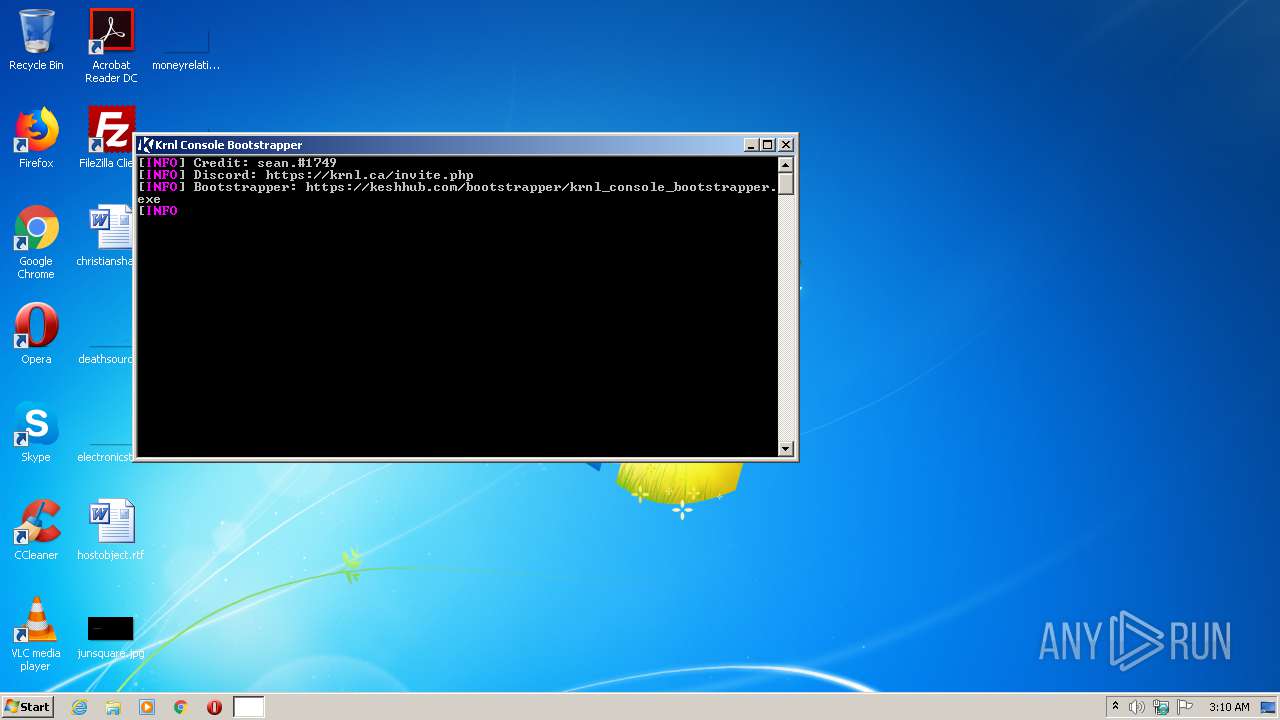
| File name: | krnl_console_bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/e66d4065-6ff9-4447-824e-6737050cc525 |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2021, 02:10:15 |
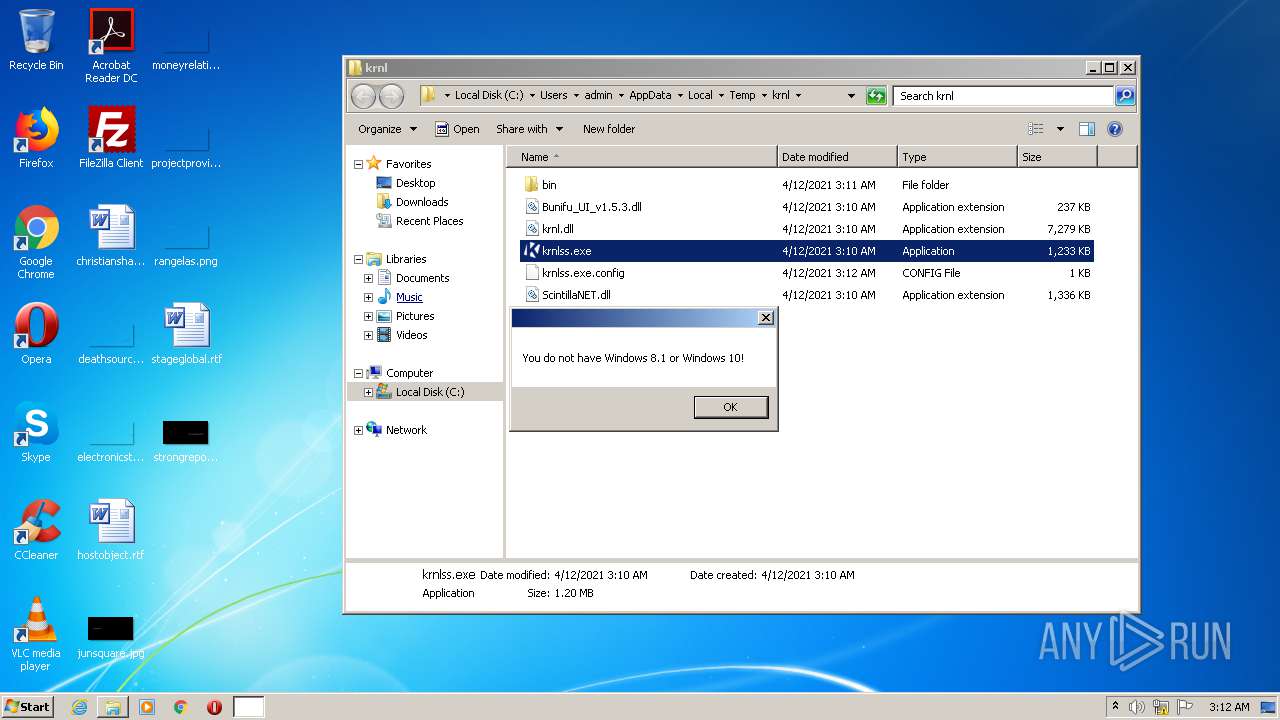
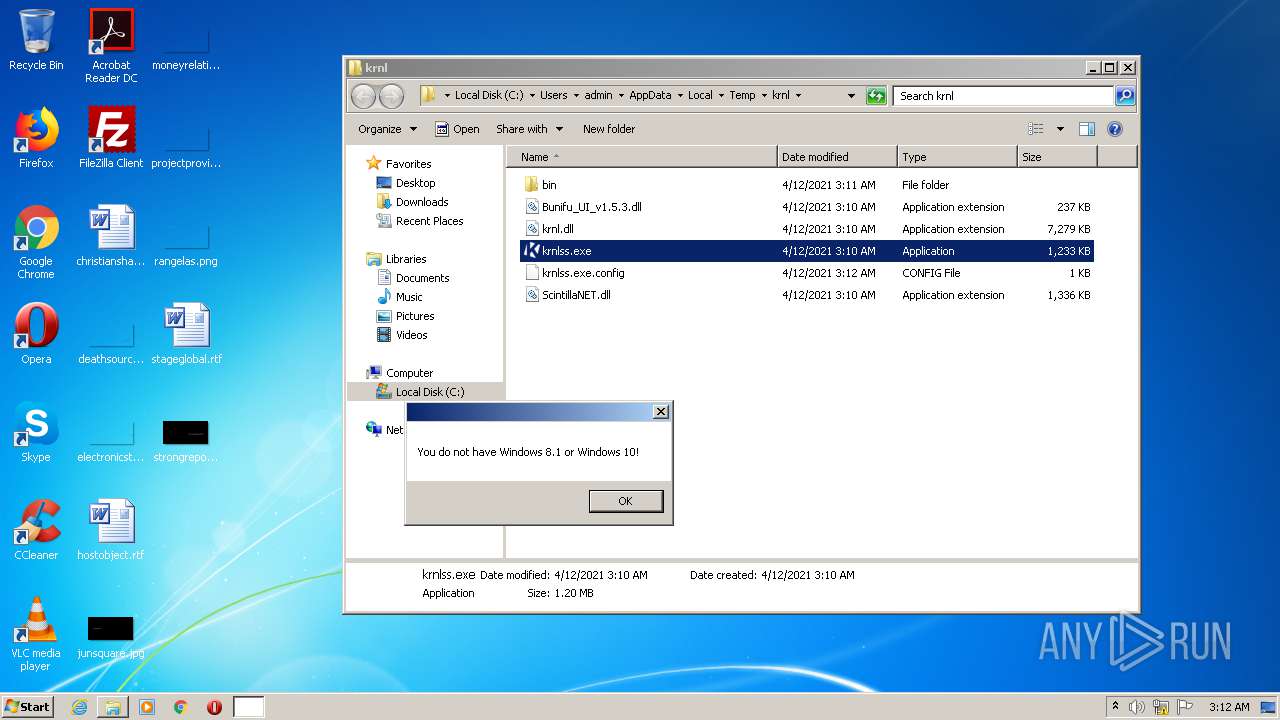
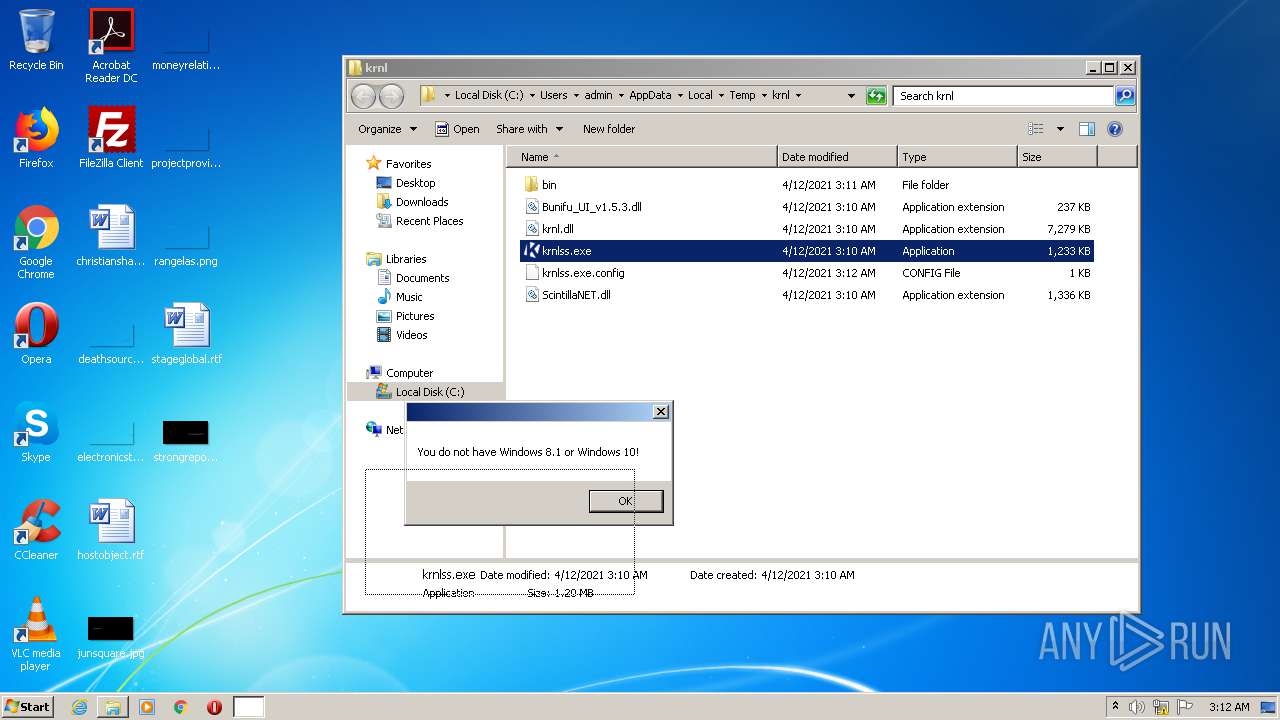
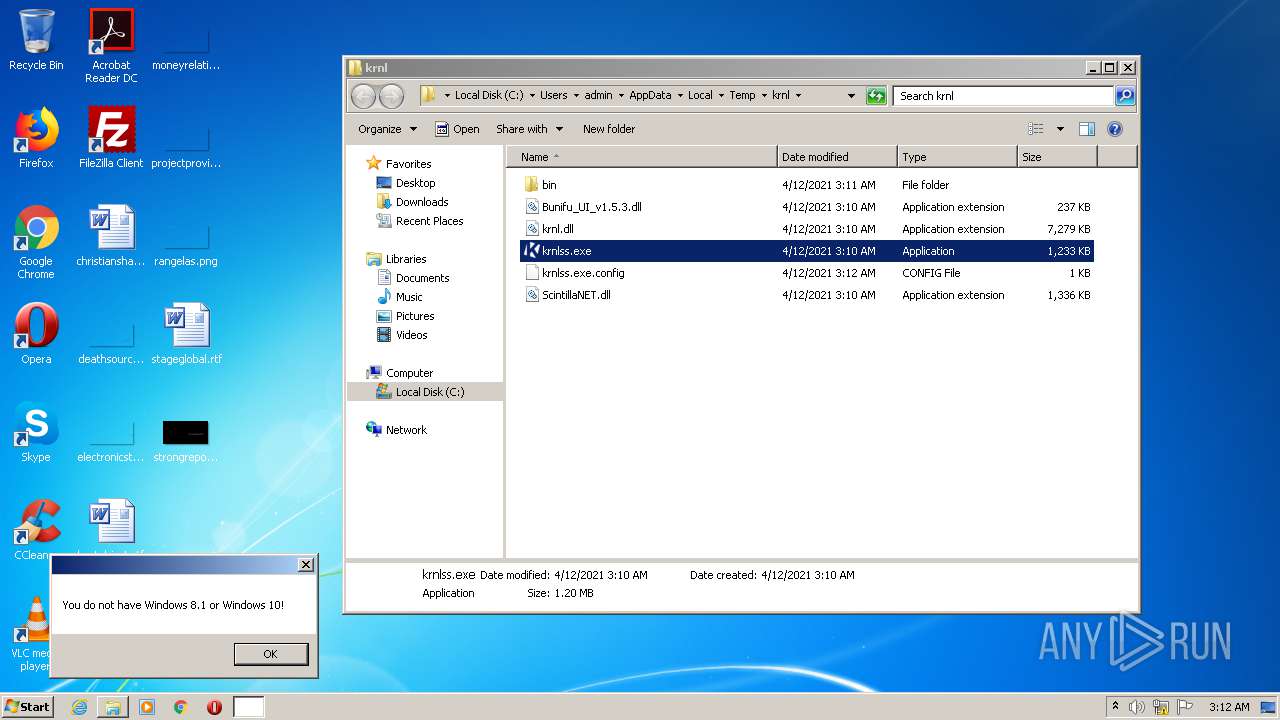
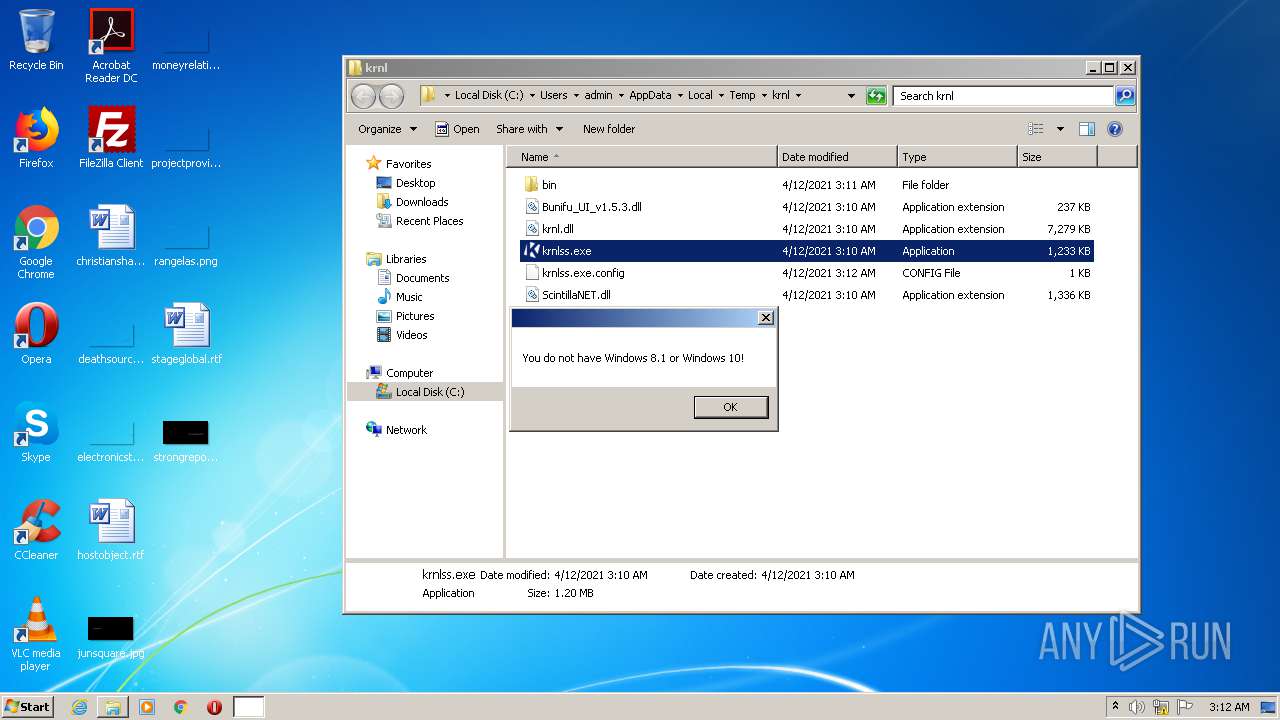
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 8F251AE83B2C4898354F35D4BBBA2C03 |
| SHA1: | C74A55808D71EE85092247BB9AB57E54349A2356 |
| SHA256: | 8E3342F663E3F729F49ACA6BF15EB99F2327BF83A7A72E8F28C04803AA766BD4 |
| SSDEEP: | 24576:gU7ecSgL6y+gk+rnxdarFc3rn0Y5zmzRf1P2MVMbx4XclQ:gUzS65+x+rnxYr8rnL5yzpVM6XcS |
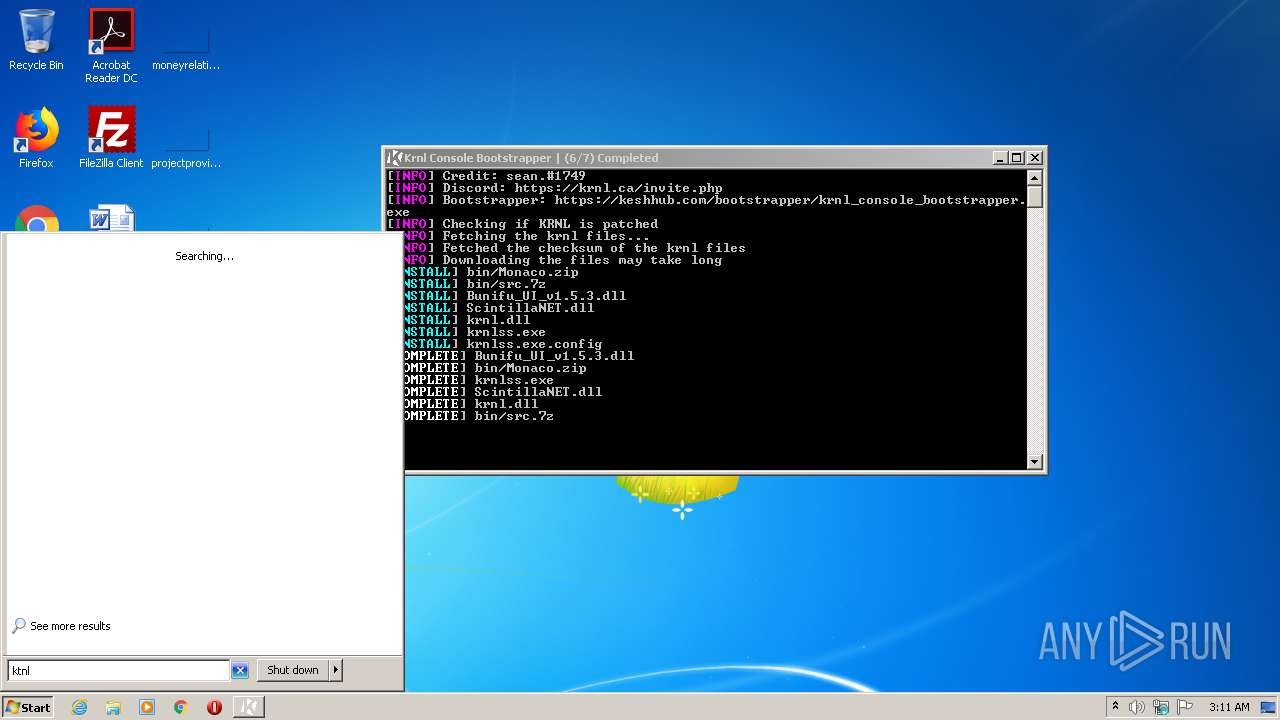
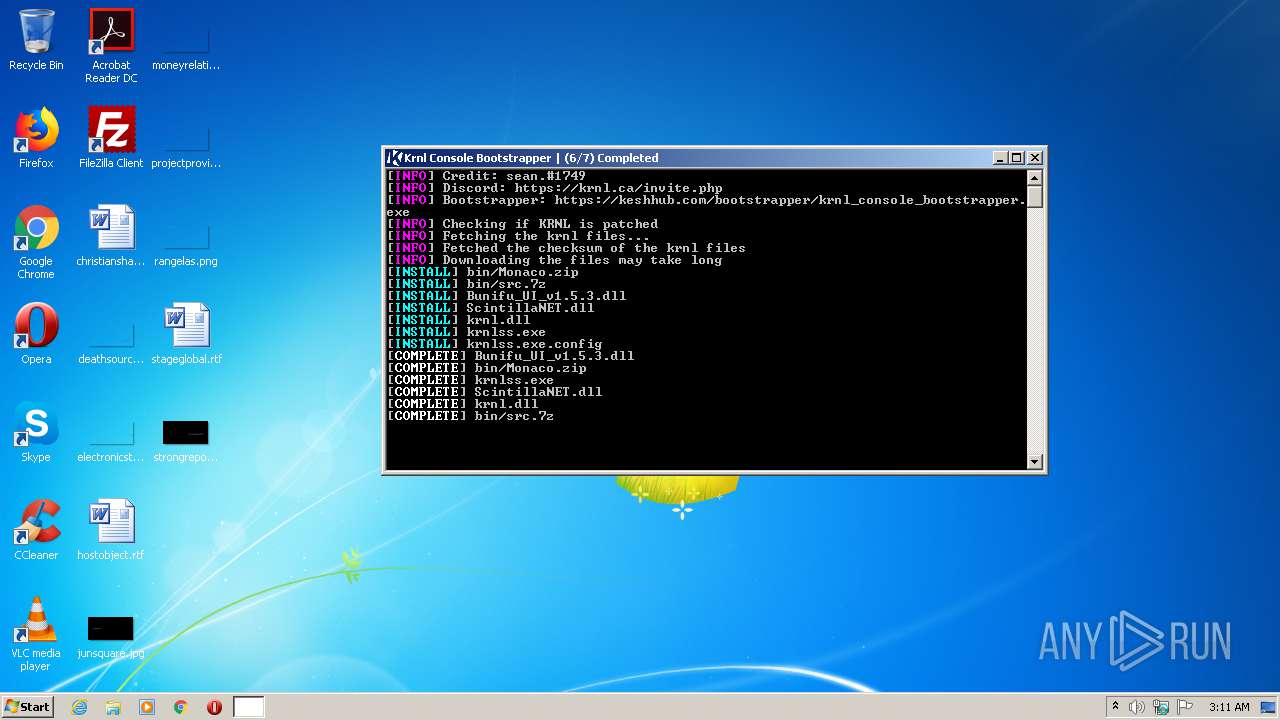
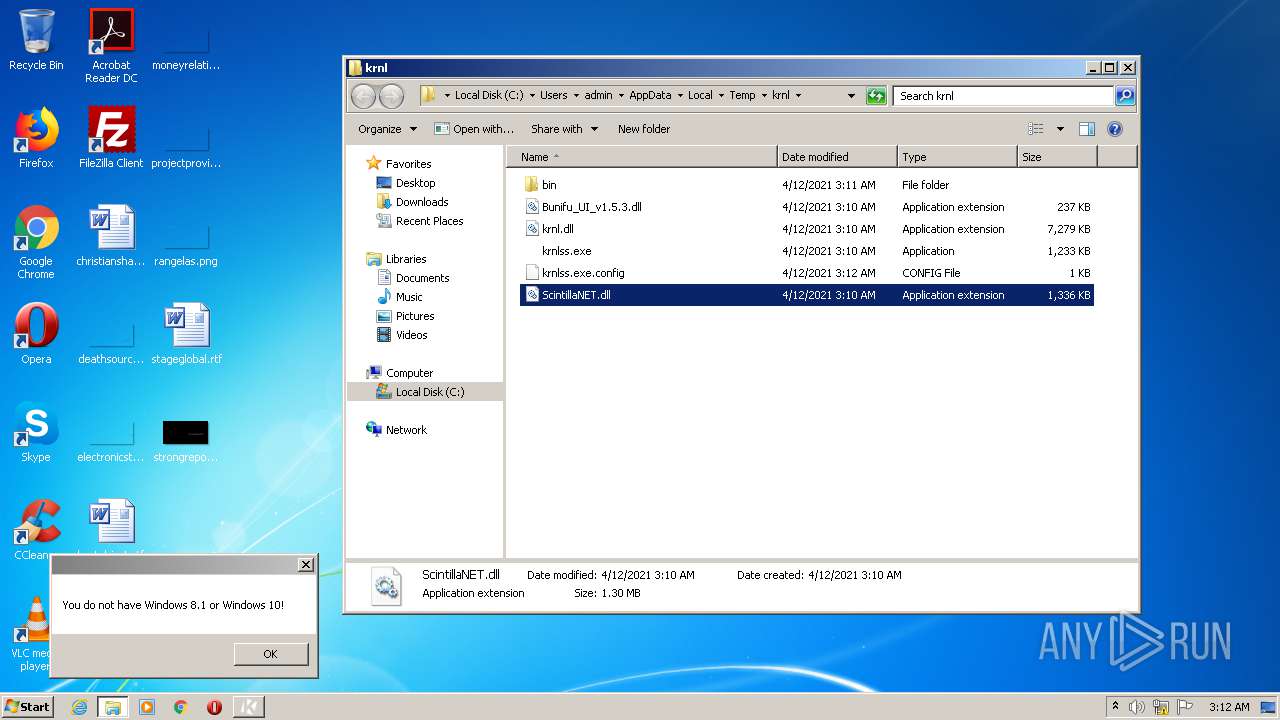
MALICIOUS
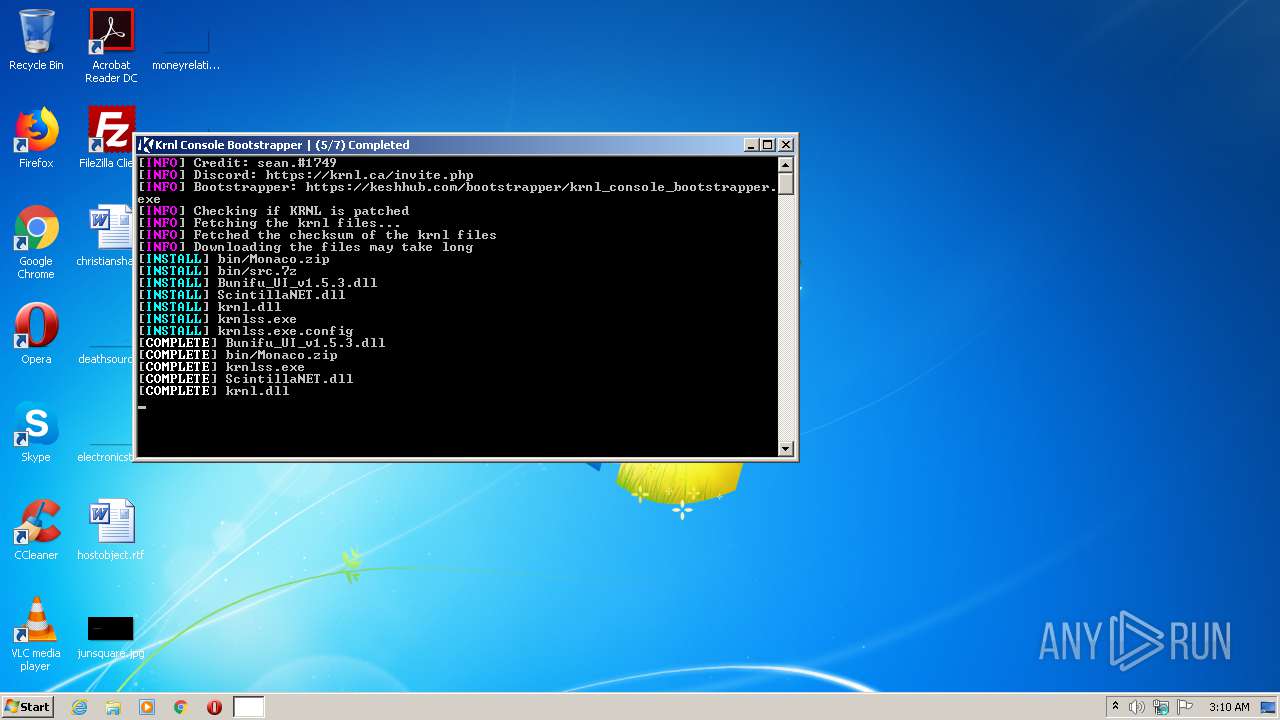
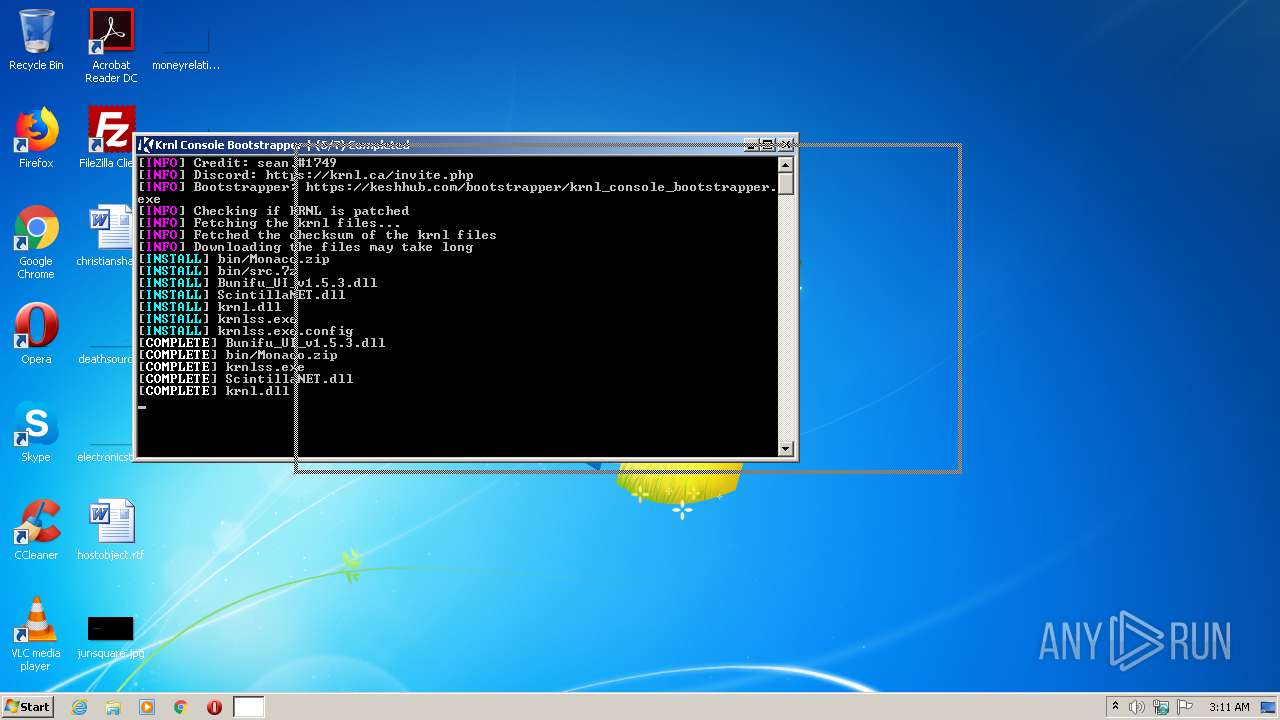
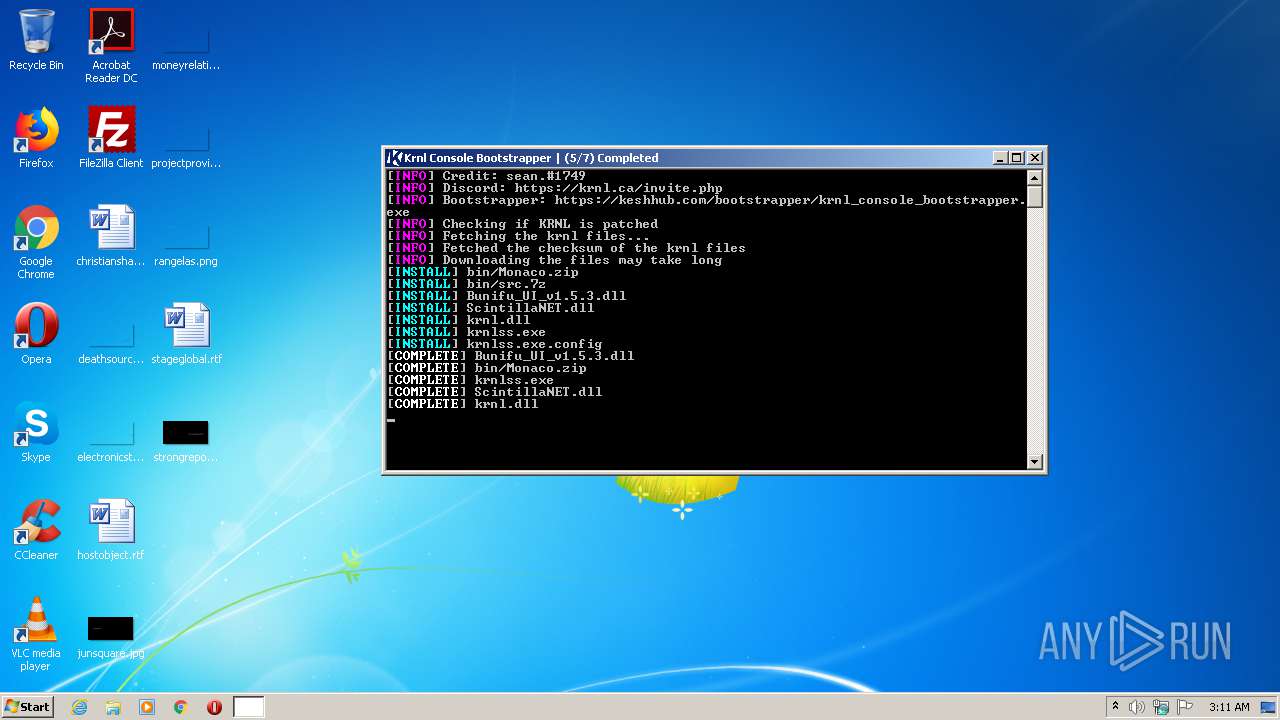
Loads dropped or rewritten executable
- krnl_console_bootstrapper.exe (PID: 548)
- krnlss.exe (PID: 3136)
- krnlss.exe (PID: 3792)
- krnlss.exe (PID: 3324)
- explorer.exe (PID: 1376)
Application was dropped or rewritten from another process
- 7za.exe (PID: 3764)
- 7za.exe (PID: 2228)
- krnlss.exe (PID: 2484)
- krnlss.exe (PID: 3136)
- krnlss.exe (PID: 3792)
- krnlss.exe (PID: 3324)
SUSPICIOUS
Executable content was dropped or overwritten
- krnl_console_bootstrapper.exe (PID: 548)
- 7za.exe (PID: 2228)
Drops a file with a compile date too recent
- krnl_console_bootstrapper.exe (PID: 548)
Drops a file that was compiled in debug mode
- krnl_console_bootstrapper.exe (PID: 548)
- 7za.exe (PID: 2228)
Executed via COM
- explorer.exe (PID: 1376)
Drops a file with too old compile date
- 7za.exe (PID: 2228)
Application launched itself
- krnlss.exe (PID: 2484)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | krnl_console_bootstrapper |
| OriginalFileName: | krnl_console_bootstrapper.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2021 |
| InternalName: | krnl_console_bootstrapper.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | krnl_console_bootstrapper |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1226ce |
| UninitializedDataSize: | - |
| InitializedDataSize: | 257024 |
| CodeSize: | 1181696 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2082:06:23 01:19:35+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 17-May-1946 16:51:19 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | krnl_console_bootstrapper |
| FileVersion: | 1.0.0.0 |
| InternalName: | krnl_console_bootstrapper.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | krnl_console_bootstrapper.exe |
| ProductName: | krnl_console_bootstrapper |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 17-May-1946 16:51:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x001206D4 | 0x00120800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58197 |
.rsrc | 0x00124000 | 0x0003E918 | 0x0003EA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.20886 |
.reloc | 0x00164000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 2.01924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
51
Monitored processes
9
Malicious processes
7
Suspicious processes
0
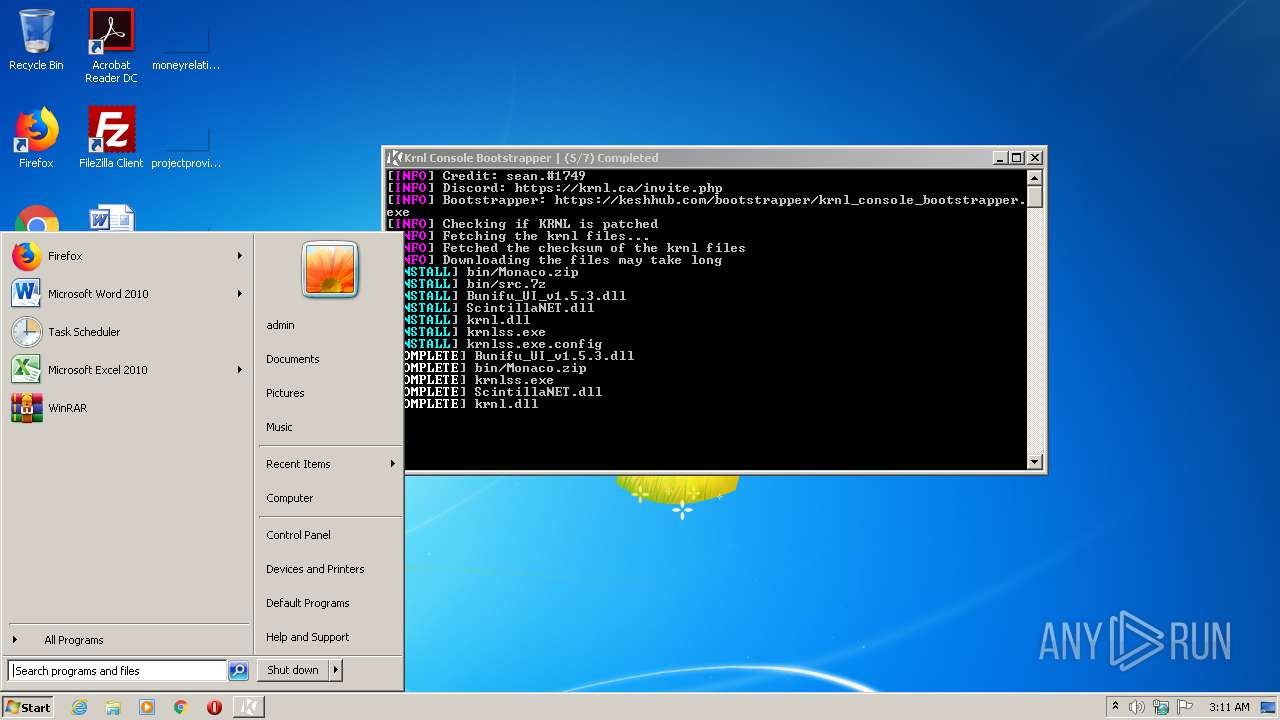
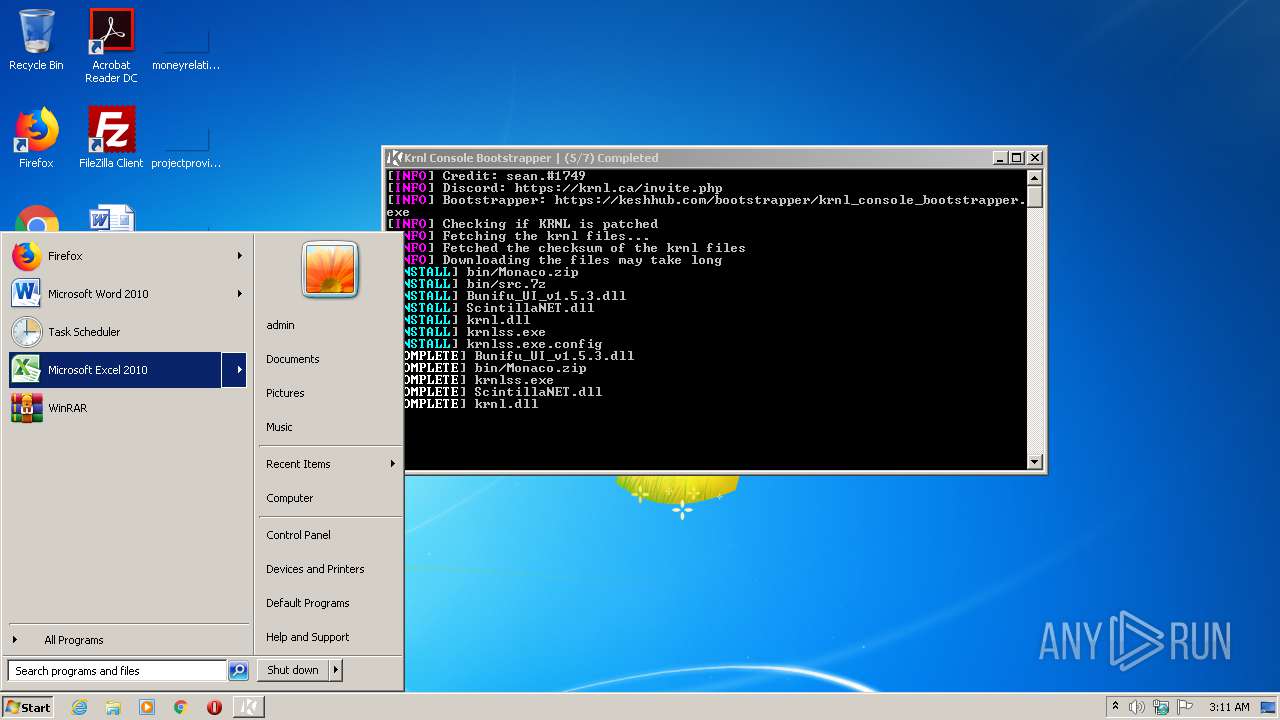
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
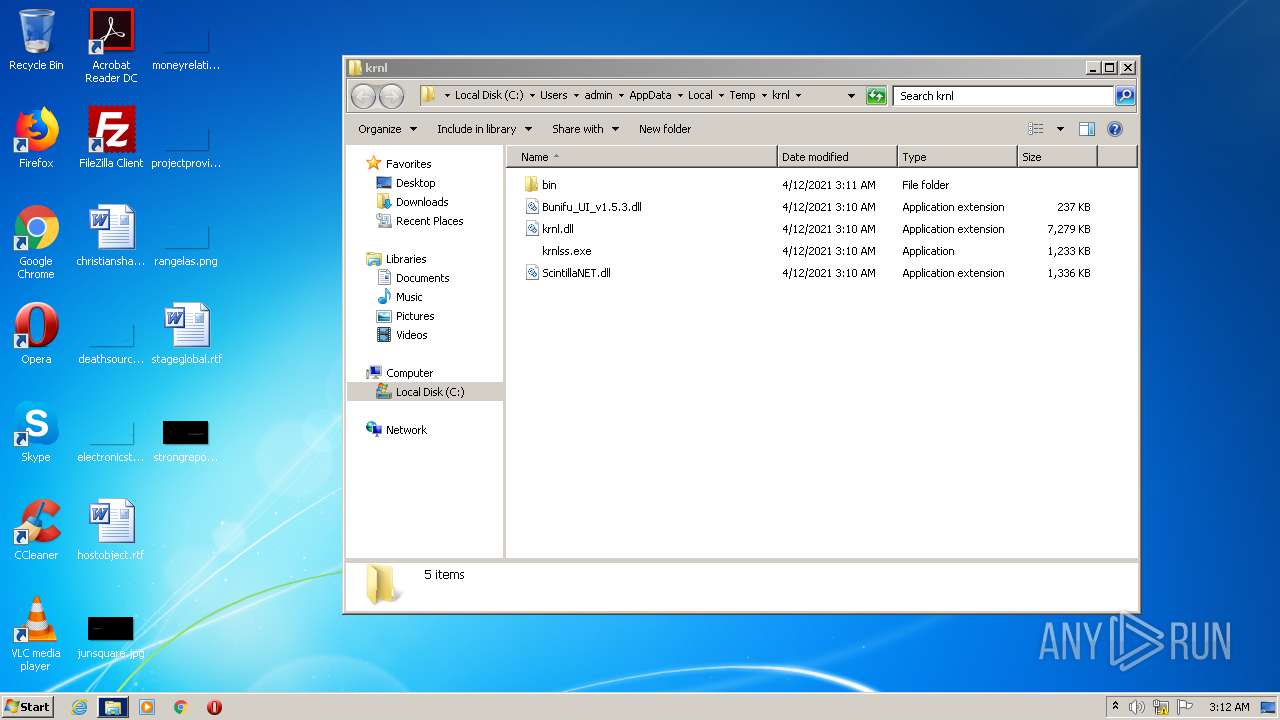
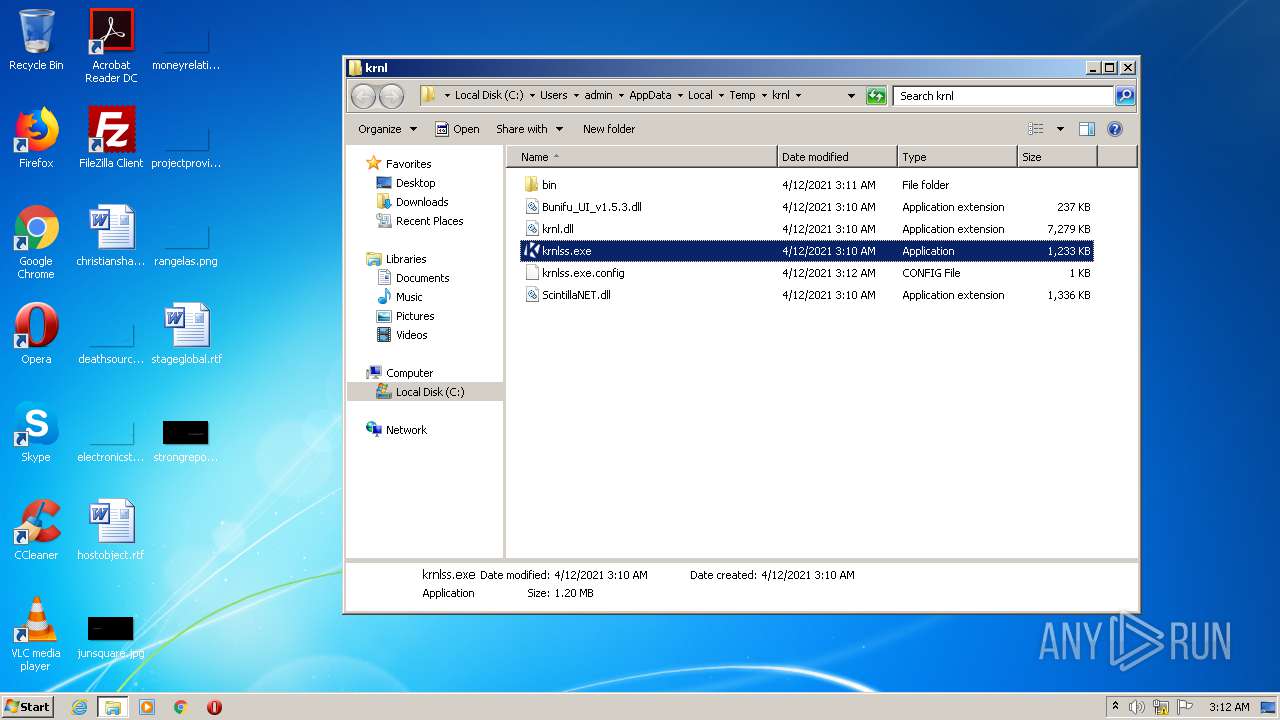
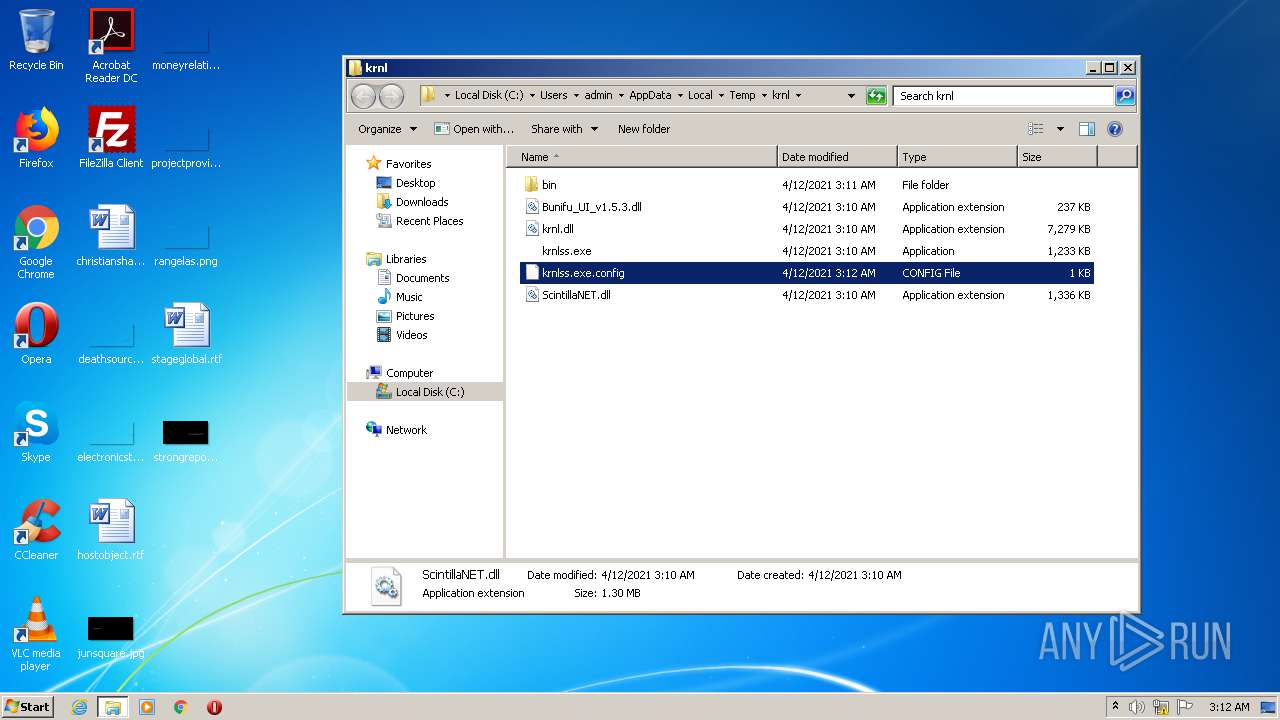
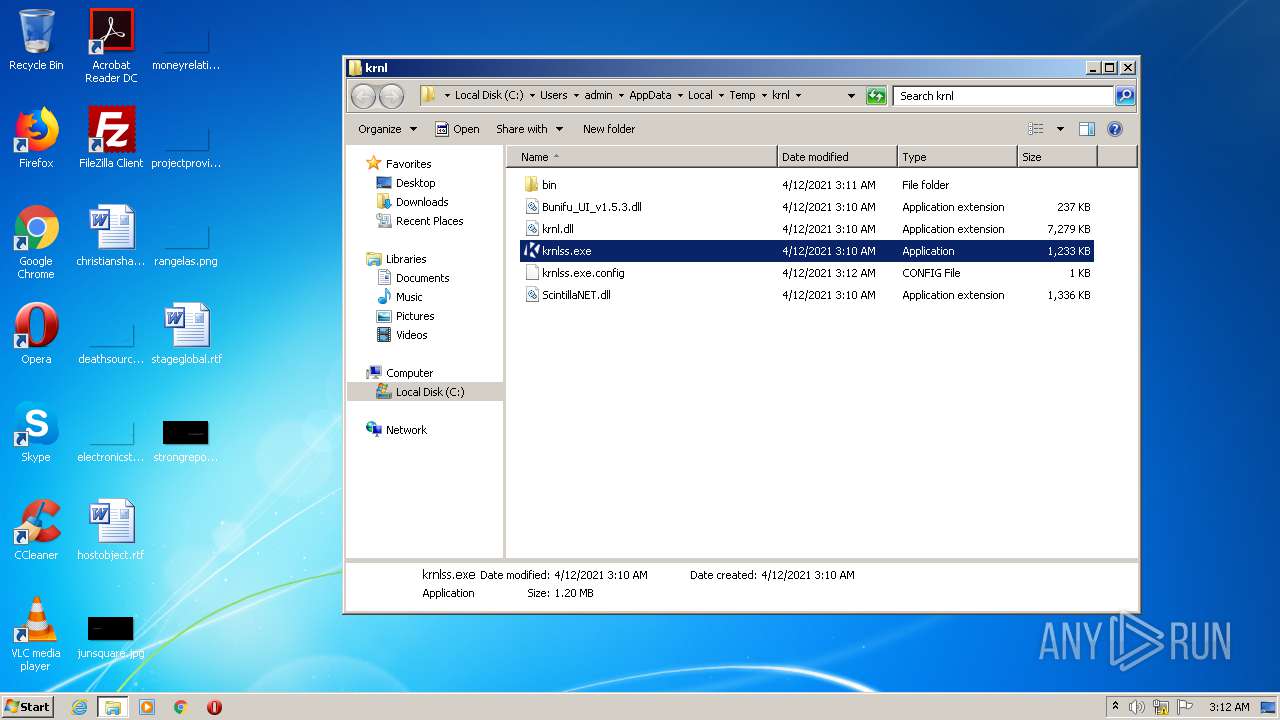
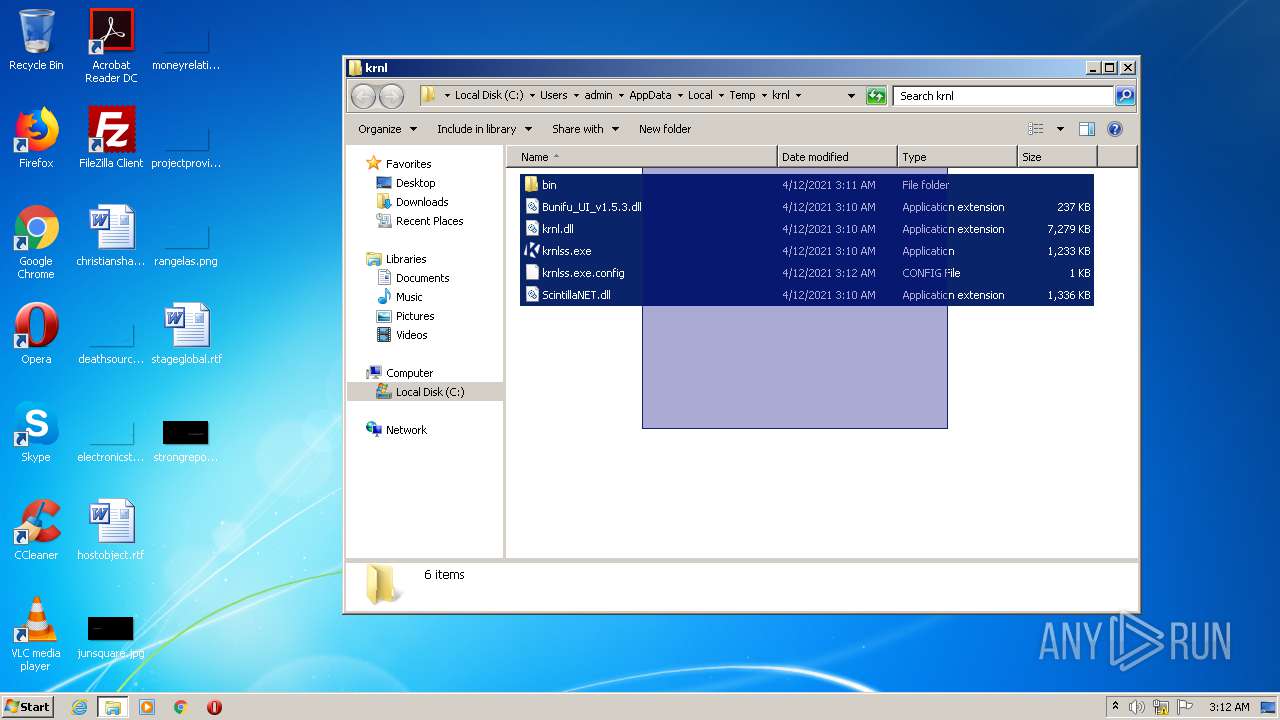
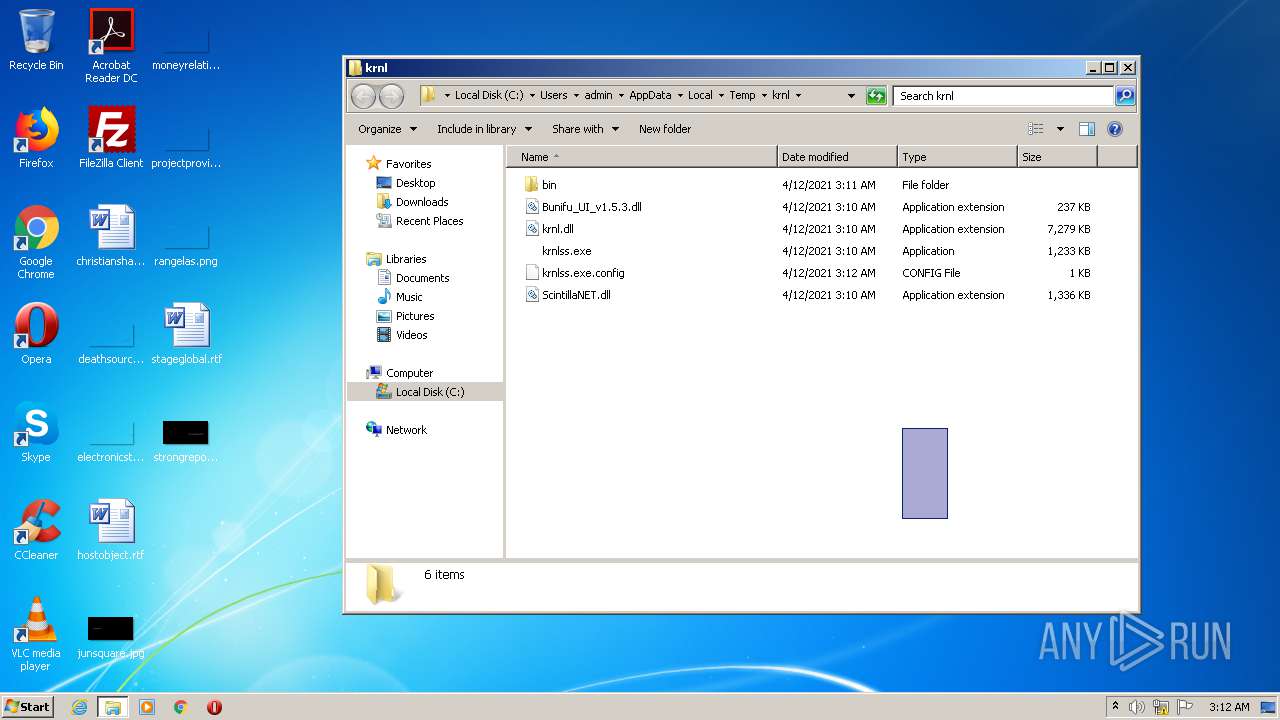
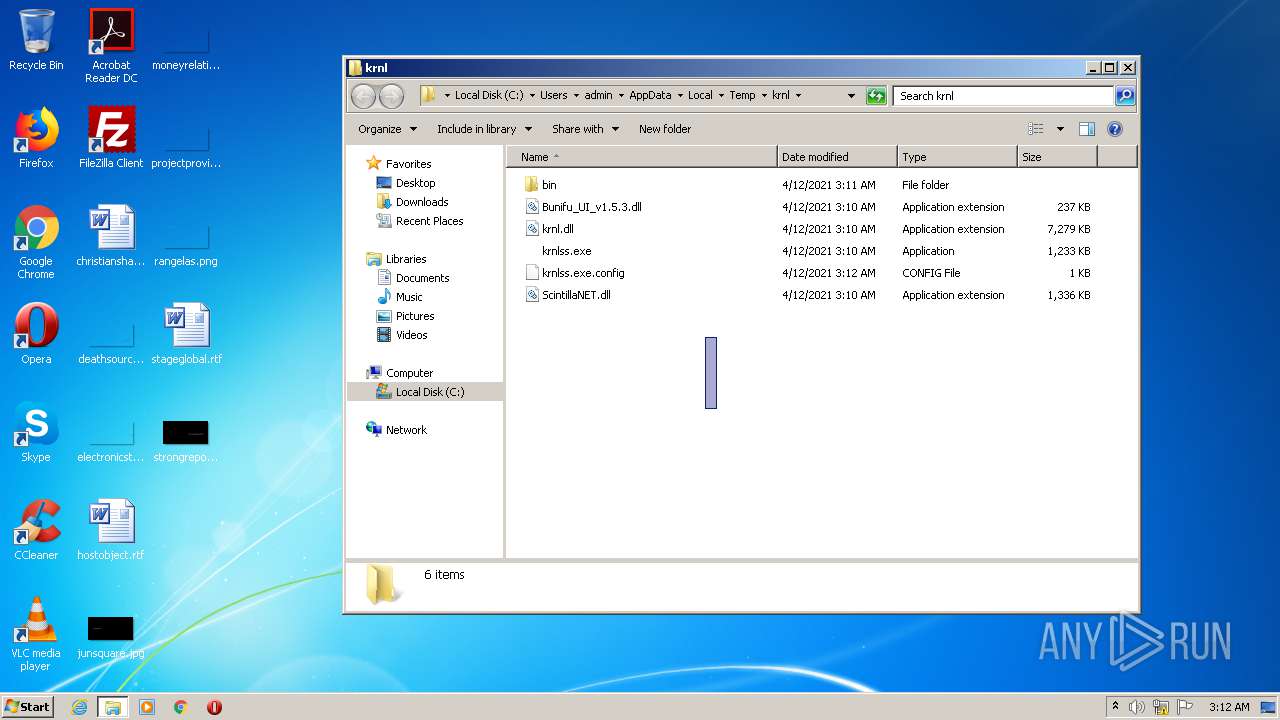
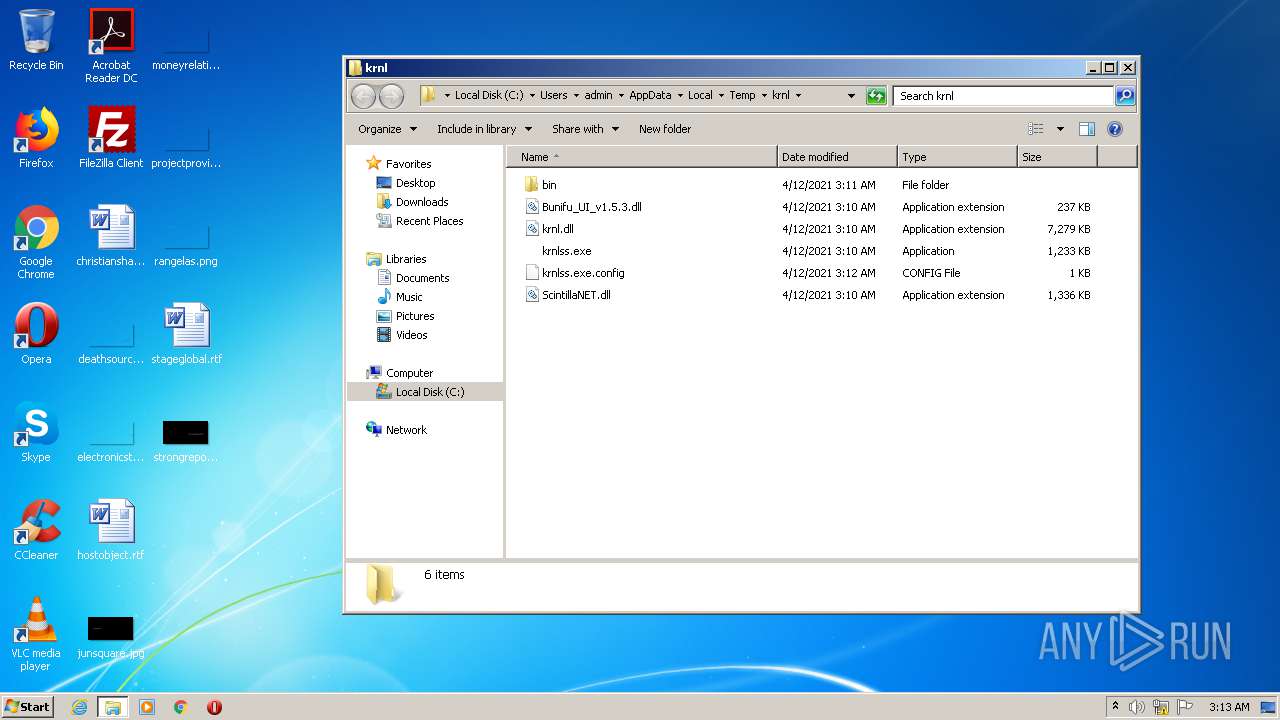
| 548 | "C:\Users\admin\AppData\Local\Temp\krnl_console_bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\krnl_console_bootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: krnl_console_bootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1376 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2228 | "C:\Users\admin\AppData\Local\Temp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\krnl\bin\src.7z" -o"C:\Users\admin\AppData\Local\Temp\krnl\bin" -aoa -bsp1 | C:\Users\admin\AppData\Local\Temp\7za.exe | krnl_console_bootstrapper.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 15.14 Modules
| |||||||||||||||
| 2484 | "C:\Users\admin\AppData\Local\Temp\krnl\krnlss.exe" | C:\Users\admin\AppData\Local\Temp\krnl\krnlss.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: krnlss Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3136 | "C:\Users\admin\AppData\Local\Temp\krnl\krnlss.exe" | C:\Users\admin\AppData\Local\Temp\krnl\krnlss.exe | — | krnlss.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: krnlss Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3324 | "C:\Users\admin\AppData\Local\Temp\krnl\krnlss.exe" | C:\Users\admin\AppData\Local\Temp\krnl\krnlss.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: krnlss Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3652 | "C:\Windows\explorer.exe" "C:\Users\admin\AppData\Local\Temp\krnl" | C:\Windows\explorer.exe | — | krnl_console_bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3764 | "C:\Users\admin\AppData\Local\Temp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\krnl\bin\Monaco.zip" -o"C:\Users\admin\AppData\Local\Temp\krnl\bin" -aoa -bsp1 | C:\Users\admin\AppData\Local\Temp\7za.exe | — | krnl_console_bootstrapper.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 15.14 Modules
| |||||||||||||||
| 3792 | "C:\Users\admin\AppData\Local\Temp\krnl\krnlss.exe" | C:\Users\admin\AppData\Local\Temp\krnl\krnlss.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: krnlss Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 875
Read events
1 633
Write events
242
Delete events
0
Modification events
| (PID) Process: | (548) krnl_console_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_console_bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (548) krnl_console_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_console_bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (548) krnl_console_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_console_bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (548) krnl_console_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_console_bootstrapper_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (548) krnl_console_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_console_bootstrapper_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (548) krnl_console_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_console_bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (548) krnl_console_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_console_bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (548) krnl_console_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_console_bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (548) krnl_console_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_console_bootstrapper_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (548) krnl_console_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_console_bootstrapper_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
135
Suspicious files
3
Text files
42
Unknown types
66
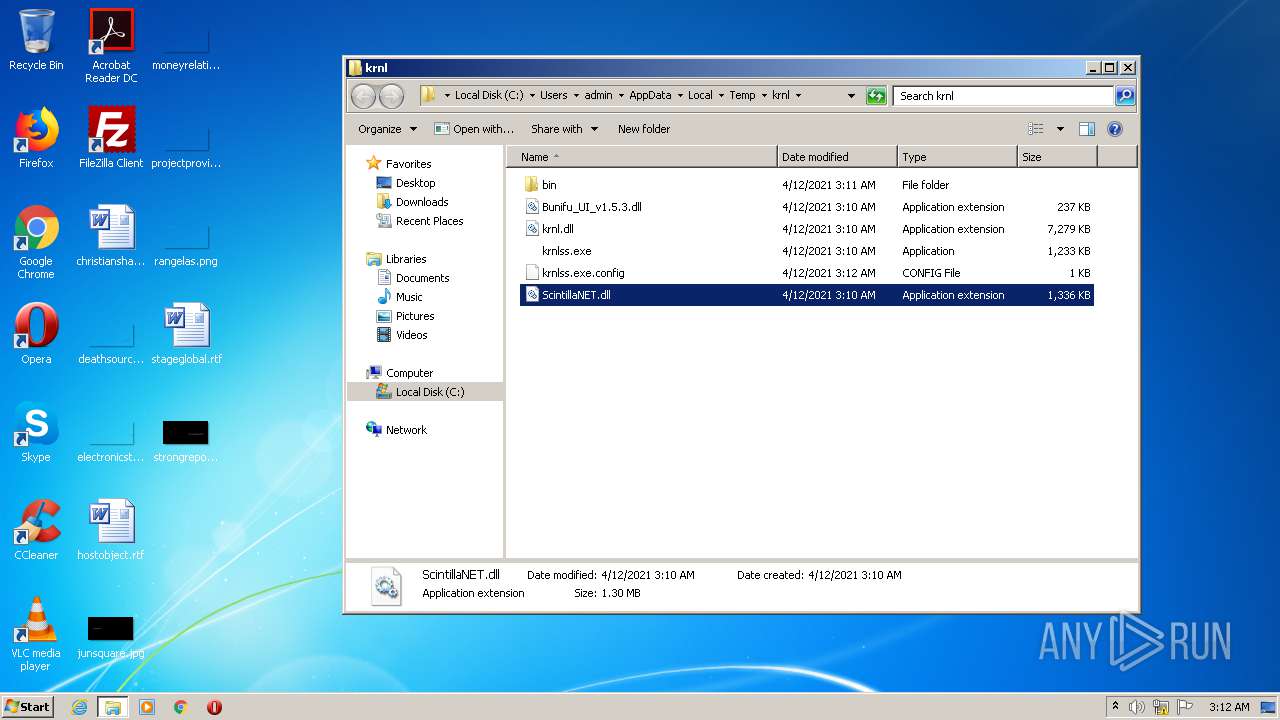
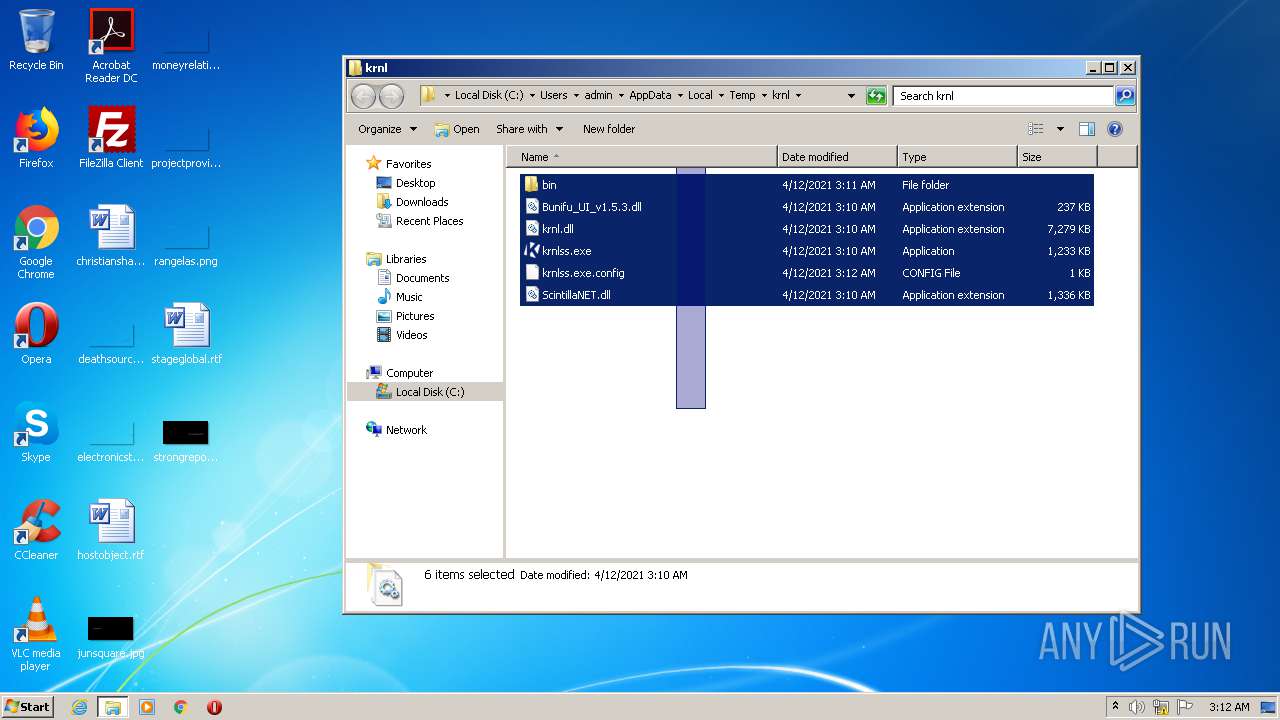
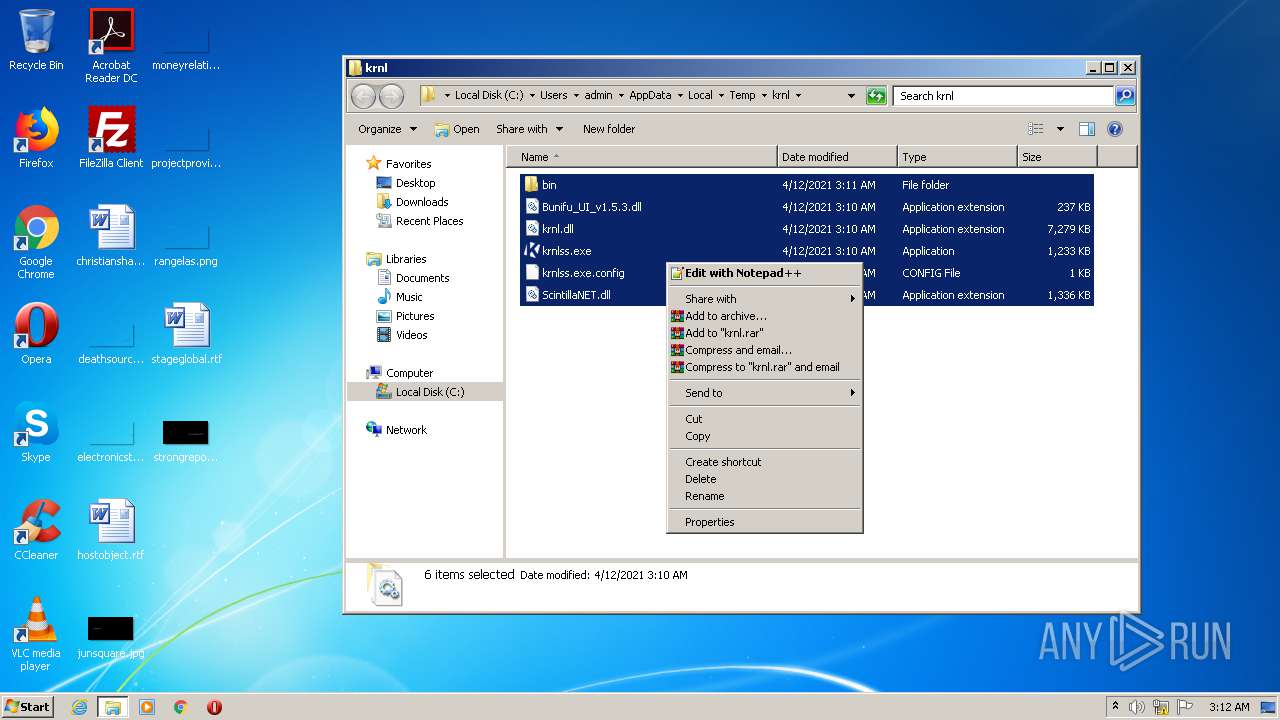
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 548 | krnl_console_bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\7z.NET.dll.txt | — | |
MD5:— | SHA256:— | |||
| 548 | krnl_console_bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\7za.exe.txt | — | |
MD5:— | SHA256:— | |||
| 548 | krnl_console_bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Bunifu_UI_v1.5.3.dll.txt | — | |
MD5:— | SHA256:— | |||
| 548 | krnl_console_bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Monaco.zip.txt | — | |
MD5:— | SHA256:— | |||
| 548 | krnl_console_bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\7z.NET.dll | executable | |
MD5:982475050787051658ABD42E890A2469 | SHA256:4E193CCDA4EF7EC7FC1BC12D7ABBA225A9AF5B4612AA0B67A02324B9DA8B268C | |||
| 3764 | 7za.exe | C:\Users\admin\AppData\Local\Temp\krnl\bin\Monaco\vs\base\worker\workerMain.js | text | |
MD5:27EAD90C7702154755785E0E53398755 | SHA256:BDF9433692A08851E13DD58504EEF19F51BD2EC7241923A68EDF5772E0E53AF5 | |||
| 3764 | 7za.exe | C:\Users\admin\AppData\Local\Temp\krnl\bin\Monaco\Monaco.html | html | |
MD5:F872D6BB3D3364428DB47E8DB7050D43 | SHA256:0F4292152A1F55A75E7DE8A5DEF919A7DDACFB9A774FD02C4B82C8FA99715E96 | |||
| 548 | krnl_console_bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\krnl\Bunifu_UI_v1.5.3.dll | executable | |
MD5:2ECB51AB00C5F340380ECF849291DBCF | SHA256:F1B3E0F2750A9103E46A6A4A34F1CF9D17779725F98042CC2475EC66484801CF | |||
| 548 | krnl_console_bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\krnlss.exe.txt | — | |
MD5:— | SHA256:— | |||
| 548 | krnl_console_bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\7za.exe | executable | |
MD5:EC79CABD55A14379E4D676BB17D9E3DF | SHA256:44A55F5D9C31D0990DE47B9893E0C927478930CEF06FBE2D1F520A6D6CBA587D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
548 | krnl_console_bootstrapper.exe | 172.67.187.183:443 | cdn.krnl.ca | — | US | unknown |
548 | krnl_console_bootstrapper.exe | 104.21.42.186:443 | k-storage.com | Cloudflare Inc | US | unknown |
548 | krnl_console_bootstrapper.exe | 172.67.208.22:443 | k-storage.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.krnl.ca |
| malicious |
k-storage.com |
| malicious |
dns.msftncsi.com |
| shared |