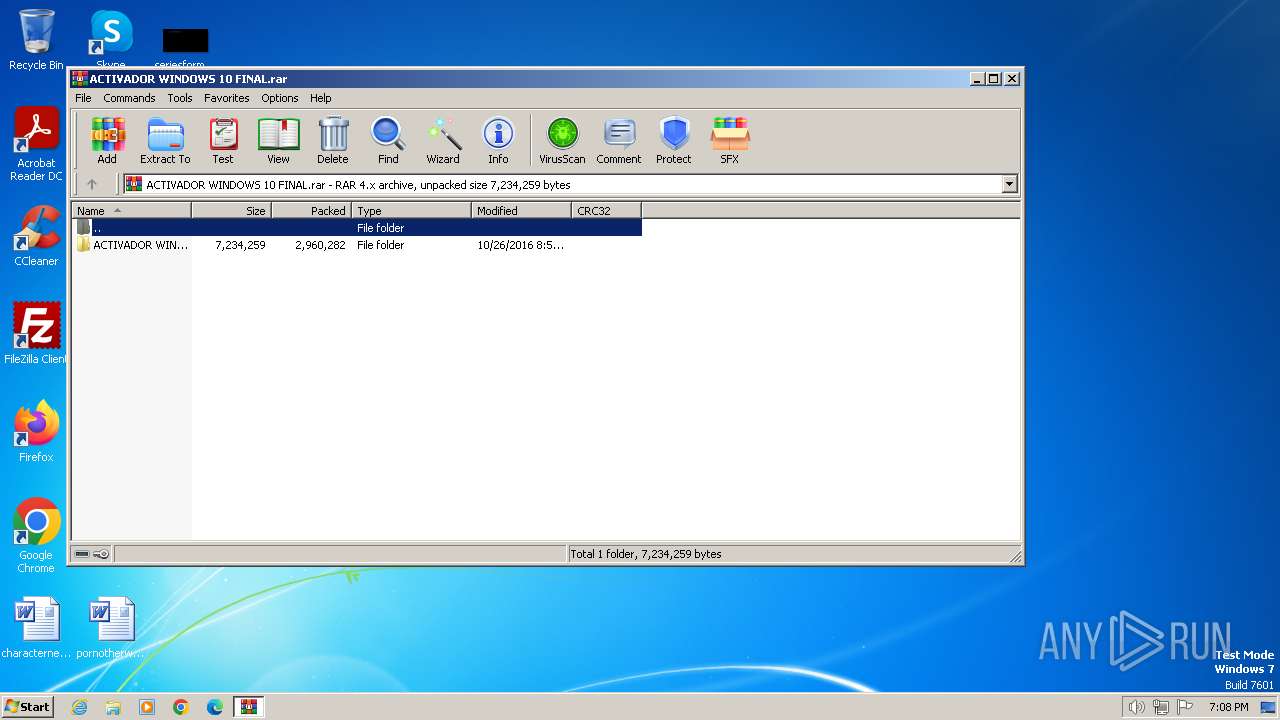
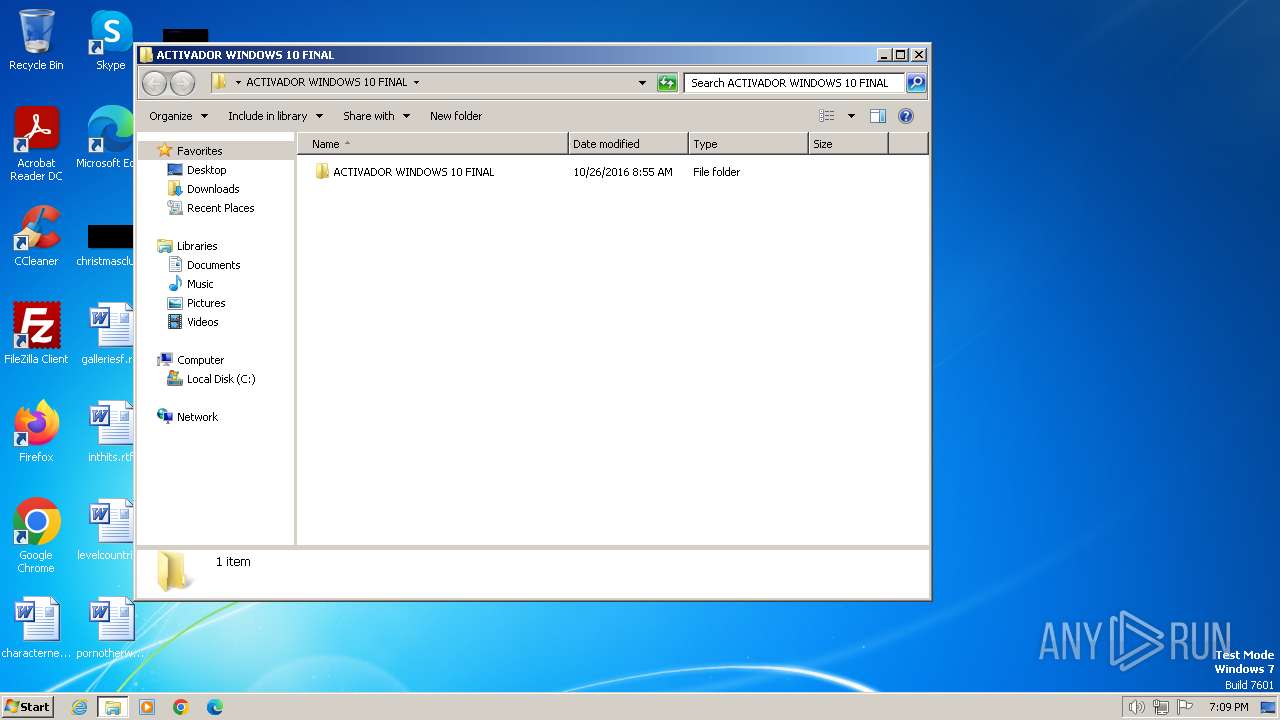
| File name: | ACTIVADOR WINDOWS 10 FINAL.rar |
| Full analysis: | https://app.any.run/tasks/21c59fe0-fa54-4d8b-94cc-e3dd9d936835 |
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2024, 19:08:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | A4476B9DB40C3420CB560EB72E6C9443 |
| SHA1: | CF6CA5141E7F65BCE02588F924A2F1861F145781 |
| SHA256: | 8EBE70793D8E4D79B54078BB6E84EFB184C76063A9ACB918B2E32BC4B29F79CE |
| SSDEEP: | 98304:uBj/F99Rj/T+KjXdgjHqXU3iF6NIBjRfUVcuvK4q1qDw6MlQvZi3ORAh9GR7zKhG:bZP |
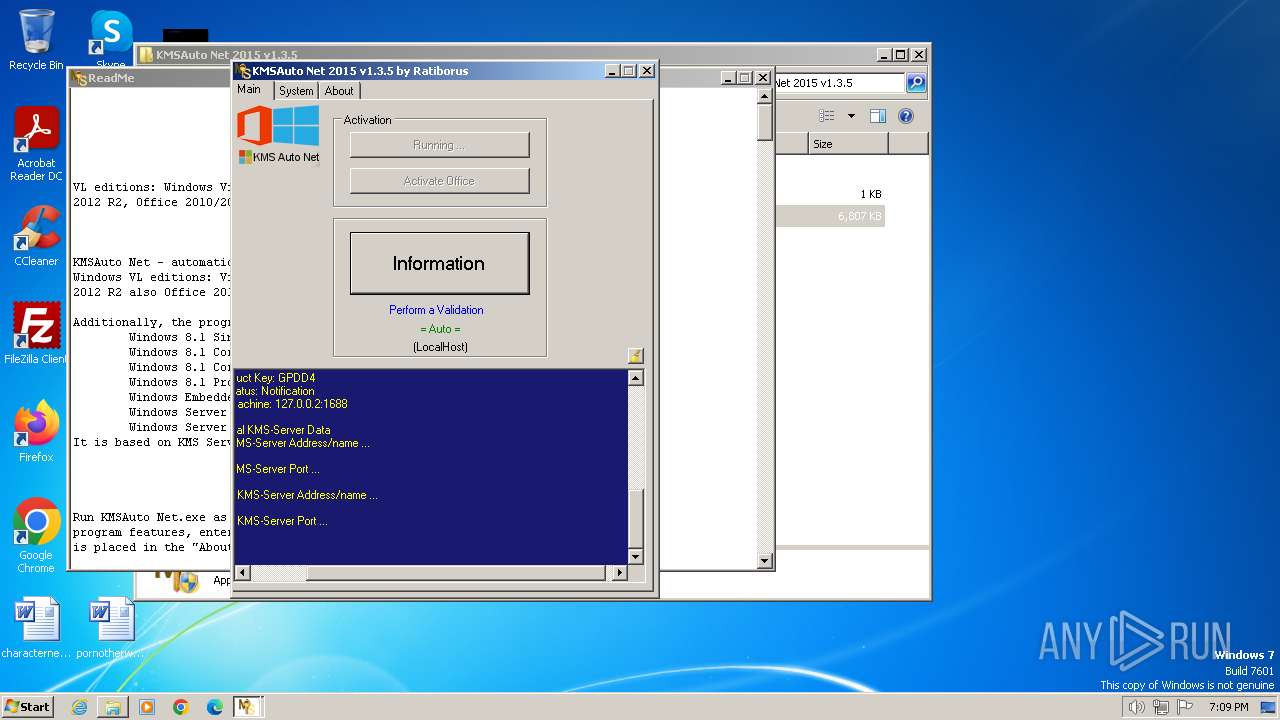
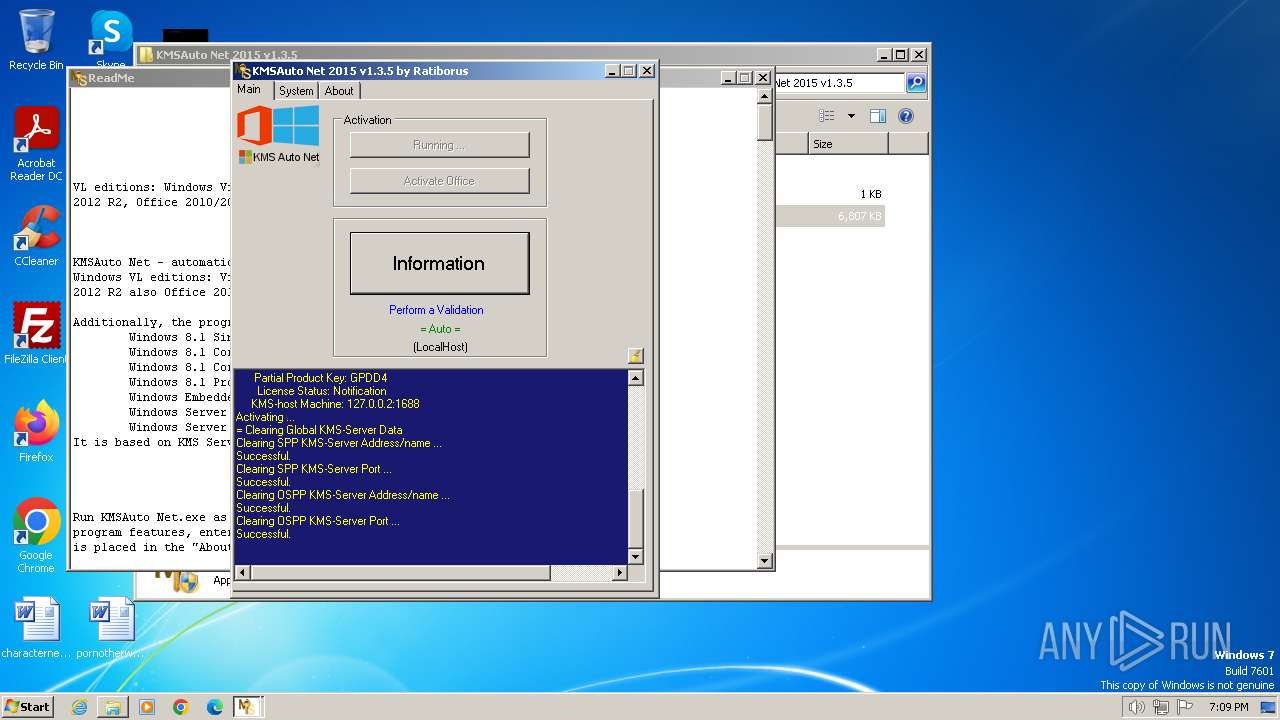
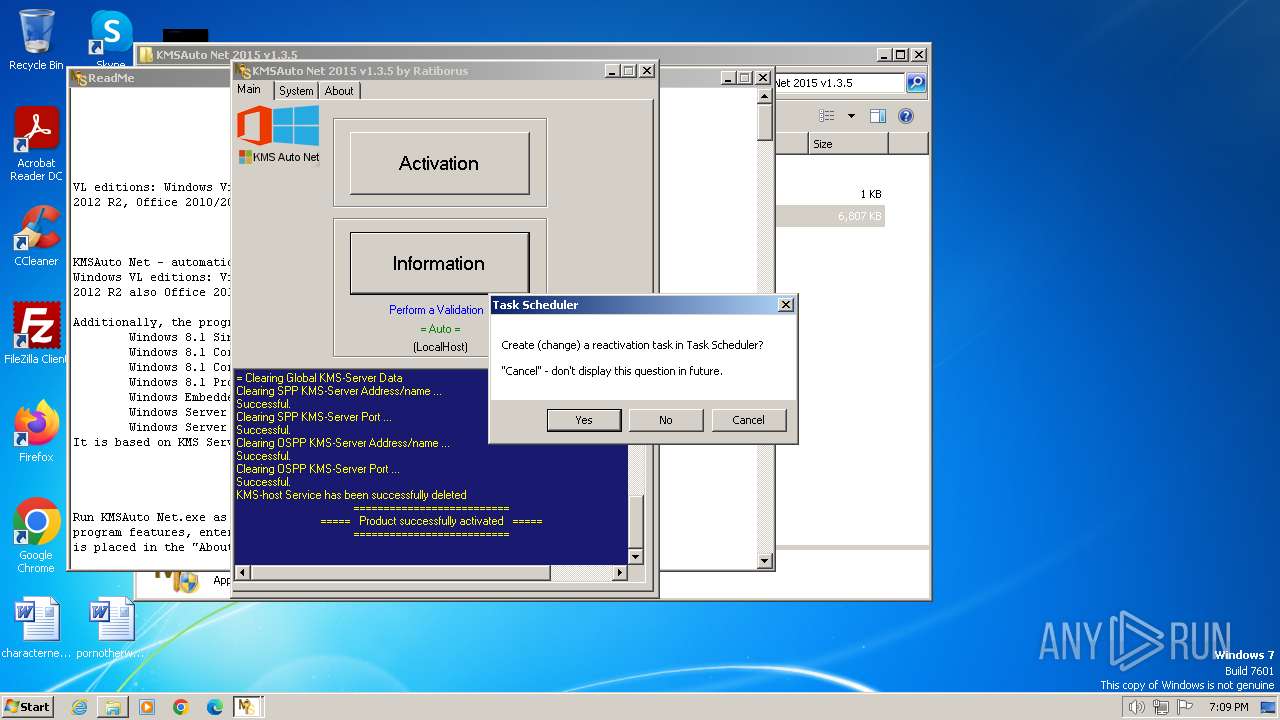
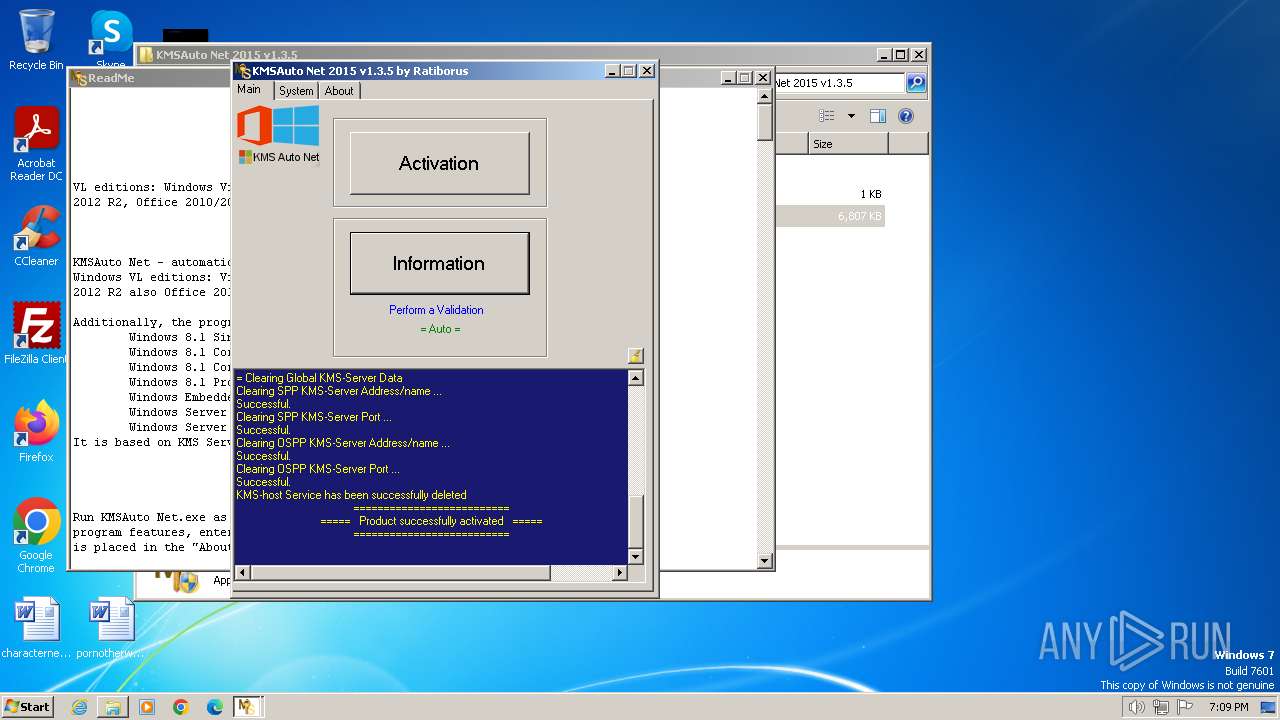
MALICIOUS
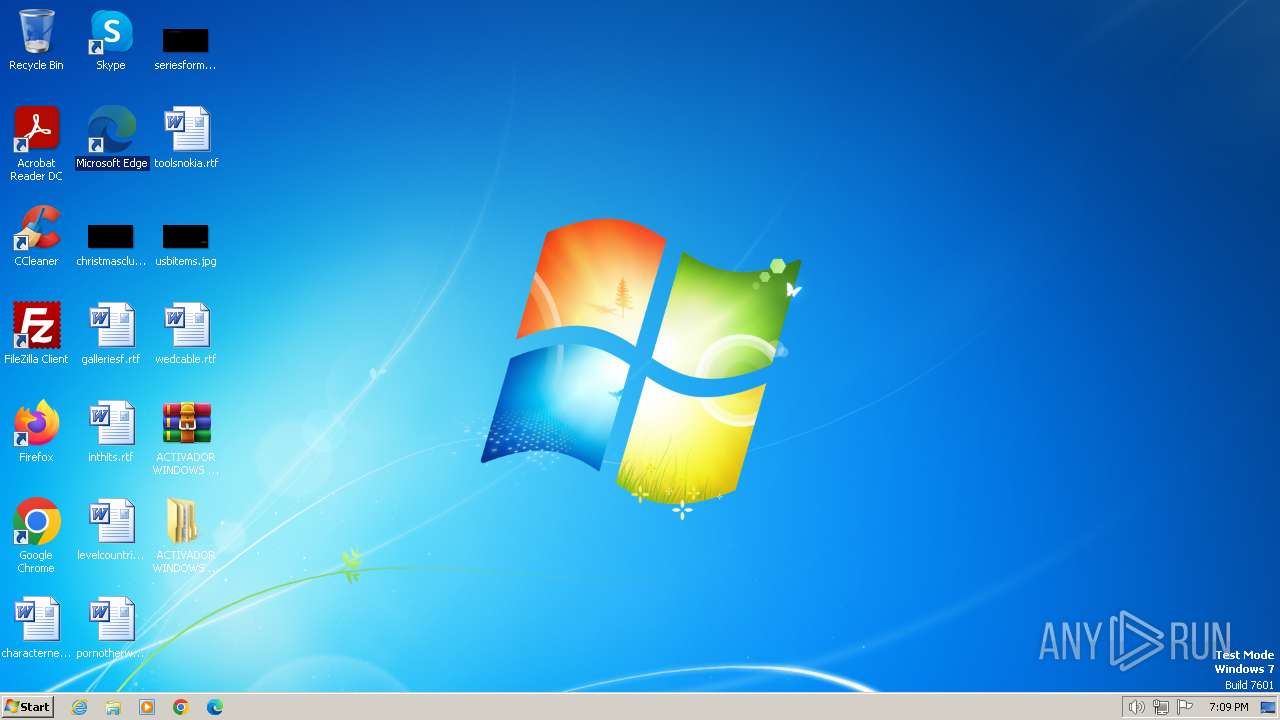
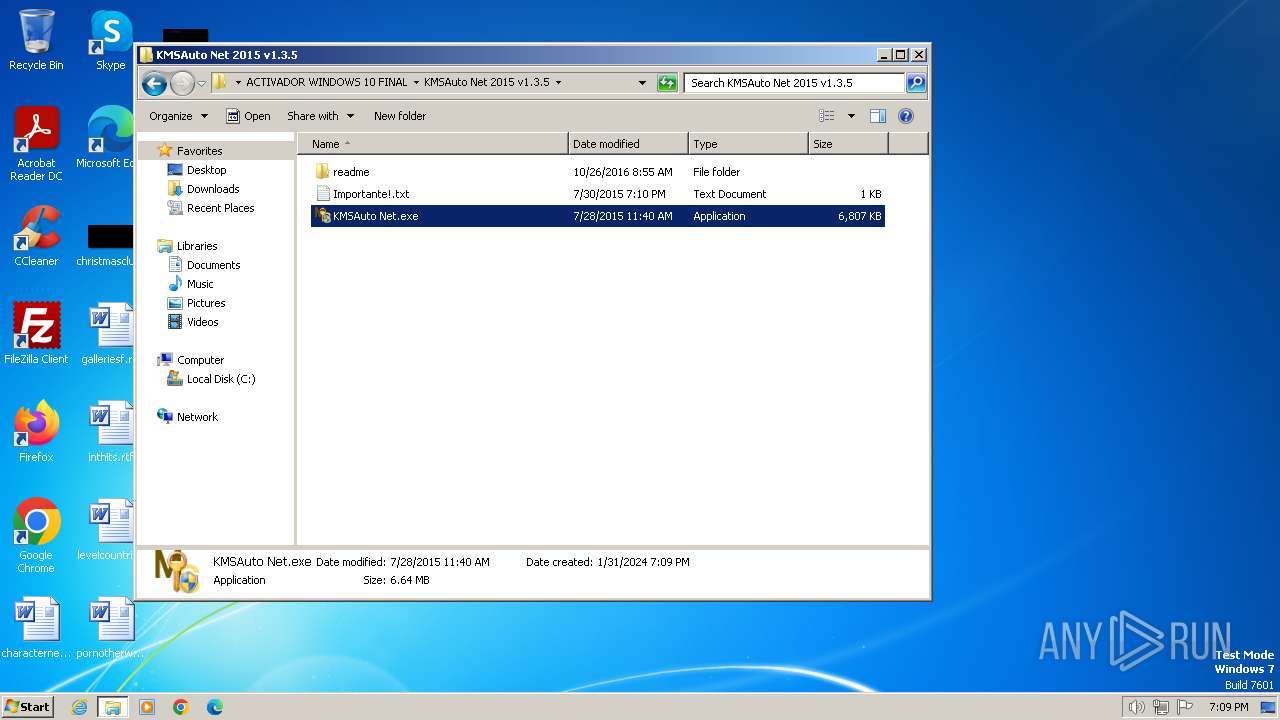
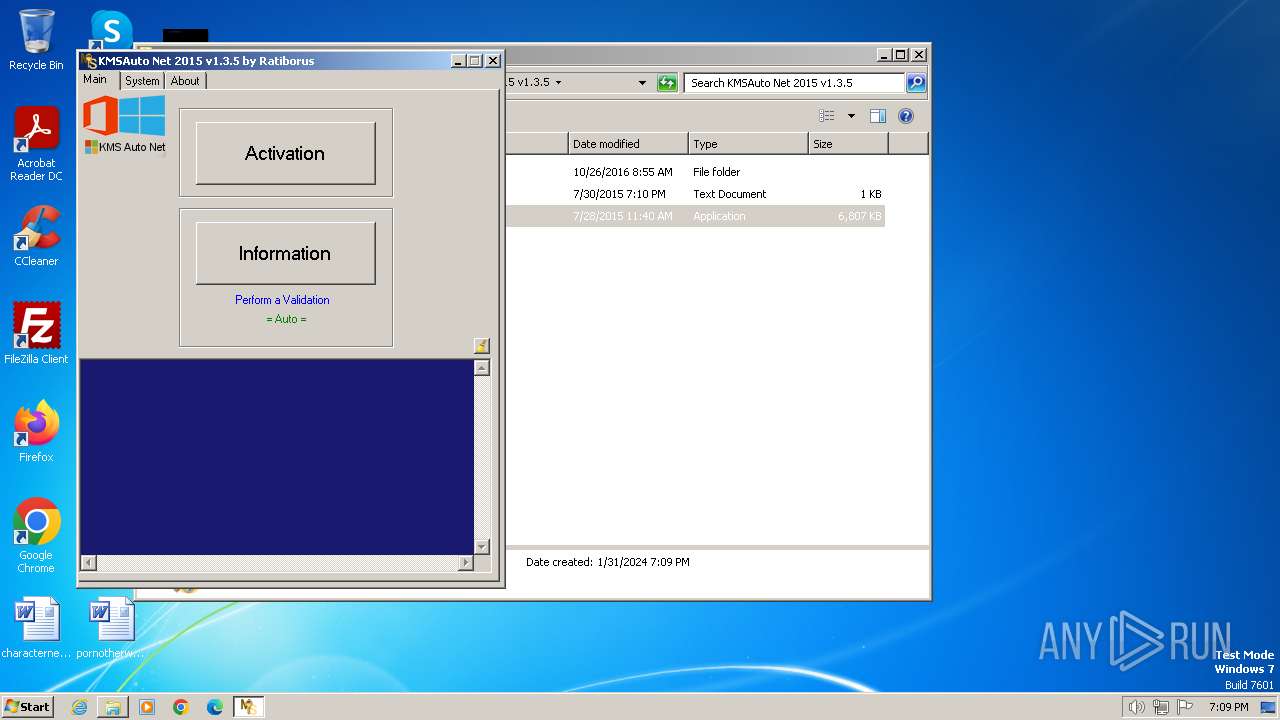
Drops the executable file immediately after the start
- WinRAR.exe (PID: 572)
- KMSAuto Net.exe (PID: 3752)
- bin.dat (PID: 3936)
- bin_x86.dat (PID: 2208)
Opens a text file (SCRIPT)
- cscript.exe (PID: 2996)
SUSPICIOUS
Executes WMI query (SCRIPT)
- cscript.exe (PID: 2996)
Reads Internet Explorer settings
- KMSAuto Net.exe (PID: 3752)
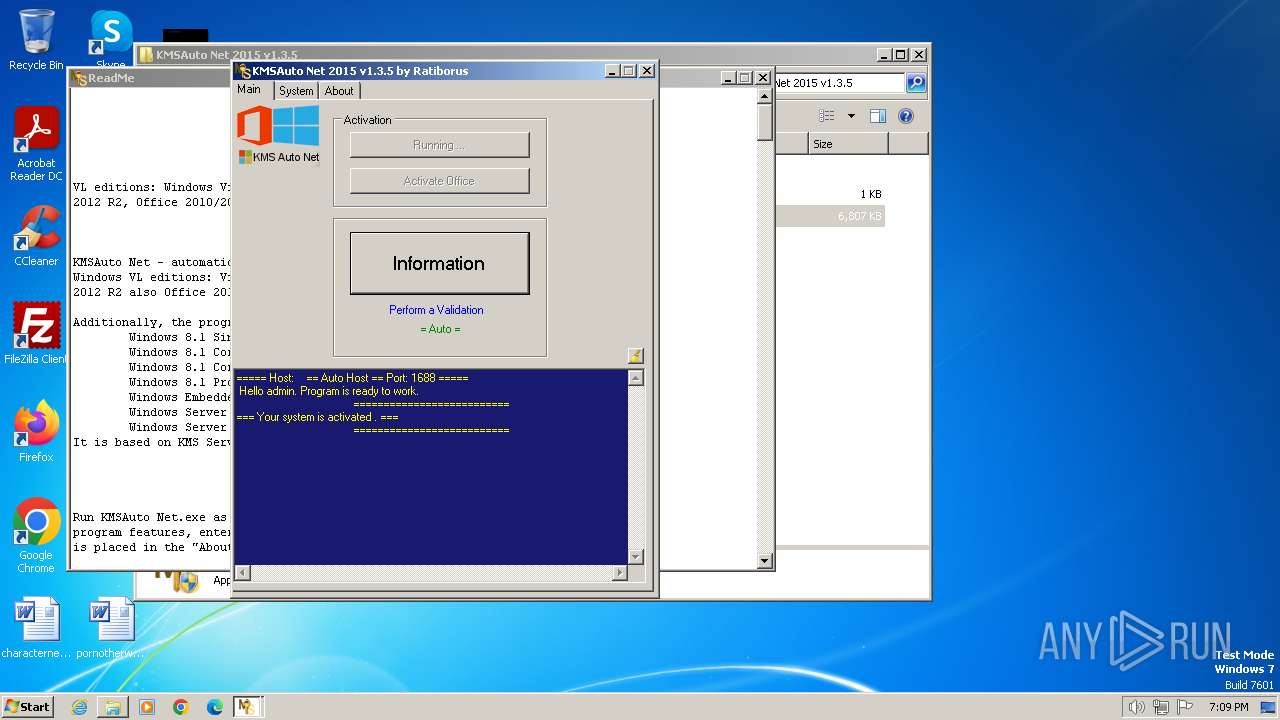
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 3752)
- cmd.exe (PID: 3724)
The process executes VB scripts
- KMSAuto Net.exe (PID: 3752)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 2996)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 2996)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 2996)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 2996)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 2996)
Executable content was dropped or overwritten
- bin.dat (PID: 3936)
- bin_x86.dat (PID: 2208)
- KMSAuto Net.exe (PID: 3752)
Starts application with an unusual extension
- cmd.exe (PID: 2292)
- cmd.exe (PID: 120)
Process drops legitimate windows executable
- bin_x86.dat (PID: 2208)
Drops a system driver (possible attempt to evade defenses)
- bin_x86.dat (PID: 2208)
Application launched itself
- cmd.exe (PID: 3724)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 3752)
