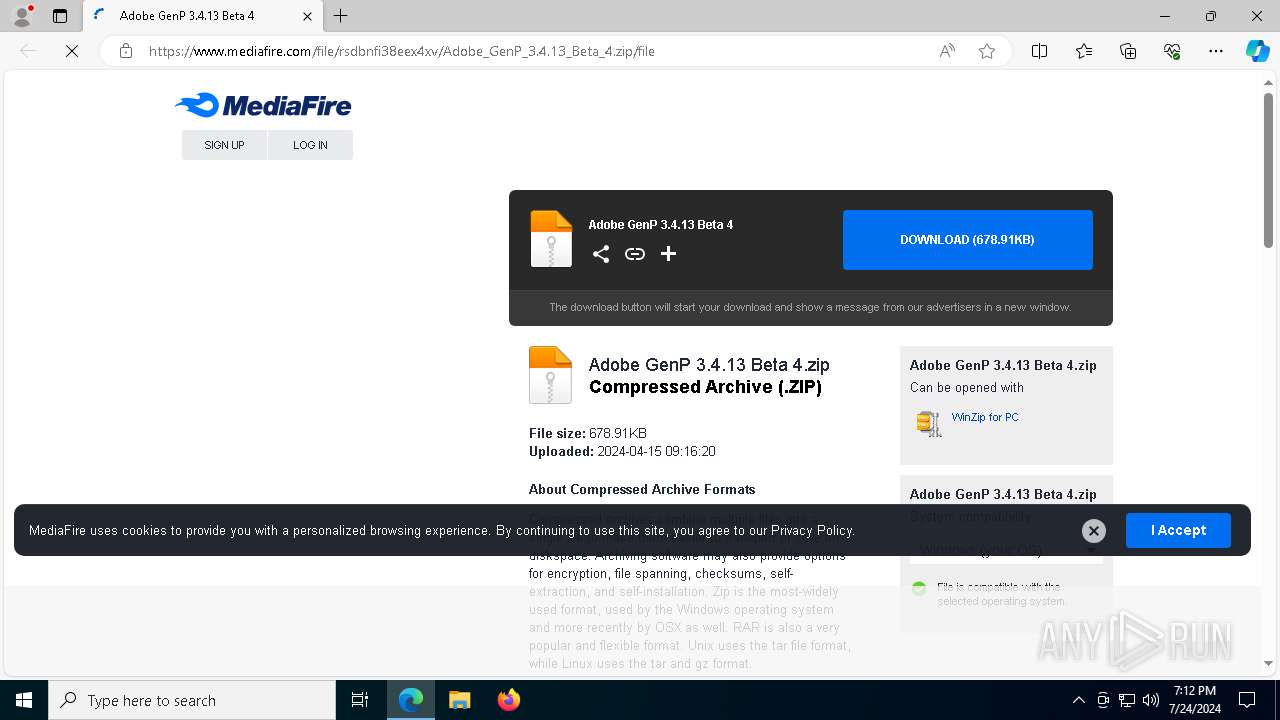
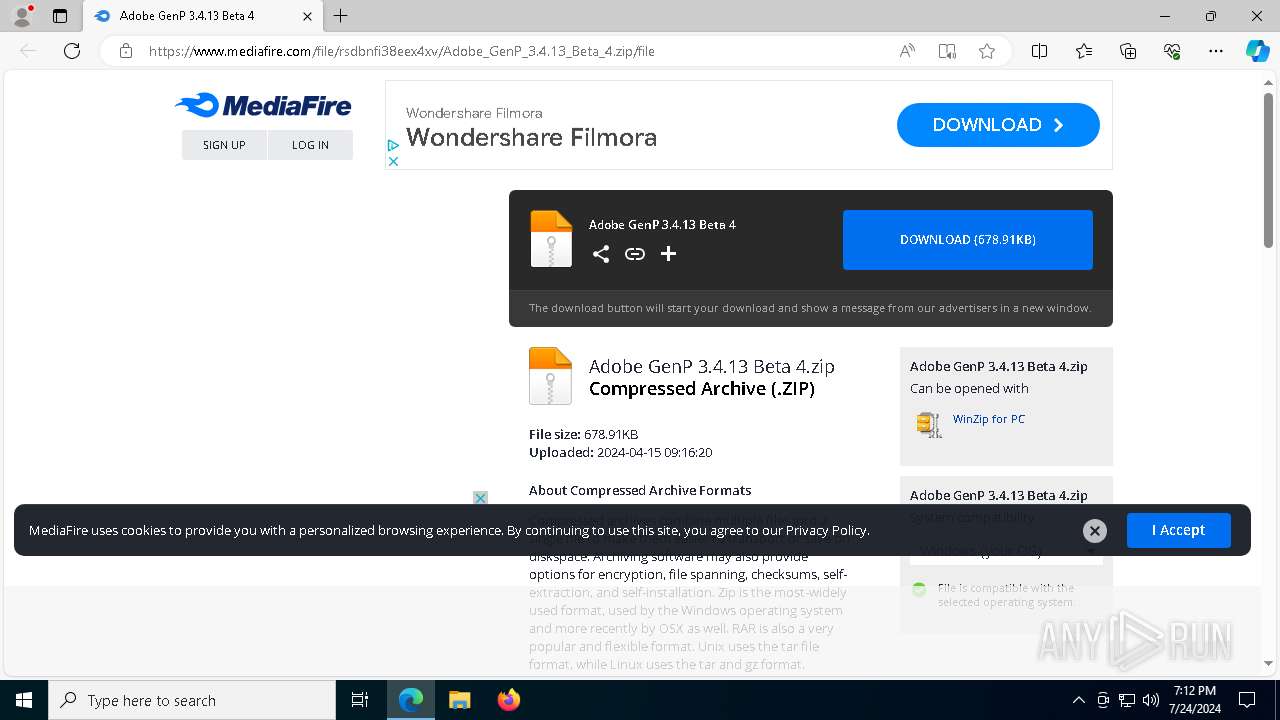
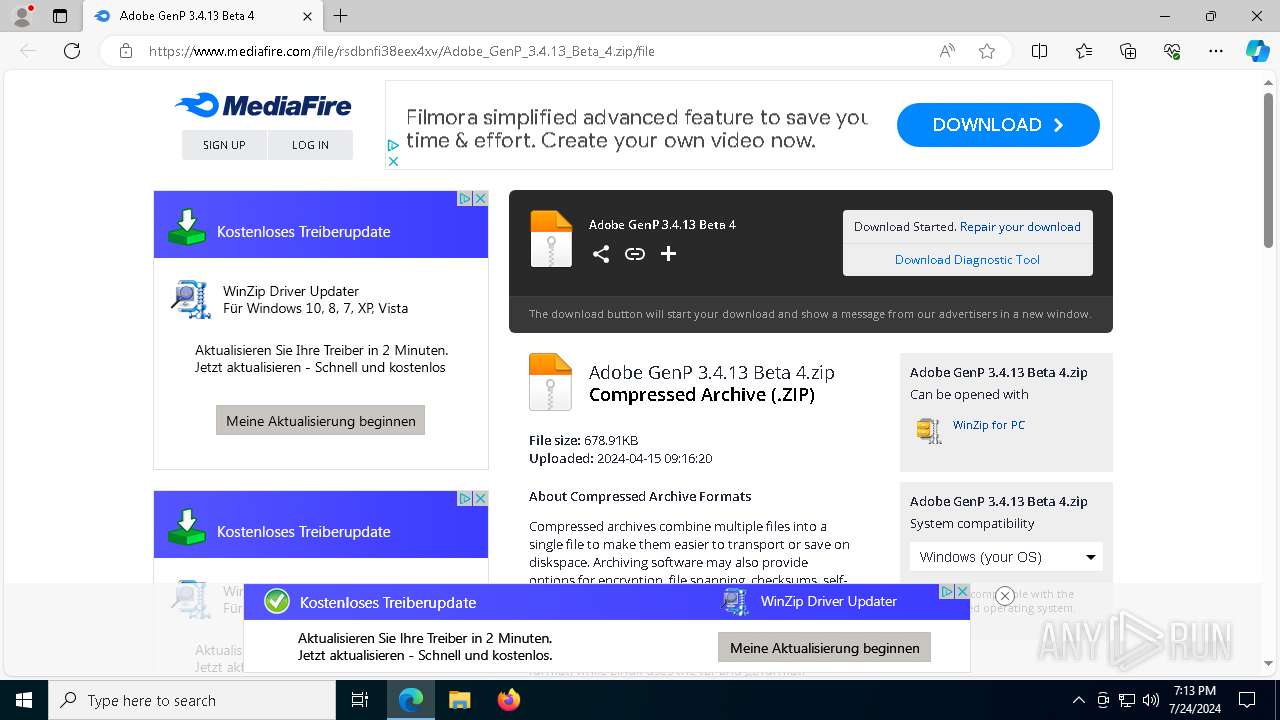
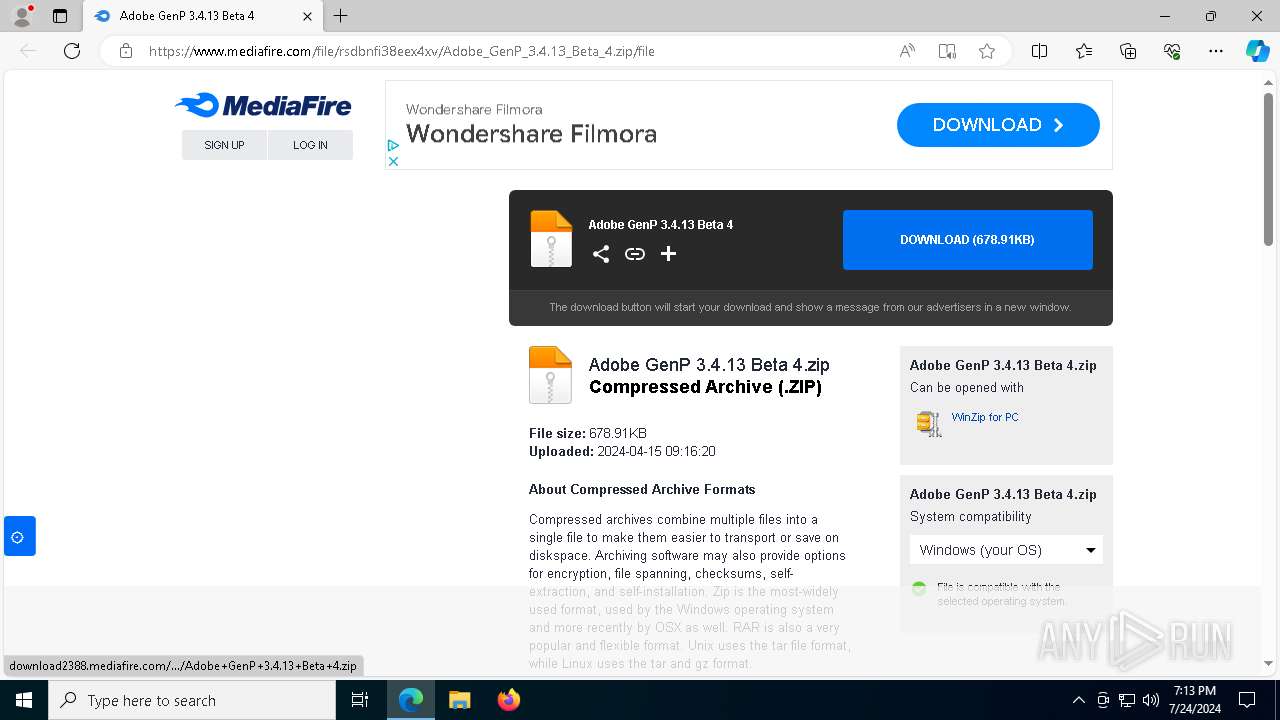
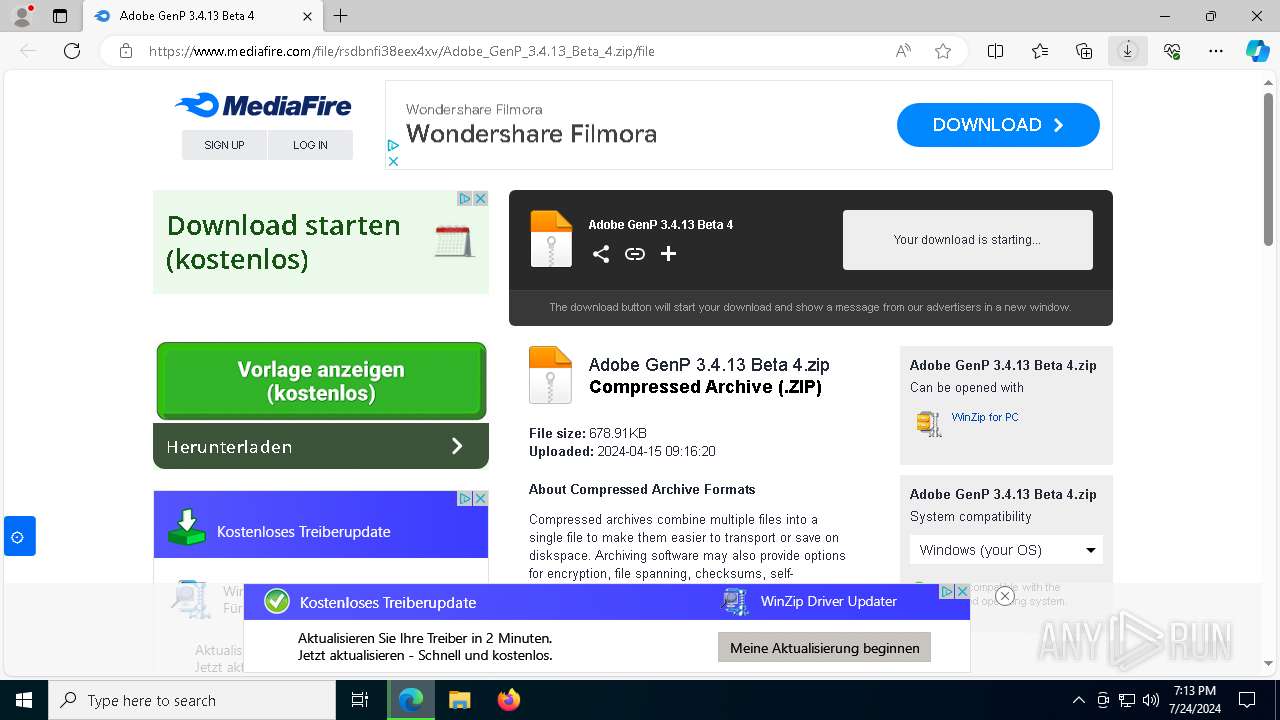
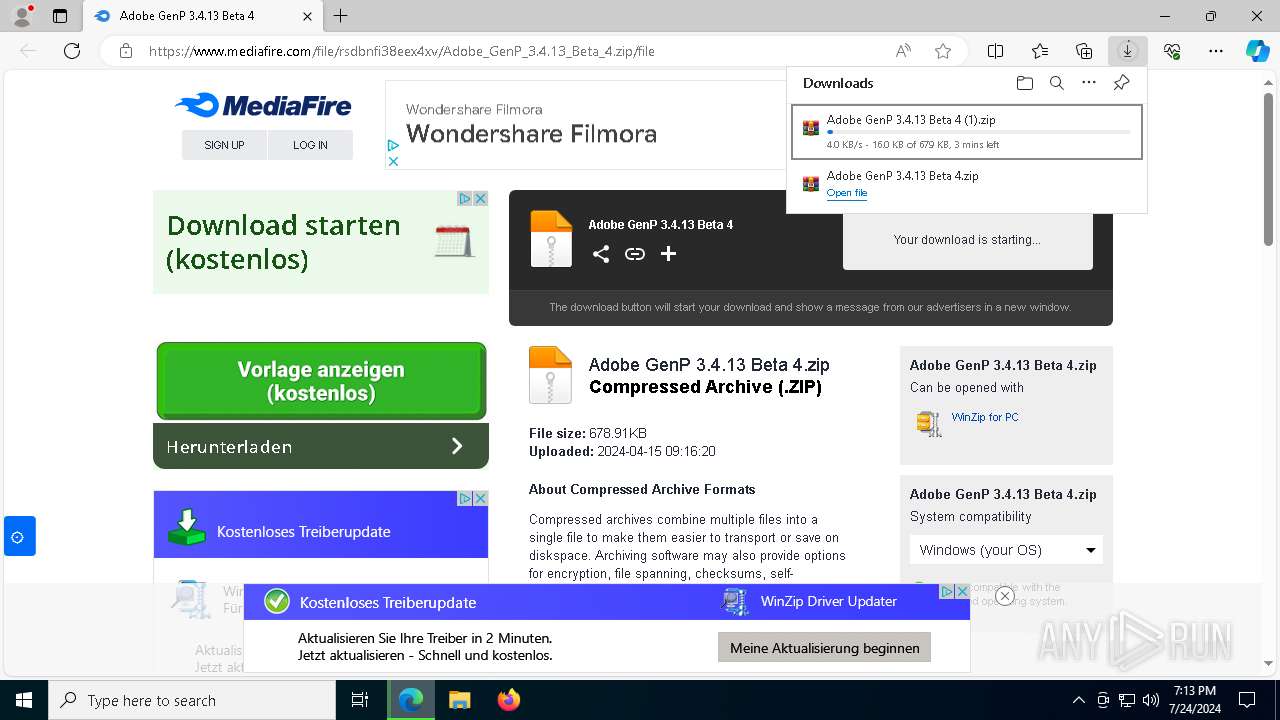
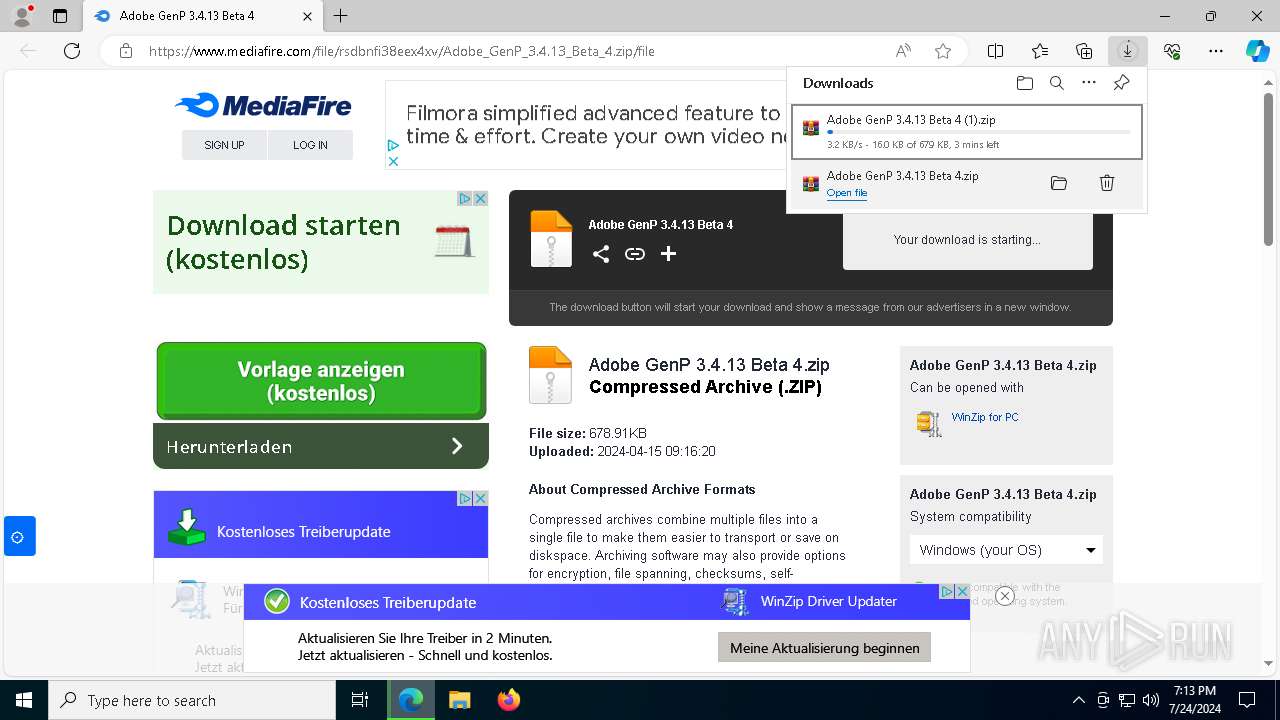
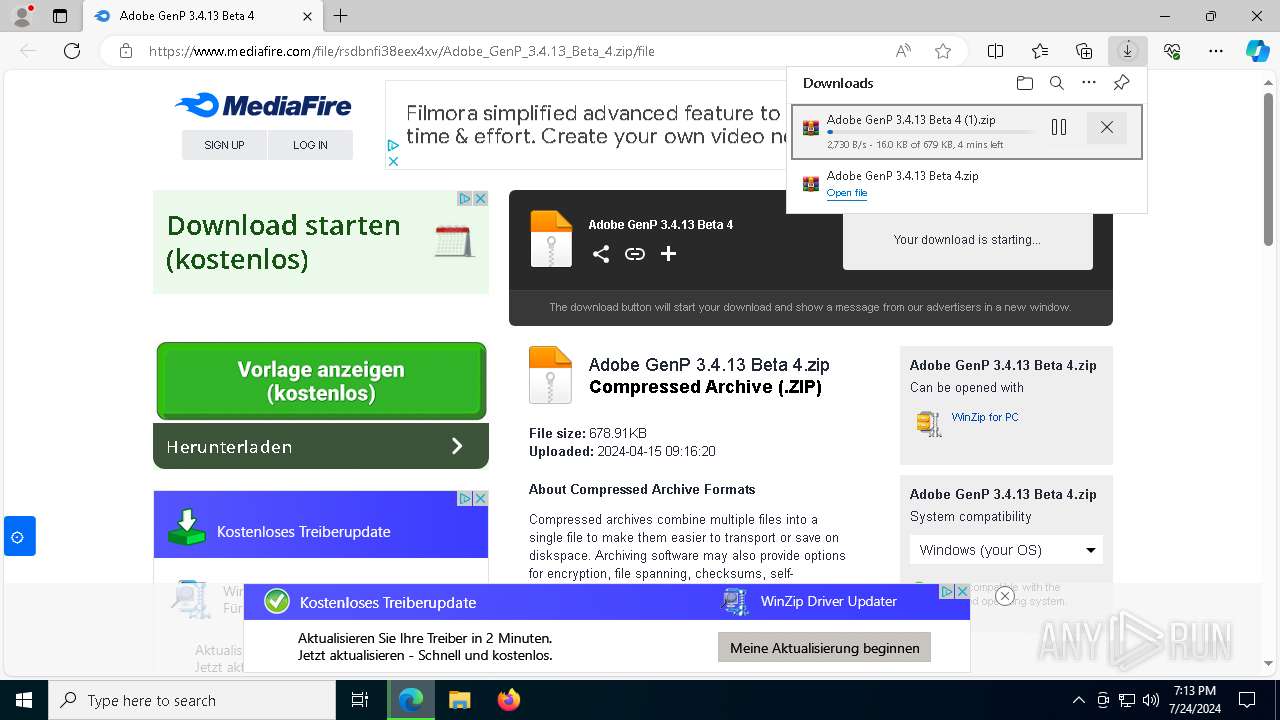
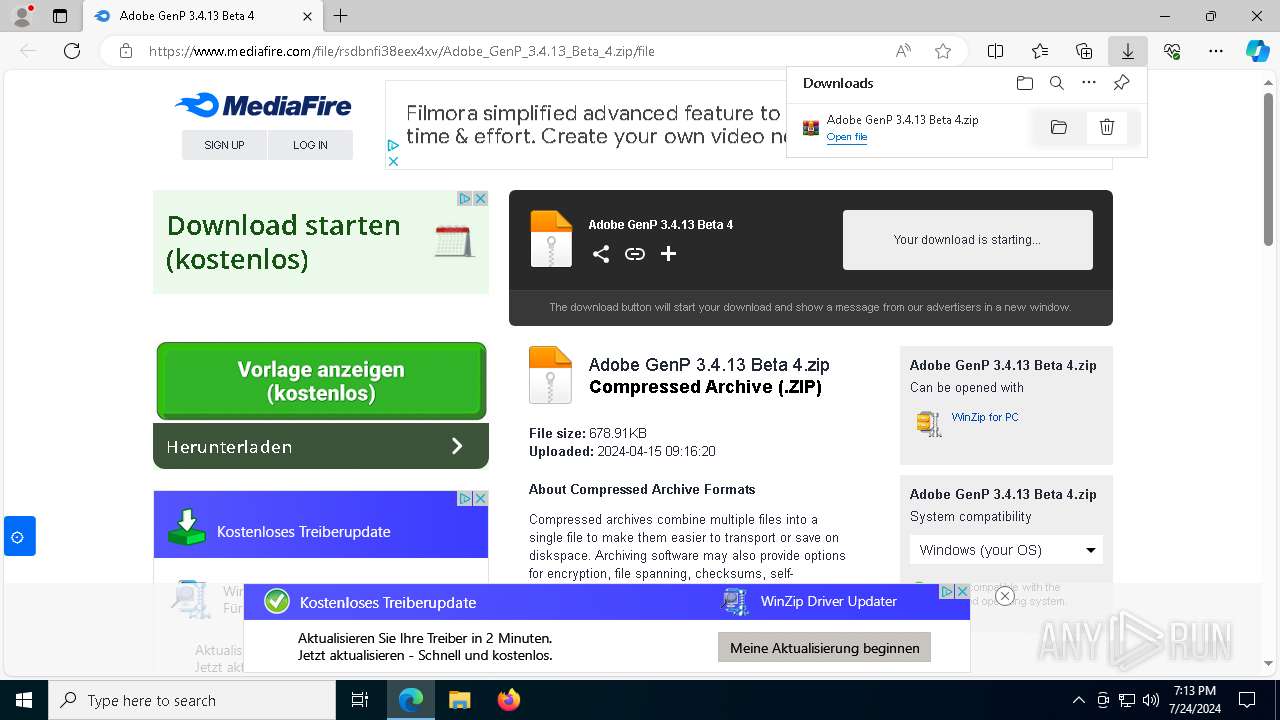
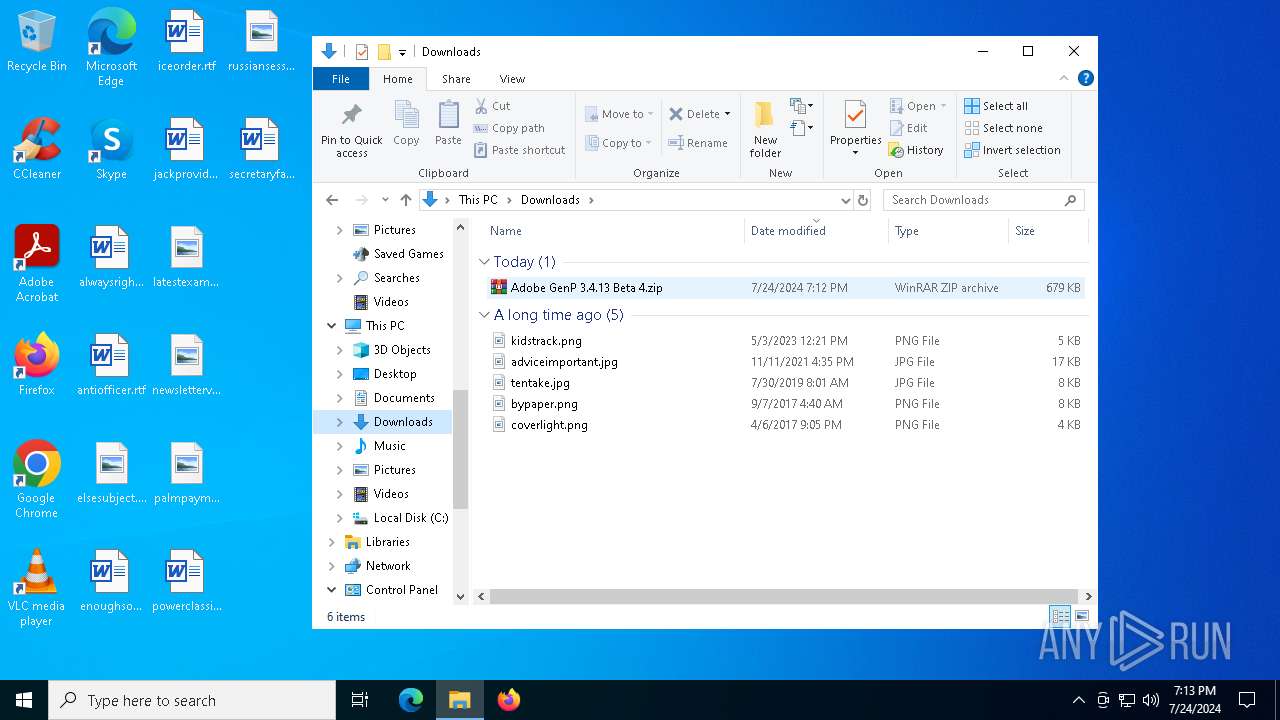
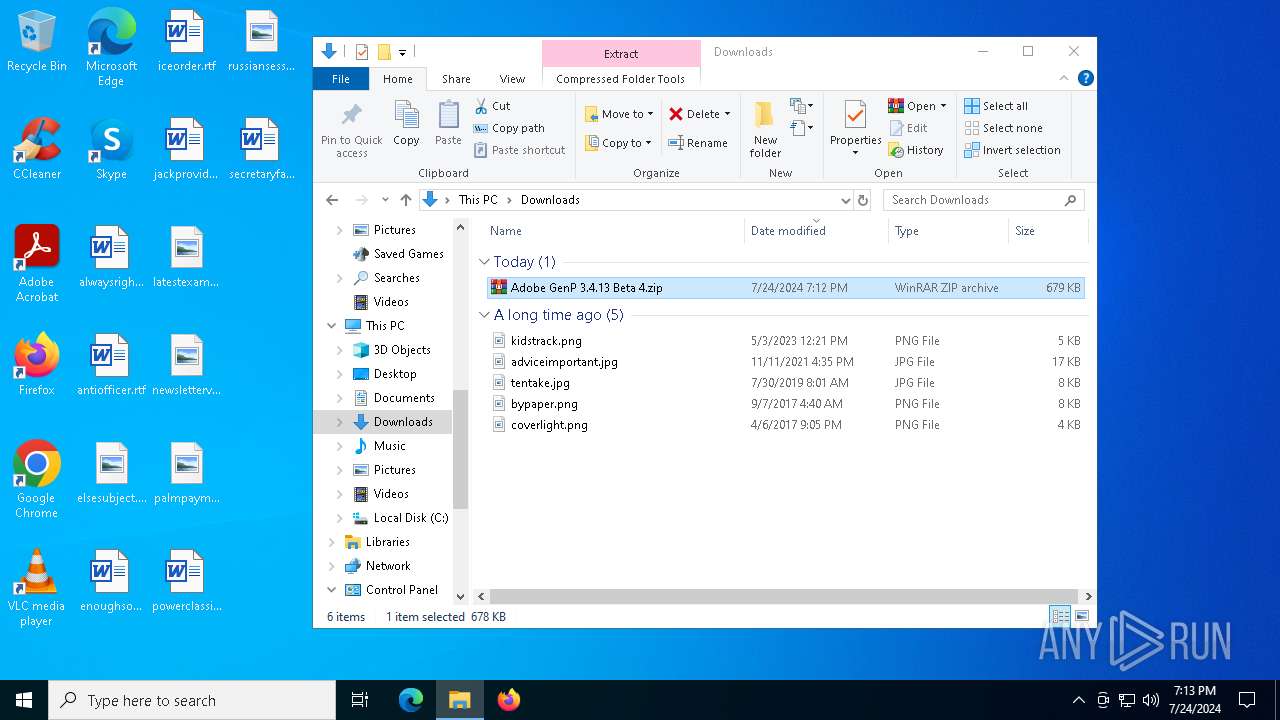
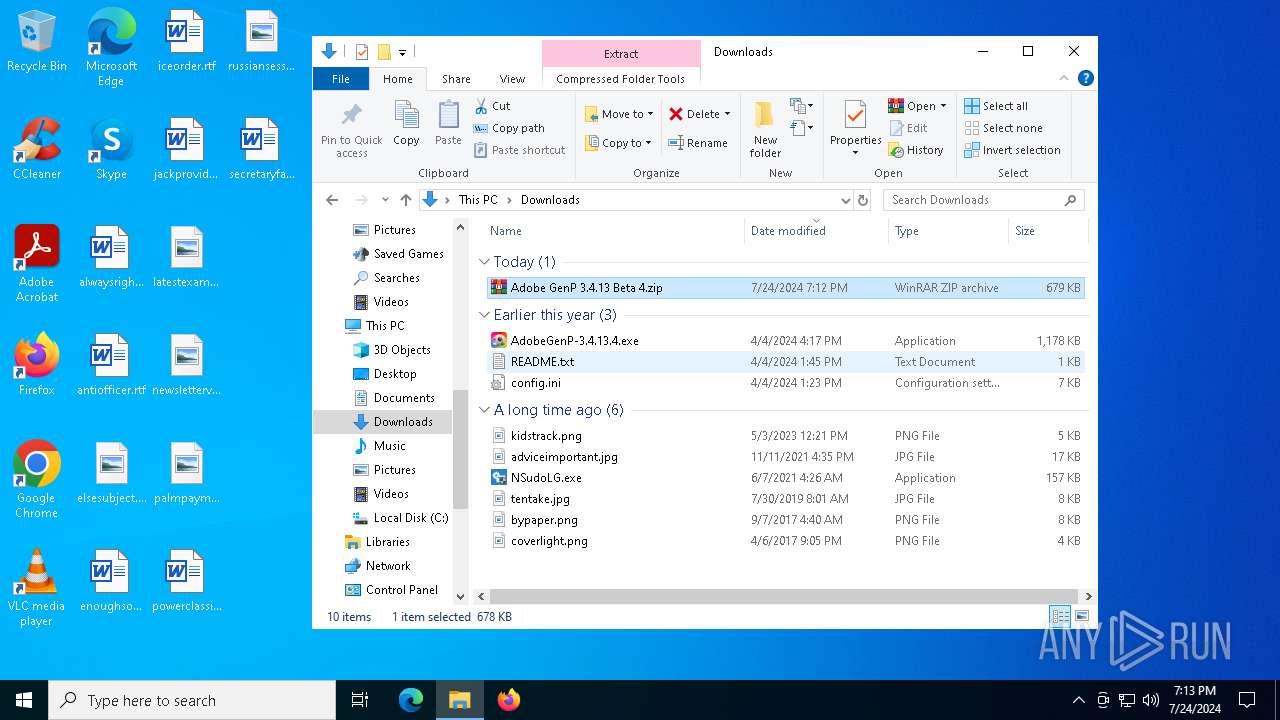
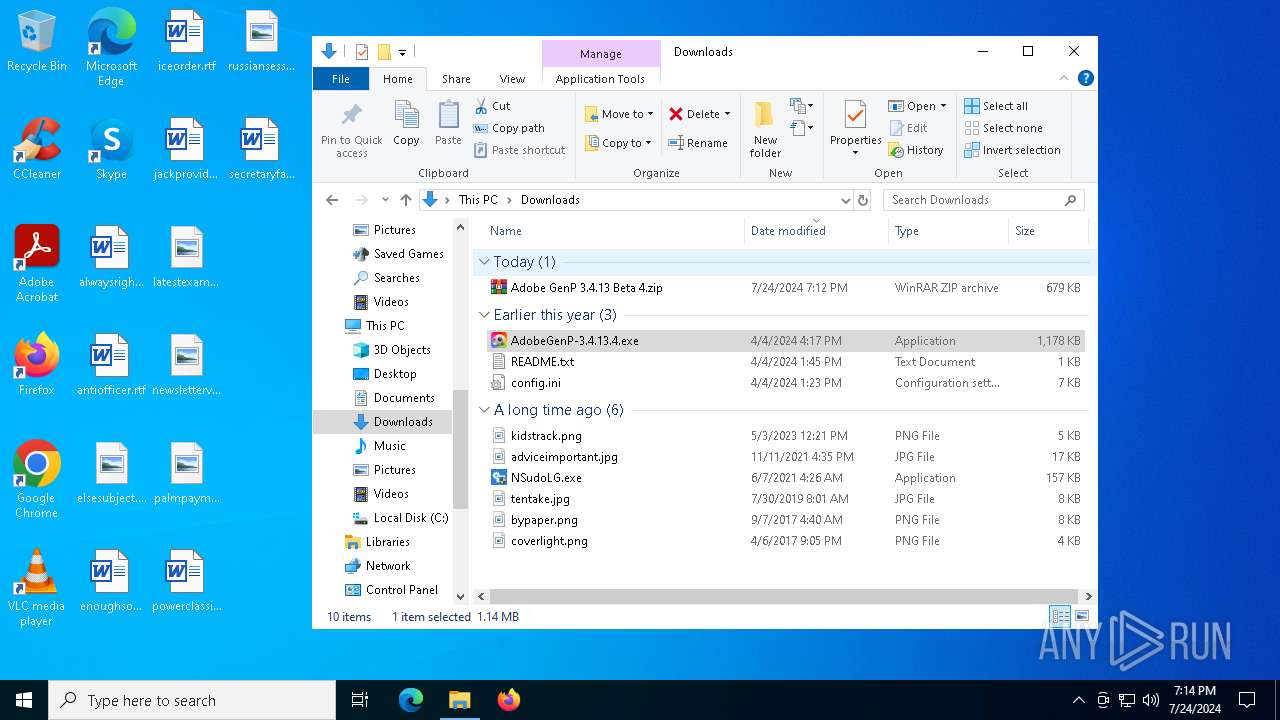
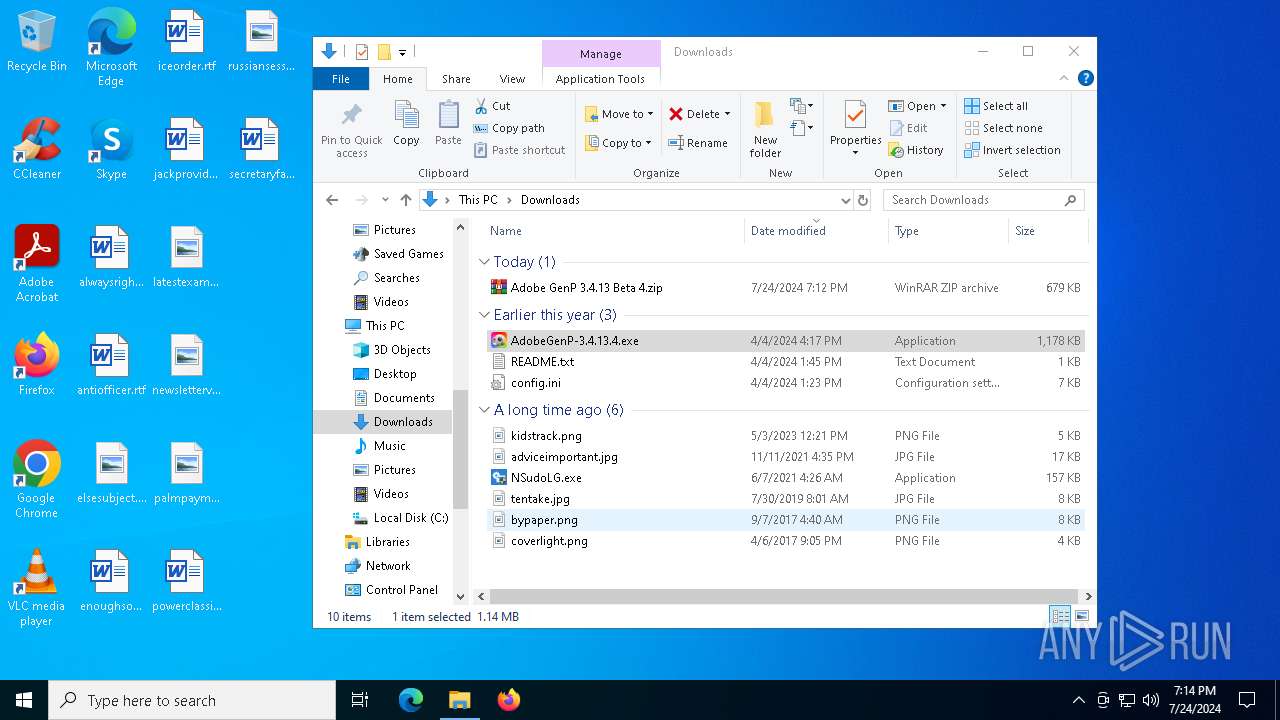
| URL: | https://www.mediafire.com/file/rsdbnfi38eex4xv/Adobe_GenP_3.4.13_Beta_4.zip/file |
| Full analysis: | https://app.any.run/tasks/dac13cc6-1819-43f3-9f02-3cdd55489673 |
| Verdict: | Malicious activity |
| Analysis date: | July 24, 2024, 19:12:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E743670D32F6ED61BF1EBDAA7B42CBE9 |
| SHA1: | 47E9966C01EC2DA3278ADC70DFC2FCACB2A51438 |
| SHA256: | 8E562504E94AA76CAF9DB3E477A3E1A3E0E352AA237DA5E70A3D951183B3E55E |
| SSDEEP: | 3:N8DSLw3eGUoWndH79AbRLk0dj9:2OLw3eGIbQLfdR |
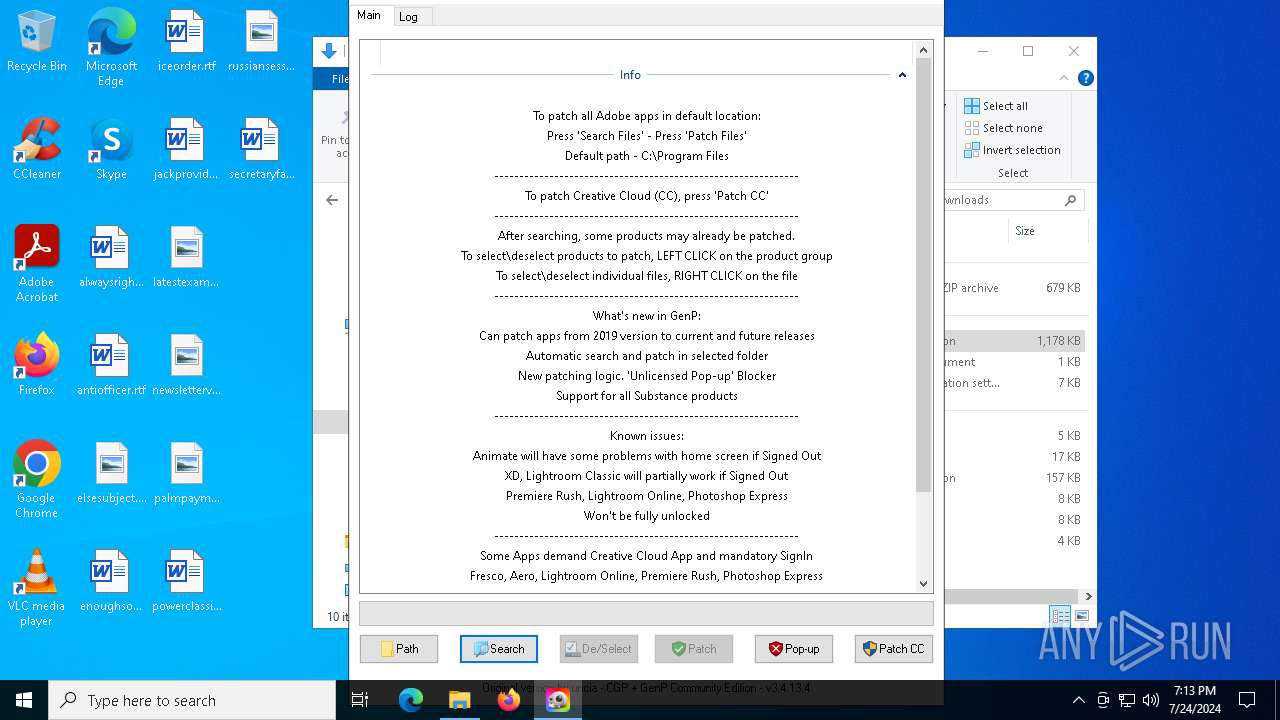
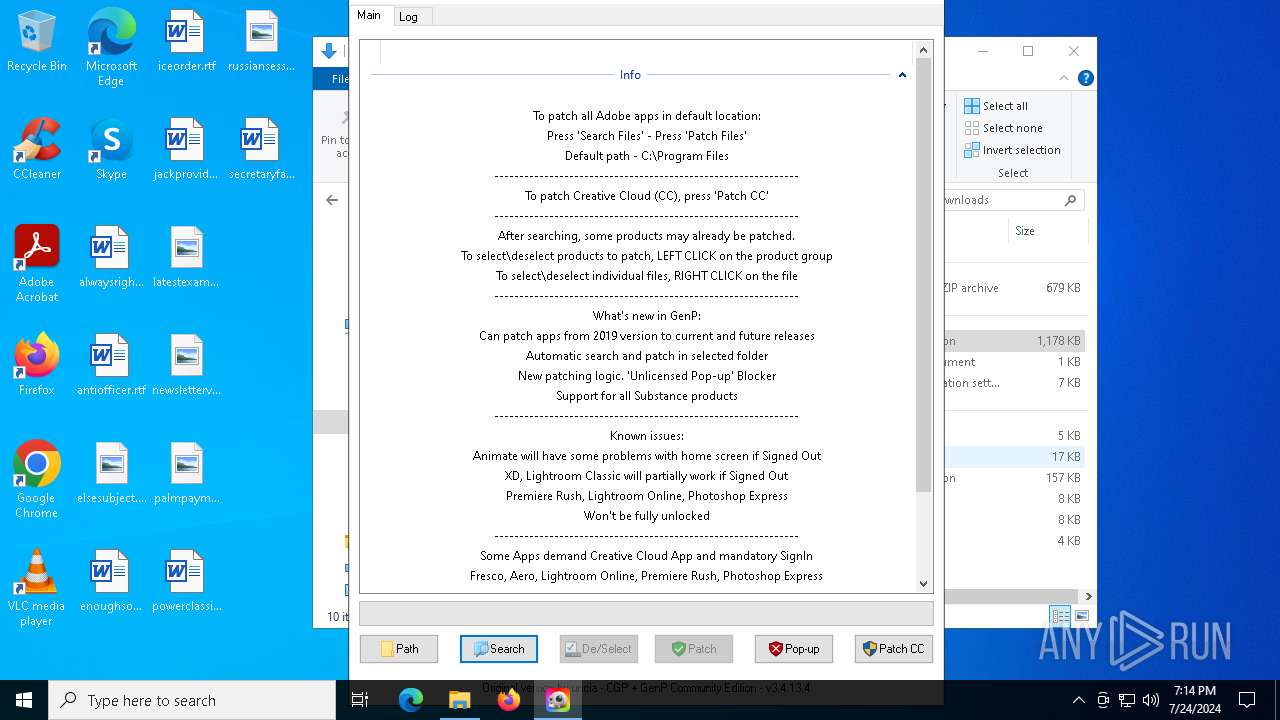
MALICIOUS
Modifies hosts file to block updates
- powershell.exe (PID: 8788)
SUSPICIOUS
Reads the date of Windows installation
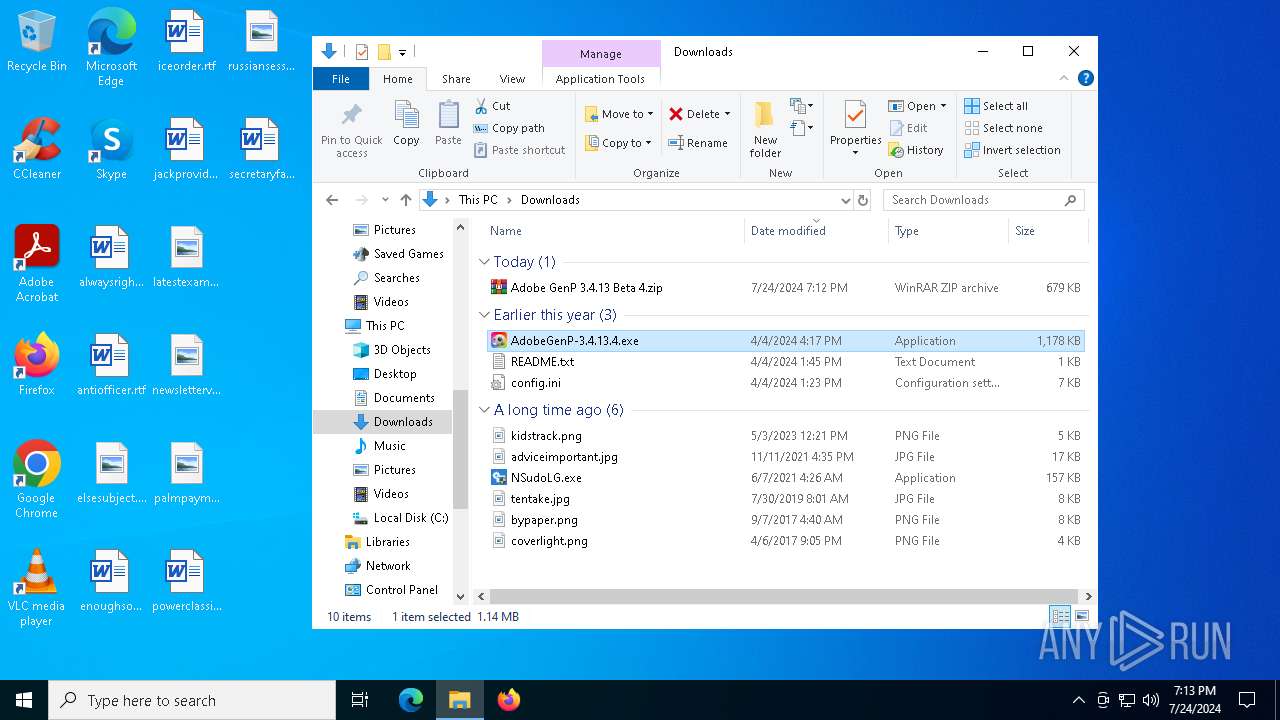
- AdobeGenP-3.4.13.4.exe (PID: 9108)
- AdobeGenP-3.4.13.4.exe (PID: 7600)
Reads security settings of Internet Explorer
- AdobeGenP-3.4.13.4.exe (PID: 9108)
- AdobeGenP-3.4.13.4.exe (PID: 6704)
- ShellExperienceHost.exe (PID: 2824)
- AdobeGenP-3.4.13.4.exe (PID: 7600)
Application launched itself
- AdobeGenP-3.4.13.4.exe (PID: 9108)
- AdobeGenP-3.4.13.4.exe (PID: 7600)
Starts POWERSHELL.EXE for commands execution
- AdobeGenP-3.4.13.4.exe (PID: 7756)
The process checks if current user has admin rights
- AdobeGenP-3.4.13.4.exe (PID: 7756)
Probably obfuscated PowerShell command line is found
- AdobeGenP-3.4.13.4.exe (PID: 7756)
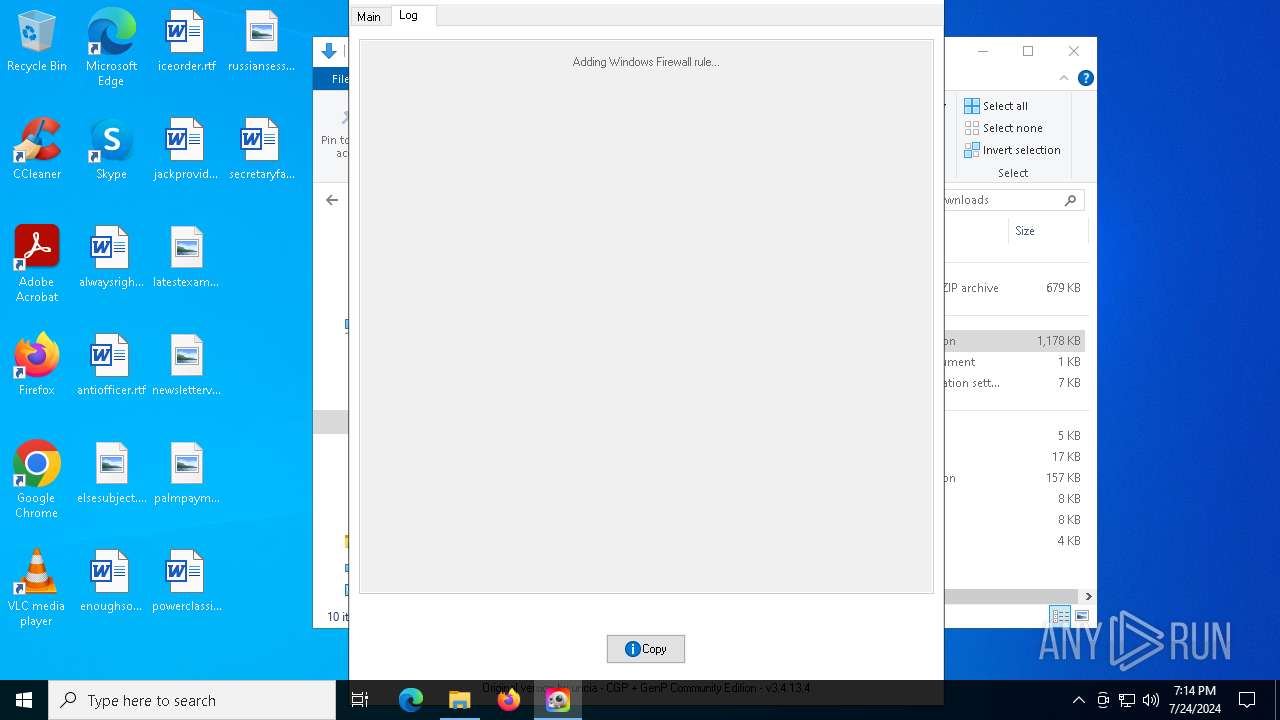
Uses NETSH.EXE to add a firewall rule or allowed programs
- AdobeGenP-3.4.13.4.exe (PID: 7756)
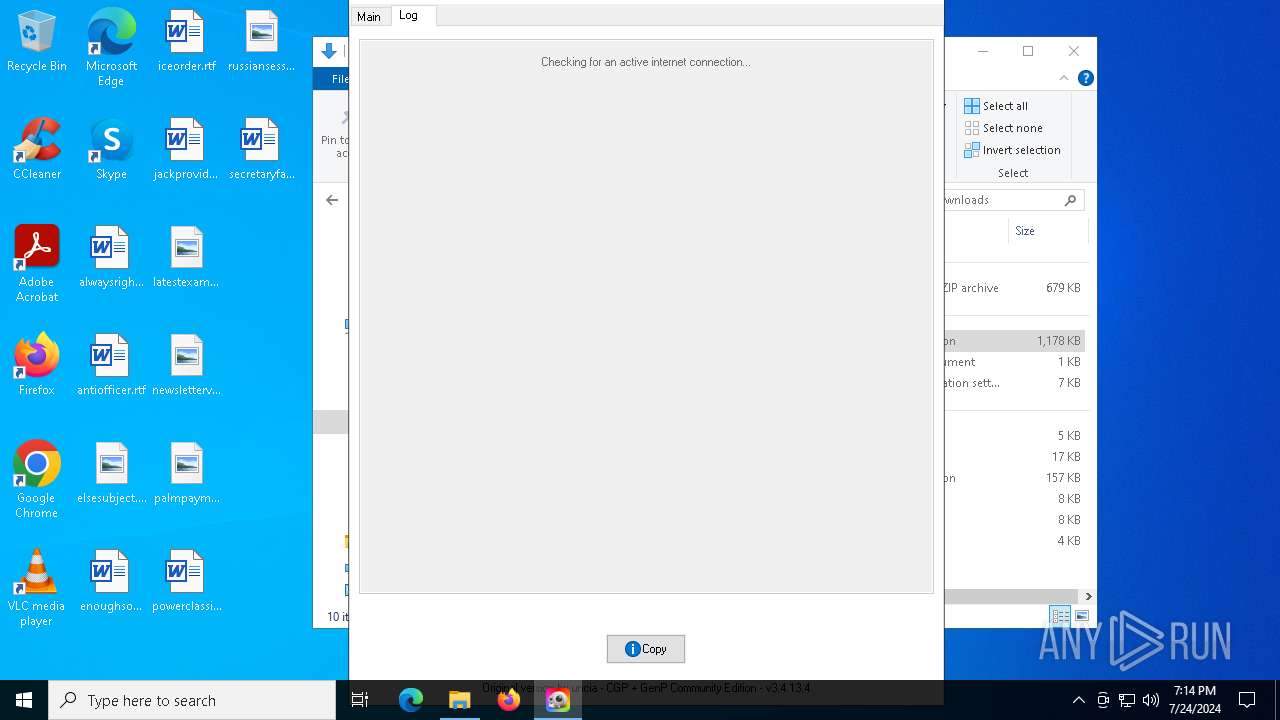
Request a resource from the Internet using PowerShell's cmdlet
- AdobeGenP-3.4.13.4.exe (PID: 7756)
The process bypasses the loading of PowerShell profile settings
- AdobeGenP-3.4.13.4.exe (PID: 7756)
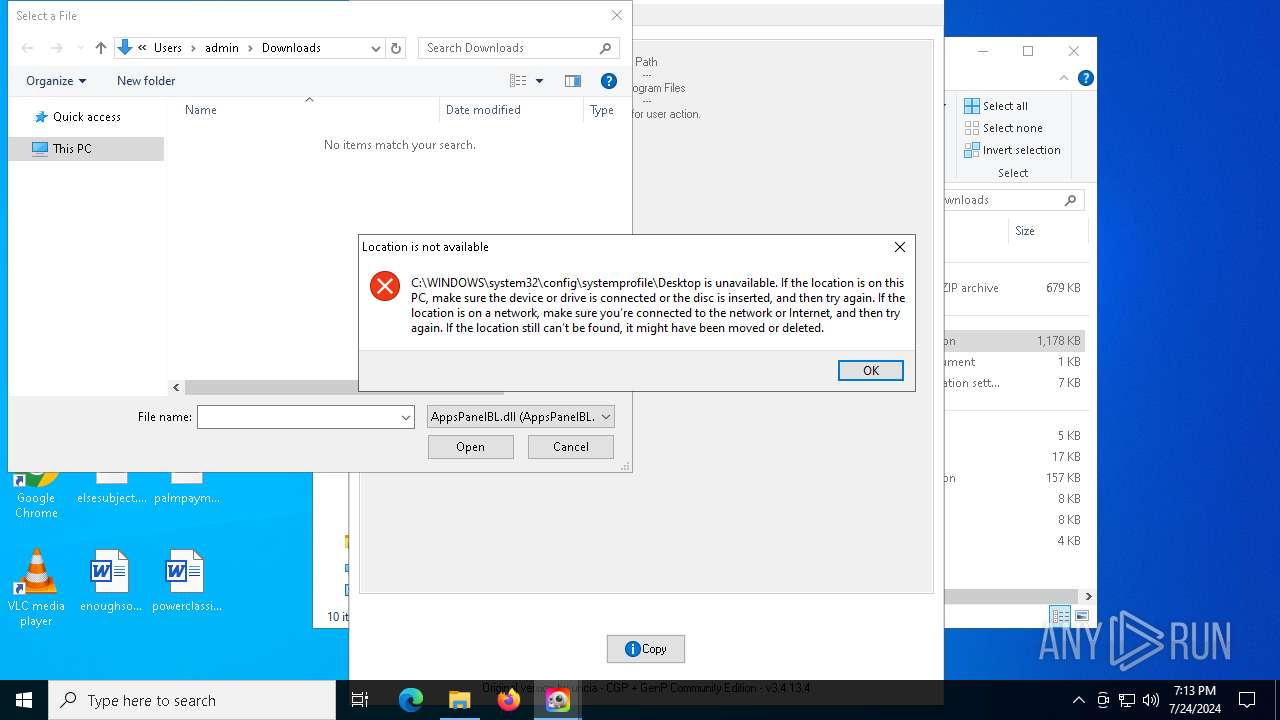
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 5740)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- AdobeGenP-3.4.13.4.exe (PID: 7756)
Found IP address in command line
- powershell.exe (PID: 5740)
INFO
Checks supported languages
- identity_helper.exe (PID: 7356)
- identity_helper.exe (PID: 7776)
- AdobeGenP-3.4.13.4.exe (PID: 9108)
- NSudoLG.exe (PID: 7956)
- AdobeGenP-3.4.13.4.exe (PID: 4936)
- AdobeGenP-3.4.13.4.exe (PID: 6704)
- ShellExperienceHost.exe (PID: 2824)
- AdobeGenP-3.4.13.4.exe (PID: 7600)
- AdobeGenP-3.4.13.4.exe (PID: 9012)
- NSudoLG.exe (PID: 7232)
- AdobeGenP-3.4.13.4.exe (PID: 7756)
Reads Environment values
- identity_helper.exe (PID: 7356)
- identity_helper.exe (PID: 7776)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5500)
- msedge.exe (PID: 396)
Application launched itself
- msedge.exe (PID: 396)
- msedge.exe (PID: 5500)
Reads the computer name
- identity_helper.exe (PID: 7356)
- identity_helper.exe (PID: 7776)
- AdobeGenP-3.4.13.4.exe (PID: 9108)
- AdobeGenP-3.4.13.4.exe (PID: 4936)
- AdobeGenP-3.4.13.4.exe (PID: 6704)
- NSudoLG.exe (PID: 7956)
- ShellExperienceHost.exe (PID: 2824)
- AdobeGenP-3.4.13.4.exe (PID: 7600)
- AdobeGenP-3.4.13.4.exe (PID: 9012)
- NSudoLG.exe (PID: 7232)
- AdobeGenP-3.4.13.4.exe (PID: 7756)
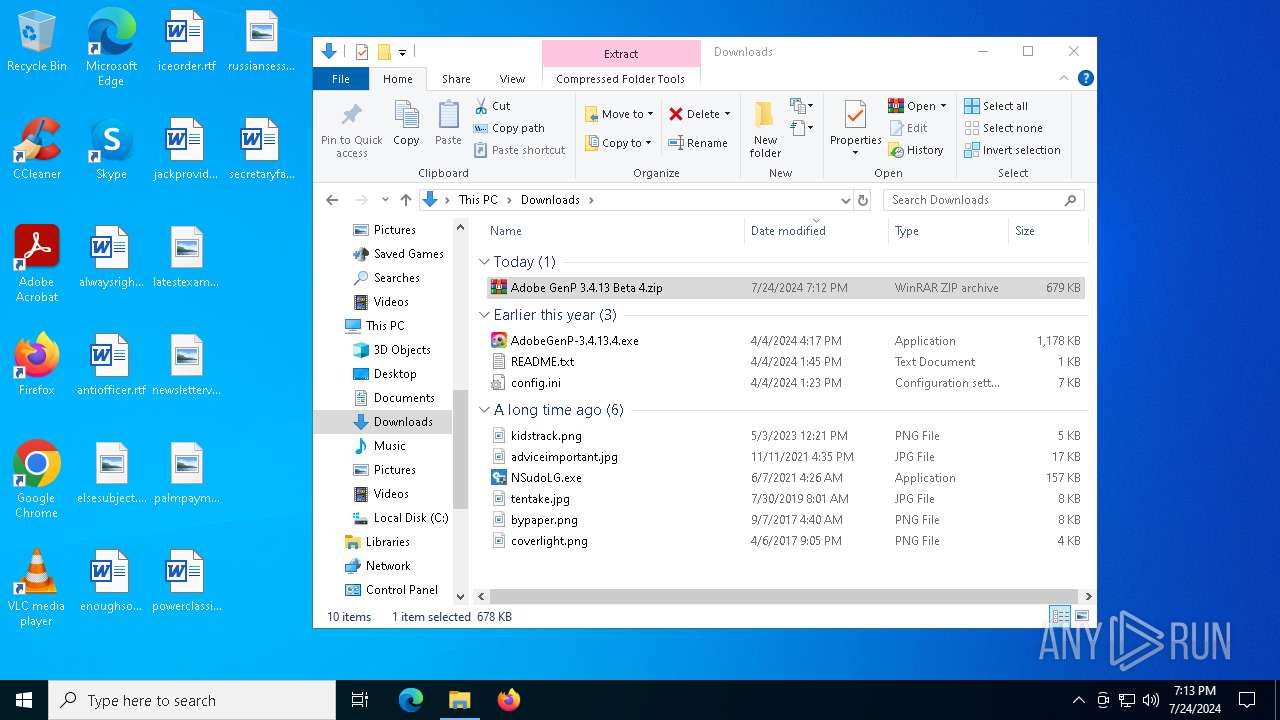
The process uses the downloaded file
- msedge.exe (PID: 7480)
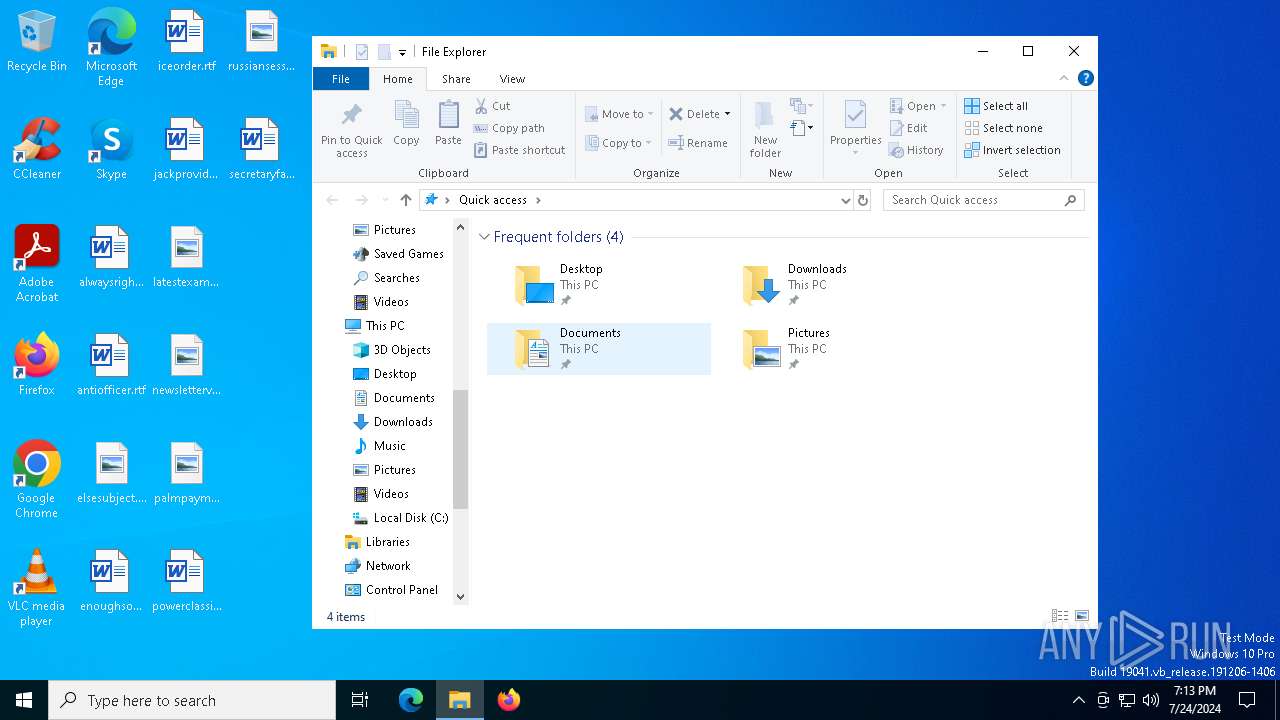
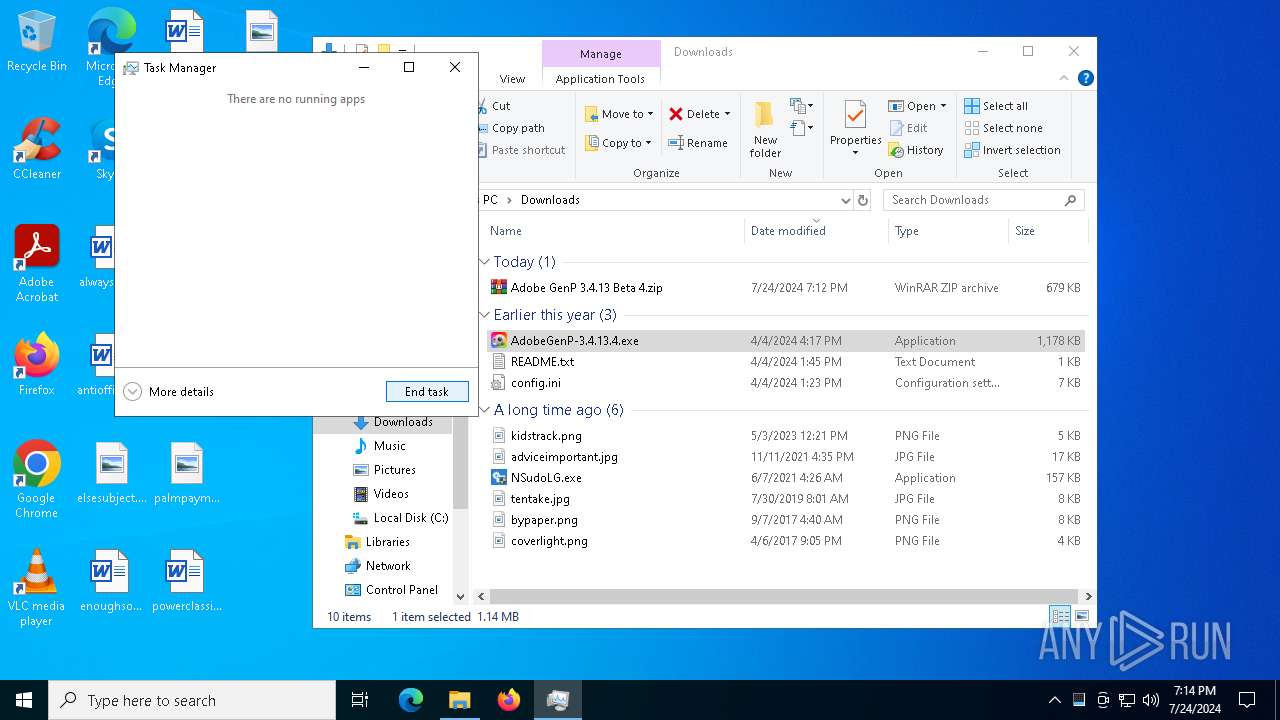
- WinRAR.exe (PID: 7196)
Drops the executable file immediately after the start
- msedge.exe (PID: 396)
- WinRAR.exe (PID: 7196)
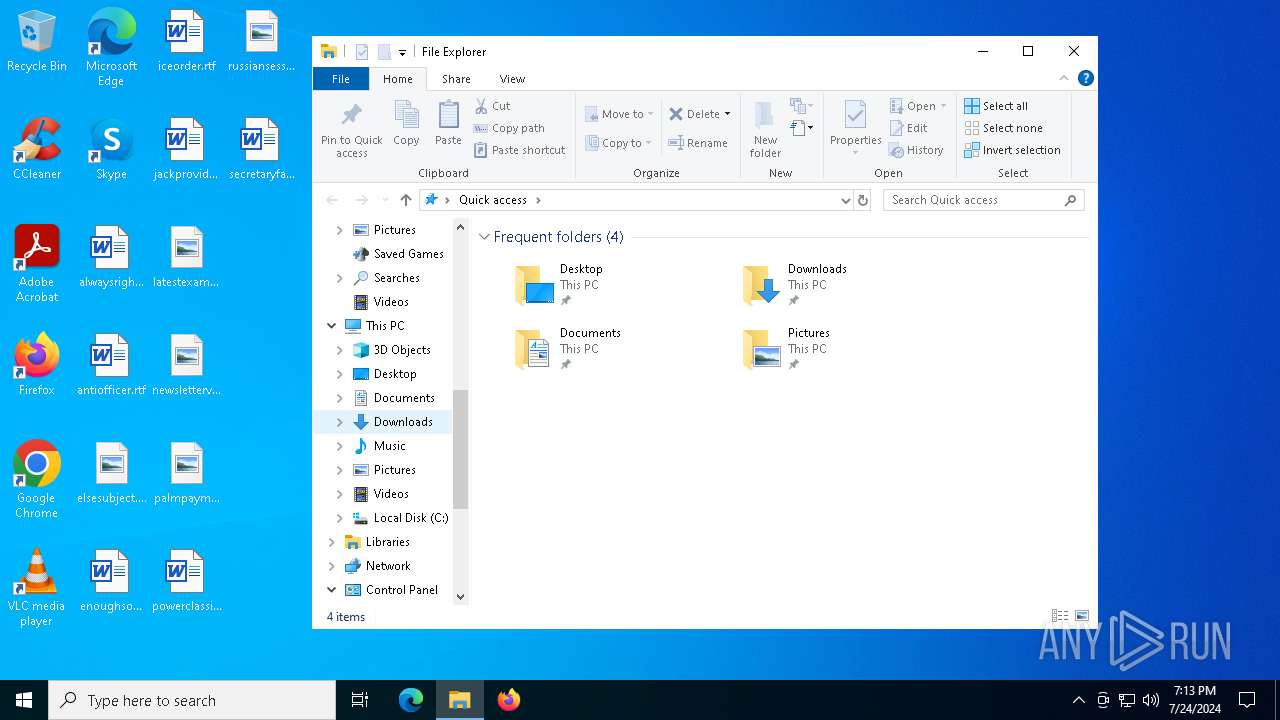
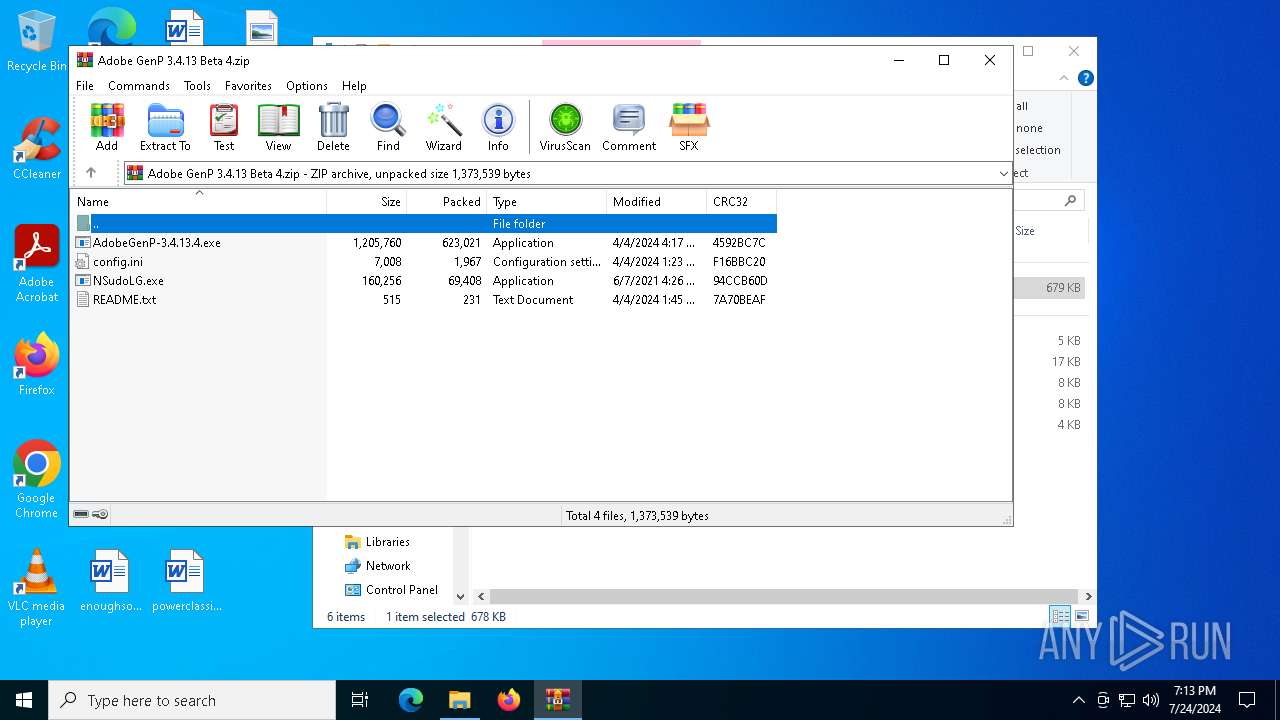
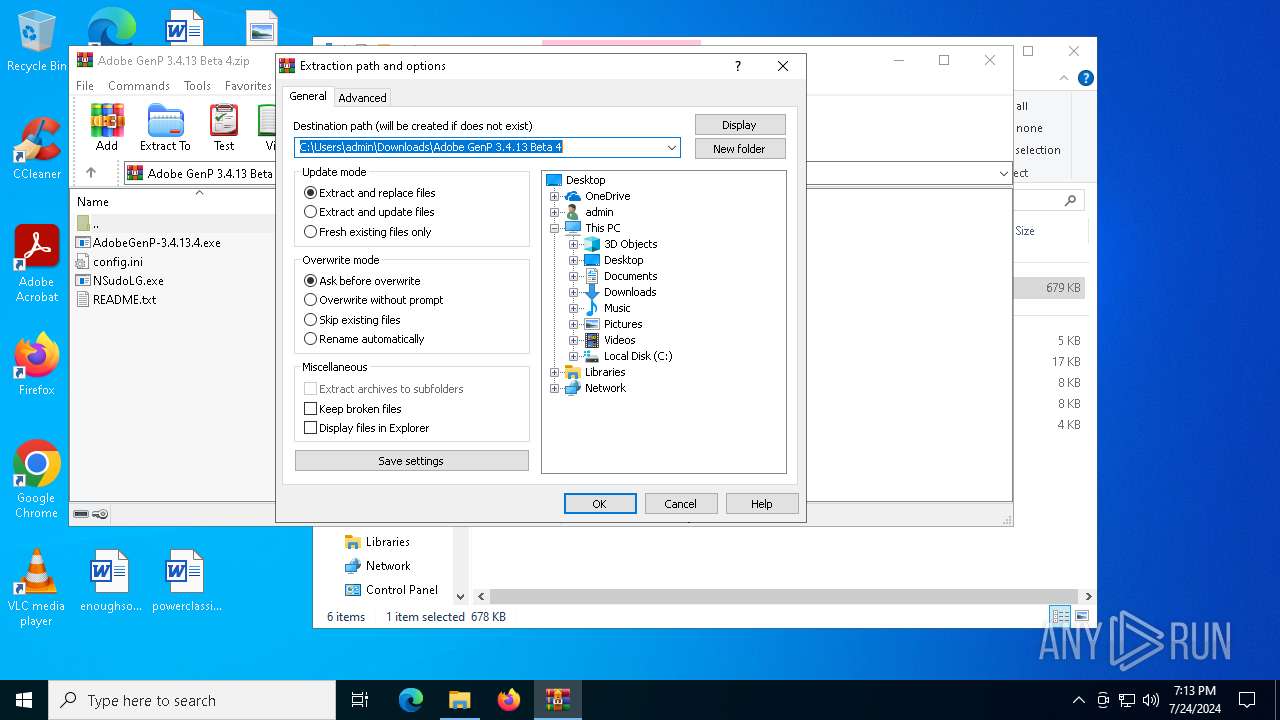
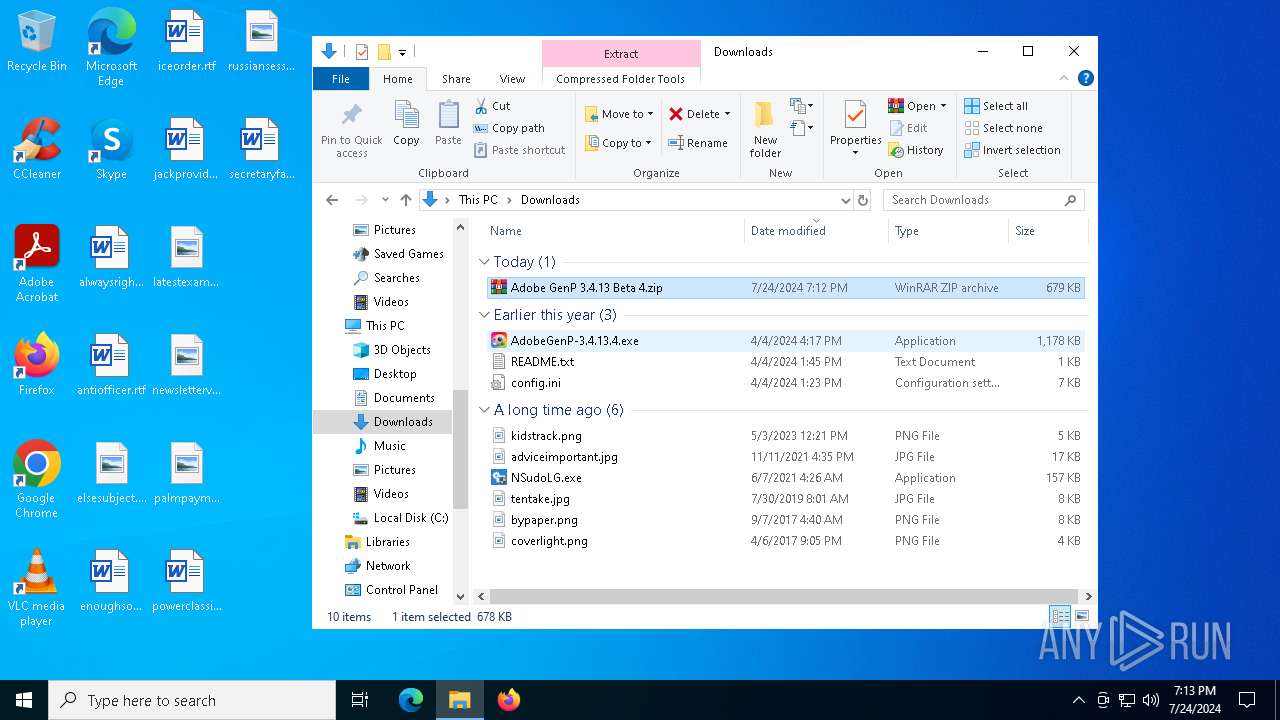
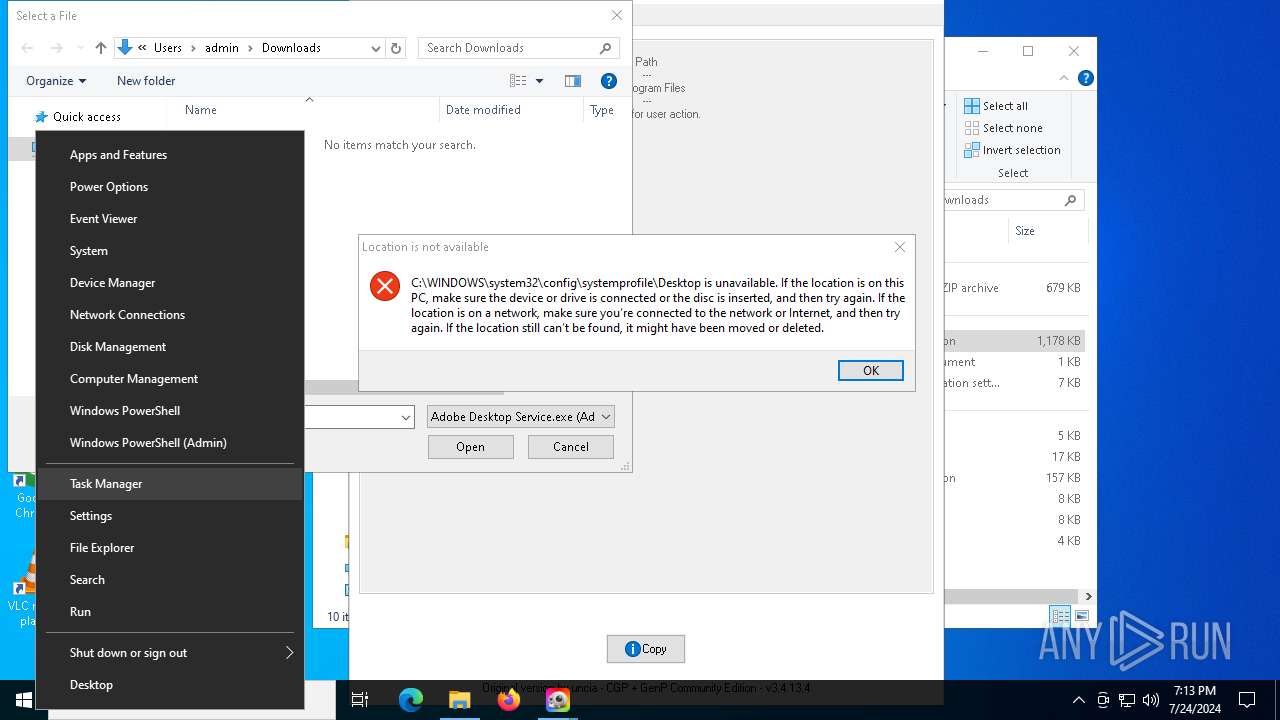
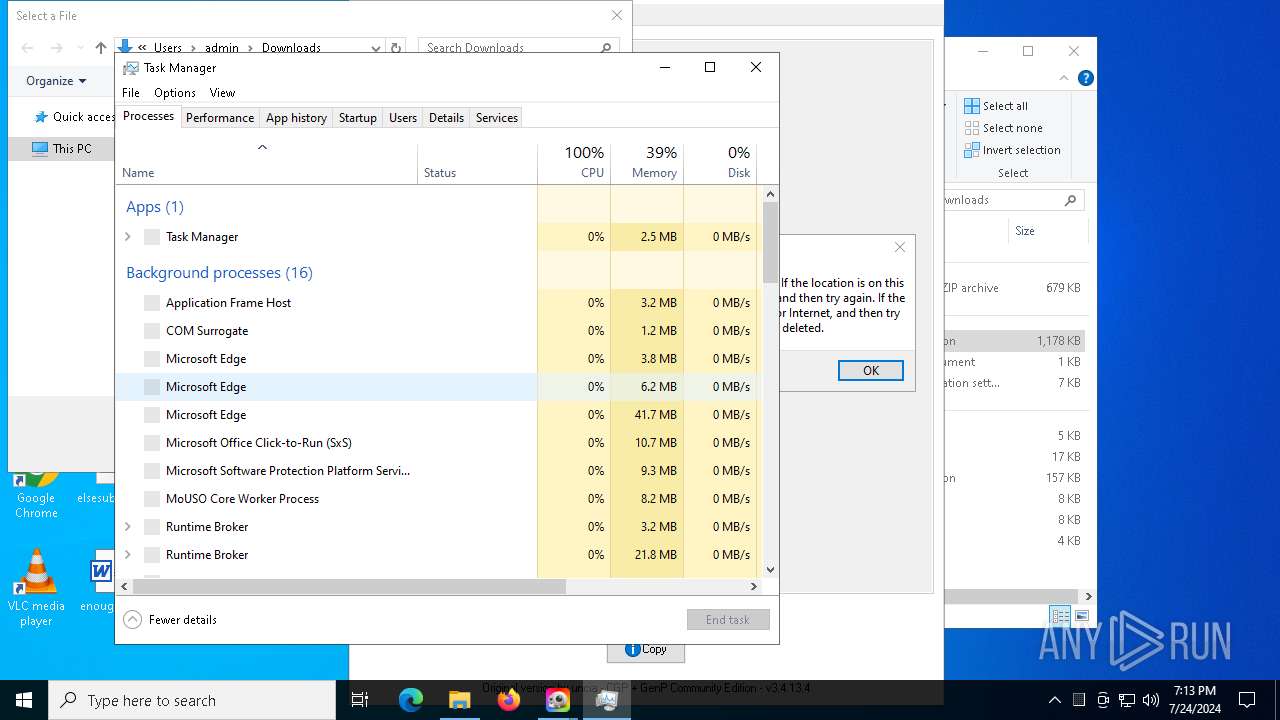
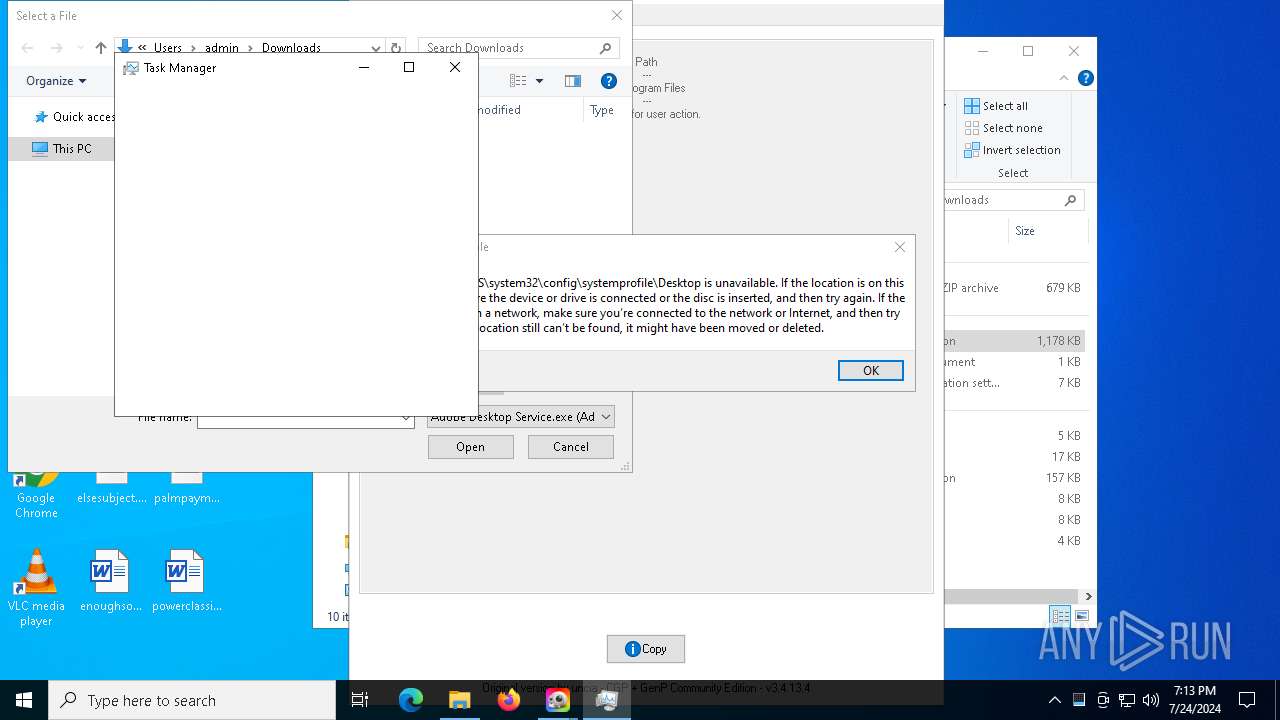
Manual execution by a user
- WinRAR.exe (PID: 7196)
- AdobeGenP-3.4.13.4.exe (PID: 9108)
- Taskmgr.exe (PID: 7496)
- Taskmgr.exe (PID: 2456)
- AdobeGenP-3.4.13.4.exe (PID: 7600)
Checks proxy server information
- slui.exe (PID: 8172)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7196)
Reads mouse settings
- AdobeGenP-3.4.13.4.exe (PID: 9108)
- AdobeGenP-3.4.13.4.exe (PID: 4936)
- AdobeGenP-3.4.13.4.exe (PID: 6704)
- AdobeGenP-3.4.13.4.exe (PID: 7600)
- AdobeGenP-3.4.13.4.exe (PID: 9012)
- AdobeGenP-3.4.13.4.exe (PID: 7756)
Process checks computer location settings
- AdobeGenP-3.4.13.4.exe (PID: 9108)
- AdobeGenP-3.4.13.4.exe (PID: 7600)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 2456)
Disables trace logs
- powershell.exe (PID: 8788)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
242
Monitored processes
97
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4864 --field-trial-handle=2196,i,12468003079902299258,2909451920127281191,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 396 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://www.mediafire.com/file/rsdbnfi38eex4xv/Adobe_GenP_3.4.13_Beta_4.zip/file" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x304,0x308,0x30c,0x300,0x314,0x7fff00f45fd8,0x7fff00f45fe4,0x7fff00f45ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1560 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --mojo-platform-channel-handle=7920 --field-trial-handle=2344,i,8329706788134654282,13711197849479733826,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1652 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1696 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2212 --field-trial-handle=2344,i,8329706788134654282,13711197849479733826,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --mojo-platform-channel-handle=8168 --field-trial-handle=2344,i,8329706788134654282,13711197849479733826,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=35 --mojo-platform-channel-handle=7804 --field-trial-handle=2344,i,8329706788134654282,13711197849479733826,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2456 | "C:\WINDOWS\system32\taskmgr.exe" /0 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3516 --field-trial-handle=2344,i,8329706788134654282,13711197849479733826,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
18 344
Read events
18 215
Write events
127
Delete events
2
Modification events
| (PID) Process: | (396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (396) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (396) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (396) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
6
Suspicious files
437
Text files
139
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe1307.TMP | — | |
MD5:— | SHA256:— | |||
| 396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe1307.TMP | — | |
MD5:— | SHA256:— | |||
| 396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe1307.TMP | — | |
MD5:— | SHA256:— | |||
| 396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe1307.TMP | — | |
MD5:— | SHA256:— | |||
| 396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe1345.TMP | — | |
MD5:— | SHA256:— | |||
| 396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
333
DNS requests
354
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8292 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/81c945d1-1834-4d97-ab56-9ed86990a128?P1=1722300339&P2=404&P3=2&P4=ipGJeNOr7cy4TR76J7qaOhMCmmGMGpL%2bf0rtpo2kA6QxDbWvNPDvjtAOE11QQ4rBJRXyMOjjtuWphyxNB%2b3PMA%3d%3d | unknown | — | — | whitelisted |
8724 | msedge.exe | GET | 304 | 2.23.197.184:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
8292 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/81c945d1-1834-4d97-ab56-9ed86990a128?P1=1722300339&P2=404&P3=2&P4=ipGJeNOr7cy4TR76J7qaOhMCmmGMGpL%2bf0rtpo2kA6QxDbWvNPDvjtAOE11QQ4rBJRXyMOjjtuWphyxNB%2b3PMA%3d%3d | unknown | — | — | whitelisted |
