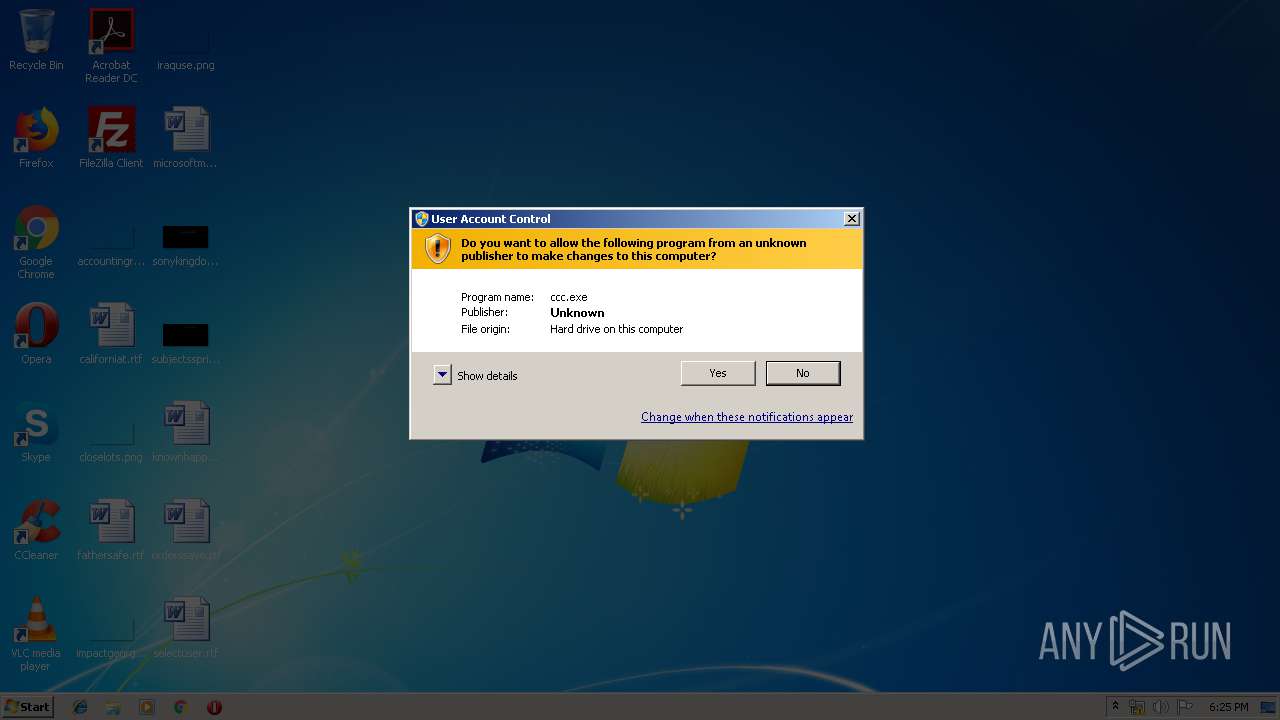
| File name: | ccc.exe |
| Full analysis: | https://app.any.run/tasks/6ac62dc8-52b6-4d78-be6a-38b05d9e41ef |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2019, 17:25:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 50A48A9069C49A3620198B66DCE6748D |
| SHA1: | B801ECE3FDADF3EED4E69D8A4FE0EB8C1007522F |
| SHA256: | 8E8276E18D3A2A84AB4D8E214F2379A0D456D2F0DAB4C4E6E15F4E46A889A3D7 |
| SSDEEP: | 3072:Cd9xR3G2BZMbBLBaYw0coLujNHCd8pFhcbX2t025zWdgI:Cd93ZBZMbqYgomHCdiF2D2tTRY |
MALICIOUS
Application was dropped or rewritten from another process
- NIRCMD.COM (PID: 1656)
SUSPICIOUS
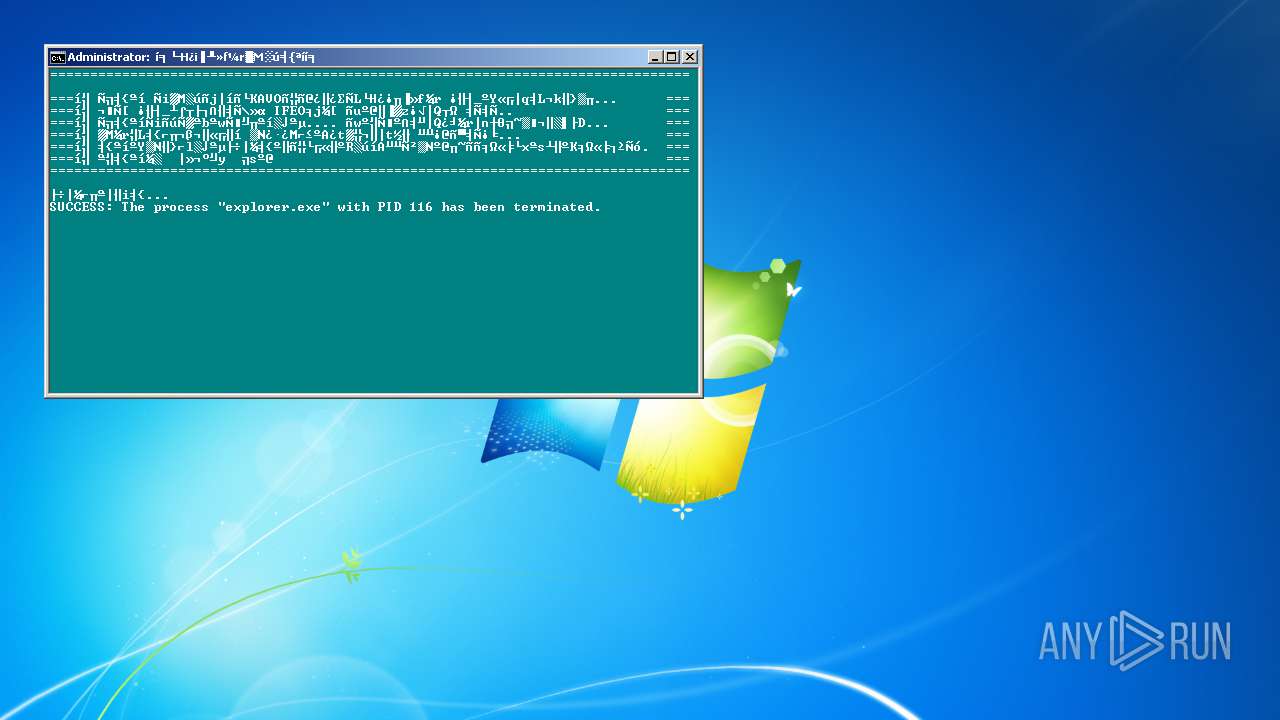
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 2116)
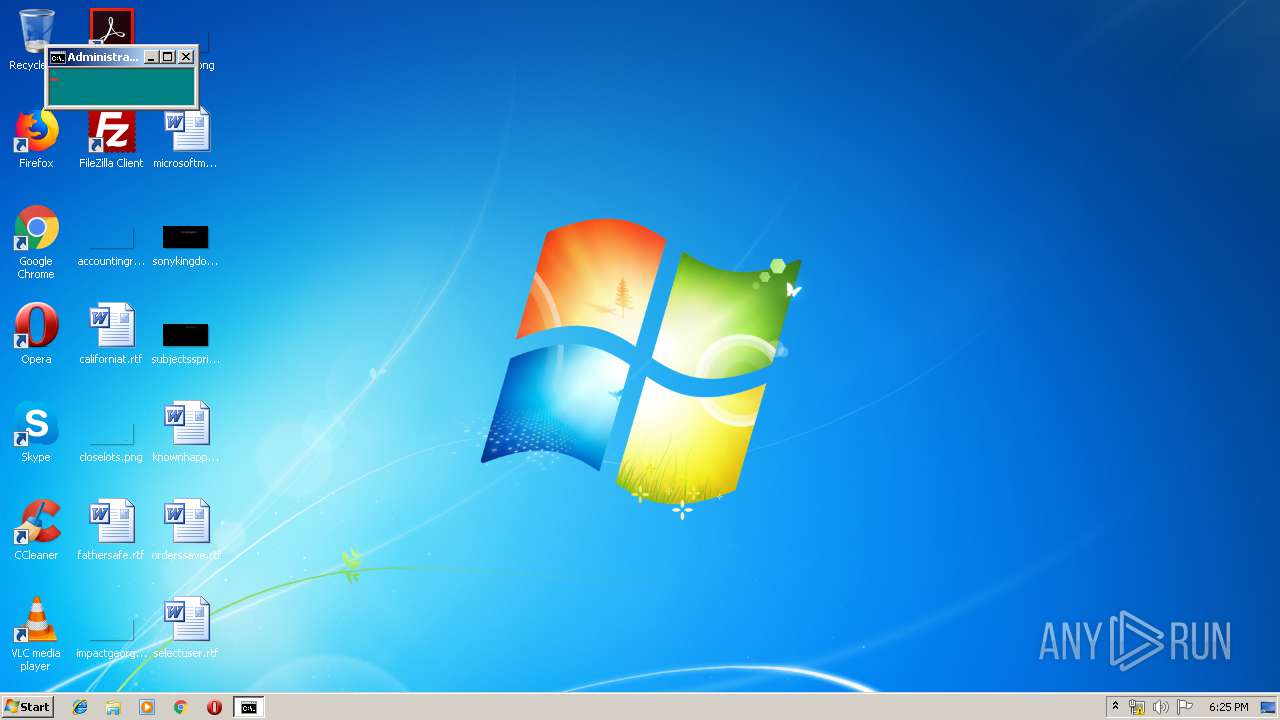
Starts CMD.EXE for commands execution
- ccc.exe (PID: 3740)
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 2116)
Executable content was dropped or overwritten
- ccc.exe (PID: 3740)
Starts application with an unusual extension
- cmd.exe (PID: 2116)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2116)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.8) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:09:13 20:20:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 77824 |
| InitializedDataSize: | 29184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Sep-2006 18:20:14 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 13-Sep-2006 18:20:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013000 | 0x00012E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46788 |
.data | 0x00014000 | 0x00007000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.75622 |
.idata | 0x0001B000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05399 |
.rsrc | 0x0001C000 | 0x00005748 | 0x00005800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94484 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.5 | 4 | Latin 1 / Western European | Chinese - PRC | UNKNOWN |
2 | 3.88998 | 1384 | Latin 1 / Western European | Chinese - Taiwan | RT_ICON |
3 | 4.12176 | 744 | Latin 1 / Western European | Chinese - Taiwan | RT_ICON |
4 | 4.68705 | 2216 | Latin 1 / Western European | Chinese - Taiwan | RT_ICON |
7 | 5.31352 | 226 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.70413 | 360 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.51373 | 216 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 4.80037 | 420 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
100 | 2.64576 | 62 | Latin 1 / Western European | Chinese - Taiwan | RT_GROUP_ICON |
101 | 4.19099 | 2998 | Latin 1 / Western European | Chinese - Taiwan | RT_BITMAP |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
54
Monitored processes
17
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | taskkill /F /IM SEVERE.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | taskkill /F /IM wscript.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 456 | taskkill /F /IM explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 936 | taskkill /F /IM OUTLOOK.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1136 | taskkill /F /IM iexplore.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
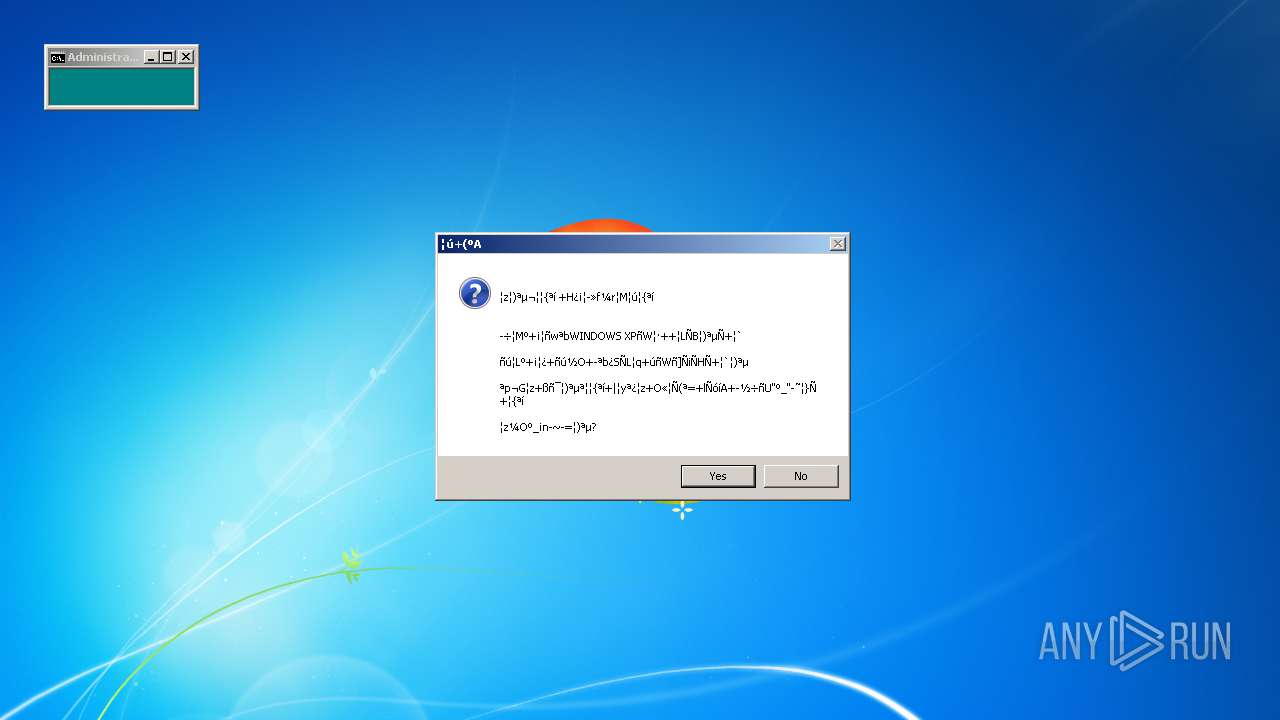
| 1656 | NIRCMD QBOXCOM "~n▒z░⌡ªµ¬║╡{ªí └H¿¡║╨»f¼r▓M░ú╡{ªí~n~n~n┴÷╡Mº┌¡╠ñwªbWINDOWS XPñW┤·╕╒╣LÑB░⌡ªµÑ┐▒`~n~nñú╣Lº┌¡╠¿├ñú½O├╥ªb¿ΣÑL╣q╕úñWñ]ÑiÑHÑ┐▒`░⌡ªµ~n~nªp¬G▒z╛ßñ▀░⌡ªµª╣╡{ªí╖|│yª¿▒z╕Ω«╞Ñ⌠ª≤╖lÑóíA╜╨½÷ñU~qº_~q┬≈╢}Ñ╗╡{ªí~n~n▒z¼Oº_¡n─~─≥░⌡ªµ?~n" "┤ú┐⌠ºA" returnval 1 | c:\ccc\NIRCMD.COM | — | cmd.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: NirCmd Exit code: 1 Version: 2.15 Modules
| |||||||||||||||
| 1860 | more c:\Temp.file | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1892 | ping -w 1 -n 5 127.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2116 | cmd /c ""C:\ccc\ccc.bat" " | C:\Windows\system32\cmd.exe | — | ccc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2888 | taskkill /F /IM msnmsgr.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
81
Read events
74
Write events
7
Delete events
0
Modification events
| (PID) Process: | (3740) ccc.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | c%%ccc% |
Value: c:\ccc\ | |||
| (PID) Process: | (3740) ccc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3740) ccc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3740) ccc.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-500\Software\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files%WinRAR |
Value: C:\Program Files\WinRAR | |||
| (PID) Process: | (3740) ccc.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-500\Software\WinRAR SFX |
| Operation: | write | Name: | c%%ccc% |
Value: c:\ccc\ | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3740 | ccc.exe | C:\ccc\ccc.bat | text | |
MD5:— | SHA256:— | |||
| 3740 | ccc.exe | C:\ccc\NIRCMD.COM | executable | |
MD5:— | SHA256:— | |||
| 2116 | cmd.exe | C:\Temp.file | text | |
MD5:— | SHA256:— | |||
| 3740 | ccc.exe | C:\Users\Administrator\NTUSER.DAT | hiv | |
MD5:— | SHA256:— | |||
| 3740 | ccc.exe | C:\Users\Administrator\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
| 3740 | ccc.exe | C:\ccc\nircmd.exe | executable | |
MD5:— | SHA256:— | |||
| 3740 | ccc.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat | hiv | |
MD5:— | SHA256:— | |||
| 3740 | ccc.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1 | log | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report