Uses NETSH.EXE to add a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 3752)
Drops 7-zip archiver for unpacking
- KMSAuto Net.exe (PID: 3752)
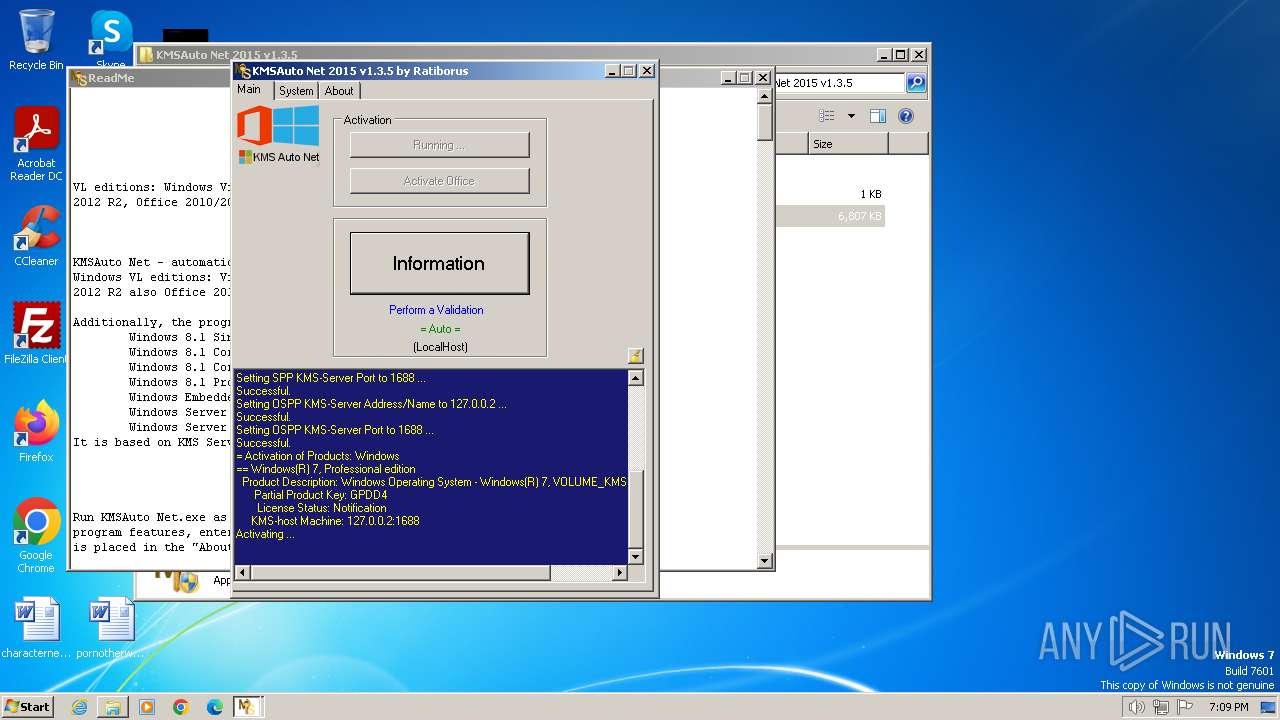
Creates or modifies Windows services
- KMSAuto Net.exe (PID: 3752)
Executes as Windows Service
- KMSSS.exe (PID: 880)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2776)
- KMSAuto Net.exe (PID: 3752)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 3752)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 572)
Checks supported languages
- KMSAuto Net.exe (PID: 3752)
- bin.dat (PID: 3936)
- bin_x86.dat (PID: 2208)
- KMSSS.exe (PID: 880)
Reads the computer name
- KMSAuto Net.exe (PID: 3752)
- KMSSS.exe (PID: 880)
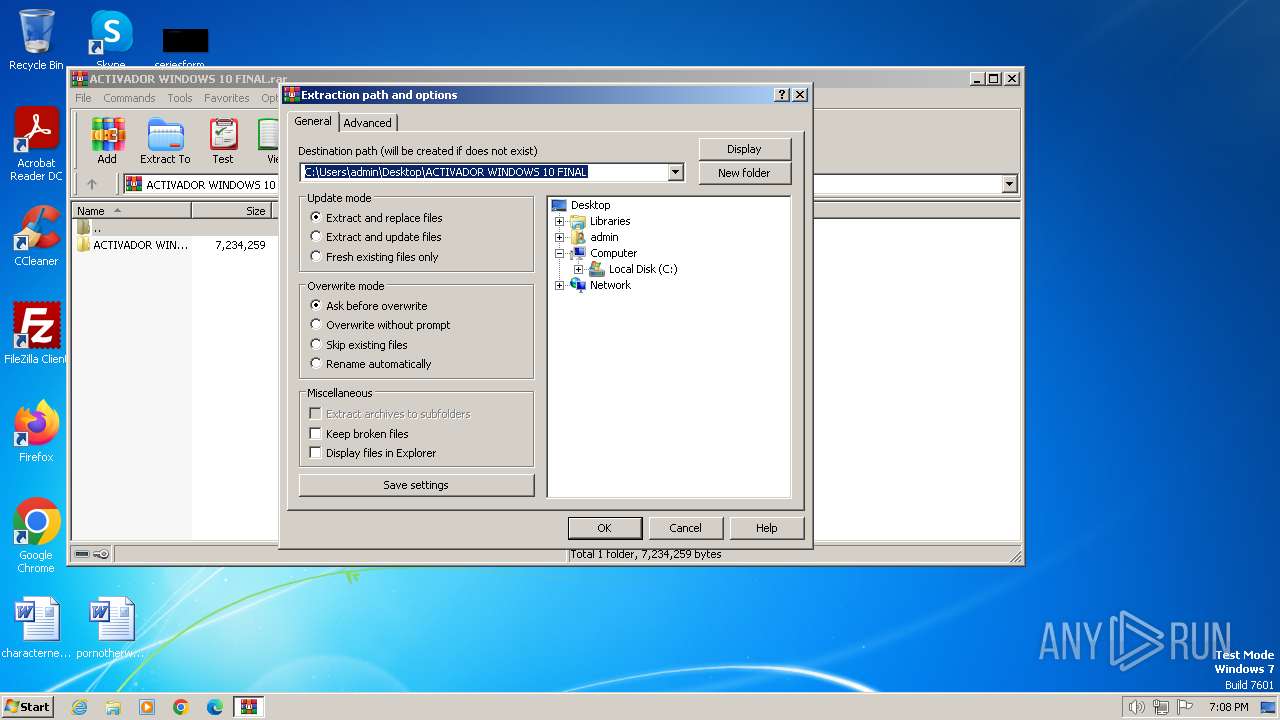
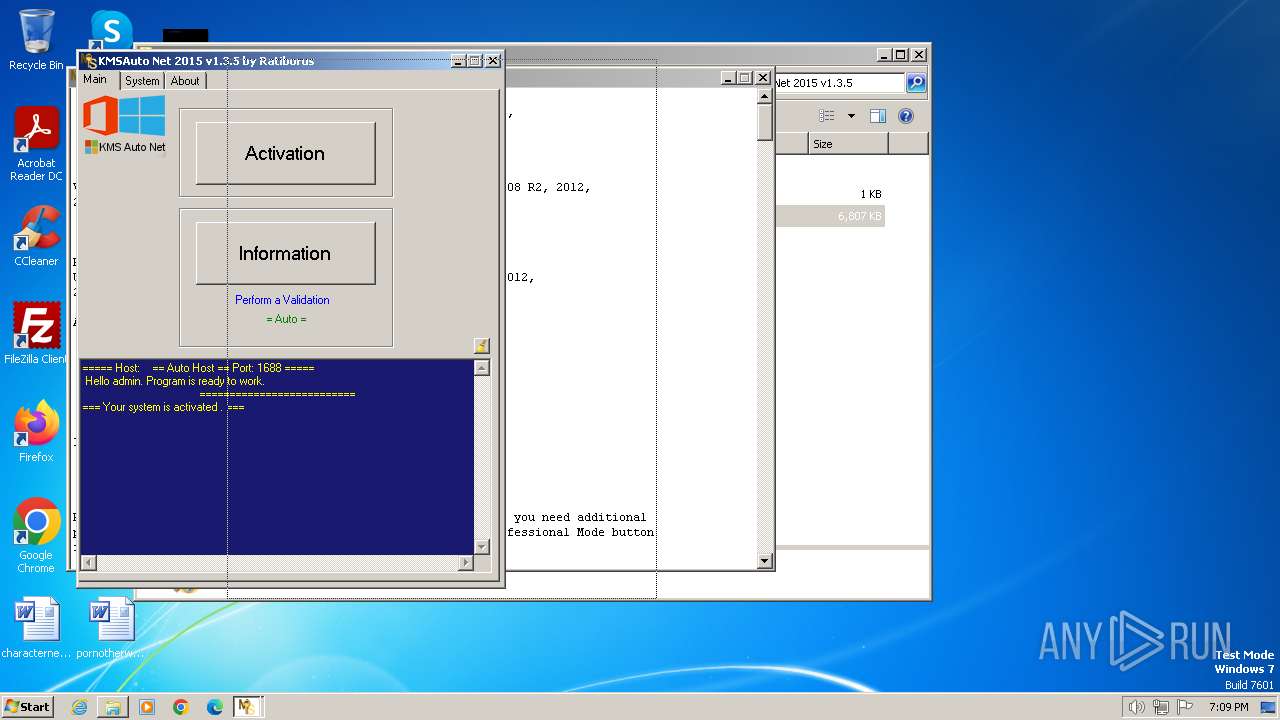
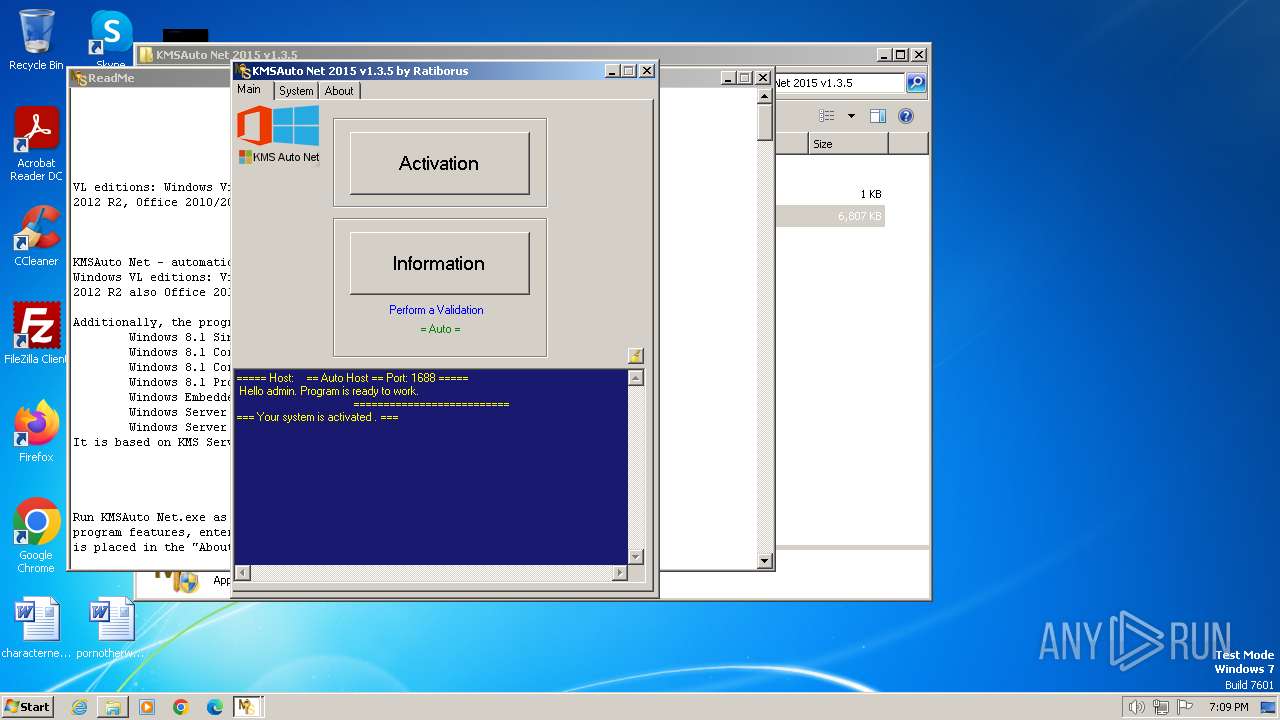
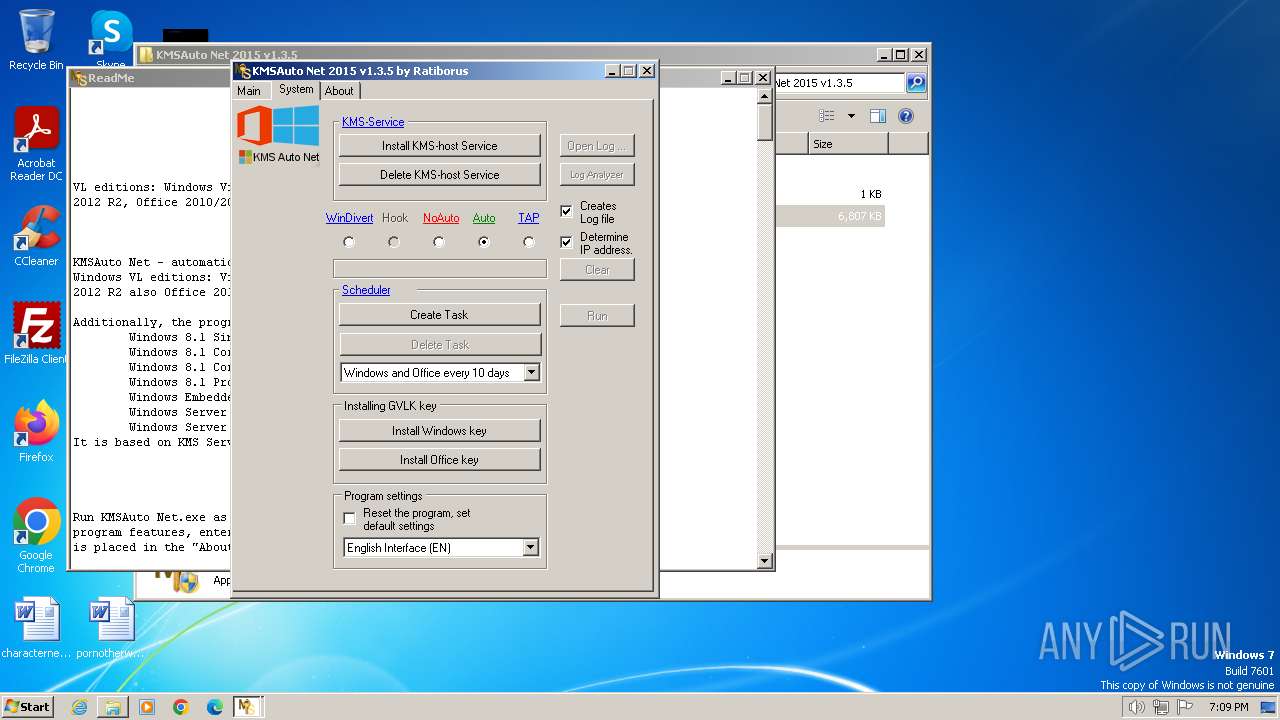
Manual execution by a user
- KMSAuto Net.exe (PID: 3752)
- KMSAuto Net.exe (PID: 1932)
Creates files in the program directory
- KMSAuto Net.exe (PID: 3752)
- bin_x86.dat (PID: 2208)
- bin.dat (PID: 3936)
- cmd.exe (PID: 2444)
- KMSSS.exe (PID: 880)
Reads the machine GUID from the registry
- KMSAuto Net.exe (PID: 3752)
- KMSSS.exe (PID: 880)
Creates files or folders in the user directory
- KMSAuto Net.exe (PID: 3752)
Reads Environment values
- KMSAuto Net.exe (PID: 3752)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2996)
Reads product name
- KMSAuto Net.exe (PID: 3752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 302 |
|---|---|
| UncompressedSize: | 387 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2015:07:30 19:10:36 |
| PackingMethod: | Normal |
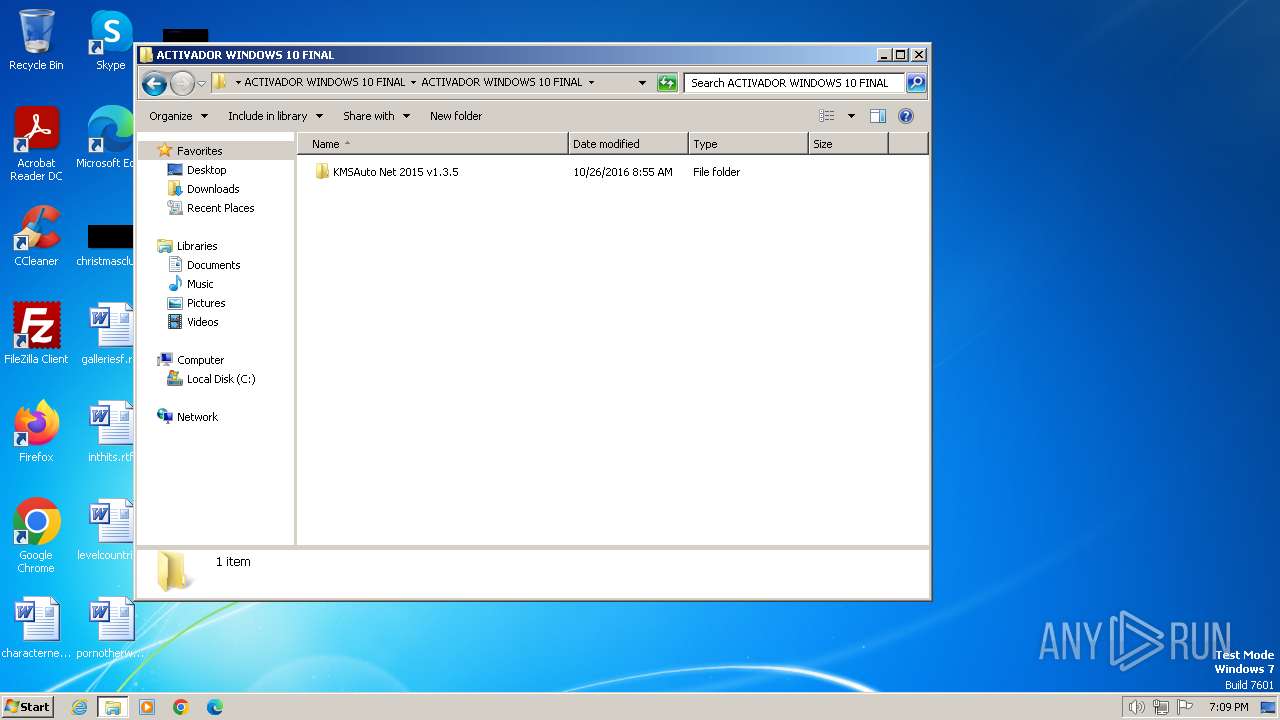
| ArchivedFileName: | ACTIVADOR WINDOWS 10 FINAL\ACTIVADOR WINDOWS 10 FINAL\KMSAuto Net 2015 v1.3.5\Importante!.txt |
Total processes
112
Monitored processes
37
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | C:\Windows\System32\cmd.exe /c bin.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 124 | C:\Windows\System32\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\0FF1CE15-A989-479D-AF46-F275C6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | C:\Windows\System32\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\59A52881-A989-479D-AF46-F275C6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | C:\Windows\System32\reg delete "HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 560 | cmd /c echo test>>"C:\Users\admin\Desktop\ACTIVADOR WINDOWS 10 FINAL\ACTIVADOR WINDOWS 10 FINAL\KMSAuto Net 2015 v1.3.5\test.test" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
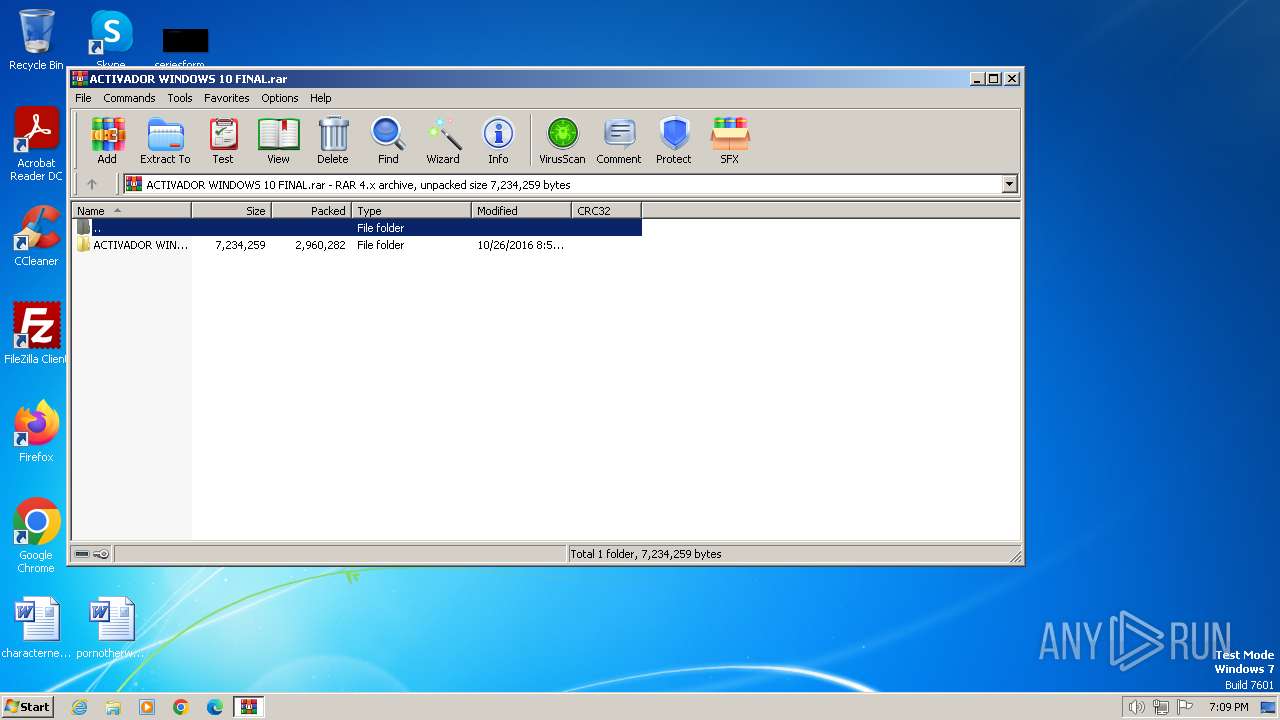
| 572 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\ACTIVADOR WINDOWS 10 FINAL.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 696 | C:\Windows\System32\cmd.exe /c del /F /Q "bin_x86.dat" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 880 | "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort -Log -IP | C:\ProgramData\KMSAuto\bin\KMSSS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: MDL Forum, mod by Ratiborus Integrity Level: SYSTEM Description: KMS Server Emulator Service (XP) Exit code: 0 Version: 1.2.1.0 Modules
| |||||||||||||||
| 1376 | reg.exe DELETE HKLM\SYSTEM\CurrentControlSet\Services\KMSEmulator /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "sc.exe" stop KMSEmulator | C:\Windows\System32\sc.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 351
Read events
3 186
Write events
161
Delete events
4
Modification events
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
16
Suspicious files
7
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
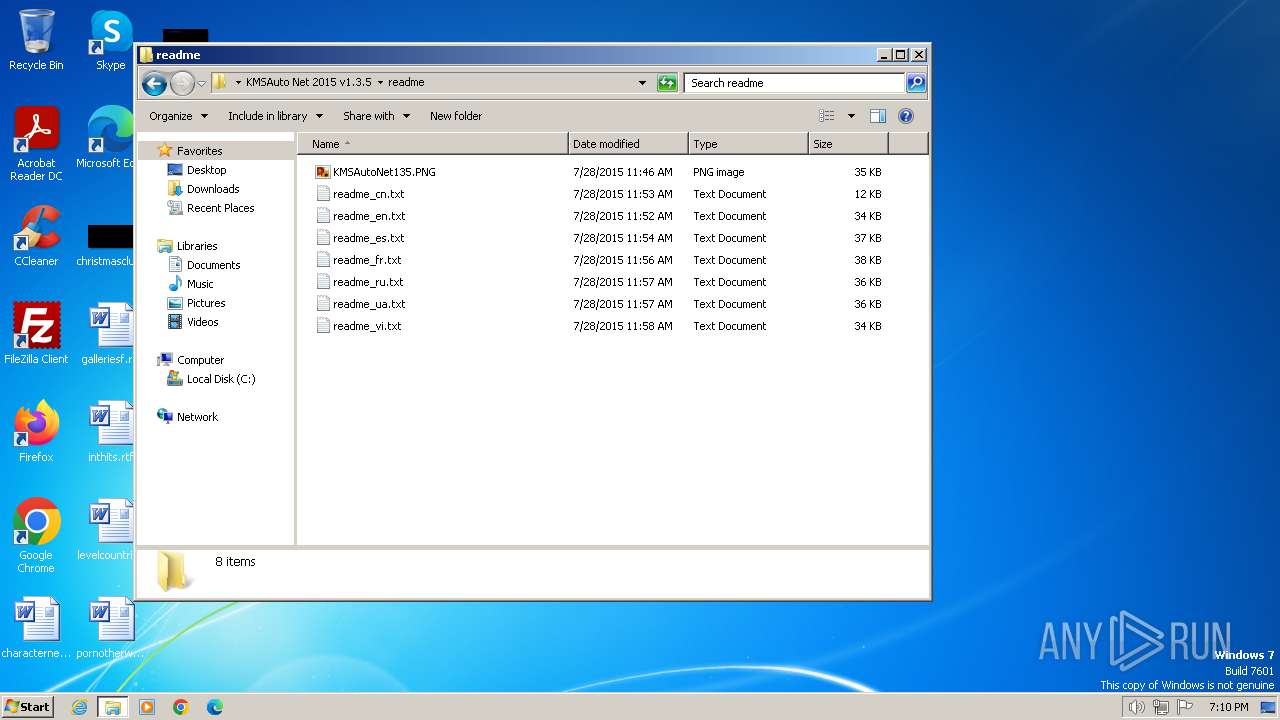
| 572 | WinRAR.exe | C:\Users\admin\Desktop\ACTIVADOR WINDOWS 10 FINAL\ACTIVADOR WINDOWS 10 FINAL\KMSAuto Net 2015 v1.3.5\Importante!.txt | text | |
MD5:52537AD40E30E02696E304454819408F | SHA256:67A7785A6DB50CEE1C7E656D437E55F74A1F3A76F5183F77B61DC50553579C2A | |||
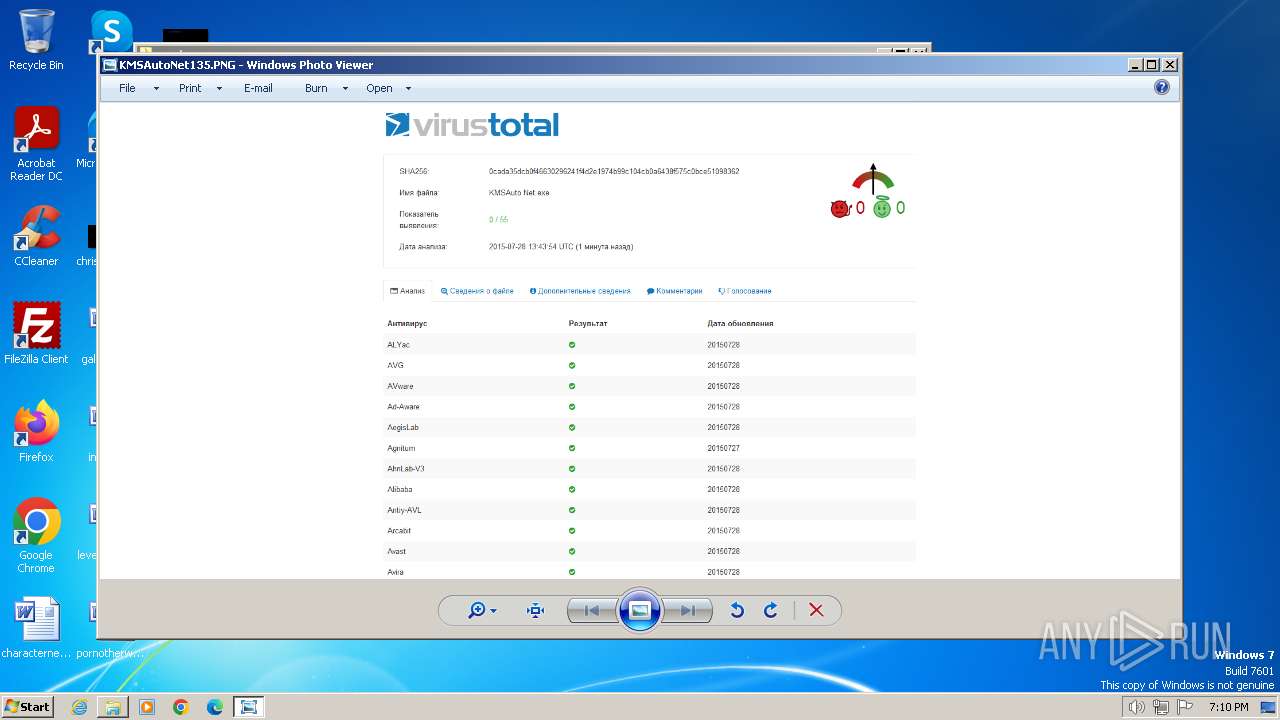
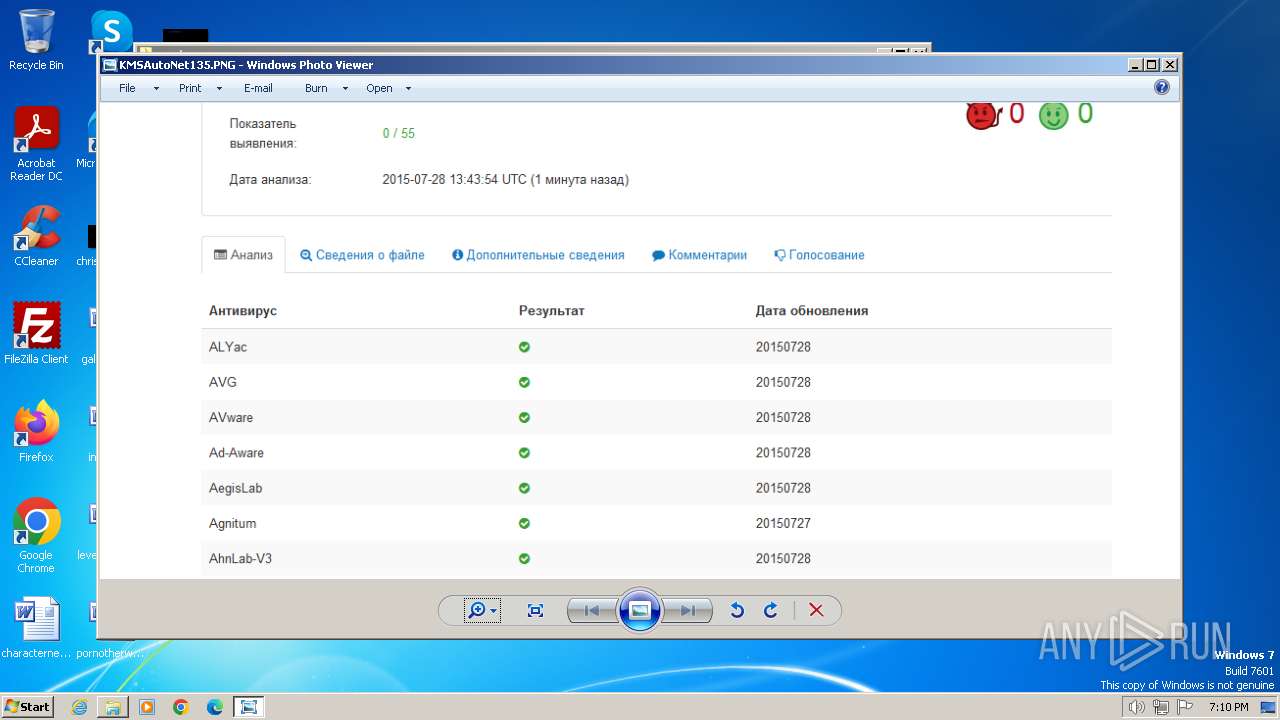
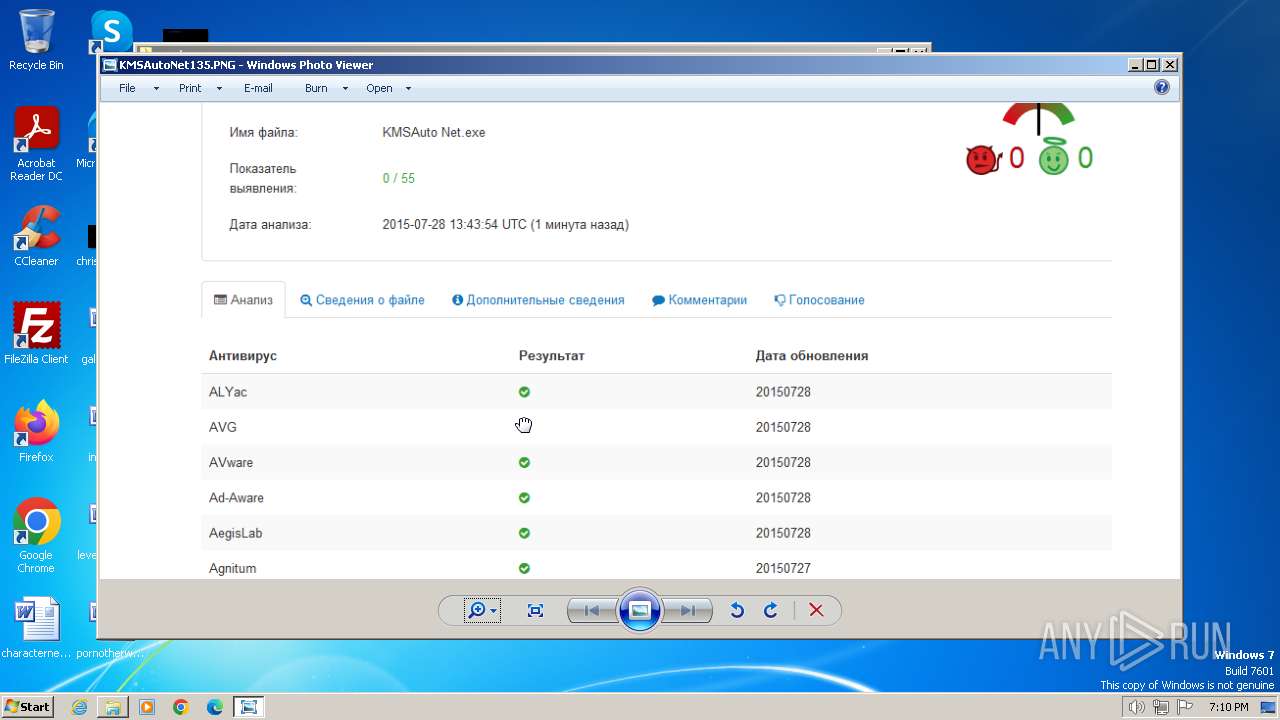
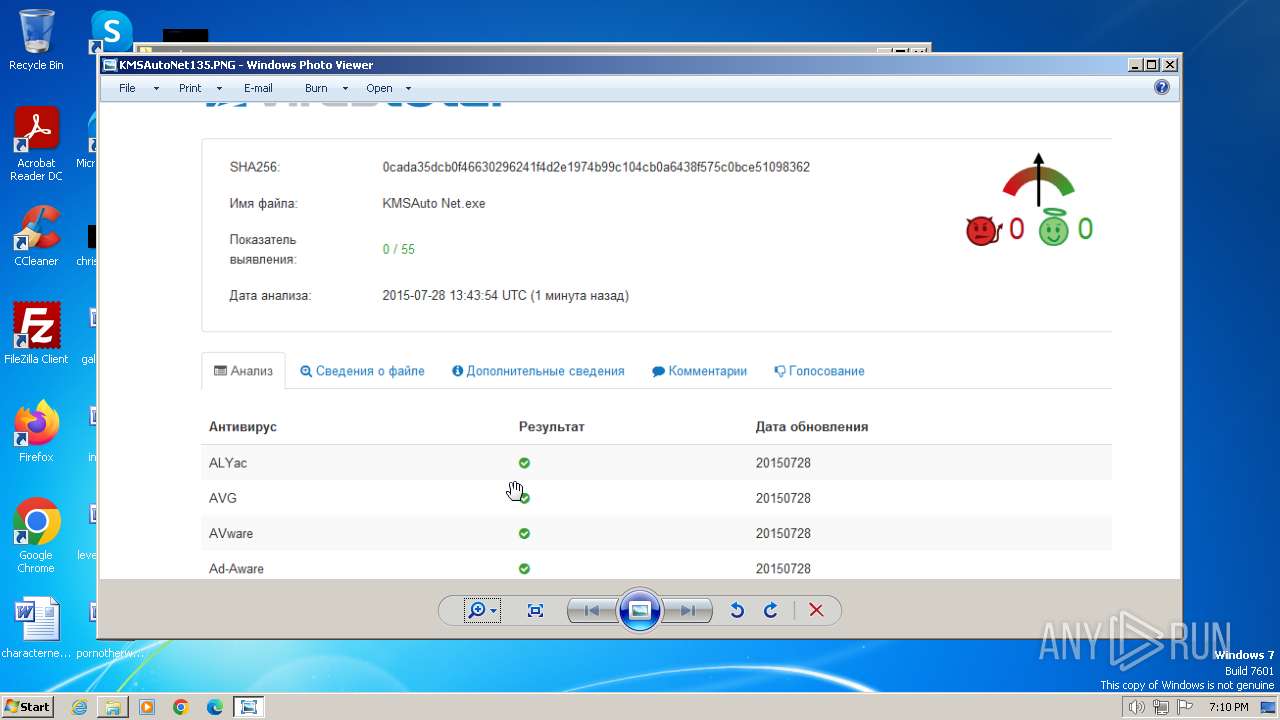
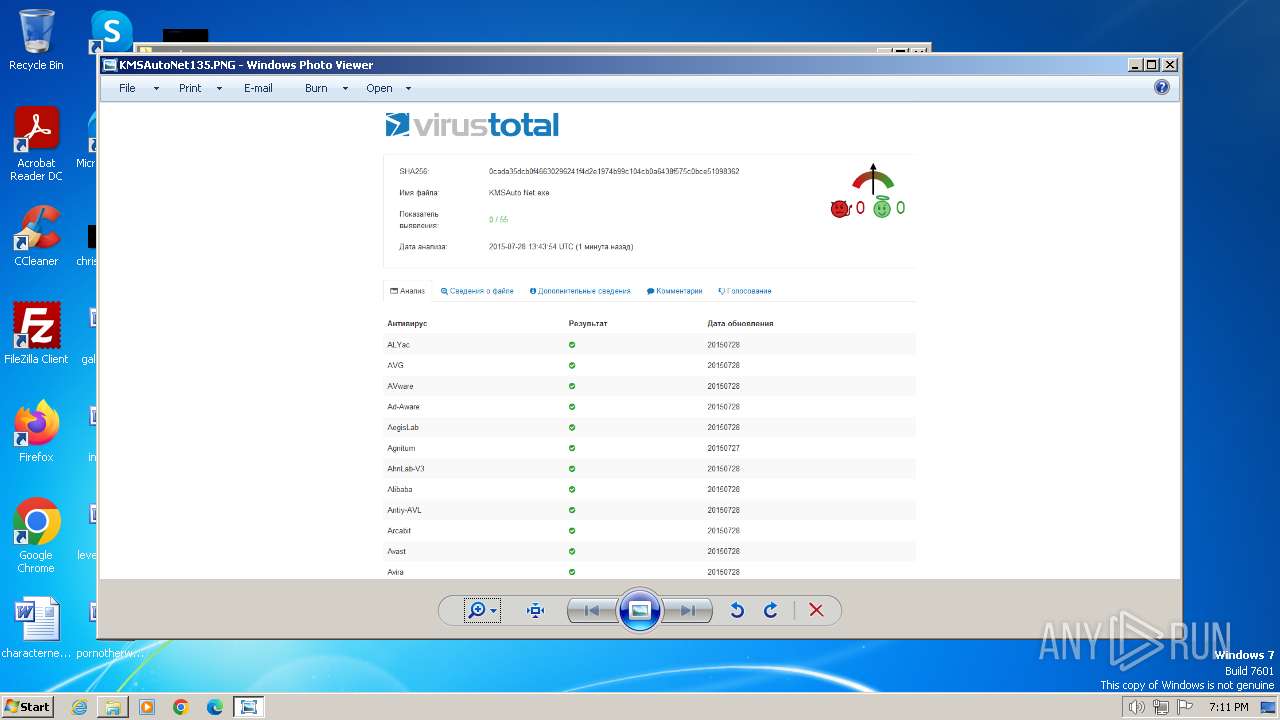
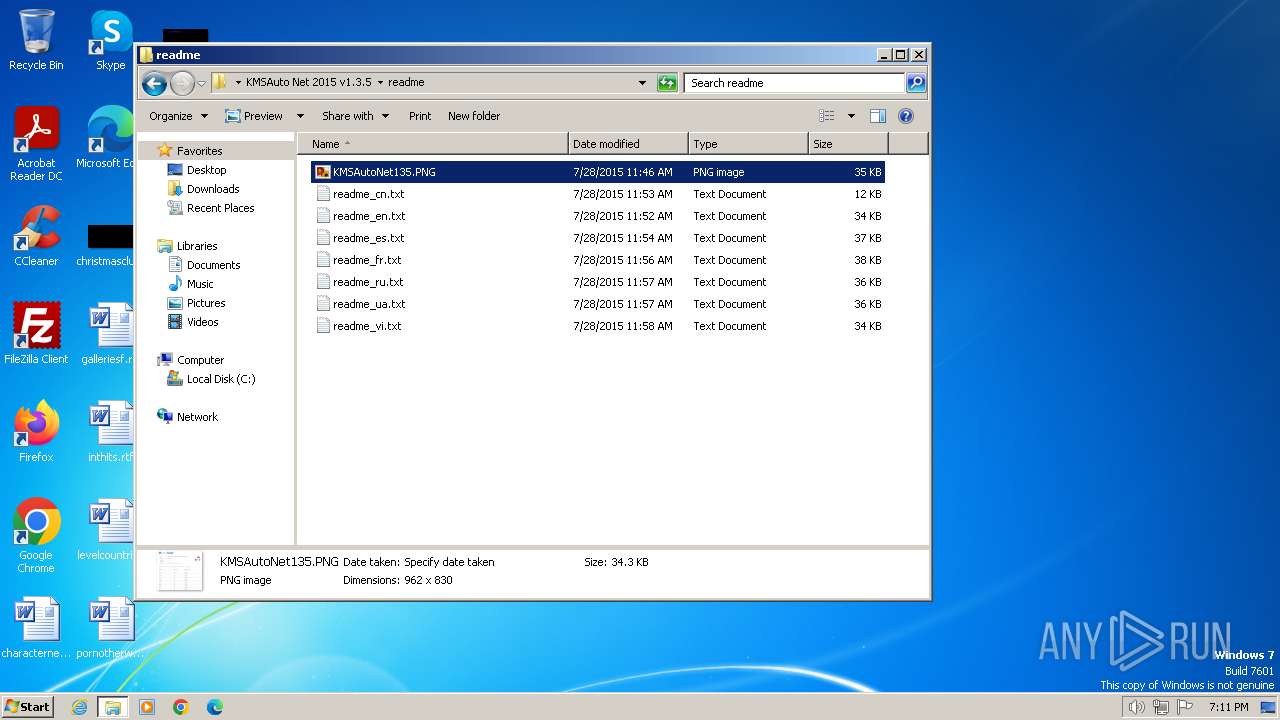
| 572 | WinRAR.exe | C:\Users\admin\Desktop\ACTIVADOR WINDOWS 10 FINAL\ACTIVADOR WINDOWS 10 FINAL\KMSAuto Net 2015 v1.3.5\readme\KMSAutoNet135.PNG | image | |
MD5:C669E33BE9AC2930C1E4933434B4BFBF | SHA256:9E43A49A896AE58745B44BBC69E27DF0885EAE3B769CEF86792EB7C1FAE868F6 | |||
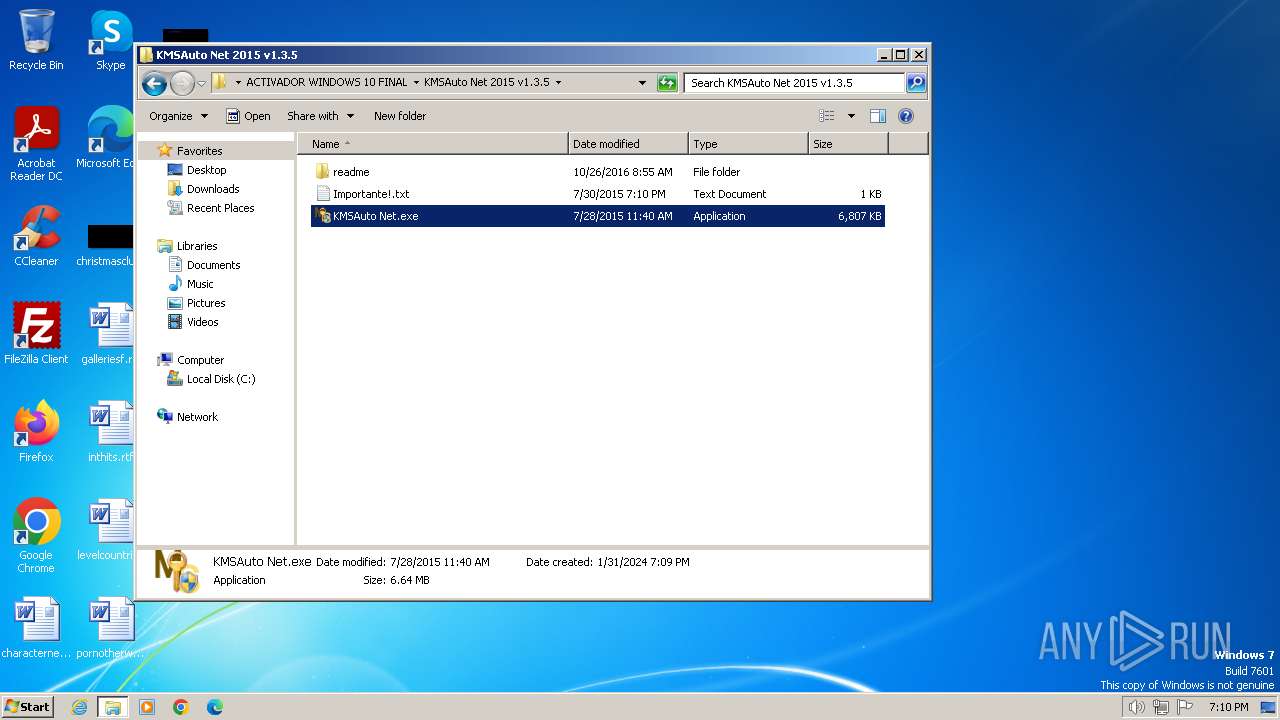
| 572 | WinRAR.exe | C:\Users\admin\Desktop\ACTIVADOR WINDOWS 10 FINAL\ACTIVADOR WINDOWS 10 FINAL\KMSAuto Net 2015 v1.3.5\KMSAuto Net.exe | executable | |
MD5:0CA71A9F5914ECA4E62D52694B3C2302 | SHA256:0CADA35DCB0F46630296241F4D2E1974B99C104CB0A6438F575C0BCE51098362 | |||
| 572 | WinRAR.exe | C:\Users\admin\Desktop\ACTIVADOR WINDOWS 10 FINAL\ACTIVADOR WINDOWS 10 FINAL\KMSAuto Net 2015 v1.3.5\readme\readme_fr.txt | text | |
MD5:3FA39B8942AD44C33E4BA2ACDAC95CF8 | SHA256:872D9C79021FDC8BAB4CD1C5D95BFDDBECADD8062D93E32B843D4D4F1FCE38A9 | |||
| 572 | WinRAR.exe | C:\Users\admin\Desktop\ACTIVADOR WINDOWS 10 FINAL\ACTIVADOR WINDOWS 10 FINAL\KMSAuto Net 2015 v1.3.5\readme\readme_en.txt | text | |
MD5:A4214551779E4D027C4C21A65FEAC0C6 | SHA256:8545638E4E191996B7D5148C838AB513C6F93C22753C83BCEE5887B82F4B1719 | |||
