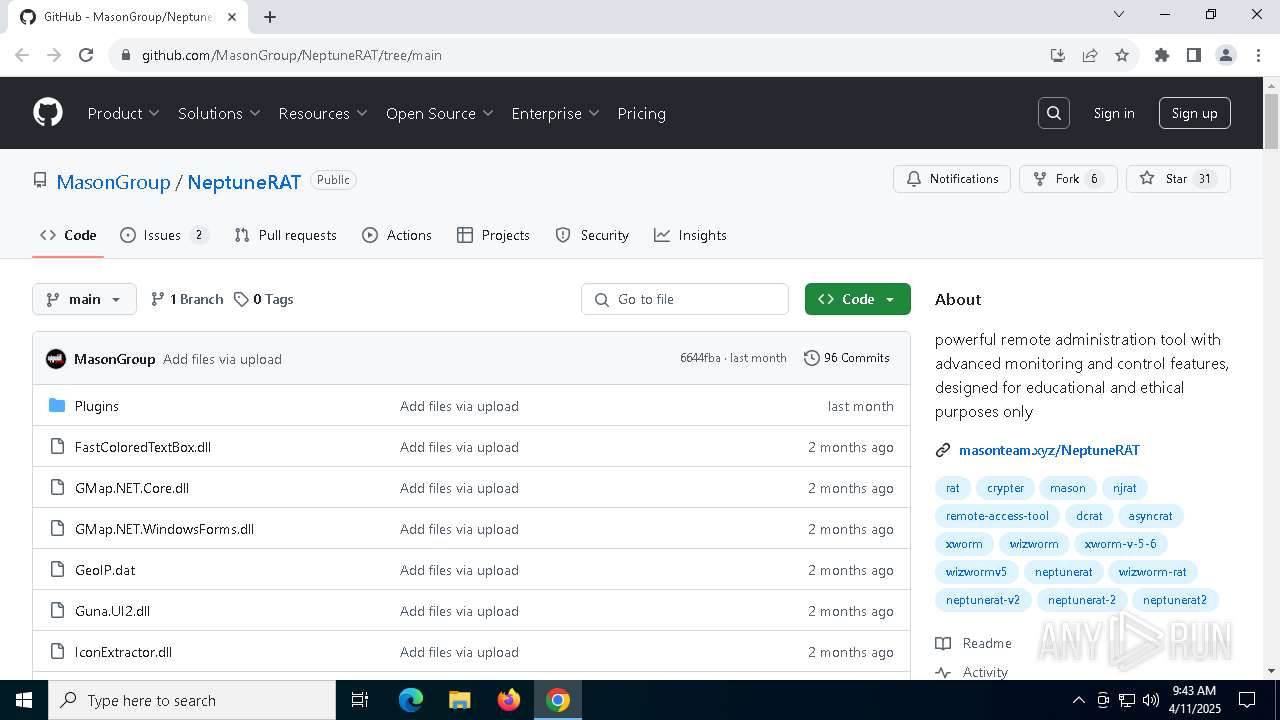
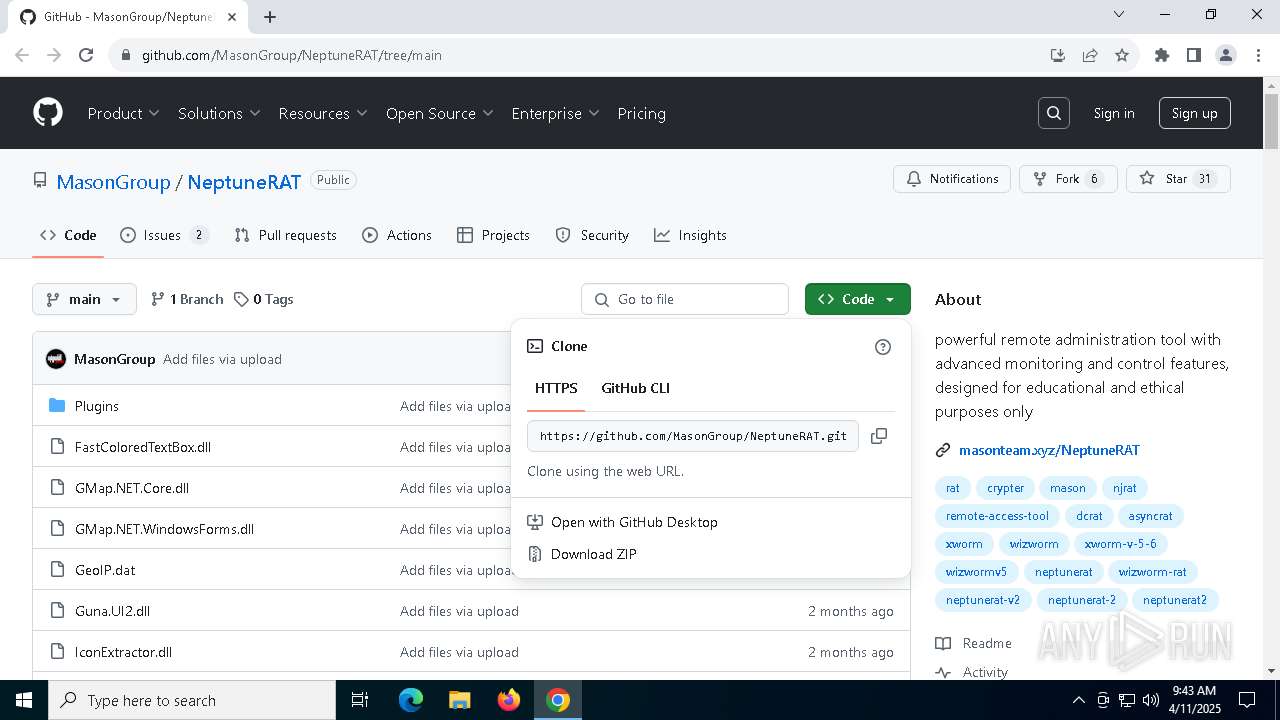
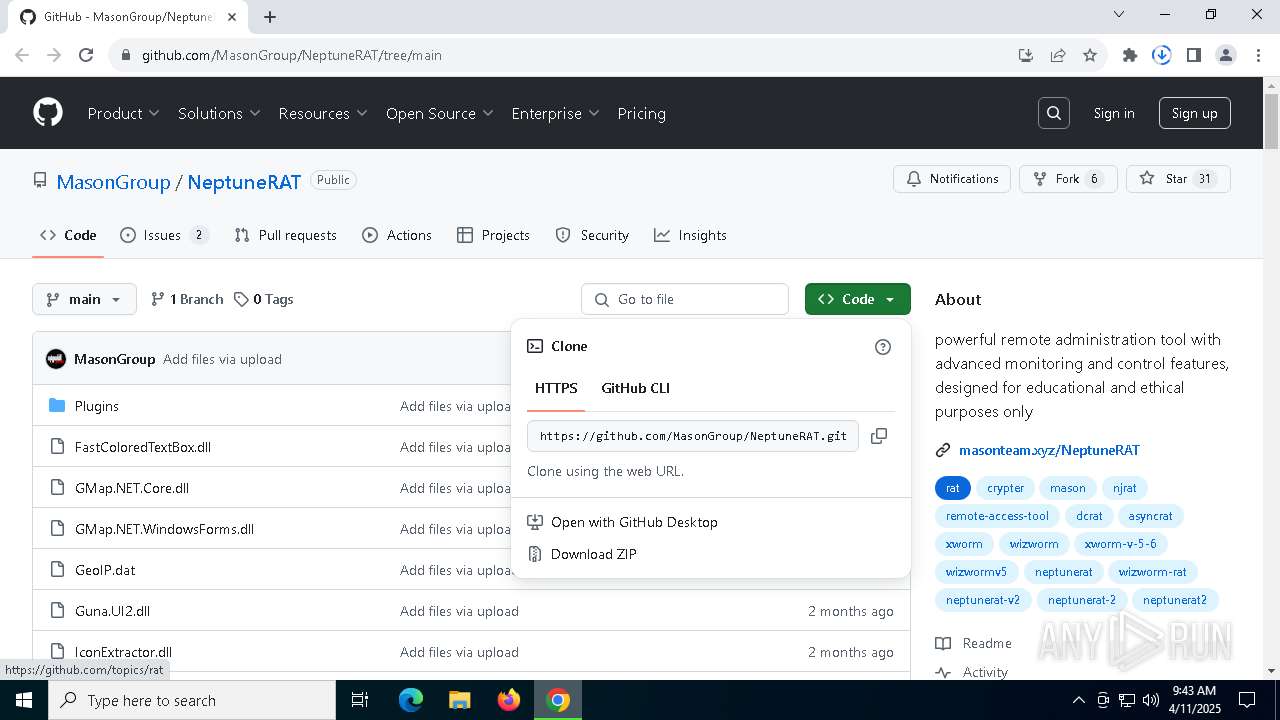
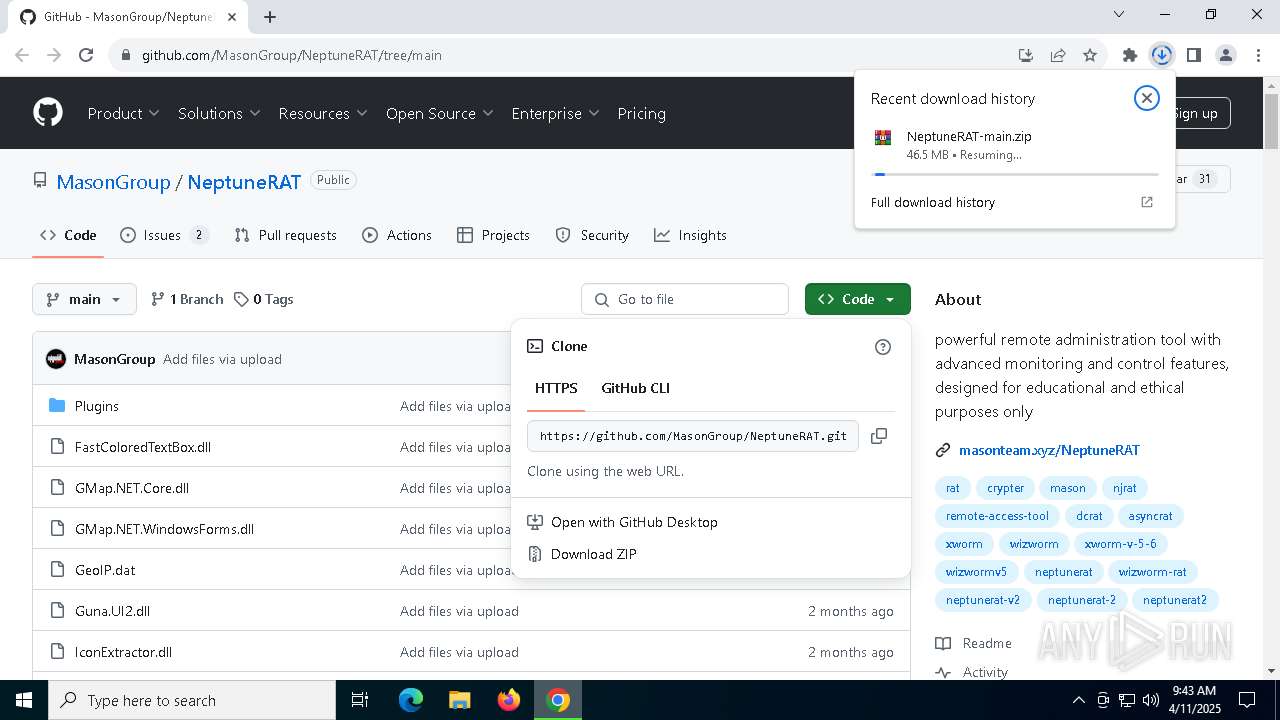
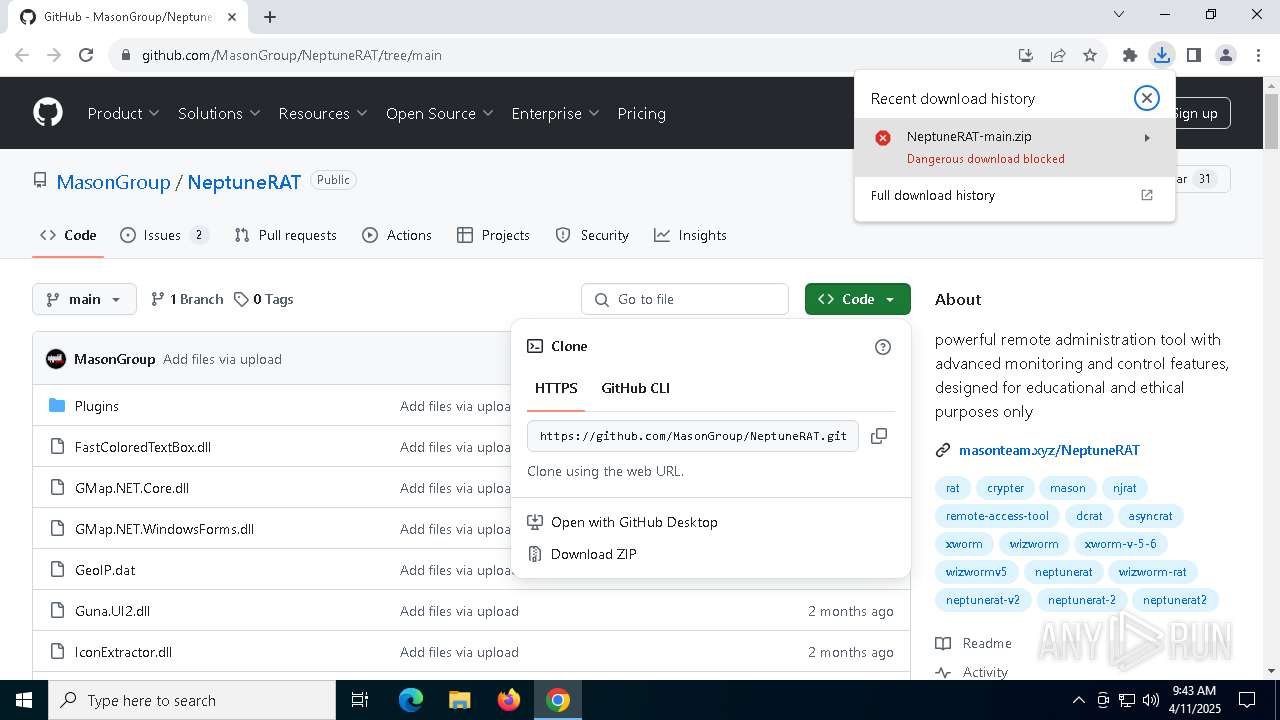
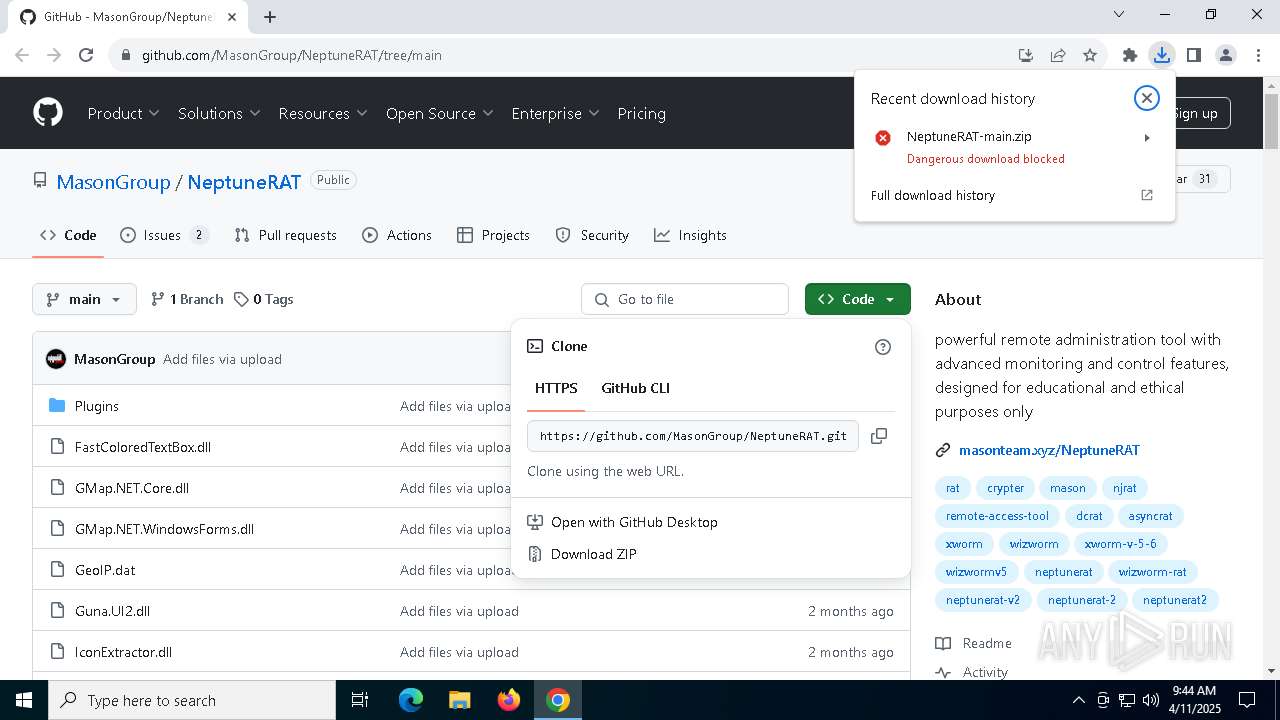
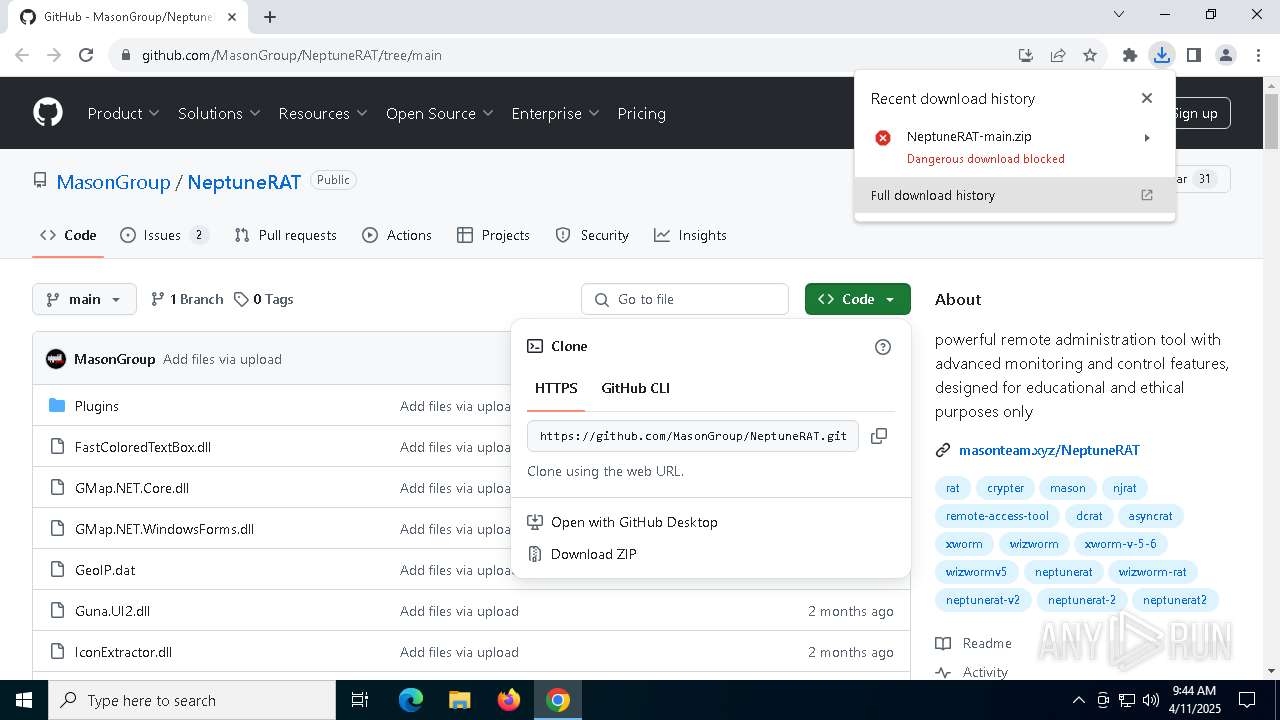
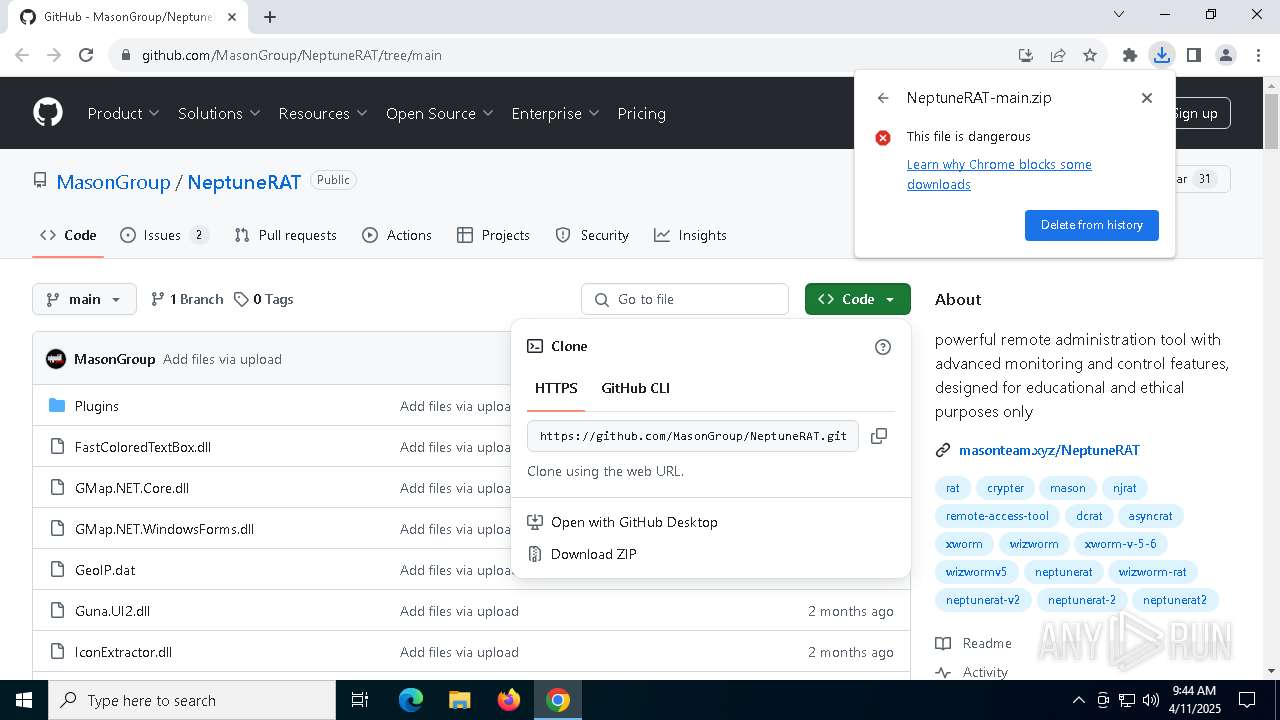
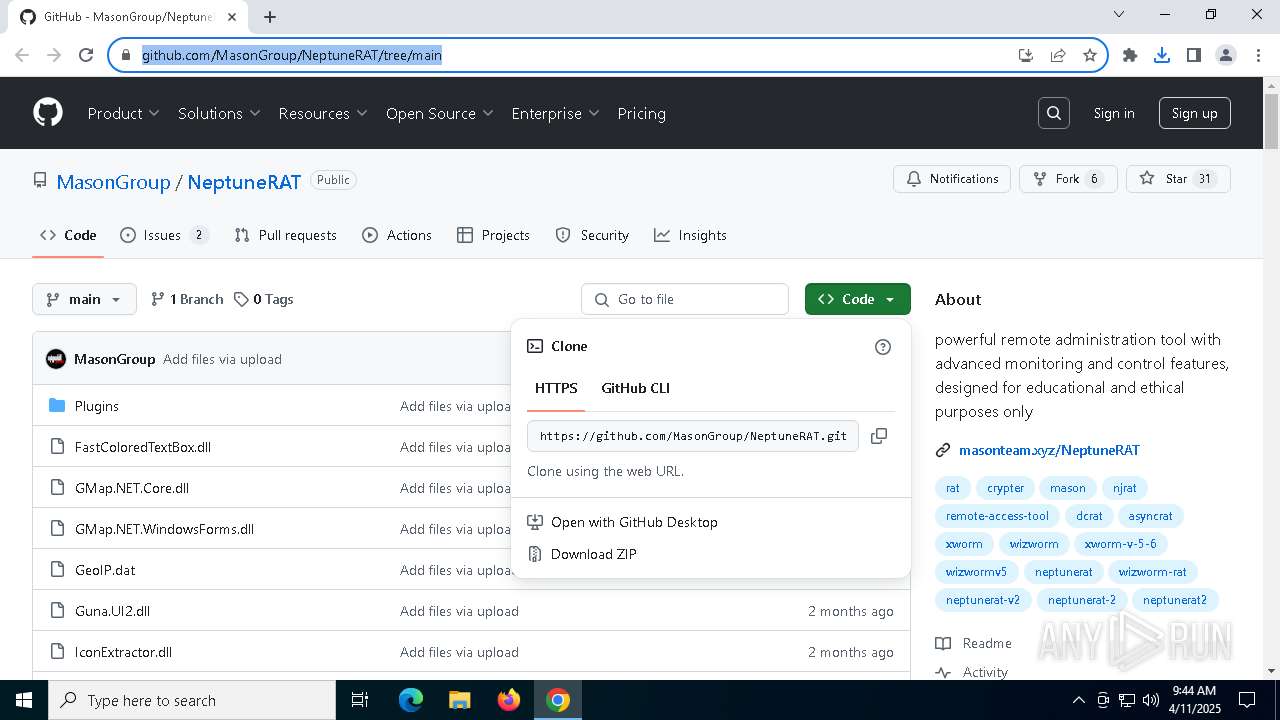
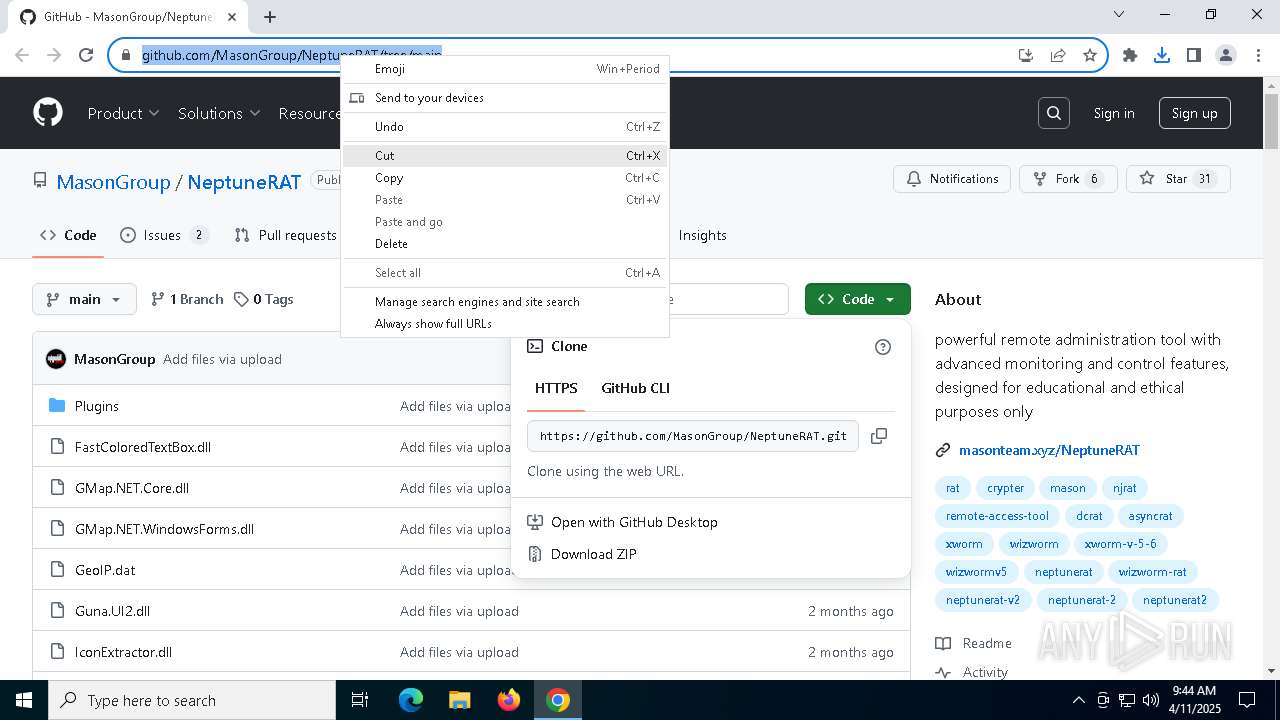
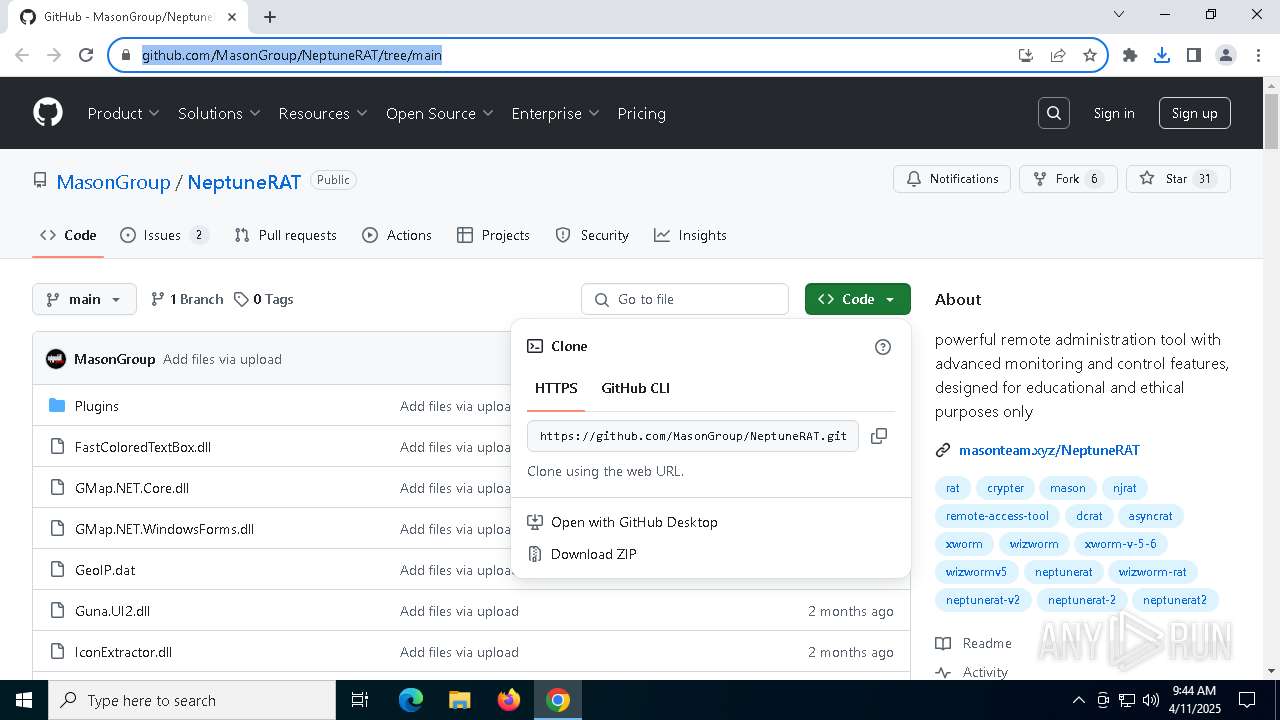
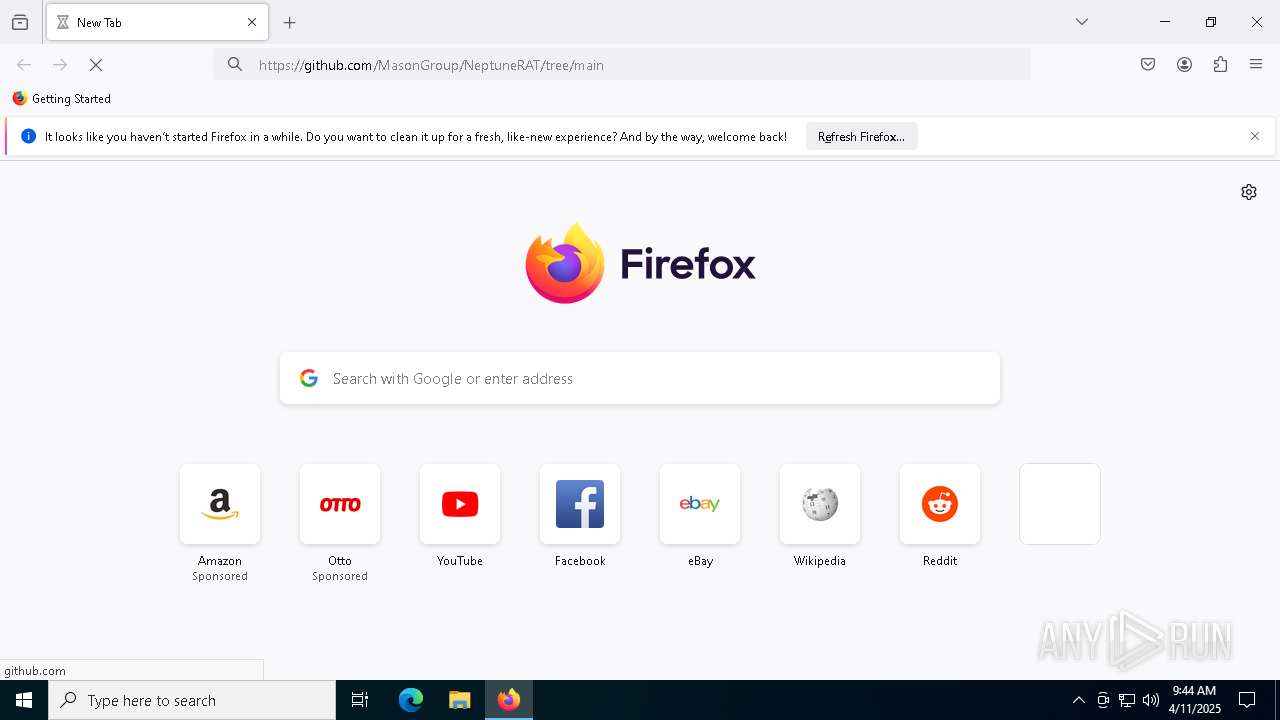
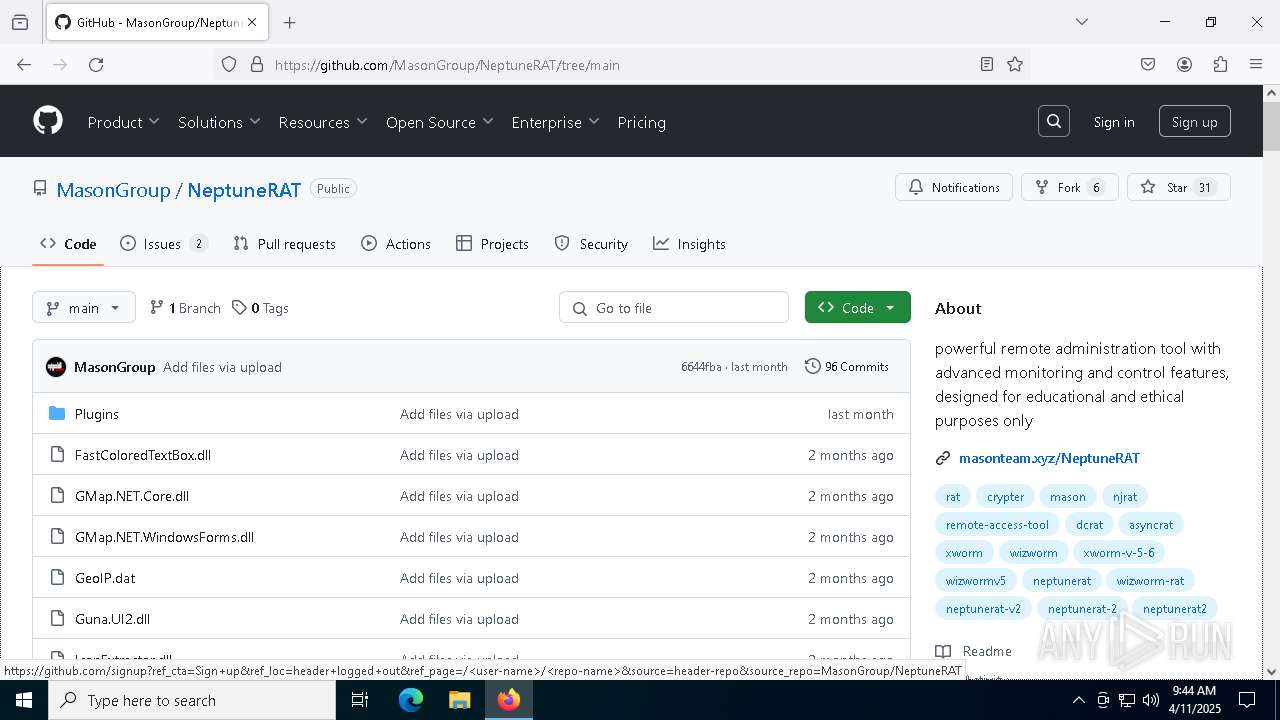
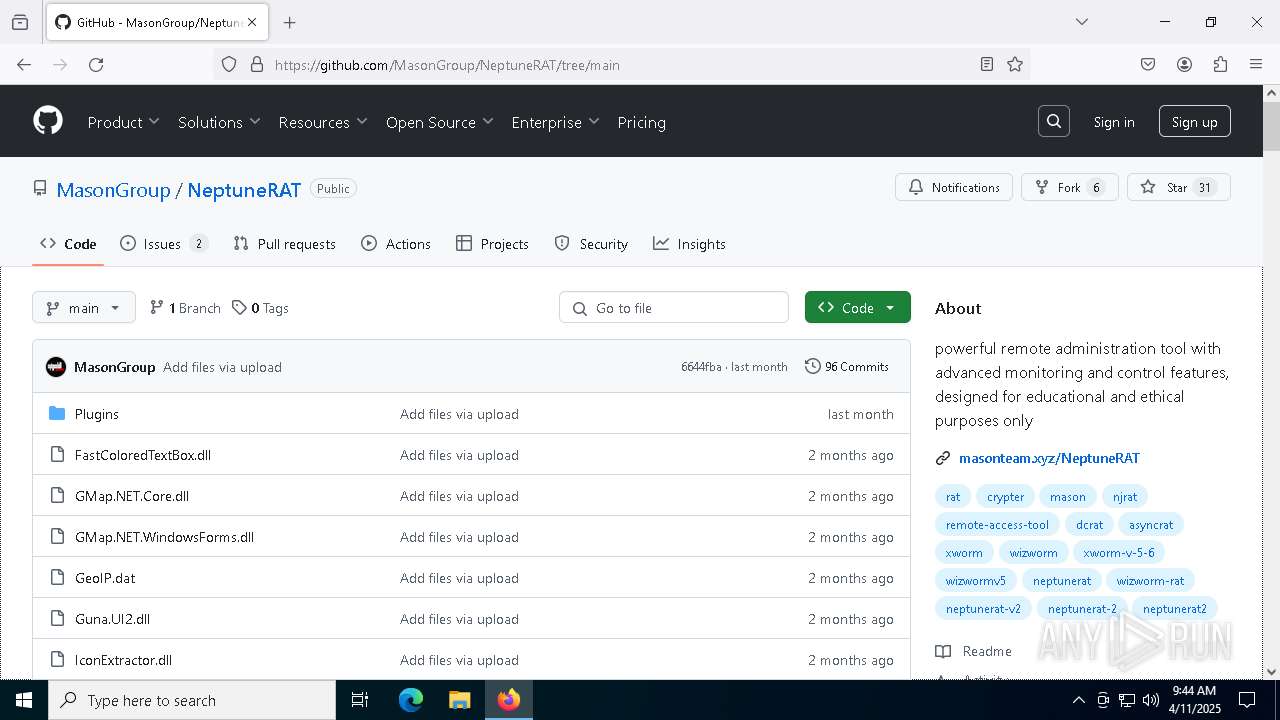
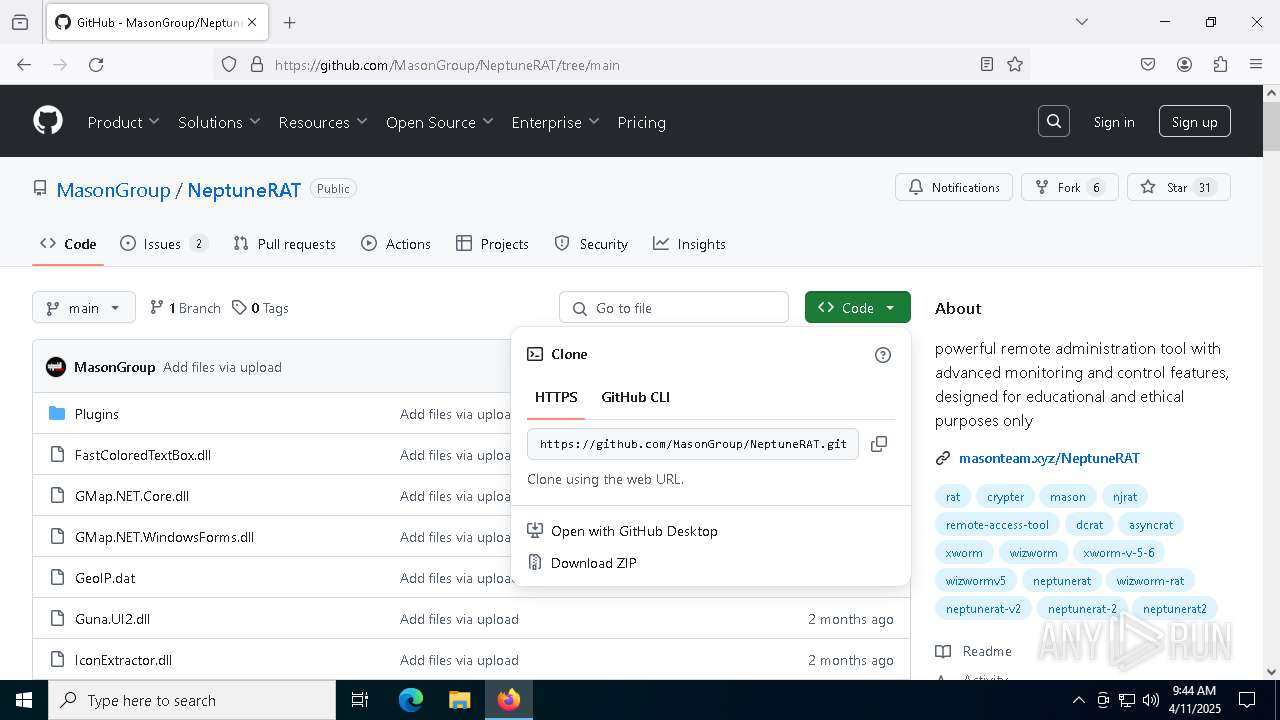
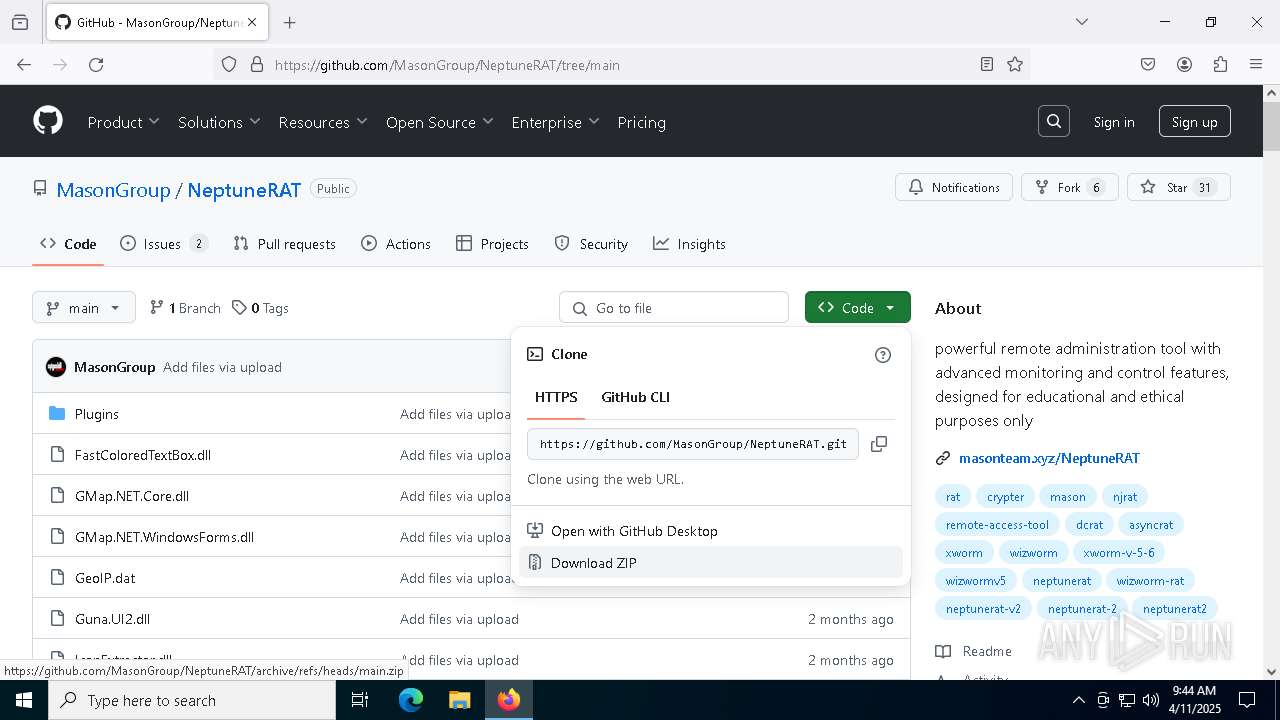
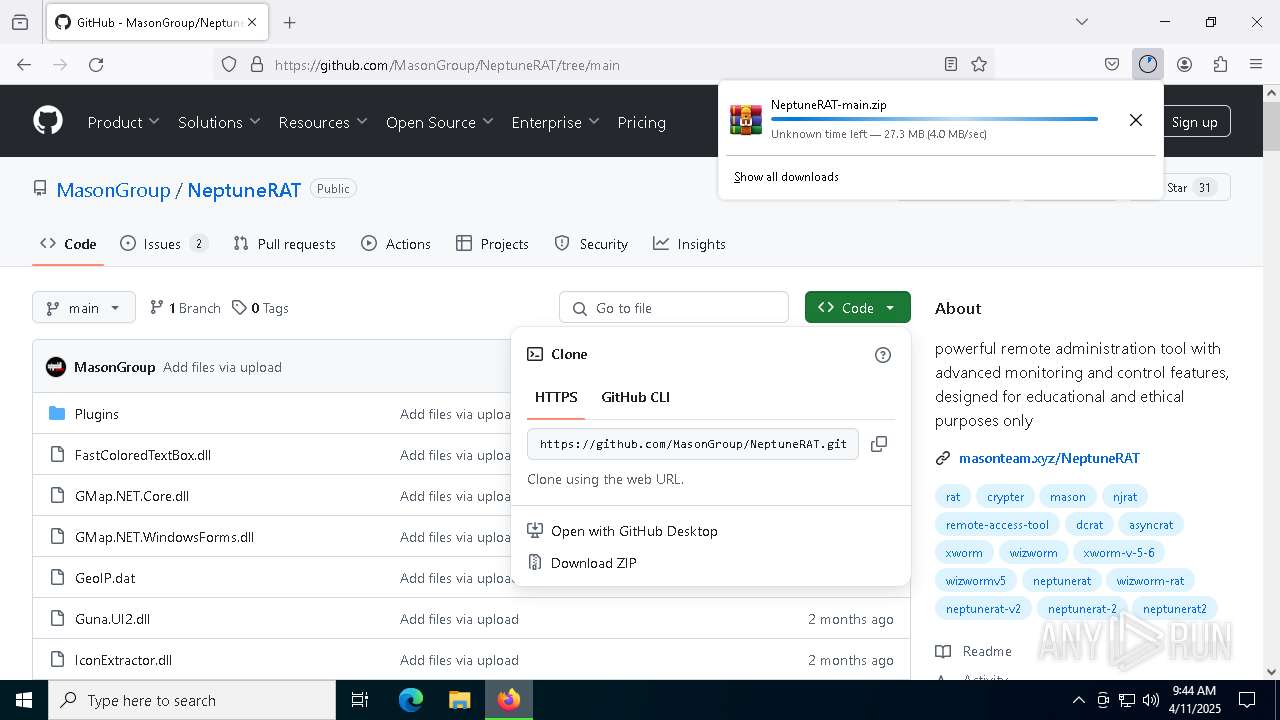
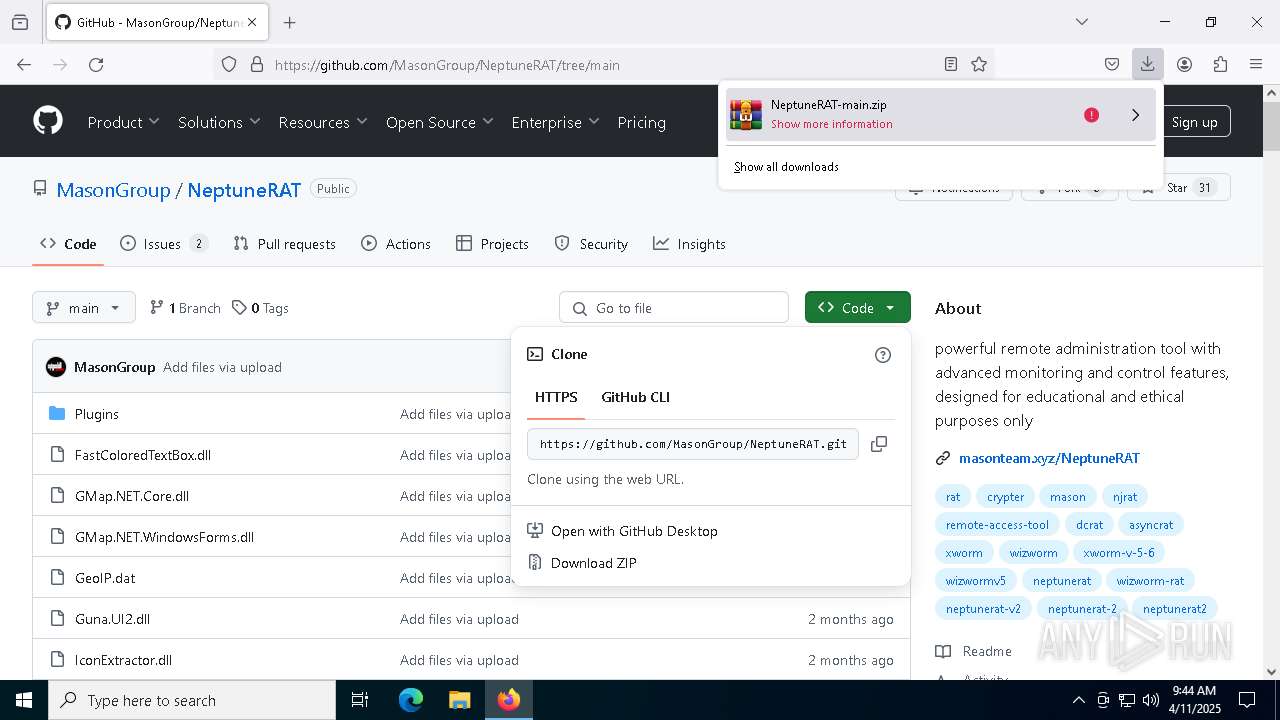
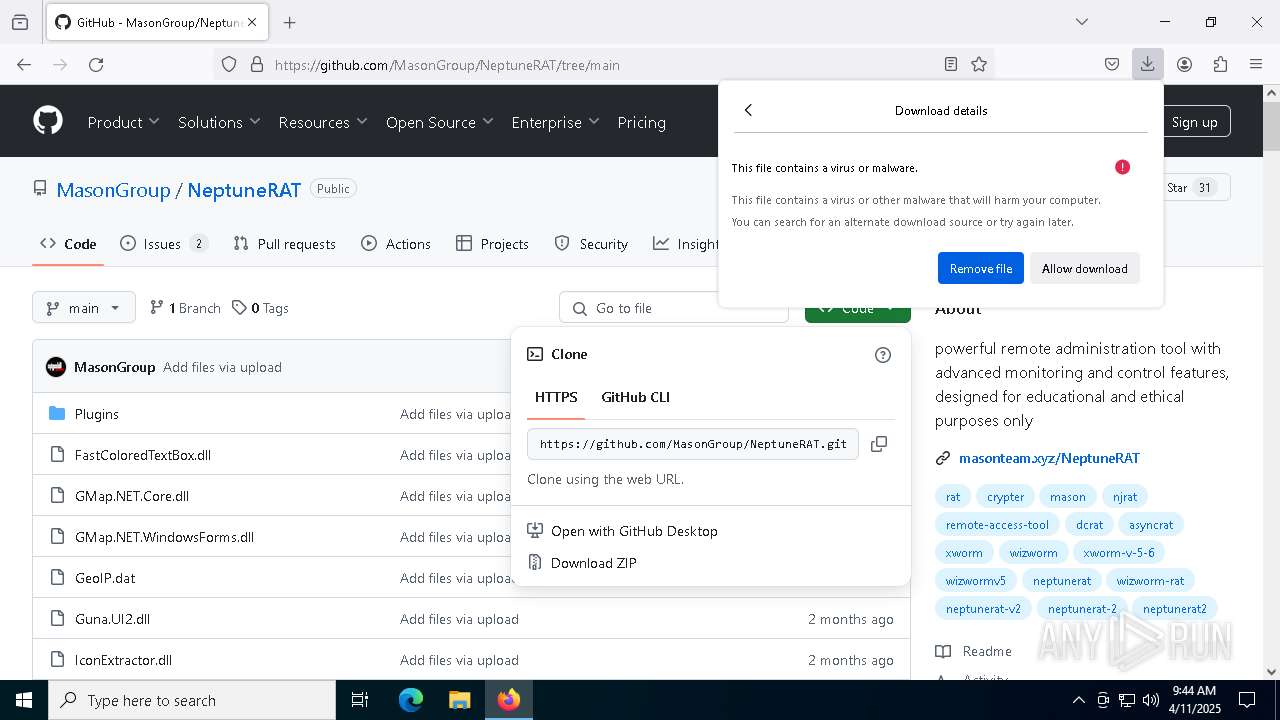
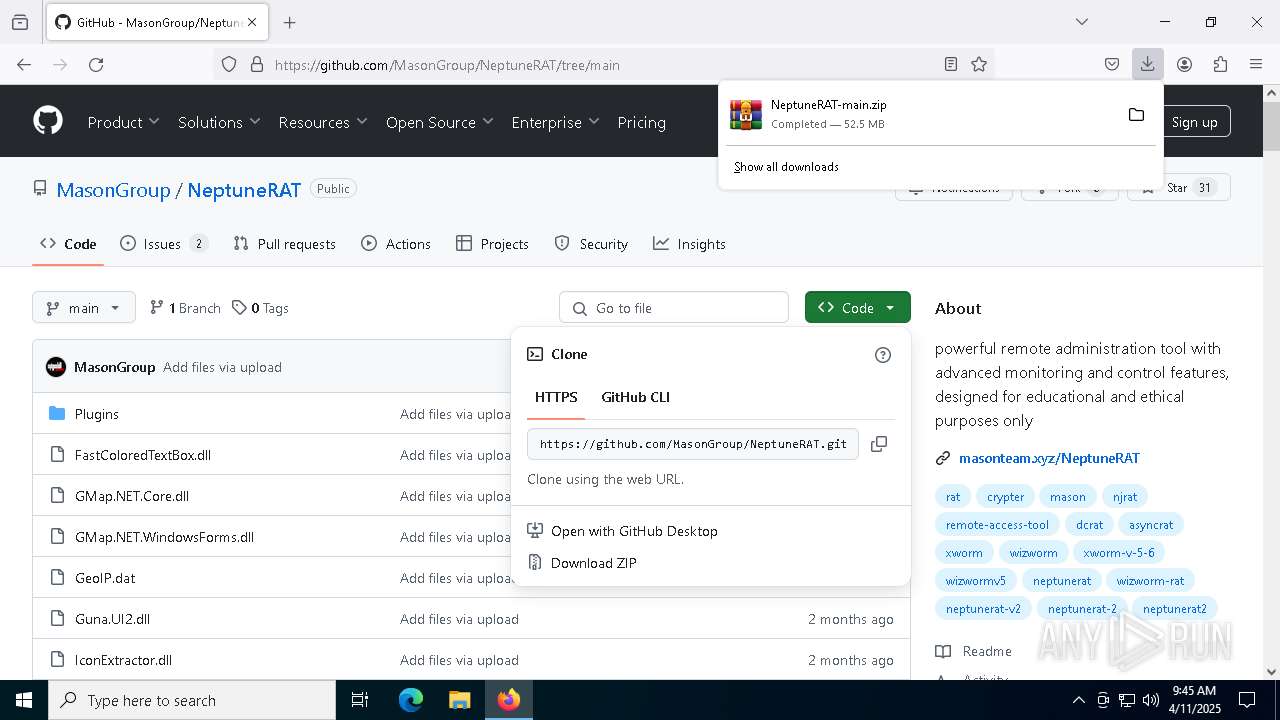
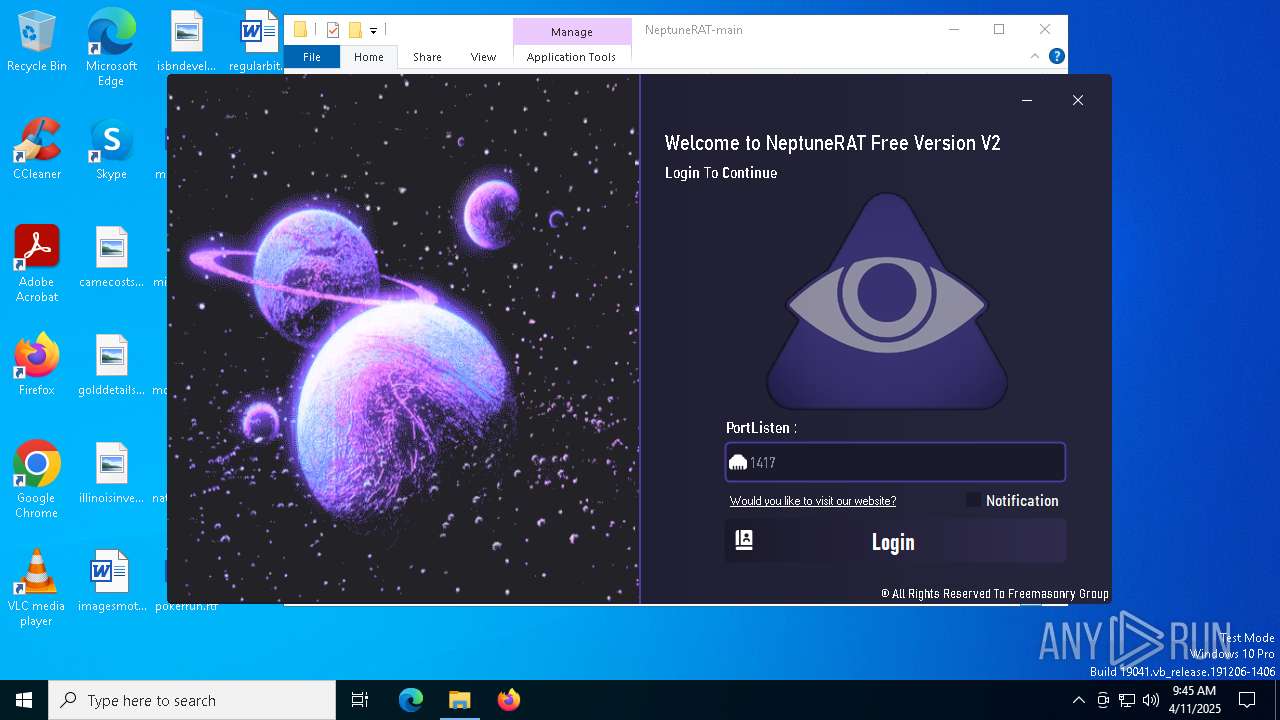
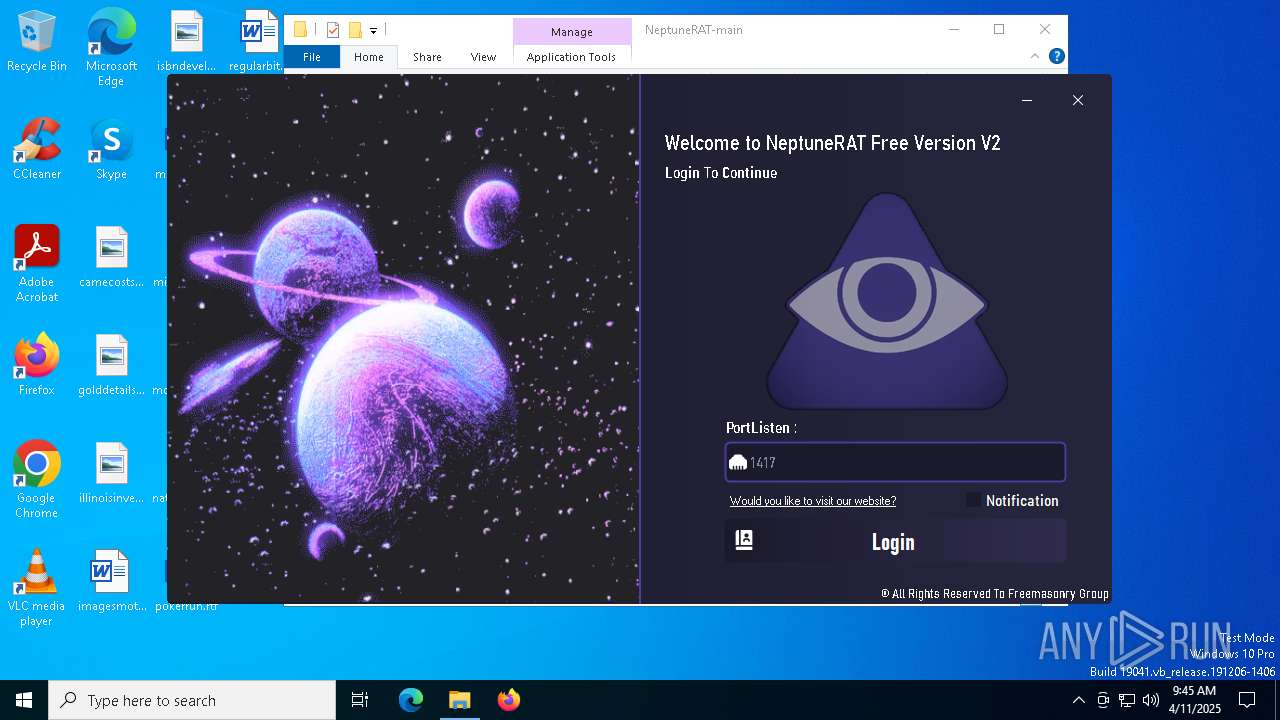
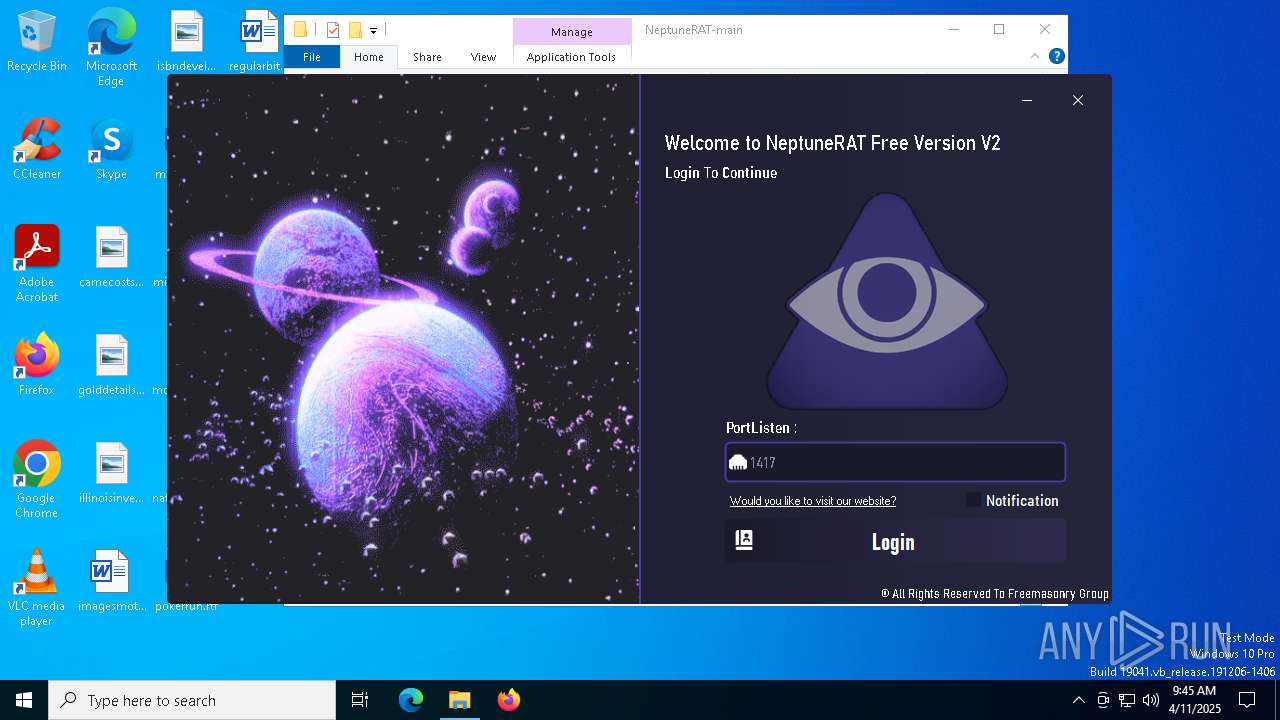
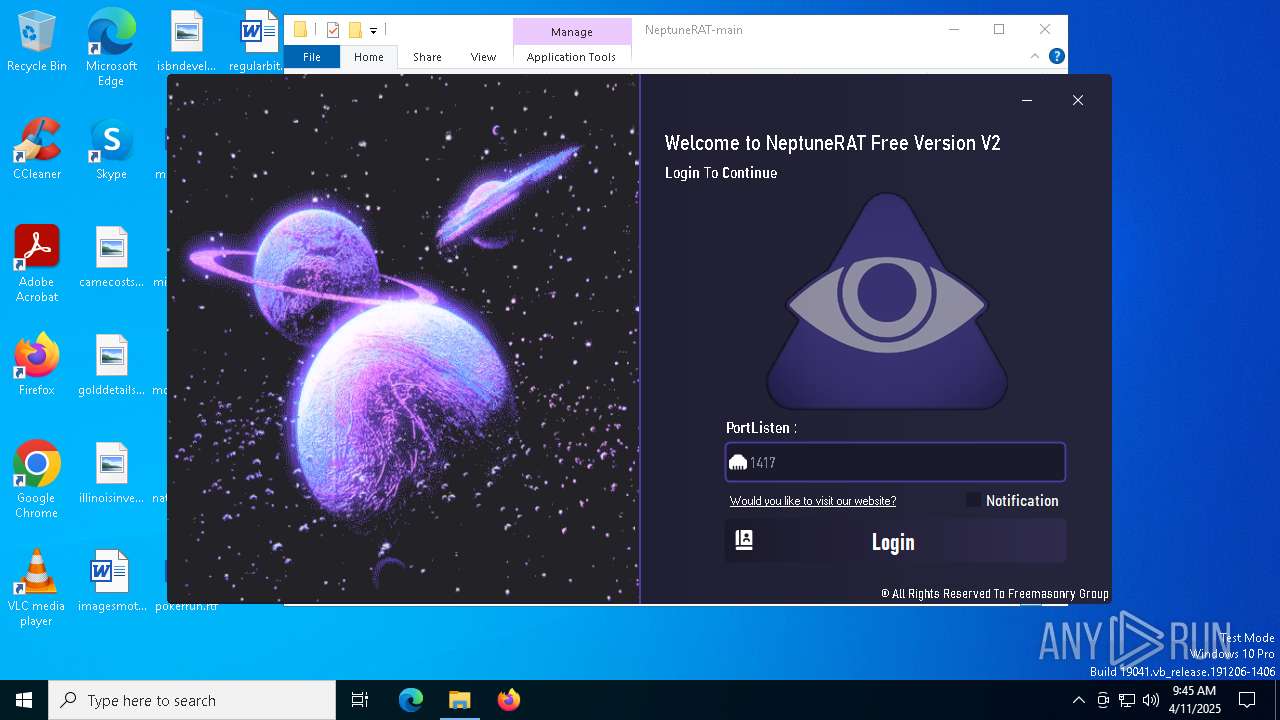
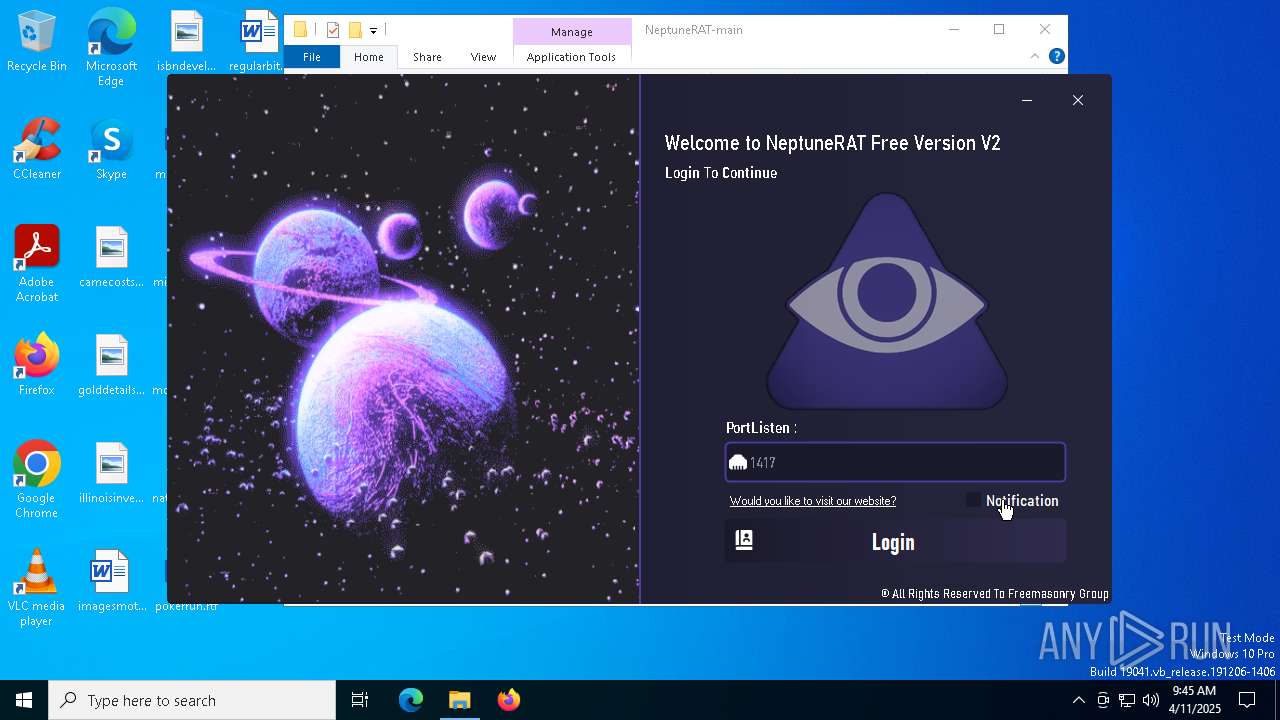
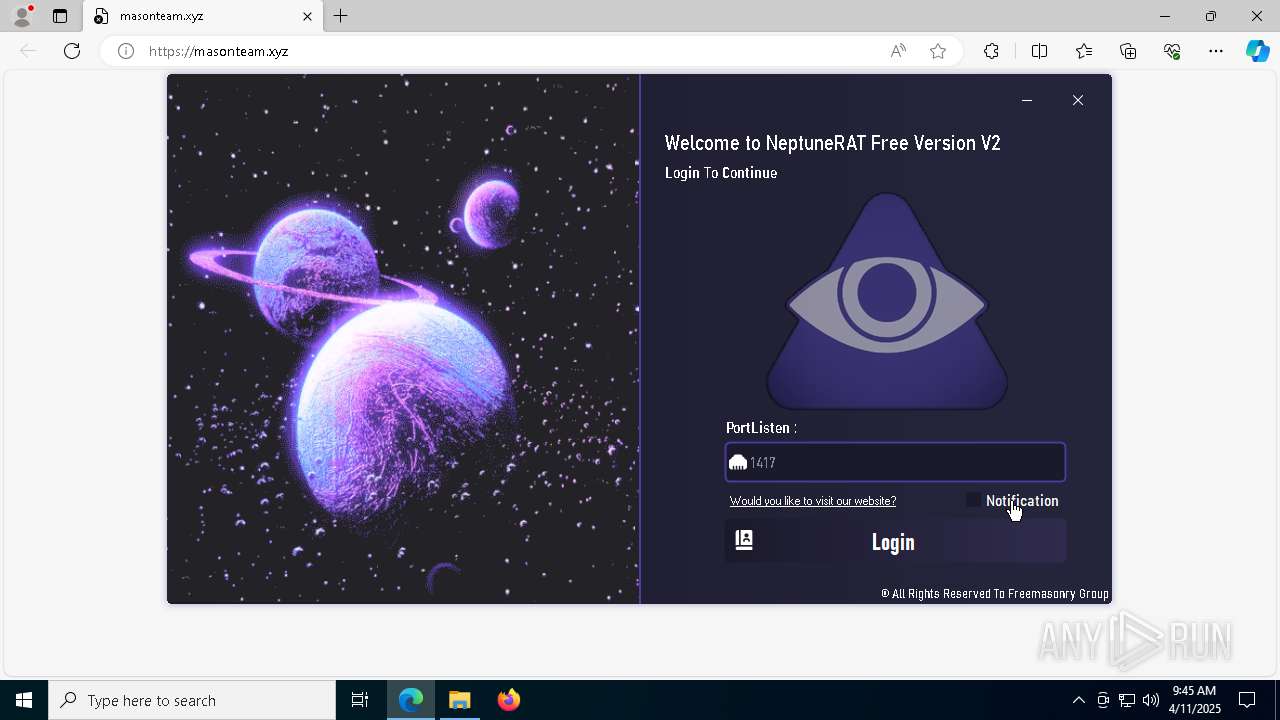
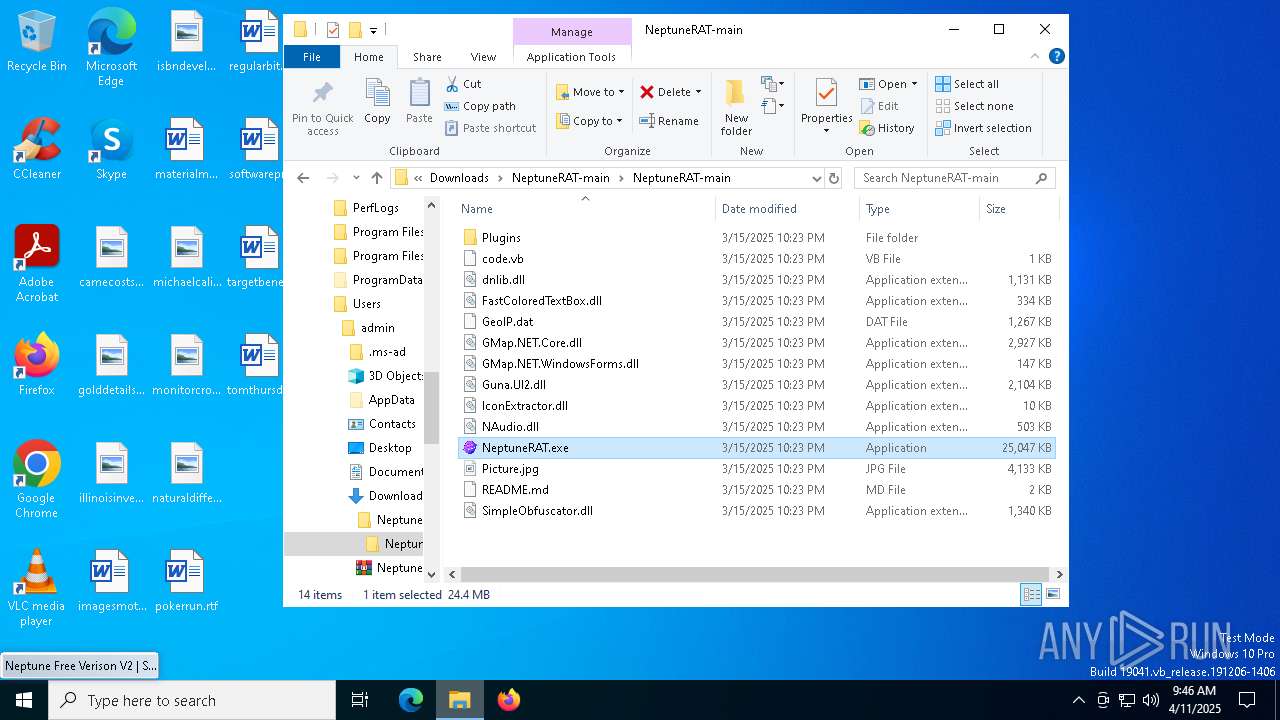
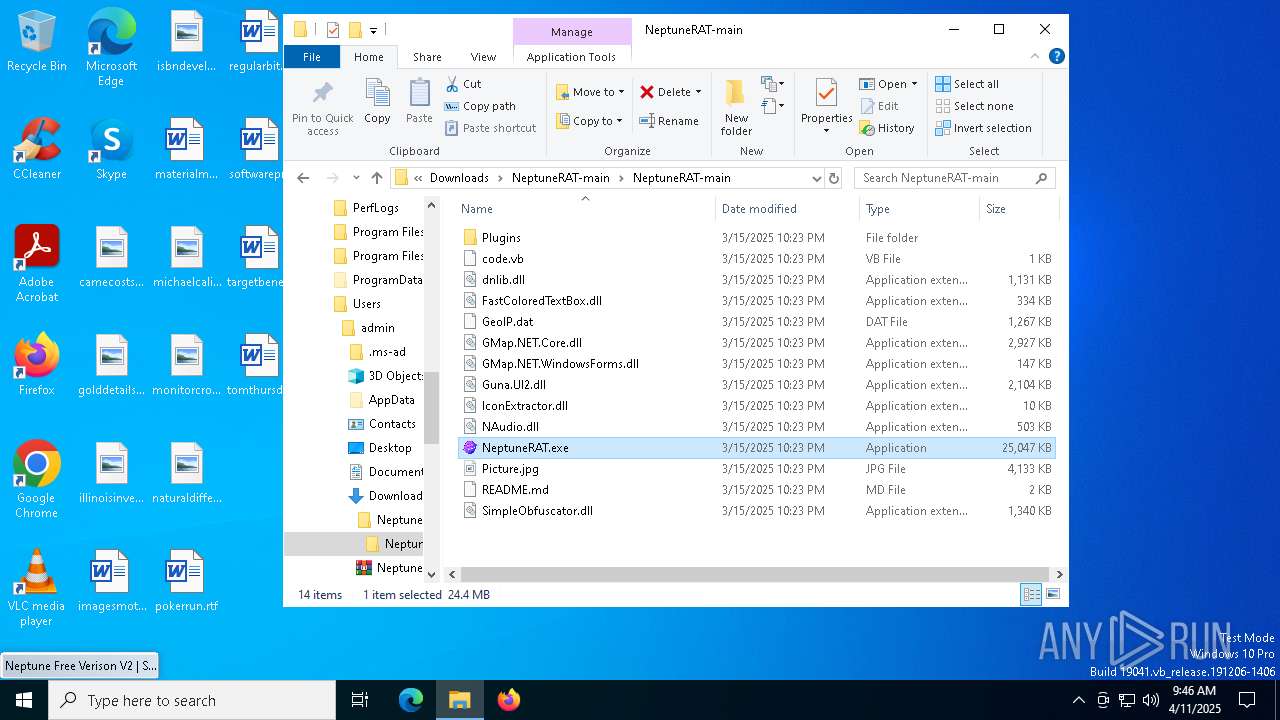
