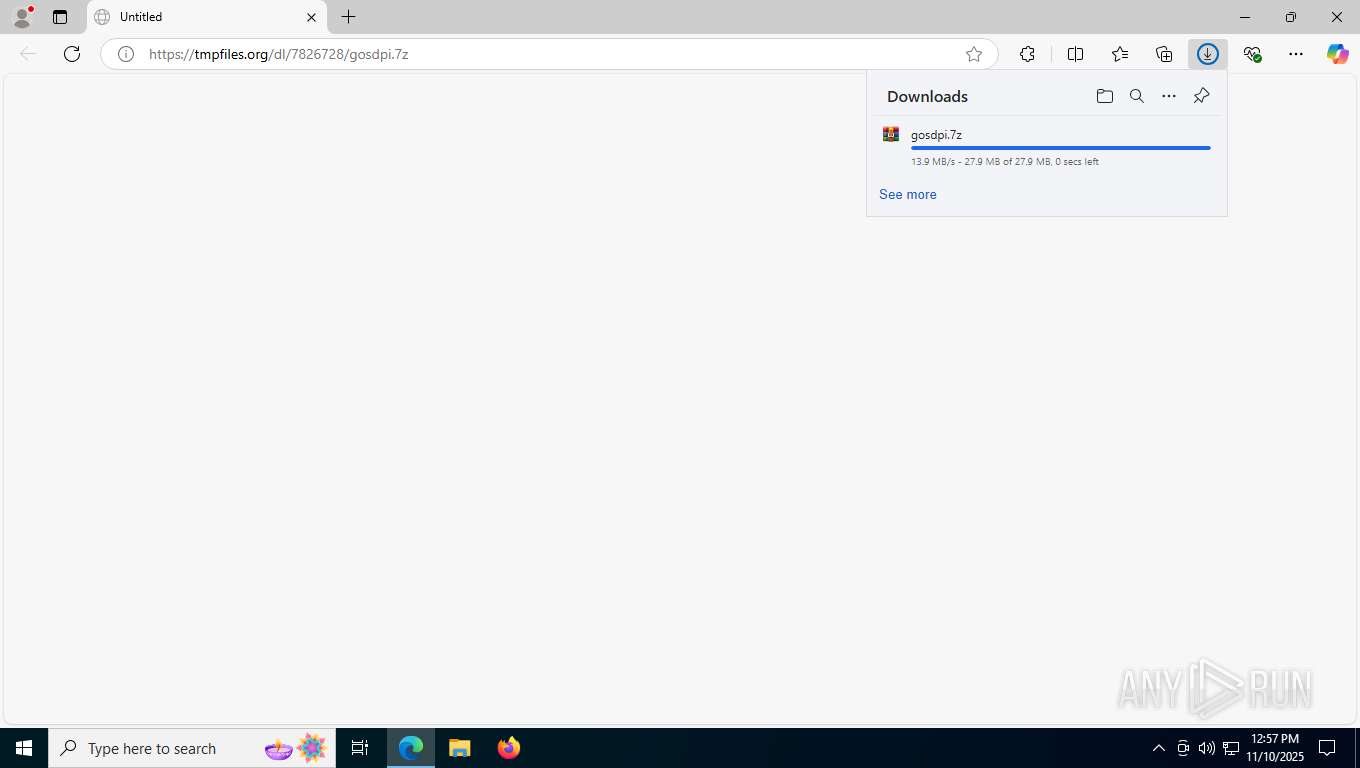
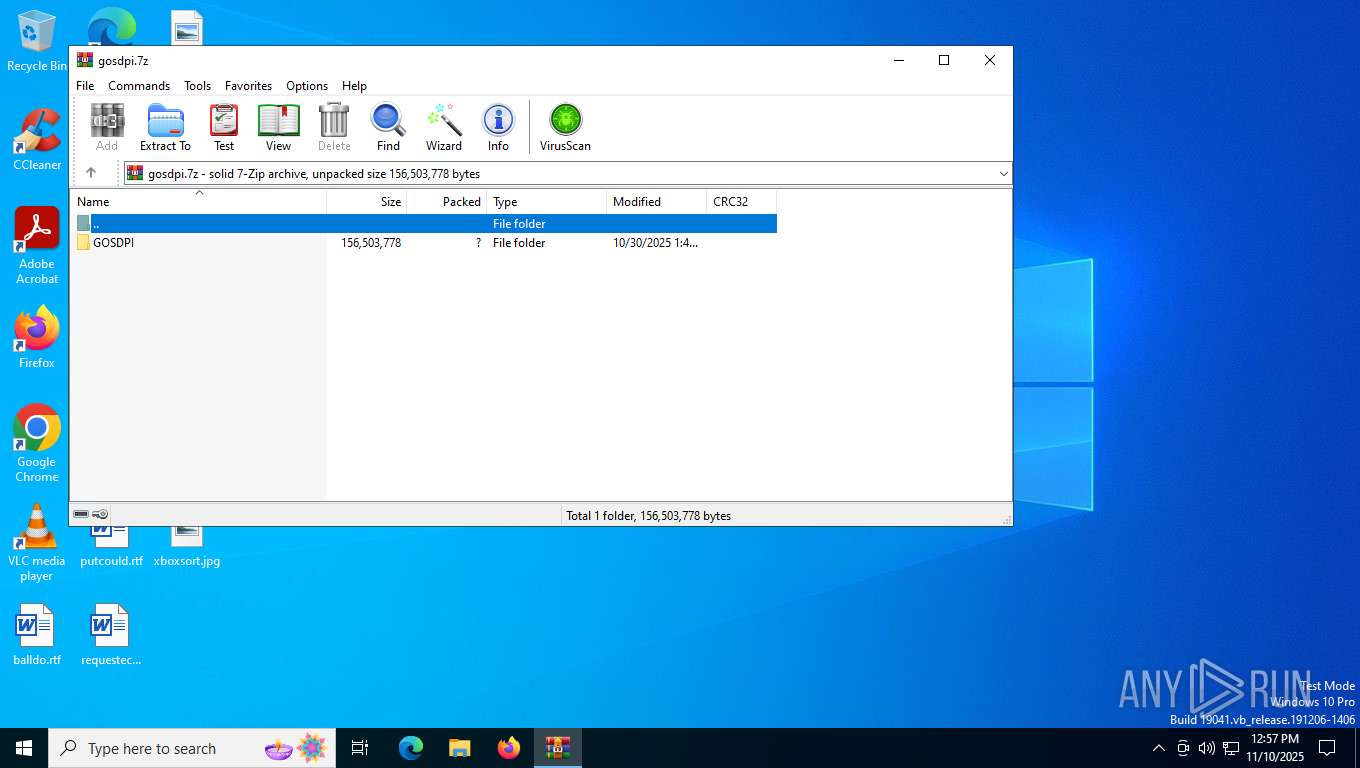
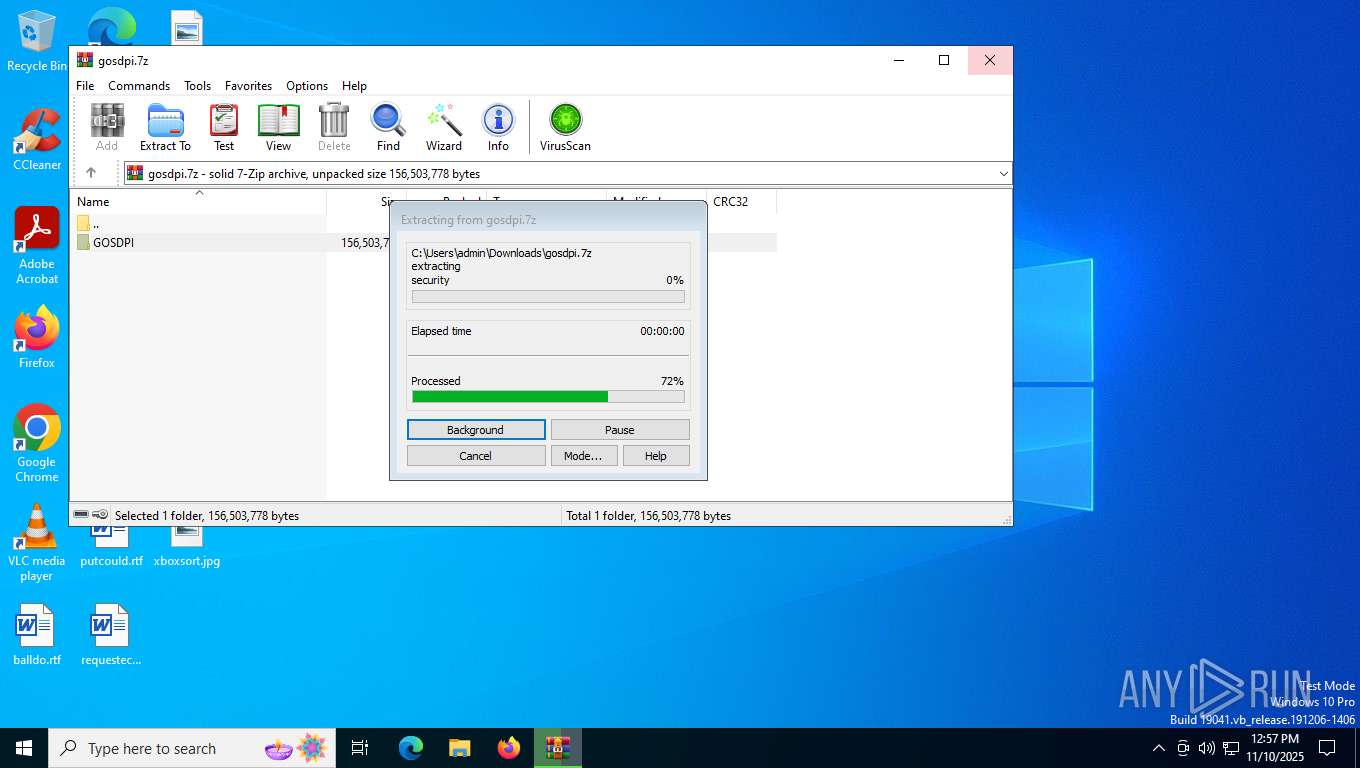
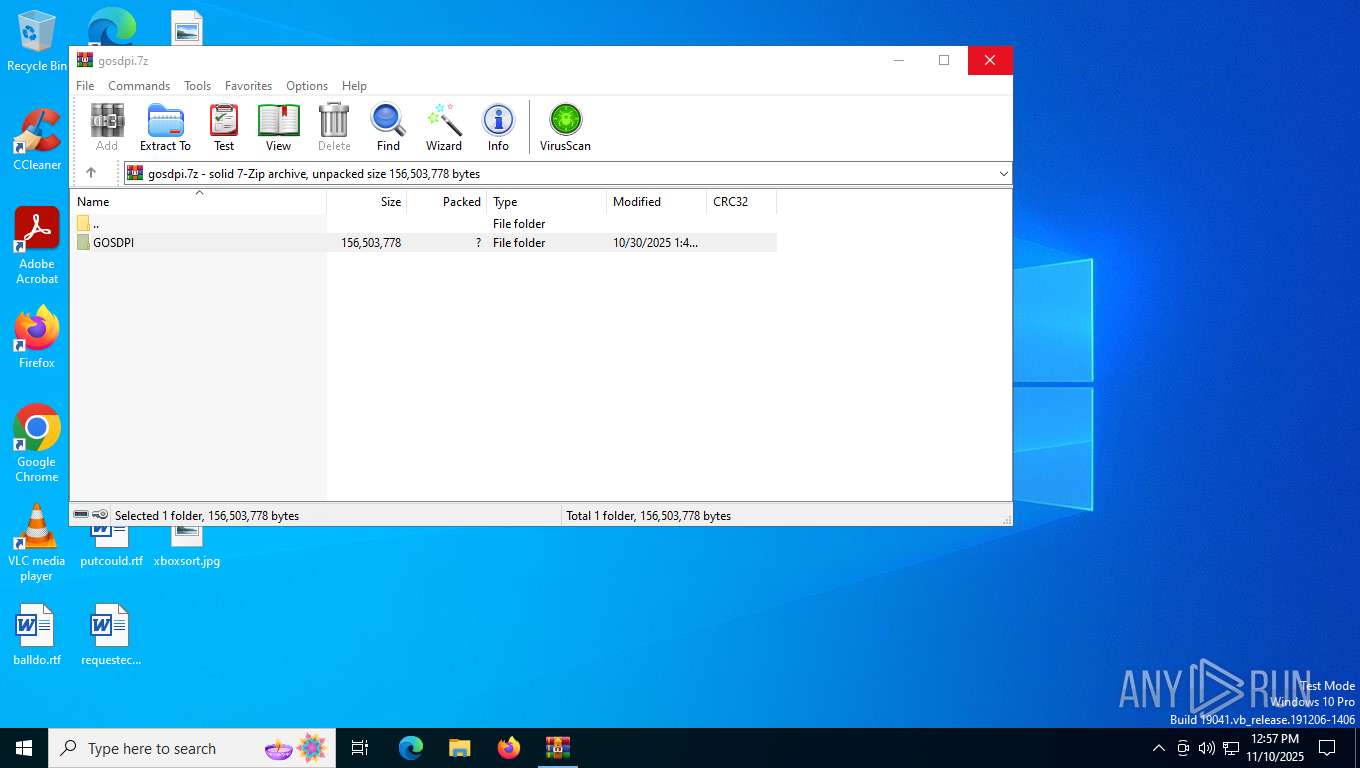
| URL: | https://tmpfiles.org/dl/7826728/gosdpi.7z |
| Full analysis: | https://app.any.run/tasks/a25ea1e5-2bde-4022-8fa9-ae5e66dee276 |
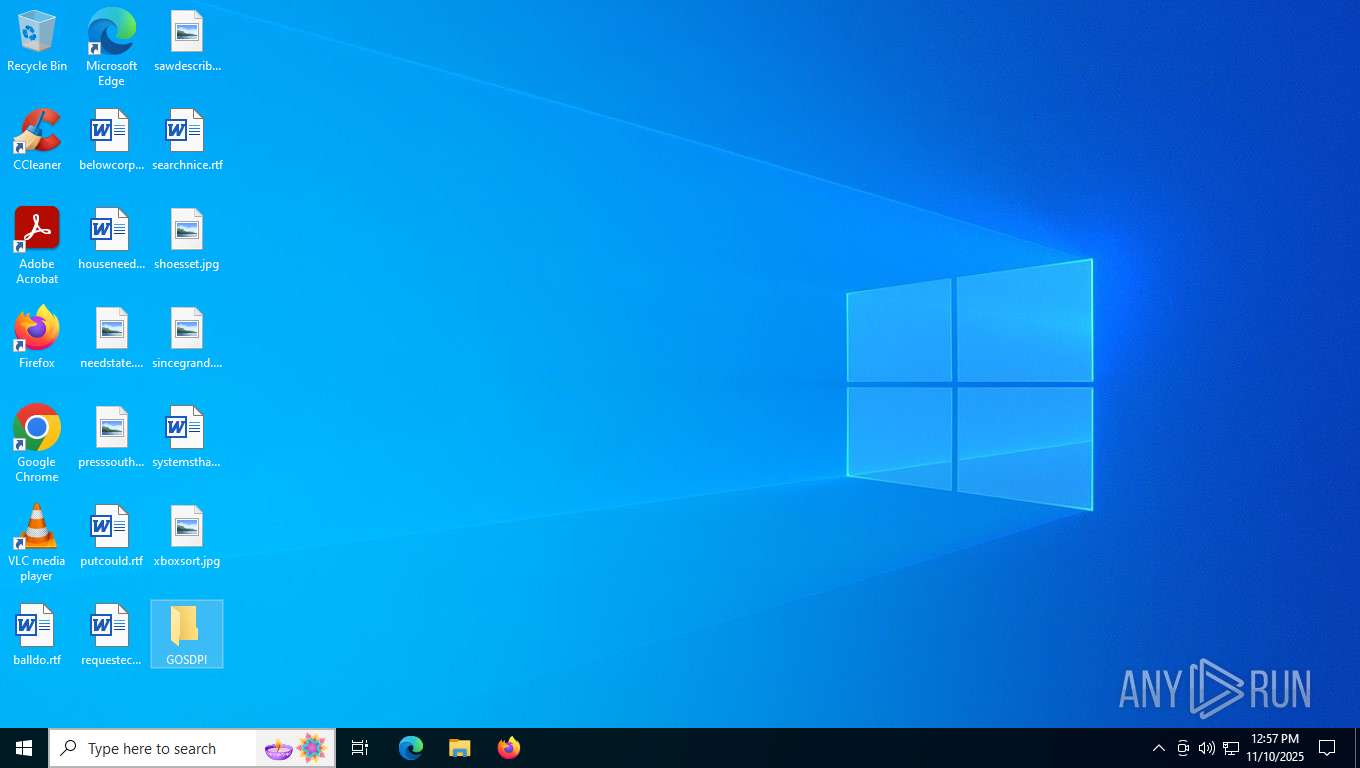
| Verdict: | Malicious activity |
