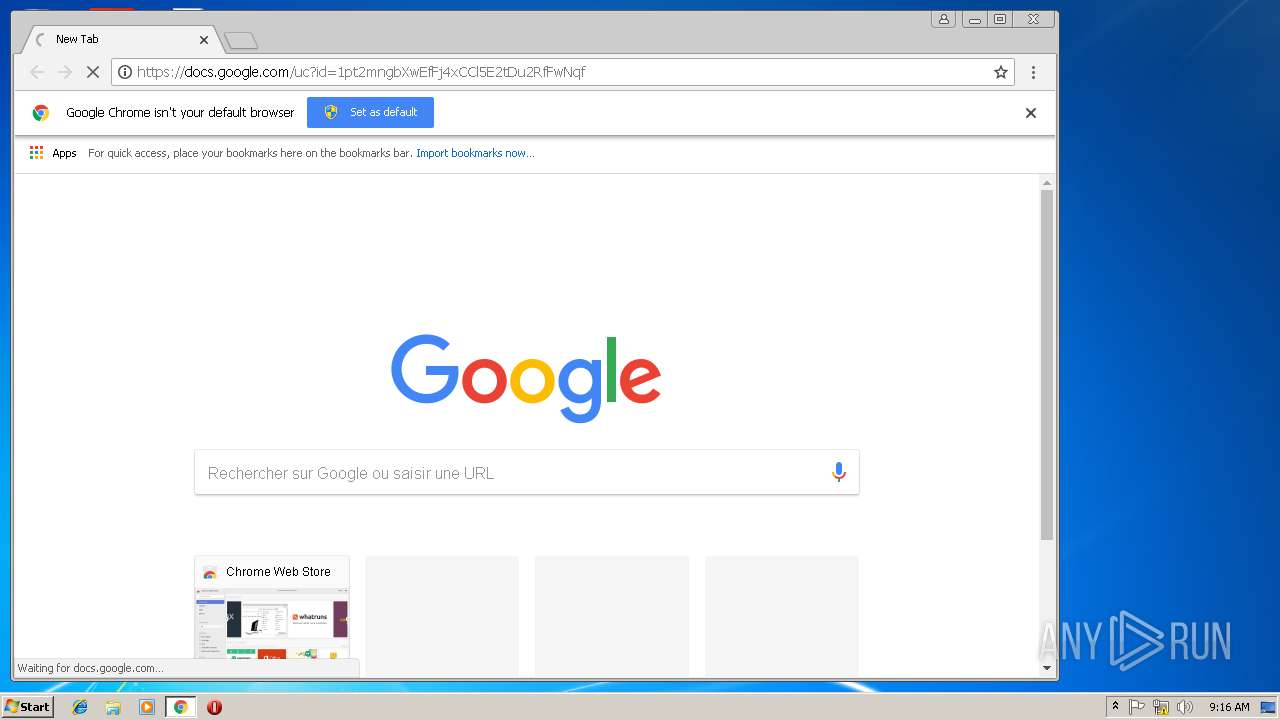
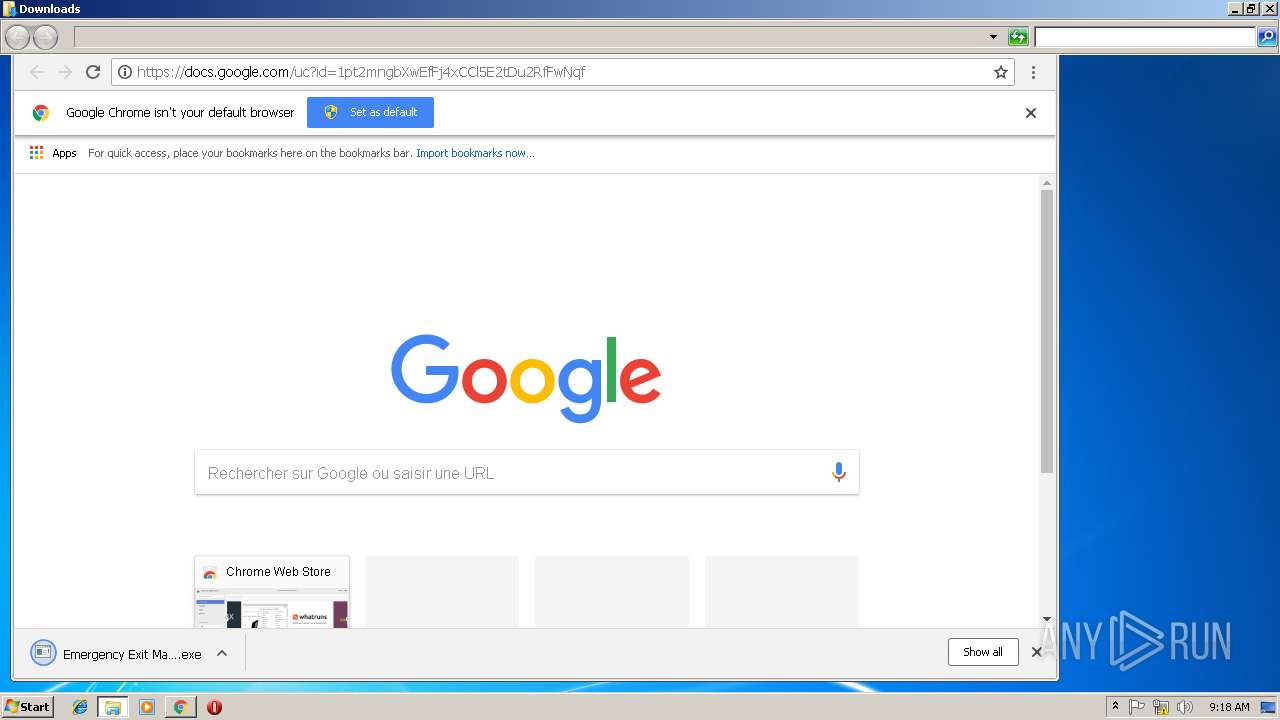
| URL: | https://docs.google.com/uc?id=1pt2mngbXwEfFj4xCCl5E2tDu2RfFwNqf |
| Full analysis: | https://app.any.run/tasks/e77ce07d-ef87-403c-9ff8-820bc404df5a |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 09:15:29 |
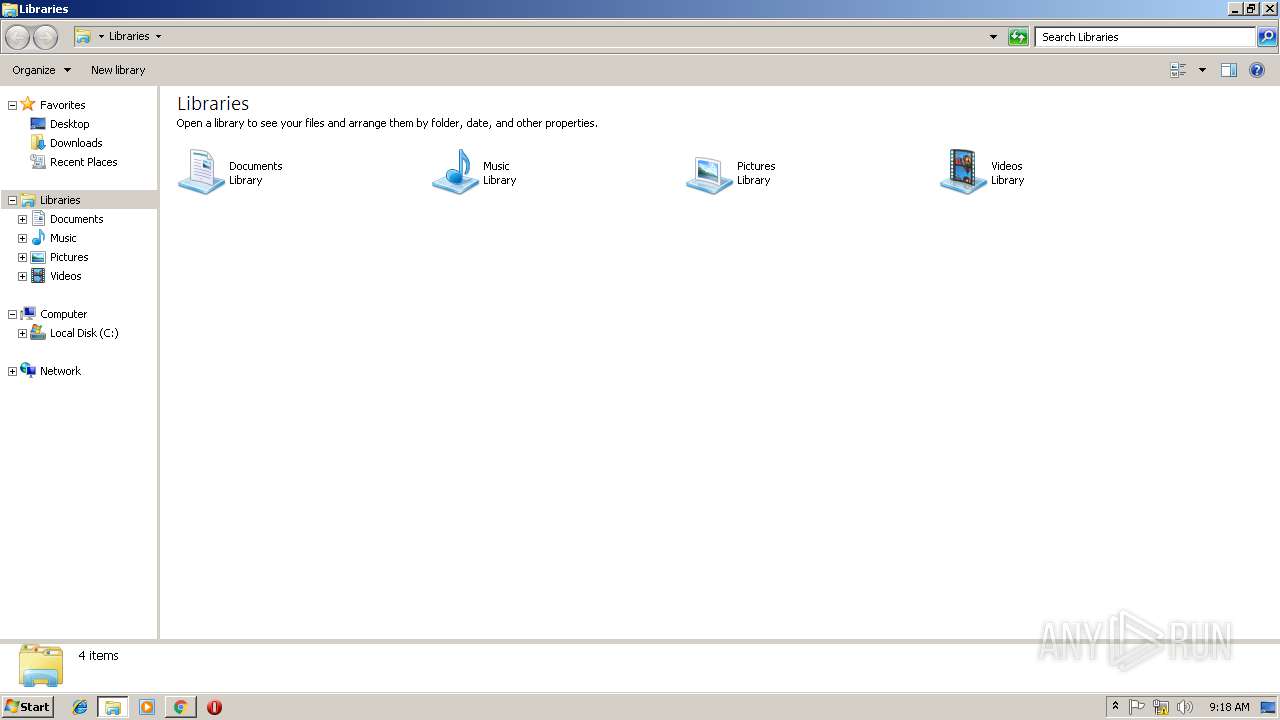
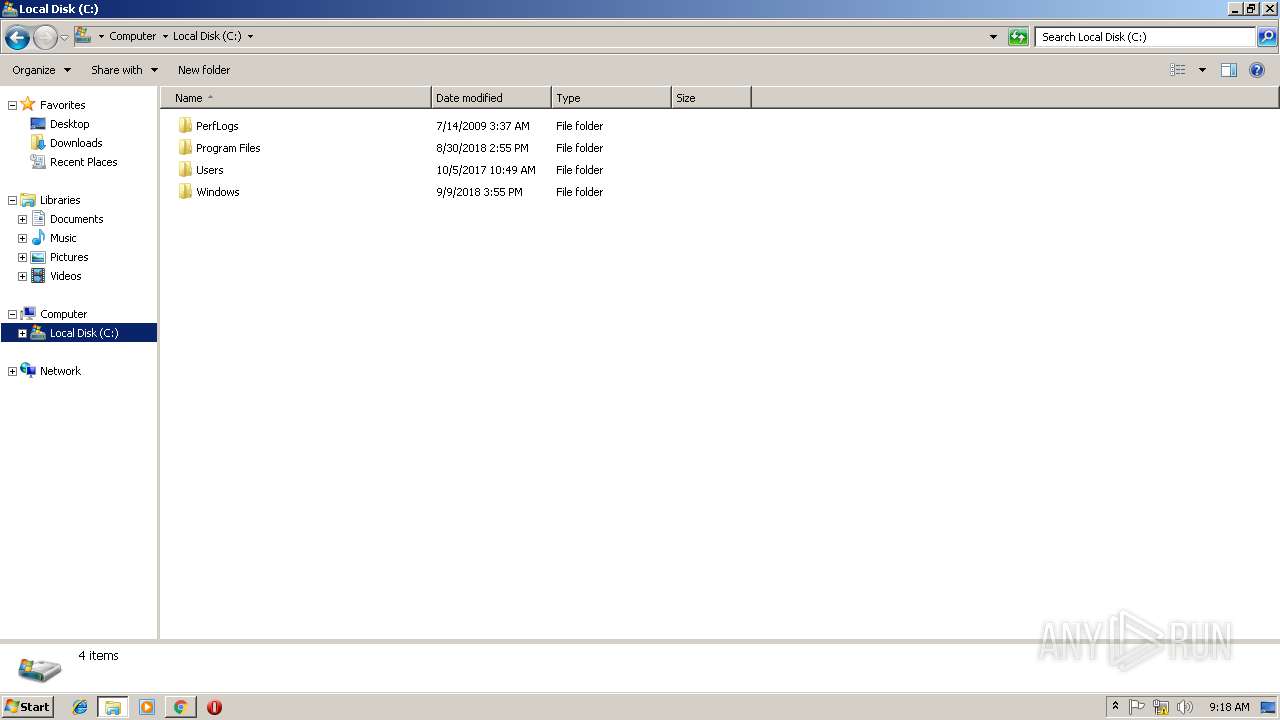
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BC002D961342999F856E66C88E160ED4 |
| SHA1: | 899FA63EA0D203EC3449EA88566E45B3D235641B |
| SHA256: | 8E65B8DA04EF27DA742AA0C47EABCB7019621EF64D832B56506D0D66ED77D2AB |
| SSDEEP: | 3:N8SP3u2NMuC/SGj9yuAD:2Sm2HCa0odD |
MALICIOUS
Connects to CnC server
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 4032)
- iexplore.exe (PID: 2780)
- iexplore.exe (PID: 2200)
- iexplore.exe (PID: 4040)
- iexplore.exe (PID: 1076)
- iexplore.exe (PID: 3020)
- iexplore.exe (PID: 3580)
- iexplore.exe (PID: 3368)
- iexplore.exe (PID: 1436)
- iexplore.exe (PID: 3340)
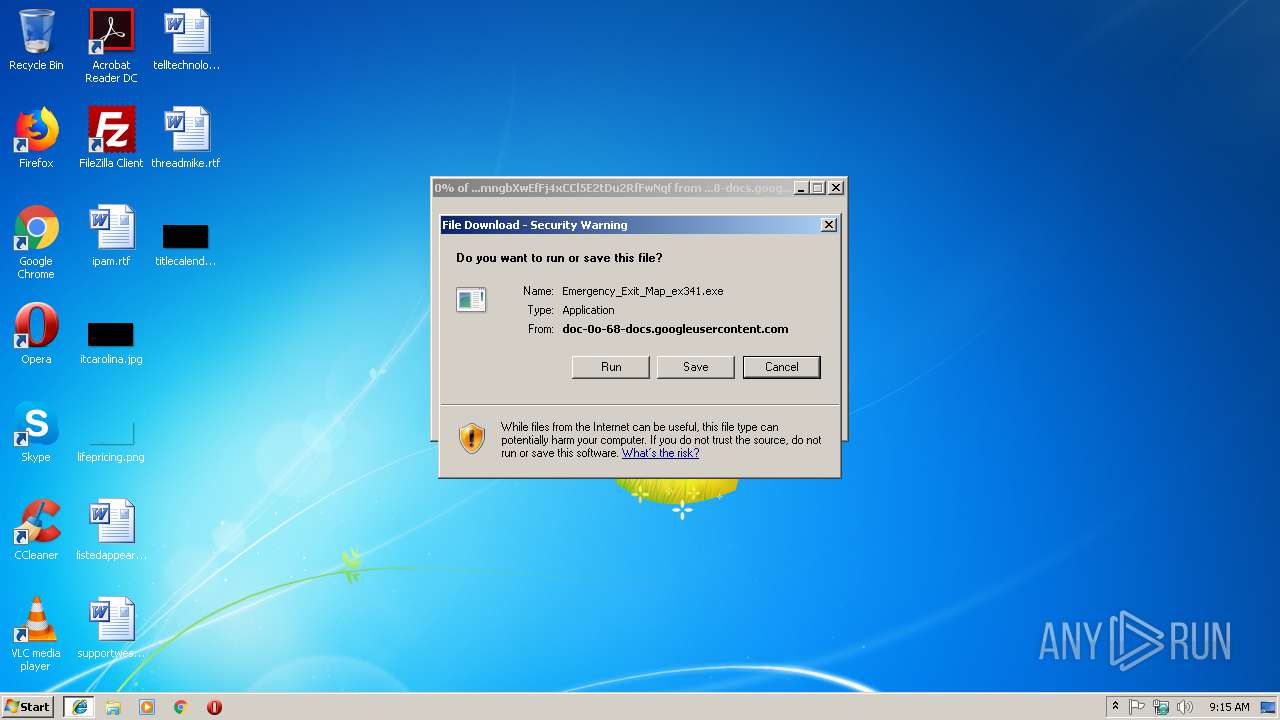
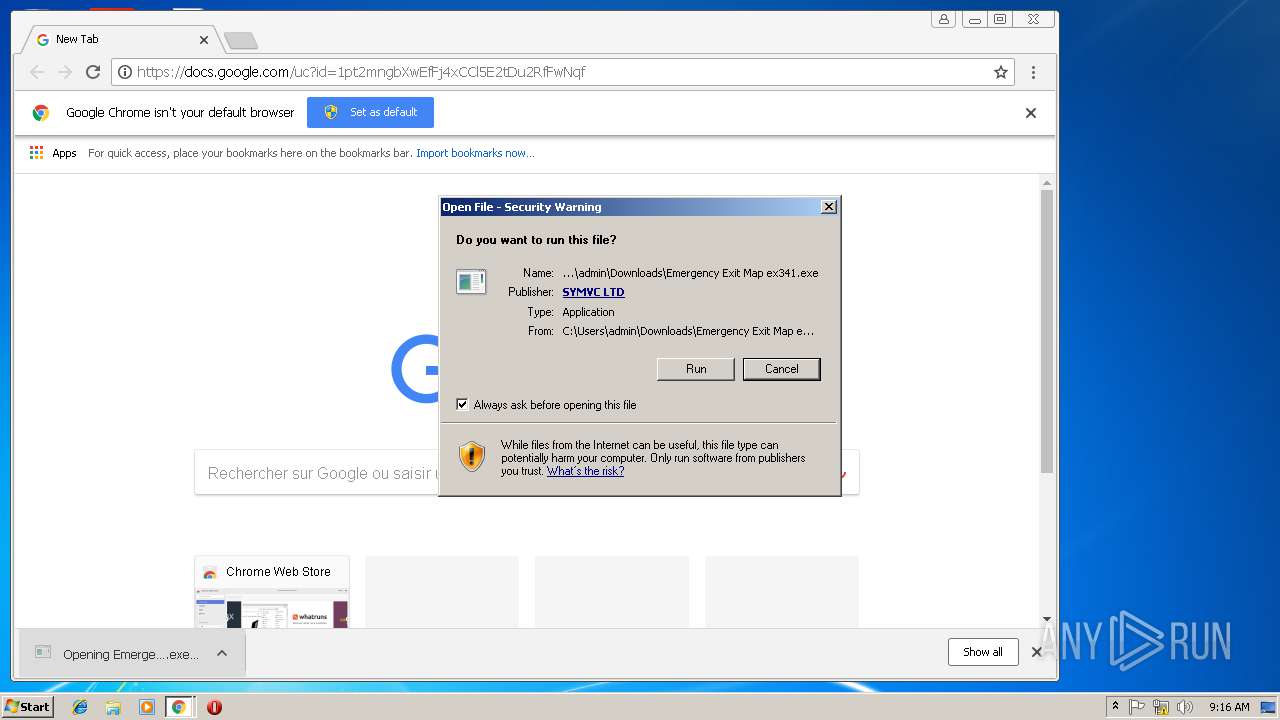
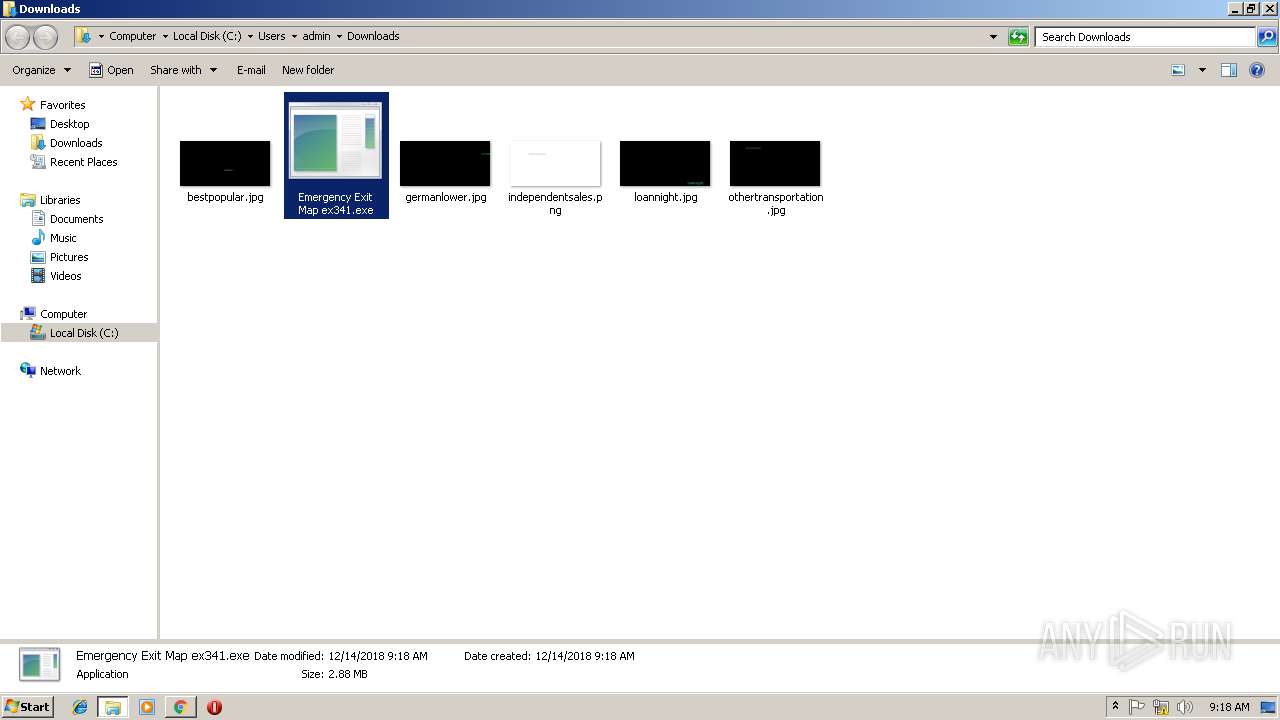
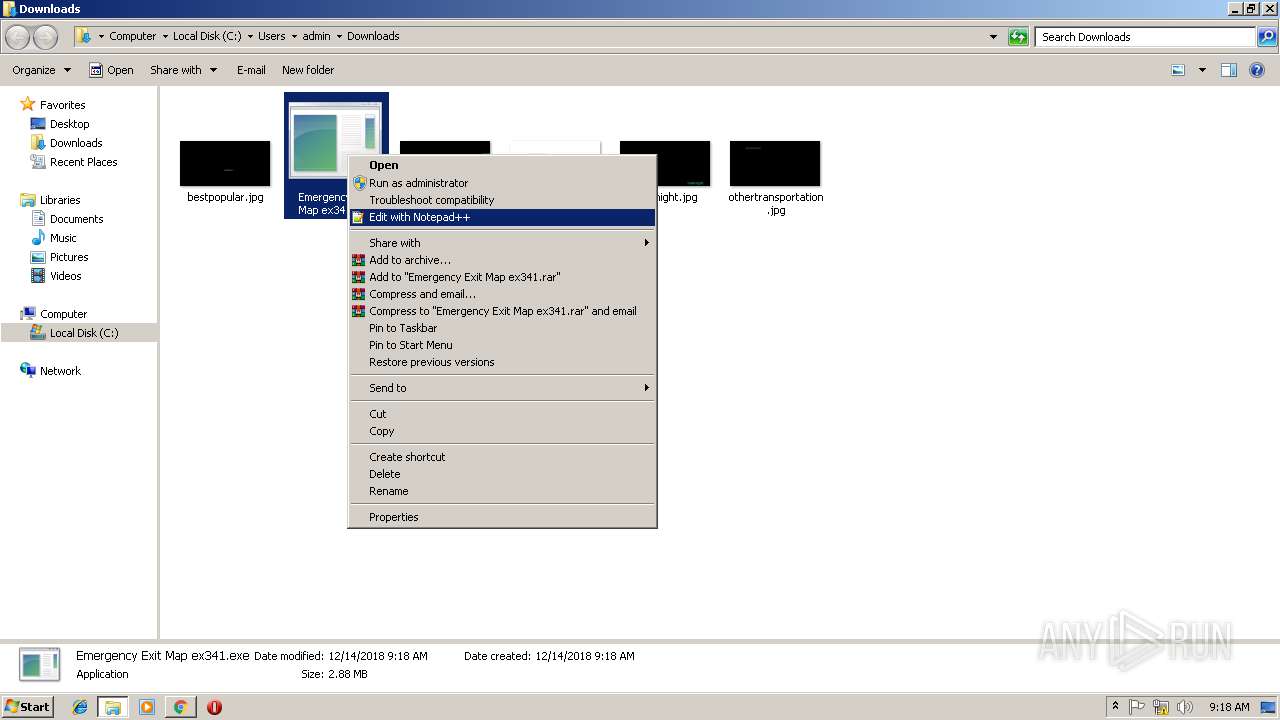
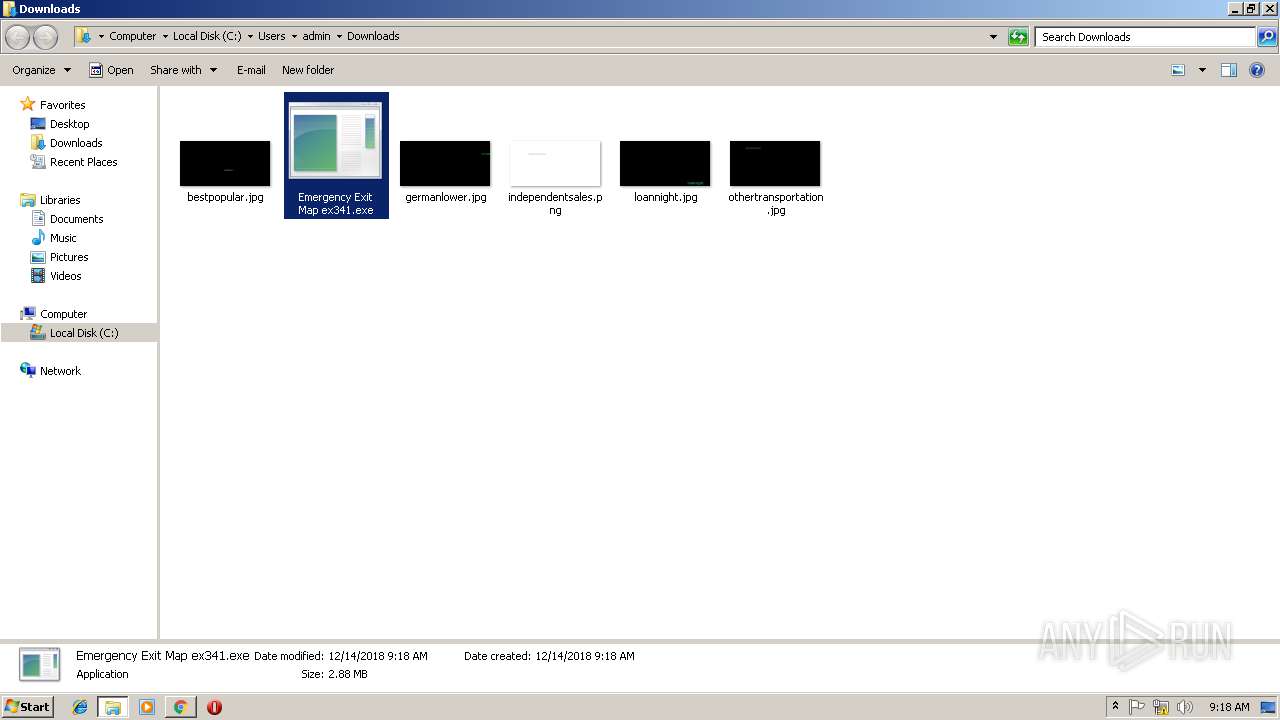
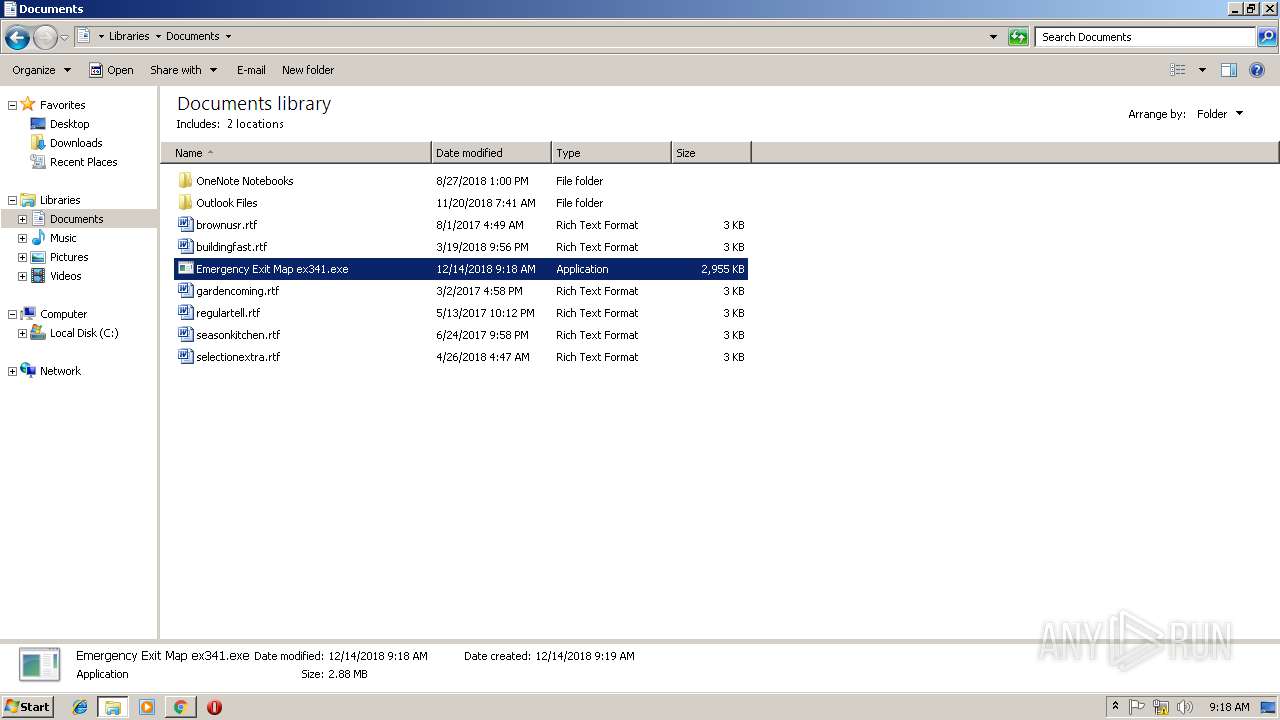
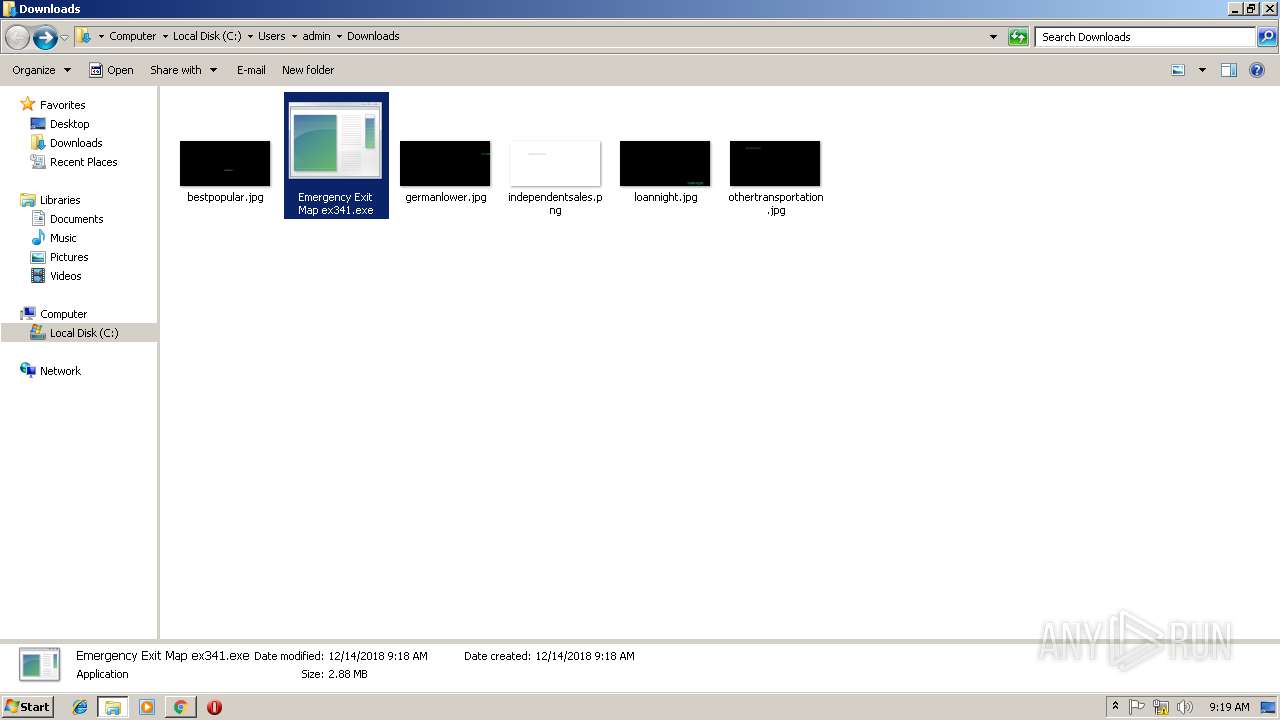
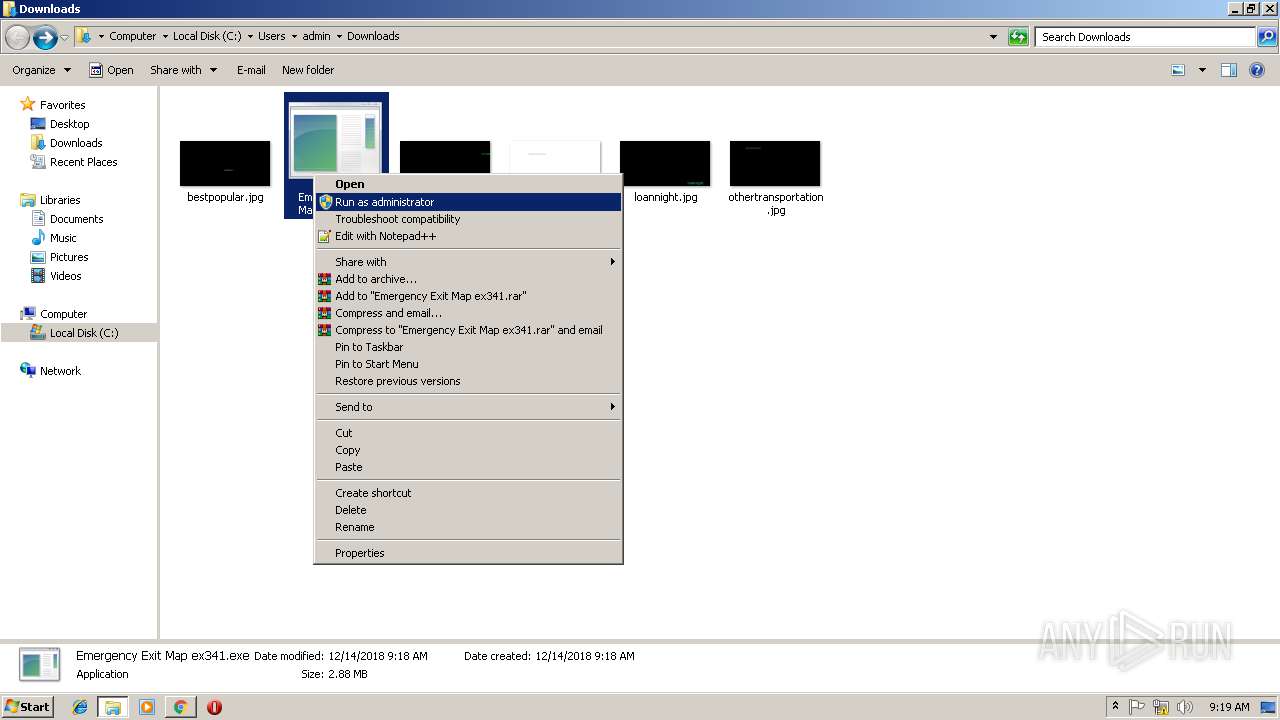
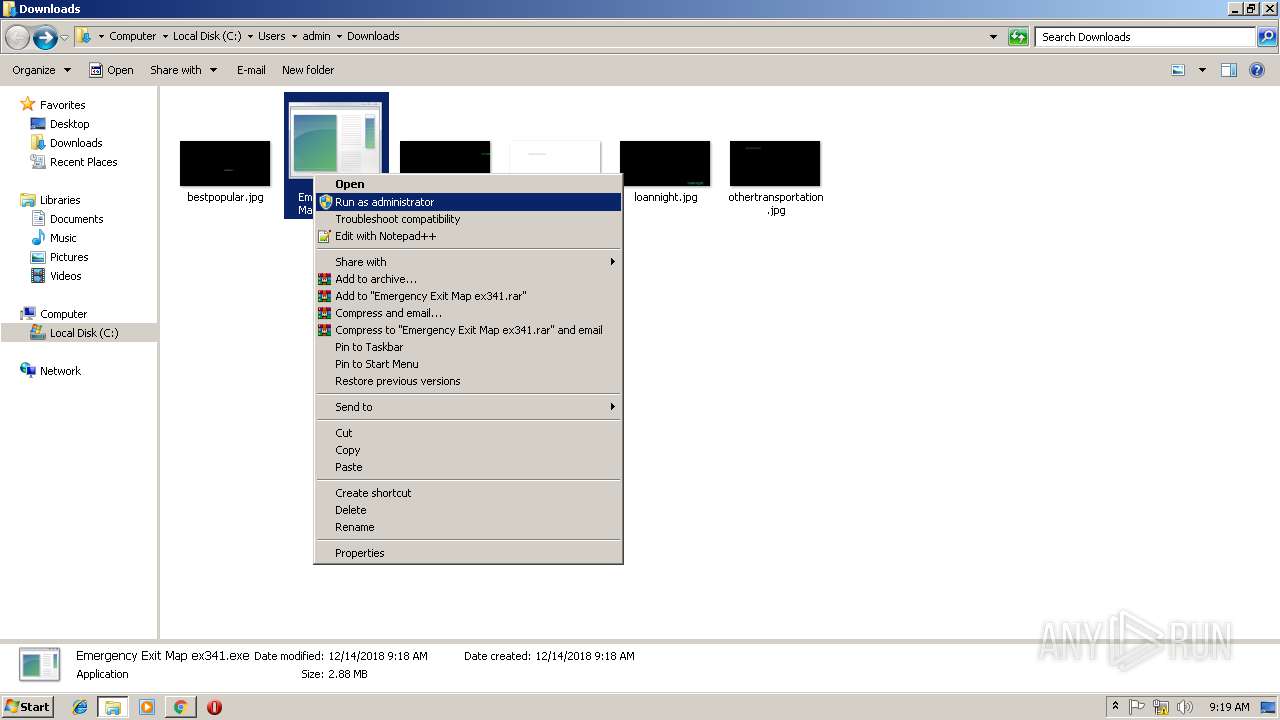
Application was dropped or rewritten from another process
- 1pt2mngbXwEfFj4xCCl5E2tDu2RfFwNqf[1].exe (PID: 2924)
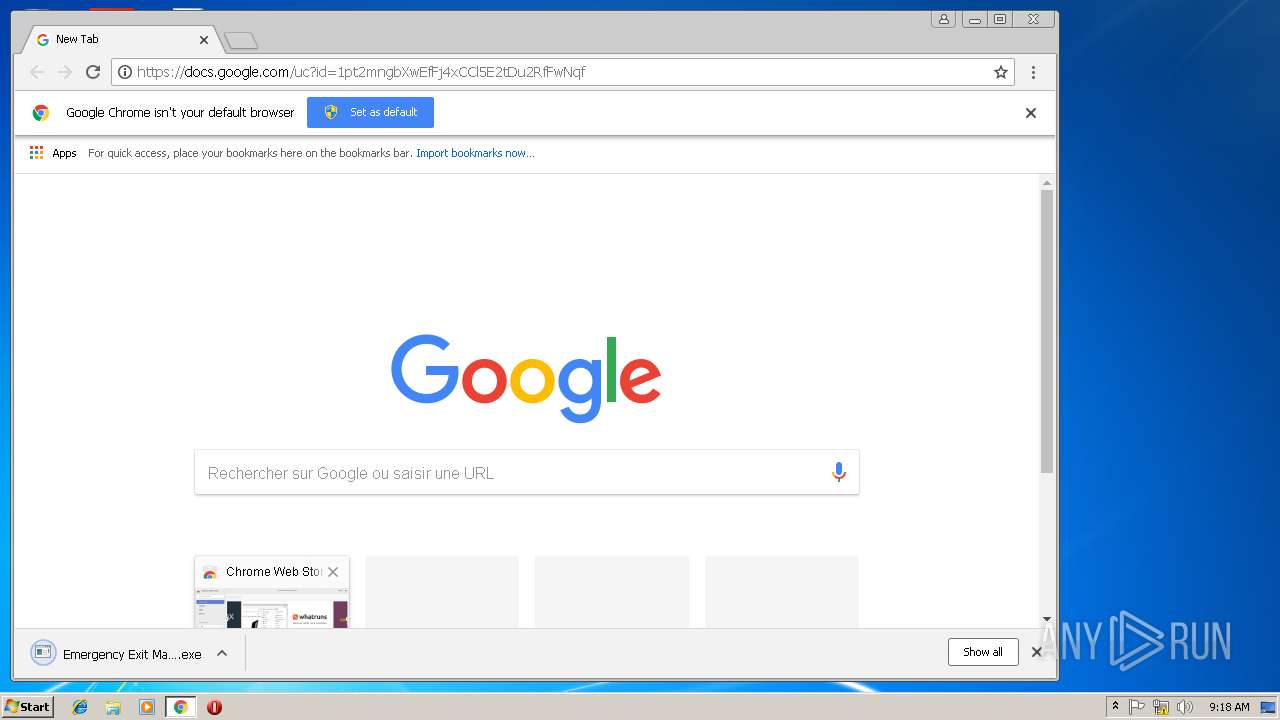
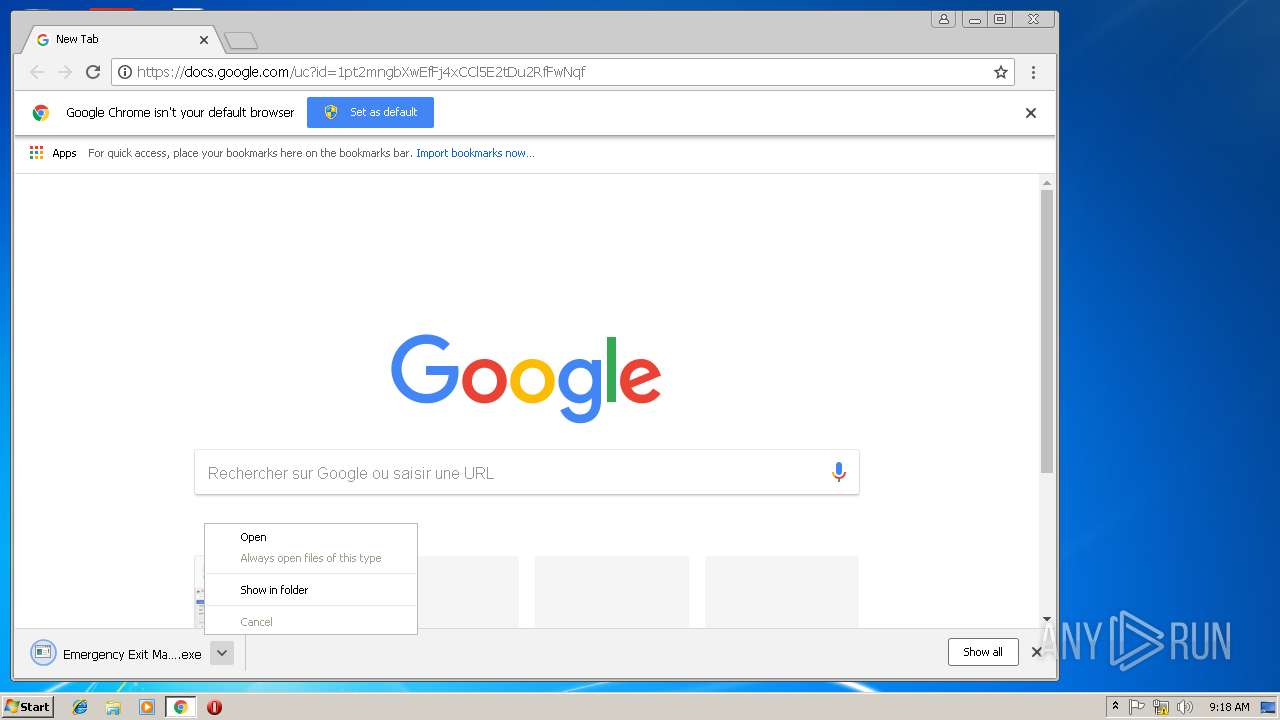
- Emergency Exit Map ex341.exe (PID: 1724)
- Emergency Exit Map ex341.exe (PID: 3696)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 3028)
- chrome.exe (PID: 3216)
INFO
Application launched itself
- iexplore.exe (PID: 2864)
- chrome.exe (PID: 3216)
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 3324)
- iexplore.exe (PID: 2984)
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 3432)
- iexplore.exe (PID: 2696)
- iexplore.exe (PID: 1696)
Reads Internet Cache Settings
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 3028)
- iexplore.exe (PID: 4032)
- chrome.exe (PID: 3216)
- iexplore.exe (PID: 2780)
- iexplore.exe (PID: 2200)
- iexplore.exe (PID: 4040)
- iexplore.exe (PID: 1076)
- iexplore.exe (PID: 3020)
- iexplore.exe (PID: 3368)
- iexplore.exe (PID: 2348)
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3580)
- iexplore.exe (PID: 1436)
Reads internet explorer settings
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 4032)
- iexplore.exe (PID: 2780)
- iexplore.exe (PID: 2200)
- iexplore.exe (PID: 4040)
- iexplore.exe (PID: 1076)
- iexplore.exe (PID: 3580)
- iexplore.exe (PID: 3368)
- iexplore.exe (PID: 2348)
- iexplore.exe (PID: 3020)
- iexplore.exe (PID: 1436)
- iexplore.exe (PID: 3340)
Changes internet zones settings
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 3324)
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 2984)
- iexplore.exe (PID: 2264)
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 2352)
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 3432)
- iexplore.exe (PID: 1696)
- iexplore.exe (PID: 2696)
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 3860)
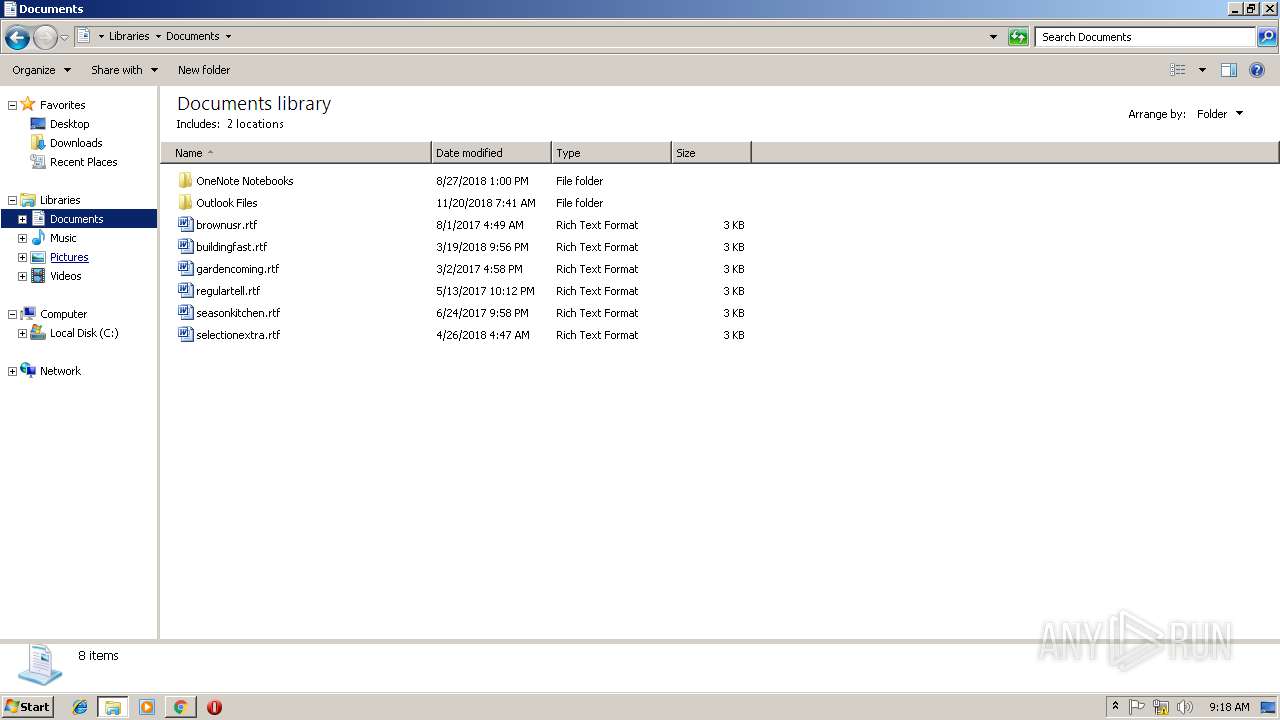
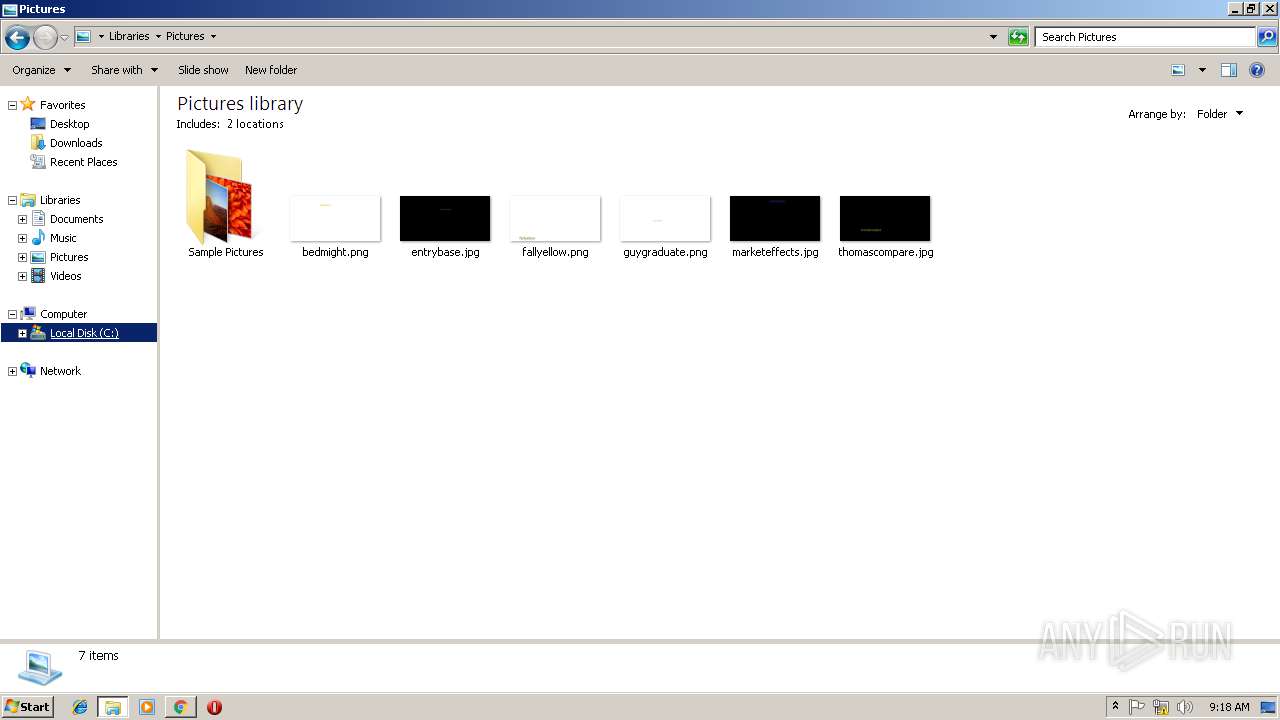
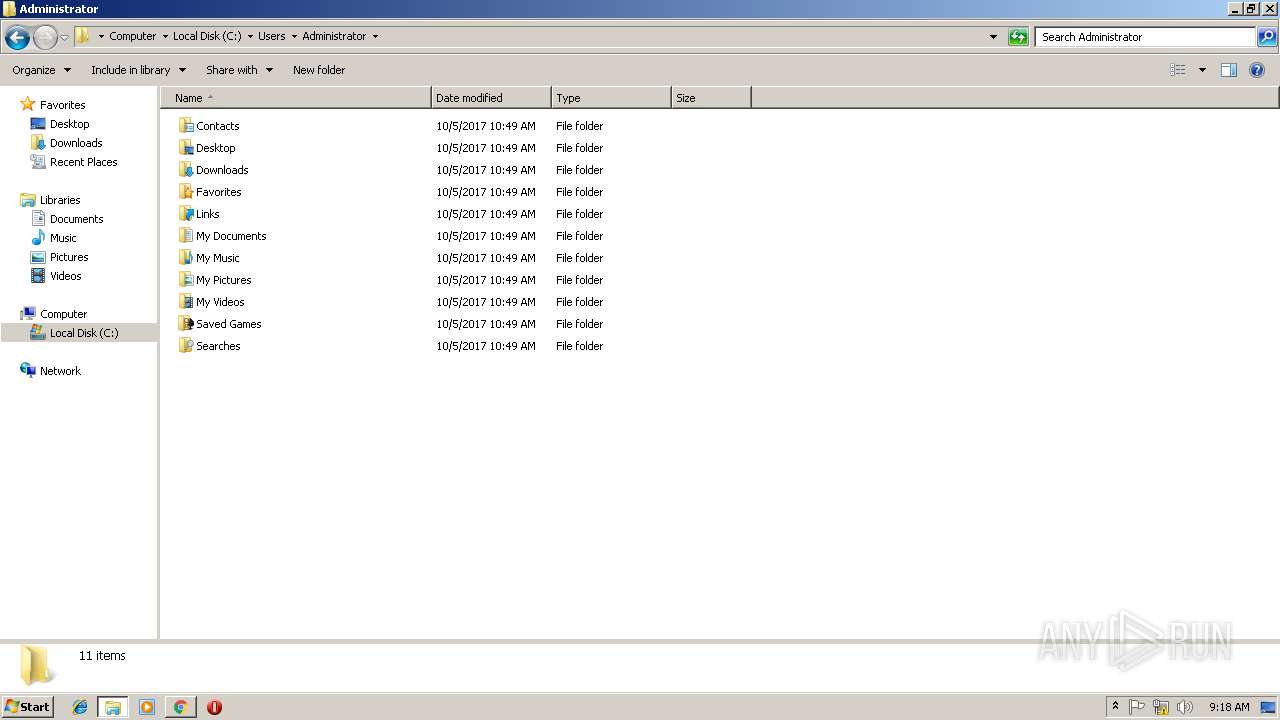
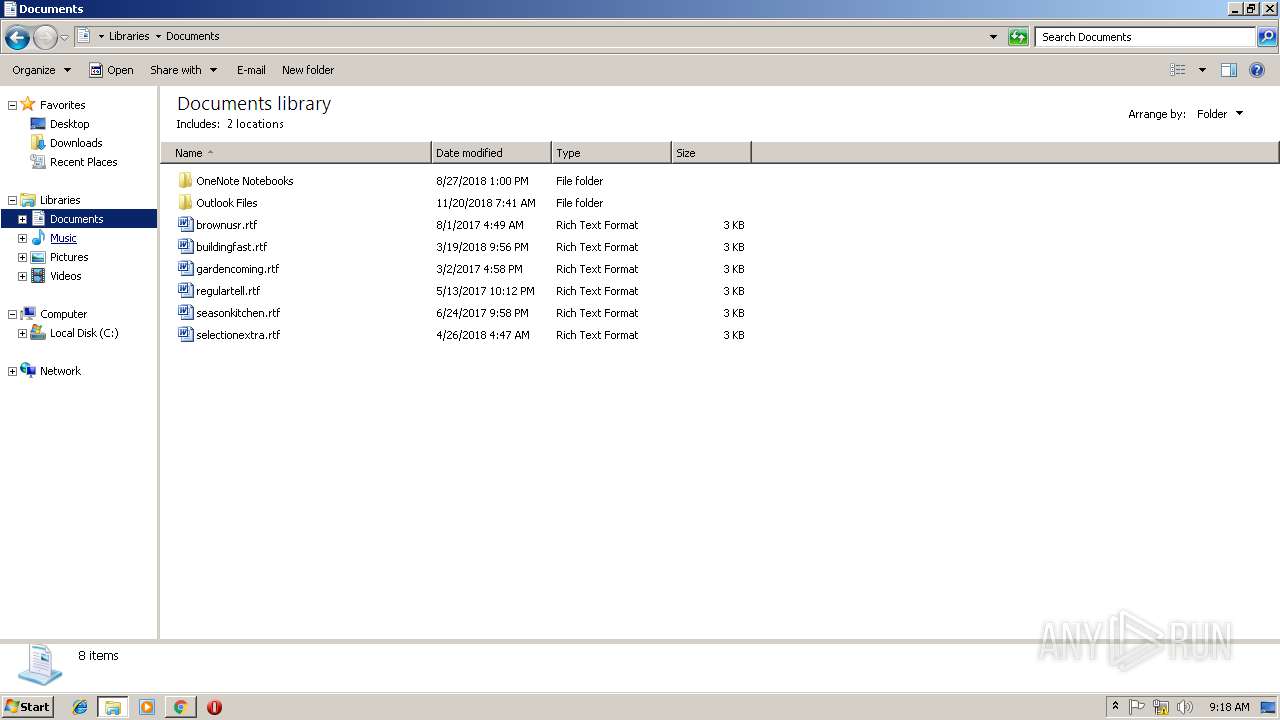
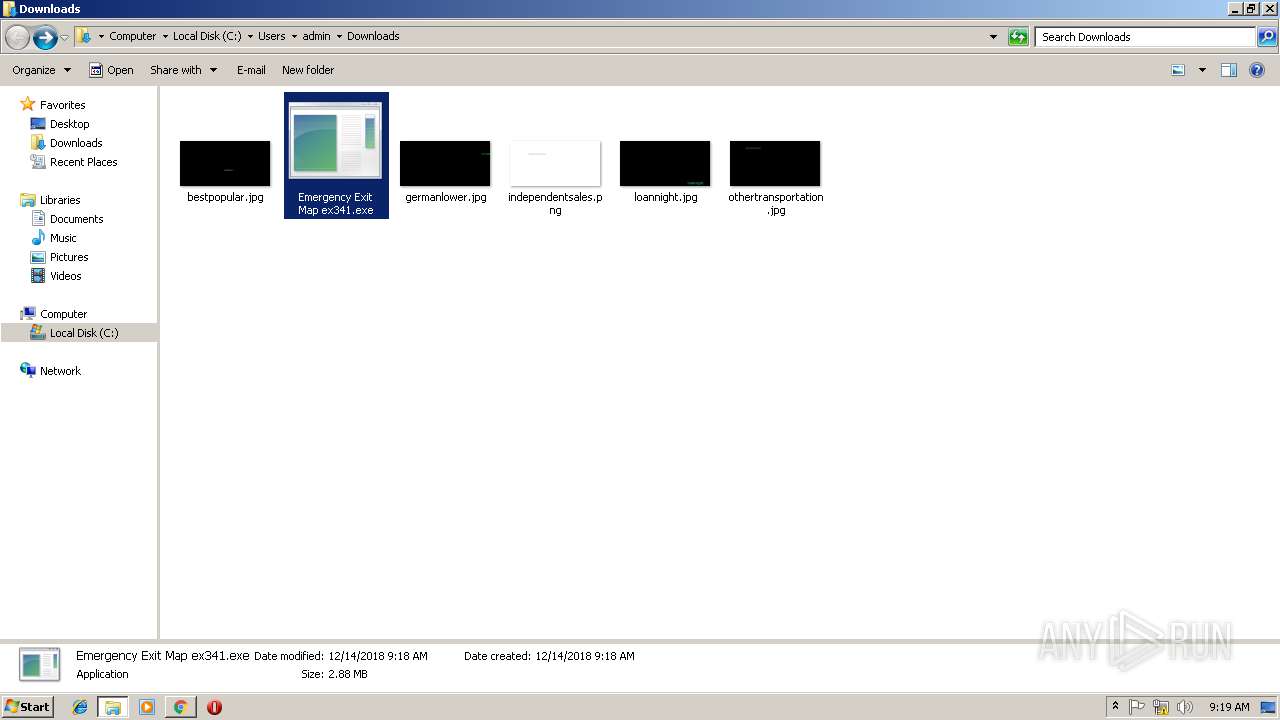
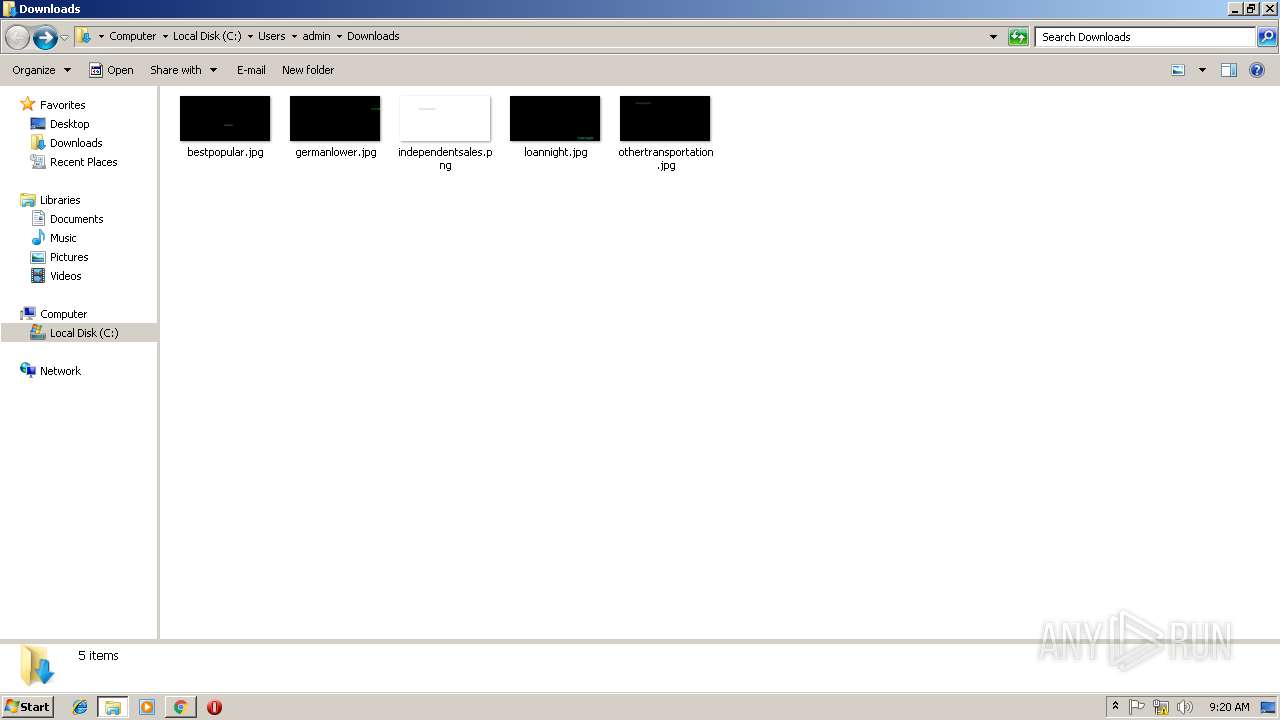
Creates files in the user directory
- iexplore.exe (PID: 3028)
Reads settings of System Certificates
- chrome.exe (PID: 3216)
Changes settings of System certificates
- chrome.exe (PID: 3216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
47
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1076 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2352 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3860 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=896,1041666173456702236,8163803520766762002,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=F1AC2BEDF6F377BDA6E85AA62B7CB469 --mojo-platform-channel-handle=4012 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=896,1041666173456702236,8163803520766762002,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=39E361472562F4D2B6A8FFCA8A9C2681 --mojo-platform-channel-handle=2452 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1664 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
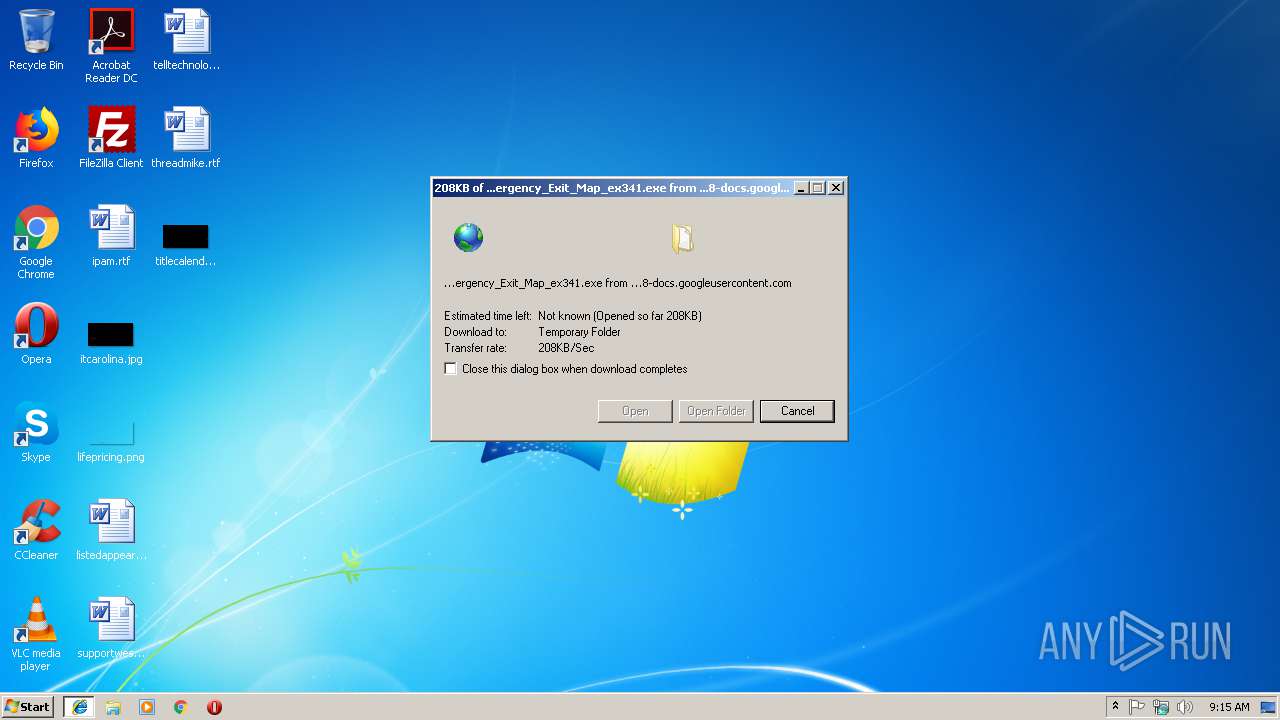
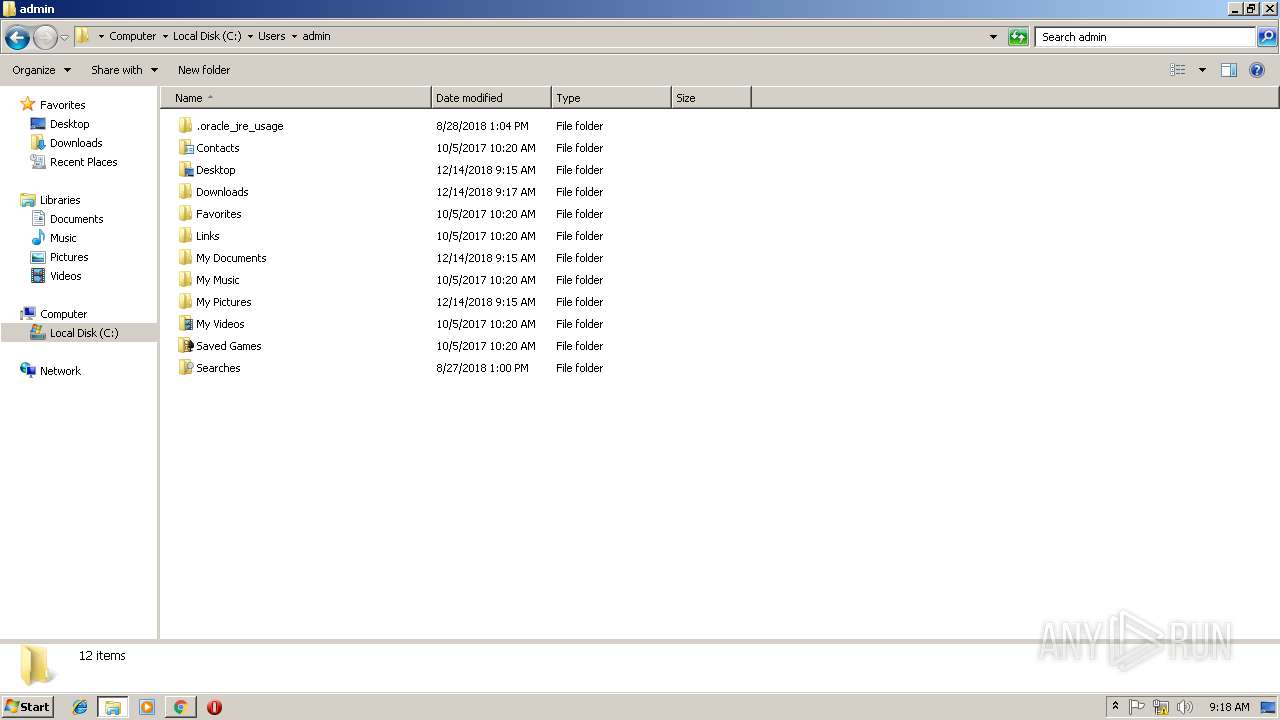
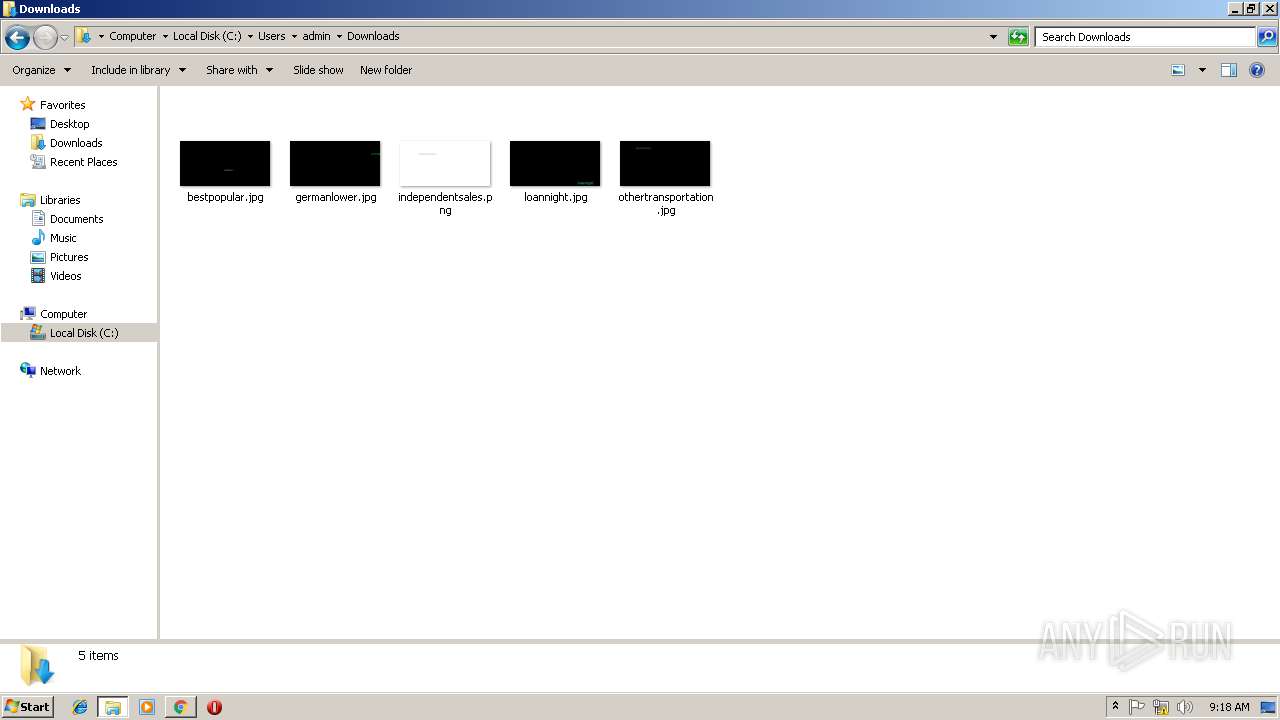
| 1724 | "C:\Users\admin\Downloads\Emergency Exit Map ex341.exe" | C:\Users\admin\Downloads\Emergency Exit Map ex341.exe | — | chrome.exe | |||||||||||
User: admin Company: Google, inc Integrity Level: MEDIUM Description: Android ADB API Exit code: 183 Version: 2.0.0.0 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,1041666173456702236,8163803520766762002,131072 --enable-features=PasswordImport --service-pipe-token=182452A9D0AE118E74CCB4AEB4917ECC --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=182452A9D0AE118E74CCB4AEB4917ECC --renderer-client-id=3 --mojo-platform-channel-handle=2096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2264 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2244 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 623
Read events
5 076
Write events
527
Delete events
20
Modification events
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {D6253BC5-FF80-11E8-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070C0005000E0009000F002E00D701 | |||
Executable files
5
Suspicious files
74
Text files
114
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5B4428646E42AF32.TMP | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCEEFC84911846877.TMP | — | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{D6253BC5-FF80-11E8-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEEAF89776FAF70CA.TMP | — | |
MD5:— | SHA256:— | |||
| 3324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{E79B94F4-FF80-11E8-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
43
DNS requests
25
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3784 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3216 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
3860 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3324 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2984 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3768 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3432 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2864 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2264 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1696 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3784 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4032 | iexplore.exe | 213.183.63.183:443 | black-transsexual-hardcore.com | Melbikomas UAB | BG | suspicious |
2864 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3028 | iexplore.exe | 108.177.15.194:443 | docs.google.com | Google Inc. | US | unknown |
3028 | iexplore.exe | 216.58.206.1:443 | doc-0o-68-docs.googleusercontent.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 216.58.206.1:443 | doc-0o-68-docs.googleusercontent.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 108.177.15.194:443 | docs.google.com | Google Inc. | US | unknown |
3216 | chrome.exe | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
3216 | chrome.exe | 216.58.210.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
docs.google.com |
| shared |
doc-0o-68-docs.googleusercontent.com |
| shared |
black-transsexual-hardcore.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3216 | chrome.exe | unknown | SURICATA IPv4 invalid checksum |
11 ETPRO signatures available at the full report