| 572 | WinRAR.exe | C:\Users\admin\Desktop\ACTIVADOR WINDOWS 10 FINAL\ACTIVADOR WINDOWS 10 FINAL\KMSAuto Net 2015 v1.3.5\readme\readme_cn.txt | text | |
MD5:53B95C350114CCA14AFDA7CBA393D8A3 | SHA256:A5010CA12FF3477DC893C86512783A1459FB612A6172A13020DF02E621D15E37 | |||
| 3936 | bin.dat | C:\ProgramData\KMSAuto\bin\KMSSS.exe | executable | |
MD5:0F03F72A92AEF6D63EB74E73F8AC201D | SHA256:ACD55C44B8B0D66D66DEFED85CA18082C092F048D3621DA827FCE593305C11FD | |||
| 3752 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\MSfree Inc\kmsauto.ini | text | |
MD5:33C2F031B8C6D6CB29F964A54FEDAA13 | SHA256:54BC7607535F2EC23A258FDD96257B2CE4374705599EF3E09A7B5643B08035E8 | |||
| 3936 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror.exe | executable | |
MD5:362498C3E71EEAA066A67E4A3F981D1C | SHA256:D87E8D9D43758CE67A8052CB2334B99CC24F9B0437EE44815F360BE0B22D835A | |||
| 3752 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin.dat | executable | |
MD5:25F096B533E87AFBA34432F577E45013 | SHA256:0B4AF6D407E5ADB4975CCB3D3B1A504F211DFC9E3307A36E8D40D8029A7D11FA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |