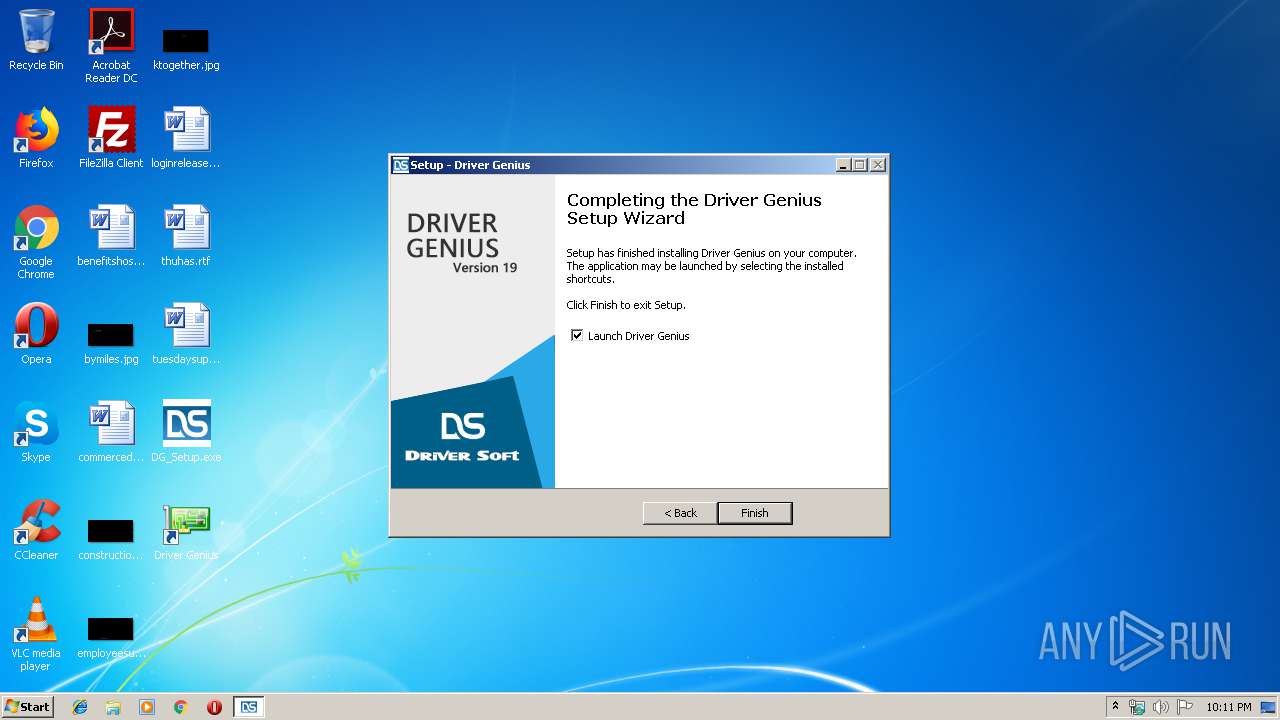
| download: | DG_Setup.exe |
| Full analysis: | https://app.any.run/tasks/7145b389-1acc-4b4f-afb8-5d3f4ed331c3 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 22:10:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E09F81BAD8DFB931FF79B66D2CB1309C |
| SHA1: | C89834071F857063D3D90F92779E72797323EB5B |
| SHA256: | 8E37B3C3556C3C845532BA6F2A5AD3E69DA27C33FE3DCDA59DE0795A12158A64 |
| SSDEEP: | 393216:I7dE2AVUQ7jUpk+f1zyD/sY1er/1gMyvj1oov:IEfUQ/UpT1zusY1Y/arvjmov |
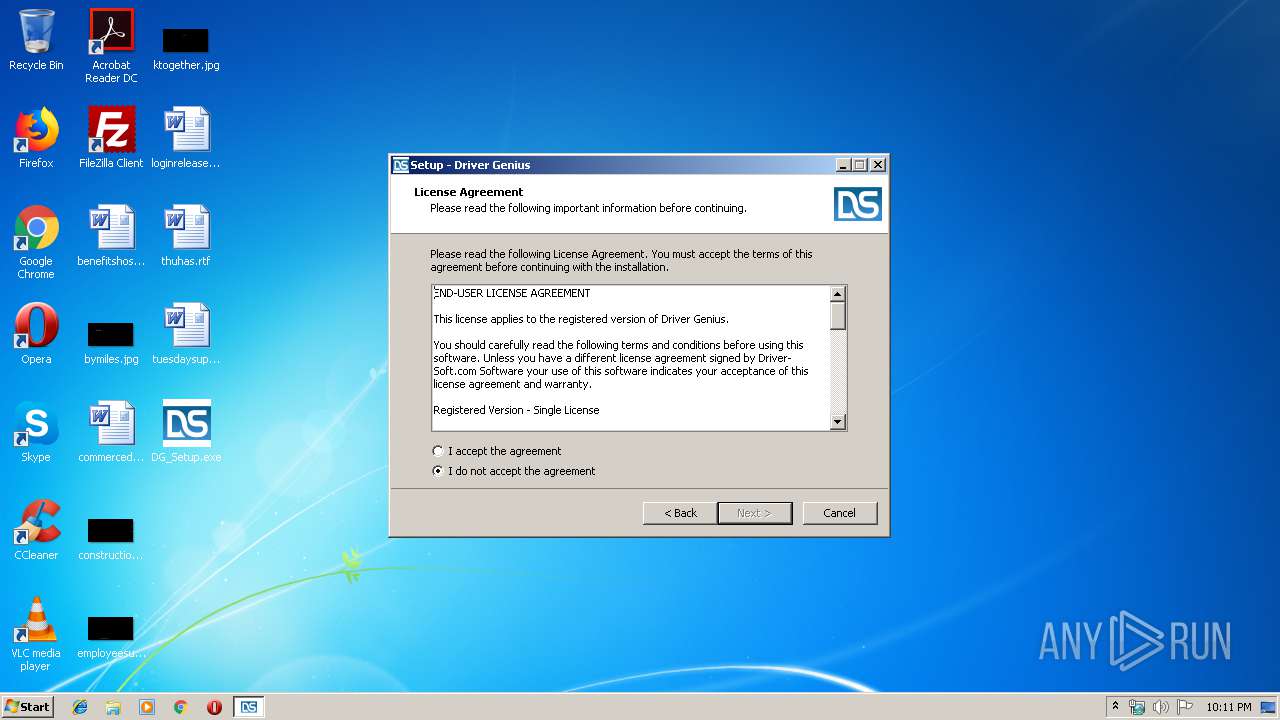
MALICIOUS
Uses Task Scheduler to run other applications
- DG_Setup.tmp (PID: 2480)
- DriverGenius.exe (PID: 624)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1784)
- SetupHelper.exe (PID: 2004)
- DriverGenius.exe (PID: 1912)
- WerFault.exe (PID: 2976)
- WerFault.exe (PID: 992)
- DriverGenius.exe (PID: 624)
- schtasks.exe (PID: 272)
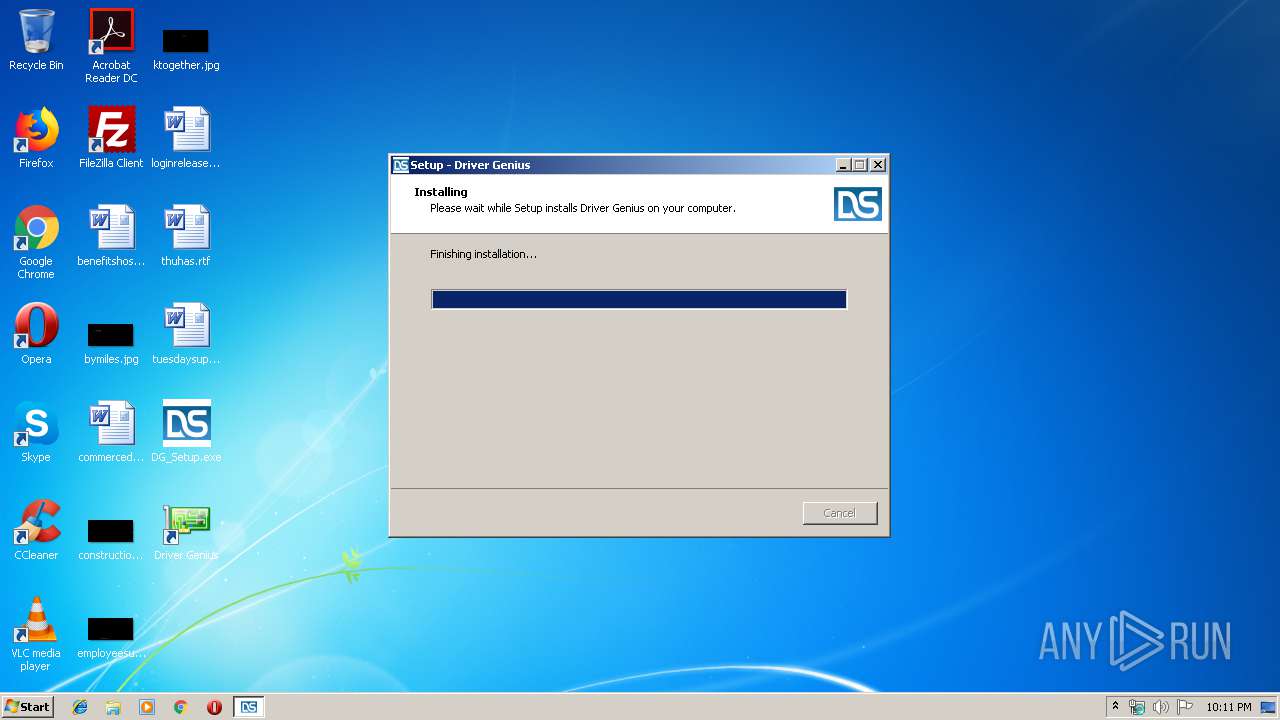
Application was dropped or rewritten from another process
- DriverGenius.exe (PID: 1912)
- installapi.exe (PID: 3076)
- installapi.exe (PID: 2352)
- installapi.exe (PID: 920)
- installapi.exe (PID: 3476)
- installapi.exe (PID: 3312)
- installapi.exe (PID: 1752)
- installapi.exe (PID: 3096)
- installapi.exe (PID: 2264)
- installapi.exe (PID: 3512)
- installapi.exe (PID: 3152)
- installapi.exe (PID: 3976)
- installapi.exe (PID: 2668)
- installapi.exe (PID: 3936)
- installapi.exe (PID: 2116)
- HWi32.exe (PID: 2544)
- SSDSpeeder.exe (PID: 920)
- installapi.exe (PID: 1252)
- installapi.exe (PID: 3960)
- SystemBooster.exe (PID: 836)
- DriverGenius.exe (PID: 3136)
- DriverGenius.exe (PID: 624)
- HWi32.exe (PID: 2280)
Loads dropped or rewritten executable
- DriverGenius.exe (PID: 1912)
- HWi32.exe (PID: 2544)
- SSDSpeeder.exe (PID: 920)
- SystemBooster.exe (PID: 836)
- WerFault.exe (PID: 2976)
- WerFault.exe (PID: 992)
- DriverGenius.exe (PID: 3136)
SUSPICIOUS
Reads Windows owner or organization settings
- DG_Setup.tmp (PID: 2480)
Executable content was dropped or overwritten
- DG_Setup.exe (PID: 2740)
- DG_Setup.exe (PID: 3600)
- DG_Setup.tmp (PID: 2480)
- DriverGenius.exe (PID: 1912)
- HWi32.exe (PID: 2544)
Starts CMD.EXE for commands execution
- DG_Setup.tmp (PID: 2480)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3432)
Reads the Windows organization settings
- DG_Setup.tmp (PID: 2480)
Creates files in the program directory
- DriverGenius.exe (PID: 1912)
- WerFault.exe (PID: 2976)
- WerFault.exe (PID: 992)
Creates files in the Windows directory
- DriverGenius.exe (PID: 1912)
Low-level read access rights to disk partition
- HWi32.exe (PID: 2544)
Executed via Task Scheduler
- DriverGenius.exe (PID: 3136)
INFO
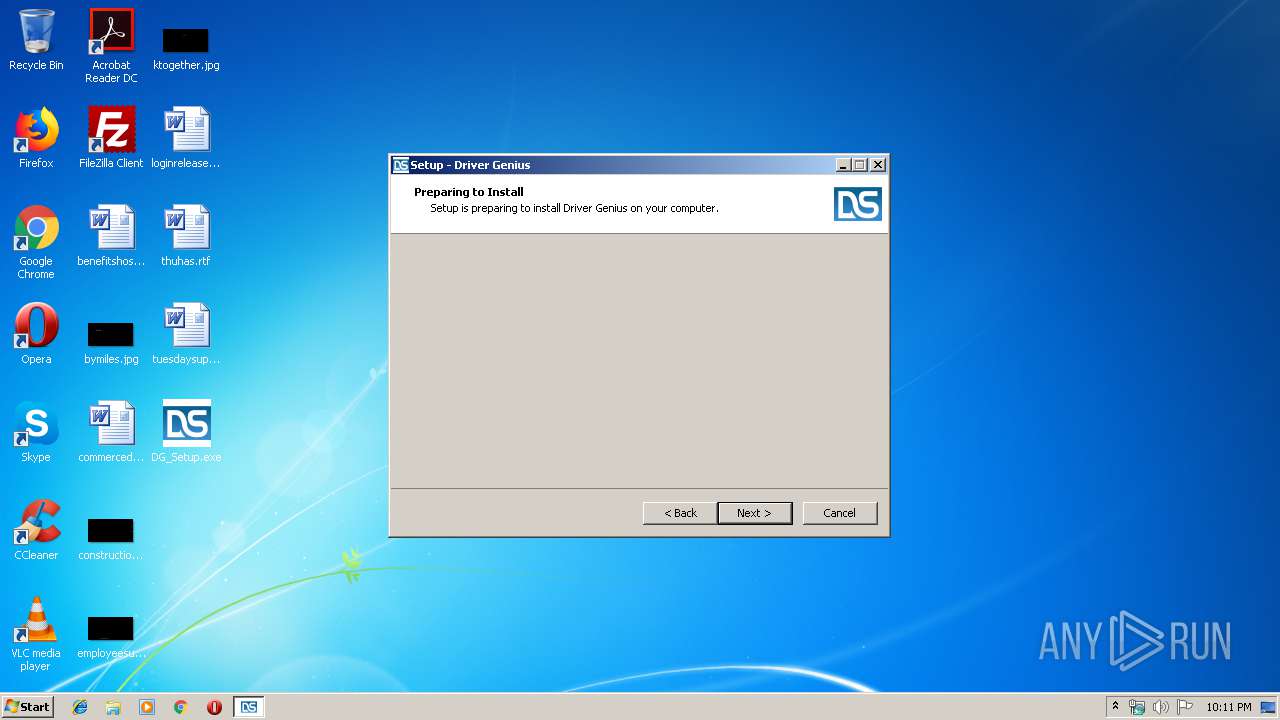
Application was dropped or rewritten from another process
- DG_Setup.tmp (PID: 2480)
- DG_Setup.tmp (PID: 3300)
- SetupHelper.exe (PID: 2004)
- 7za.exe (PID: 1252)
Dropped object may contain Bitcoin addresses
- DG_Setup.tmp (PID: 2480)
Creates files in the program directory
- DG_Setup.tmp (PID: 2480)
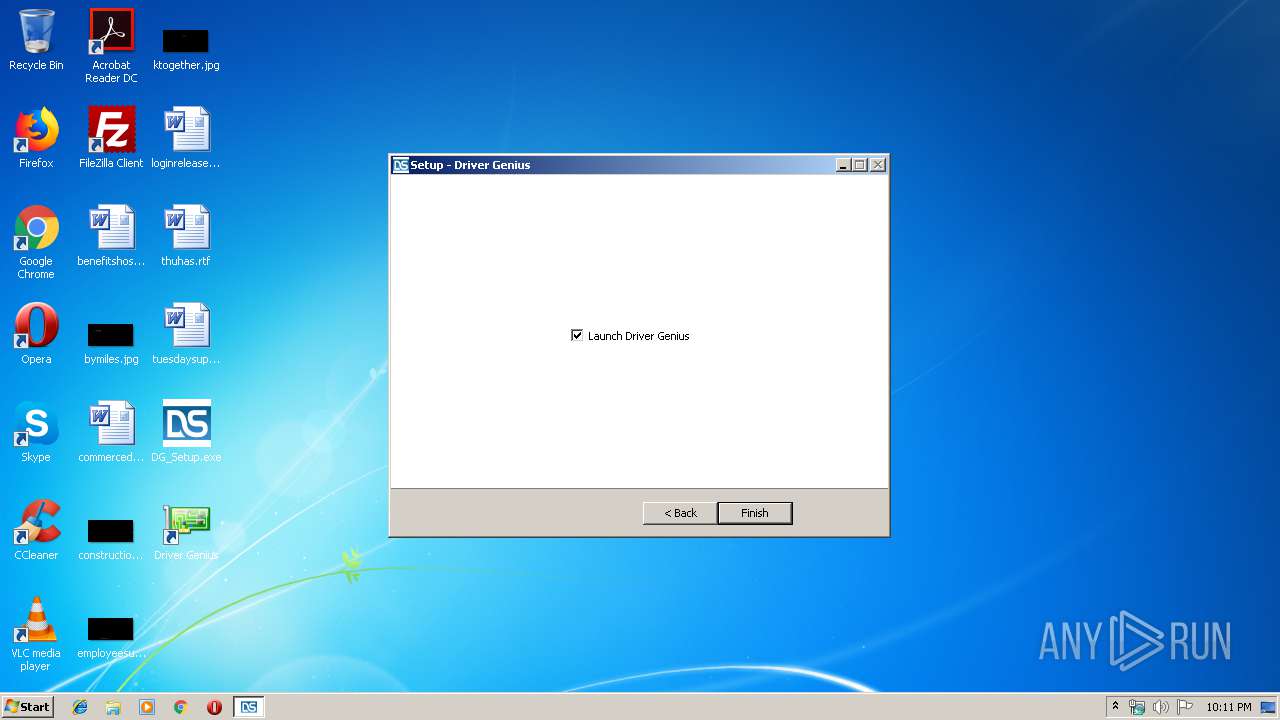
Creates a software uninstall entry
- DG_Setup.tmp (PID: 2480)
Loads dropped or rewritten executable
- DG_Setup.tmp (PID: 2480)
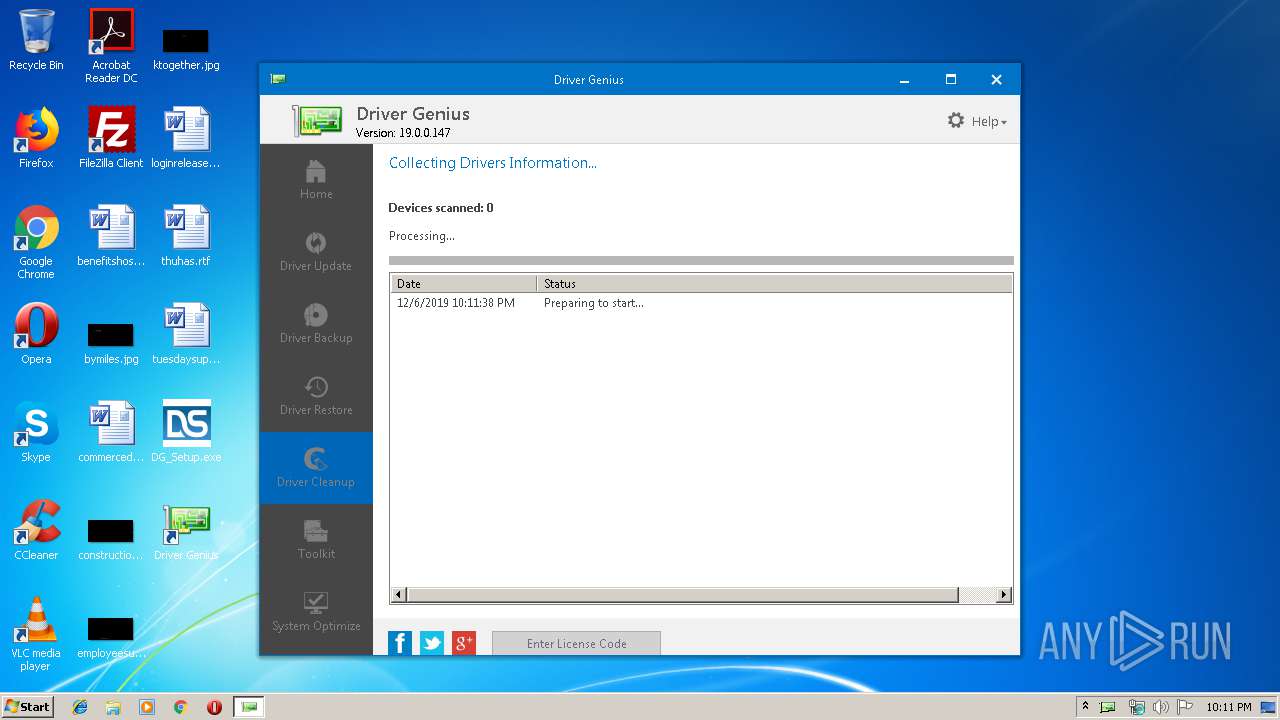
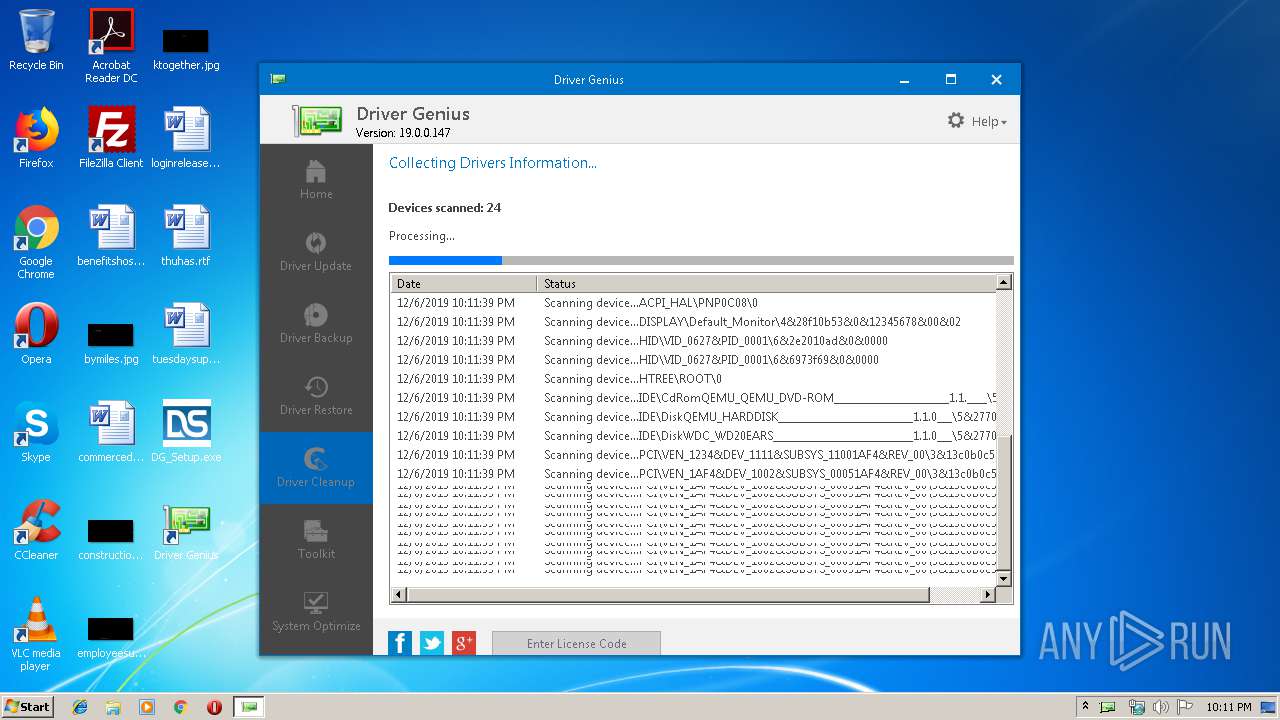
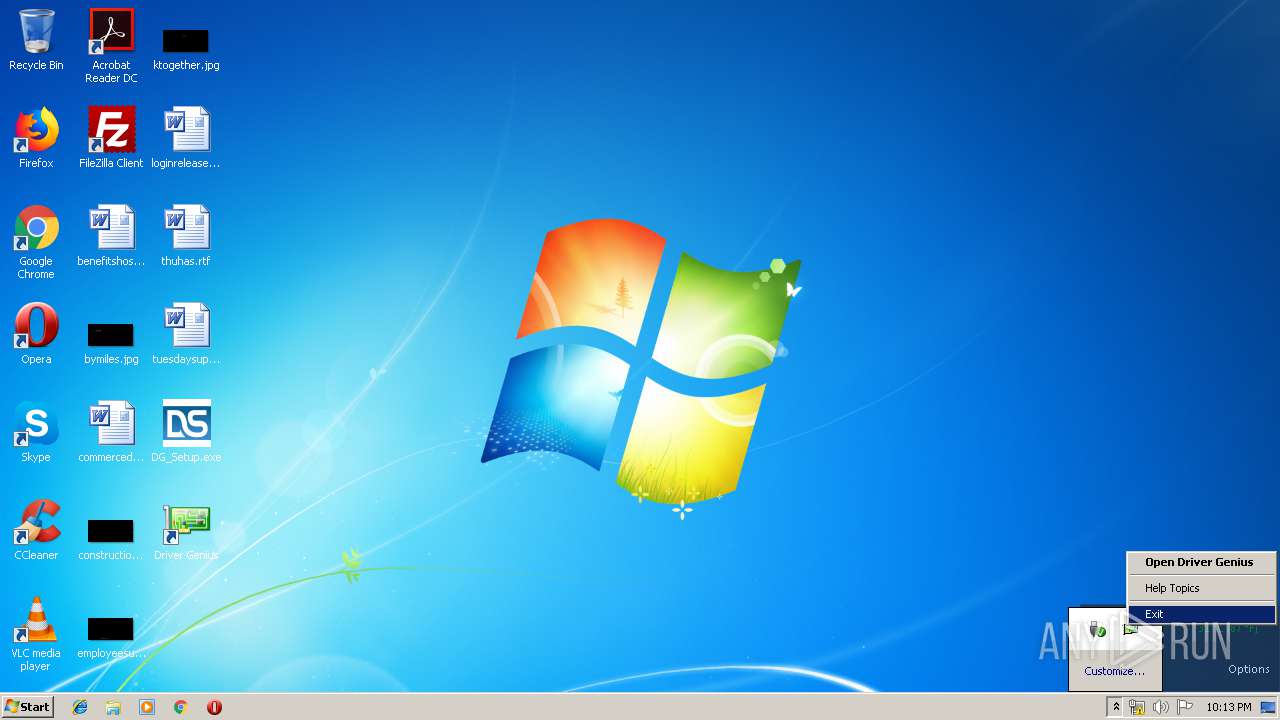
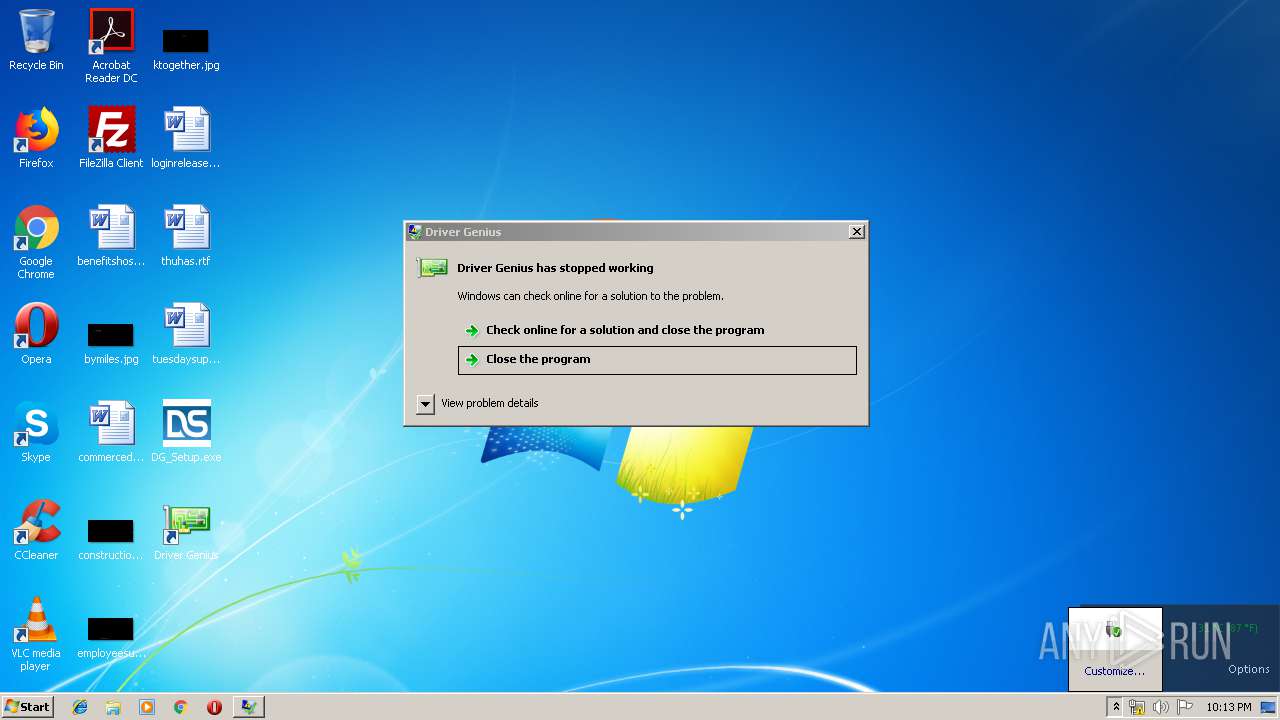
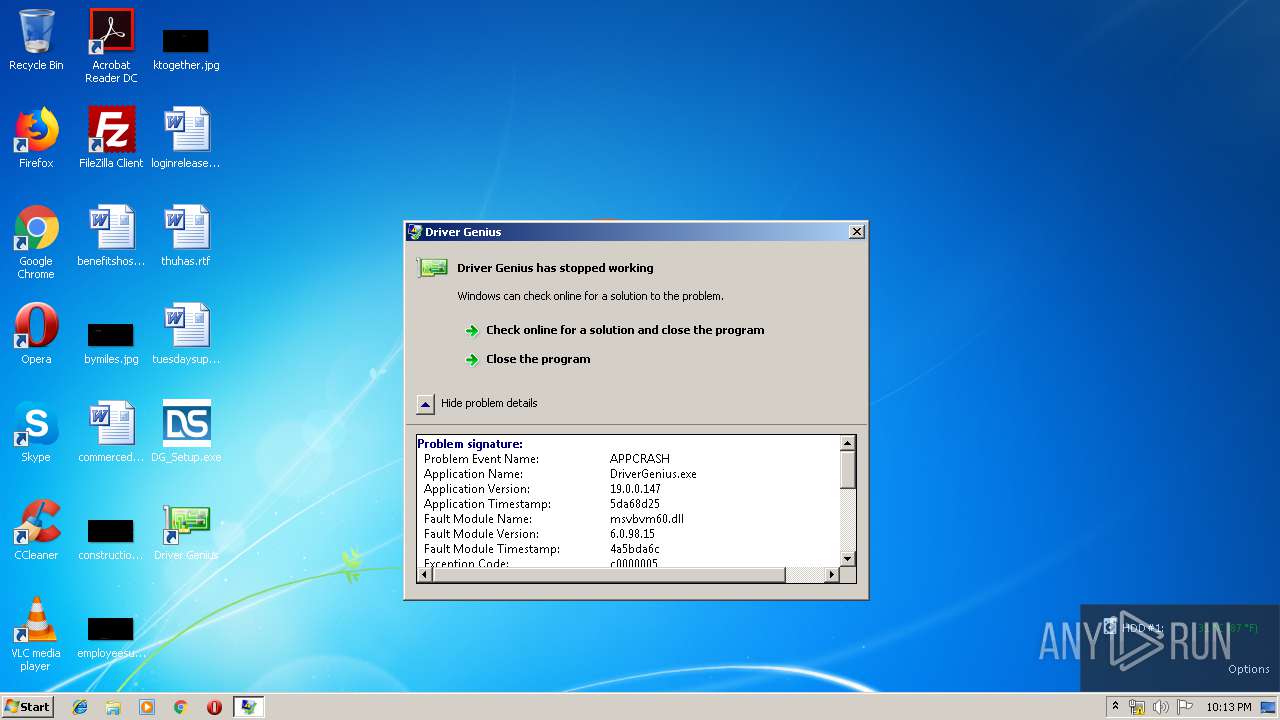
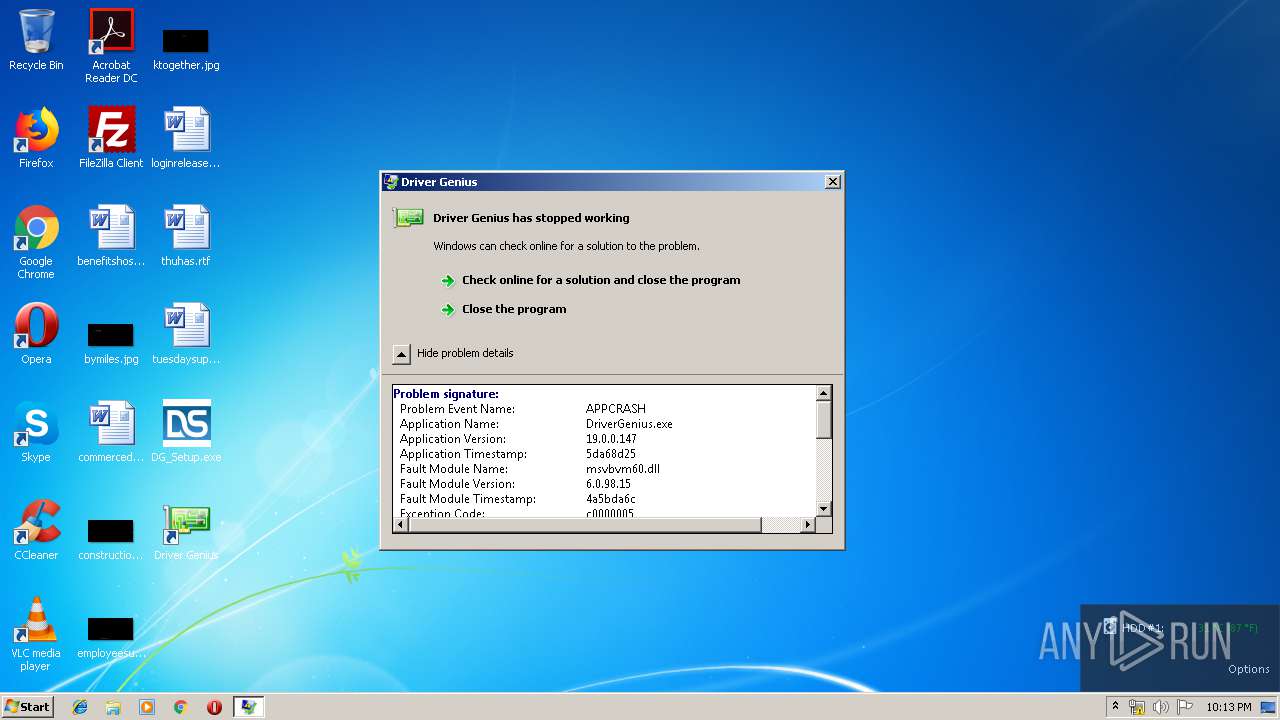
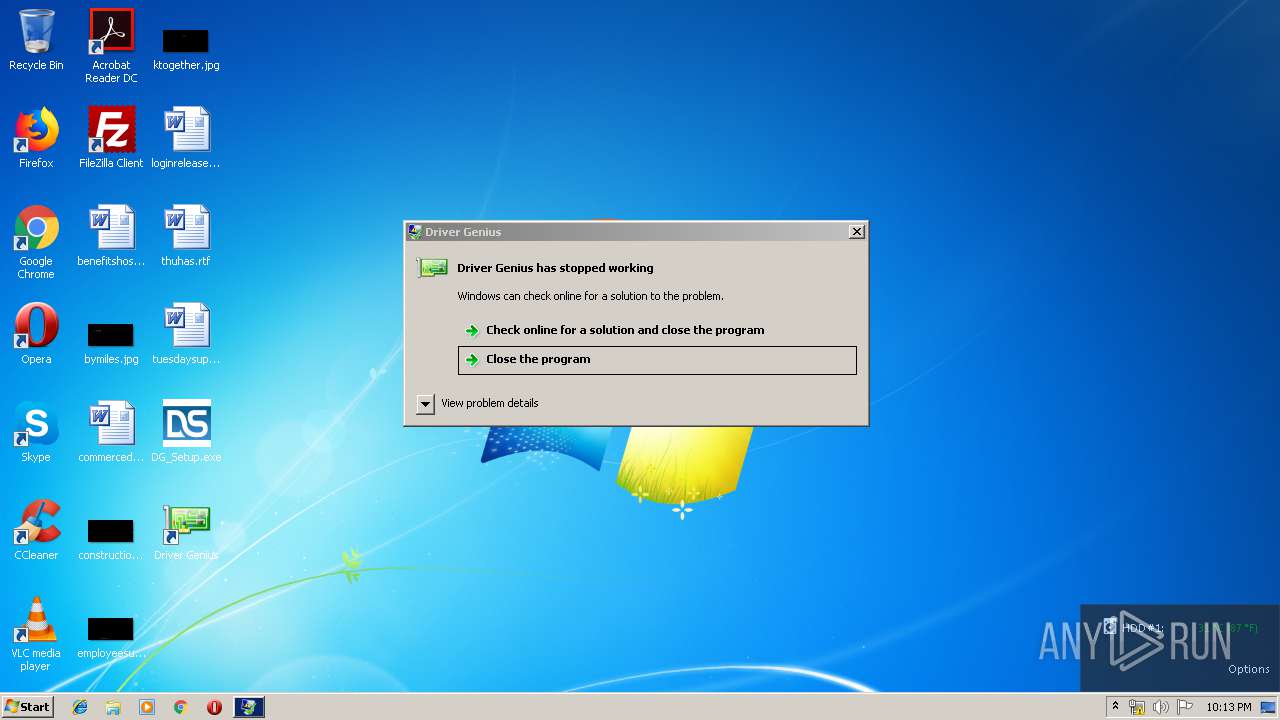
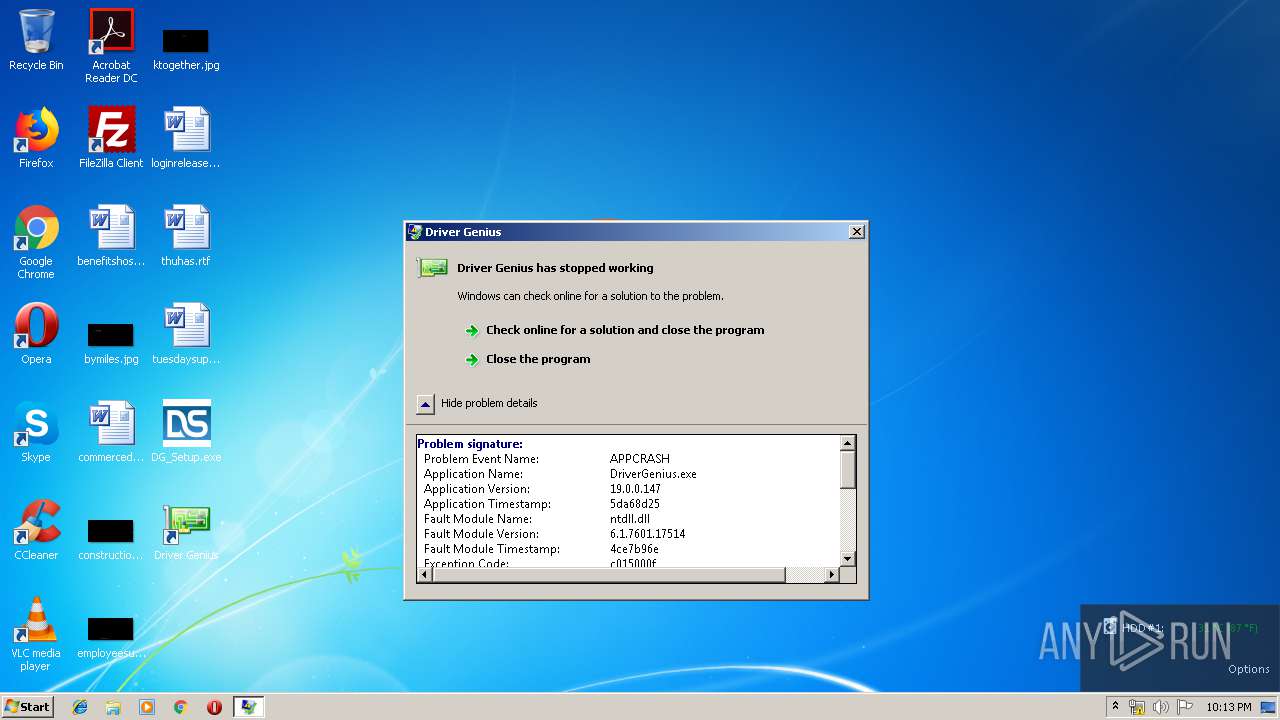
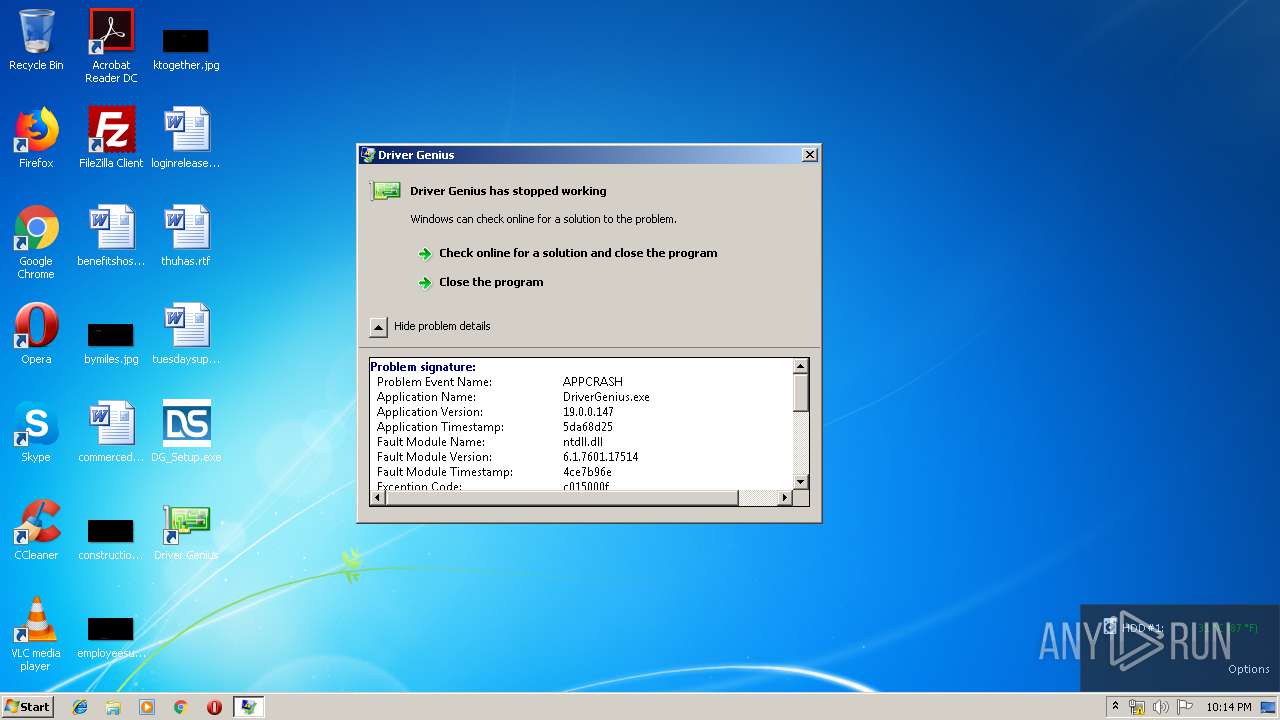
Application was crashed
- DriverGenius.exe (PID: 1912)
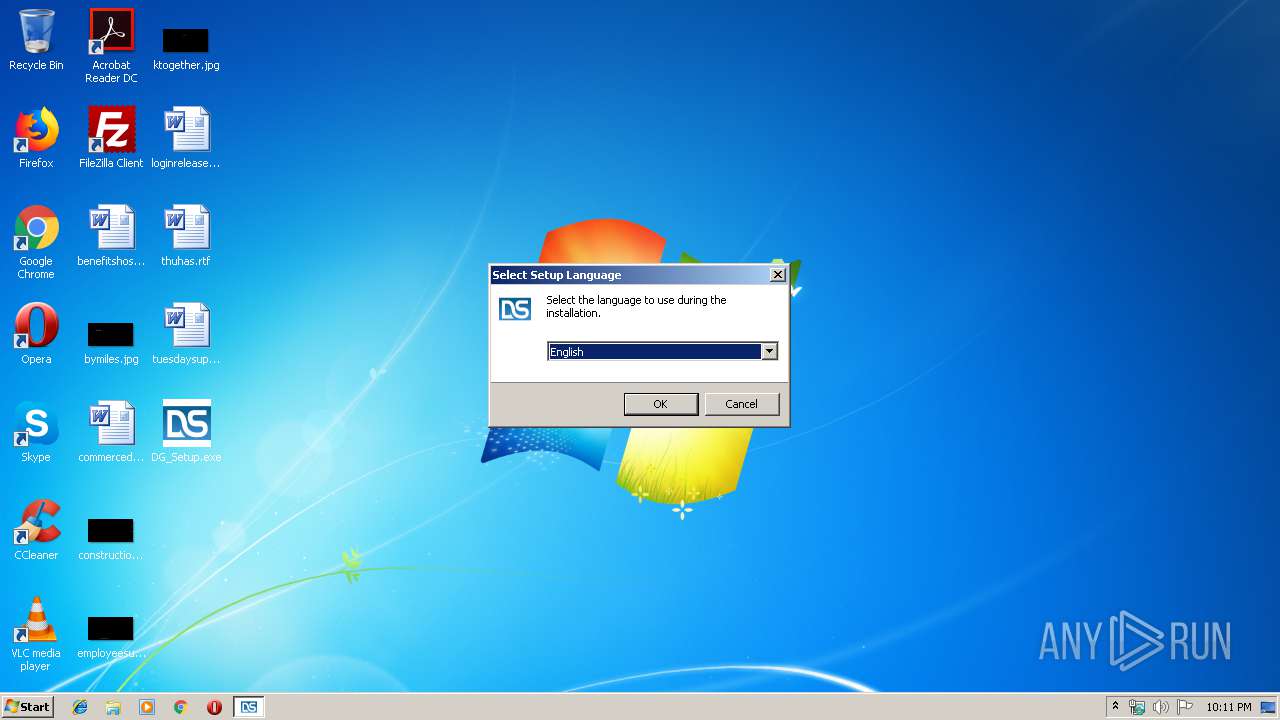
Manual execution by user
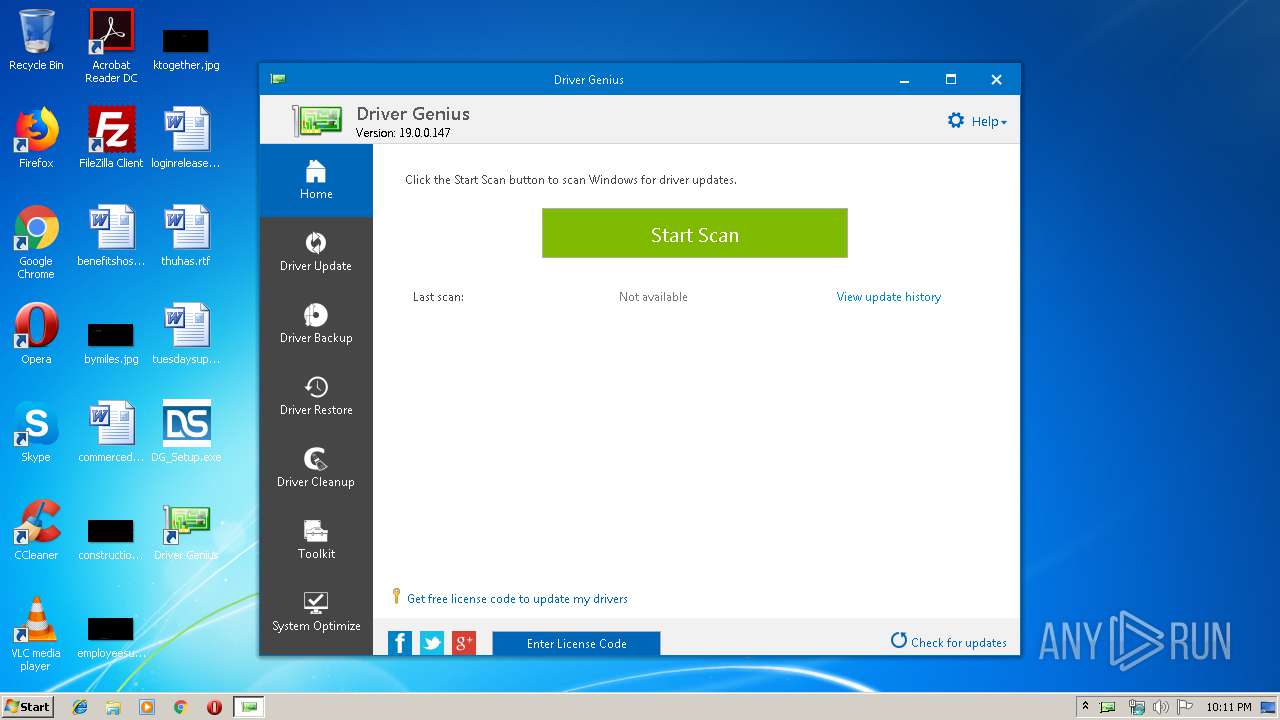
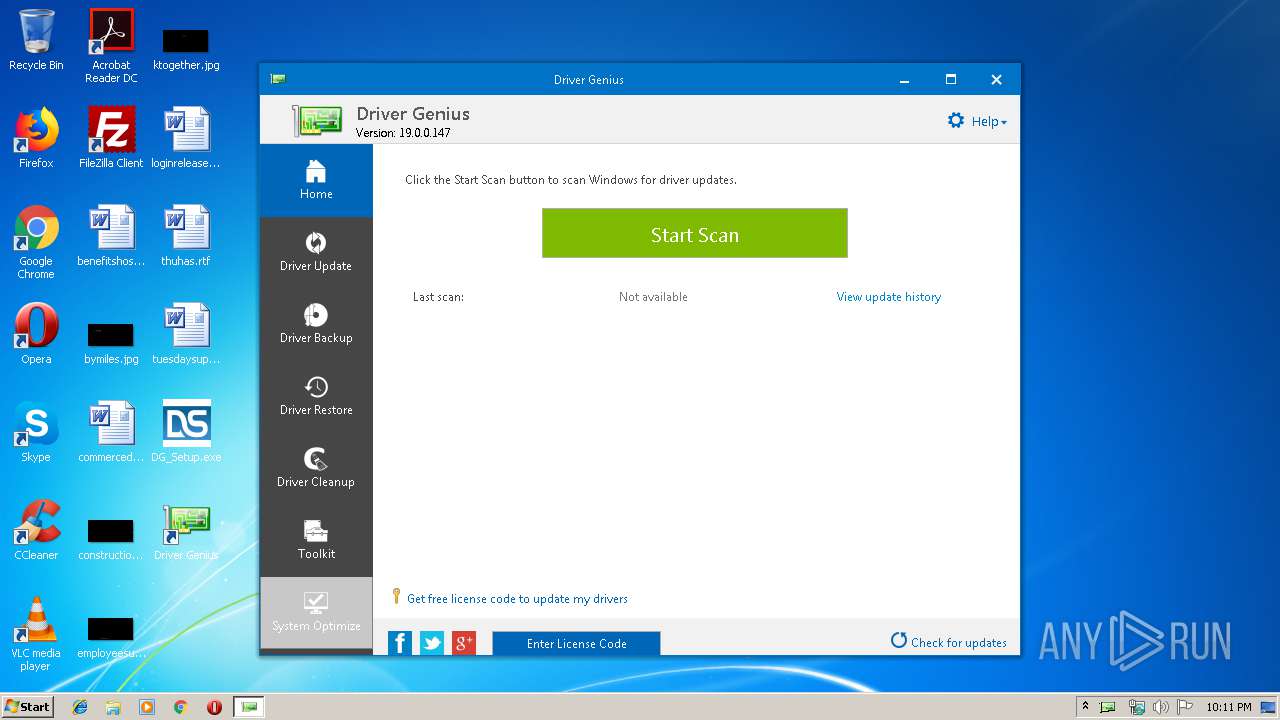
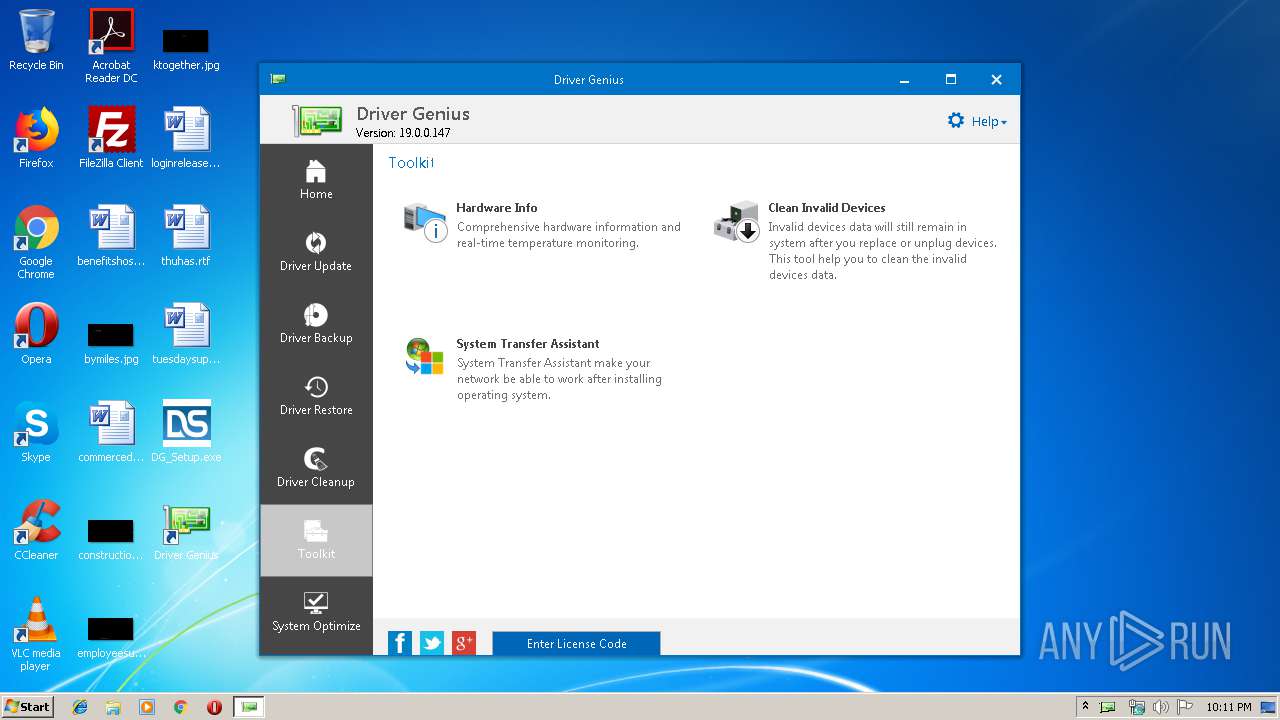
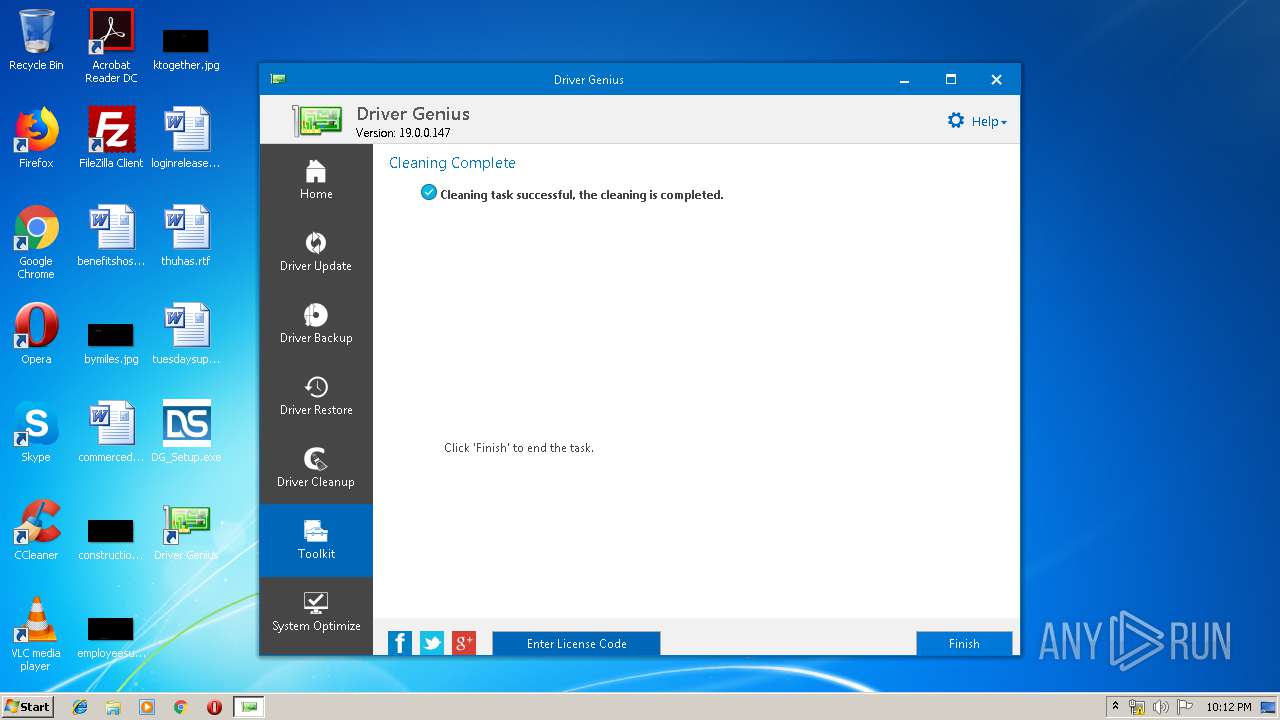
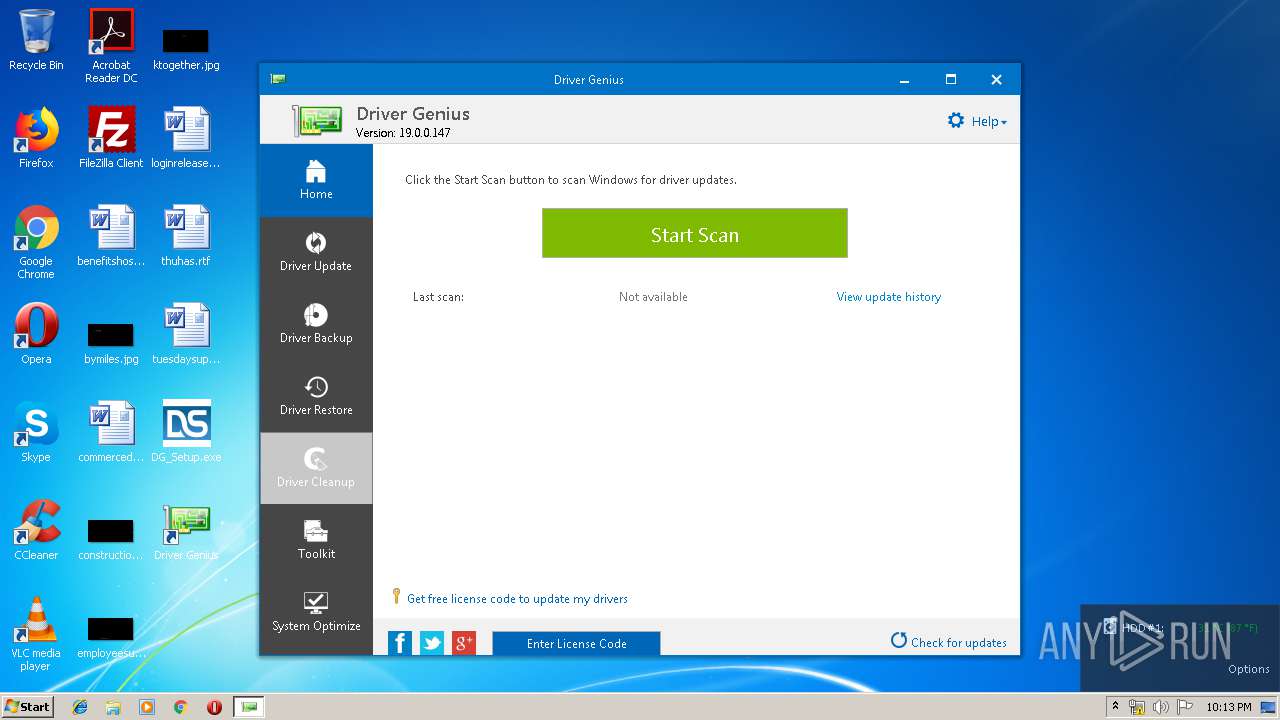
- DriverGenius.exe (PID: 624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:27 10:22:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 682496 |
| InitializedDataSize: | 88576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7ed0 |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.0.0.0 |
| ProductVersionNumber: | 19.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
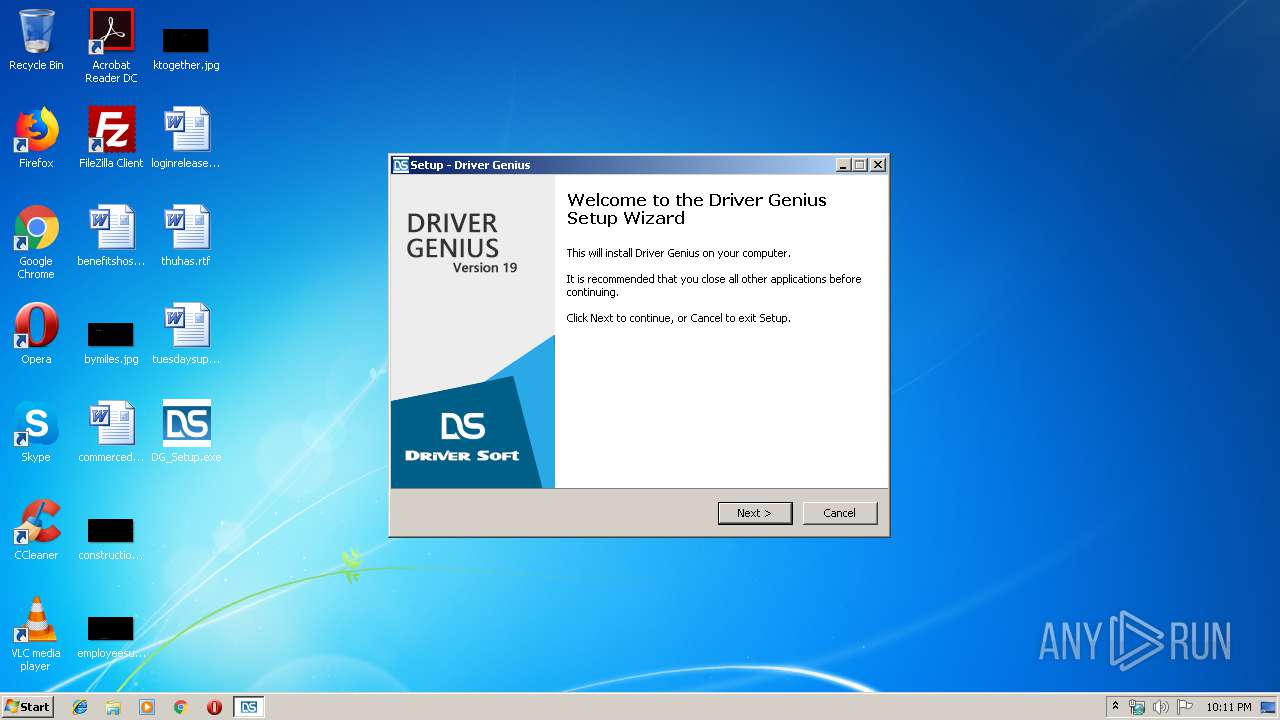
| CompanyName: | Driver-Soft Inc. |
| FileDescription: | Driver Genius Setup |
| FileVersion: | 19.0 |
| LegalCopyright: | Copyright © 2002-2019 Driver-Soft Inc. All rights reserved. |
| OriginalFileName: | |
| ProductName: | Driver Genius |
| ProductVersion: | 19.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2019 08:22:11 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Driver-Soft Inc. |
| FileDescription: | Driver Genius Setup |
| FileVersion: | 19.0 |
| LegalCopyright: | Copyright © 2002-2019 Driver-Soft Inc. All rights reserved. |
| OriginalFileName: | - |
| ProductName: | Driver Genius |
| ProductVersion: | 19.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 27-Apr-2019 08:22:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A50E0 | 0x000A5200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.36825 |
.itext | 0x000A7000 | 0x00001668 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95049 |
.data | 0x000A9000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.02787 |
.bss | 0x000AD000 | 0x0000676C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000B4000 | 0x00000F1C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.79161 |
.didata | 0x000B5000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74582 |
.edata | 0x000B6000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.88107 |
.tls | 0x000B7000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000B8000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.36974 |
.rsrc | 0x000B9000 | 0x00010B30 | 0x00010C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.89035 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.7544 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.56935 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 7.98742 | 32743 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.3888 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.09121 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.64482 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000B063C |
__dbk_fcall_wrapper | 2 | 0x0000D3DC |
TMethodImplementationIntercept | 3 | 0x00053ABC |
Total processes
101
Monitored processes
37
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Windows\System32\schtasks.exe" /Run /I /TN "Driver Genius Skip UAC" | C:\Windows\System32\schtasks.exe | — | DriverGenius.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 624 | "C:\Program Files\Driver-Soft\DriverGenius\DriverGenius.exe" | C:\Program Files\Driver-Soft\DriverGenius\DriverGenius.exe | — | explorer.exe | |||||||||||
User: admin Company: Driver-Soft Inc. Integrity Level: MEDIUM Description: Driver Genius Exit code: 0 Version: 19.00.0147 Modules
| |||||||||||||||
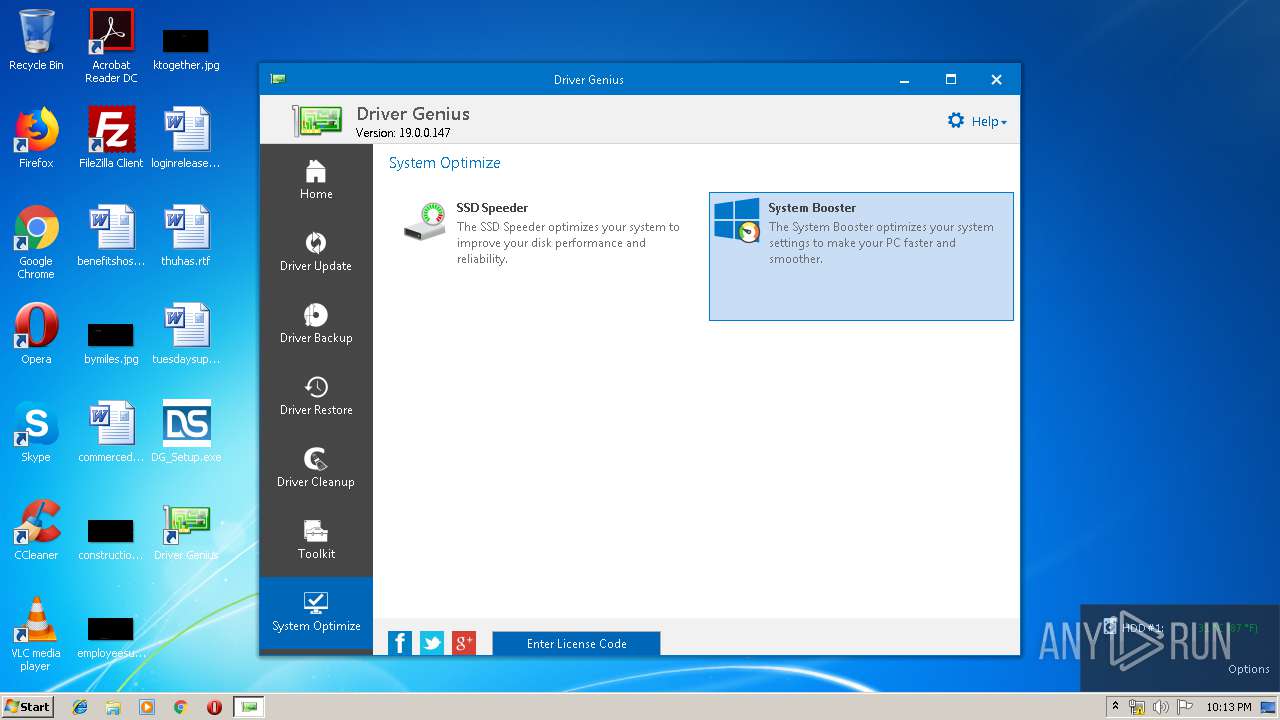
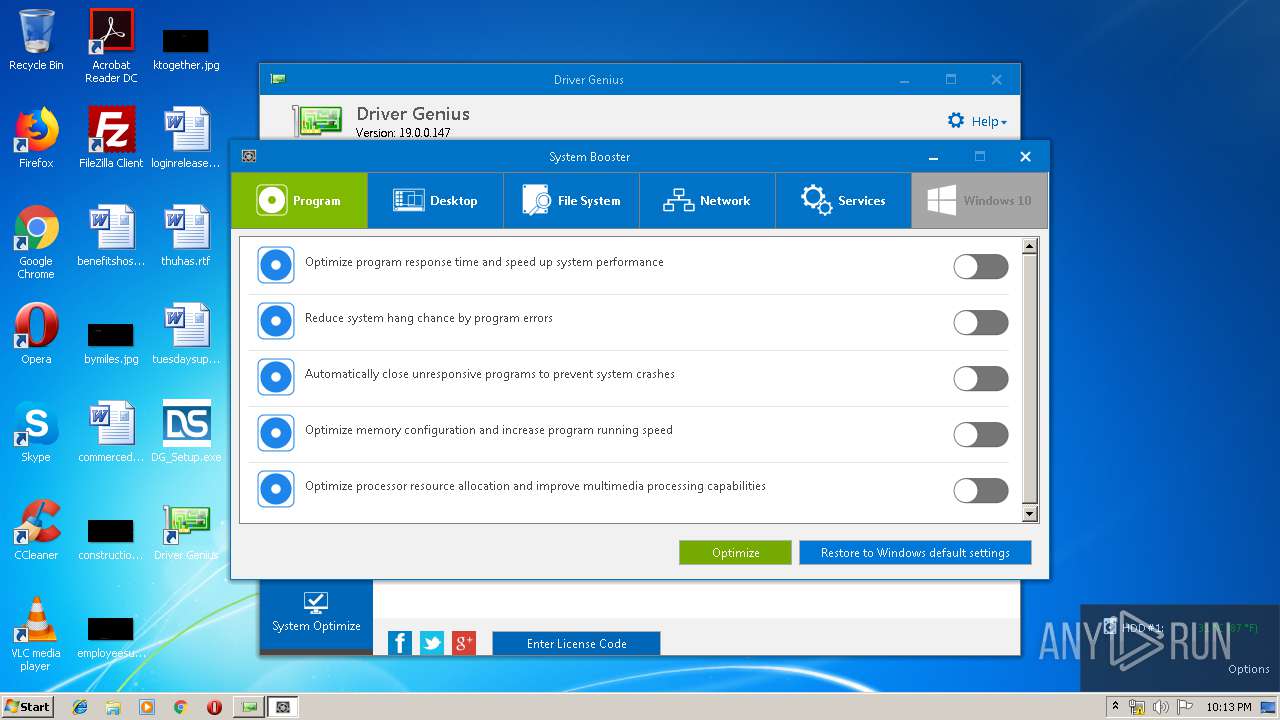
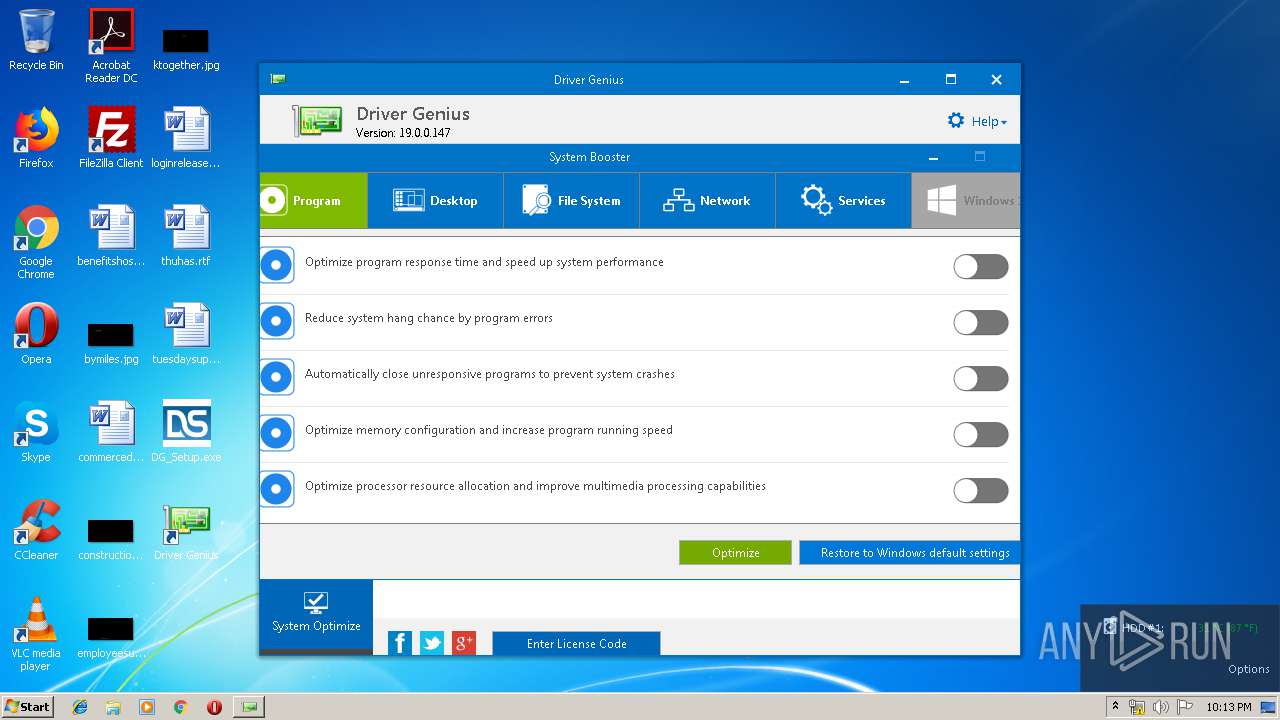
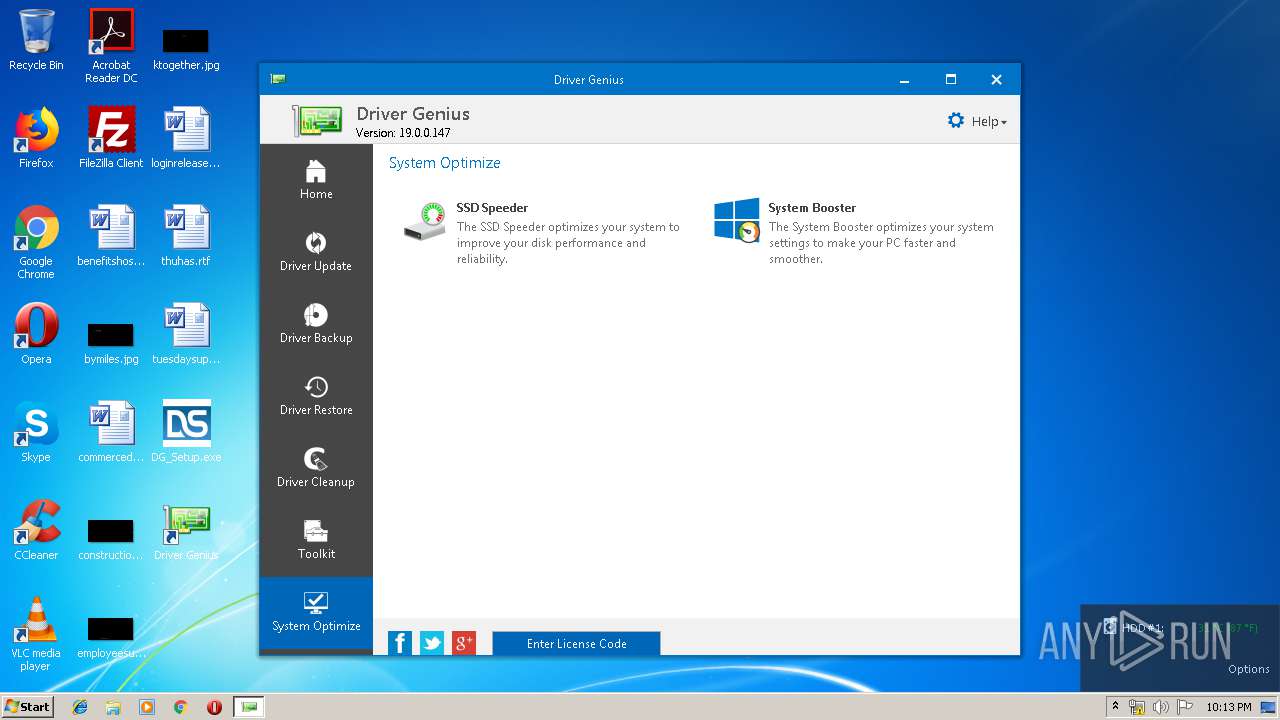
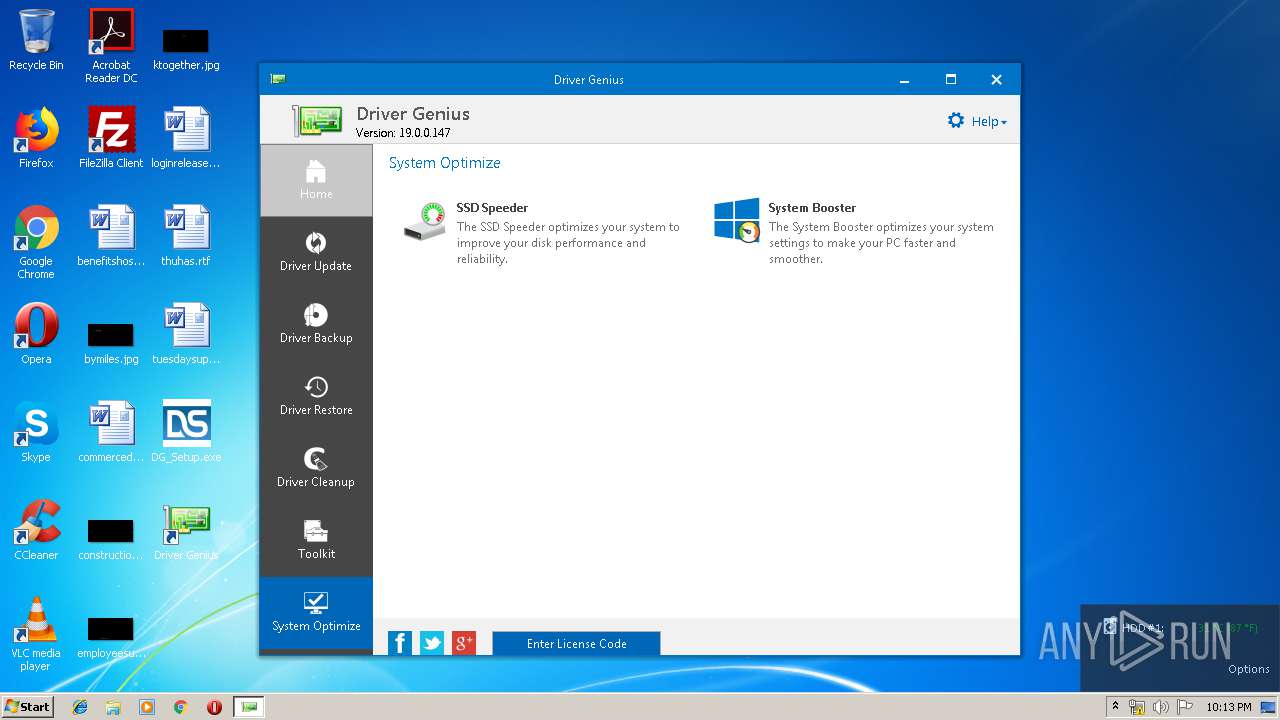
| 836 | "C:\Program Files\Driver-Soft\DriverGenius\SystemBooster.exe" | C:\Program Files\Driver-Soft\DriverGenius\SystemBooster.exe | — | DriverGenius.exe | |||||||||||
User: admin Company: Driver-Soft Inc Integrity Level: HIGH Description: System Booster Exit code: 0 Version: 1.01 Modules
| |||||||||||||||
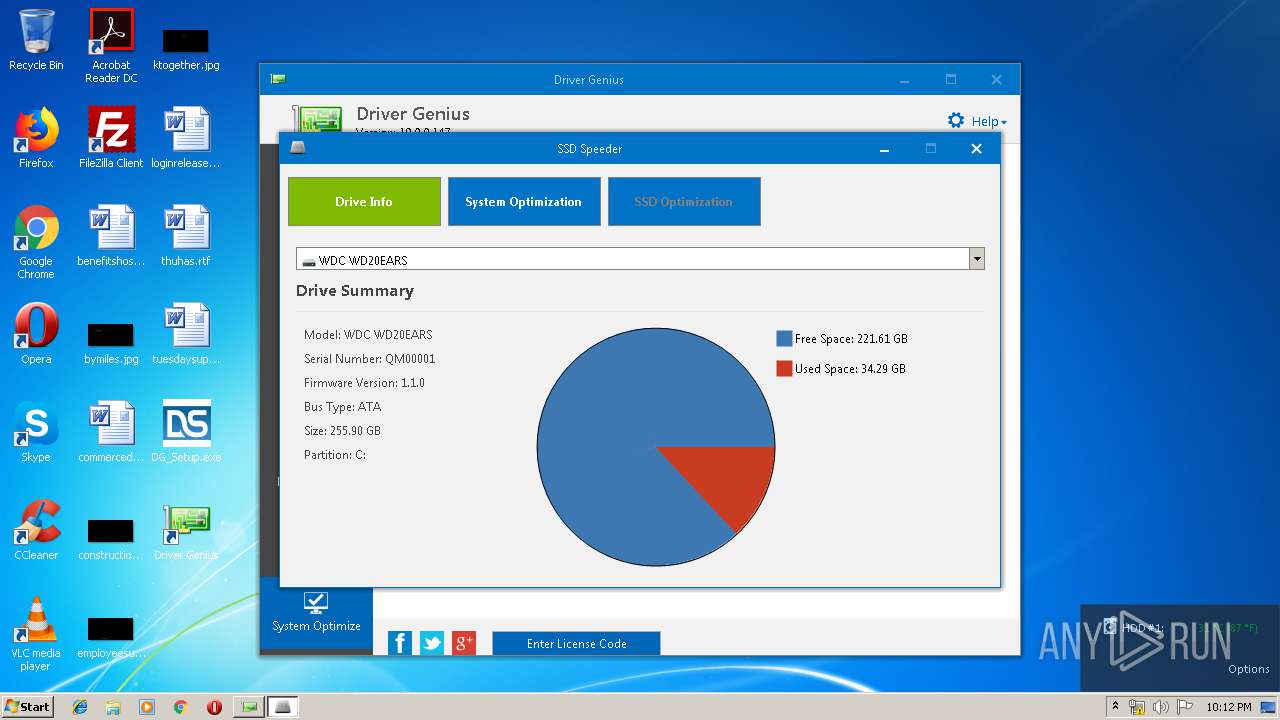
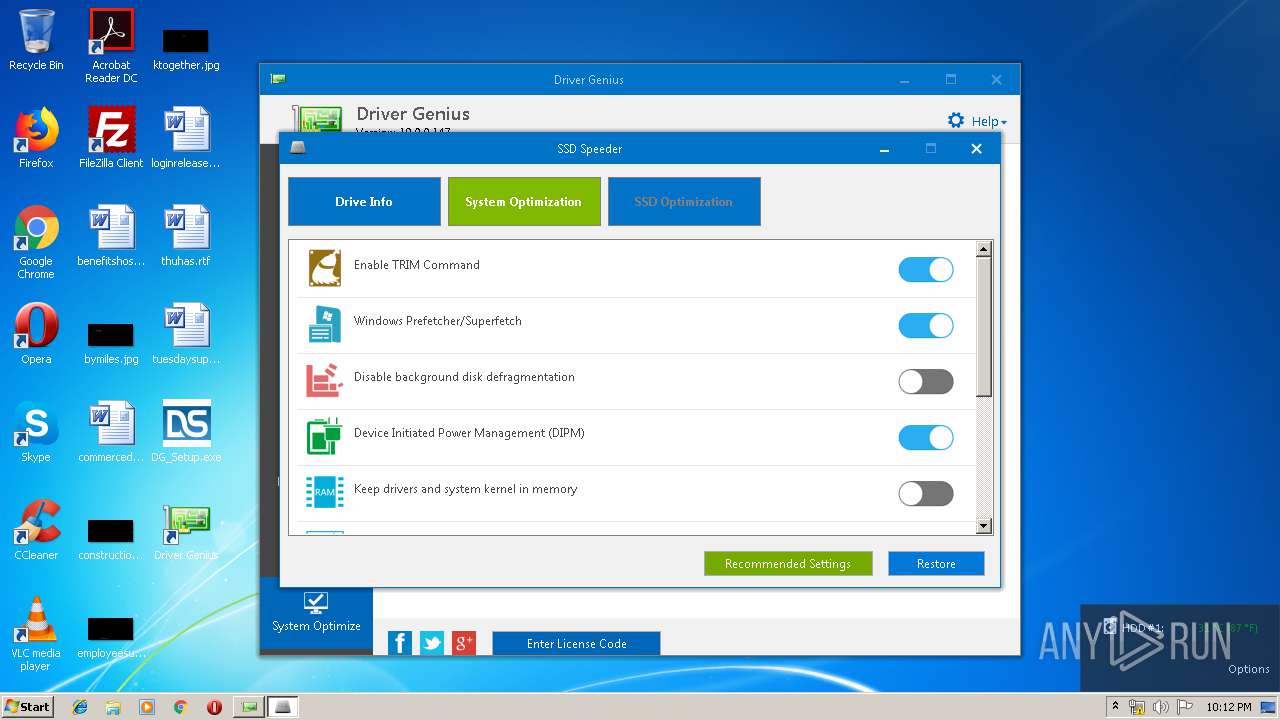
| 920 | "C:\Program Files\Driver-Soft\DriverGenius\SSDSpeeder.exe" | C:\Program Files\Driver-Soft\DriverGenius\SSDSpeeder.exe | — | DriverGenius.exe | |||||||||||
User: admin Company: Driver-Soft Inc Integrity Level: HIGH Description: SSD Speeder Exit code: 0 Version: 1.02.0006 Modules
| |||||||||||||||
| 920 | "C:\Users\admin\AppData\Local\Temp\installapi.exe" remove @"IDE\CdRomQEMU_QEMU_DVD-ROM_______________________1.1.____\5&3a2a5854&0&1.0.0" | C:\Users\admin\AppData\Local\Temp\installapi.exe | — | DriverGenius.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 10.0.18362.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 992 | C:\Windows\system32\WerFault.exe -u -p 1912 -s 1416 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | "C:\Users\admin\AppData\Local\Temp\is-JG2I9.tmp\7za.exe" x -aoa "C:\Users\admin\AppData\Local\Temp\is-JG2I9.tmp\liveupdate.zip" | C:\Users\admin\AppData\Local\Temp\is-JG2I9.tmp\7za.exe | — | DG_Setup.tmp | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 1252 | "C:\Users\admin\AppData\Local\Temp\installapi.exe" remove @"STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot25" | C:\Users\admin\AppData\Local\Temp\installapi.exe | — | DriverGenius.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 10.0.18362.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | "C:\Users\admin\AppData\Local\Temp\installapi.exe" remove @"HID\VID_0627&PID_0001\6&2e2010ad&0&0000" | C:\Users\admin\AppData\Local\Temp\installapi.exe | — | DriverGenius.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 10.0.18362.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1784 | "C:\Windows\system32\schtasks.exe" /delete /tn "Driver Genius" /f | C:\Windows\system32\schtasks.exe | — | DG_Setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 299
Read events
707
Write events
585
Delete events
7
Modification events
| (PID) Process: | (2480) DG_Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B00900009873BC0E82ACD501 | |||
| (PID) Process: | (2480) DG_Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 009B0FE32E35D3A51545183964642E53BBAA5C50B118E4107332063EDA520917 | |||
| (PID) Process: | (2480) DG_Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2480) DG_Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Driver-Soft\DriverGenius\DriverGenius.exe | |||
| (PID) Process: | (2480) DG_Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: ECED43DA0F67039ABC28A1C4F352391737A98F47C1AC52E546BC7AE3AFB98C41 | |||
| (PID) Process: | (2480) DG_Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Driver-Soft\DriverGenius |
| Operation: | write | Name: | FirstRun |
Value: 1 | |||
| (PID) Process: | (2480) DG_Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Driver-Soft\DriverGenius |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files\Driver-Soft\DriverGenius | |||
| (PID) Process: | (2480) DG_Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Driver-Soft\DriverGenius |
| Operation: | write | Name: | UILanguage |
Value: 0409 | |||
| (PID) Process: | (2480) DG_Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Driver Genius_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.0.2 (u) | |||
| (PID) Process: | (2480) DG_Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Driver Genius_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Driver-Soft\DriverGenius | |||
Executable files
20
Suspicious files
6
Text files
134
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | DG_Setup.tmp | C:\Program Files\Driver-Soft\DriverGenius\is-PN9B4.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | DG_Setup.tmp | C:\Program Files\Driver-Soft\DriverGenius\is-2UPEJ.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | DG_Setup.tmp | C:\Program Files\Driver-Soft\DriverGenius\is-D4P46.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | DG_Setup.tmp | C:\Program Files\Driver-Soft\DriverGenius\is-3HB5A.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | DG_Setup.tmp | C:\Program Files\Driver-Soft\DriverGenius\is-1MFL6.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | DG_Setup.tmp | C:\Program Files\Driver-Soft\DriverGenius\Resource\is-O21NS.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | DG_Setup.tmp | C:\Program Files\Driver-Soft\DriverGenius\Resource\is-8GE5G.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | DG_Setup.tmp | C:\Program Files\Driver-Soft\DriverGenius\Resource\is-K7EB0.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | DG_Setup.tmp | C:\Program Files\Driver-Soft\DriverGenius\is-5F1CO.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | DG_Setup.tmp | C:\Program Files\Driver-Soft\DriverGenius\is-9A3KN.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2480 | DG_Setup.tmp | GET | 200 | 169.62.150.26:80 | http://www.driver-soft.com/liveupdate/liveupdate.zip | US | compressed | 2.21 Kb | malicious |
2480 | DG_Setup.tmp | HEAD | 200 | 169.62.150.26:80 | http://www.driver-soft.com/liveupdate/DriverDB_V19.dbd | US | compressed | 2.21 Kb | malicious |
2480 | DG_Setup.tmp | GET | 200 | 169.62.150.26:80 | http://www.driver-soft.com/liveupdate/DriverDB_V19.dbd | US | binary | 698 Kb | malicious |
1912 | DriverGenius.exe | GET | 200 | 169.62.150.26:80 | http://www.driver-soft.com/liveupdate/liveupdate.zip | US | compressed | 2.21 Kb | malicious |
1912 | DriverGenius.exe | GET | 206 | 169.62.150.26:80 | http://www.driver-soft.com/liveupdate/liveupdate.zip | US | compressed | 2.21 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2480 | DG_Setup.tmp | 169.62.150.26:80 | www.driver-soft.com | — | US | malicious |
— | — | 169.62.150.26:80 | www.driver-soft.com | — | US | malicious |
1912 | DriverGenius.exe | 169.62.150.26:80 | www.driver-soft.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.driver-soft.com |
| malicious |