| download: | 1100559 |
| Full analysis: | https://app.any.run/tasks/5b63a6cf-b4b9-40a2-9949-2bb6af48d0e8 |
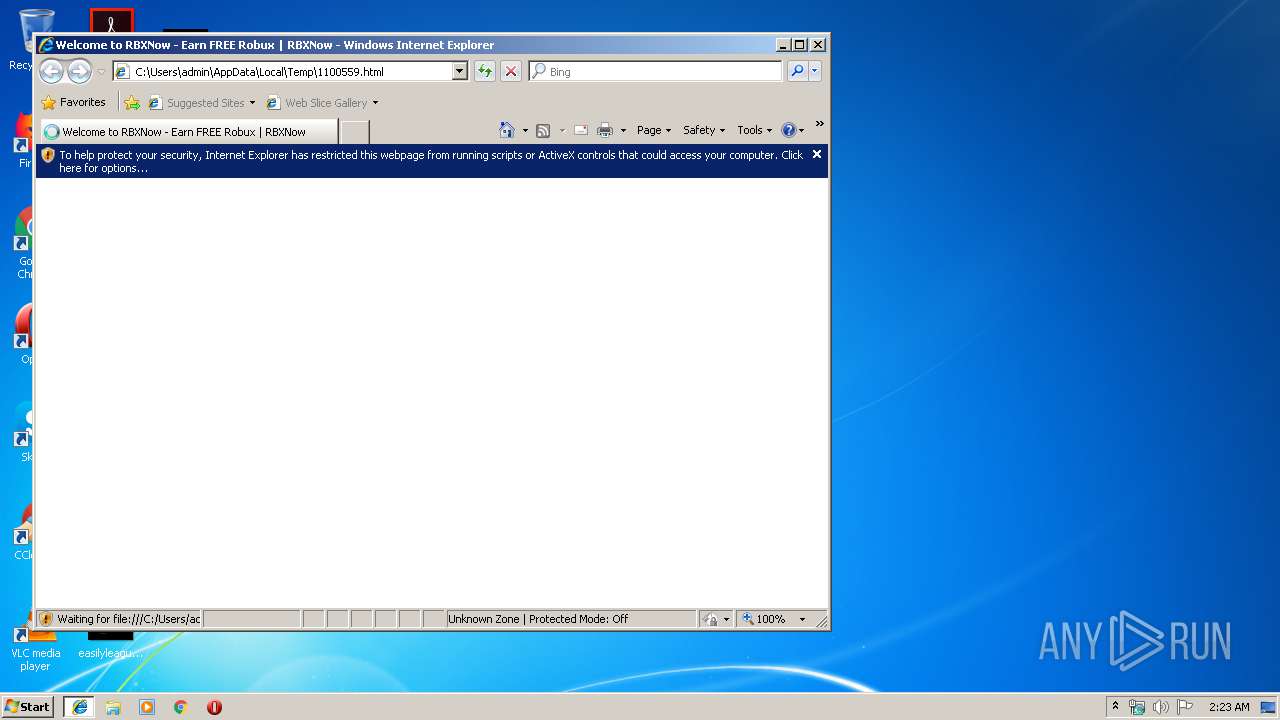
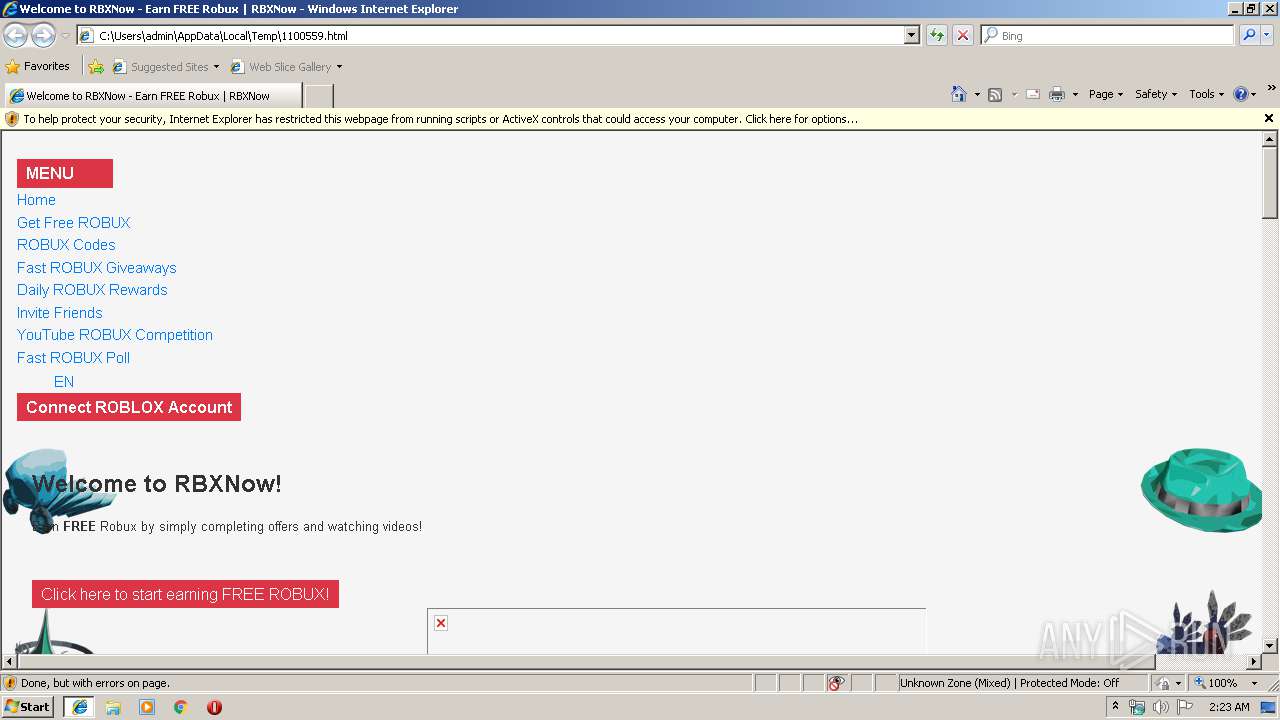
| Verdict: | Malicious activity |
| Analysis date: | January 04, 2020, 02:22:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | 0336A1A373204FB6374206FCF2D49A12 |
| SHA1: | E7F43AF400D938E7FF59768C69A7CBF205D6C376 |
| SHA256: | 8E9E409710103F267EC11C825847B71C13857571BFB8F6CCB9FE06ACF78E282E |
| SSDEEP: | 384:D8gm5EwJHdUVuXP/YBPZvnQB0bxgzEcKWrjtGBZy/U:Y0wJHdMuXP/YBPZvnQB0zcJ0ny/U |
MALICIOUS
No malicious indicators.SUSPICIOUS
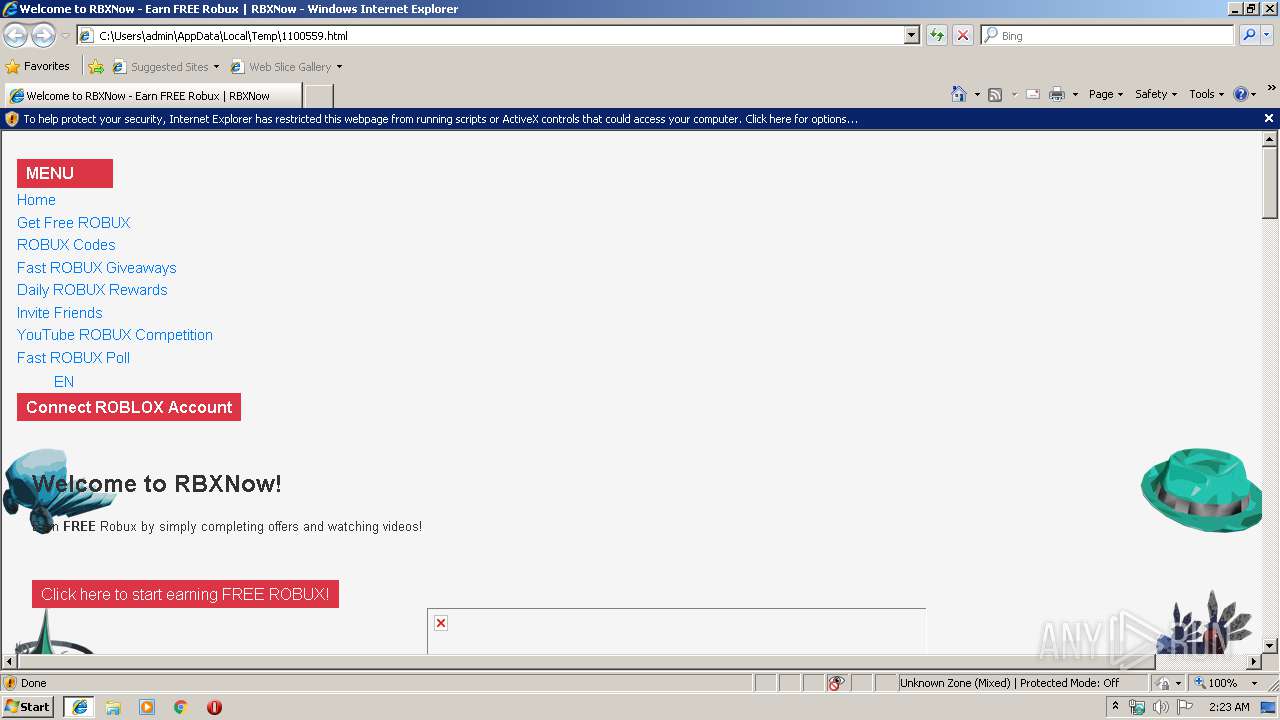
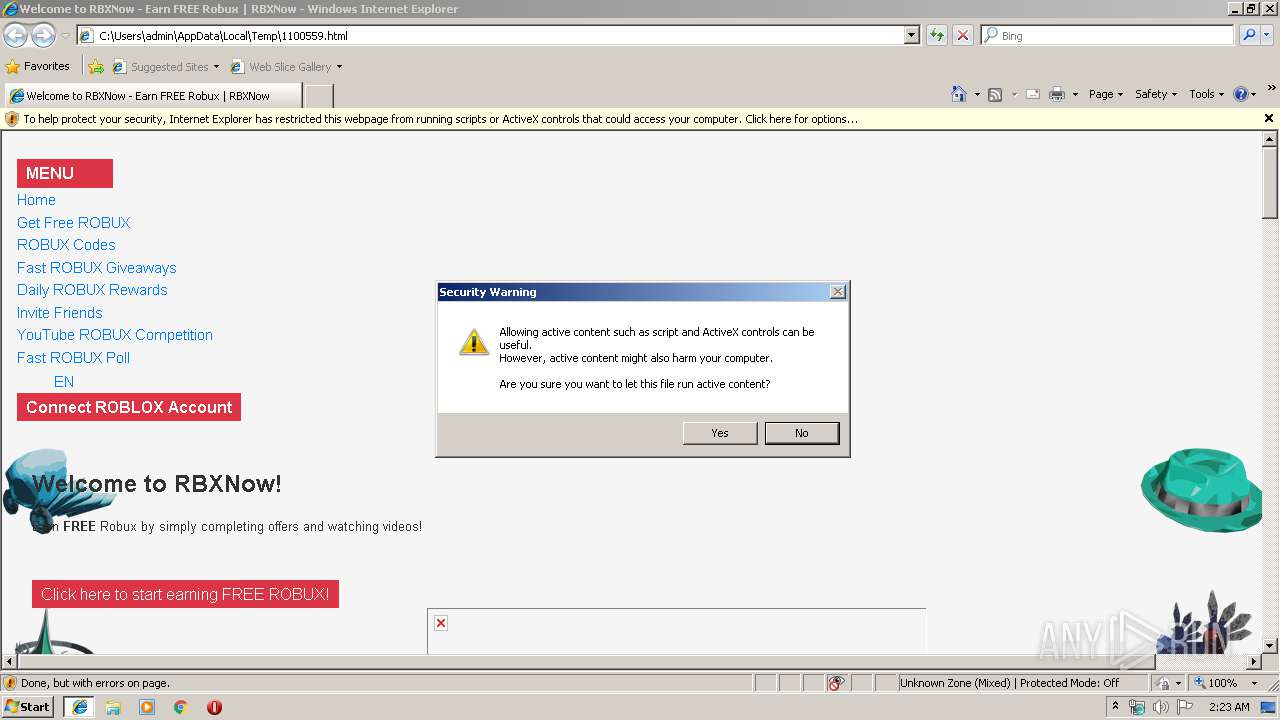
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3848)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 2152)
- iexplore.exe (PID: 3356)
Creates files in the user directory
- iexplore.exe (PID: 2368)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3848)
- iexplore.exe (PID: 2152)
- iexplore.exe (PID: 3356)
Reads Internet Cache Settings
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 2368)
Reads internet explorer settings
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 2368)
Application launched itself
- iexplore.exe (PID: 2152)
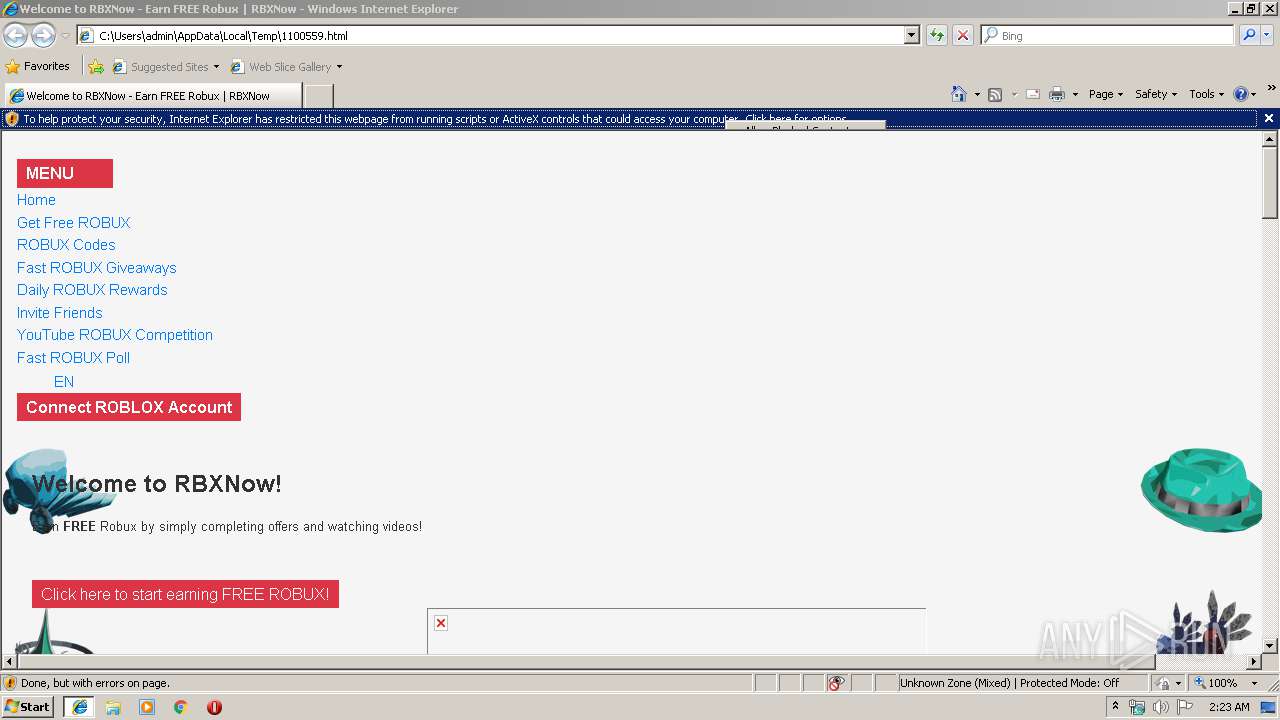
Changes internet zones settings
- iexplore.exe (PID: 2152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
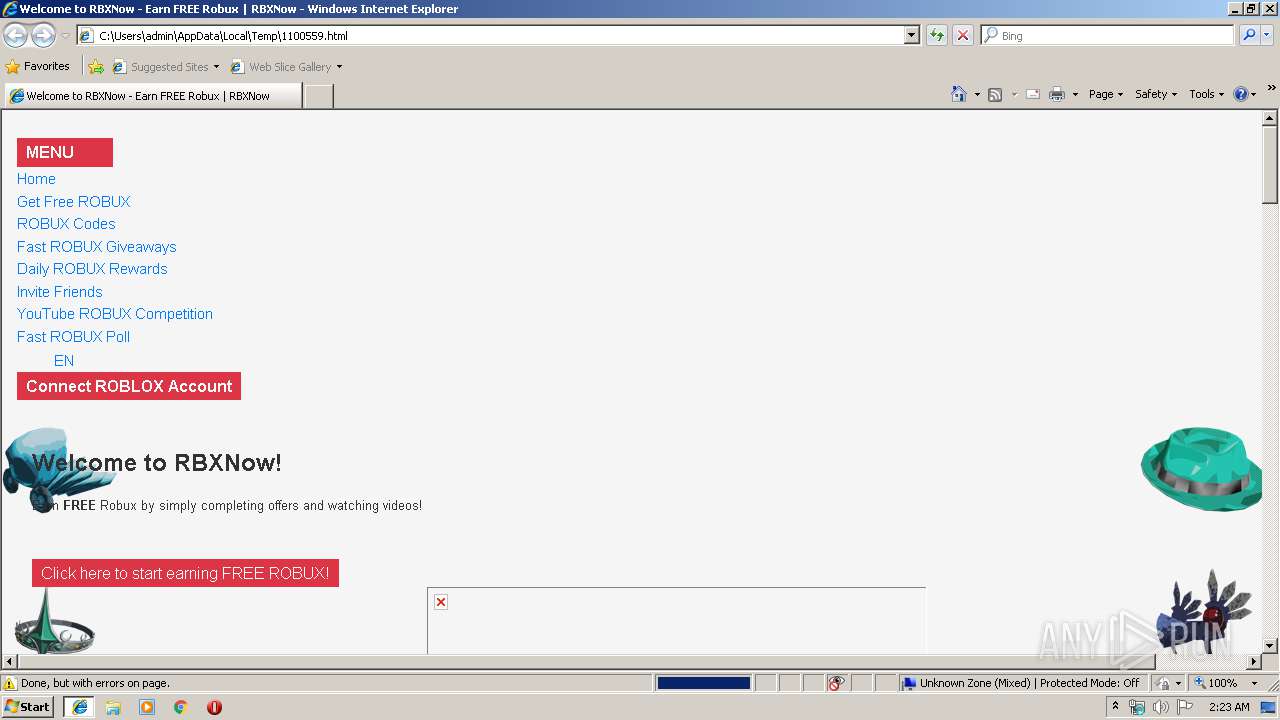
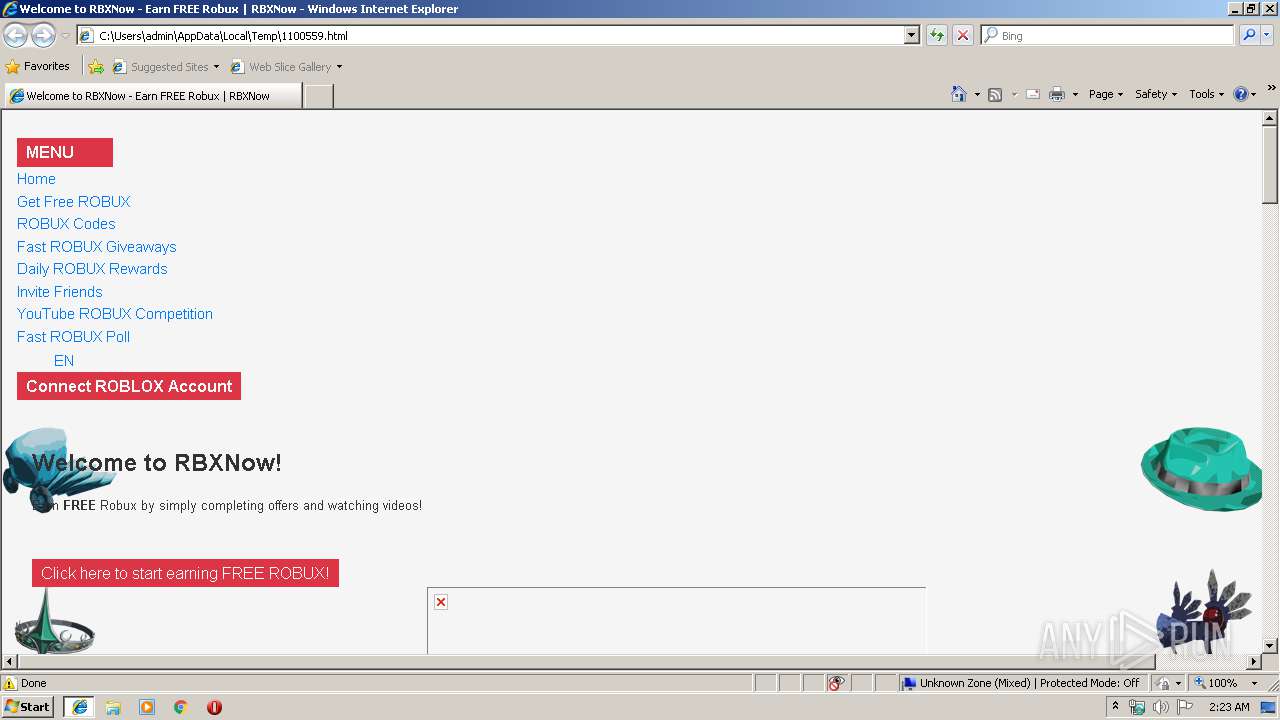
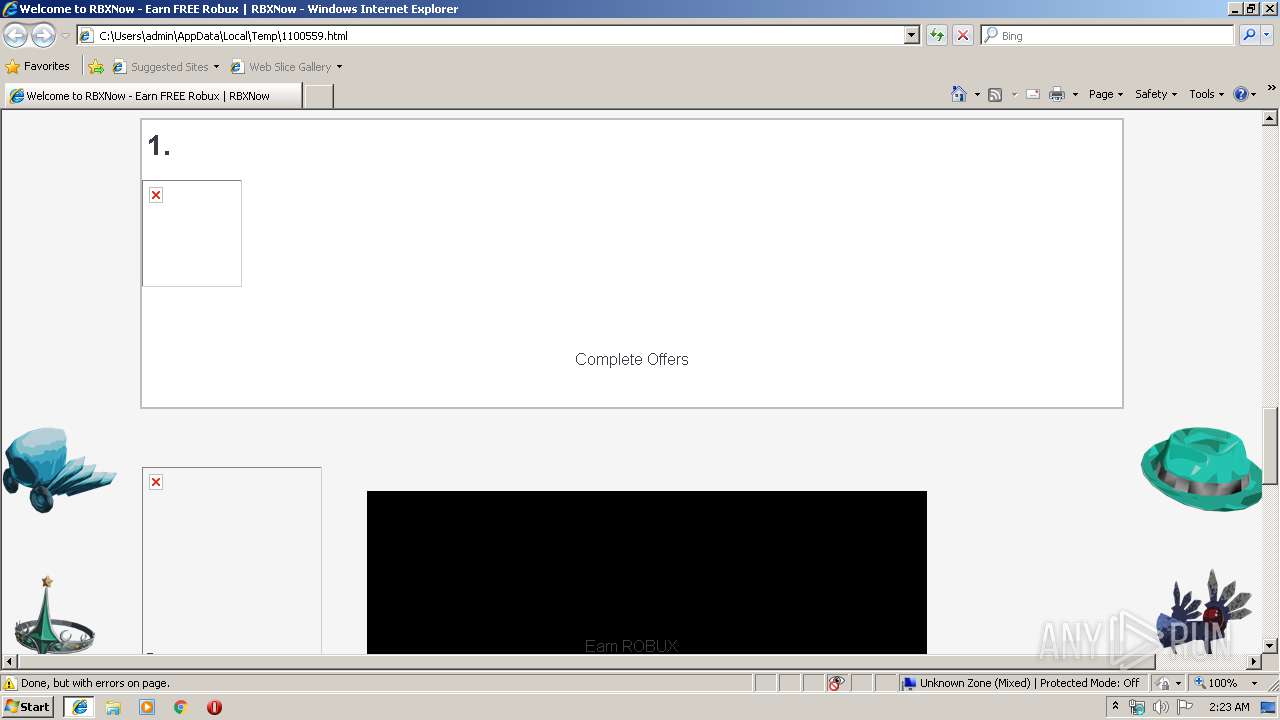
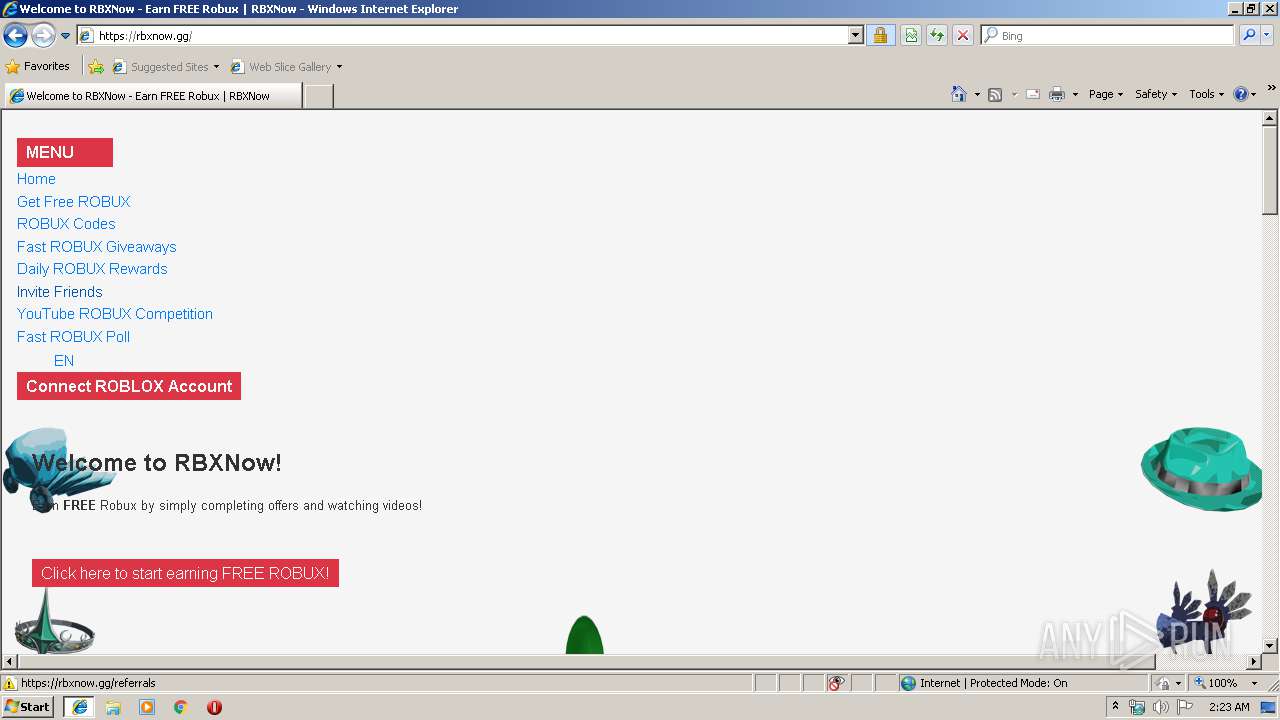
| HTTPEquivContentSecurityPolicy: | upgrade-insecure-requests |
|---|---|
| viewport: | width=device-width, initial-scale=1.0, maximum-scale=1.0, user-scalable=no |
| themeColor: | #FF0000 |
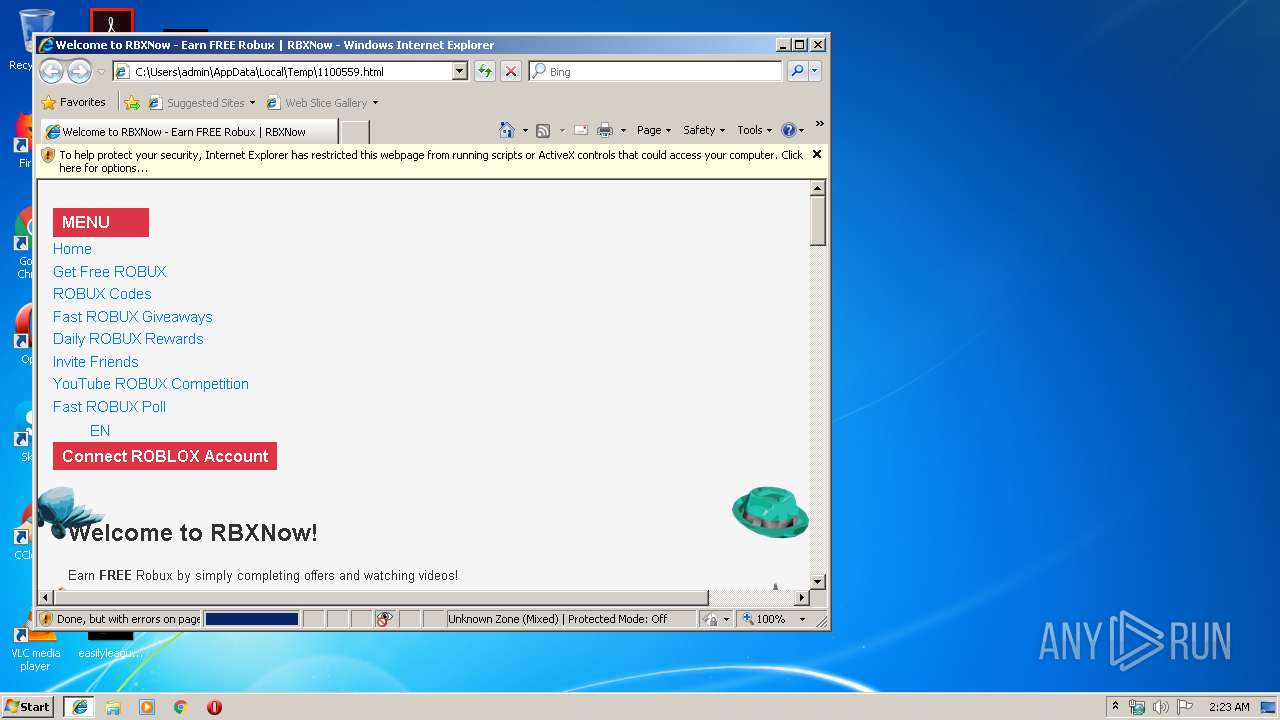
| Author: | RBXNow |
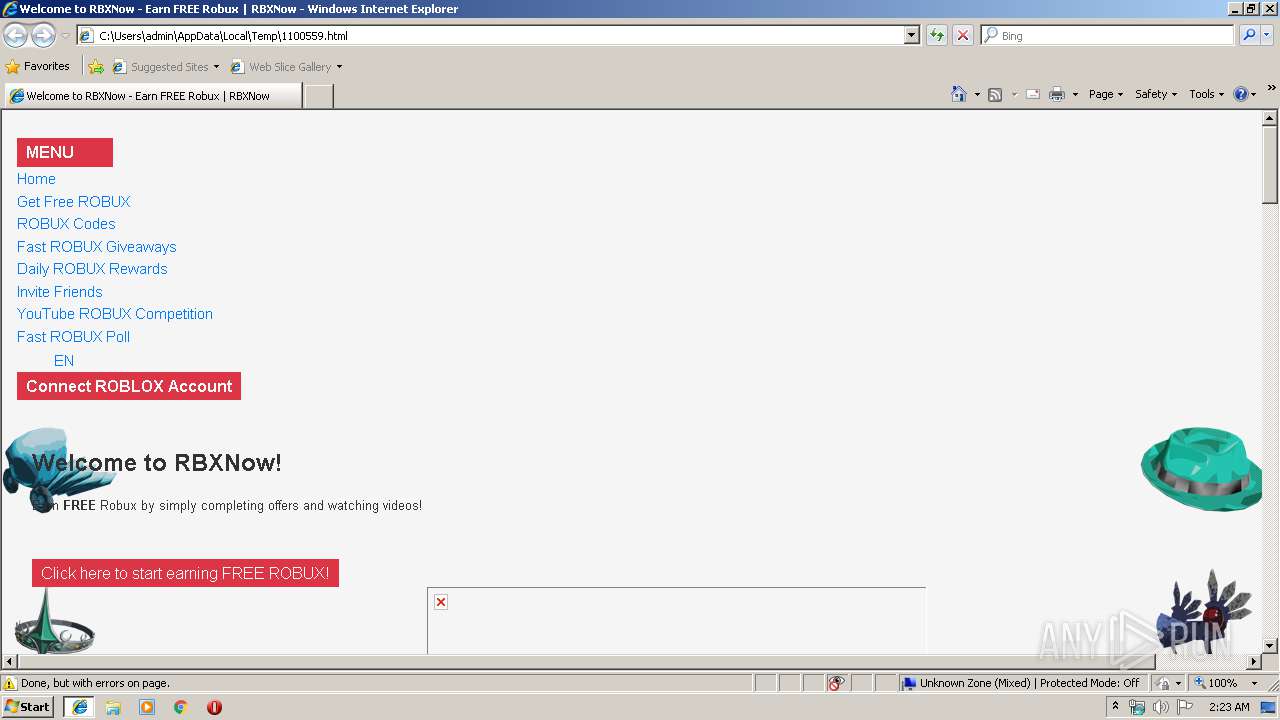
| Keywords: | rblx,free robux,roblox,rbxfree,rbx,rbxnowgg,rbxnow.gg,rbxnow,free roblox,rbxnow,free,robux,robux now,secret robux,rbxnow,rbxn,rbxno,rbxnow.gg,roblox free robux,how to get robux,free robux roblox,roblox fun,free roux,rblxnow,rblxnow.gg,rblxnowgg,how to get rich on roblox,roblox rich,bacon to rich,how to get free robux,how do i get free robux,free robux glitch,free robux secret method,yummers,military dave |
| twitterCard: | summary_large_image |
| twitterImage: | https://rbxnow.gg/assets/images/logo-bg.gif |
| twitterDescription: | Earn FREE ROBUX by completing surveys & watching videos! |
| Title: | Welcome to RBXNow - Earn FREE Robux | RBXNow |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2152 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\1100559.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2152 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3356 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2152 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3848 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
892
Read events
775
Write events
115
Delete events
2
Modification events
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {28F302B3-2E99-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E407010006000400020017000F000E02 | |||
Executable files
0
Suspicious files
1
Text files
102
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3356 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\login[1].js | text | |
MD5:CA2A5BA5EE6ED254791C005F0257EE49 | SHA256:85A357B195BE68D2131534B7F0D4169B23E62DF758732808C64D3BD6029881B5 | |||
| 3356 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\jquery.magnific-popup.min[1].js | text | |
MD5:9D95010930658A125D3C8D884BE92E1F | SHA256:7225B2B7E152392A5B6D596946195325D1E050D2DAA6147B3332B07109C50FD7 | |||
| 3356 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\OneSignalSDK[1].js | text | |
MD5:2A5DE8DD720175AA229445A5937A6C43 | SHA256:B0B41EAD7D73C51545A6B97022FDF4A60C64D4910136516F2F8832D2F11D7BED | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3356 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\style[1].css | text | |
MD5:33A5577662065029117BE9F98C138B7C | SHA256:9FC8CA353AE7F82BEA4C4A10606BEE67469E7802A6E0AC47503CA1E1B0214519 | |||
| 3356 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\11277b4f51[1].js | text | |
MD5:5D98ADC2C09B812C26CB7D74DD50152E | SHA256:78430AACDED9BC766CA632D544407A3DED6EB62F7C296F29E668E21FEEFA5E3B | |||
| 3356 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\magnific-popup[1].css | text | |
MD5:ADA56C4D727D6DE54B4DB7F0E542249A | SHA256:0187C5BFD4FB8CFFD683346F9896147A8EED232298447EB642DF3FBC06D30ACE | |||
| 3356 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\js[1] | text | |
MD5:7C58FA6637202D61C539502E79D9575F | SHA256:BFA1620C2AF661732E3E40464679A0F5E098B6E01E7E7CD1D3FBE906FAA67AB0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
72
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2152 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
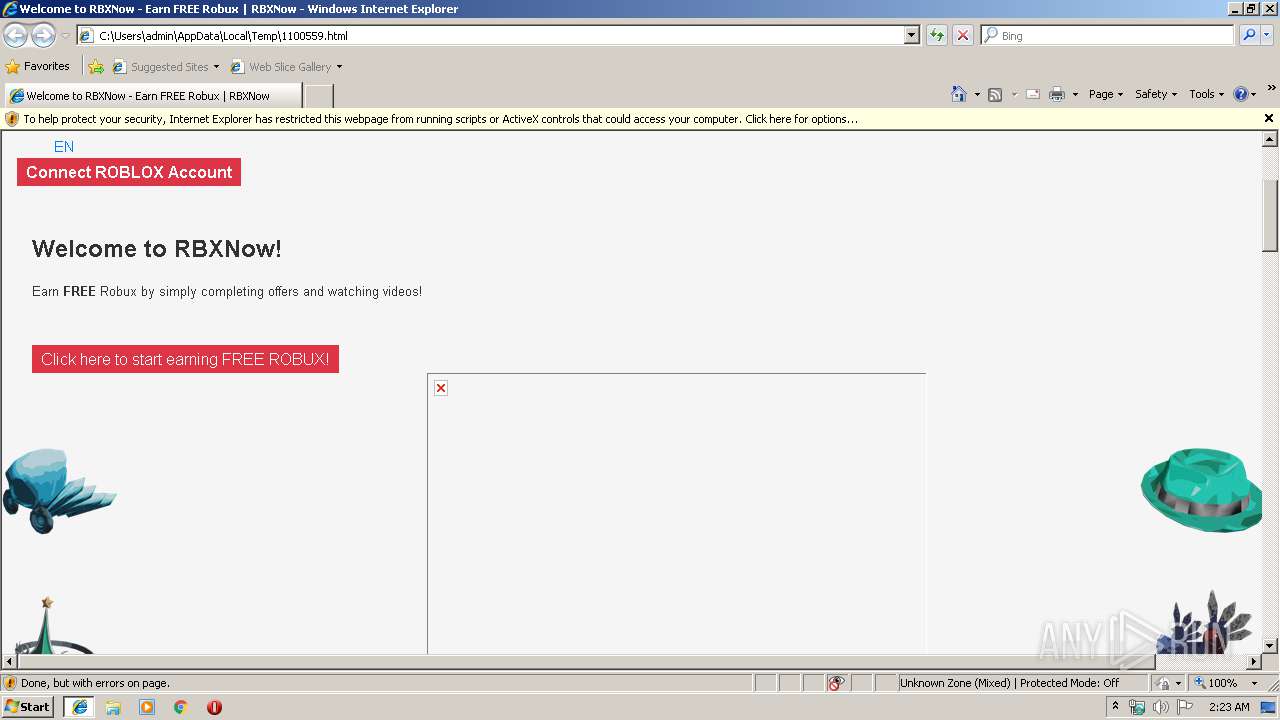
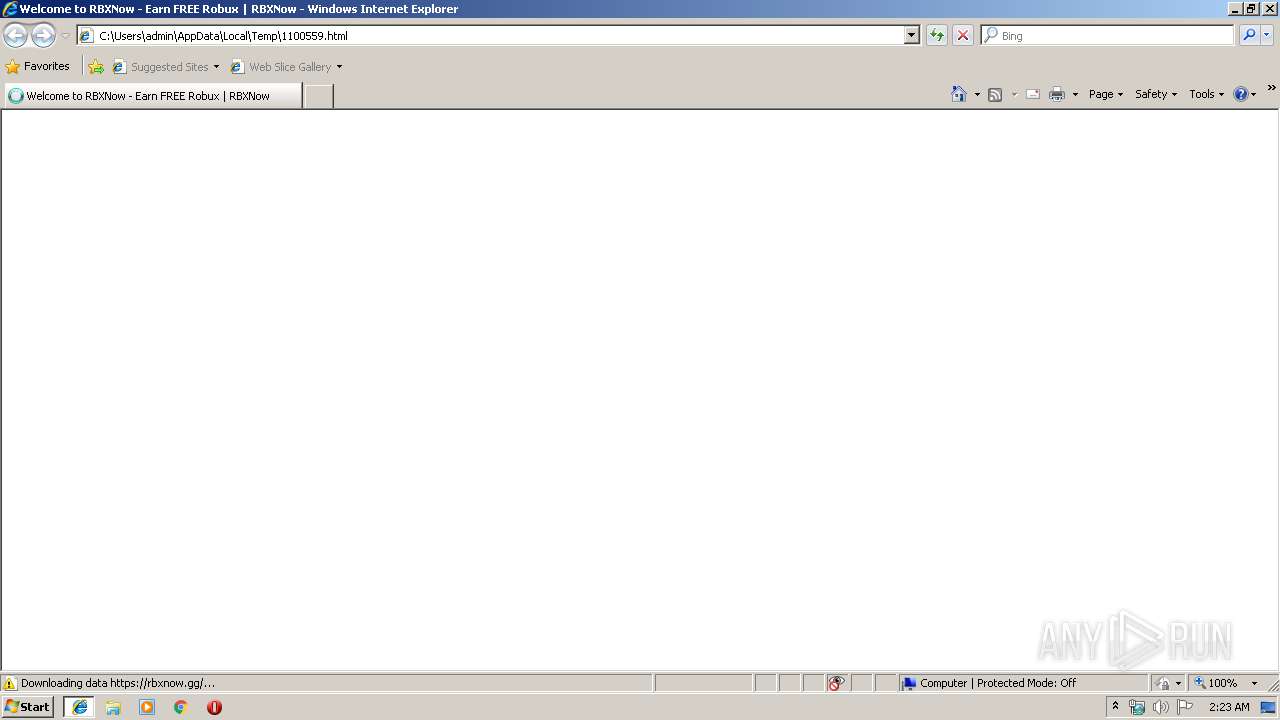
3356 | iexplore.exe | 151.139.128.10:443 | kit.fontawesome.com | Highwinds Network Group, Inc. | US | malicious |
3356 | iexplore.exe | 104.18.225.52:443 | cdn.onesignal.com | Cloudflare Inc | US | malicious |
3356 | iexplore.exe | 104.20.173.8:443 | rbxnow.gg | Cloudflare Inc | US | unknown |
3356 | iexplore.exe | 209.197.3.15:443 | stackpath.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3356 | iexplore.exe | 172.217.18.2:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3356 | iexplore.exe | 172.217.21.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3356 | iexplore.exe | 151.101.2.109:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
3356 | iexplore.exe | 23.111.9.35:443 | use.fontawesome.com | netDNA | US | suspicious |
3356 | iexplore.exe | 104.17.64.4:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3356 | iexplore.exe | 143.204.214.82:443 | platform-api.sharethis.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stackpath.bootstrapcdn.com |
| whitelisted |
cdn.onesignal.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
kit.fontawesome.com |
| whitelisted |
code.jquery.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
platform-api.sharethis.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
rbxnow.gg |
| unknown |