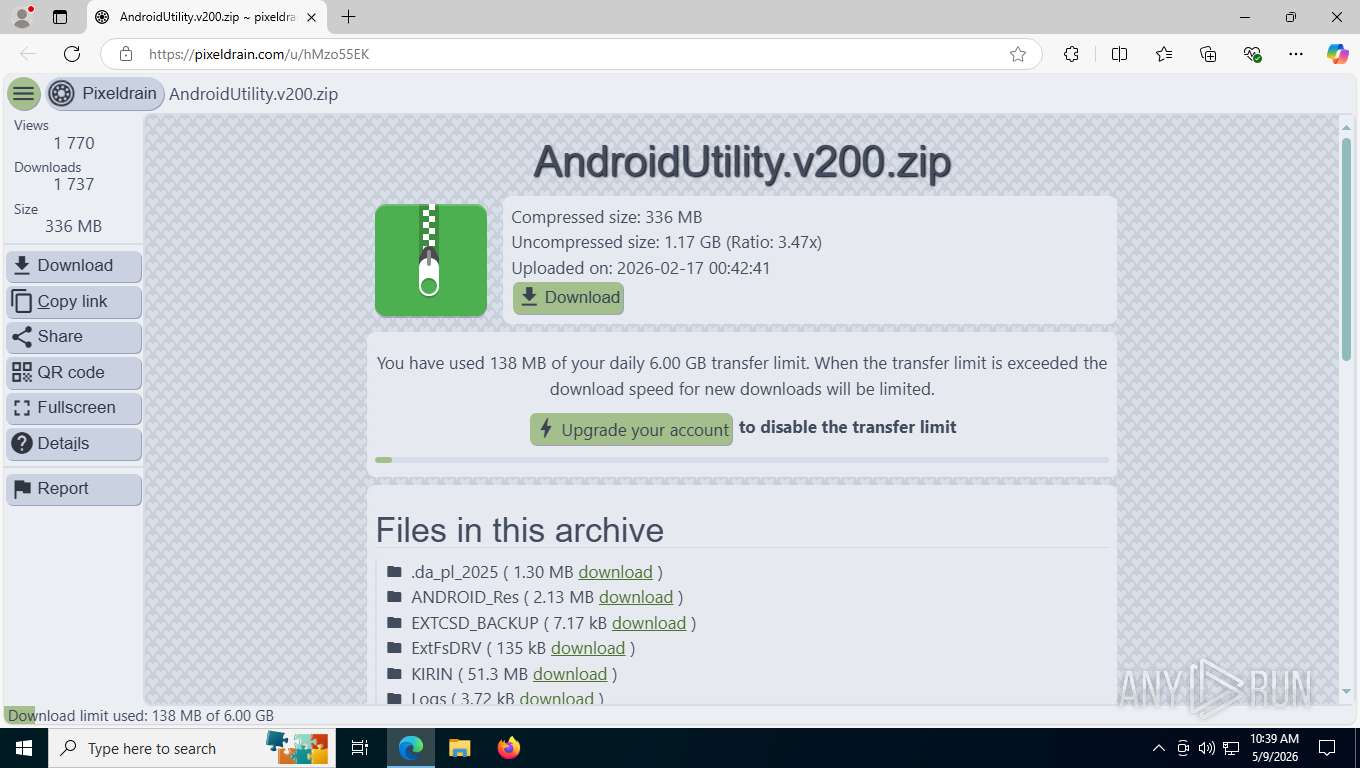
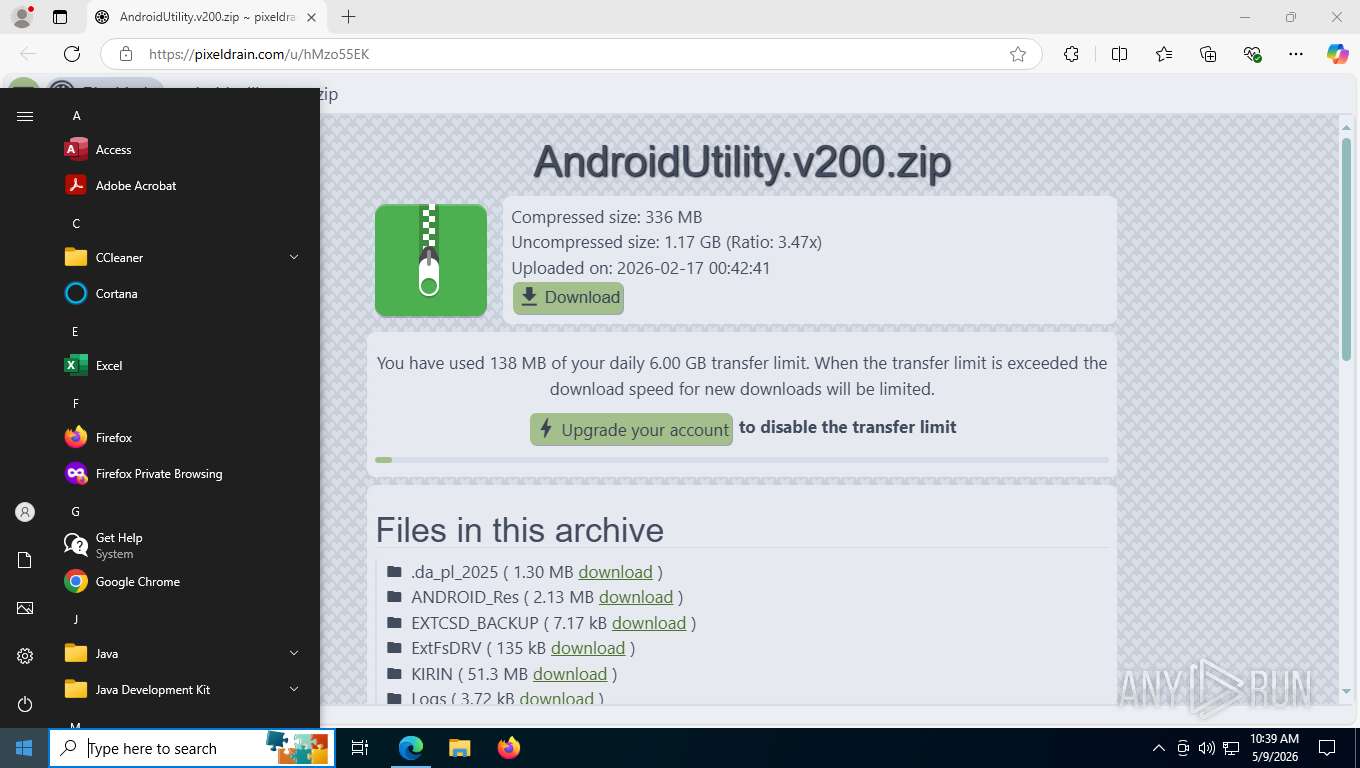
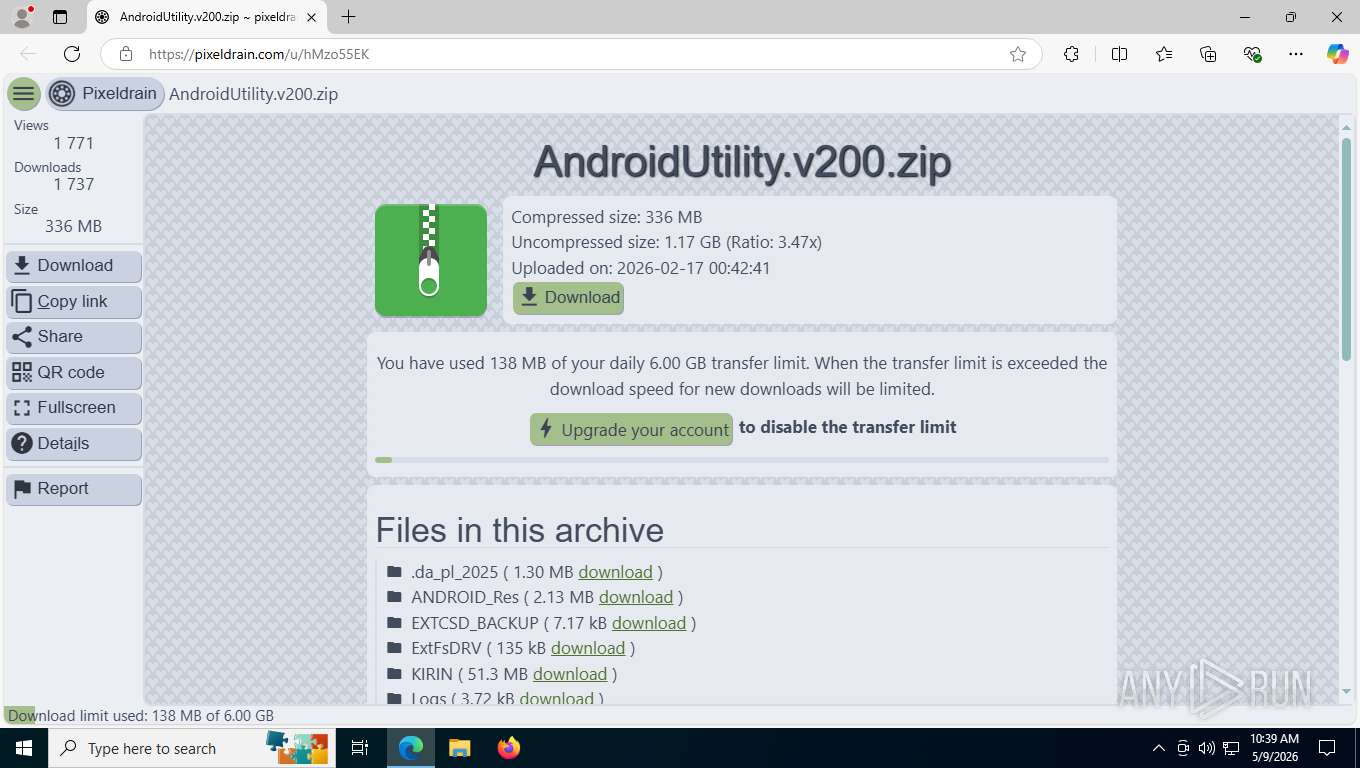
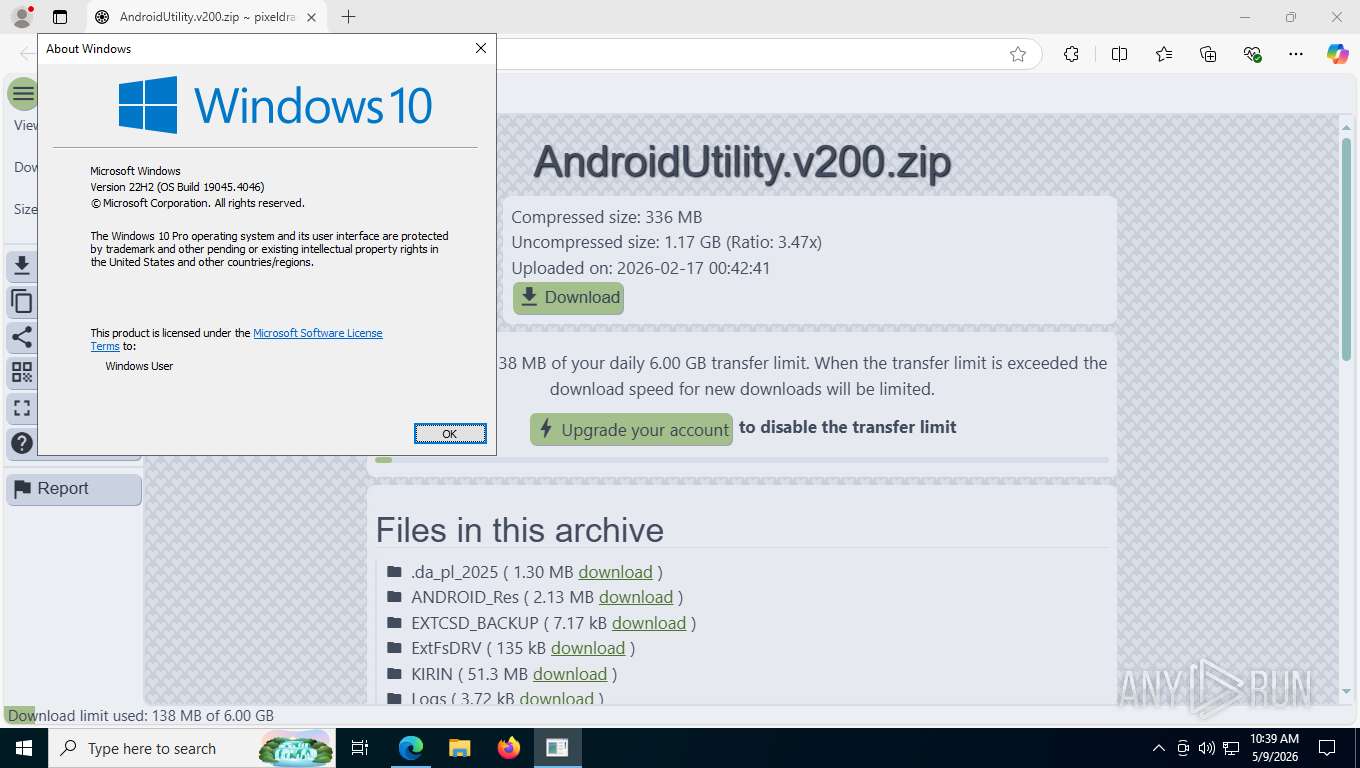
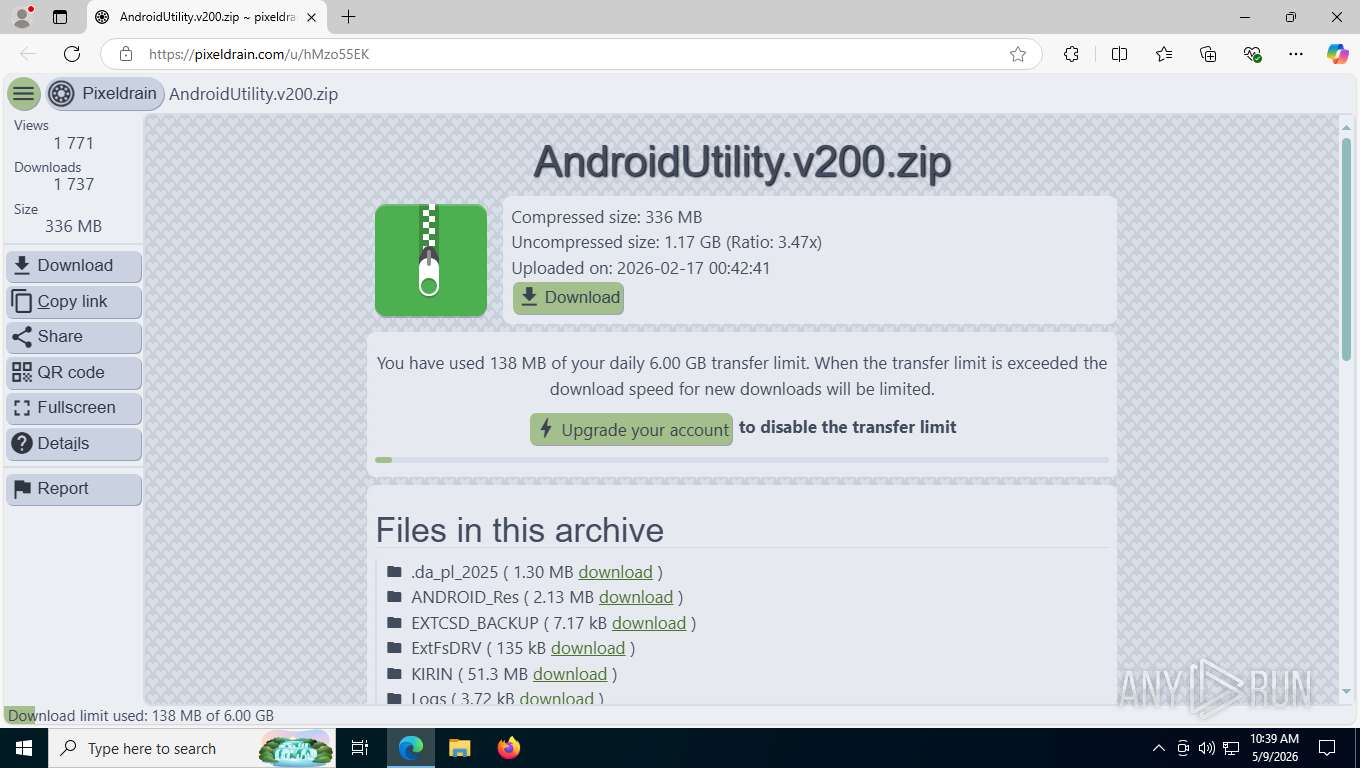
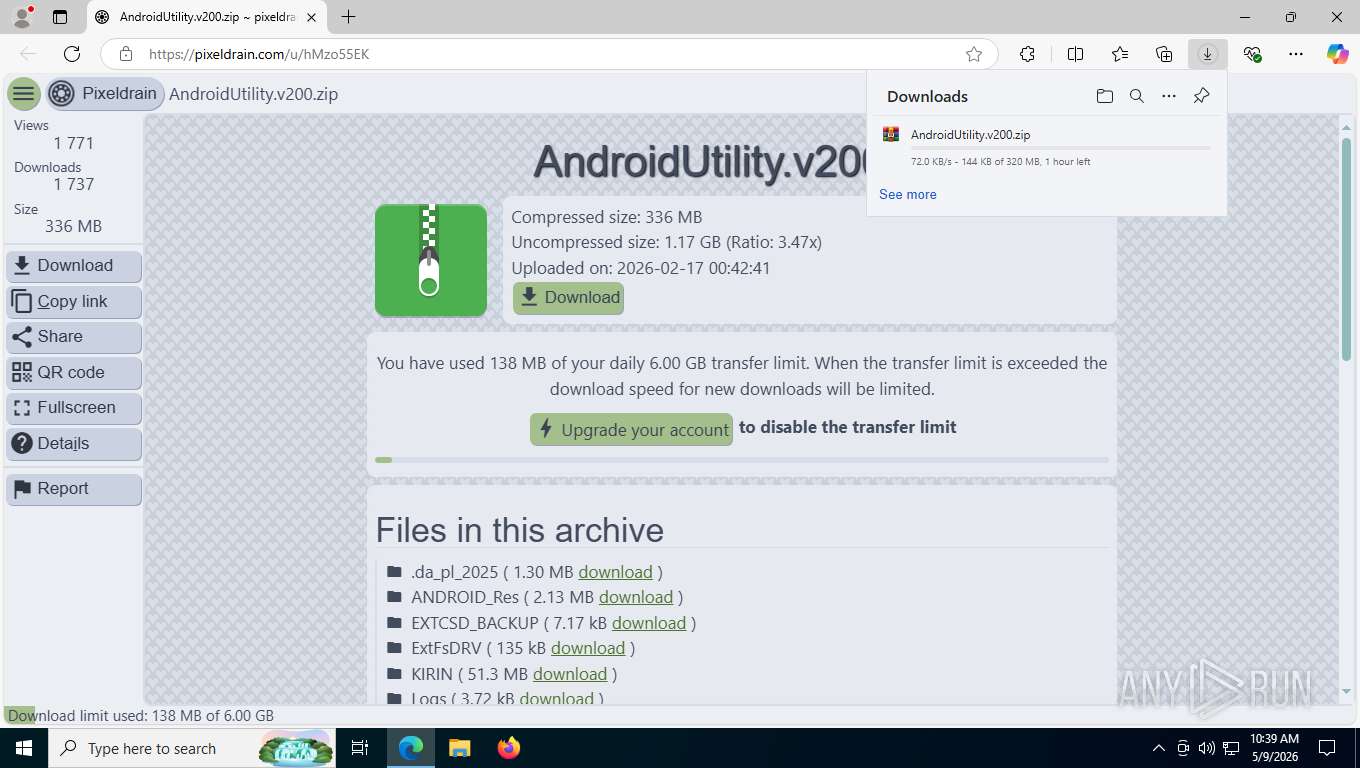
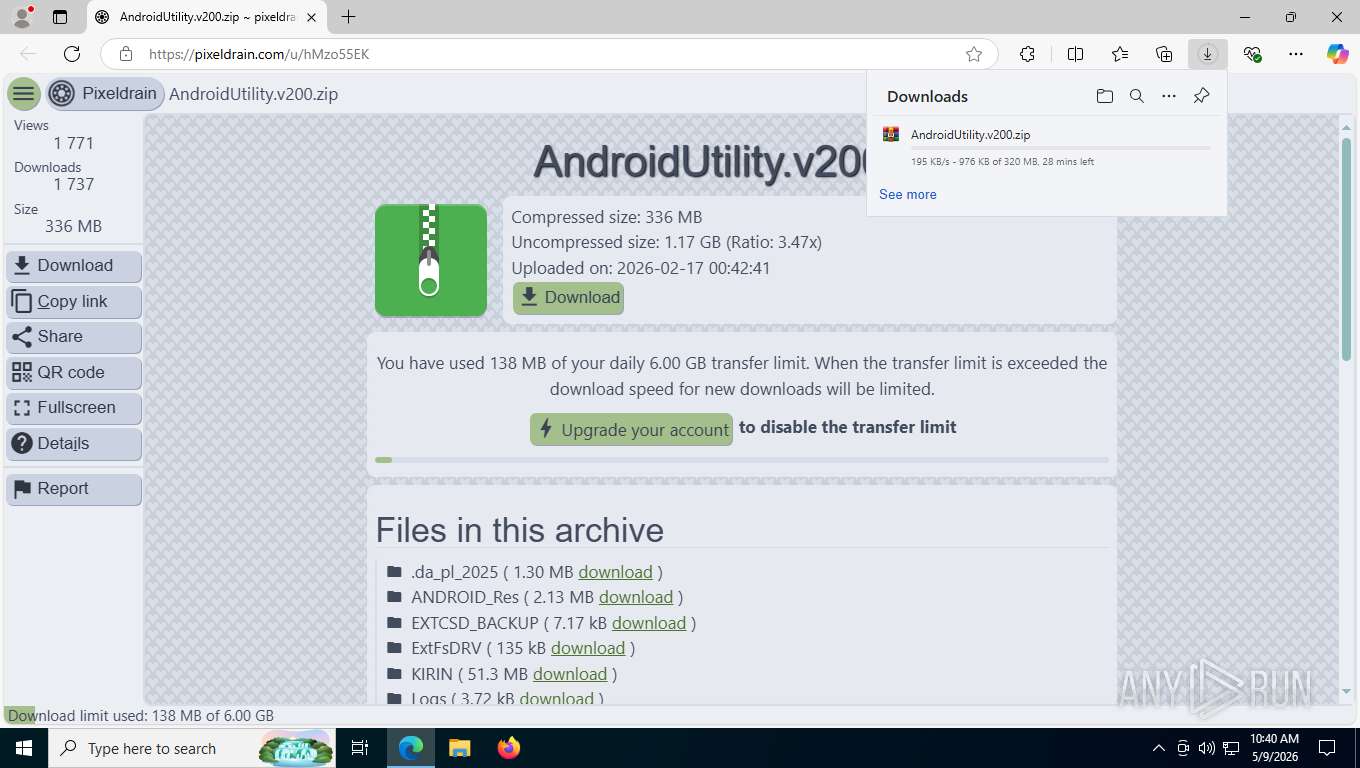
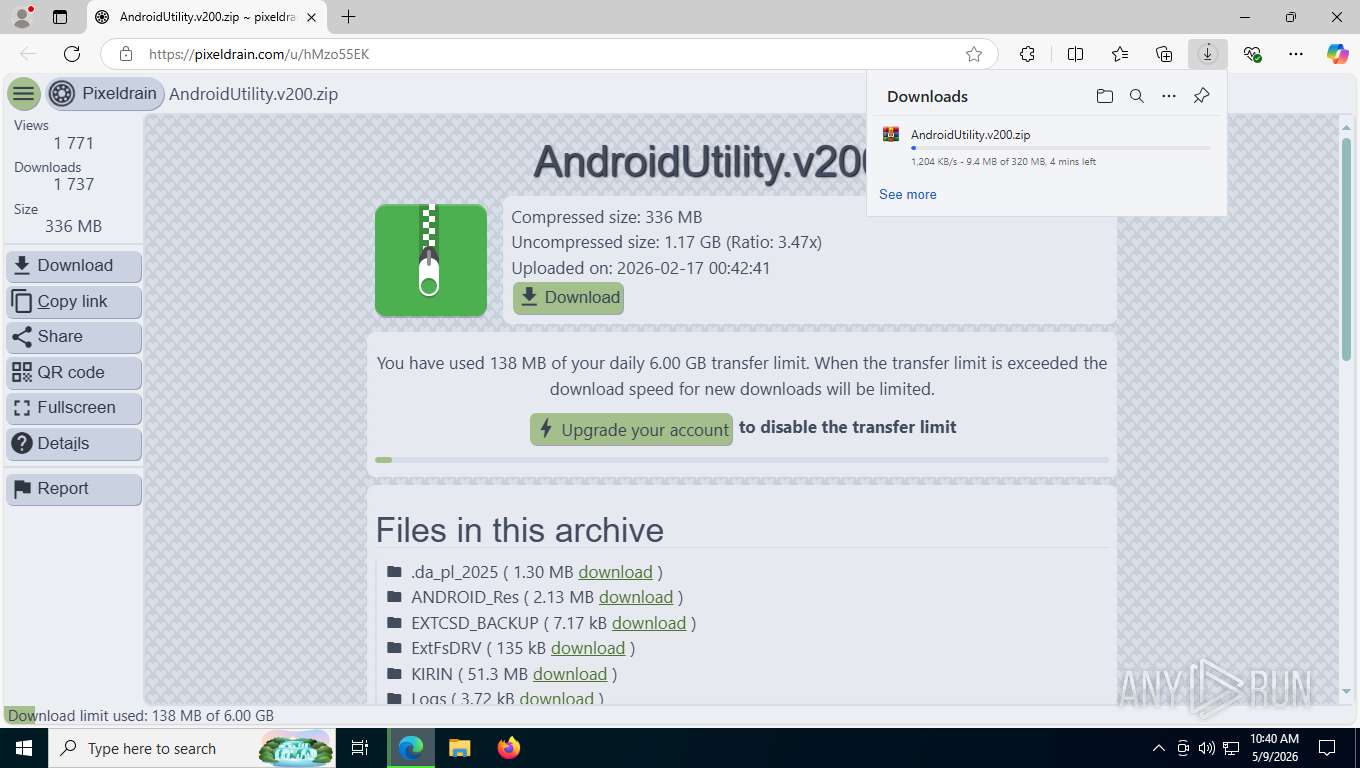
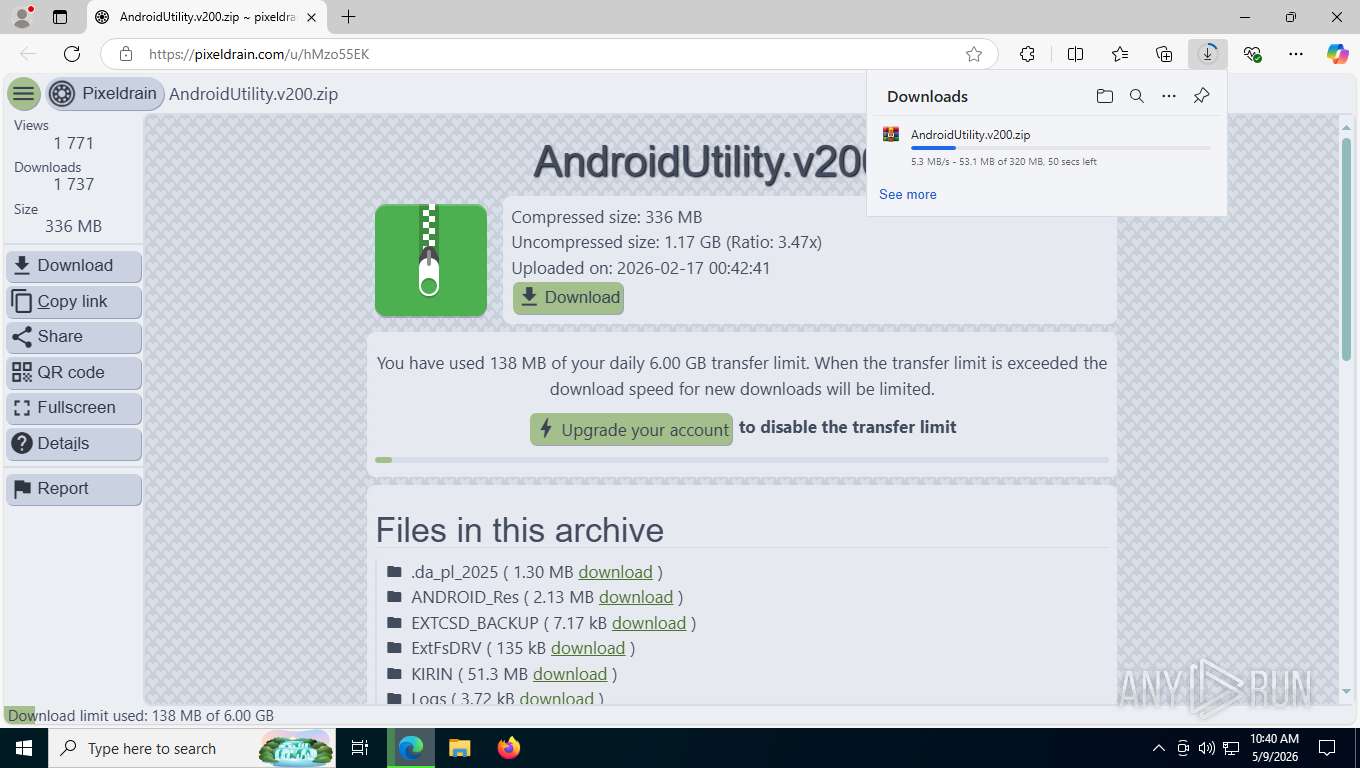
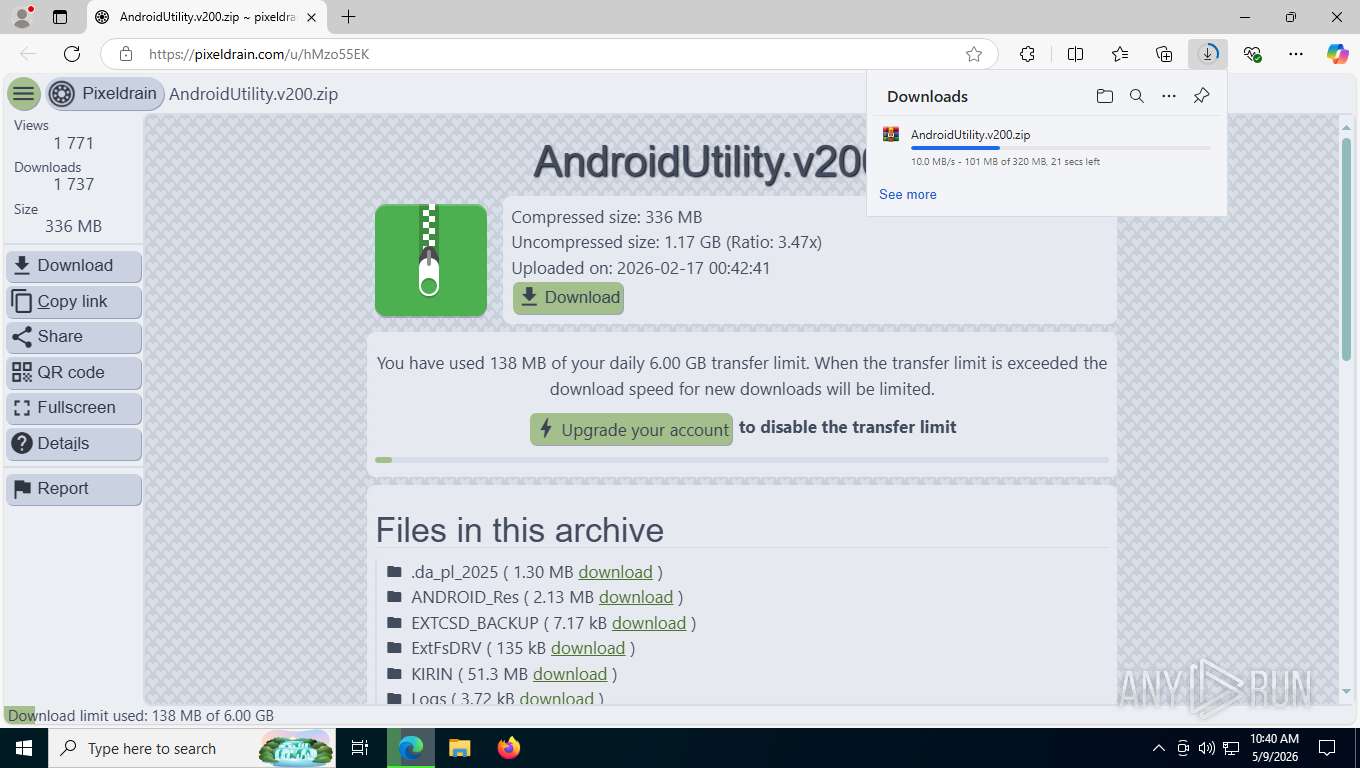
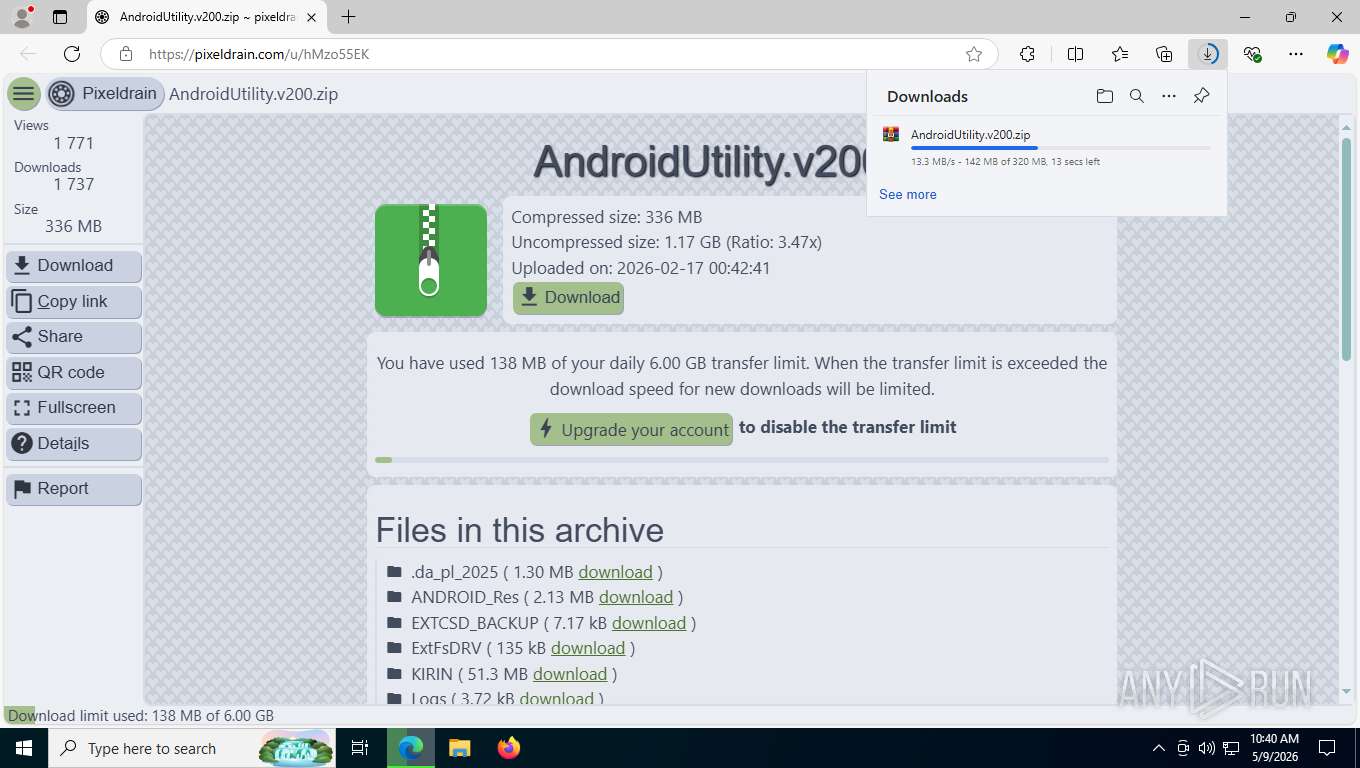
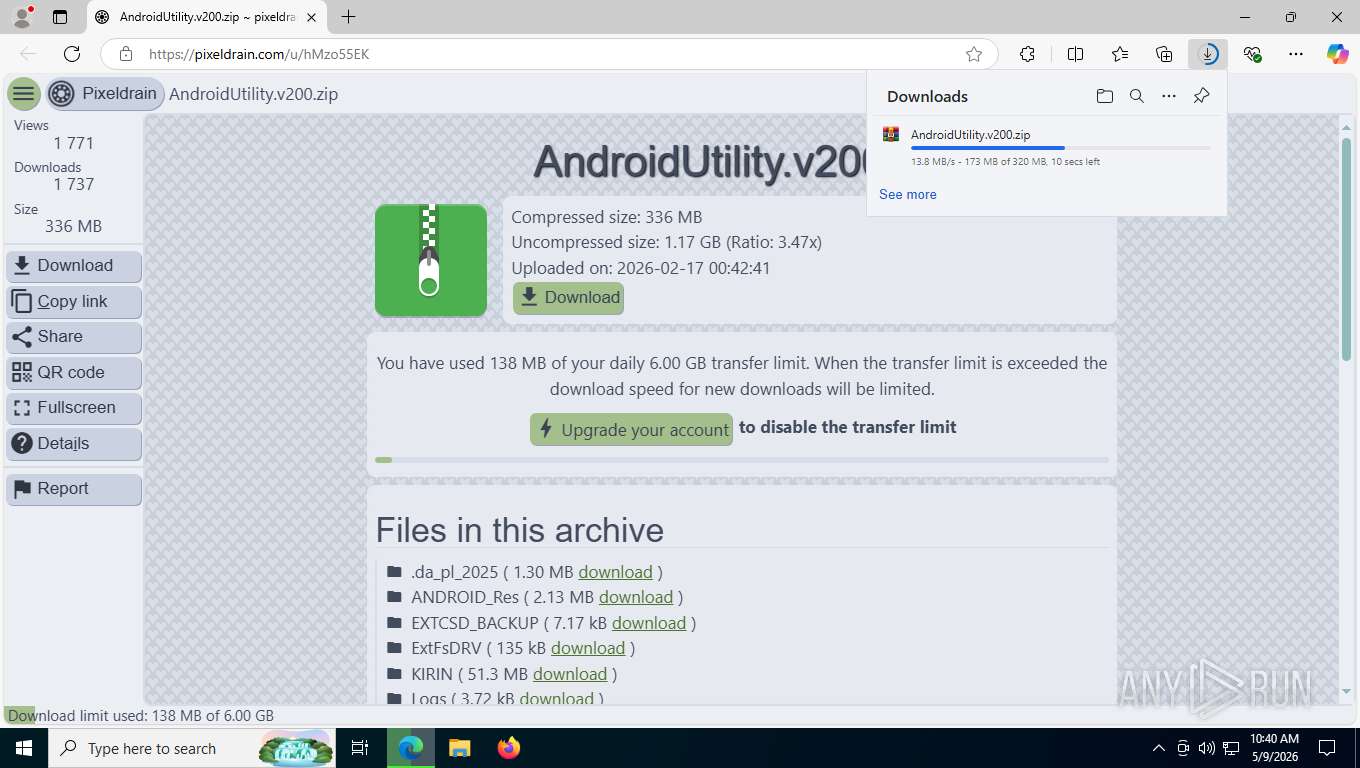
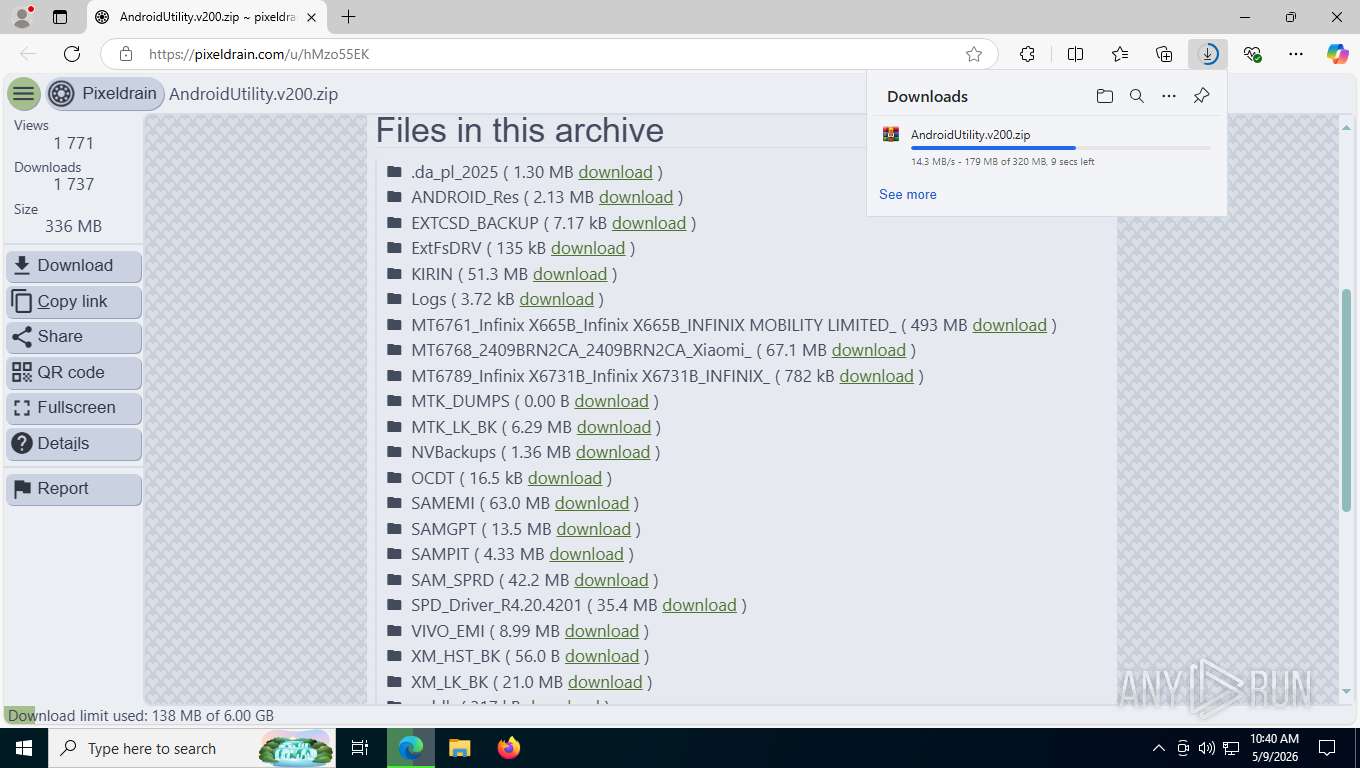
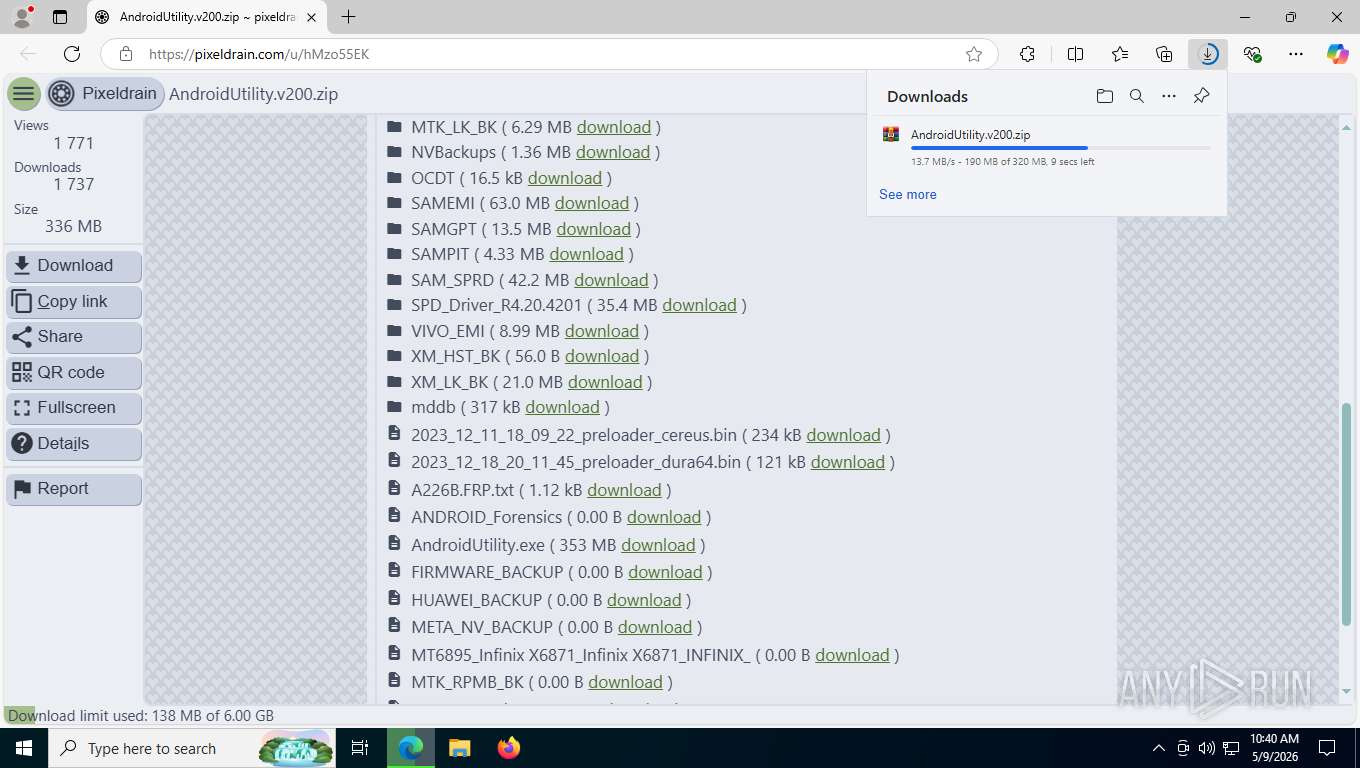
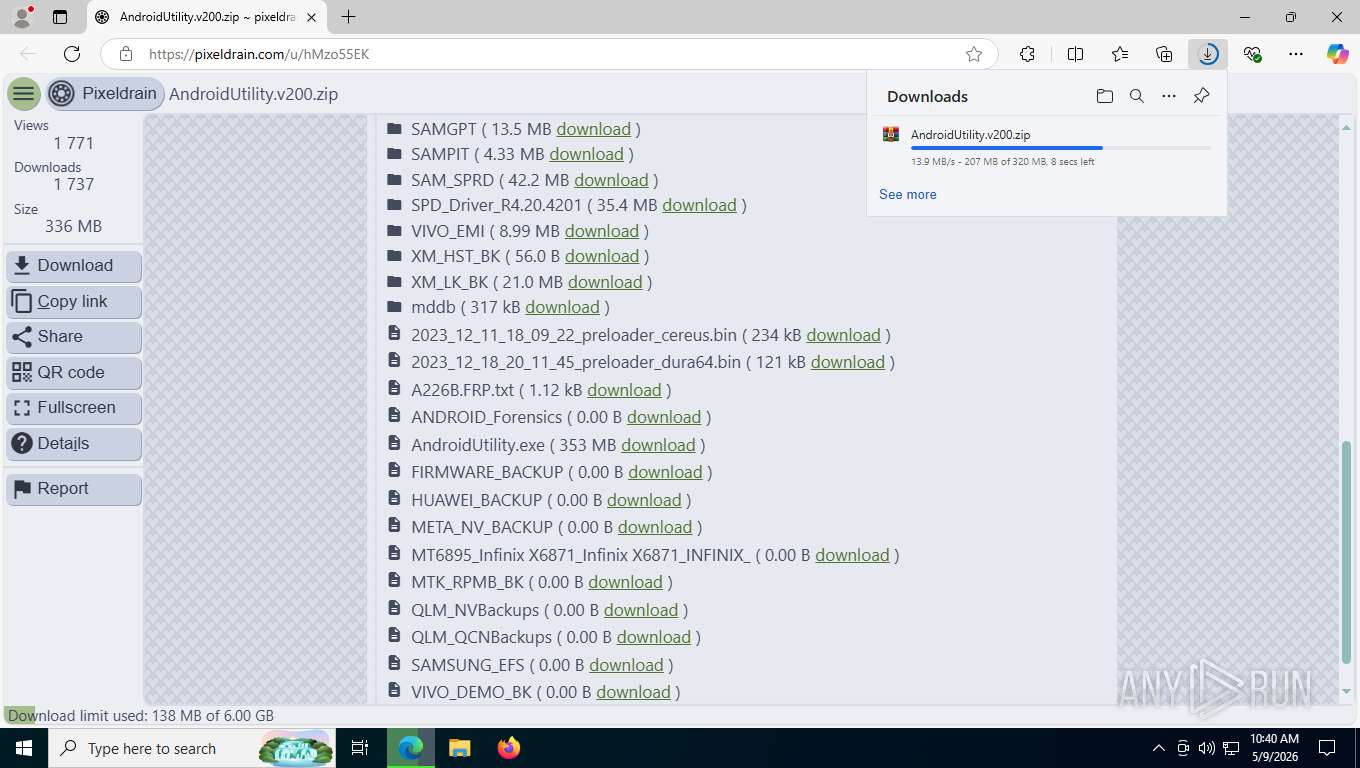
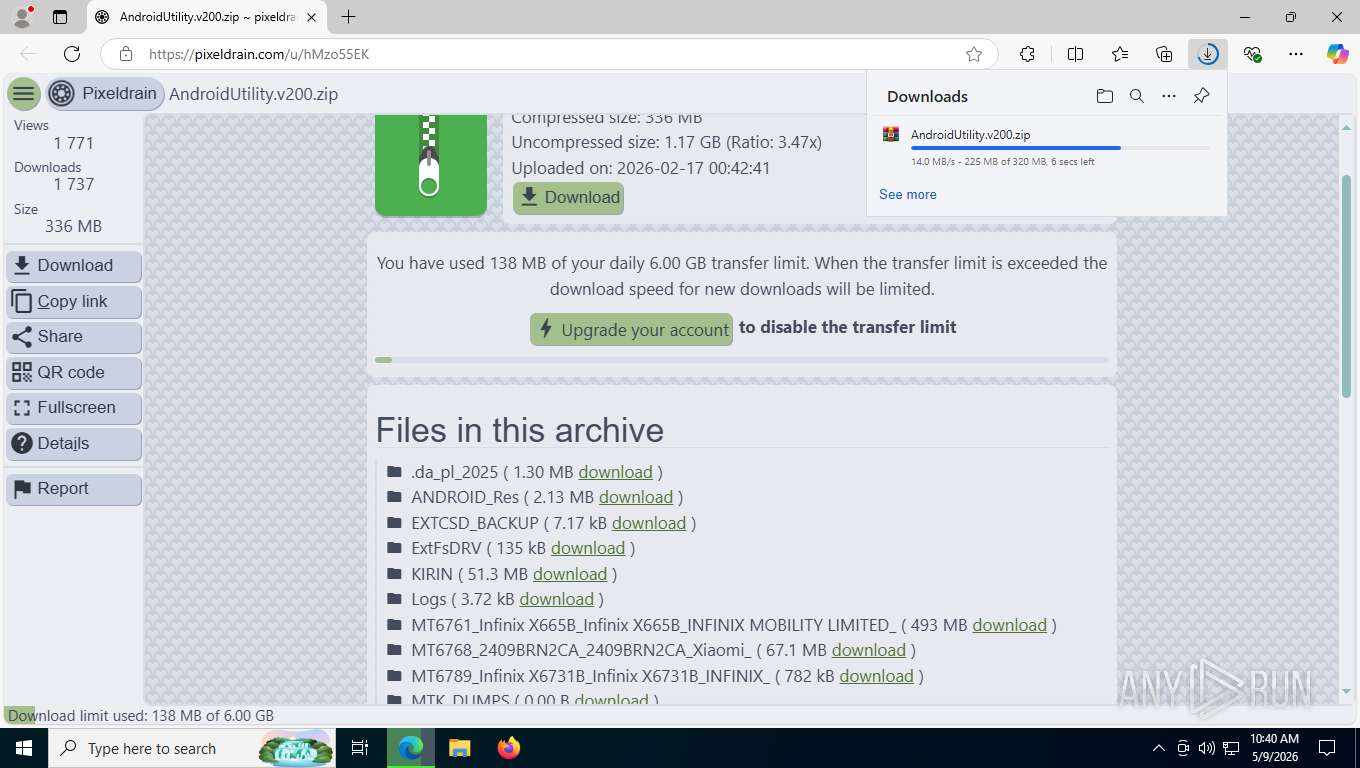
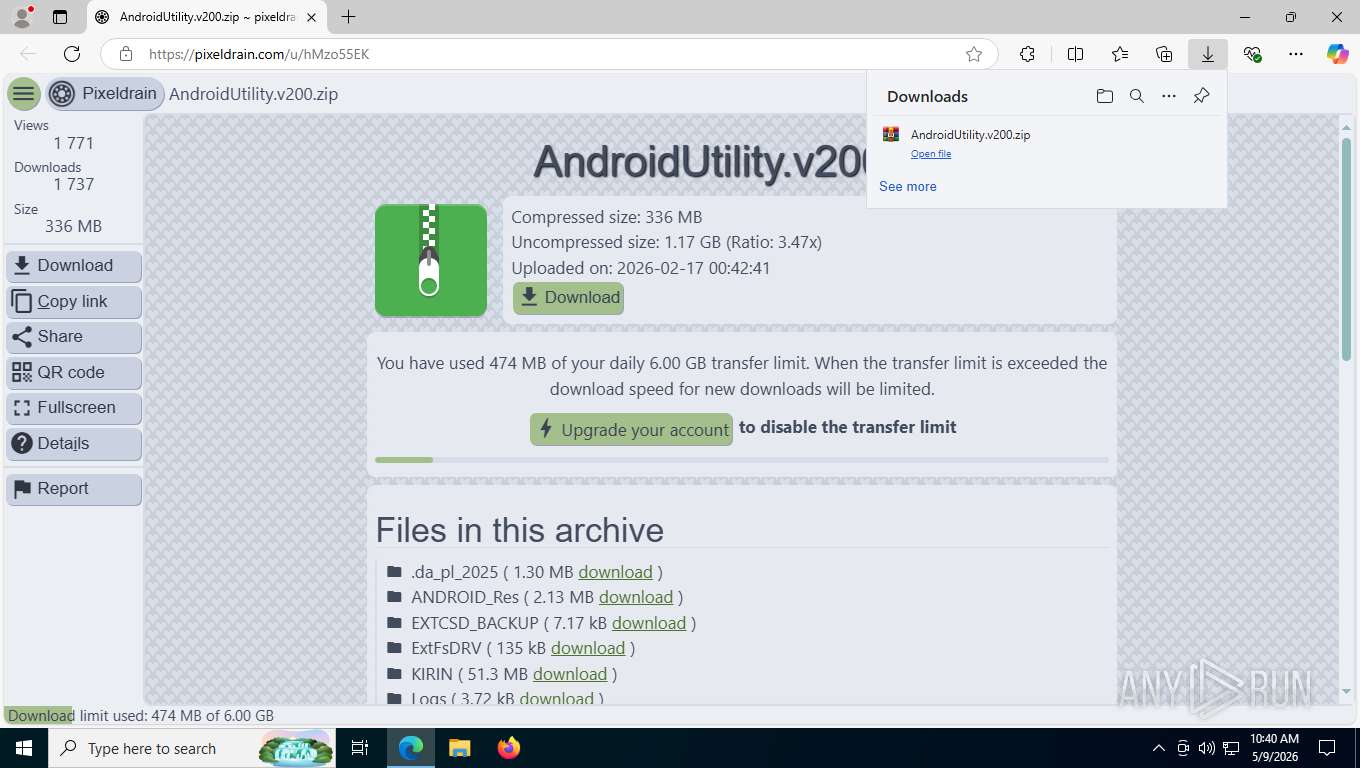
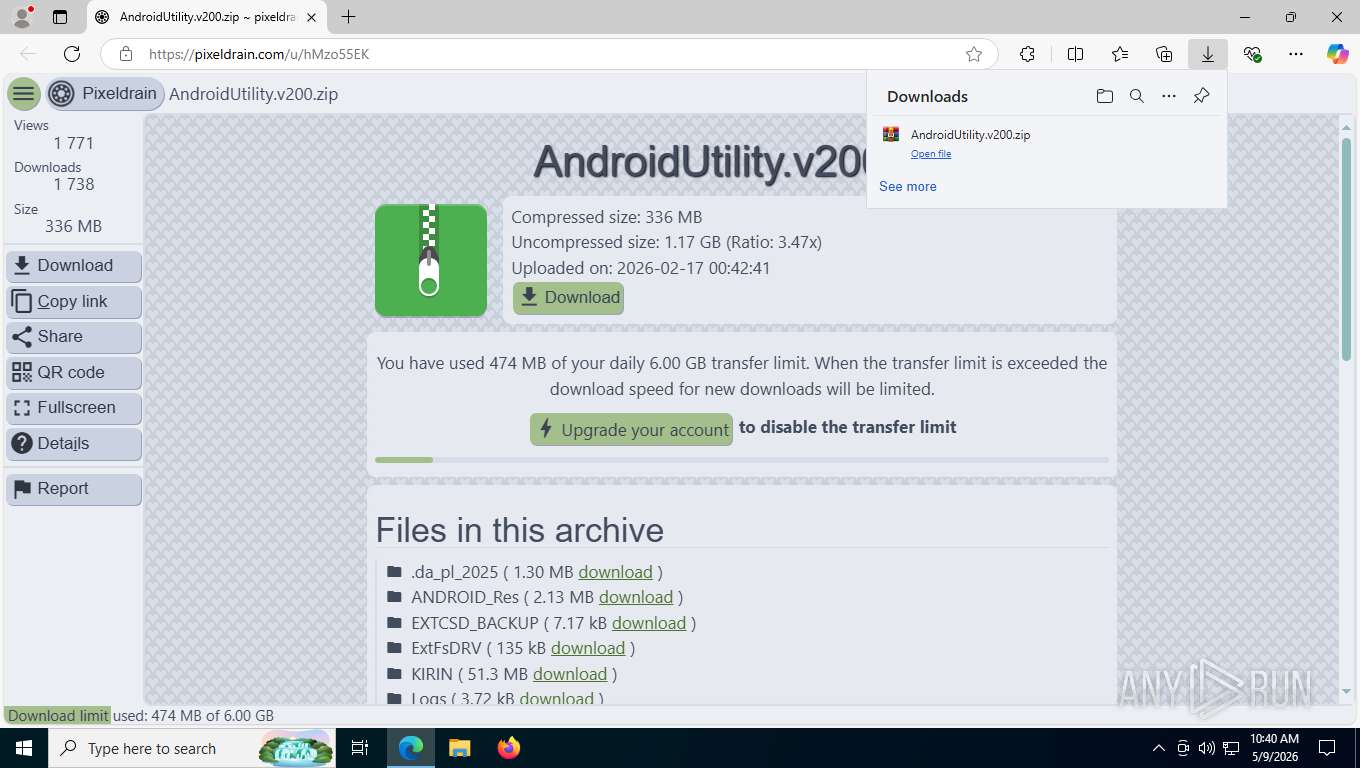
| URL: | https://pixeldrain.com/u/hMzo55EK |
| Full analysis: | https://app.any.run/tasks/ba3bfa8f-583a-4c05-9b05-cd92625b3de2 |
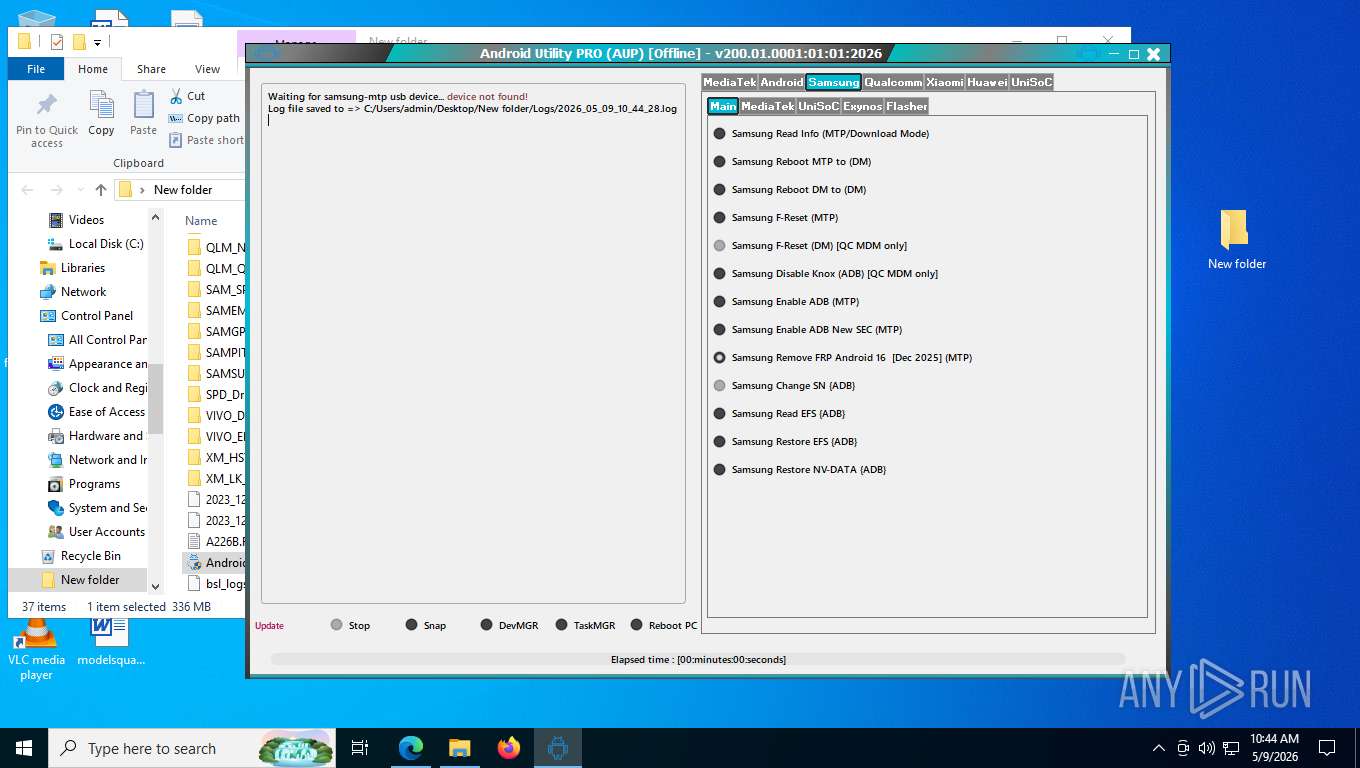
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2026, 14:39:31 |
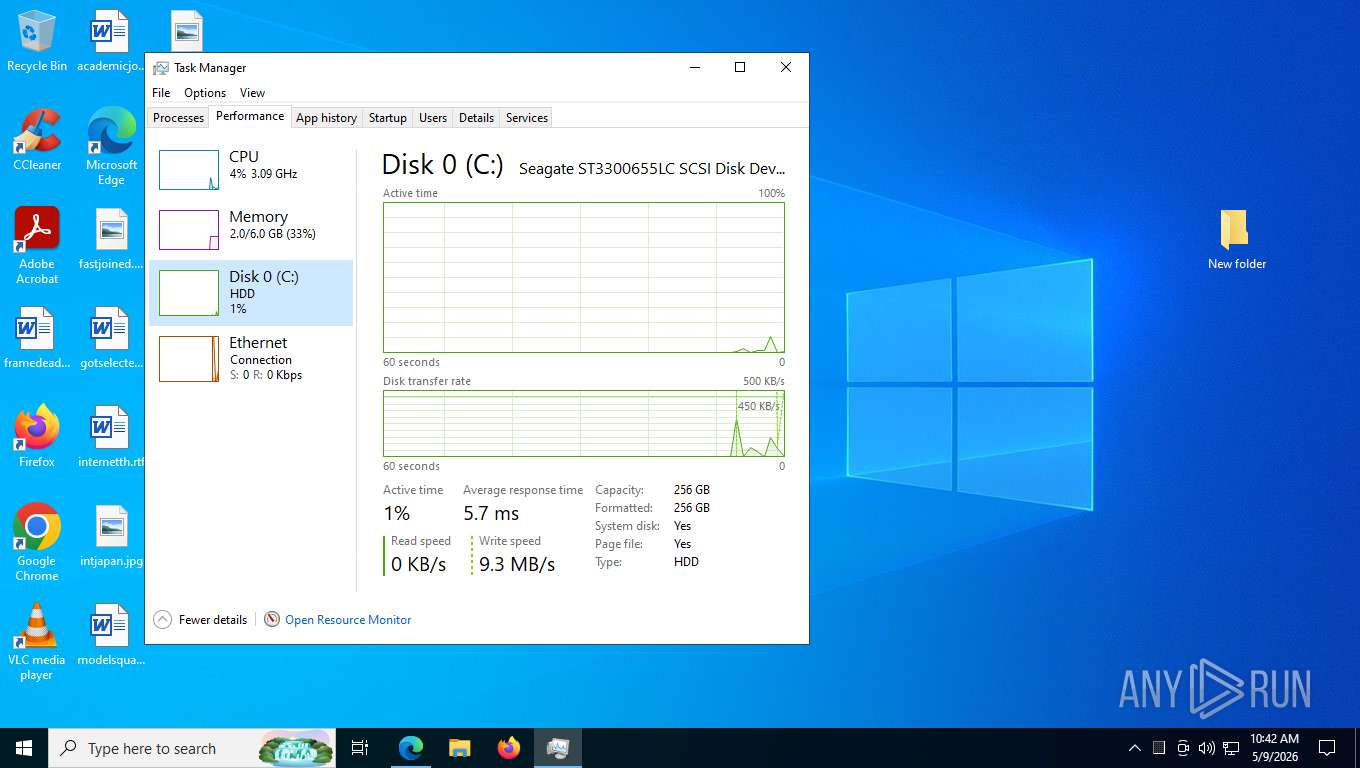
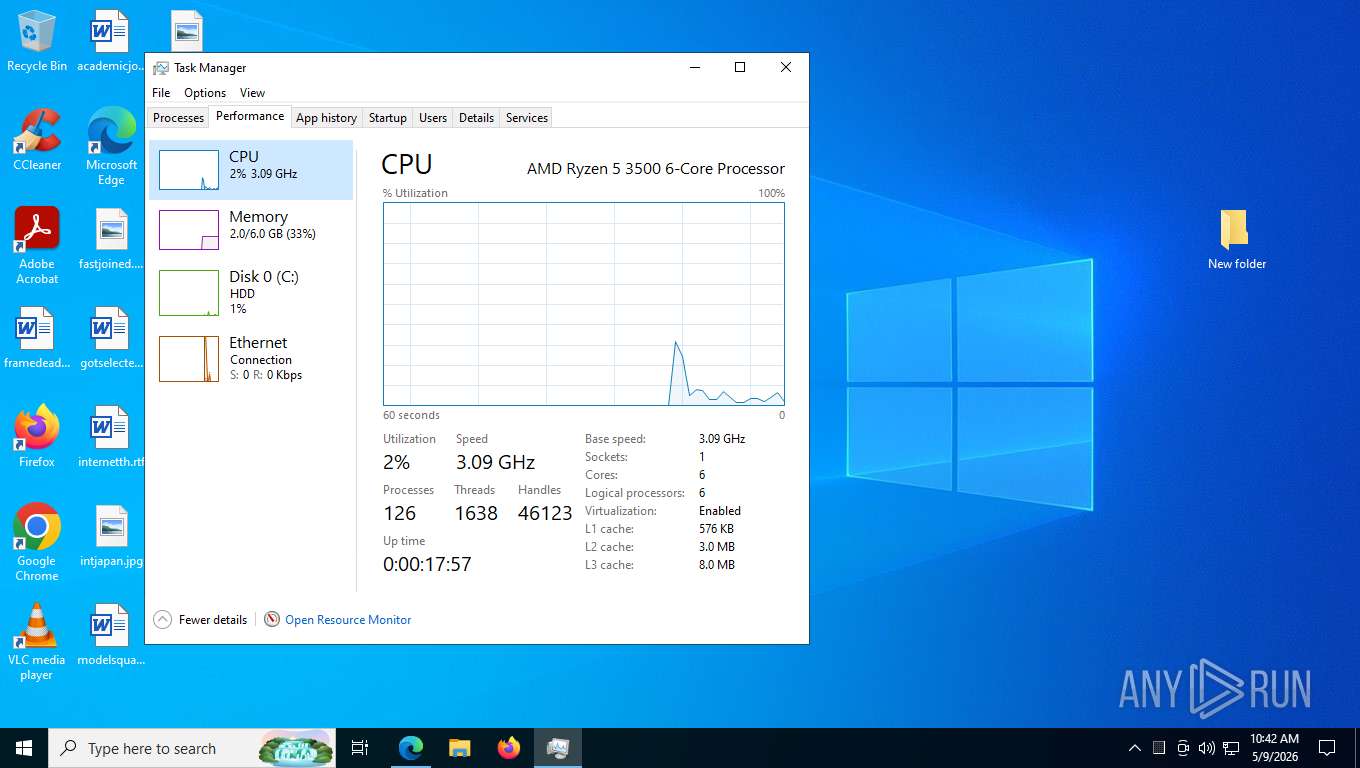
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 362518961FEE5A0450F062ADE42212DF |
| SHA1: | 017A2F745A6467C71EBB3D0ECB30F0C2BD3BEE15 |
