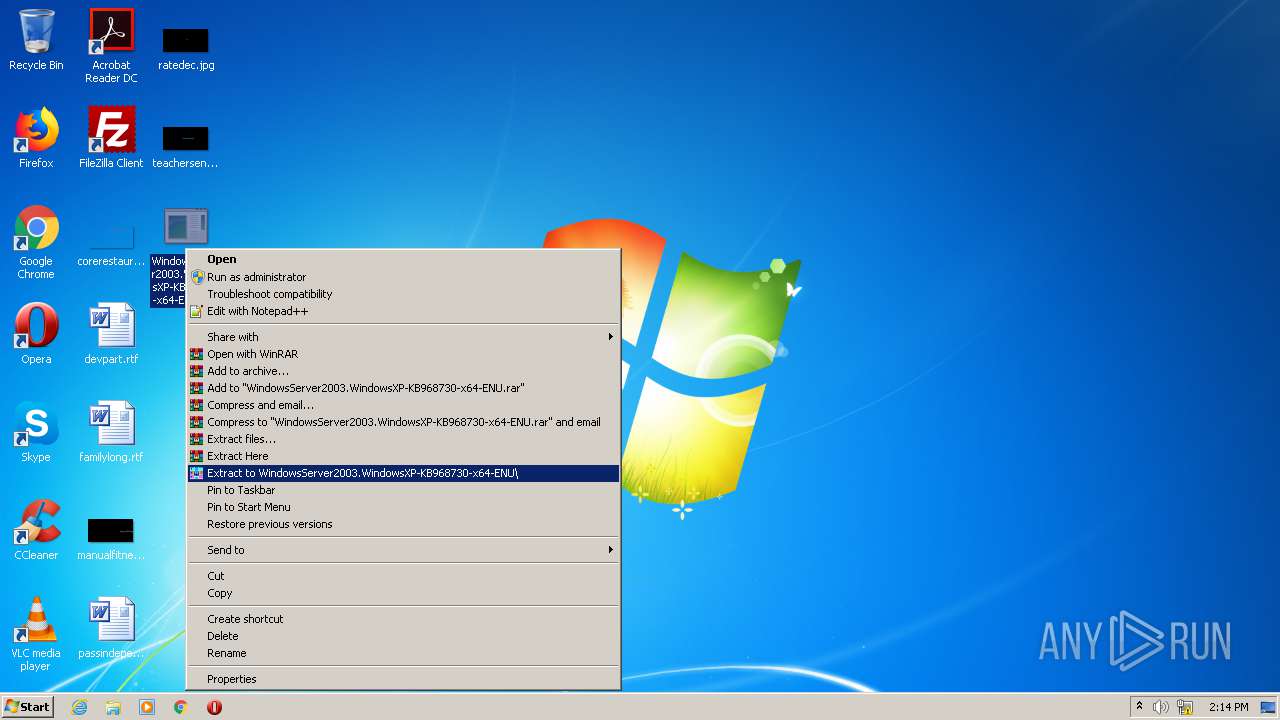
Manual execution by user
- WinRAR.exe (PID: 1728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
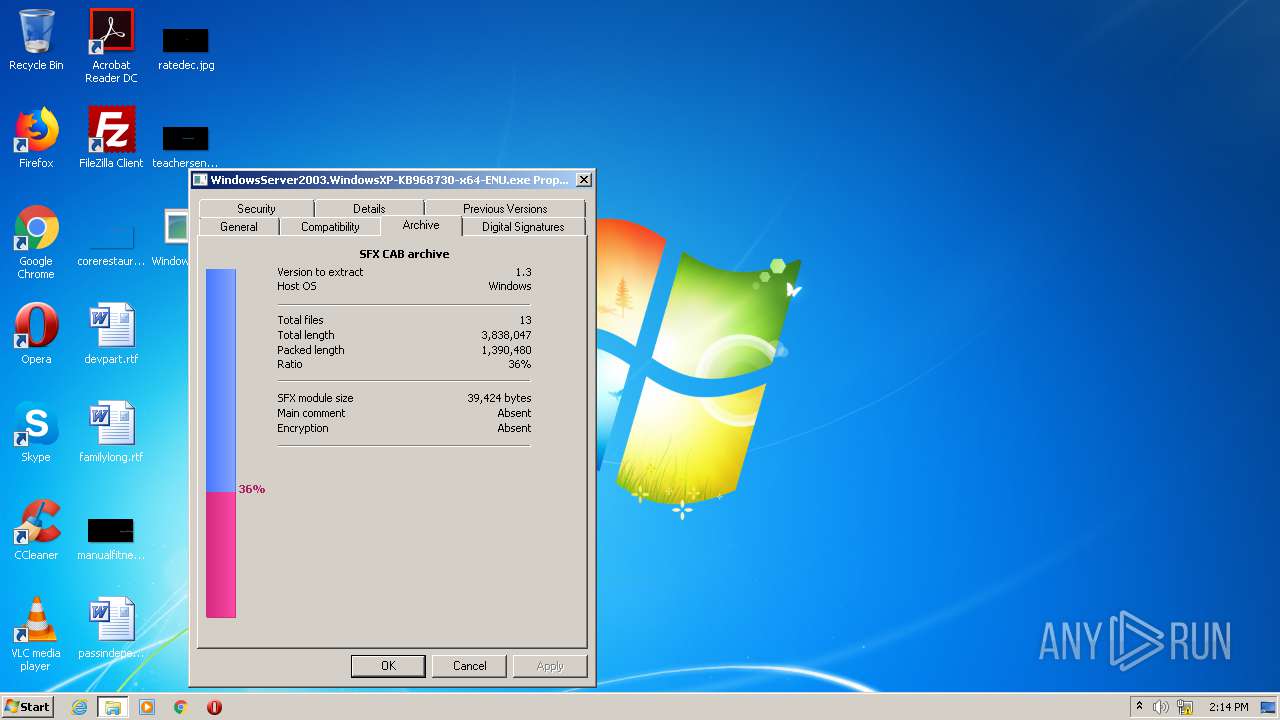
TRiD
| .exe | | | MS generic-sfx Cabinet File Unpacker (32/64bit MSCFU) (82.5) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (7.3) |
| .exe | | | Win64 Executable (generic) (6.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.5) |
| .exe | | | Win32 Executable (generic) (1) |
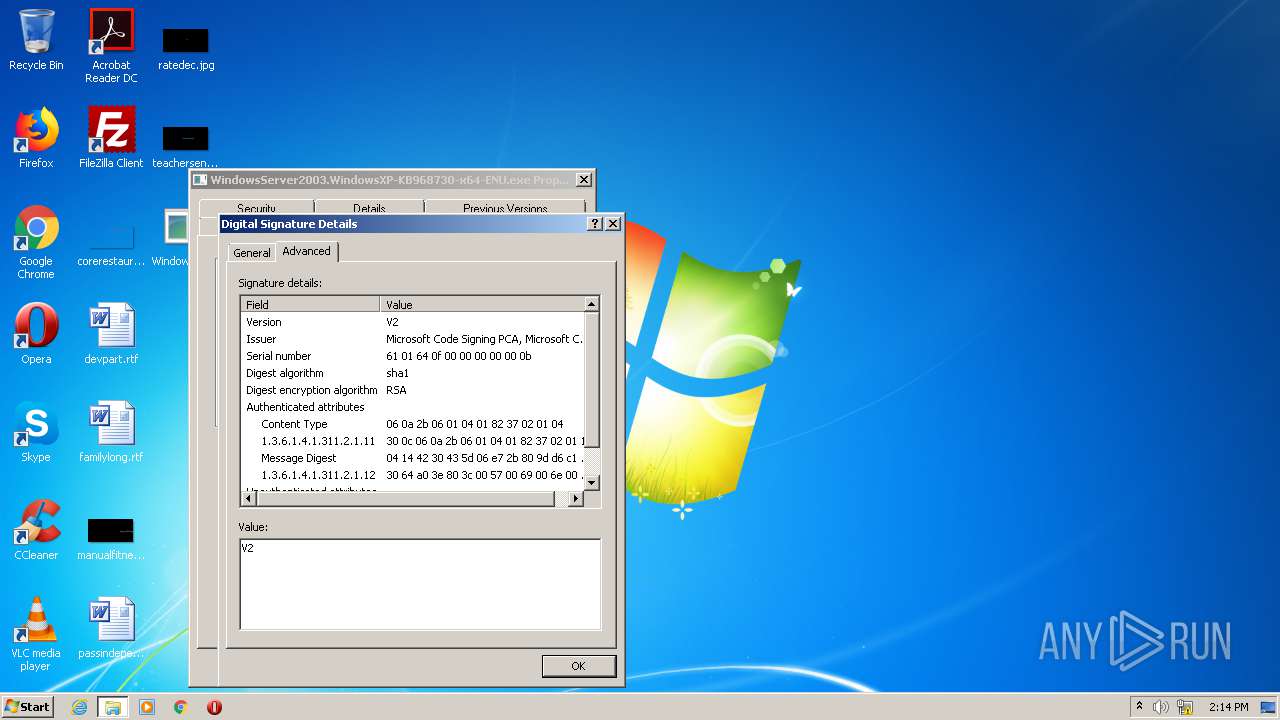
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:12:07 00:48:12+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 34304 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x63ff |
| OSVersion: | 5.2 |
| ImageVersion: | 5.2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 6.3.4.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
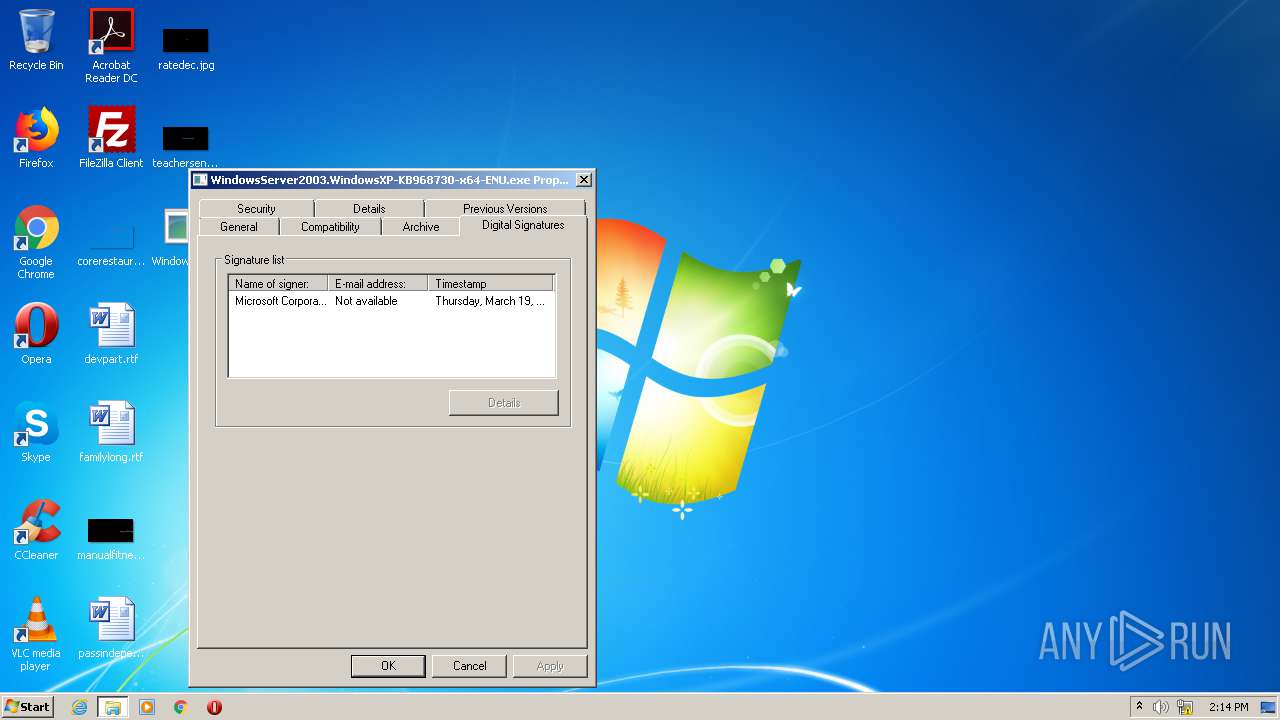
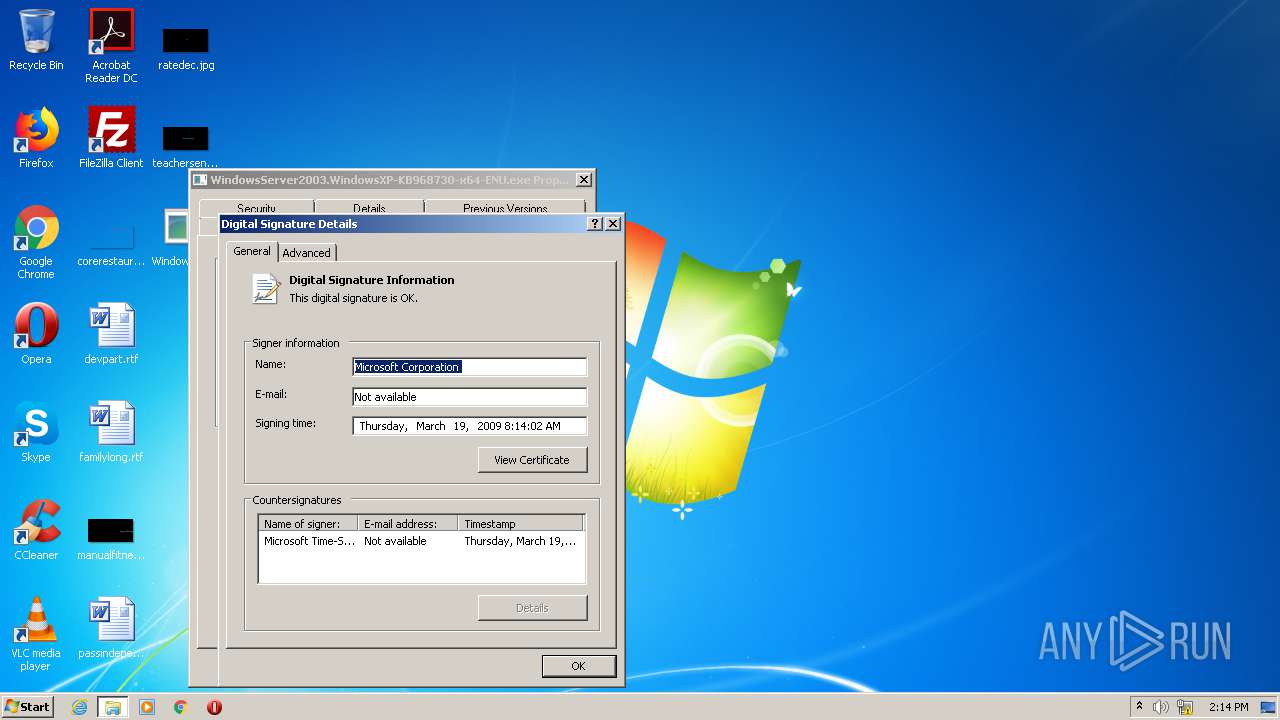
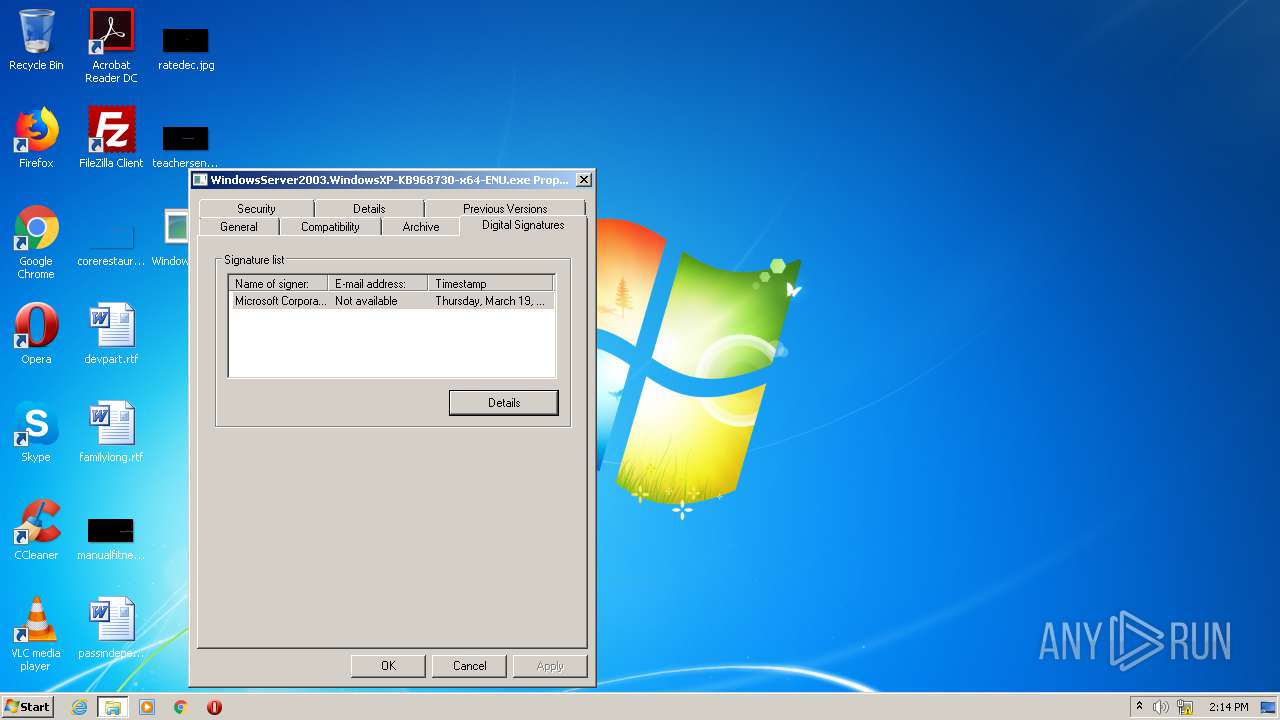
| CompanyName: | Microsoft Corporation |
| FileDescription: | Hotfix Package |
| FileVersion: | 1 |
| InternalName: | SFXCAB.EXE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | SFXCAB.EXE |
| ProductName: | Windows Server 2003/Windows XP x64 Family |
| ProductVersion: | 6.3.0004.1 |
| BuildDate: | 2009/03/19 |
| Appliesto: | Windows Server 2003/Windows XP x64 Service Pack 2 |
| InstallationType: | Full |
| InstallerVersion: | 6.3.4.1 |
| InstallerEngine: | update.exe |
| KBArticleNumber: | 968730 |
| SupportLink: | http://support.microsoft.com?kbid=968730 |
| PackageType: | Hotfix |
| ProcArchitecture: | amd64 |
| Self-ExtractorVersion: | SFXCAB v6.3.4.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Dec-2006 23:48:12 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Hotfix Package |
| FileVersion: | 1 |
| InternalName: | SFXCAB.EXE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | SFXCAB.EXE |
| ProductName: | Windows Server 2003/Windows XP x64 Family |
| ProductVersion: | 6.3.0004.1 |
| Build Date: | 2009/03/19 |
| Applies to: | Windows Server 2003/Windows XP x64 Service Pack 2 |
| Installation Type: | Full |
| Installer Version: | 6.3.4.1 |
| Installer Engine: | update.exe |
| KB Article Number: | 968730 |
| Support Link: | http://support.microsoft.com?kbid=968730 |
| Package Type: | Hotfix |
| Proc. Architecture: | amd64 |
| Self-Extractor Version: | SFXCAB v6.3.4.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 06-Dec-2006 23:48:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0000841E | 0x00008600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.509 |
.data | 0x0000C000 | 0x000113F8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.498823 |
.rsrc | 0x0001E000 | 0x00000D5C | 0x00152A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99917 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.02272 | 1900 | Latin 1 / Western European | English - United States | RT_VERSION |
100 | 3.0946 | 282 | Latin 1 / Western European | English - United States | RT_DIALOG |
107 | 2.9591 | 224 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
ntdll.dll |
Total processes
36
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1728 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe" C:\Users\admin\Desktop\WindowsServer2003.WindowsXP-KB968730-x64-ENU\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3272 | "C:\Users\admin\Desktop\WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe" | C:\Users\admin\Desktop\WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Hotfix Package Exit code: 216 Version: 1 Modules
| |||||||||||||||
Total events
43
Read events
37
Write events
6
Delete events
0
Modification events
| (PID) Process: | (1728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1728) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
12
Suspicious files
0
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3272 | WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe | C:\d7c0cc3ace53a20acd0dd6fe4d06a319\$shtdwn$.req | — | |
MD5:— | SHA256:— | |||
| 3272 | WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe | C:\d7c0cc3ace53a20acd0dd6fe4d06a319\SP2QFE\crypt32.dll | executable | |
MD5:— | SHA256:— | |||
| 3272 | WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe | C:\d7c0cc3ace53a20acd0dd6fe4d06a319\update\KB968730.CAT | cat | |
MD5:— | SHA256:— | |||
| 3272 | WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe | C:\d7c0cc3ace53a20acd0dd6fe4d06a319\SP2QFE\wow\wcrypt32.dll | executable | |
MD5:— | SHA256:— | |||
| 3272 | WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe | C:\d7c0cc3ace53a20acd0dd6fe4d06a319\update\updatebr.inf | text | |
MD5:— | SHA256:— | |||
| 1728 | WinRAR.exe | C:\Users\admin\Desktop\WindowsServer2003.WindowsXP-KB968730-x64-ENU\SP2QFE\crypt32.dll | executable | |
MD5:— | SHA256:— | |||
| 1728 | WinRAR.exe | C:\Users\admin\Desktop\WindowsServer2003.WindowsXP-KB968730-x64-ENU\SP2QFE\wow\wcrypt32.dll | executable | |
MD5:— | SHA256:— | |||
| 1728 | WinRAR.exe | C:\Users\admin\Desktop\WindowsServer2003.WindowsXP-KB968730-x64-ENU\update\KB968730.CAT | cat | |
MD5:— | SHA256:— | |||
| 1728 | WinRAR.exe | C:\Users\admin\Desktop\WindowsServer2003.WindowsXP-KB968730-x64-ENU\update\branches.inf | text | |
MD5:— | SHA256:— | |||
| 3272 | WindowsServer2003.WindowsXP-KB968730-x64-ENU.exe | C:\d7c0cc3ace53a20acd0dd6fe4d06a319\update\branches.inf | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report