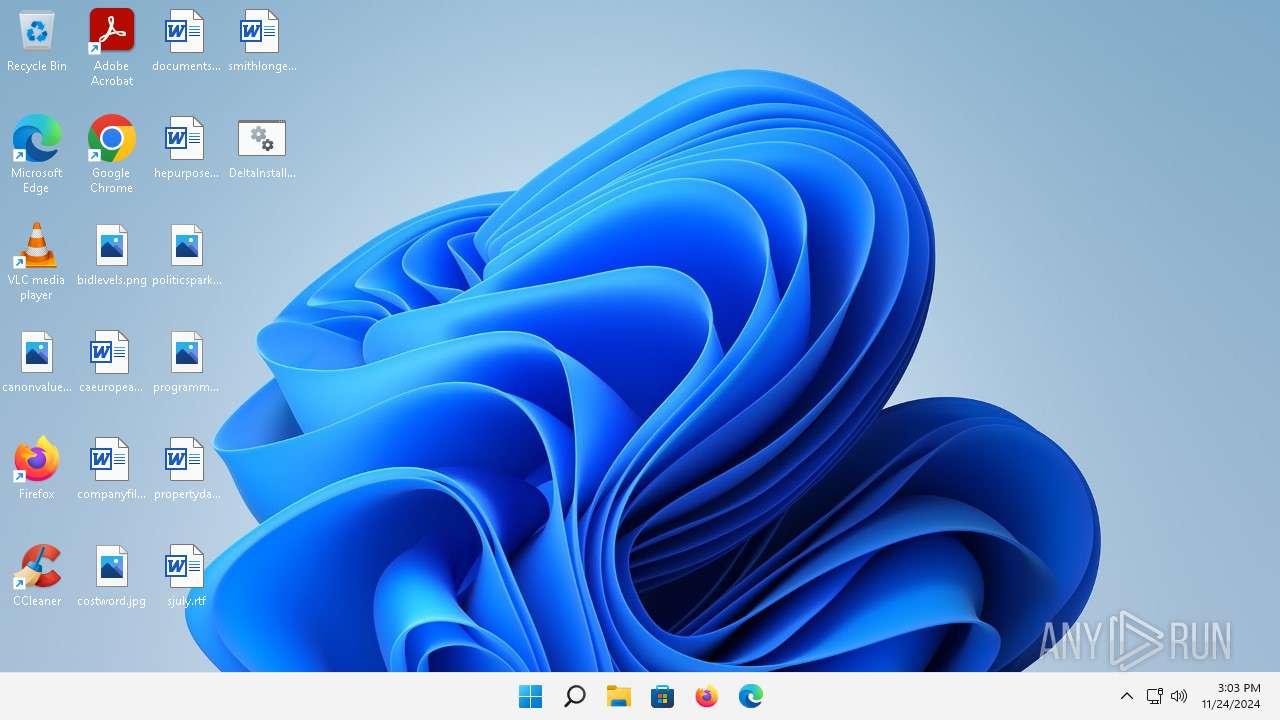
| File name: | DeltaInstaller.bat |
| Full analysis: | https://app.any.run/tasks/08bd12bc-5a0b-499a-aab7-aa41be2fb225 |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2024, 15:03:45 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 51DFCD466DC358D53AF79757929DE943 |
| SHA1: | DFD5CCB39B0D29597431885A1CE2B13EF28913B8 |
| SHA256: | 8E87EAA40D7E13010E91BA80605DC367F4AF43B71ADF9D9452D659828F867446 |
| SSDEEP: | 12:wpzHipHmMSI88dfKLerEtm0yy5No9kj2rxvbHVQ:wpzHOeI8sfJ0yb20BHVQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- cmd.exe (PID: 4012)
- wscript.exe (PID: 1832)
The process executes VB scripts
- cmd.exe (PID: 4012)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 4012)
- cmd.exe (PID: 1484)
Executing commands from a ".bat" file
- wscript.exe (PID: 1832)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1832)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1832)
INFO
The process uses the downloaded file
- wscript.exe (PID: 1832)
- cmd.exe (PID: 4012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
118
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1380 | "C:\Windows\system32\cacls.exe" "C:\Windows\system32\config\system" | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1484 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\Desktop\DELTAI~1.BAT | C:\Windows\System32\cmd.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
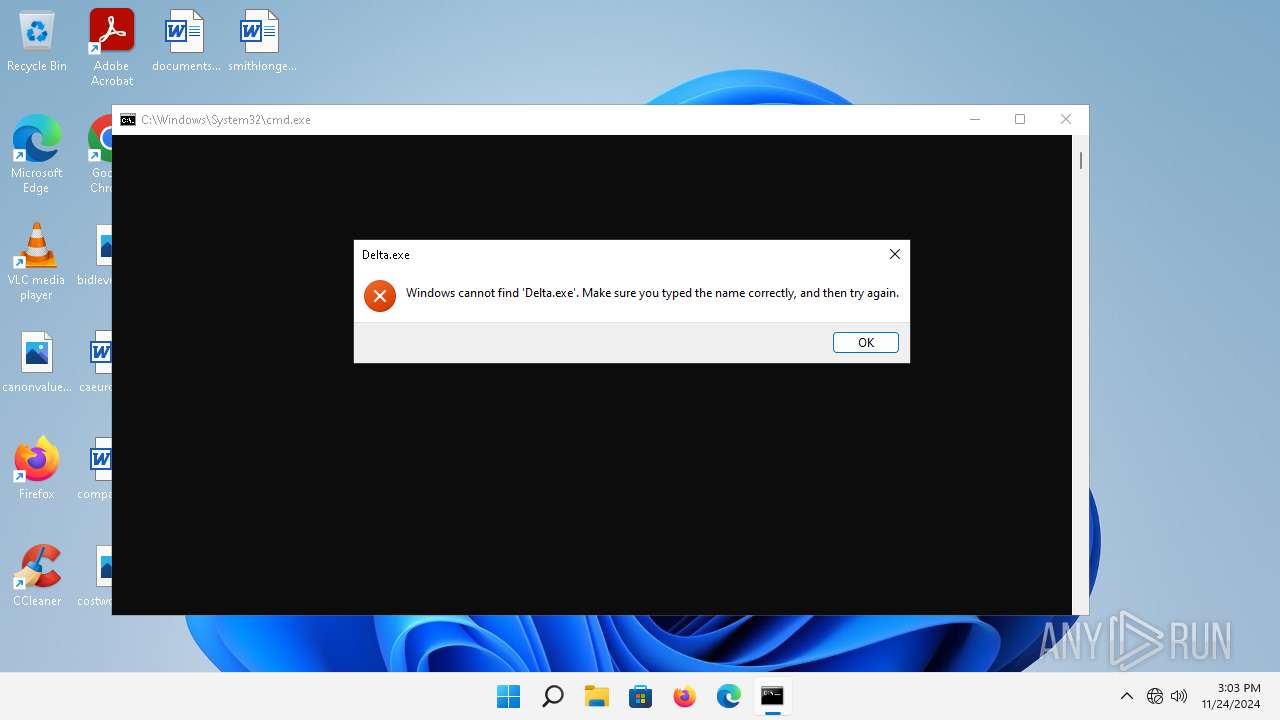
| 1832 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\getadmin.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4012 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\DeltaInstaller.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4652 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6468 | "C:\Windows\system32\cacls.exe" "C:\Windows\system32\config\system" | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 5 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6900 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 940
Read events
1 918
Write events
22
Delete events
0
Modification events
| (PID) Process: | (4012) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\ApplicationAssociationToasts |
| Operation: | write | Name: | VBSFile_.vbs |
Value: 0 | |||
| (PID) Process: | (4012) cmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\System32\WScript.exe.FriendlyAppName |
Value: Microsoft ® Windows Based Script Host | |||
| (PID) Process: | (4012) cmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\System32\WScript.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (4012) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (4012) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4012) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4012) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4012) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1832) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1832) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4012 | cmd.exe | C:\Users\admin\AppData\Local\Temp\getadmin.vbs | text | |
MD5:D14A6C18536B08C2D91CC10129CEC2CA | SHA256:88F0E55BE41422957E8F4FEC8CAF0F9ED4E68D1F0290171BA8F4BD26C19FA17D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
26
DNS requests
29
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 23.53.40.49:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9a41b9a9770e1e93 | unknown | — | — | whitelisted |
1296 | svchost.exe | GET | 200 | 23.55.161.133:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
3124 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
3124 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
3124 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
3124 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.213.168.137:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
3124 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2860 | svchost.exe | GET | 200 | 217.20.57.25:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?8a3f5205275d40c7 | unknown | — | — | whitelisted |
2860 | svchost.exe | GET | 304 | 217.20.57.25:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?47af650c0811ccc6 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3124 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
3124 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
1296 | svchost.exe | 23.55.161.133:80 | — | Akamai International B.V. | DE | unknown |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.49:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
— | — | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ecs.office.com |
| whitelisted |
r10.o.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1296 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |