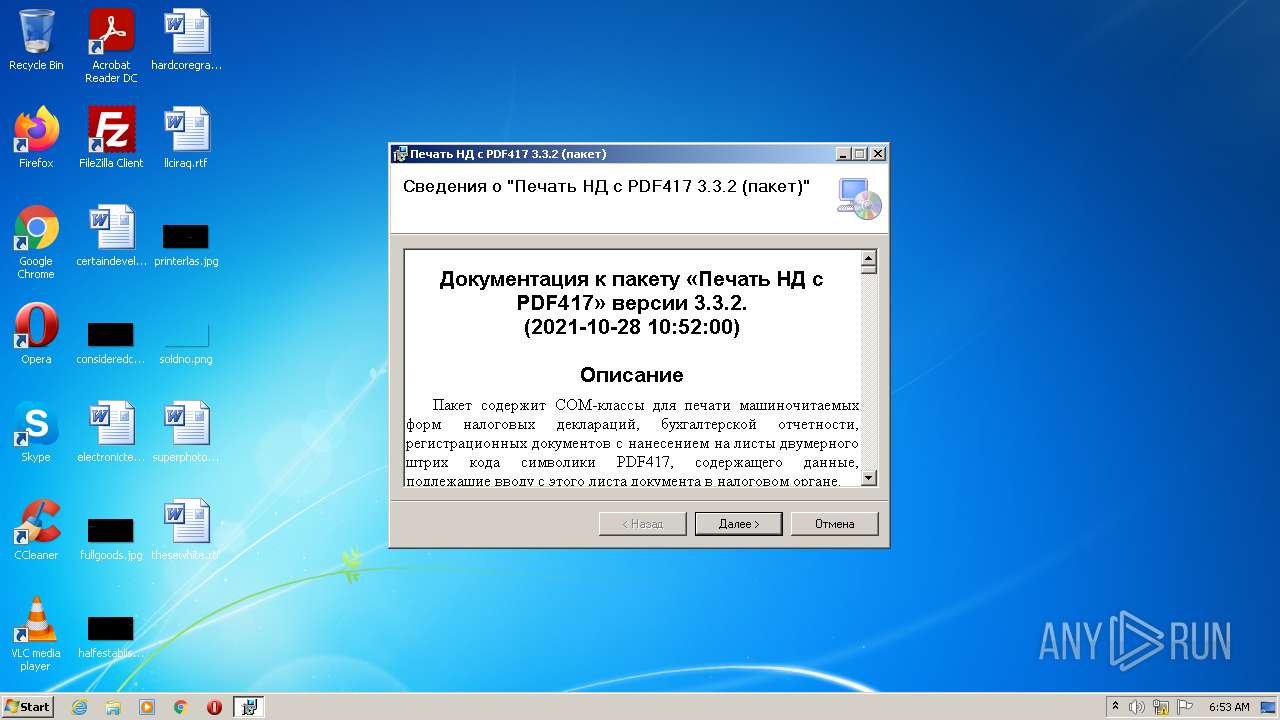
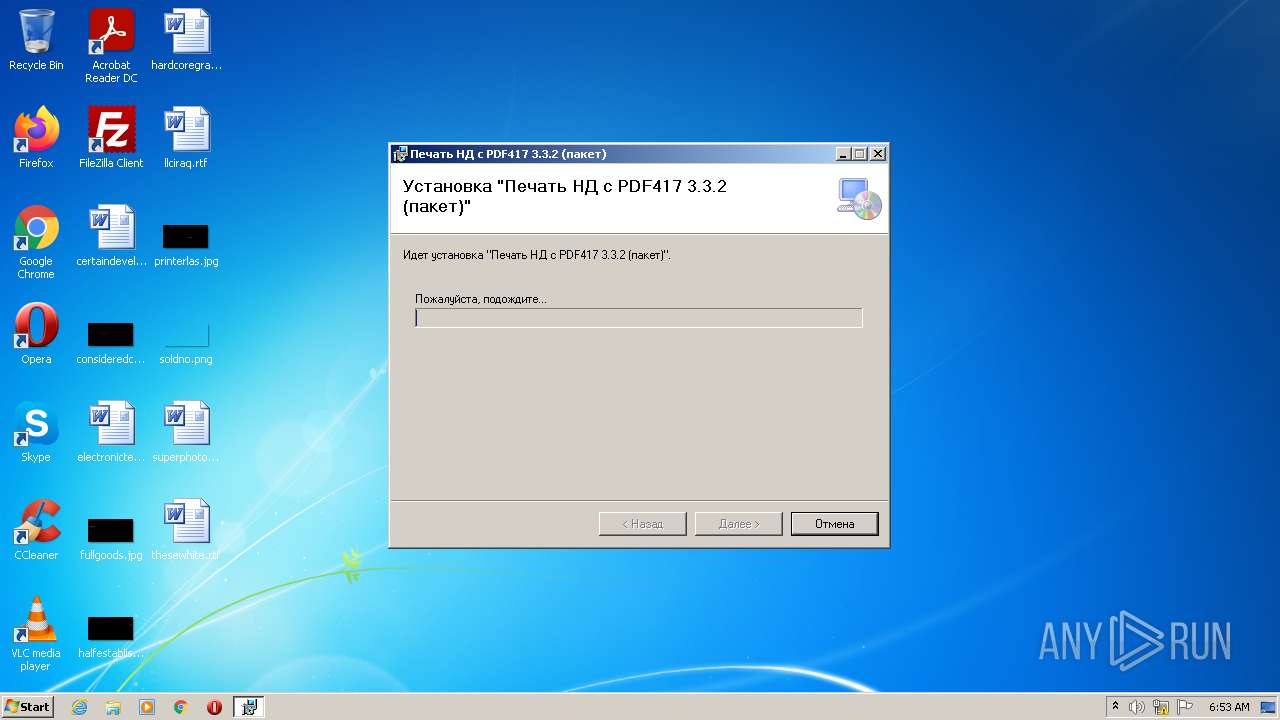
| File name: | Печать НД с PDF417(3.3.2).msi |
| Full analysis: | https://app.any.run/tasks/b1a6d1f0-9829-492a-aed5-672ed75ddcd1 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 05:53:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Create Time/Date: Mon Jun 21 08:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1251, Template: Intel;1049, Number of Pages: 200, Revision Number: {960DC5F6-8C21-4211-9AE3-619BA8656BD7}, Title: PDF417, Author: , Comments: - PDF417, Number of Words: 2, Last Saved Time/Date: Thu Oct 28 15:21:14 2021, Last Printed: Thu Oct 28 15:21:14 2021 |
| MD5: | E85DBA1288DA3DC9A7CB02B436B3ABC4 |
| SHA1: | A21EB055C3F724E7E69AFA6F4C4E6B83F19A169E |
| SHA256: | 8E975674713B5090AE92515EF8BA608EE29D2B9F8584003256E5AD252F9C202E |
| SSDEEP: | 98304:lyx7I/NaWlyEnr2/wwAmG2+unZN2hNYgCiba2ApxVEEnXpVOX:l+7I/TyYqiunGNY4baRgunOX |
MALICIOUS
Drops executable file immediately after starts
- msiexec.exe (PID: 2740)
Loads dropped or rewritten executable
- msiexec.exe (PID: 3176)
- MsiExec.exe (PID: 3528)
SUSPICIOUS
Checks supported languages
- msiexec.exe (PID: 2740)
Reads the computer name
- msiexec.exe (PID: 2740)
Reads the Windows organization settings
- msiexec.exe (PID: 3176)
- msiexec.exe (PID: 2740)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3176)
- msiexec.exe (PID: 2740)
Executed as Windows Service
- vssvc.exe (PID: 3884)
Reads Environment values
- vssvc.exe (PID: 3884)
Creates a directory in Program Files
- msiexec.exe (PID: 2740)
Creates files in the Windows directory
- msiexec.exe (PID: 2740)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 2740)
- MsiExec.exe (PID: 3528)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2740)
Drops a file with a compile date too recent
- msiexec.exe (PID: 2740)
Executed via COM
- DllHost.exe (PID: 3440)
INFO
Checks supported languages
- msiexec.exe (PID: 3176)
- vssvc.exe (PID: 3884)
- MsiExec.exe (PID: 3528)
- WINWORD.EXE (PID: 4028)
- WINWORD.EXE (PID: 2192)
- DllHost.exe (PID: 3440)
Reads the computer name
- msiexec.exe (PID: 3176)
- vssvc.exe (PID: 3884)
- MsiExec.exe (PID: 3528)
- WINWORD.EXE (PID: 4028)
- WINWORD.EXE (PID: 2192)
- DllHost.exe (PID: 3440)
Creates files in the program directory
- msiexec.exe (PID: 2740)
Application launched itself
- msiexec.exe (PID: 2740)
Loads dropped or rewritten executable
- msiexec.exe (PID: 2740)
Manual execution by user
- WINWORD.EXE (PID: 4028)
- WINWORD.EXE (PID: 2192)
Creates a software uninstall entry
- msiexec.exe (PID: 2740)
Creates files in the user directory
- WINWORD.EXE (PID: 4028)
- WINWORD.EXE (PID: 2192)
Searches for installed software
- msiexec.exe (PID: 2740)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2192)
- WINWORD.EXE (PID: 4028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2021:10:28 14:21:14 |
|---|---|
| ModifyDate: | 2021:10:28 14:21:14 |
| Words: | 2 |
| Comments: | Печать налоговых документов со штрих-кодом PDF417 |
| Keywords: | - |
| Author: | АО «ГНИВЦ» |
| Subject: | - |
| Title: | Печать НД с PDF417 |
| RevisionNumber: | {960DC5F6-8C21-4211-9AE3-619BA8656BD7} |
| Pages: | 200 |
| Template: | Intel;1049 |
| CodePage: | Windows Cyrillic |
| Security: | Password protected |
| Software: | Windows Installer |
| CreateDate: | 1999:06:21 07:00:00 |
Total processes
45
Monitored processes
7
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\superphotos.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2740 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3176 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Печать НД с PDF417(3.3.2).msi" | C:\Windows\System32\msiexec.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3440 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3528 | "C:\Windows\system32\MsiExec.exe" /Y "C:\Program Files\gnivc\print-nd-pdf417\TAXDOCPrt.dll" | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3884 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4028 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\thesewhite.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
8 386
Read events
7 050
Write events
1 024
Delete events
312
Modification events
| (PID) Process: | (2740) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000C0DB4C32EA89D801B40A000060010000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2740) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000C0DB4C32EA89D801B40A000060010000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2740) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (2740) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000005A899B32EA89D801B40A000060010000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2740) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005A899B32EA89D801B40A0000F8080000E8030000010000000000000000000000E354B7CF30F9864485D02E1B5698D6350000000000000000 | |||
| (PID) Process: | (3884) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000068B0A232EA89D8012C0F000010080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3884) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000068B0A232EA89D8012C0F0000C40E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3884) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000068B0A232EA89D8012C0F0000FC070000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3884) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000068B0A232EA89D8012C0F0000FC0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3884) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000001C75A732EA89D8012C0F0000FC0F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
10
Suspicious files
10
Text files
2
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2740 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2740 | msiexec.exe | C:\Windows\Installer\f9784.msi | — | |
MD5:— | SHA256:— | |||
| 2740 | msiexec.exe | C:\Windows\Installer\f9785.ipi | binary | |
MD5:— | SHA256:— | |||
| 2740 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF2AB4B16F605FB677.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2740 | msiexec.exe | C:\Windows\Installer\MSI9C18.tmp | binary | |
MD5:— | SHA256:— | |||
| 2740 | msiexec.exe | C:\Windows\Installer\f9787.msi | — | |
MD5:— | SHA256:— | |||
| 2740 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{cfb754e3-f930-4486-85d0-2e1b5698d635}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 2740 | msiexec.exe | C:\Program Files\gnivc\print-nd-pdf417\-problem.zip | compressed | |
MD5:— | SHA256:— | |||
| 2740 | msiexec.exe | C:\Program Files\gnivc\print-nd-pdf417\-test.zip | compressed | |
MD5:— | SHA256:— | |||
| 2740 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report