| File name: | Xvideos Live Sex.exe |
| Full analysis: | https://app.any.run/tasks/cd1a023d-2c2e-4689-8dd8-e17efa3b52c7 |
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2020, 12:16:12 |
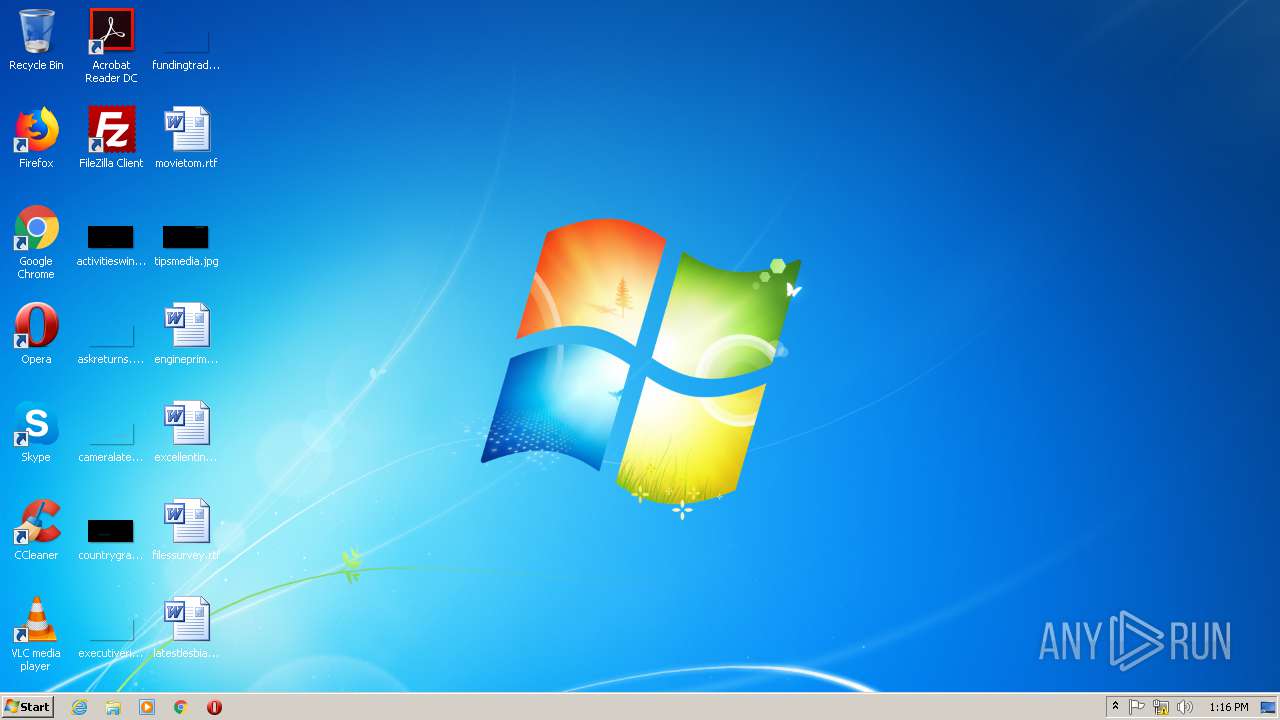
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9E4BE44CD94BF353C0A358A1D22D40CE |
| SHA1: | B8B9E7AA4B7E4AD8DB7400620A2F2E198655213D |
| SHA256: | 8E2F624F7BF79F35951FA8A434537CAA7D82DFBDF0BCD97461F879C43EECE7FA |
| SSDEEP: | 49152:jdBg7bH9b6q9ezAErA7TL0hVnWBgXDVIP:jAb0SvErA7TQhVWBdP |
MALICIOUS
Changes the autorun value in the registry
- Xvideos Live Sex.exe (PID: 3964)
Actions looks like stealing of personal data
- DllHost.exe (PID: 3272)
SUSPICIOUS
Low-level read access rights to disk partition
- Xvideos Live Sex.exe (PID: 3964)
- Wejrz6gl.exe (PID: 2156)
Starts itself from another location
- Xvideos Live Sex.exe (PID: 3964)
Creates files in the program directory
- Xvideos Live Sex.exe (PID: 3964)
Executable content was dropped or overwritten
- Xvideos Live Sex.exe (PID: 3964)
Executed via COM
- DllHost.exe (PID: 3272)
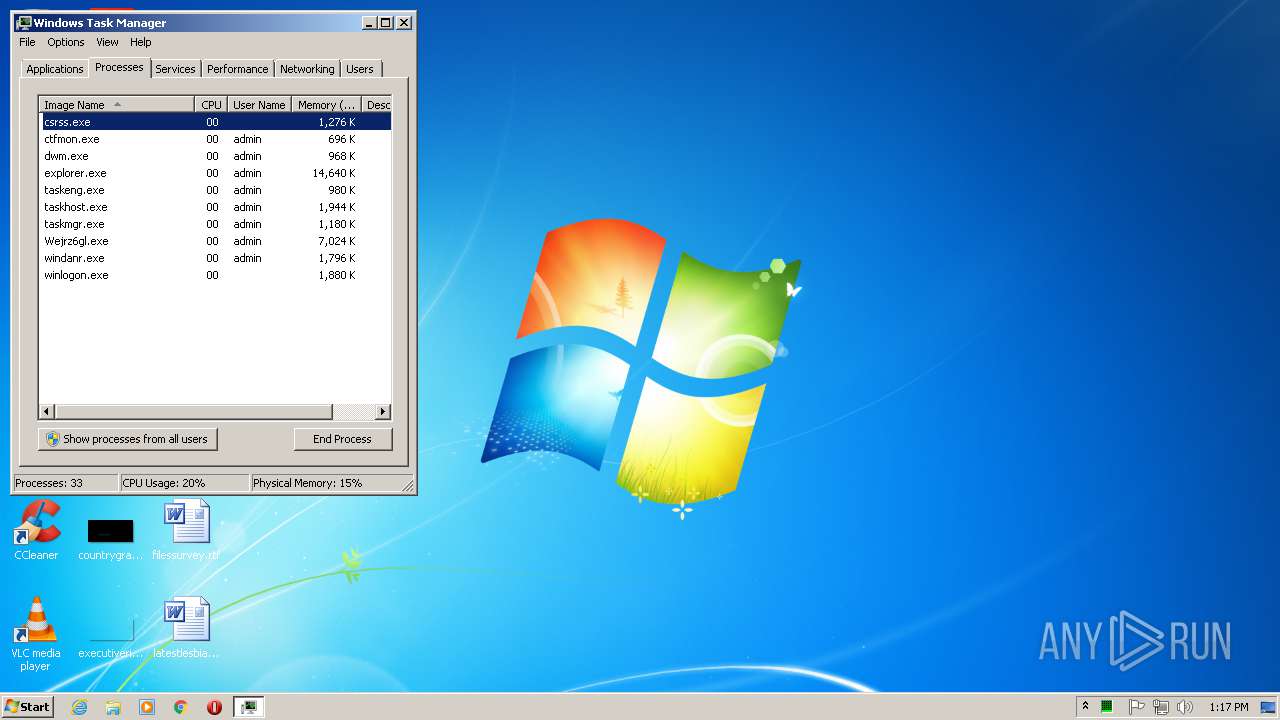
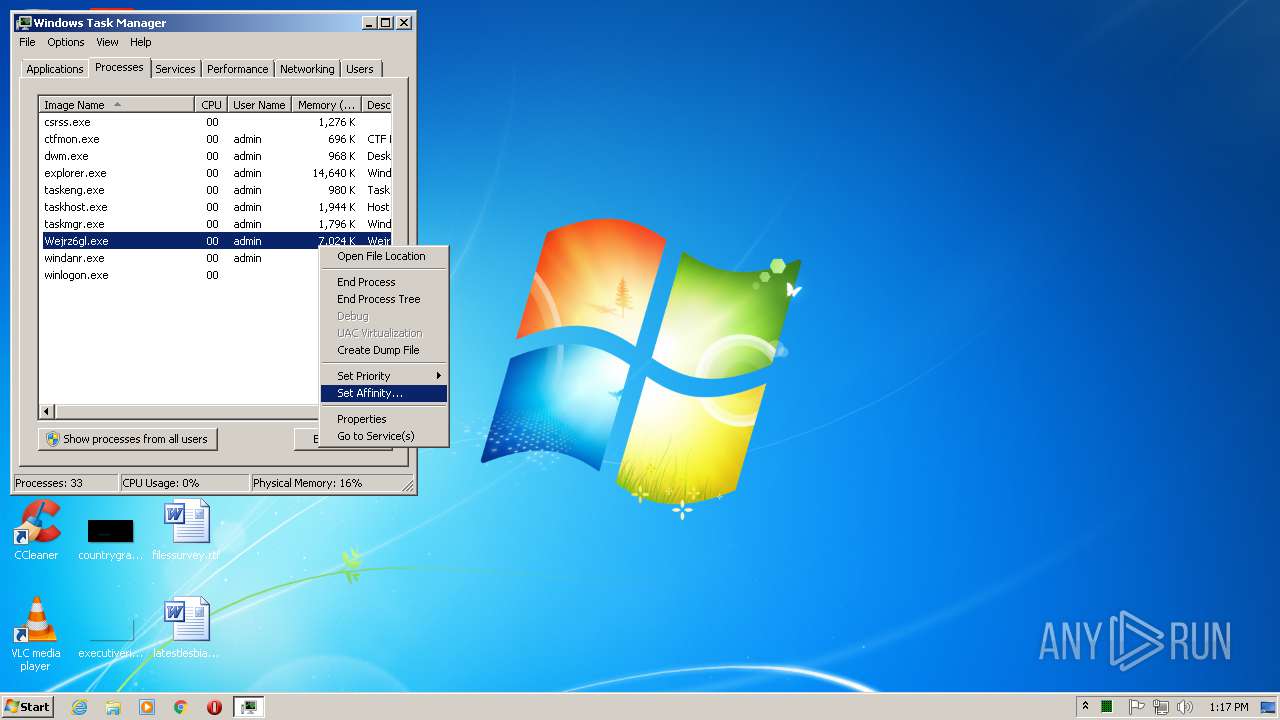
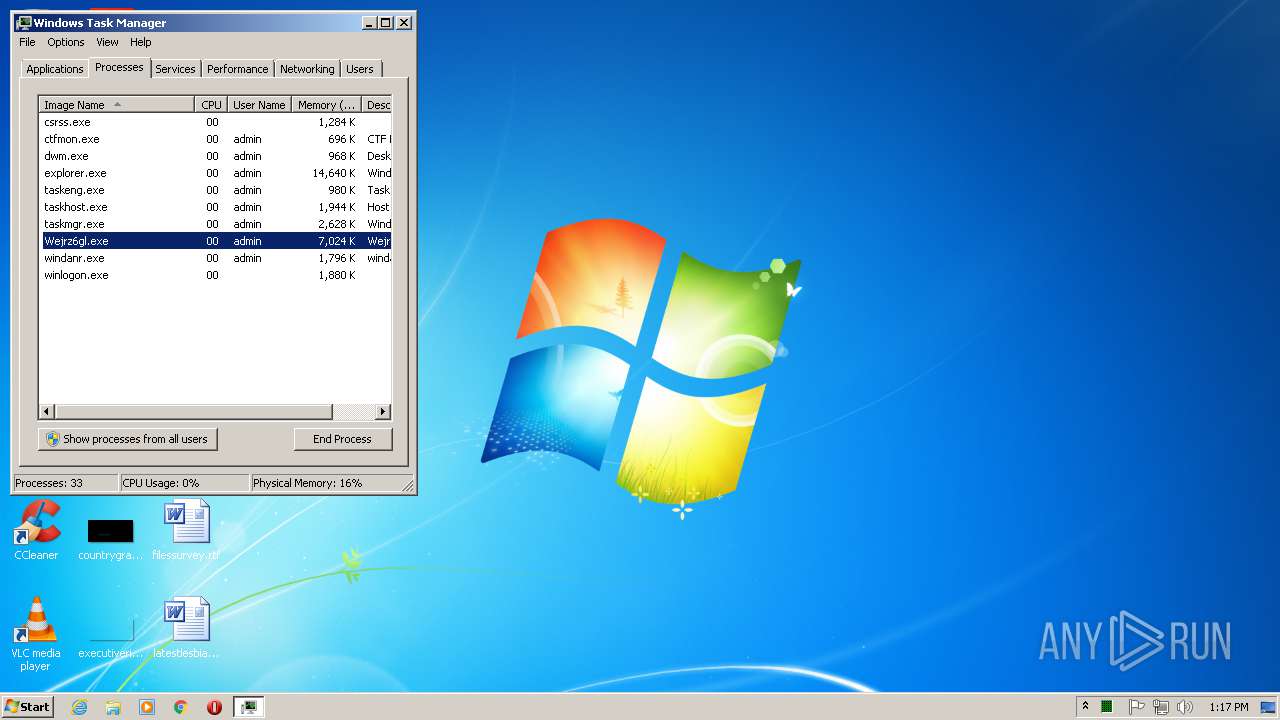
INFO
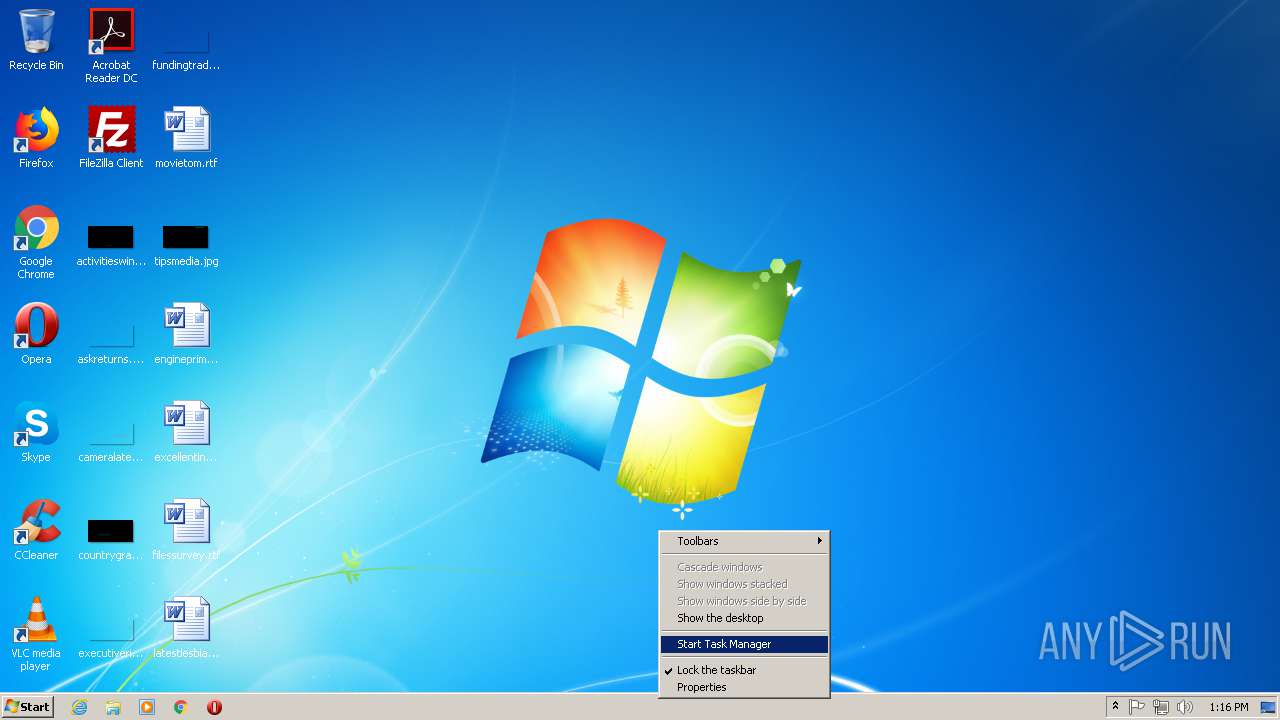
Manual execution by user
- taskmgr.exe (PID: 2708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 645632 |
| InitializedDataSize: | 1641472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x40a000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| TLS Callbacks: | 81 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x000B5000 | 0x00050A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.98442 | |
.rsrc | 0x000B6000 | 0x00180000 | 0x00059800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93648 |
.idata | 0x00236000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.27936 |
0x00237000 | 0x000FB000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.260771 | |
fxeqrxnm | 0x00332000 | 0x000D8000 | 0x000D7800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.85632 |
bbiriihq | 0x0040A000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.71384 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.88668 | 371 | UNKNOWN | Chinese - PRC | RT_MANIFEST |
2 | 6.80496 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 6.72819 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 6.84209 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 6.83345 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 7.07758 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 7.20301 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
148 | 7.92965 | 121446 | UNKNOWN | Chinese - PRC | RT_BITMAP |
179 | 7.90958 | 34062 | UNKNOWN | Chinese - PRC | RT_BITMAP |
180 | 7.90069 | 34062 | UNKNOWN | Chinese - PRC | RT_BITMAP |
Imports
comctl32.dll |
kernel32.dll |
Total processes
41
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
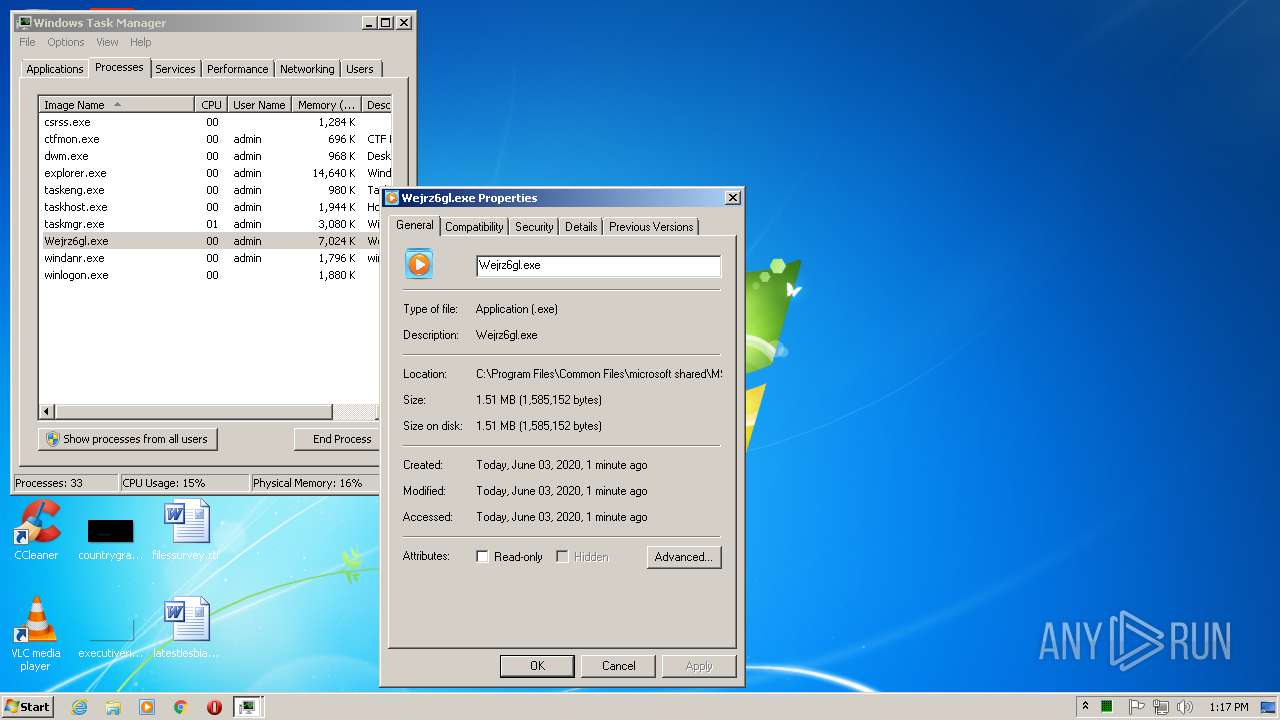
| 2156 | "C:\Program Files\Common Files\Microsoft Shared\MSINFO\Wejrz6gl.exe" | C:\Program Files\Common Files\Microsoft Shared\MSINFO\Wejrz6gl.exe | Xvideos Live Sex.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2708 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Temp\Xvideos Live Sex.exe" | C:\Users\admin\AppData\Local\Temp\Xvideos Live Sex.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3272 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | "C:\Users\admin\AppData\Local\Temp\Xvideos Live Sex.exe" | C:\Users\admin\AppData\Local\Temp\Xvideos Live Sex.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
114
Read events
109
Write events
5
Delete events
0
Modification events
| (PID) Process: | (3964) Xvideos Live Sex.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Wejrz6gl |
Value: "C:\Program Files\Common Files\Microsoft Shared\MSINFO\Wejrz6gl.exe" | |||
| (PID) Process: | (3272) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (3272) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (2708) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (2708) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000000A0000000A000000A2010000F00100000100000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | Xvideos Live Sex.exe | C:\Program Files\Common Files\Microsoft Shared\MSINFO\Wejrz6gl.exe | executable | |
MD5:9E4BE44CD94BF353C0A358A1D22D40CE | SHA256:8E2F624F7BF79F35951FA8A434537CAA7D82DFBDF0BCD97461F879C43EECE7FA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2156 | Wejrz6gl.exe | 142.54.162.66:8010 | eth.ceo | DataShack, LC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
eth.ceo |
| malicious |
Threats
Process | Message |
|---|---|
Xvideos Live Sex.exe |
%s------------------------------------------------
--- WinLicense Professional ---
--- (c)2009 Oreans Technologies ---
------------------------------------------------
|
Wejrz6gl.exe |
%s------------------------------------------------
--- WinLicense Professional ---
--- (c)2009 Oreans Technologies ---
------------------------------------------------
|