8292 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/81c945d1-1834-4d97-ab56-9ed86990a128?P1=1722300339&P2=404&P3=2&P4=ipGJeNOr7cy4TR76J7qaOhMCmmGMGpL%2bf0rtpo2kA6QxDbWvNPDvjtAOE11QQ4rBJRXyMOjjtuWphyxNB%2b3PMA%3d%3d | unknown | — | — | whitelisted |
8292 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/81c945d1-1834-4d97-ab56-9ed86990a128?P1=1722300339&P2=404&P3=2&P4=ipGJeNOr7cy4TR76J7qaOhMCmmGMGpL%2bf0rtpo2kA6QxDbWvNPDvjtAOE11QQ4rBJRXyMOjjtuWphyxNB%2b3PMA%3d%3d | unknown | — | — | whitelisted |
8292 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/81c945d1-1834-4d97-ab56-9ed86990a128?P1=1722300339&P2=404&P3=2&P4=ipGJeNOr7cy4TR76J7qaOhMCmmGMGpL%2bf0rtpo2kA6QxDbWvNPDvjtAOE11QQ4rBJRXyMOjjtuWphyxNB%2b3PMA%3d%3d | unknown | — | — | whitelisted |
8292 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/81c945d1-1834-4d97-ab56-9ed86990a128?P1=1722300339&P2=404&P3=2&P4=ipGJeNOr7cy4TR76J7qaOhMCmmGMGpL%2bf0rtpo2kA6QxDbWvNPDvjtAOE11QQ4rBJRXyMOjjtuWphyxNB%2b3PMA%3d%3d | unknown | — | — | whitelisted |
8292 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/81c945d1-1834-4d97-ab56-9ed86990a128?P1=1722300339&P2=404&P3=2&P4=ipGJeNOr7cy4TR76J7qaOhMCmmGMGpL%2bf0rtpo2kA6QxDbWvNPDvjtAOE11QQ4rBJRXyMOjjtuWphyxNB%2b3PMA%3d%3d | unknown | — | — | whitelisted |
8292 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8bc315ba-54e5-49f4-9b75-997d7071eb06?P1=1722400012&P2=404&P3=2&P4=k4OVT5vzGA5lPwtxGeSzMdZS6qASWk%2fKLn9PFfux%2f2jqCQz1OJFC3AUkVIQYpJGDWKW0p0zg9GUVCKeZo9dO2Q%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6012 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4288 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3060 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 104.126.37.171:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4204 | svchost.exe | 4.209.32.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6584 | msedge.exe | 104.16.113.74:443 | www.mediafire.com | — | — | unknown |
6584 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6584 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.mediafire.com |
| shared |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6584 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6584 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6584 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6584 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6584 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
8724 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
8724 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2284 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |