| File name: | Email_Tools_1.0.exe |
| Full analysis: | https://app.any.run/tasks/1f4bb7e6-3771-463c-871c-a168b7ae38fd |
| Verdict: | Malicious activity |
| Analysis date: | September 05, 2019, 15:35:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 15426C7EF693C662375EF748E72079F7 |
| SHA1: | D14187980B8B45D9E9F6918A8805EBD0D5FD9593 |
| SHA256: | 8EAA27BF1C73FE65C189ACC378067AFABF7A8819B4739AC9E129D51470729D41 |
| SSDEEP: | 49152:tU8ARQ6SCppkDw9BmpZ3aTPIyv5sdiYKFGjQ2svD/DX+y4onCYDoDY:W8ASDw9Bw4KAGjlsvD/D+donCYUs |
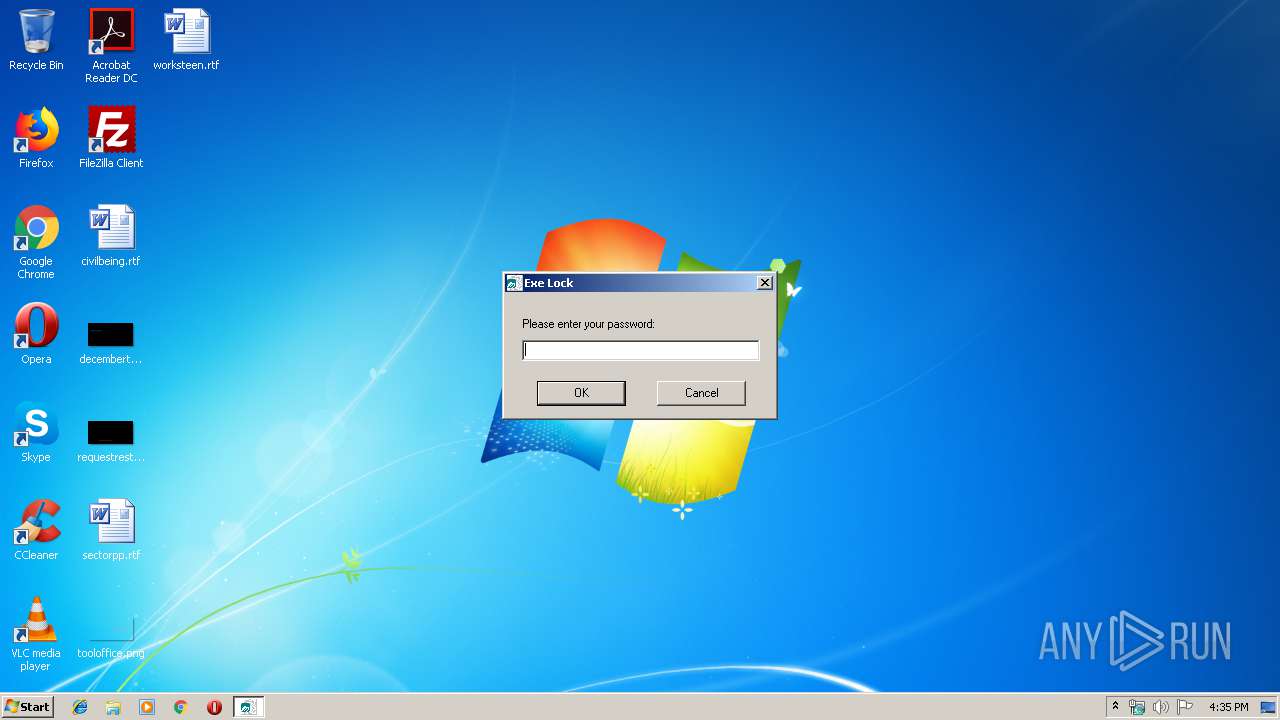
MALICIOUS
Application was dropped or rewritten from another process
- __Email_Tools_1.0.exe (PID: 1424)
- temp2.tem (PID: 3300)
SUSPICIOUS
Executable content was dropped or overwritten
- __Email_Tools_1.0.exe (PID: 1424)
- Email_Tools_1.0.exe (PID: 3788)
Starts application with an unusual extension
- __Email_Tools_1.0.exe (PID: 1424)
INFO
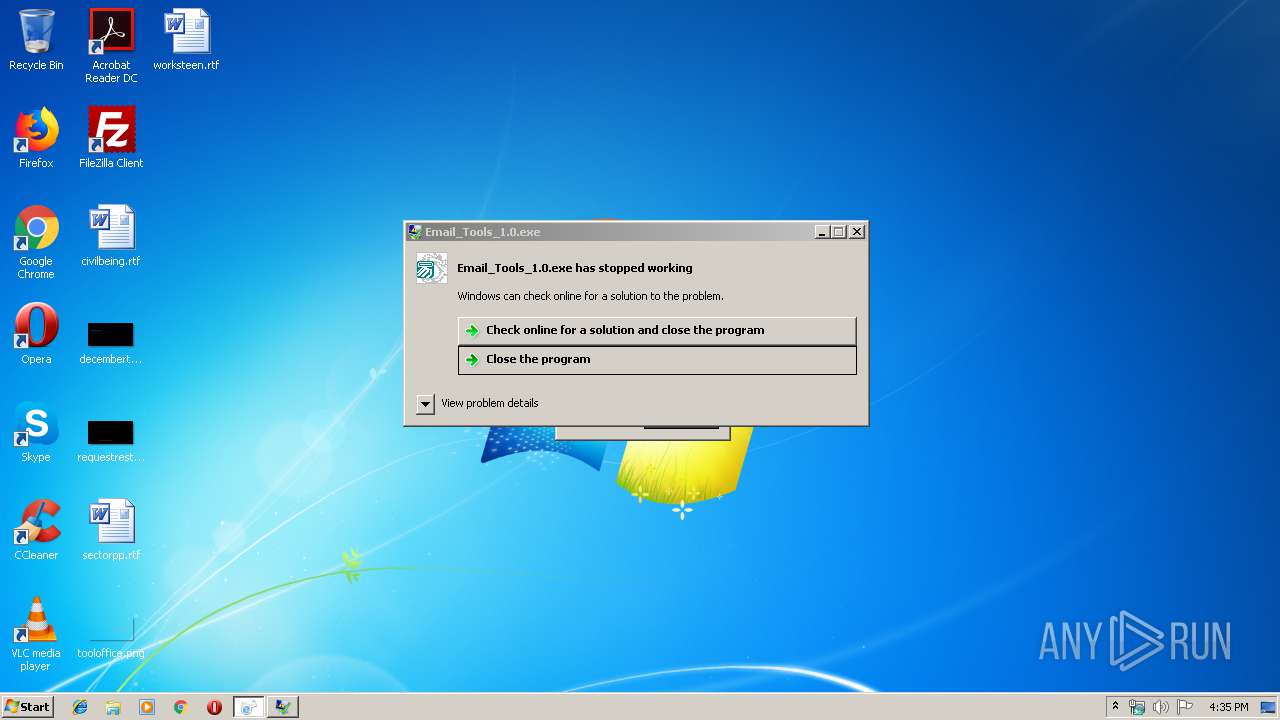
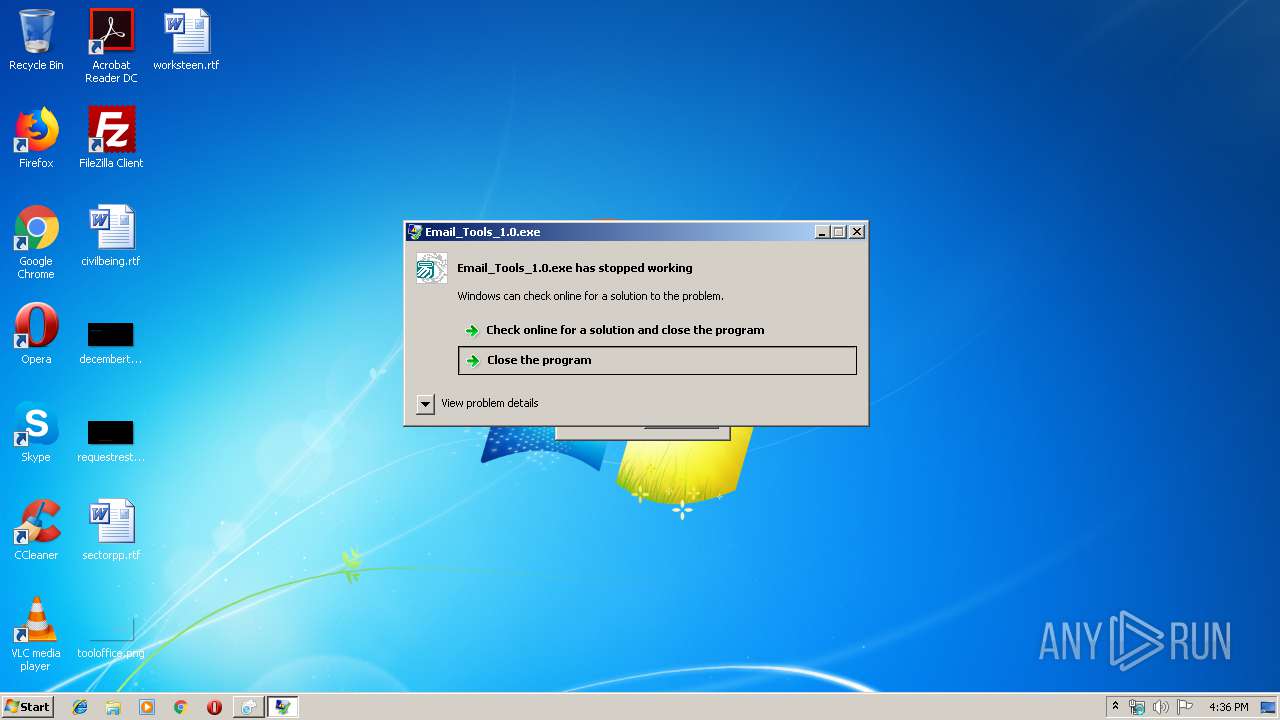
Application was crashed
- Email_Tools_1.0.exe (PID: 3788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:30 11:31:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1594368 |
| InitializedDataSize: | 284160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x18655c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.5 |
| ProductVersionNumber: | 2.0.0.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
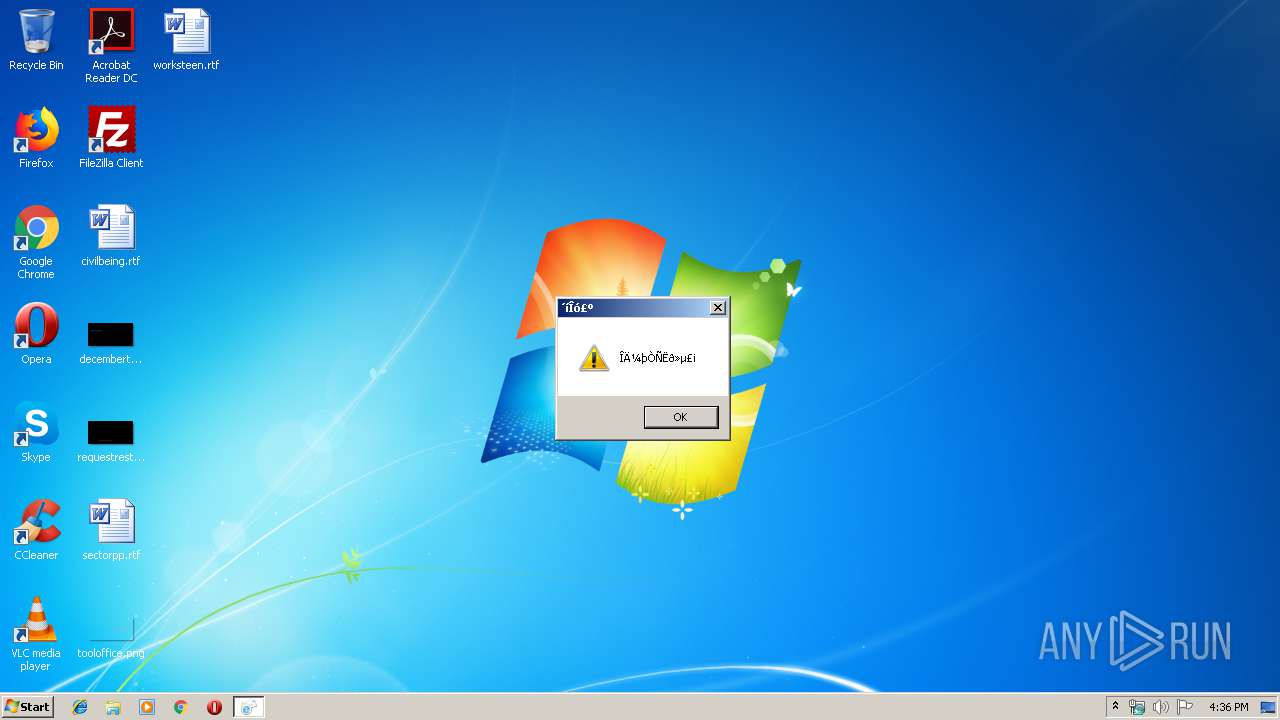
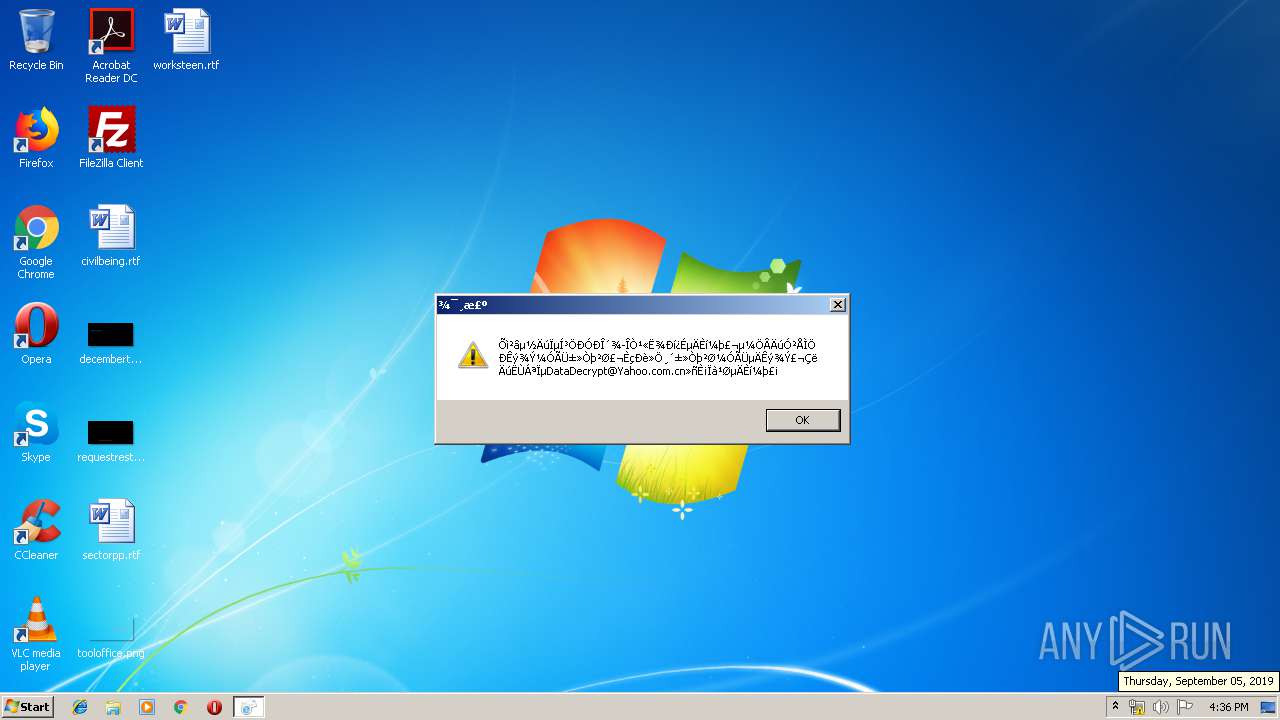
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 2.0.0.5 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 2.0.0.0 |
| Comments: | - |
| LastCompiledTime: | 2012-09-20 16:21:19 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Oct-2012 10:31:14 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 2.0.0.5 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 2.0.0.0 |
| Comments: | - |
| LastCompiledTime: | 2012-09-20 16:21:19 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 30-Oct-2012 10:31:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00183D14 | 0x00183E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.38124 |
.itext | 0x00185000 | 0x000015B0 | 0x00001600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.00677 |
.data | 0x00187000 | 0x00008618 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.67644 |
.bss | 0x00190000 | 0x00005908 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00196000 | 0x000038DA | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.13914 |
.didata | 0x0019A000 | 0x00000326 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29656 |
.tls | 0x0019B000 | 0x00000048 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0019C000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.210826 |
.reloc | 0x0019D000 | 0x000216A4 | 0x00021800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.70396 |
.rsrc | 0x001BF000 | 0x000174F4 | 0x00017600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59527 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91814 | 850 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 2.80231 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4069 | 2.74725 | 160 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4070 | 3.32872 | 1212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4071 | 3.3817 | 968 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
msimg32.dll |
msvcrt.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1424 | __Email_Tools_1.0.exe | C:\Users\admin\AppData\Local\Temp\__Email_Tools_1.0.exe | Email_Tools_1.0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2768 | C:\Users\admin\AppData\Local\Temp\temp1.tem | C:\Users\admin\AppData\Local\Temp\temp1.tem | — | __Email_Tools_1.0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3300 | C:\Users\admin\AppData\Local\Temp\temp2.tem | C:\Users\admin\AppData\Local\Temp\temp2.tem | — | __Email_Tools_1.0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3788 | "C:\Users\admin\AppData\Local\Temp\Email_Tools_1.0.exe" | C:\Users\admin\AppData\Local\Temp\Email_Tools_1.0.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 250477278 Version: 2.0.0.5 Modules
| |||||||||||||||
Total events
104
Read events
104
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1424 | __Email_Tools_1.0.exe | C:\Users\admin\AppData\Local\Temp\temp1.tem | — | |
MD5:— | SHA256:— | |||
| 2768 | temp1.tem | C:\Users\admin\AppData\Local\Temp\1502015\....\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 2768 | temp1.tem | C:\Users\admin\AppData\Local\Temp\1502015\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 3788 | Email_Tools_1.0.exe | C:\Users\admin\AppData\Local\Temp\__Email_Tools_1.0.exe | executable | |
MD5:— | SHA256:— | |||
| 3788 | Email_Tools_1.0.exe | C:\Users\admin\AppData\Local\lck | text | |
MD5:— | SHA256:— | |||
| 1424 | __Email_Tools_1.0.exe | C:\Users\admin\AppData\Local\Temp\temp2.tem | executable | |
MD5:— | SHA256:— | |||
| 1424 | __Email_Tools_1.0.exe | C:\Users\admin\AppData\Local\Temp\E_4\krnln.fnr | executable | |
MD5:97C8FE752E354B2945E4C593A87E4A8B | SHA256:820D8DD49BAED0DA44D42555AD361D78E068115661DCE72AE6578DCDAB6BAEAD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3788 | Email_Tools_1.0.exe | 50.93.203.14:80 | www.kakasoft.com | Jazz Network Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakasoft.com |
| malicious |