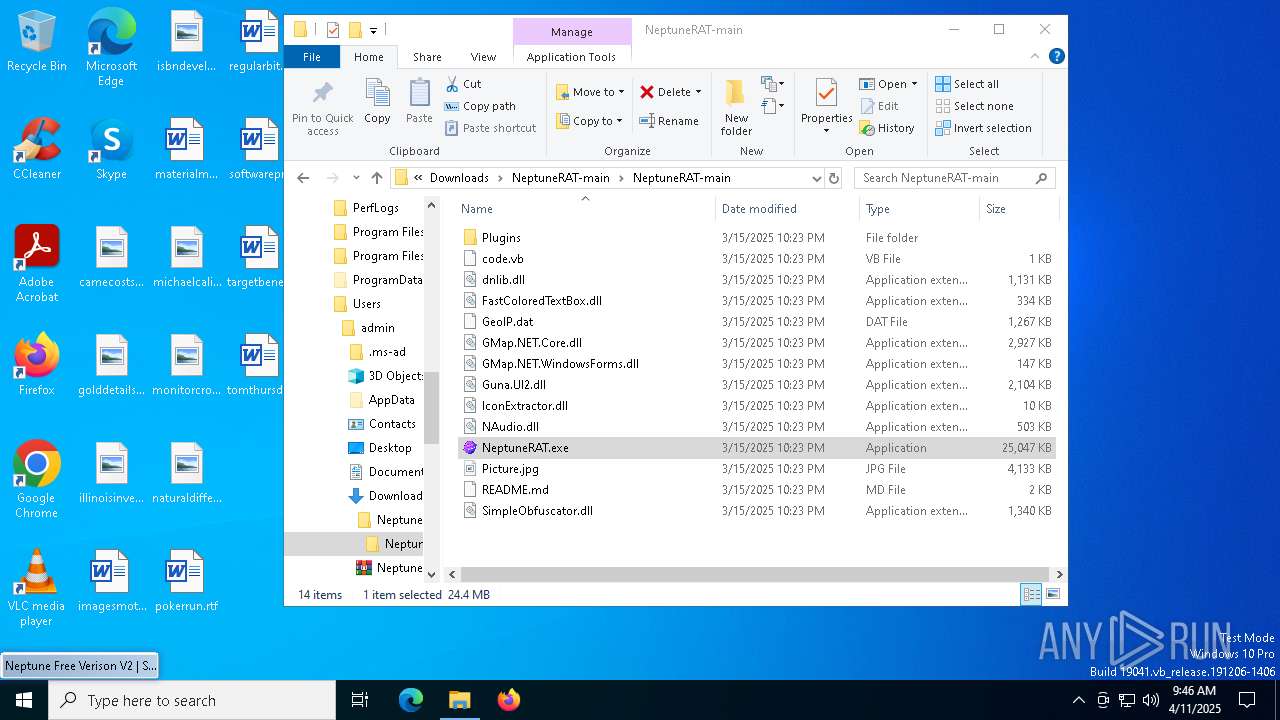
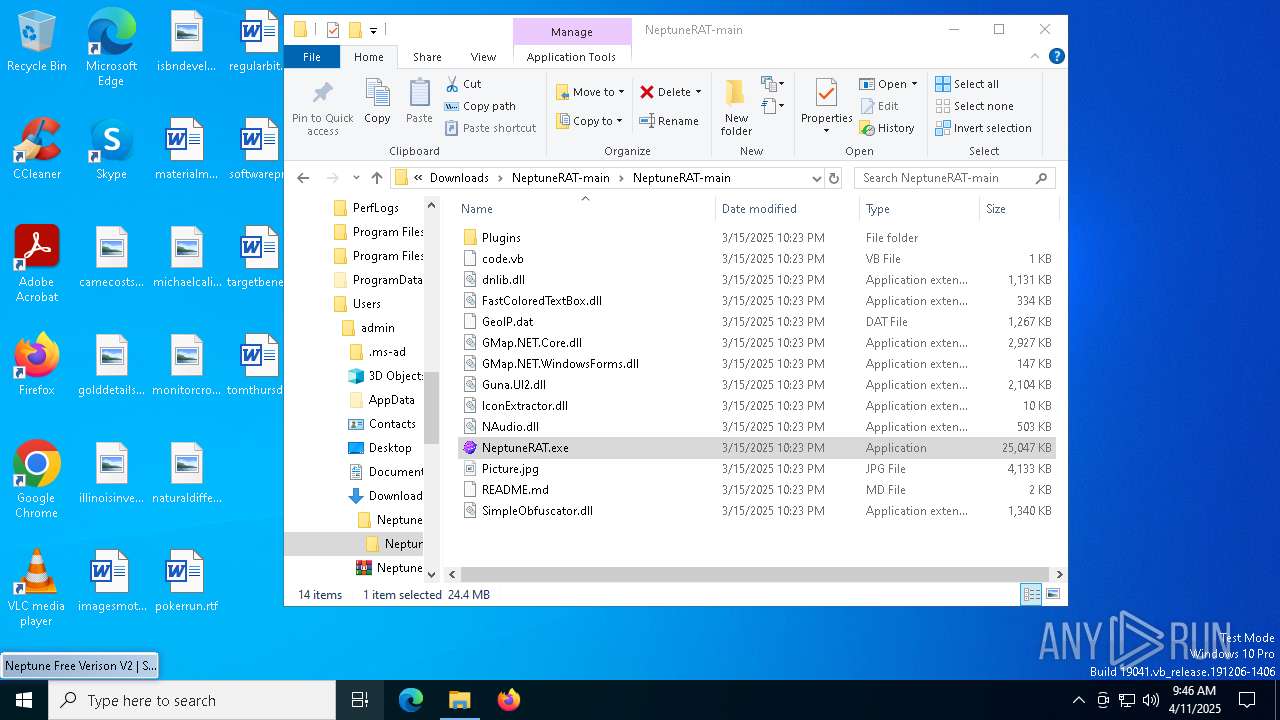
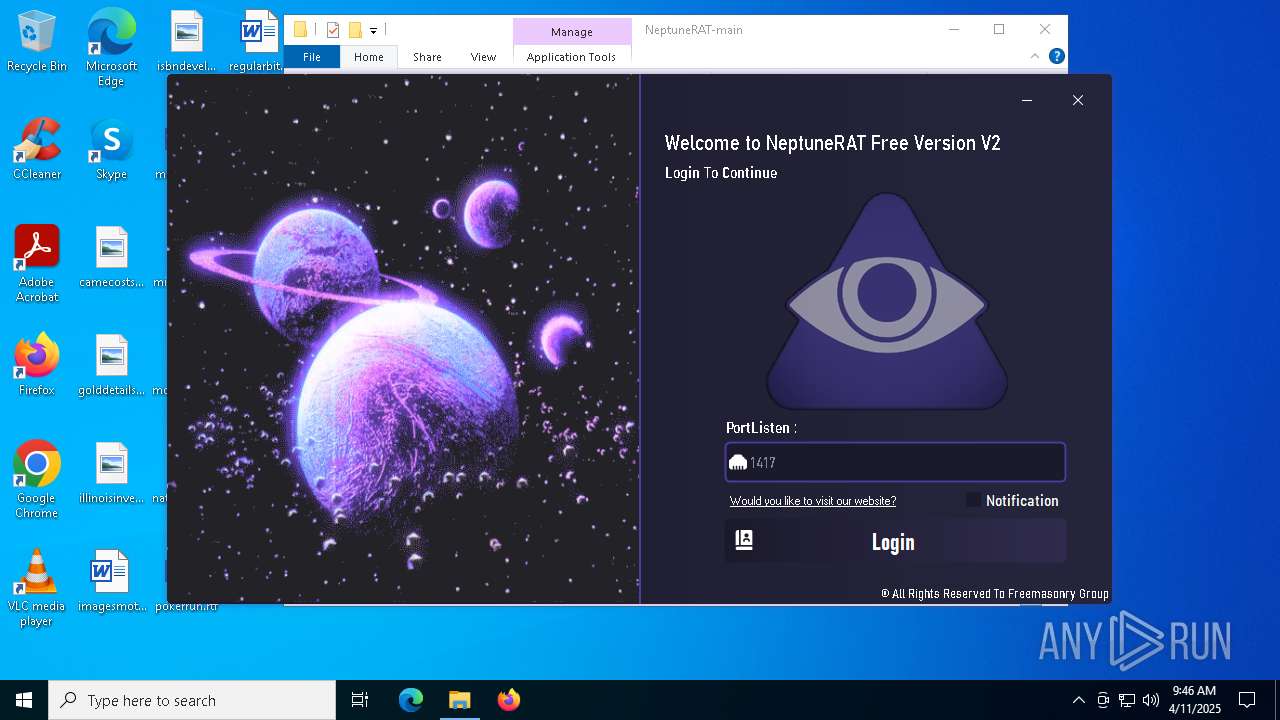
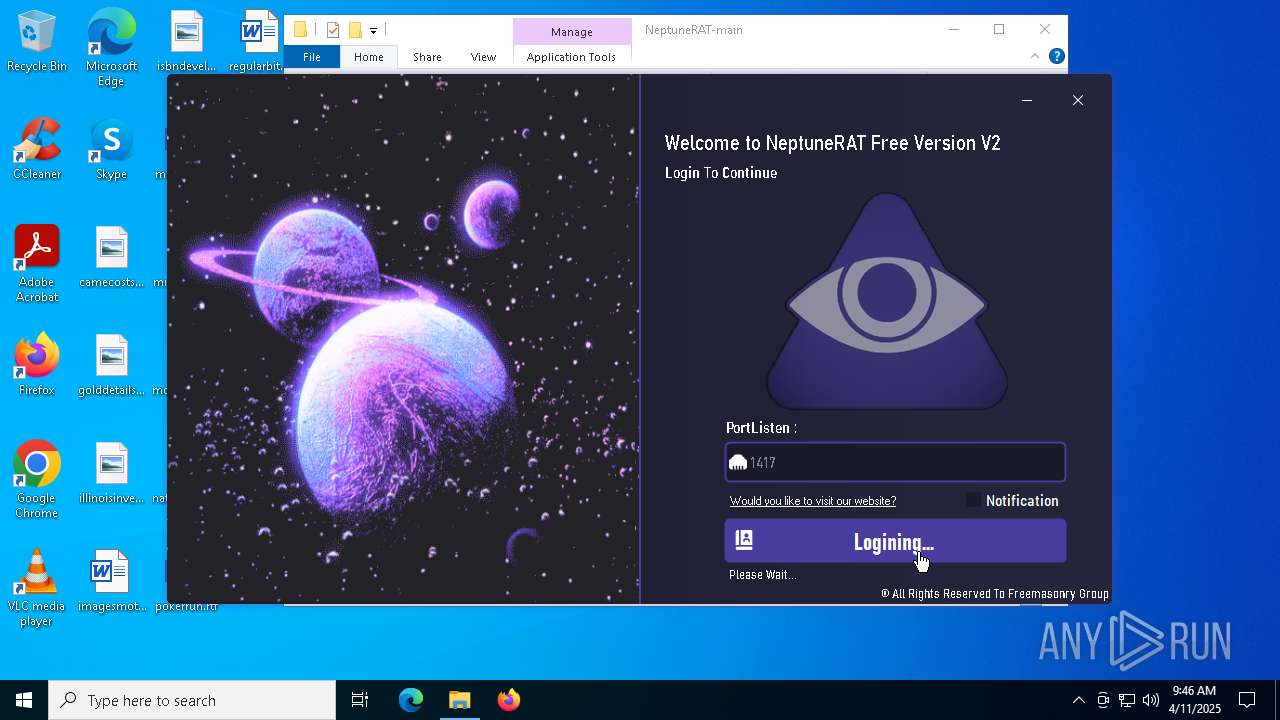
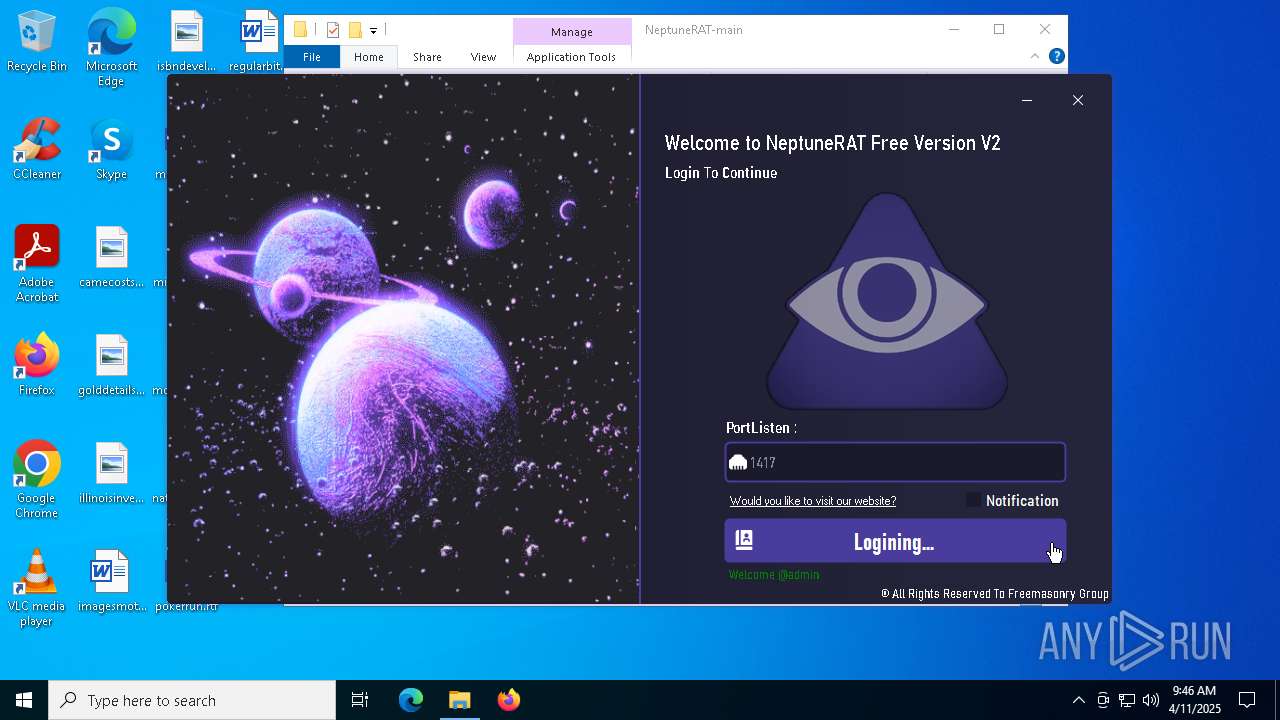
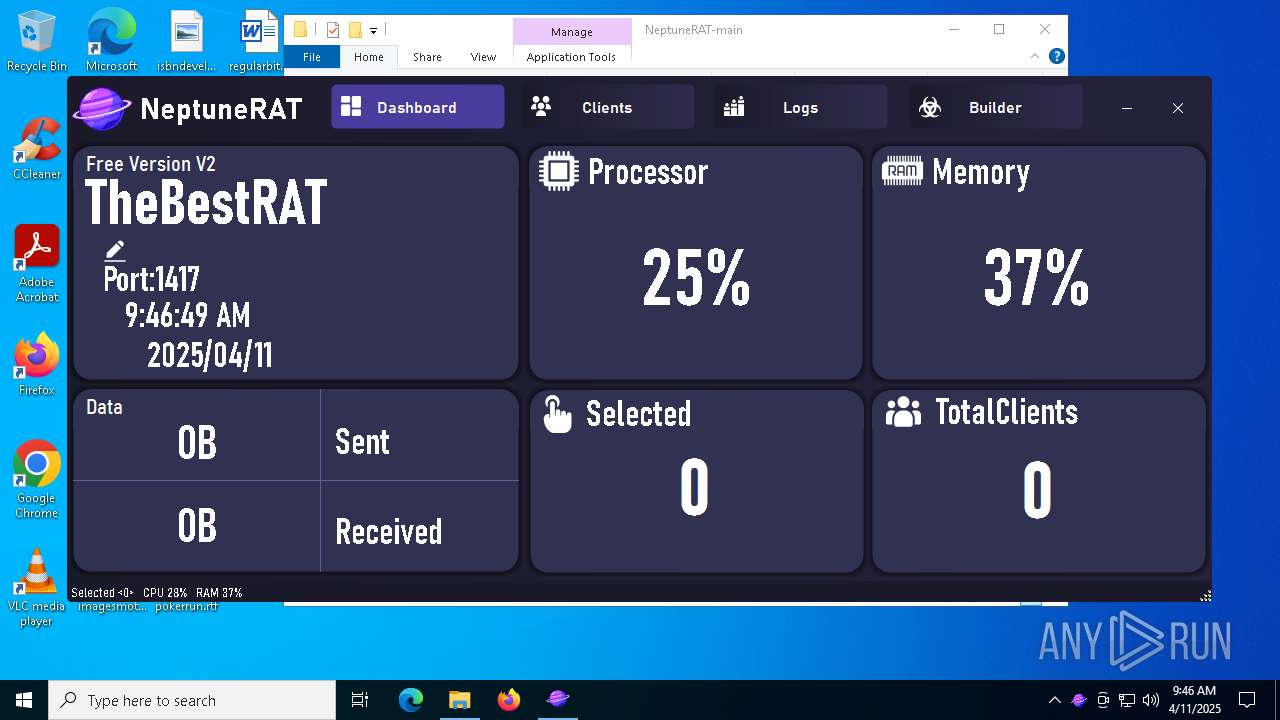
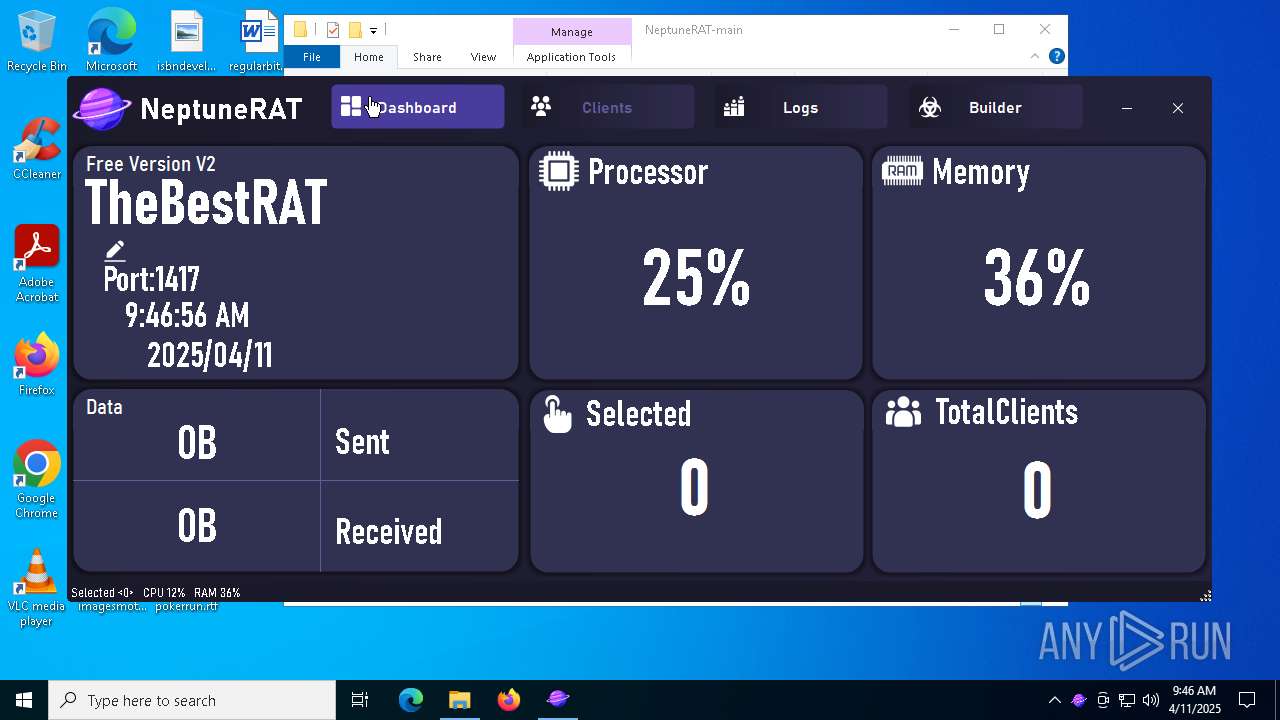
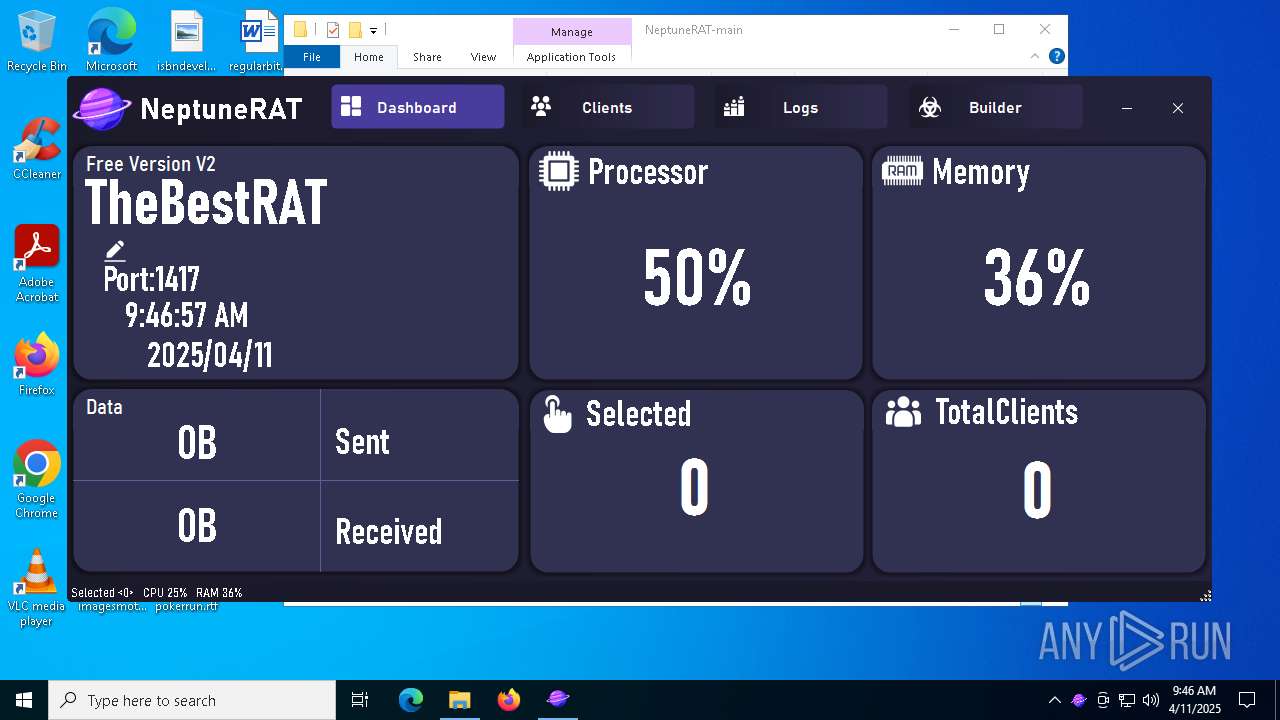
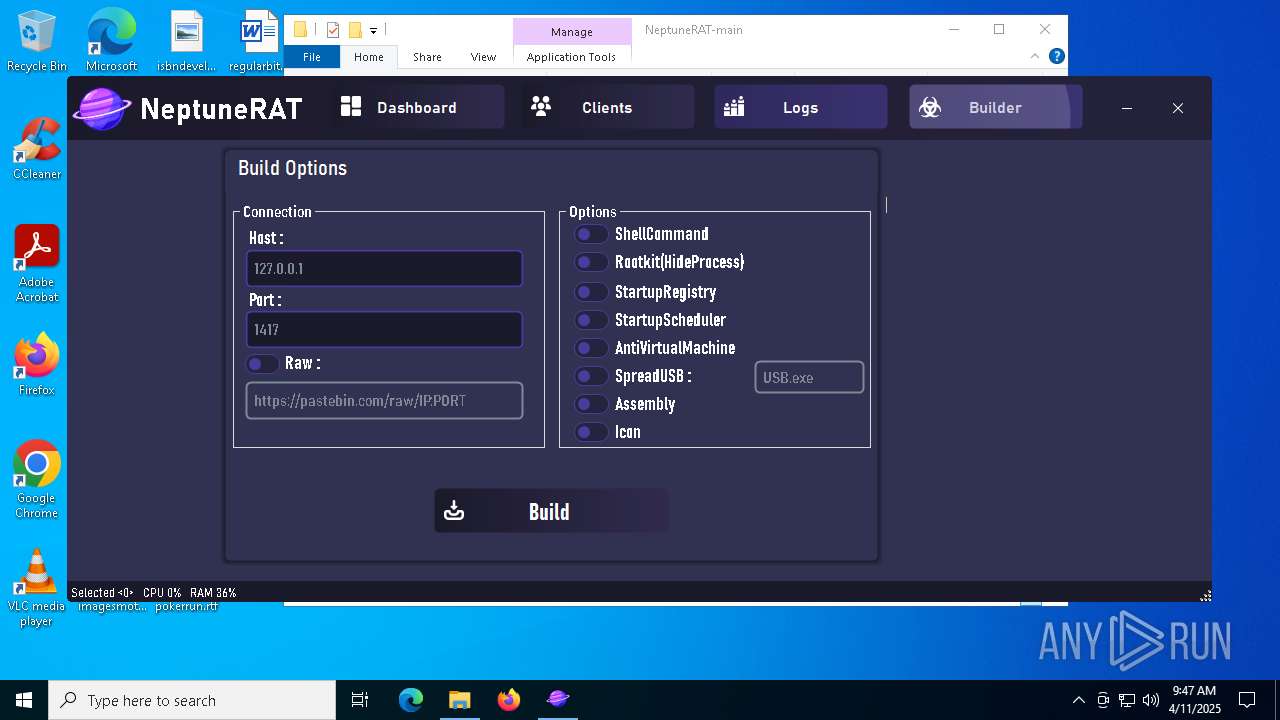
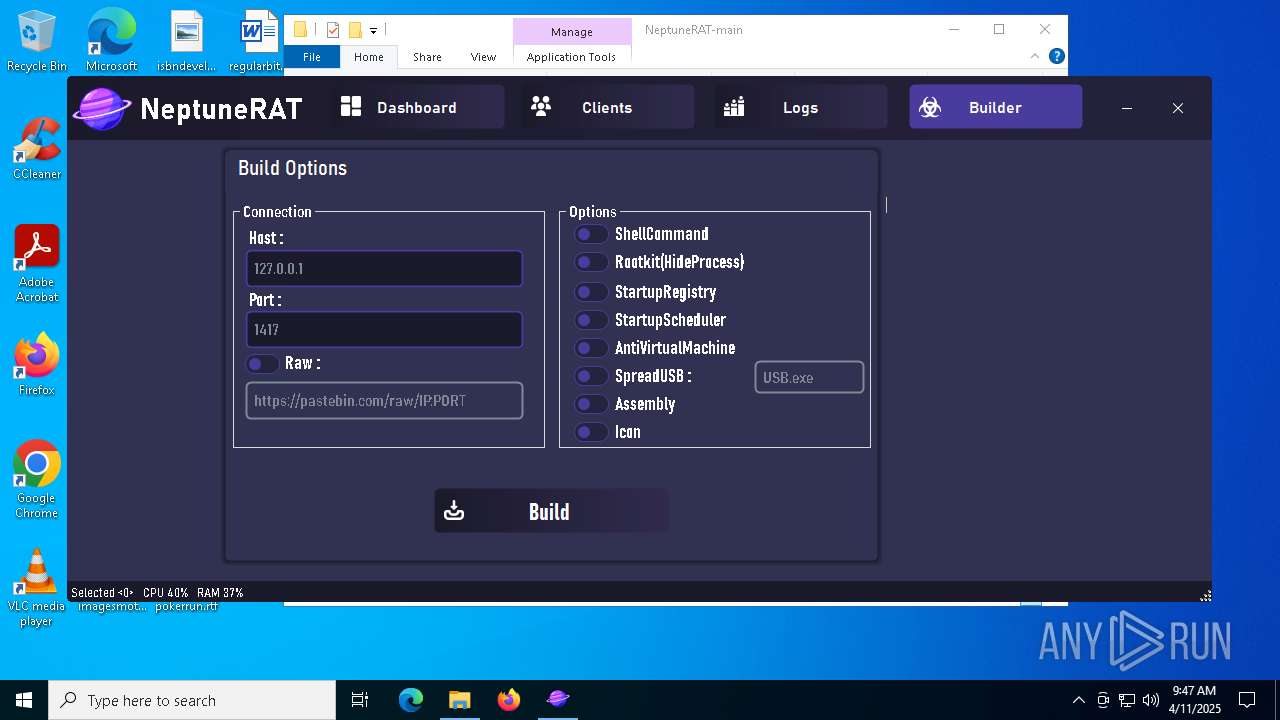
| URL: | https://github.com/MasonGroup/NeptuneRAT/tree/main |
| Full analysis: | https://app.any.run/tasks/ebb30121-63d0-442b-886c-5d0227828103 |
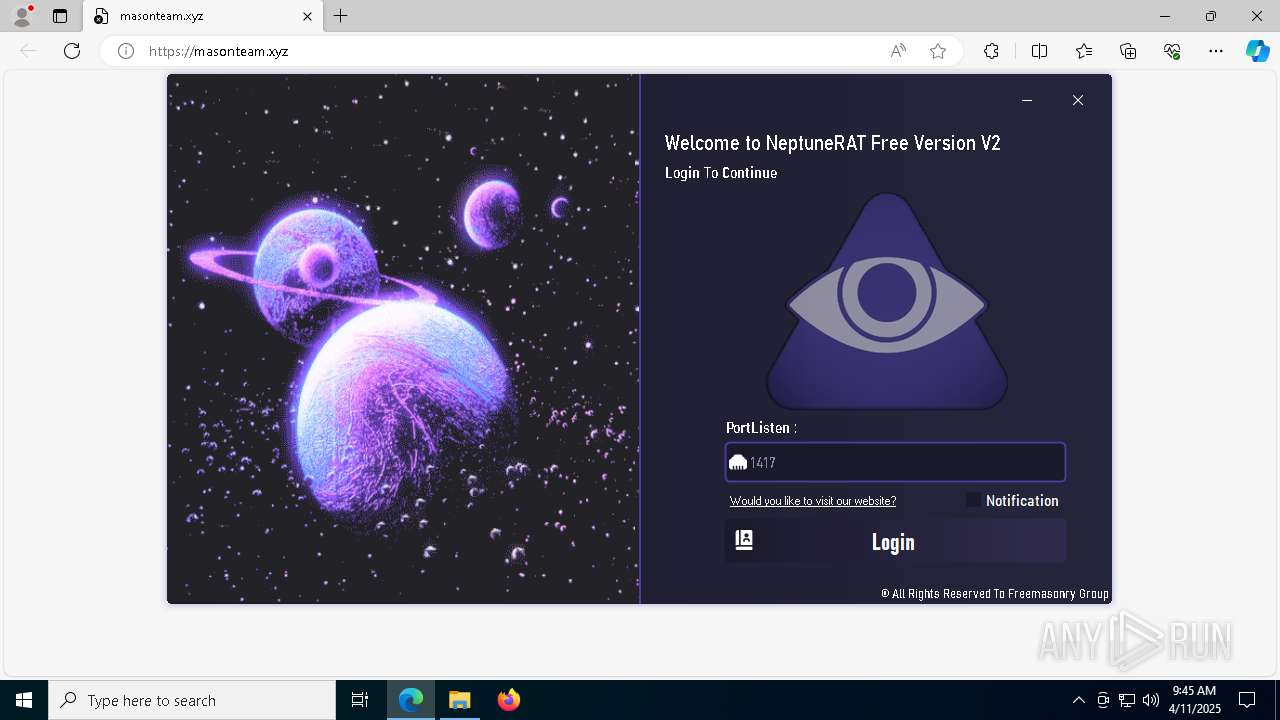
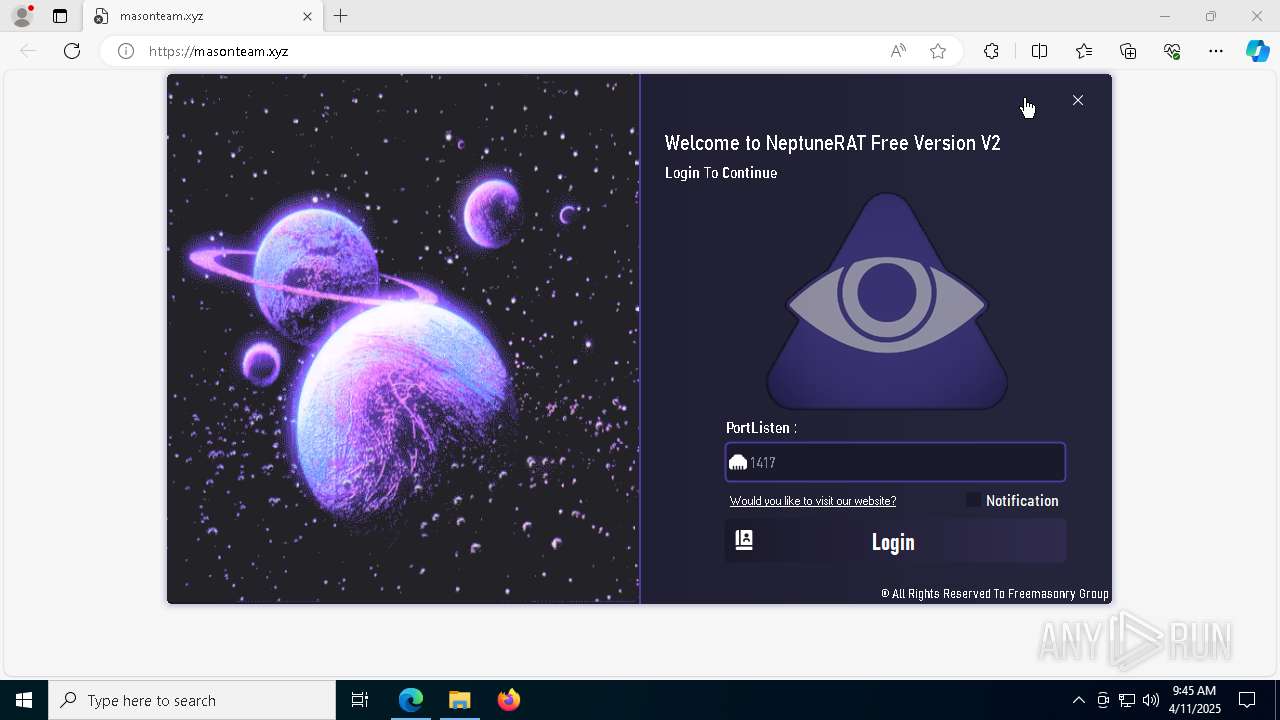
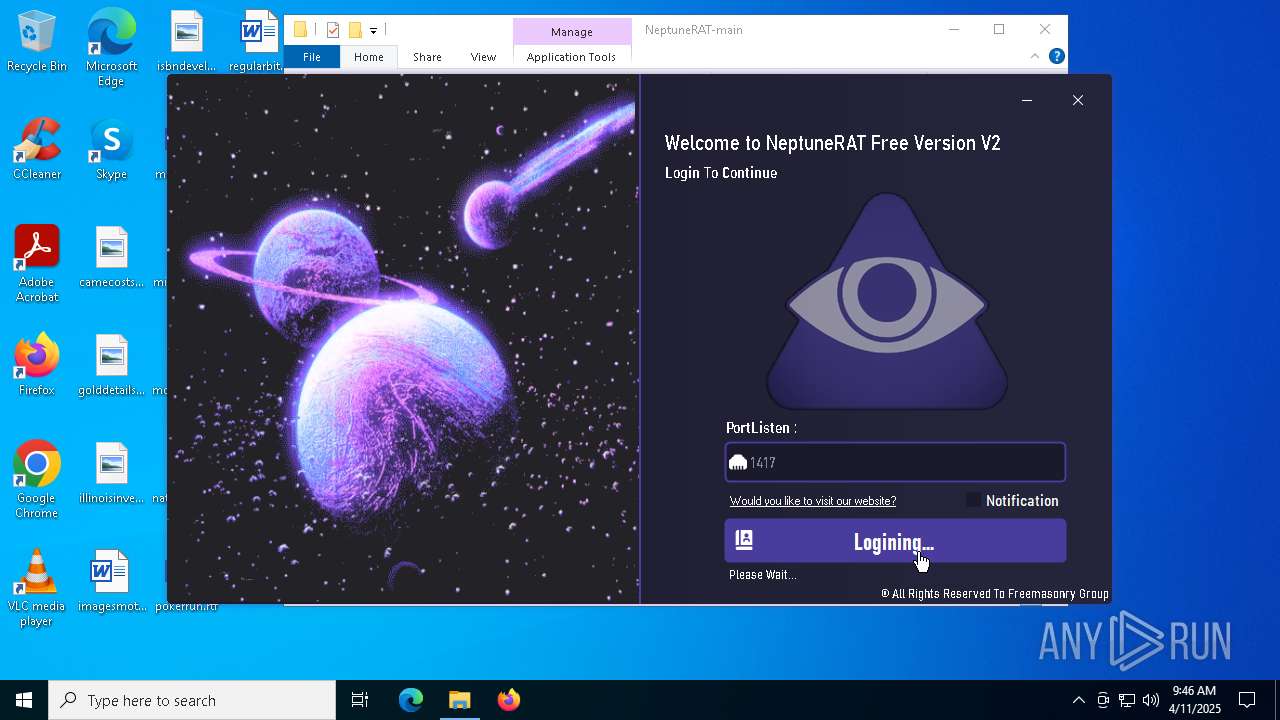
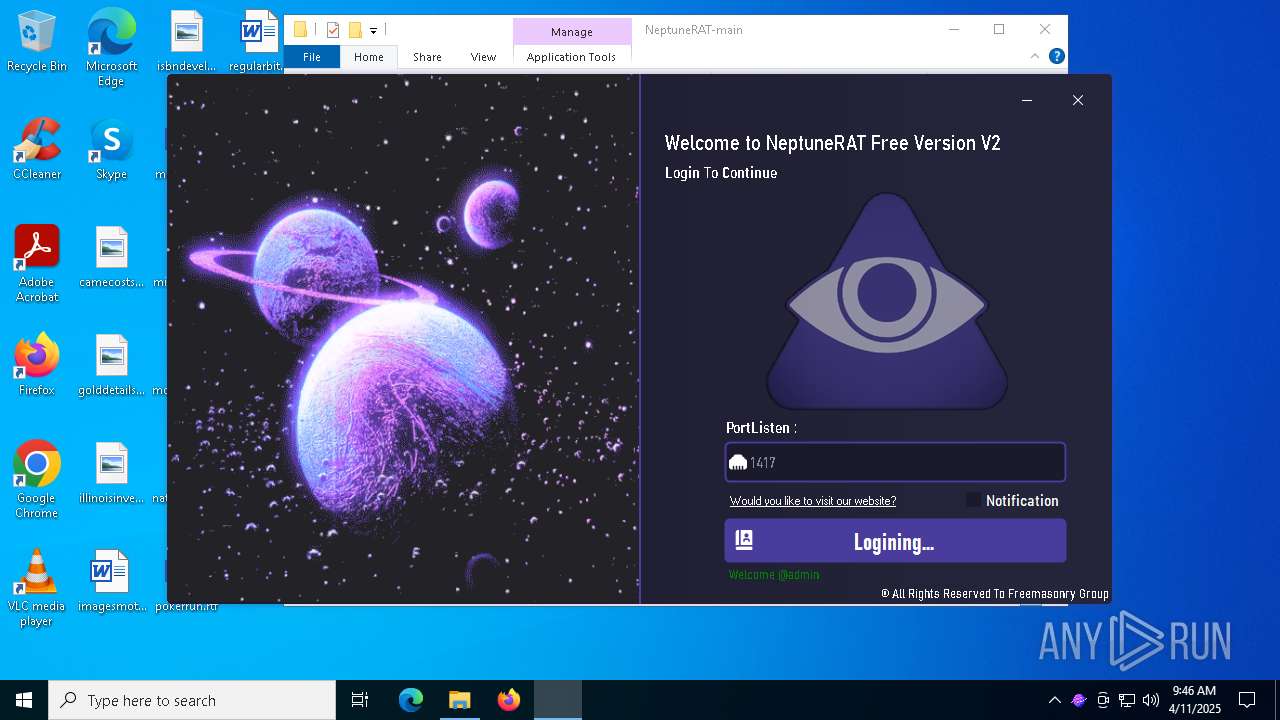
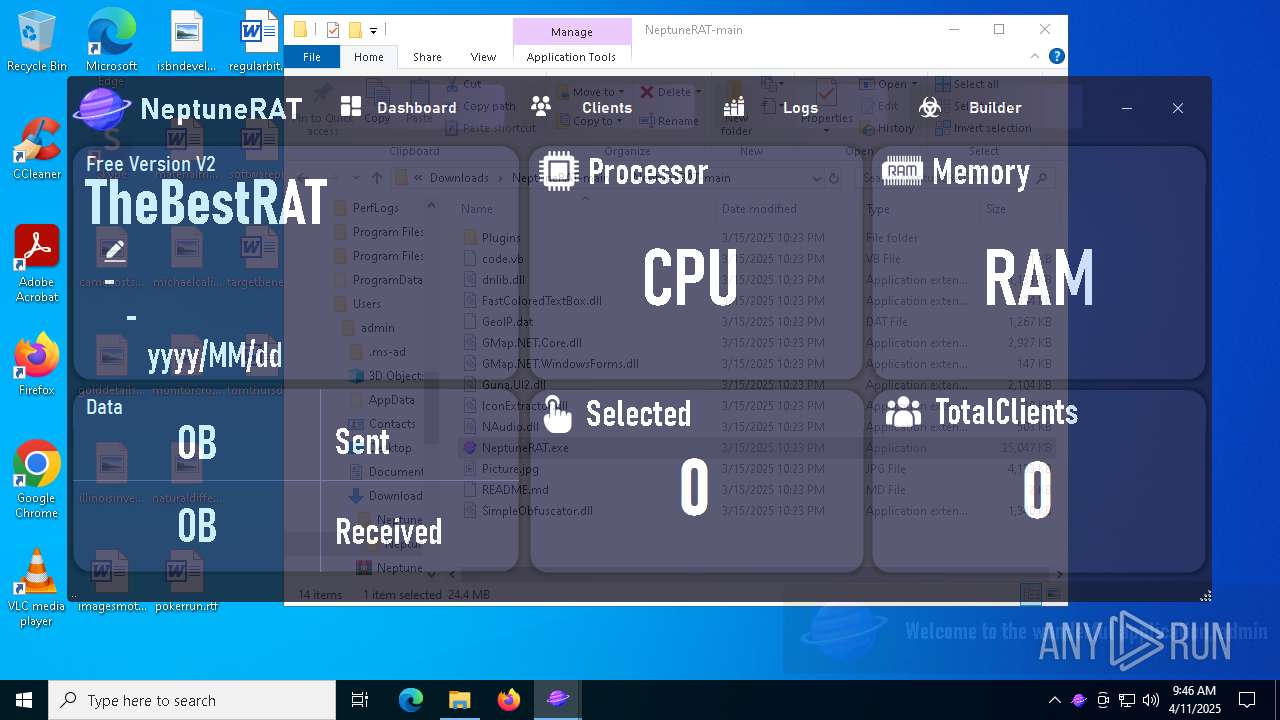
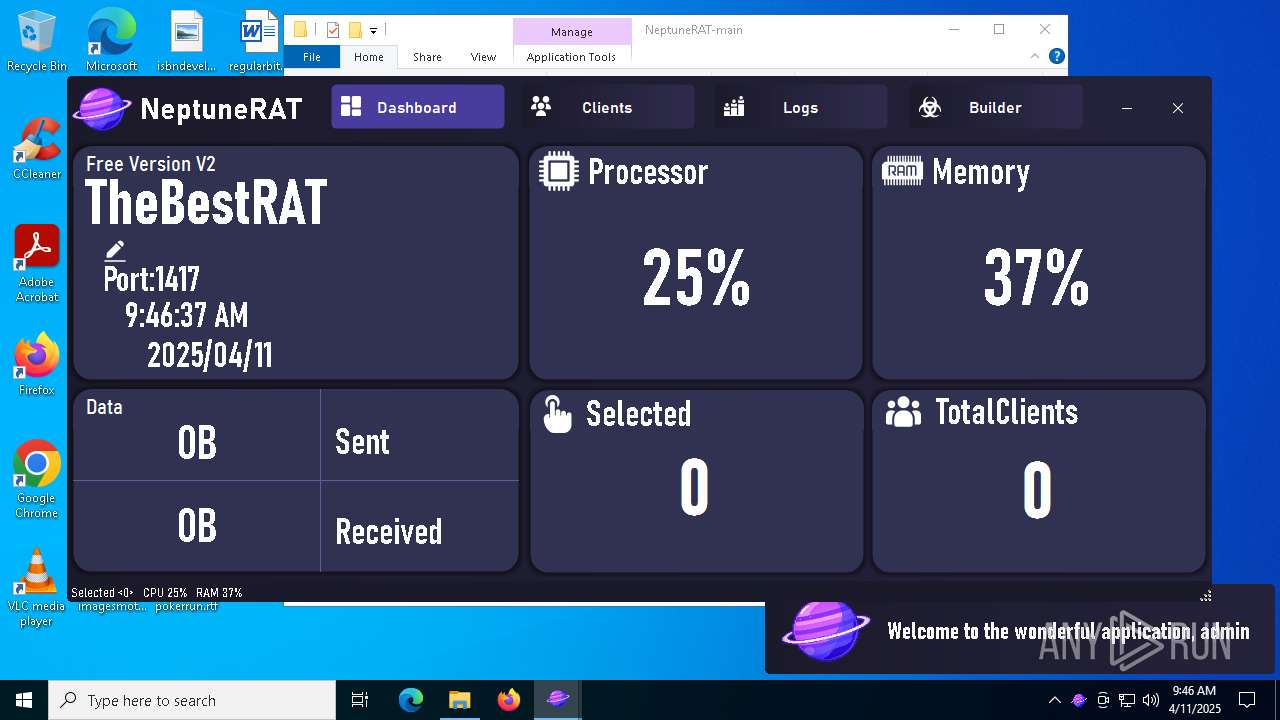
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2025, 09:43:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2FF8E5884824F9F759F7B04F9298043C |
| SHA1: | 4EDEDFADC2FF74465BC2AB1444FB2104AEE1042D |
| SHA256: | 8E6679417FA38916E9A51FD2C93910F92B3D794298386A3DC924DEE8A53D5D27 |
| SSDEEP: | 3:N8tEd437VRQLhMQIRn:2uYR2LhtIRn |
MALICIOUS
No malicious indicators.SUSPICIOUS
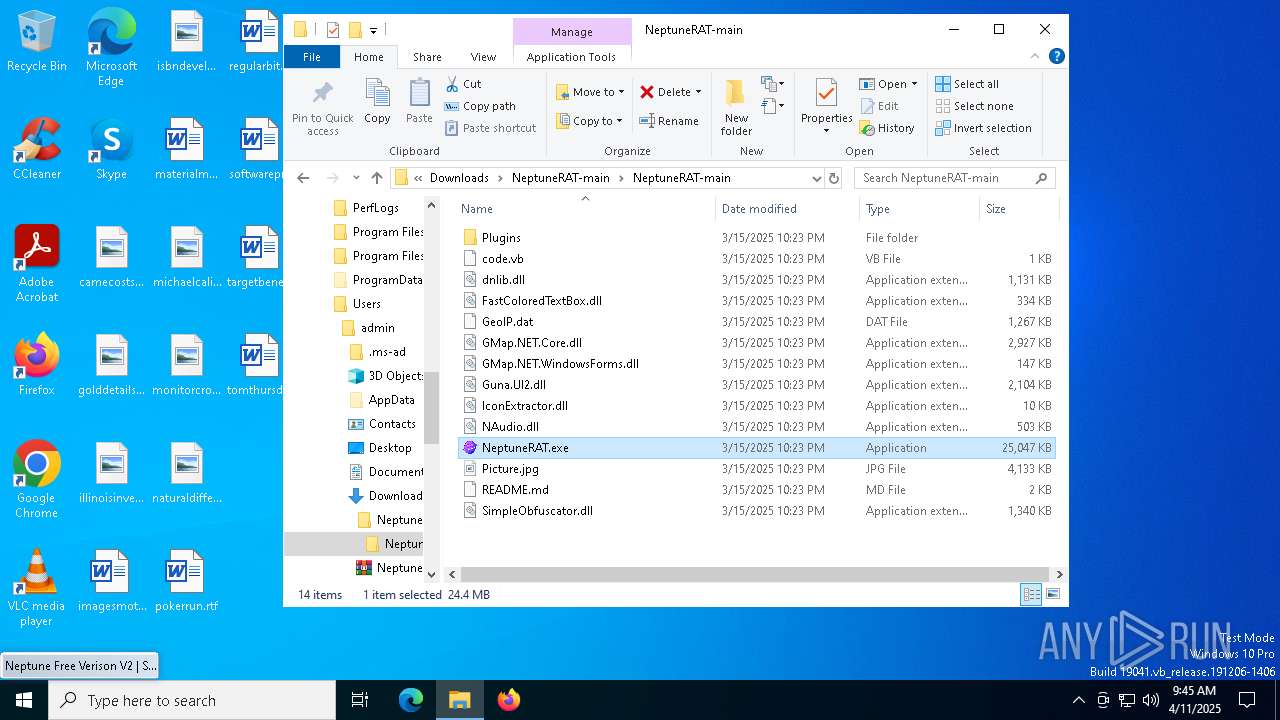
Process drops legitimate windows executable
- WinRAR.exe (PID: 5892)
- bomber.dll (PID: 6652)
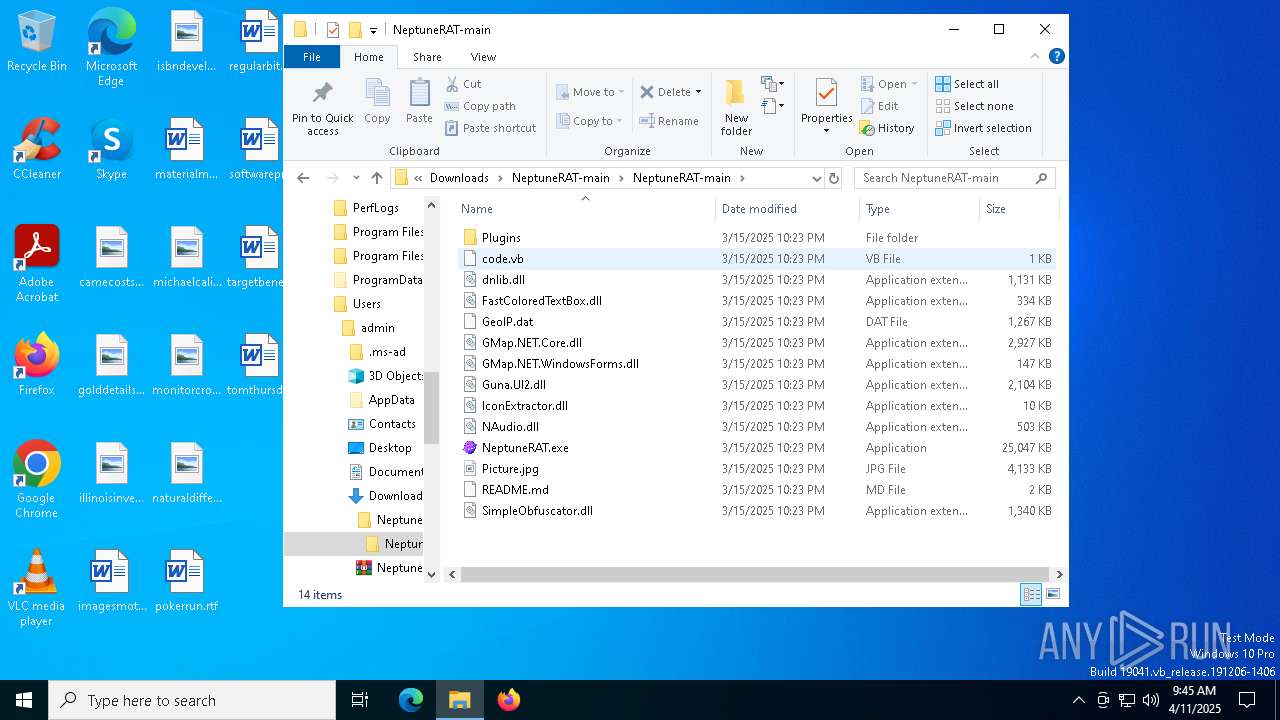
There is functionality for taking screenshot (YARA)
- NeptuneRAT.exe (PID: 5744)
There is functionality for capture public ip (YARA)
- NeptuneRAT.exe (PID: 5744)
The process checks if it is being run in the virtual environment
- NeptuneRAT.exe (PID: 5744)
Reads security settings of Internet Explorer
- NeptuneRAT.exe (PID: 5744)
- ShellExperienceHost.exe (PID: 8148)
Starts application with an unusual extension
- cmd.exe (PID: 6384)
The process executes VB scripts
- NeptuneRAT.exe (PID: 5744)
Executable content was dropped or overwritten
- vbc.exe (PID: 4308)
- bomber.dll (PID: 6652)
Starts CMD.EXE for commands execution
- NeptuneRAT.exe (PID: 5744)
The executable file from the user directory is run by the CMD process
- bomber.dll (PID: 6652)
Process drops python dynamic module
- bomber.dll (PID: 6652)
The process drops C-runtime libraries
- bomber.dll (PID: 6652)
INFO
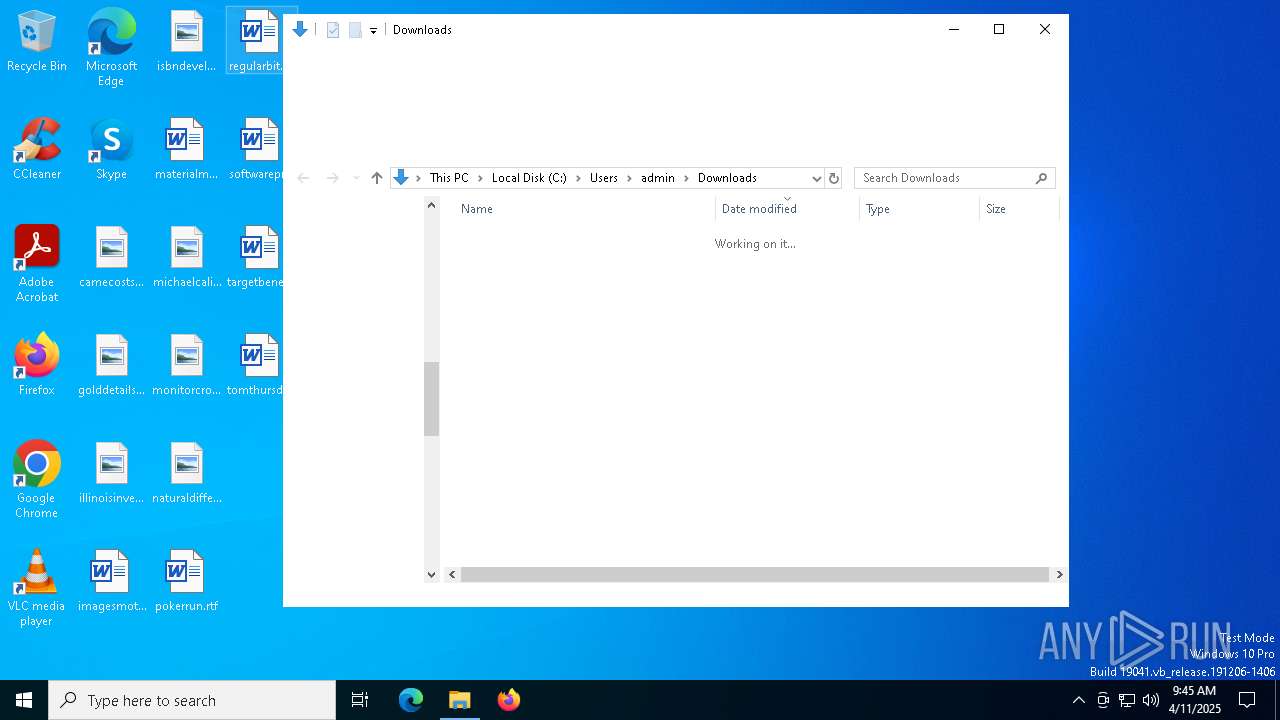
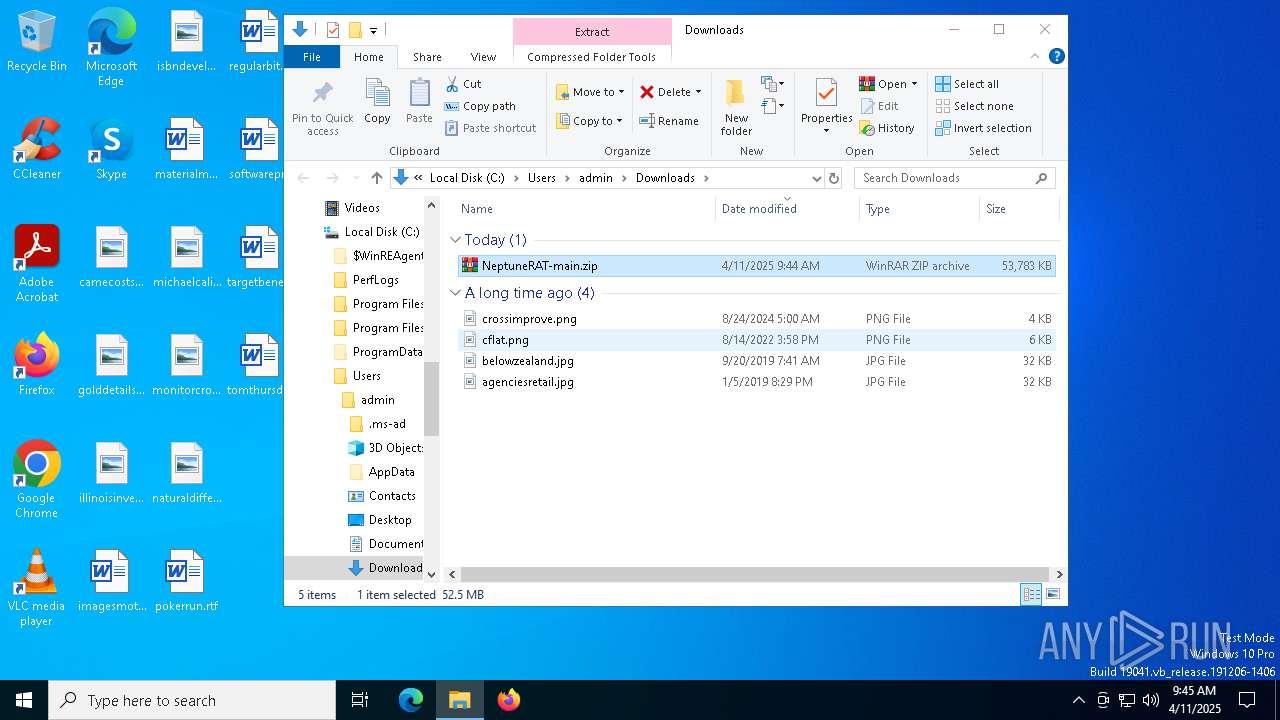
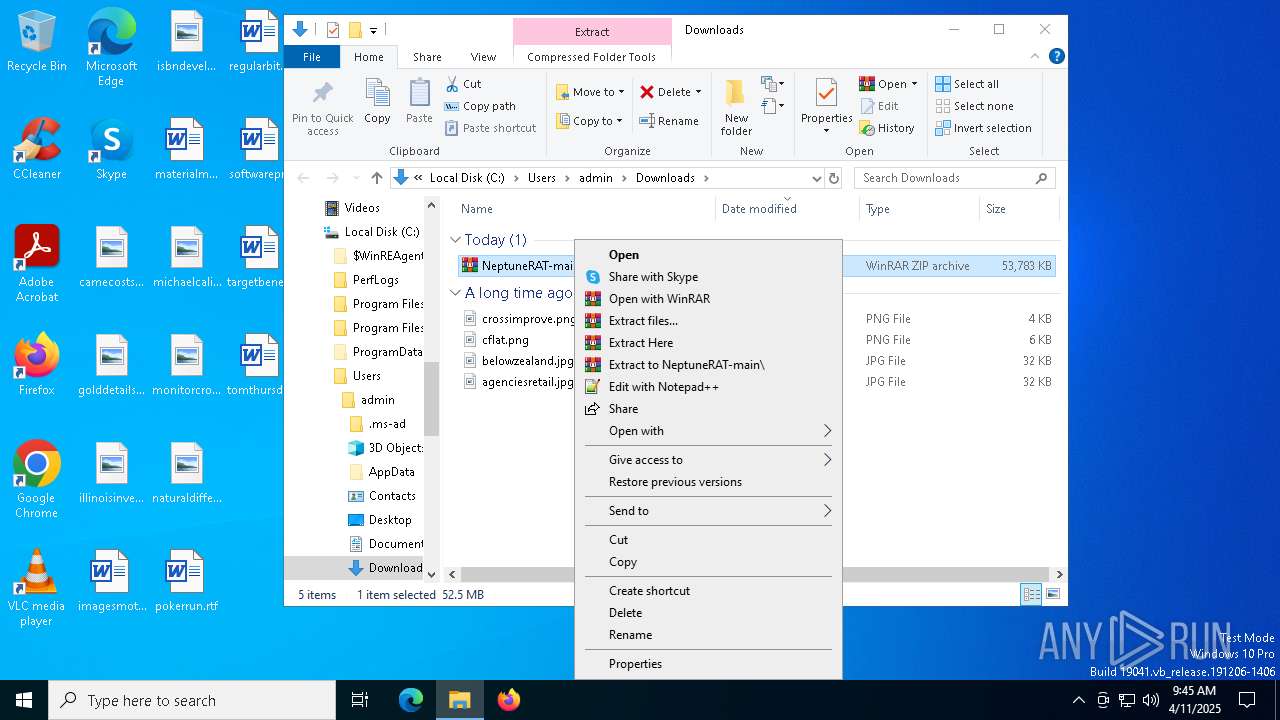
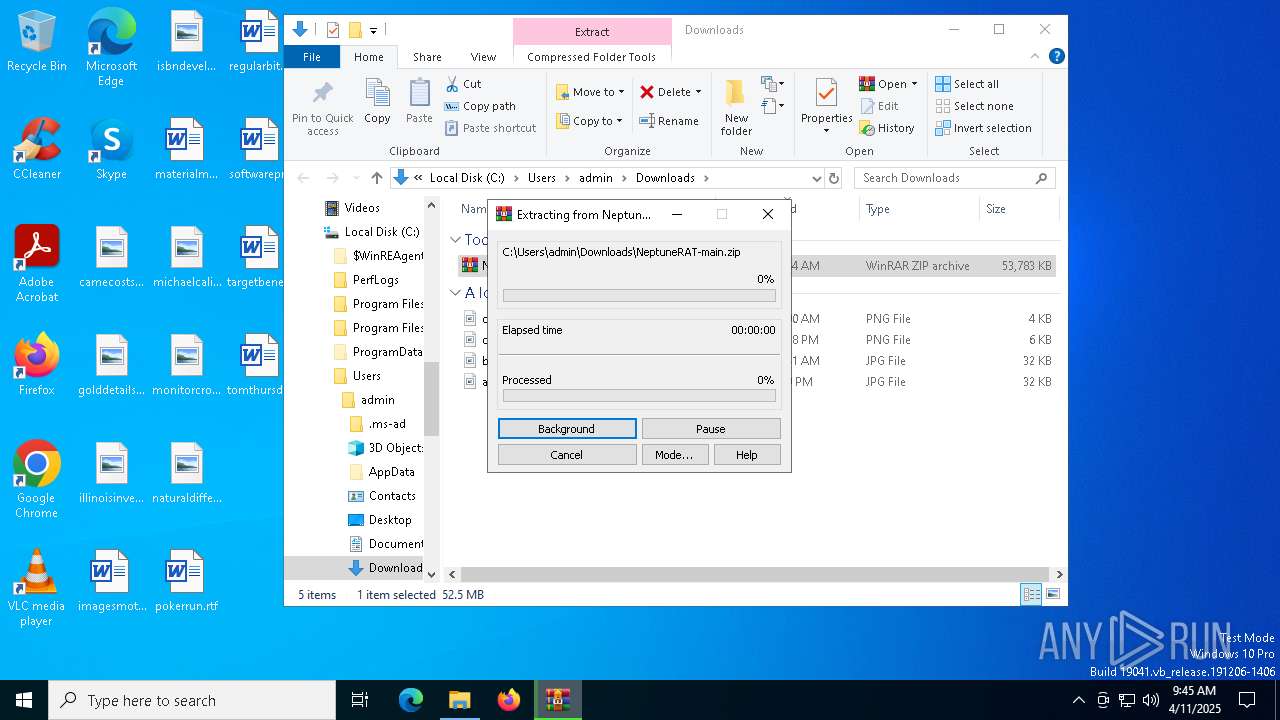
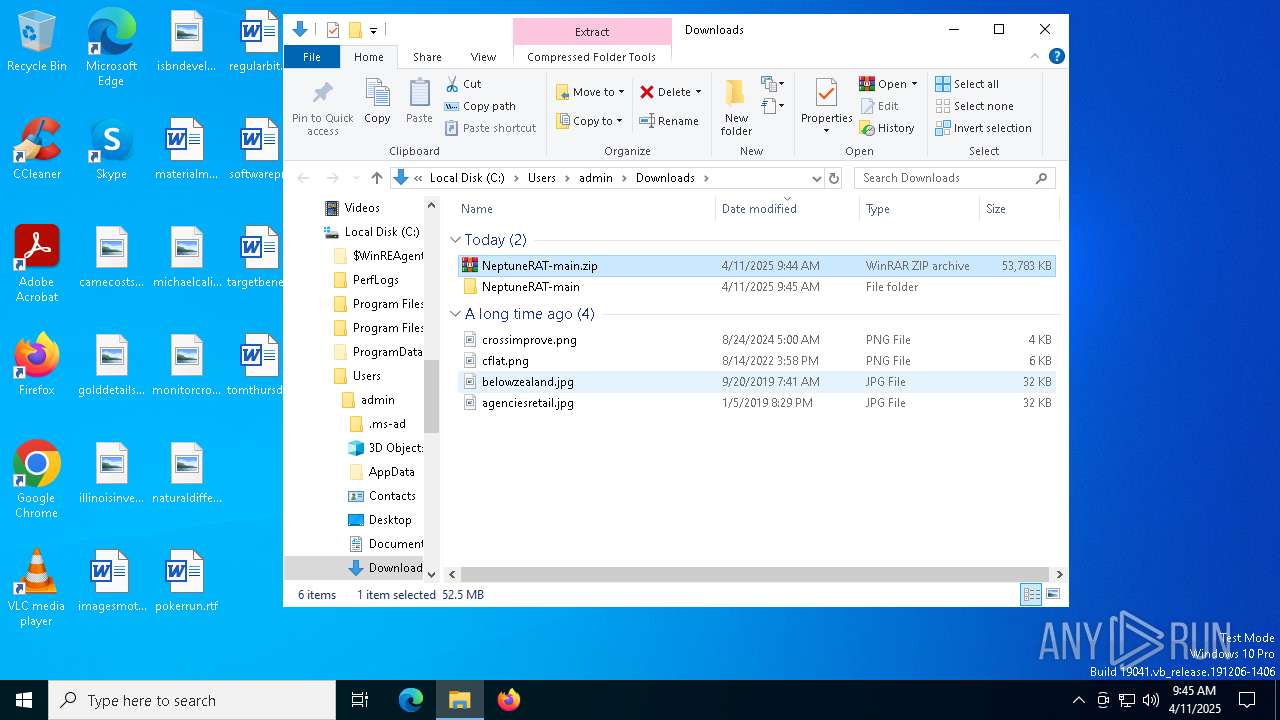
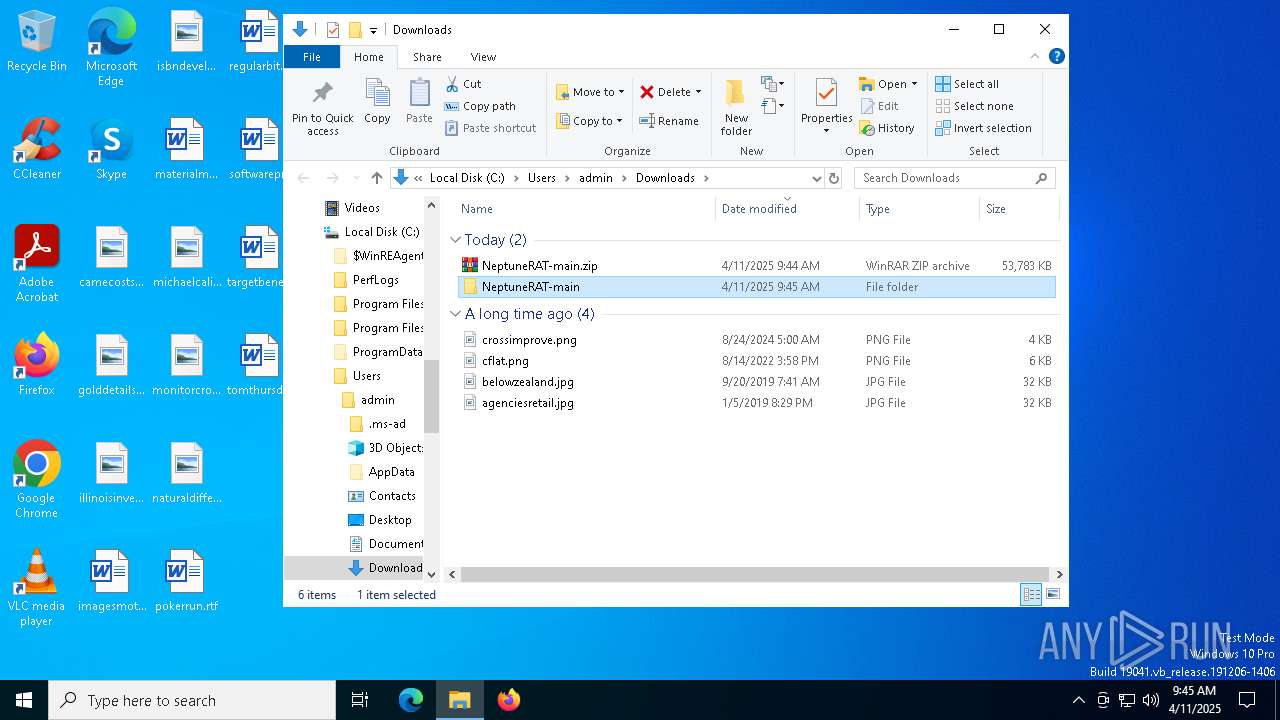
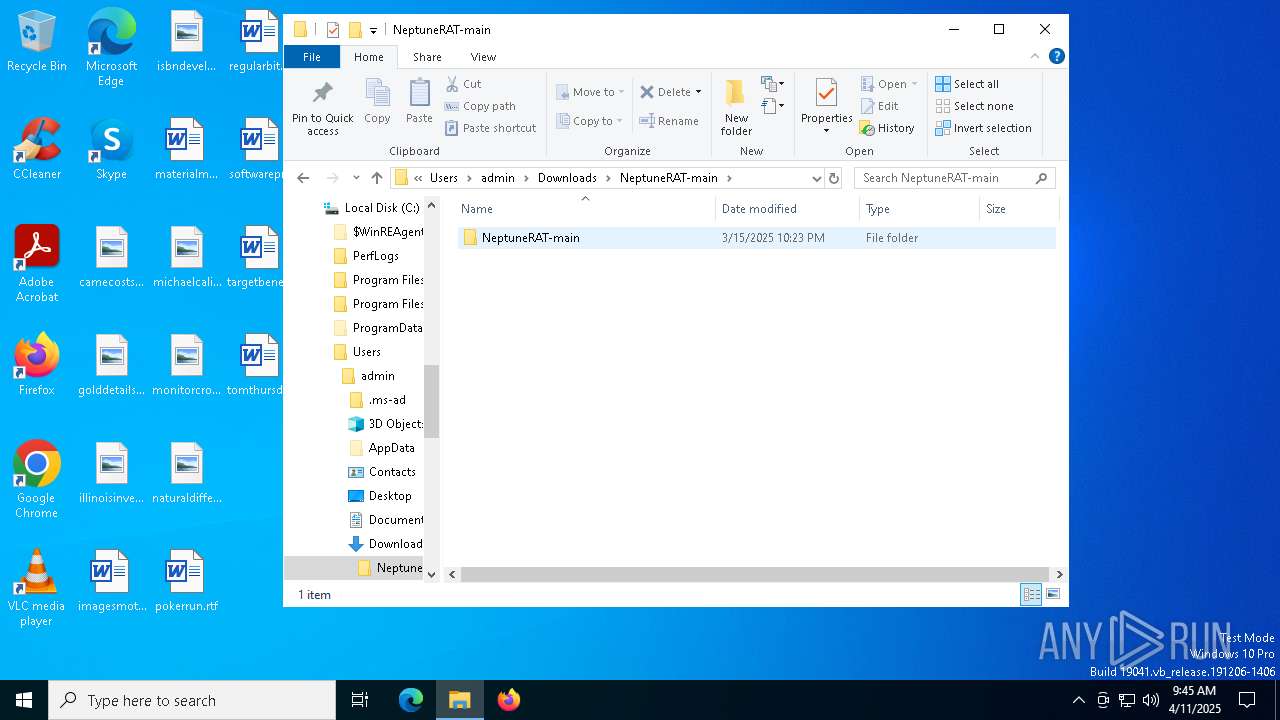
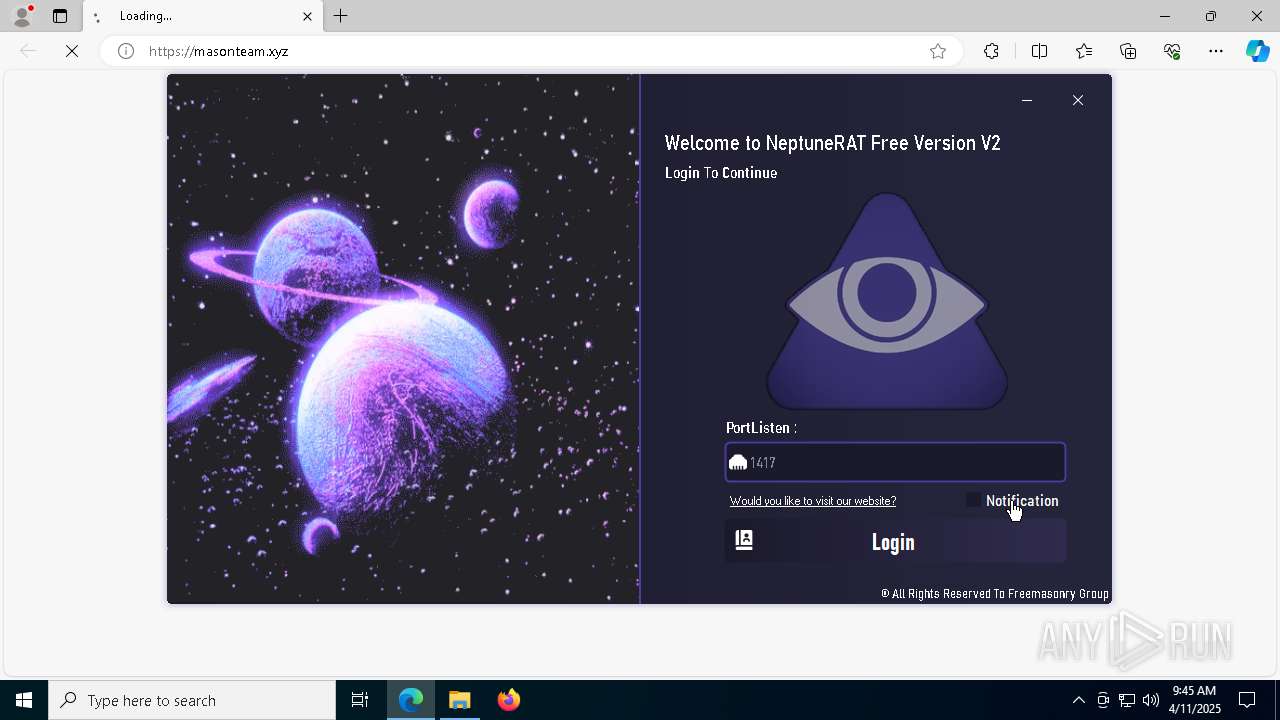
Manual execution by a user
- firefox.exe (PID: 4756)
- WinRAR.exe (PID: 5892)
- NeptuneRAT.exe (PID: 5744)
Application launched itself
- firefox.exe (PID: 4756)
- chrome.exe (PID: 7448)
- firefox.exe (PID: 7348)
- msedge.exe (PID: 3100)
- msedge.exe (PID: 1004)
Reads the software policy settings
- slui.exe (PID: 8156)
- slui.exe (PID: 7668)
- BackgroundTransferHost.exe (PID: 8128)
Autorun file from Downloads
- firefox.exe (PID: 7348)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5892)
- msedge.exe (PID: 3800)
Checks supported languages
- NeptuneRAT.exe (PID: 5744)
- identity_helper.exe (PID: 4188)
- identity_helper.exe (PID: 4464)
- ShellExperienceHost.exe (PID: 8148)
- vbc.exe (PID: 4308)
- cvtres.exe (PID: 6728)
Reads the computer name
- NeptuneRAT.exe (PID: 5744)
- identity_helper.exe (PID: 4464)
- identity_helper.exe (PID: 4188)
Reads the machine GUID from the registry
- NeptuneRAT.exe (PID: 5744)
- vbc.exe (PID: 4308)
Checks proxy server information
- slui.exe (PID: 7668)
- BackgroundTransferHost.exe (PID: 8128)
Reads Environment values
- identity_helper.exe (PID: 4188)
- identity_helper.exe (PID: 4464)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 1328)
- BackgroundTransferHost.exe (PID: 8128)
- BackgroundTransferHost.exe (PID: 4868)
- BackgroundTransferHost.exe (PID: 7264)
- BackgroundTransferHost.exe (PID: 4024)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8128)
Create files in a temporary directory
- NeptuneRAT.exe (PID: 5744)
- vbc.exe (PID: 4308)
- cvtres.exe (PID: 6728)
- bomber.dll (PID: 6652)
The sample compiled with english language support
- msedge.exe (PID: 3800)
- bomber.dll (PID: 6652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
239
Monitored processes
94
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5088 --field-trial-handle=2344,i,12023007760484150849,525579870889066929,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2420 --field-trial-handle=2440,i,15442657189409388207,6096216017736741413,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4728 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4700 -prefMapHandle 2748 -prefsLen 36588 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2e4201bf-742a-4744-8ec8-28b2ce08b1e4} 7348 "\\.\pipe\gecko-crash-server-pipe.7348" 1e3c2437310 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6772 --field-trial-handle=2440,i,15442657189409388207,6096216017736741413,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6428 --field-trial-handle=2440,i,15442657189409388207,6096216017736741413,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5772 --field-trial-handle=2440,i,15442657189409388207,6096216017736741413,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1004 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6128 --field-trial-handle=2440,i,15442657189409388207,6096216017736741413,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3276 --field-trial-handle=2344,i,12023007760484150849,525579870889066929,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
49 294
Read events
49 144
Write events
144
Delete events
6
Modification events
| (PID) Process: | (7448) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7448) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7448) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7448) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7448) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7448) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (7448) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (7348) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5892) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5892) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
77
Suspicious files
770
Text files
681
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c71a.TMP | — | |
MD5:— | SHA256:— | |||
| 7448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c71a.TMP | — | |
MD5:— | SHA256:— | |||
| 7448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c72a.TMP | — | |
MD5:— | SHA256:— | |||
| 7448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c71a.TMP | — | |
MD5:— | SHA256:— | |||
| 7448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c72a.TMP | — | |
MD5:— | SHA256:— | |||
| 7448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
172
DNS requests
243
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7348 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5508 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5508 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7348 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
7348 | firefox.exe | POST | 200 | 95.101.54.131:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7348 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7348 | firefox.exe | POST | 200 | 95.101.54.131:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7348 | firefox.exe | POST | 200 | 95.101.54.131:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7448 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7680 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7680 | chrome.exe | 142.250.153.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7680 | chrome.exe | 185.199.108.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
camo.githubusercontent.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| whitelisted |