| SHA256: | 8EA0268D0A73CE463387731D449ED8B6447F0E2739AD42B5D3EDF404760D9DA6 |
| SSDEEP: | 3:N8Icl/GKgrk:2IG/dgg |
MALICIOUS
No malicious indicators.SUSPICIOUS
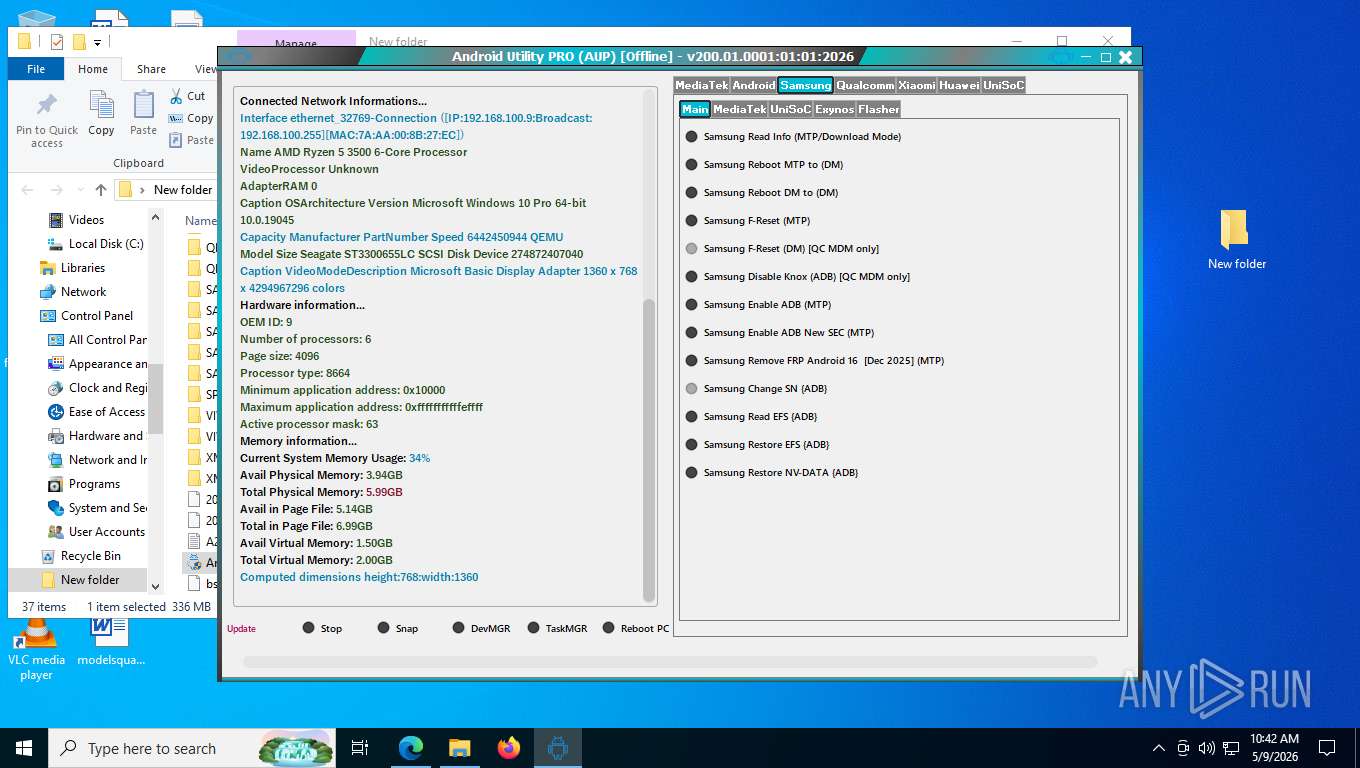
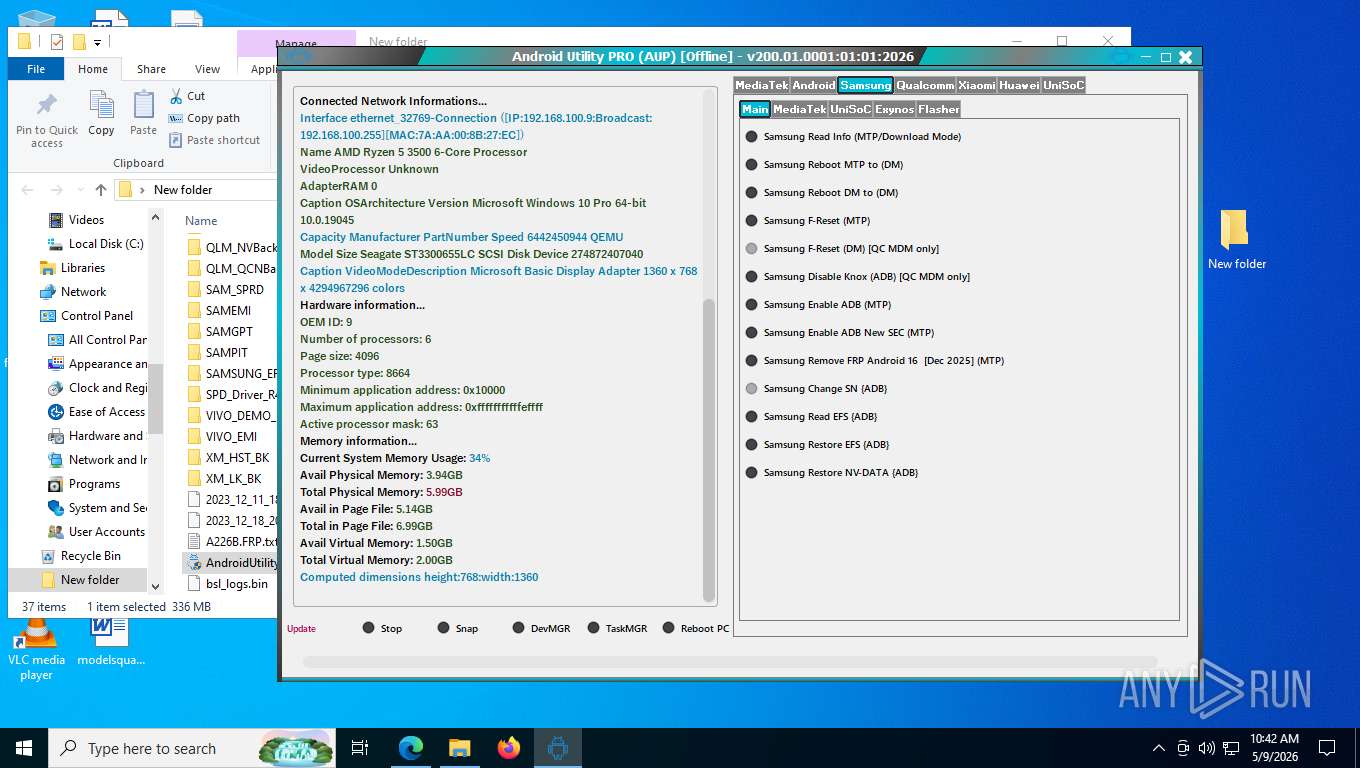
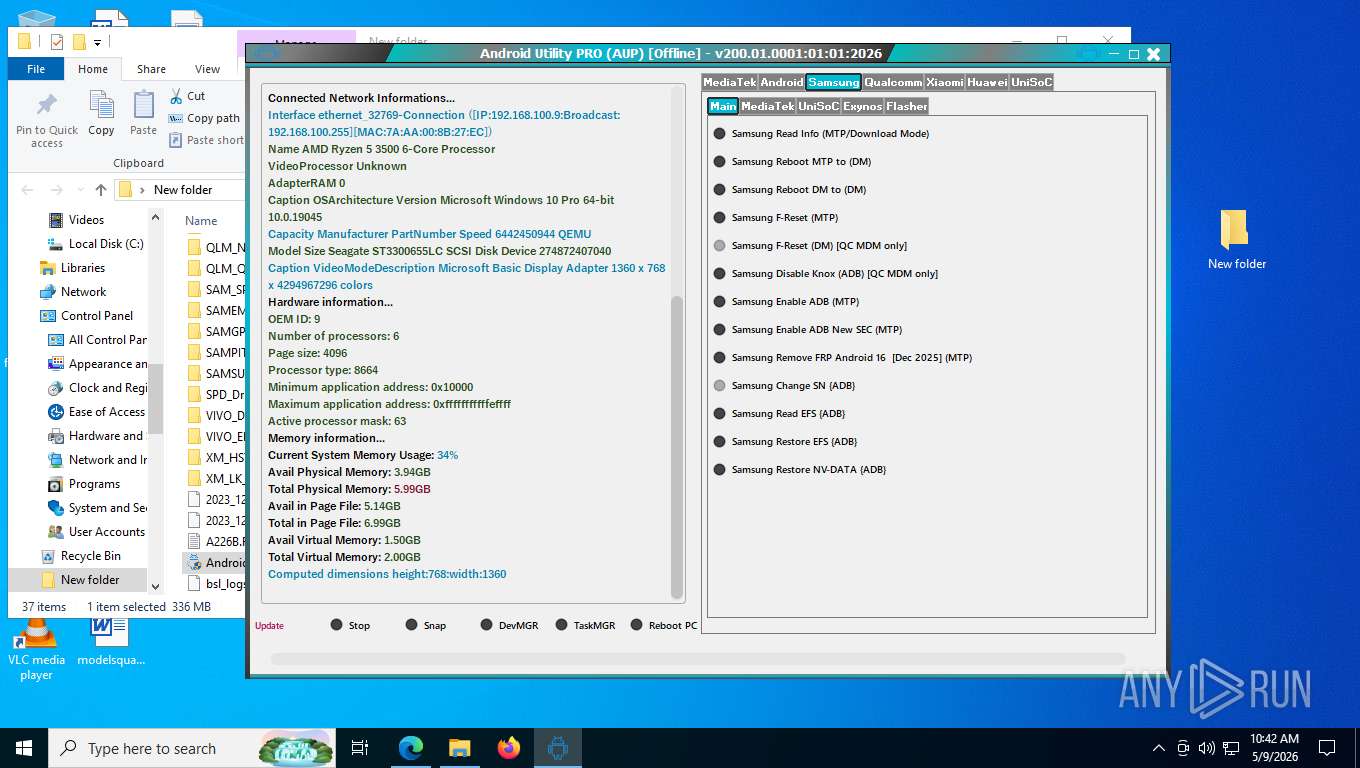
Reads the BIOS version
- AndroidUtility.exe (PID: 4172)
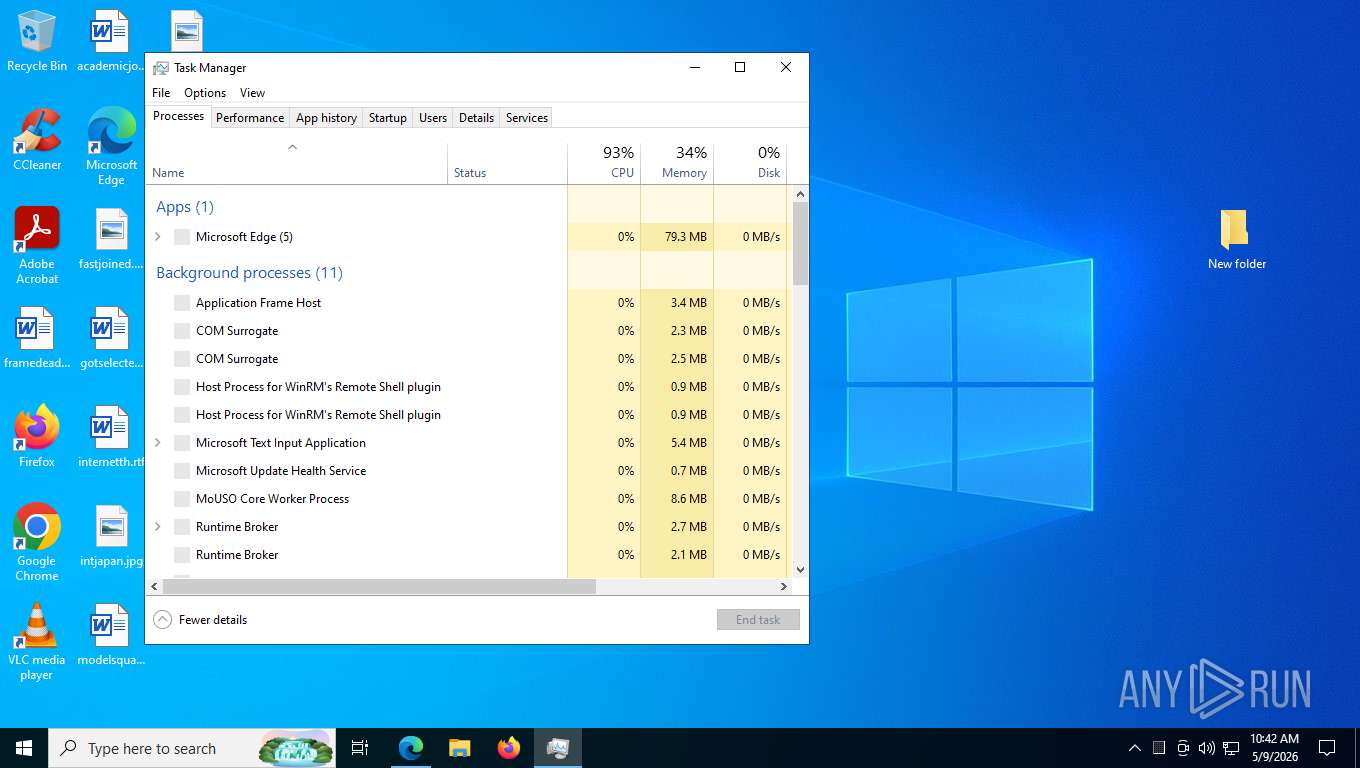
Uses WMIC.EXE to obtain CPU information
- AndroidUtility.exe (PID: 4172)
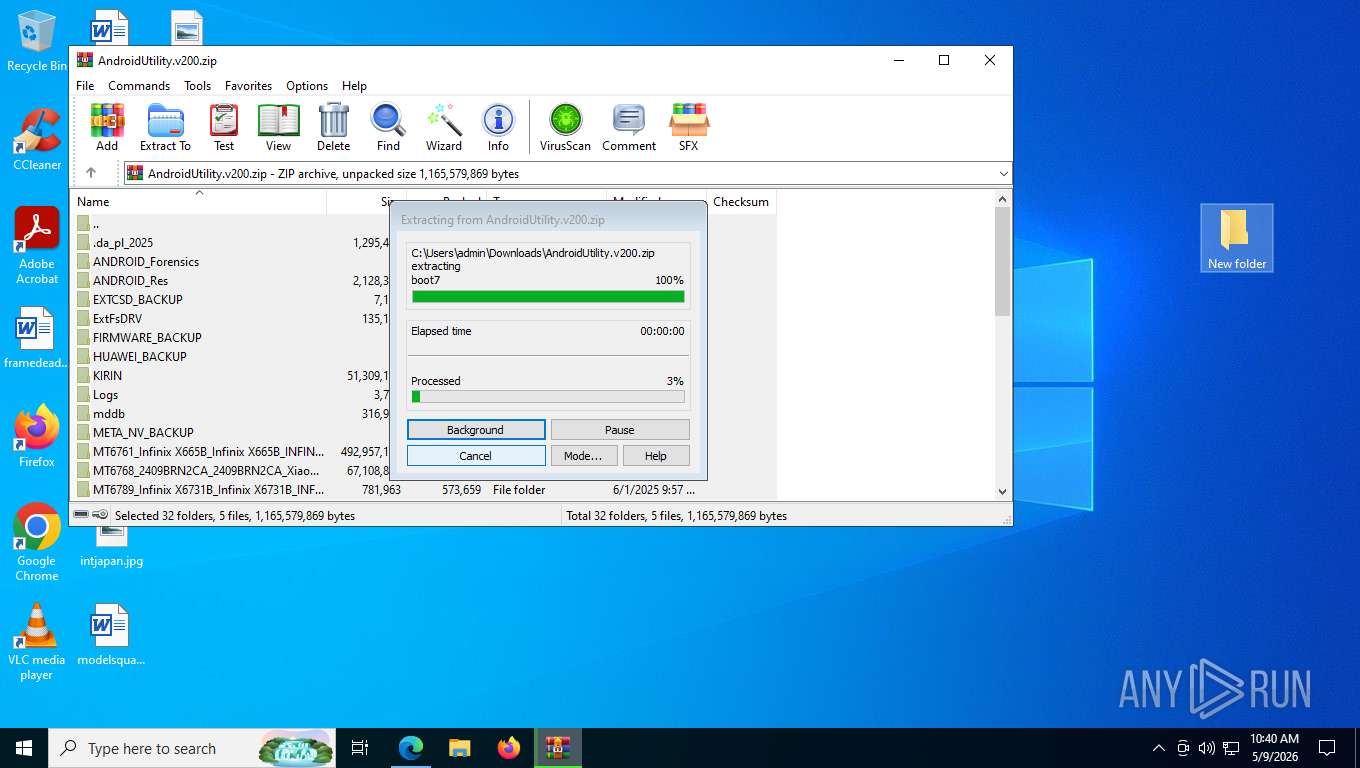
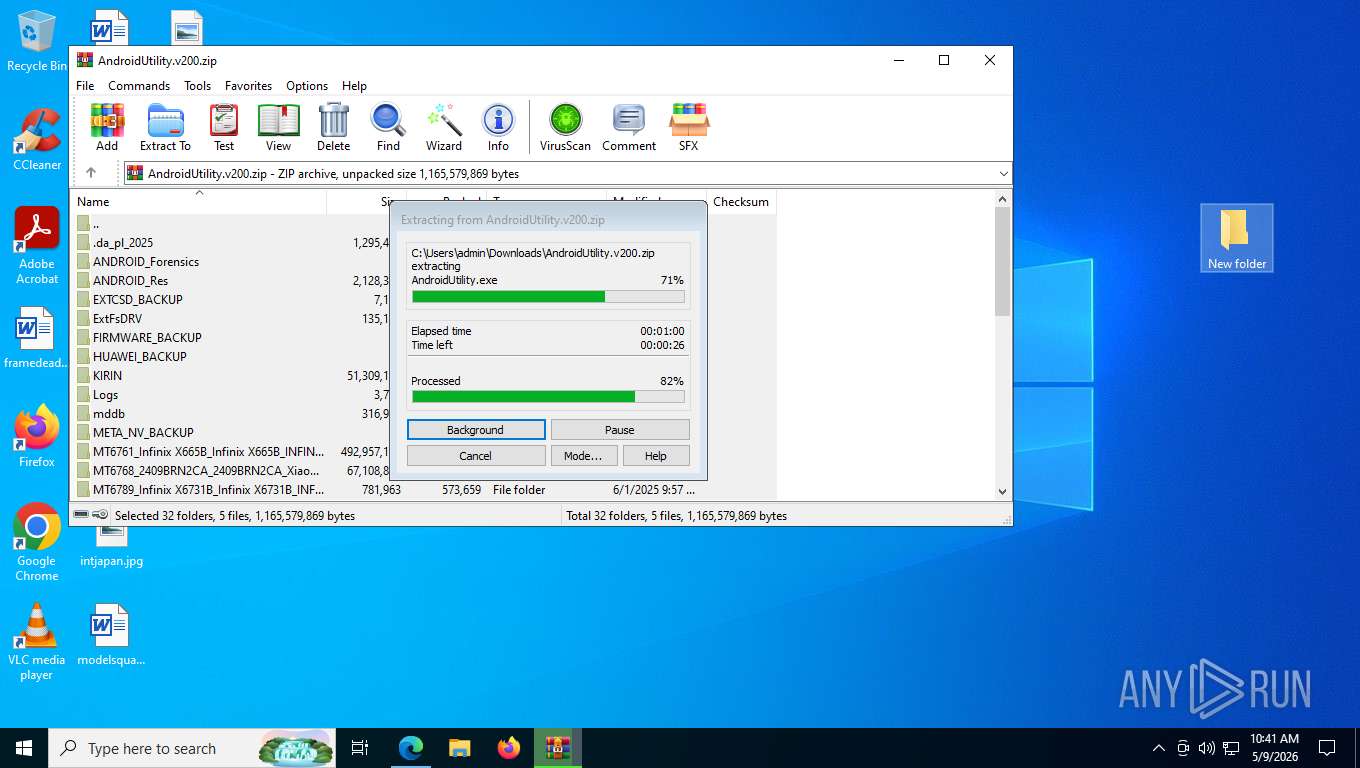
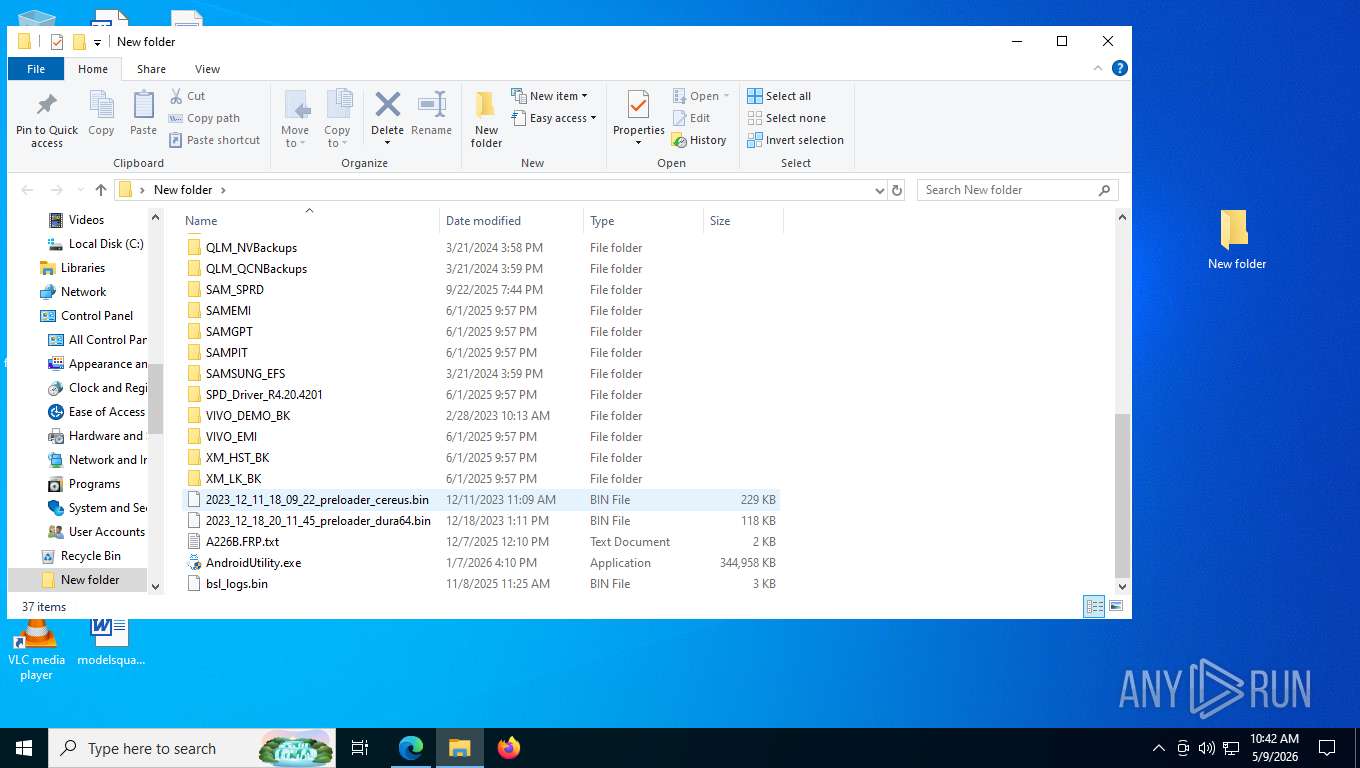
Executable content was dropped or overwritten
- AndroidUtility.exe (PID: 4172)
Uses WMIC.EXE to obtain operating system information
- AndroidUtility.exe (PID: 4172)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 8084)
Uses WMIC.EXE to obtain memory chip information
- AndroidUtility.exe (PID: 4172)
Uses WMIC.EXE to obtain physical disk drive information
- AndroidUtility.exe (PID: 4172)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 3168)
Uses WMIC.EXE to obtain a list of video controllers
- AndroidUtility.exe (PID: 4172)
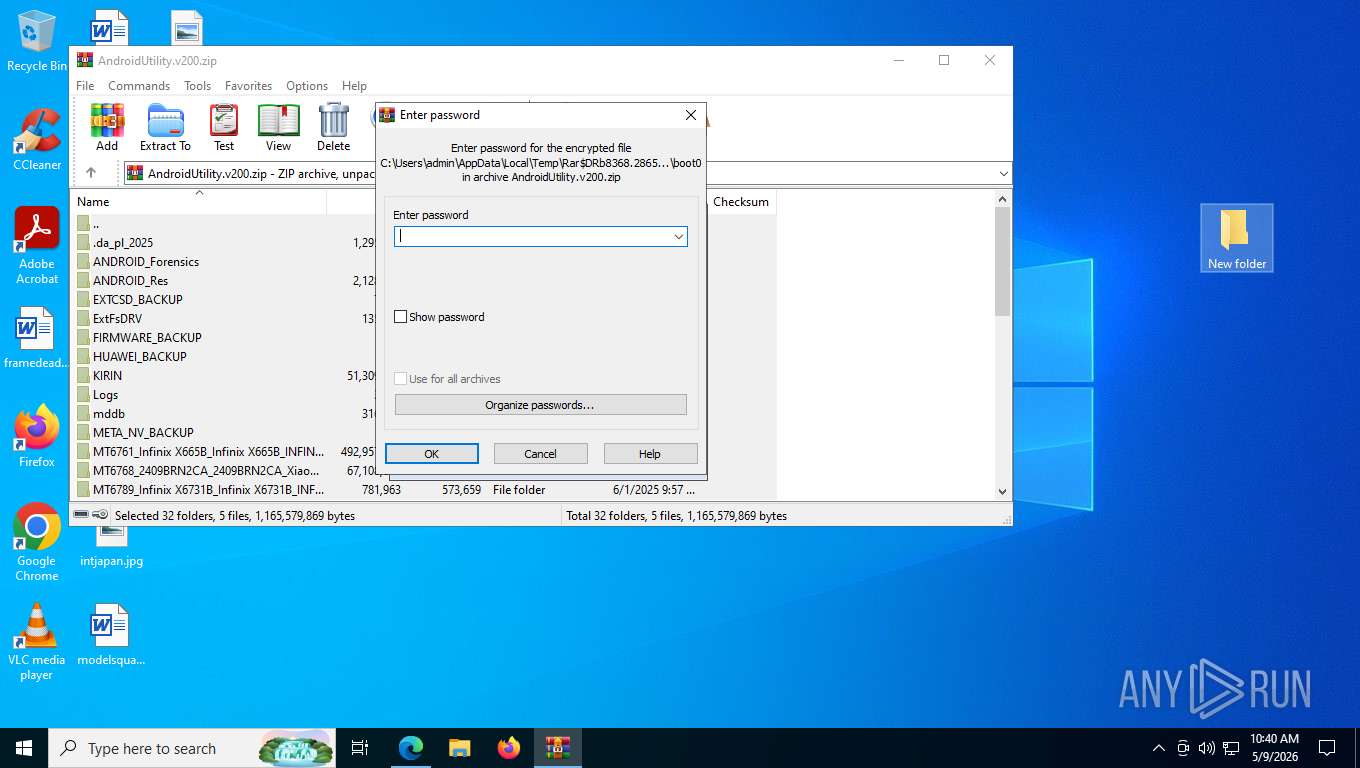
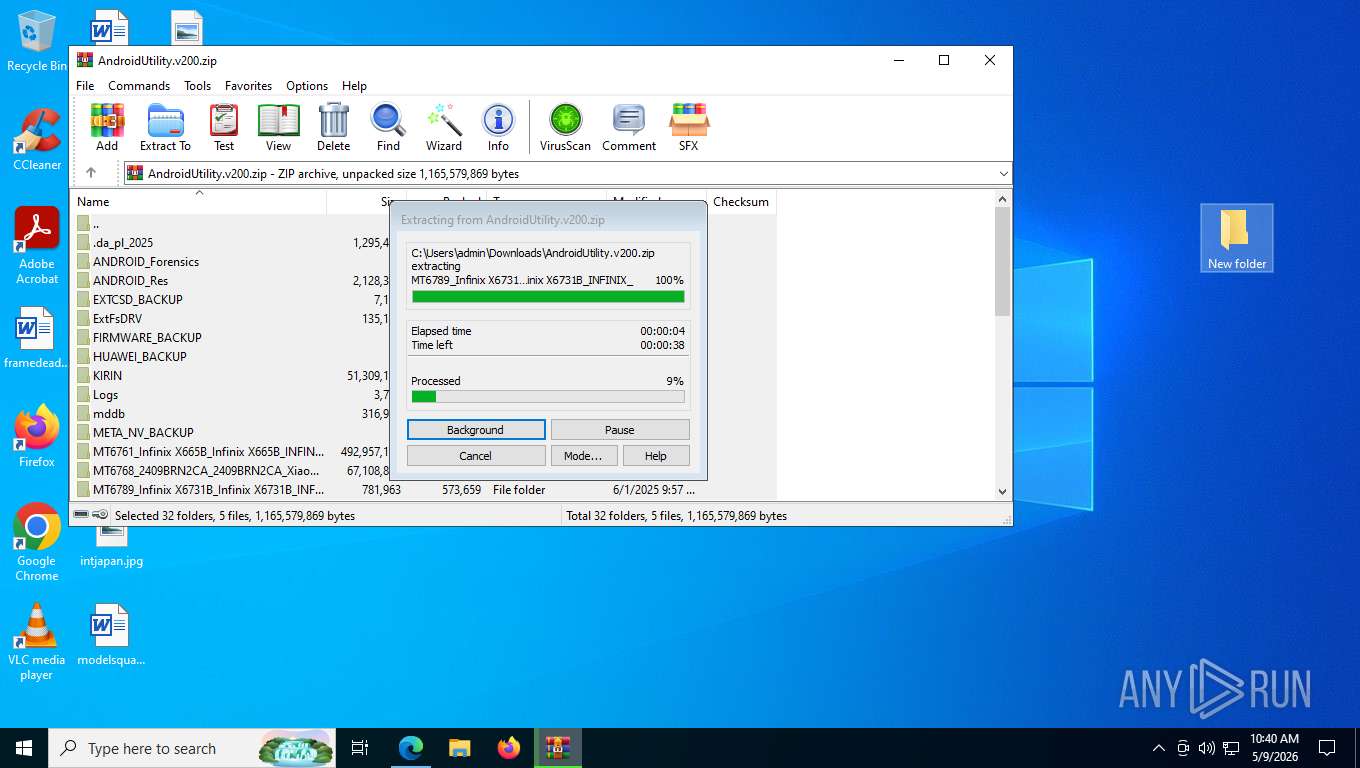
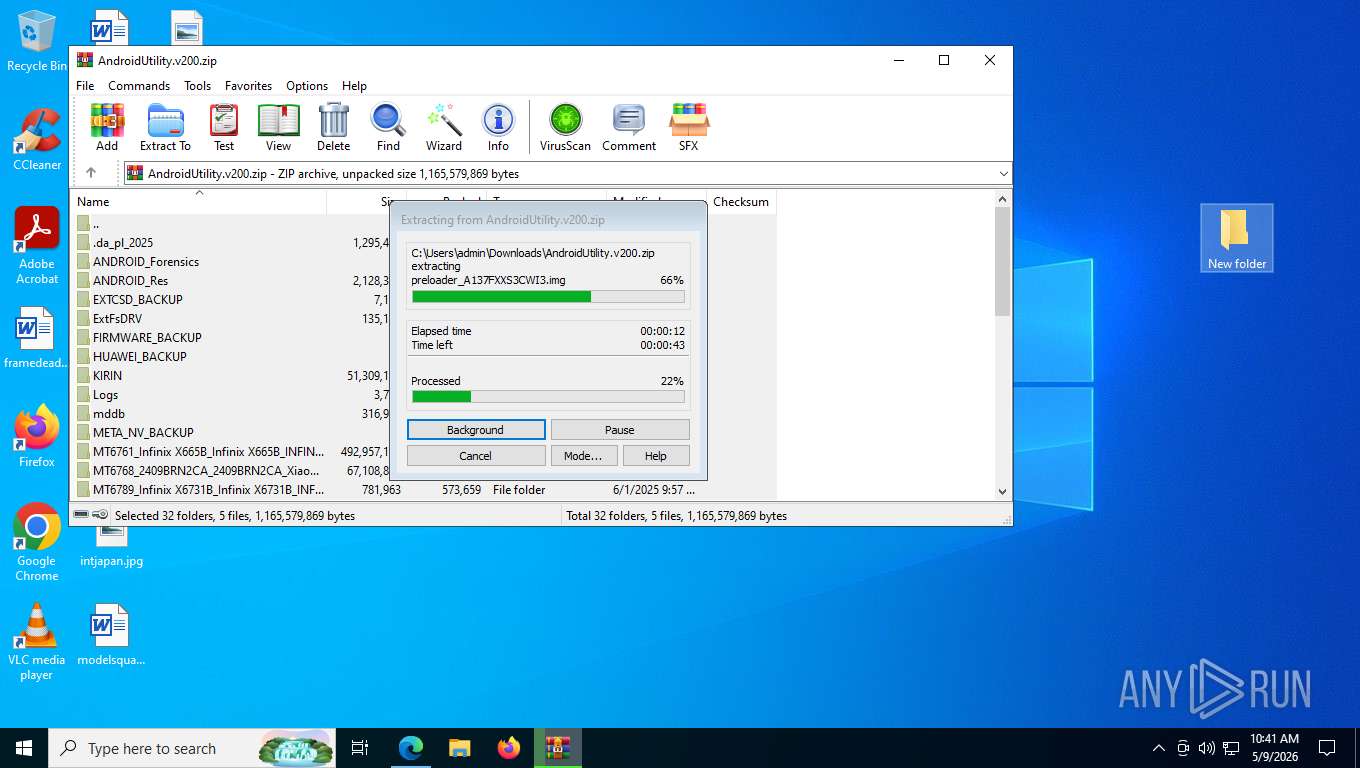
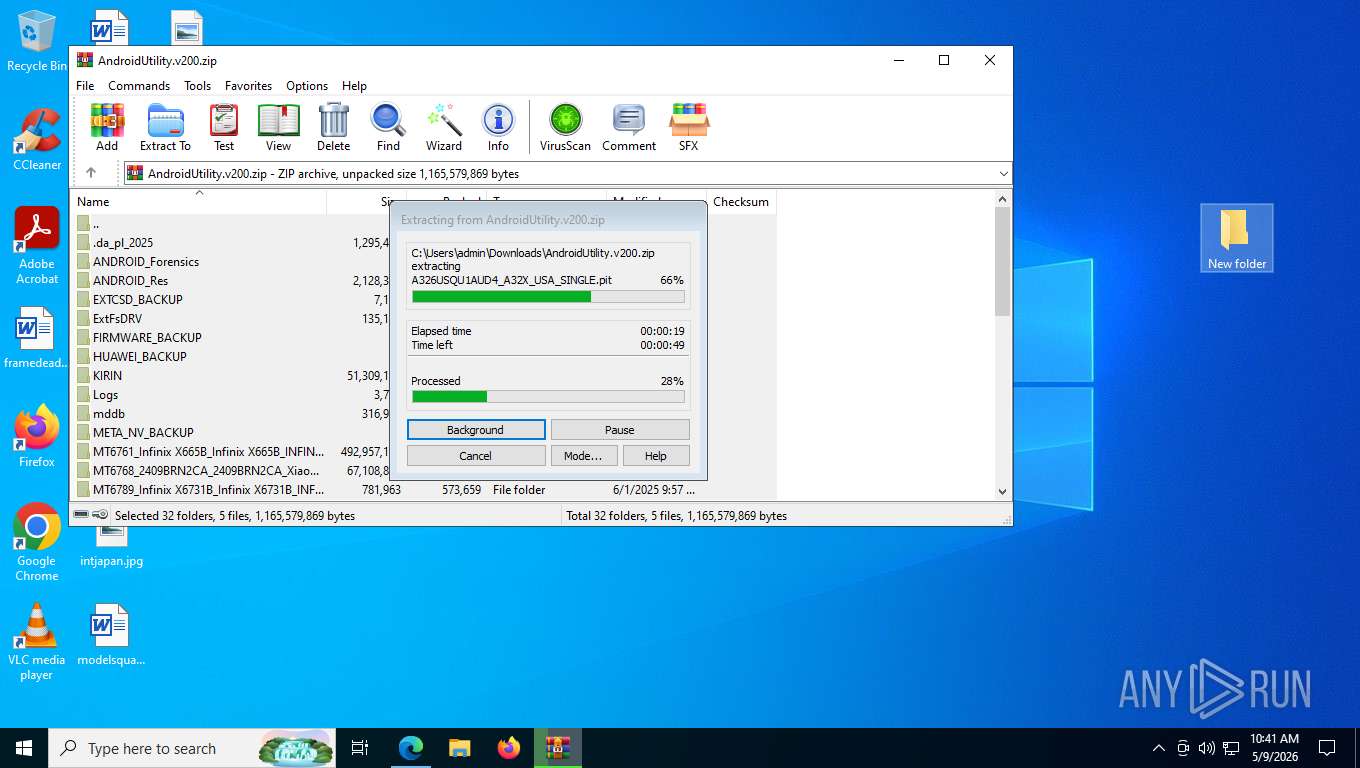
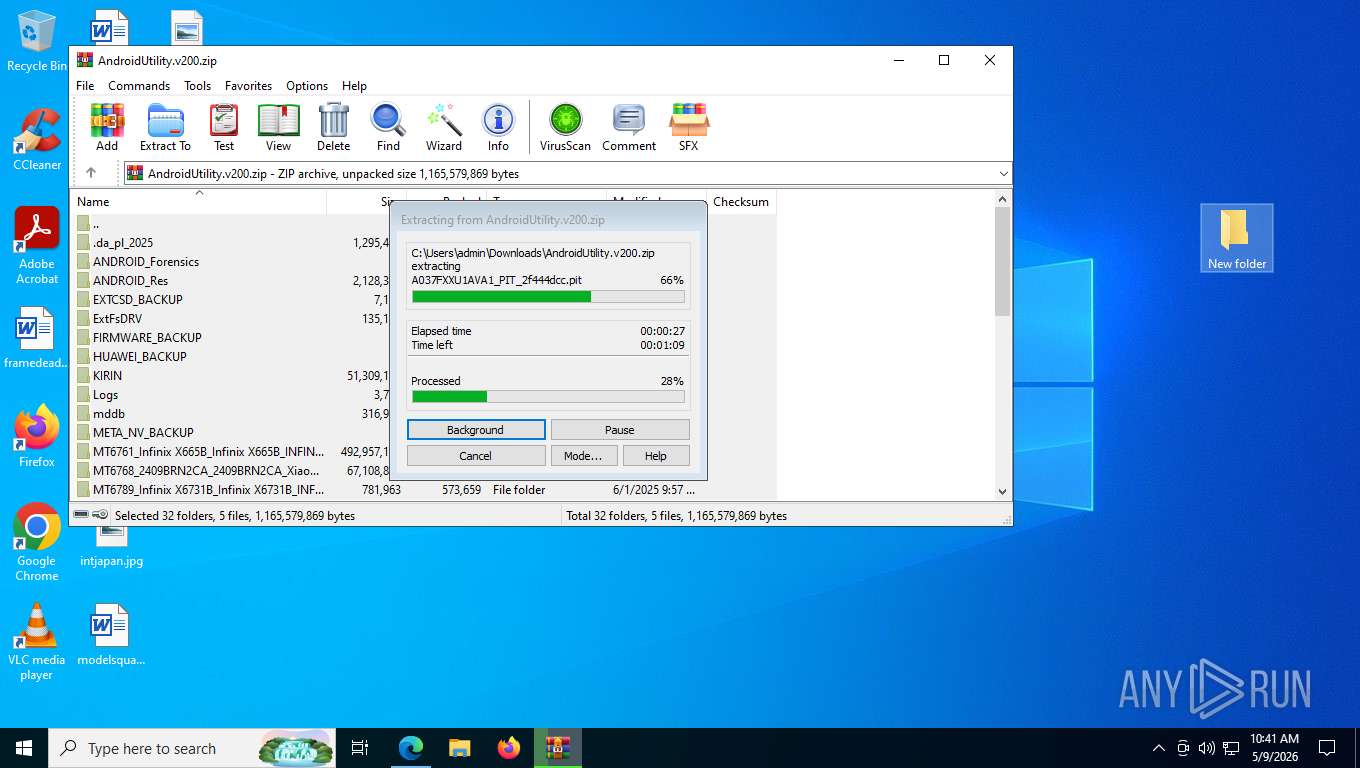
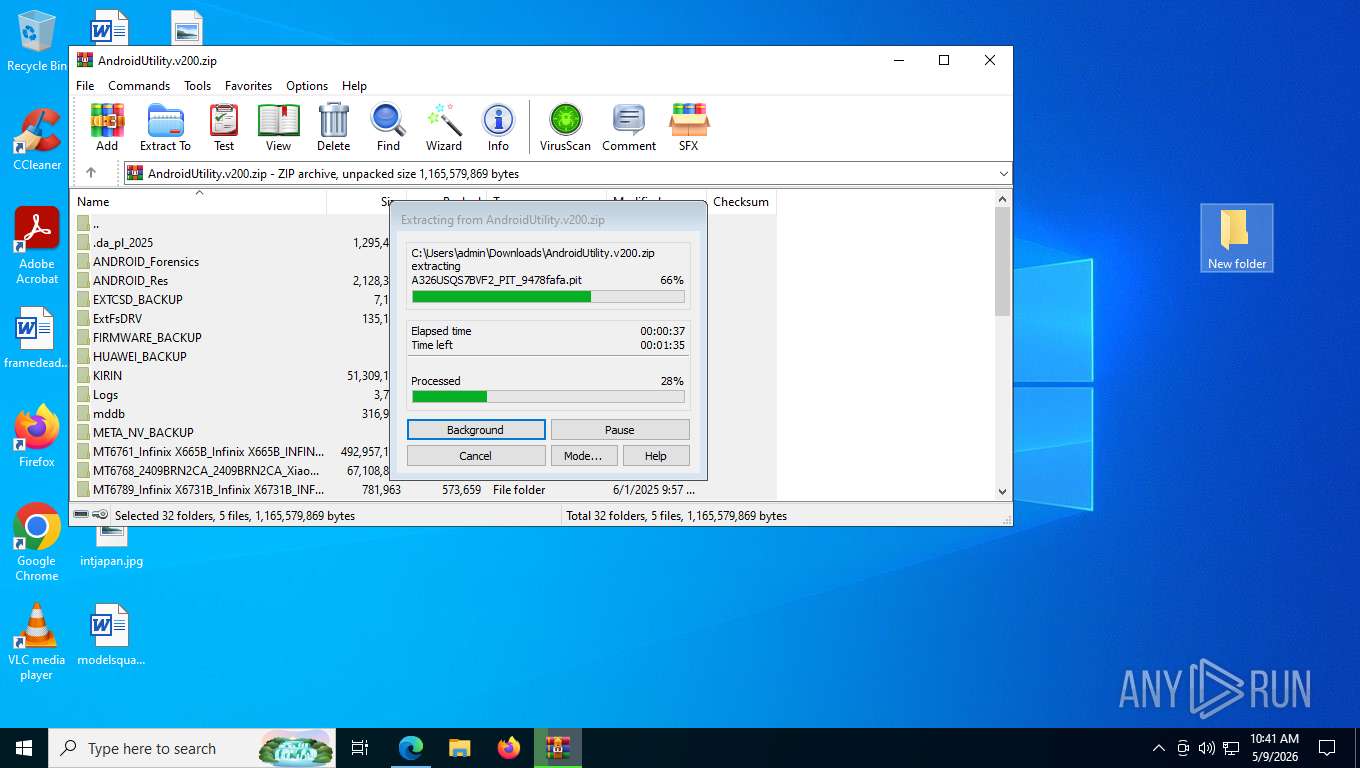
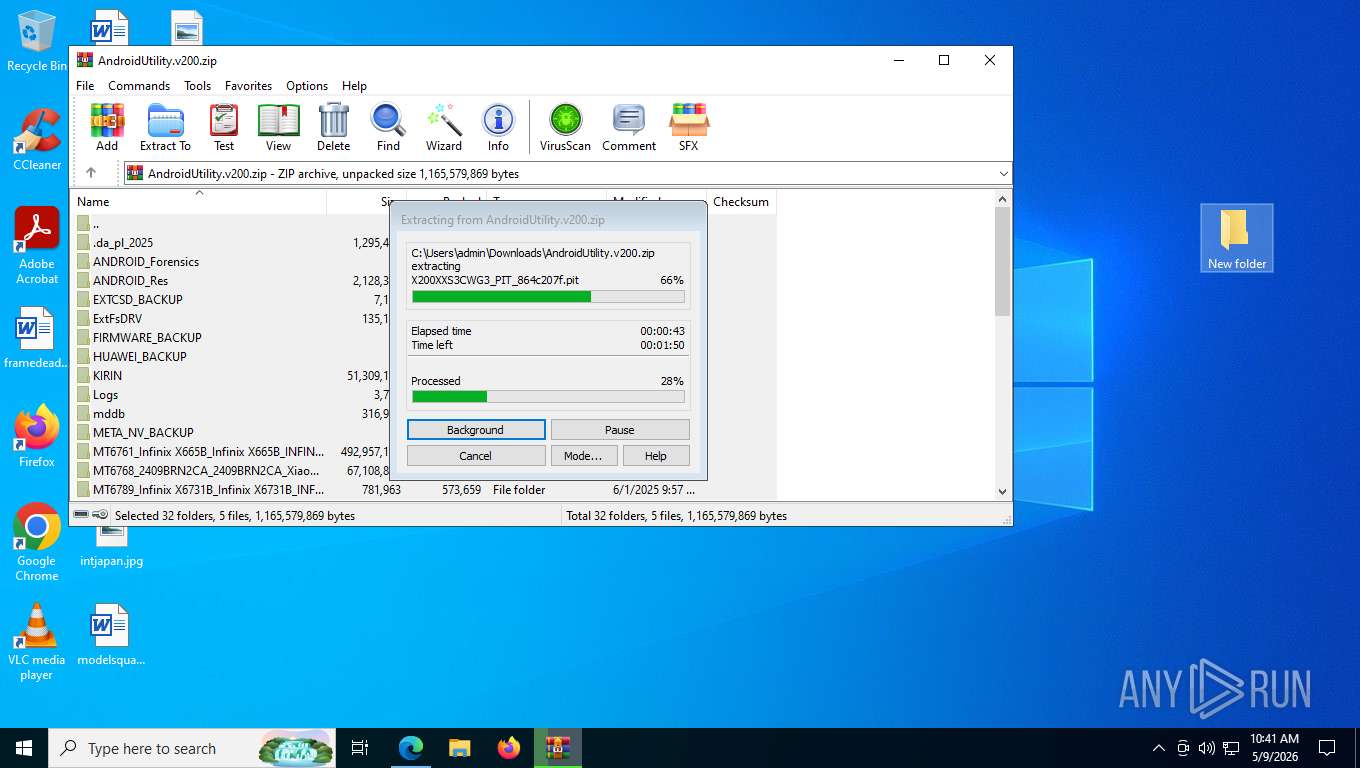
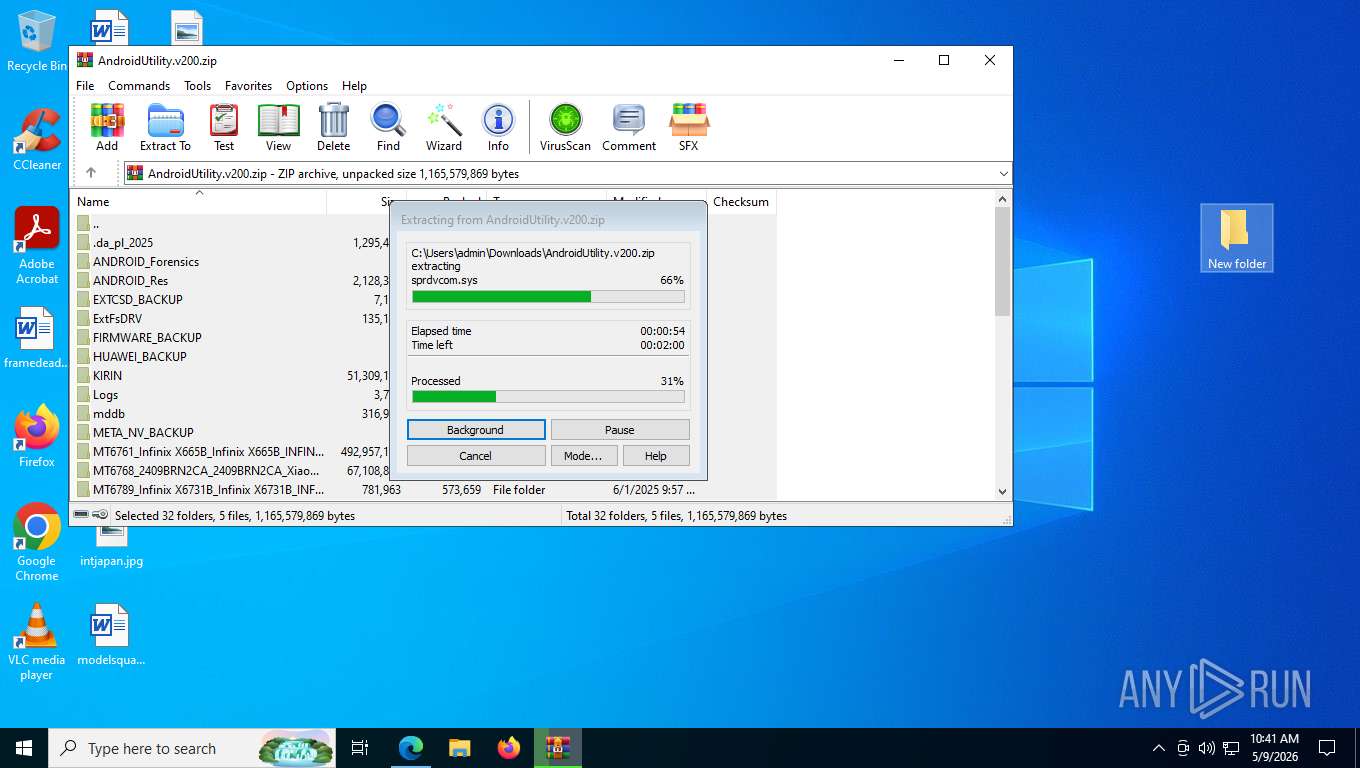
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 8368)
INFO
Checks supported languages
- identity_helper.exe (PID: 4524)
- AndroidUtility.exe (PID: 4172)
Application launched itself
- msedge.exe (PID: 4968)
Reads the computer name
- identity_helper.exe (PID: 4524)
- AndroidUtility.exe (PID: 4172)
Attempting to connect via WebSocket
- msedge.exe (PID: 4260)
Reads Environment values
- identity_helper.exe (PID: 4524)
The sample compiled with arabic language support
- WinRAR.exe (PID: 8368)
The sample compiled with english language support
- WinRAR.exe (PID: 8368)
- AndroidUtility.exe (PID: 4172)
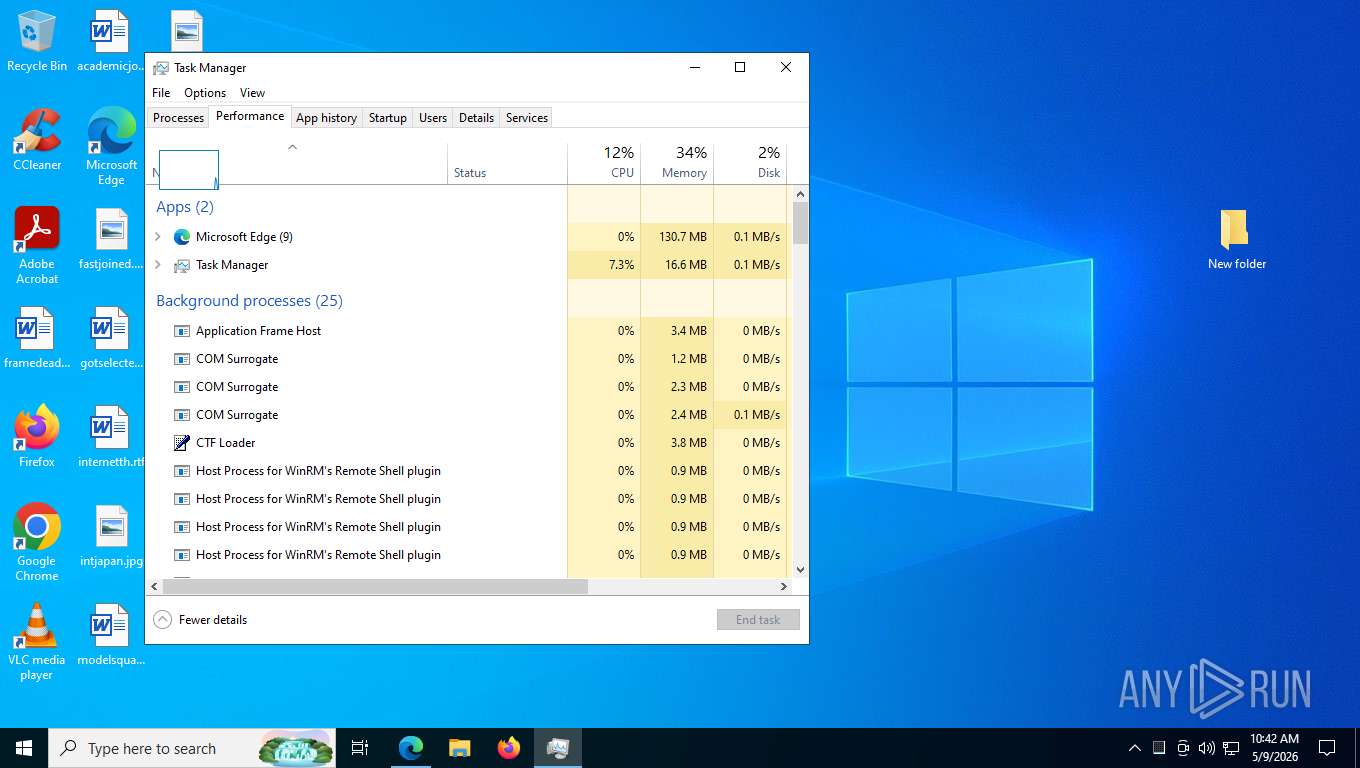
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 8232)
- WMIC.exe (PID: 8492)
- WMIC.exe (PID: 8404)
- WMIC.exe (PID: 6116)
- WMIC.exe (PID: 8280)
- WMIC.exe (PID: 5916)
- WMIC.exe (PID: 8084)
- WMIC.exe (PID: 3168)
Reads the machine GUID from the registry
- AndroidUtility.exe (PID: 4172)
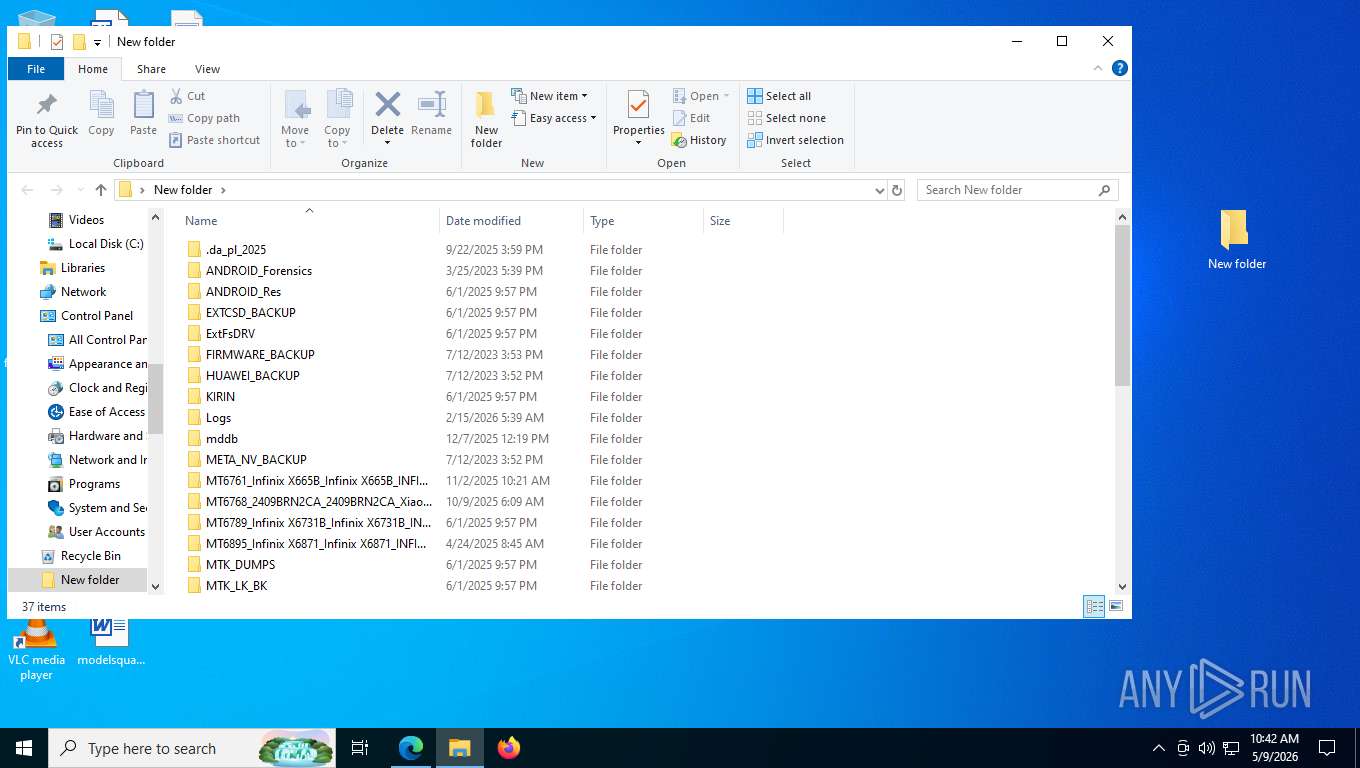
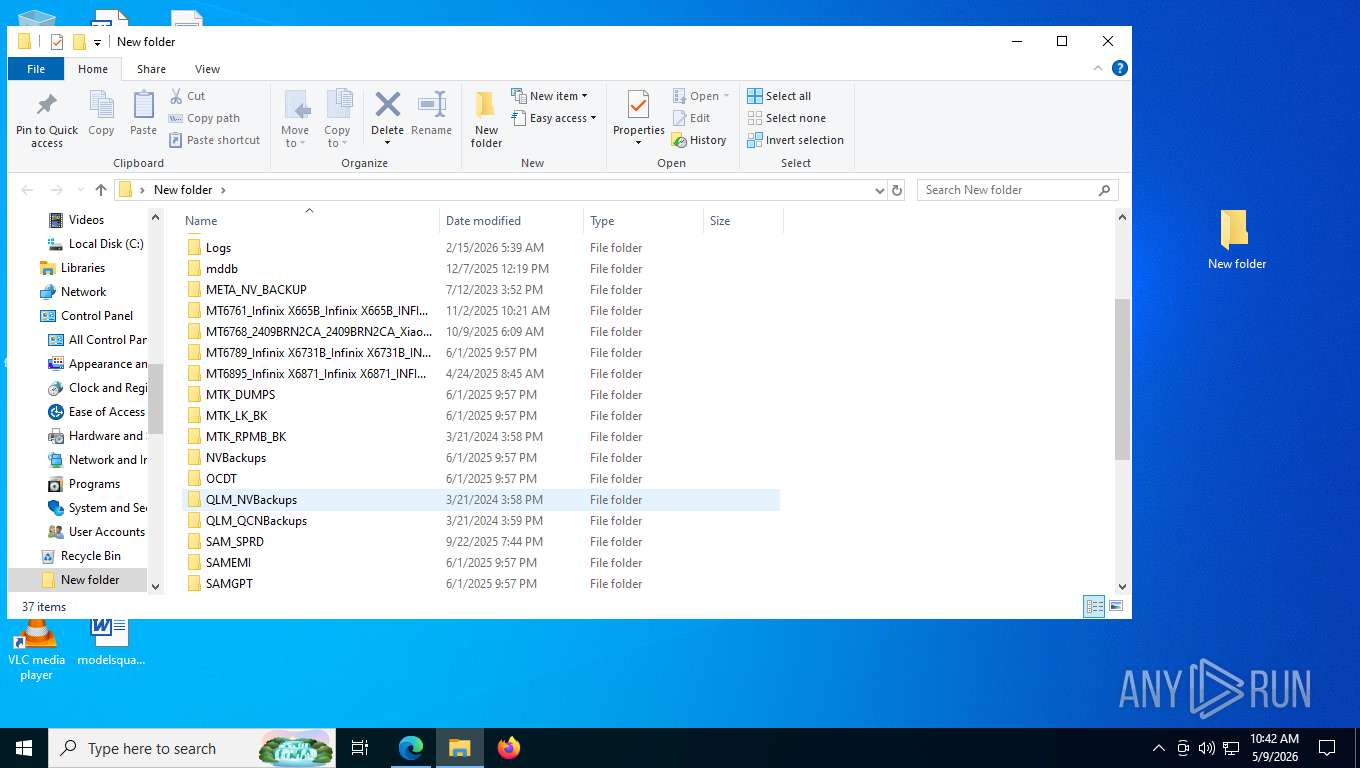
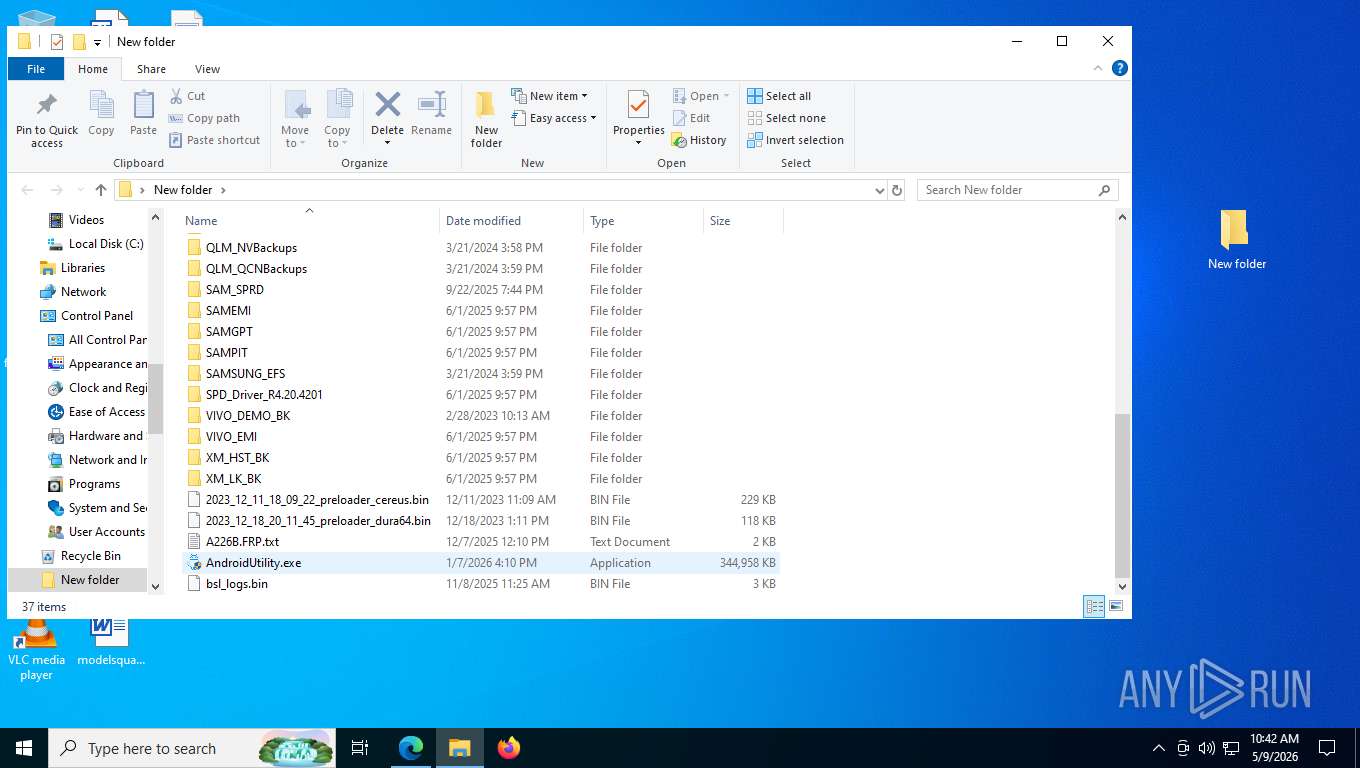
Manual execution by a user
- AndroidUtility.exe (PID: 4172)
- Taskmgr.exe (PID: 8232)
- Taskmgr.exe (PID: 7976)
- AndroidUtility.exe (PID: 9064)
The sample compiled with chinese language support
- AndroidUtility.exe (PID: 4172)
- WinRAR.exe (PID: 8368)
There is functionality for taking screenshot (YARA)
- AndroidUtility.exe (PID: 4172)
Create files in a temporary directory
- AndroidUtility.exe (PID: 4172)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
199
Monitored processes
56
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3516,i,11695799228027231282,11929009385305669490,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3828 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1500 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5364,i,11695799228027231282,11929009385305669490,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5344 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffe2392f208,0x7ffe2392f214,0x7ffe2392f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1724 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1748,i,11695799228027231282,11929009385305669490,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6228 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1772 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5504,i,11695799228027231282,11929009385305669490,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5528 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3084 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5996,i,11695799228027231282,11929009385305669490,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6132 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3152 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1684,i,11695799228027231282,11929009385305669490,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5160 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3168 | wmic Path Win32_VideoController get Caption,VideoModeDescription | C:\Windows\SysWOW64\wbem\WMIC.exe | — | AndroidUtility.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2596,i,11695799228027231282,11929009385305669490,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2724 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
5 116
Read events
5 094
Write events
21
Delete events
1
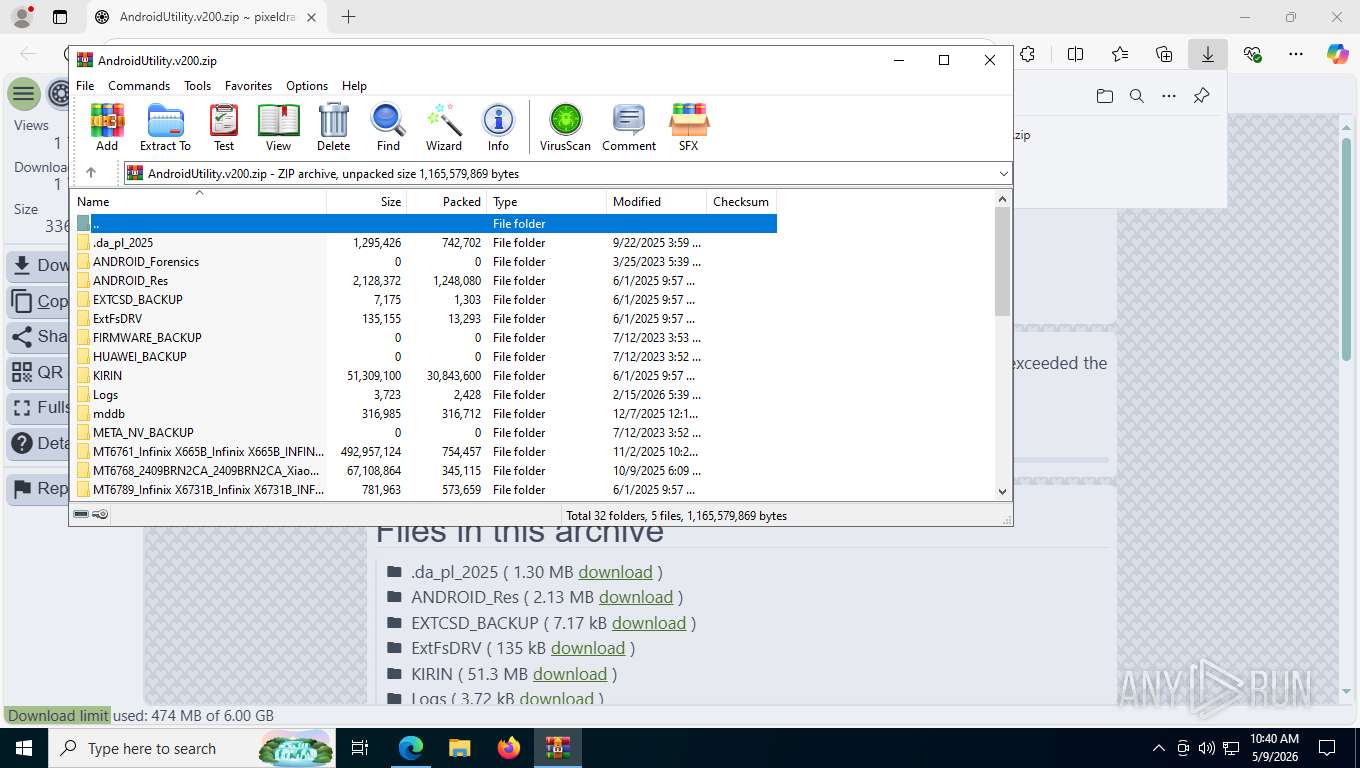
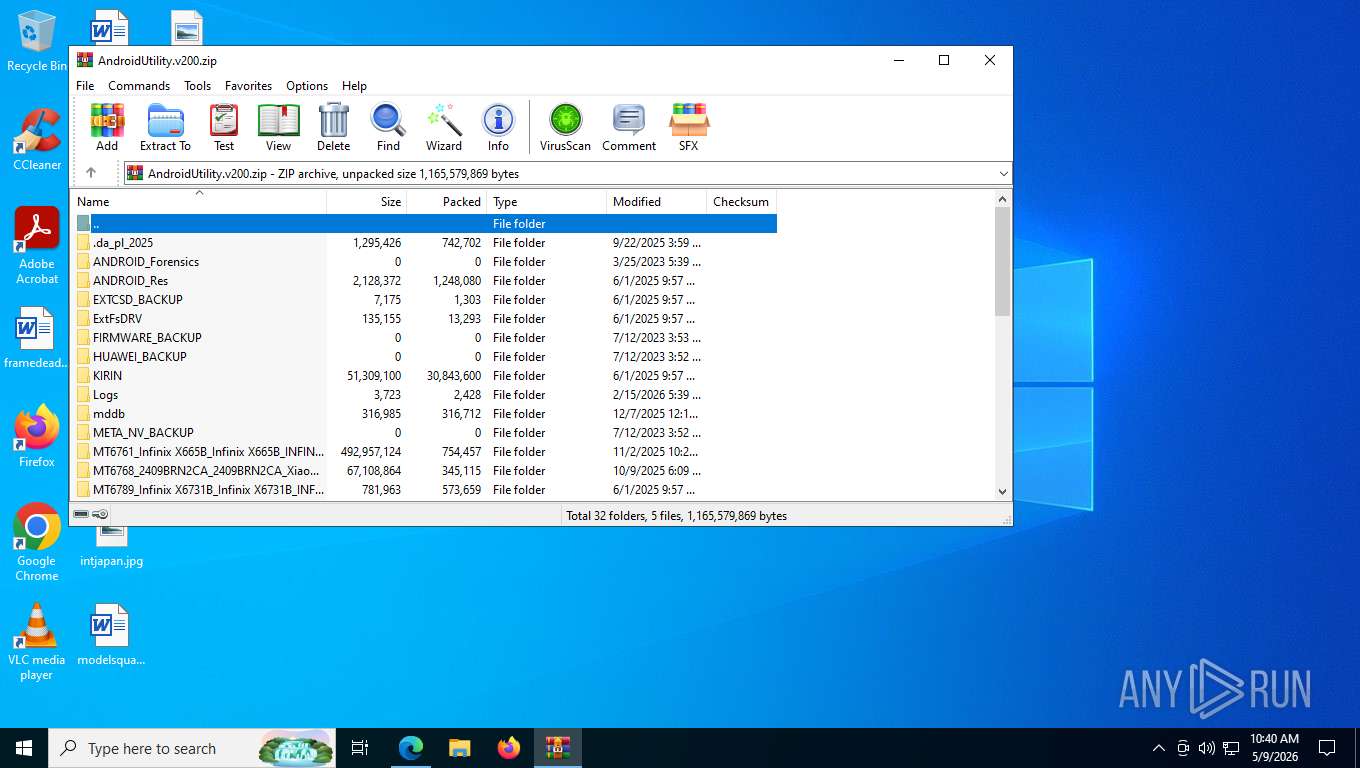
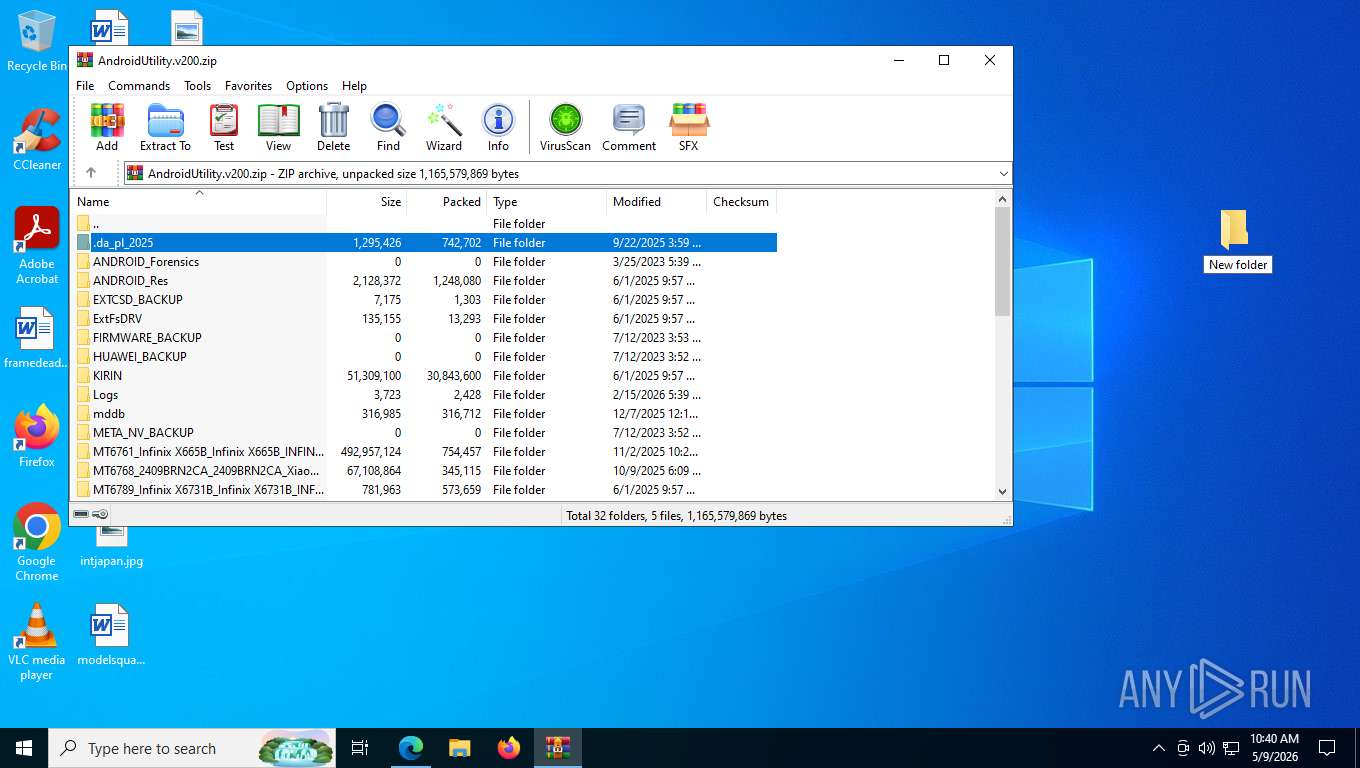
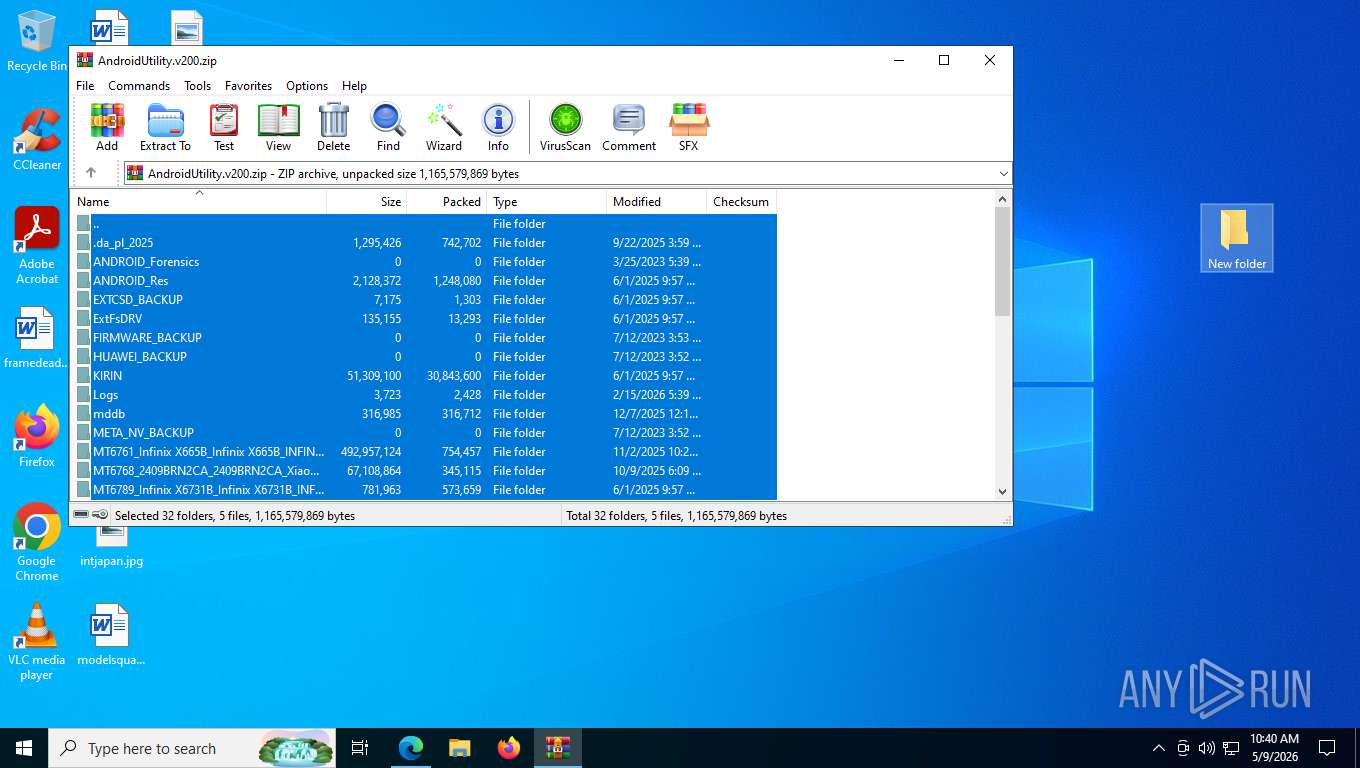
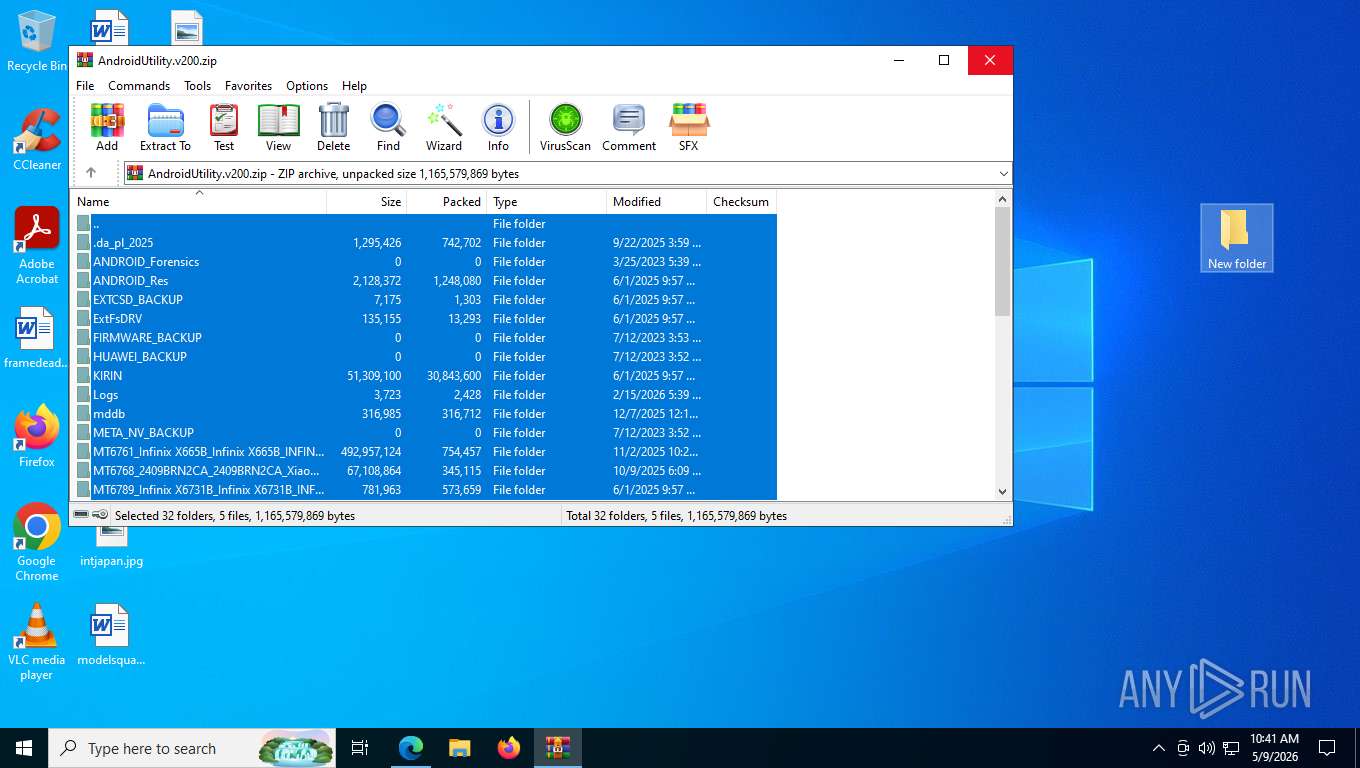
Modification events
| (PID) Process: | (8368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\AndroidUtility.v200.zip | |||
| (PID) Process: | (8368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (8368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
41
Suspicious files
841
Text files
395
Unknown types
71
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFdfea4.TMP | — | |
MD5:— | SHA256:— | |||
| 4968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFdfeb3.TMP | — | |
MD5:— | SHA256:— | |||
| 4968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFdfeb3.TMP | — | |
MD5:— | SHA256:— | |||
| 4968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFdfeb3.TMP | — | |
MD5:— | SHA256:— | |||
| 4968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFdfec3.TMP | — | |
MD5:— | SHA256:— | |||
| 4968 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
203
TCP/UDP connections
84
DNS requests
78
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4260 | msedge.exe | GET | 101 | 203.23.179.11:443 | https://pixeldrain.com/api/file_stats | AU | — | — | unknown |
4260 | msedge.exe | GET | 200 | 150.171.109.101:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
4260 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
4260 | msedge.exe | GET | 200 | 203.23.179.11:443 | https://pixeldrain.com/api/file/hMzo55EK/thumbnail | AU | image | 2.40 Kb | unknown |
4260 | msedge.exe | GET | 200 | 203.23.179.11:443 | https://pixeldrain.com/res/svelte/file_viewer.js?v493848 | AU | text | 442 Kb | unknown |
4260 | msedge.exe | GET | 200 | 51.158.202.5:443 | https://stats.pixeldrain.com/js/script.js | FR | text | 2.93 Kb | unknown |
4260 | msedge.exe | GET | 200 | 203.23.179.11:443 | https://pixeldrain.com/u/hMzo55EK | AU | html | 3.97 Kb | unknown |
4260 | msedge.exe | GET | 200 | 203.23.179.11:443 | https://pixeldrain.com/res/style/layout.css?v493848 | AU | text | 13.0 Kb | unknown |
4260 | msedge.exe | GET | 200 | 203.23.179.11:443 | https://pixeldrain.com/theme.css | AU | text | 2.25 Kb | unknown |
4260 | msedge.exe | GET | 200 | 203.23.179.11:443 | https://pixeldrain.com/res/img/background_patterns/checker6_transparent.png | AU | image | 362 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7984 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4260 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4260 | msedge.exe | 203.23.179.11:443 | pixeldrain.com | GSLNETWORKS-AS-AP GSL Networks Pty LTD | AU | whitelisted |
4260 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4260 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4260 | msedge.exe | 150.171.109.101:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
pixeldrain.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
stats.pixeldrain.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4260 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
4260 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
4260 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
4260 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
4260 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
4260 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
4260 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
4260 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
4260 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
4260 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
Process | Message |
|---|---|
AndroidUtility.exe | Read Debug Info::TurnOnDebugLog from C:\Users\admin\Desktop\New folder\../configs/MF_Setup.txt failed (load file failed) |
AndroidUtility.exe | Read Debug Info::TurnOnDebugLog from C:\Users\admin\Desktop\New folder\MF_Setup.txt failed (load file failed) |