| Analysis date: | November 10, 2025, 12:57:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A8912C0848086E62F8826C3CCB0320B7 |
| SHA1: | 66F9172096B49C34E5E6C3EB8F0B9A08689BB342 |
| SHA256: | 8E2E0818D1DF7B8A11760F7936AACA51429558ED5A6830F8B70309904CAED51C |
| SSDEEP: | 3:N8AB4CWjMLs:2AvWwo |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 8128)
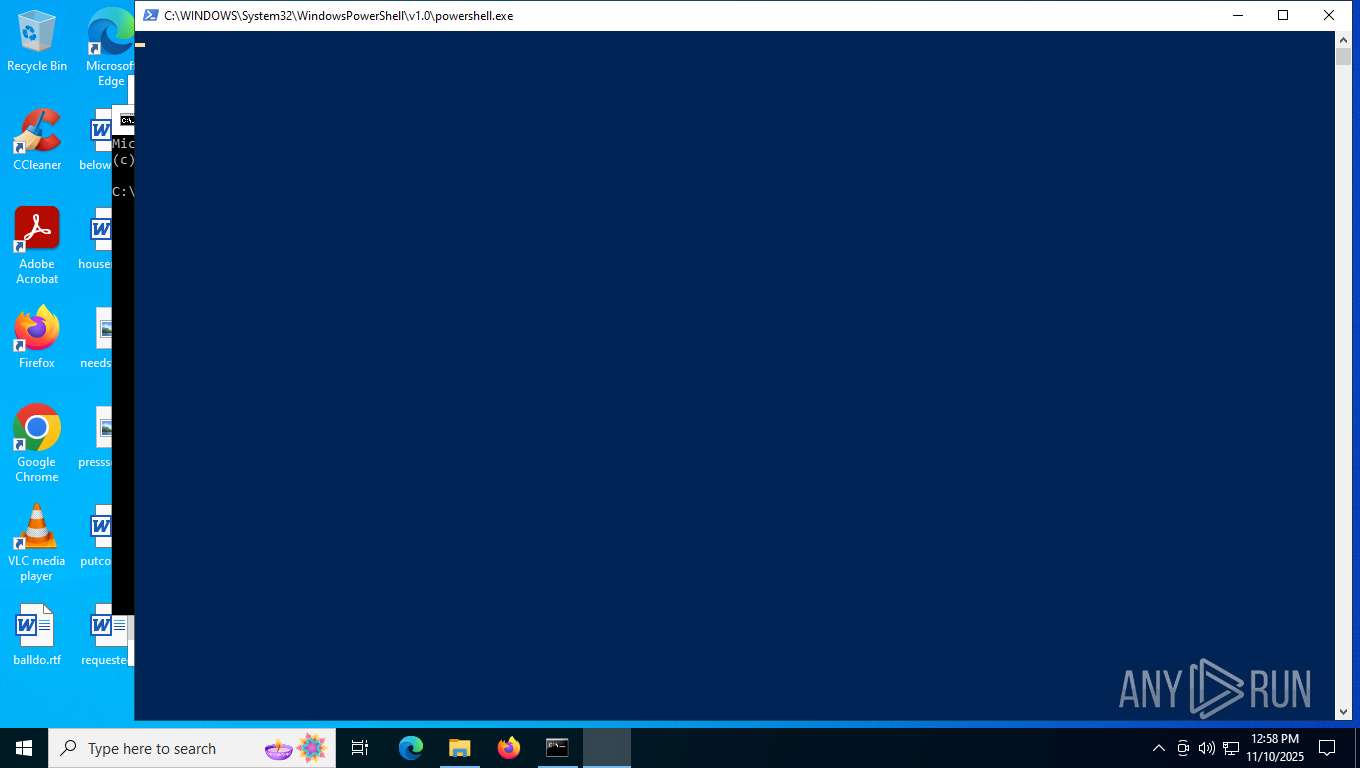
Bypass execution policy to execute commands
- powershell.exe (PID: 7984)
Changes powershell execution policy (Bypass)
- dllhost.exe (PID: 8128)
Executing a file with an untrusted certificate
- ChipsetSetup.exe (PID: 8324)
SUSPICIOUS
Possible Social Engineering Attempted
- msedge.exe (PID: 7740)
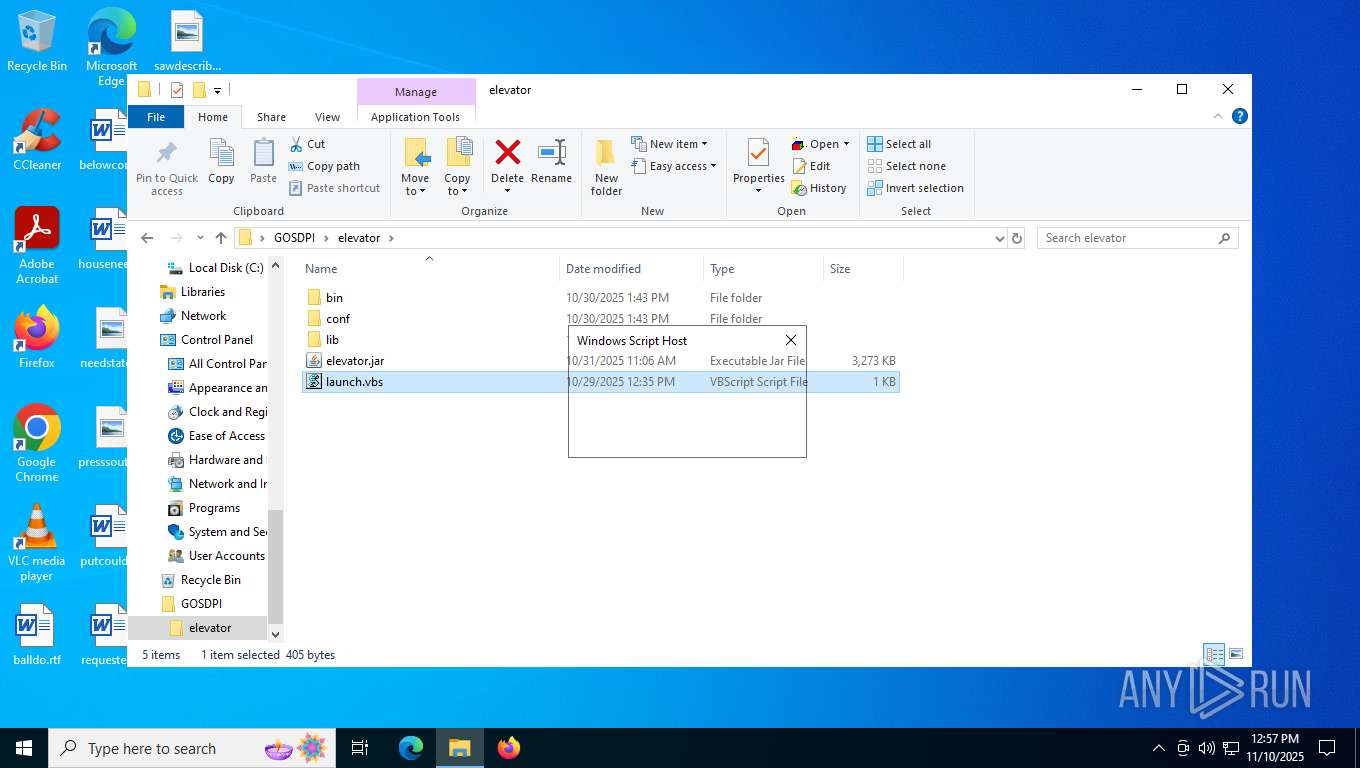
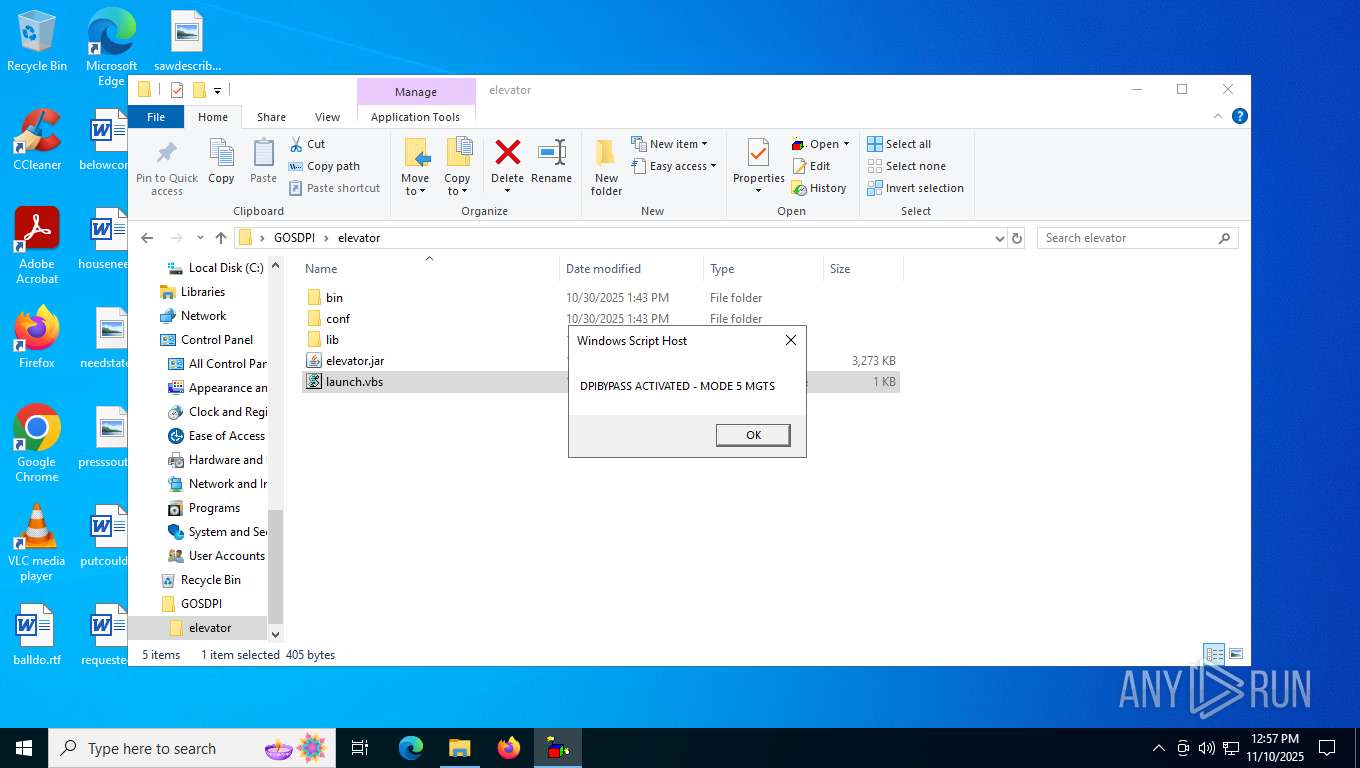
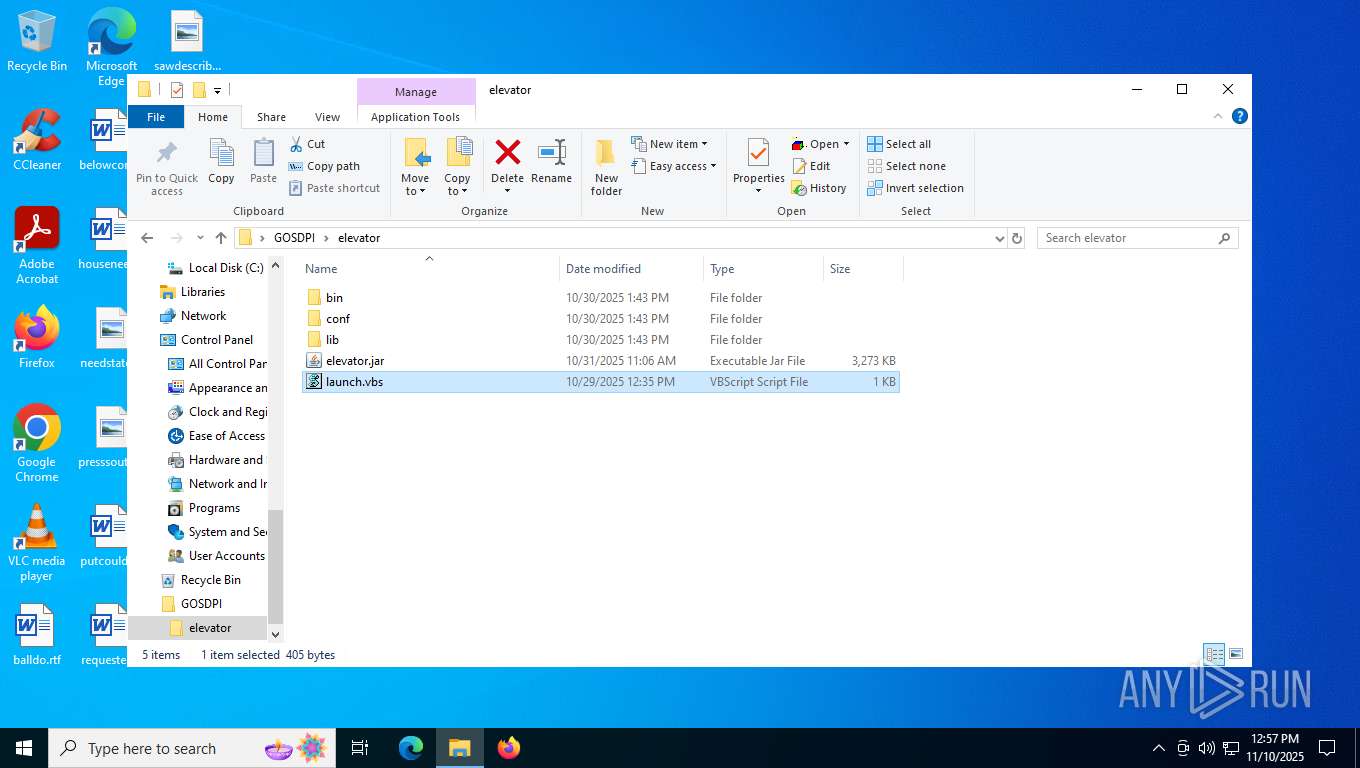
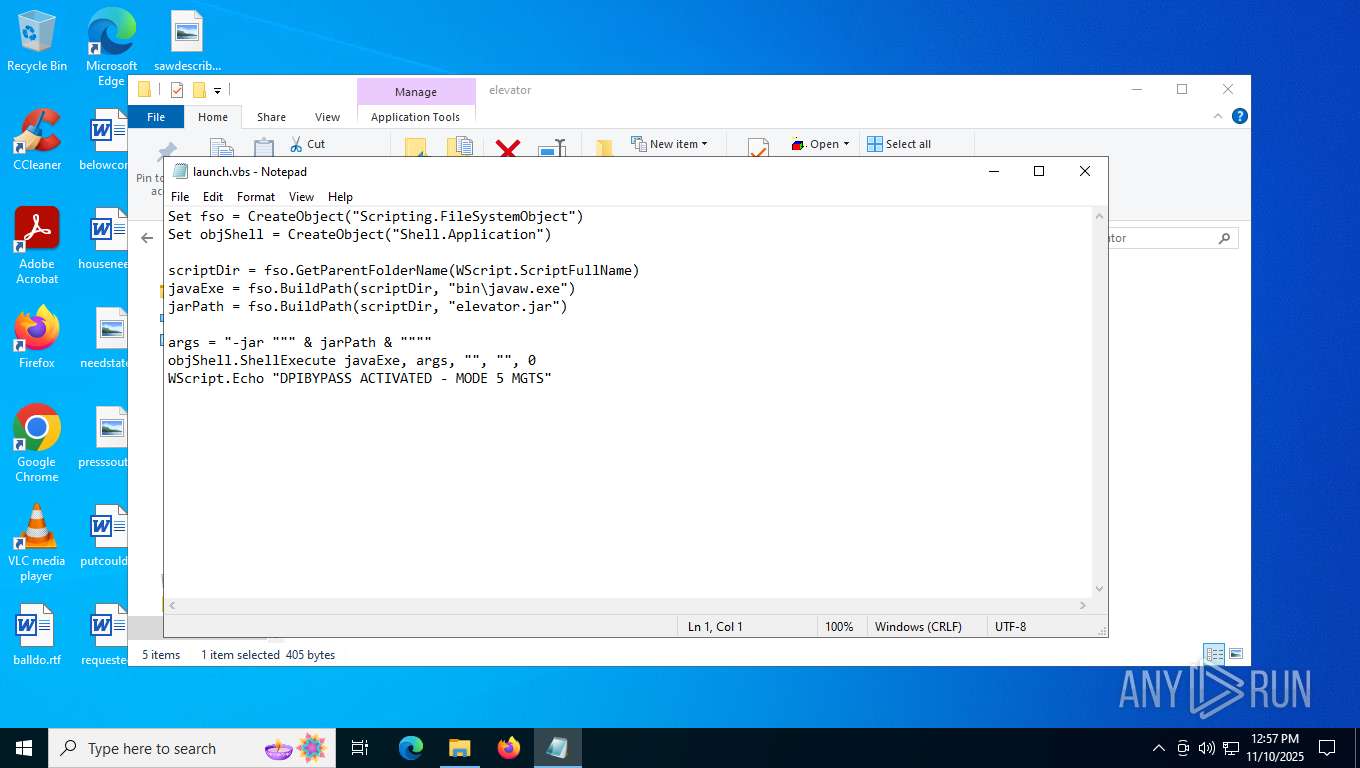
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 8616)
Process drops legitimate windows executable
- WinRAR.exe (PID: 8244)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8616)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8616)
There is functionality for VM detection VMWare (YARA)
- javaw.exe (PID: 8668)
There is functionality for VM detection VirtualBox (YARA)
- javaw.exe (PID: 8668)
Executable content was dropped or overwritten
- javaw.exe (PID: 8668)
- ChipsetSetup.exe (PID: 8324)
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- javaw.exe (PID: 8668)
The process bypasses the loading of PowerShell profile settings
- dllhost.exe (PID: 8128)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 7984)
Starts POWERSHELL.EXE for commands execution
- dllhost.exe (PID: 8128)
- ChipsetSetup.exe (PID: 8324)
Get information on the list of running processes
- dllhost.exe (PID: 8128)
The process executes Powershell scripts
- dllhost.exe (PID: 8128)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7984)
There is functionality for VM detection antiVM strings (YARA)
- javaw.exe (PID: 8668)
Uses TASKKILL.EXE to kill process
- dllhost.exe (PID: 8128)
Drops 7-zip archiver for unpacking
- ChipsetSetup.exe (PID: 8324)
Executes application which crashes
- ChipsetSetup.exe (PID: 8324)
INFO
Reads the computer name
- identity_helper.exe (PID: 3356)
- javaw.exe (PID: 8668)
- ChipsetSetup.exe (PID: 8324)
- 7df13.exe (PID: 7848)
- 7df13.exe (PID: 5276)
Application launched itself
- msedge.exe (PID: 7400)
Reads Environment values
- identity_helper.exe (PID: 3356)
- javaw.exe (PID: 8668)
- ChipsetSetup.exe (PID: 8324)
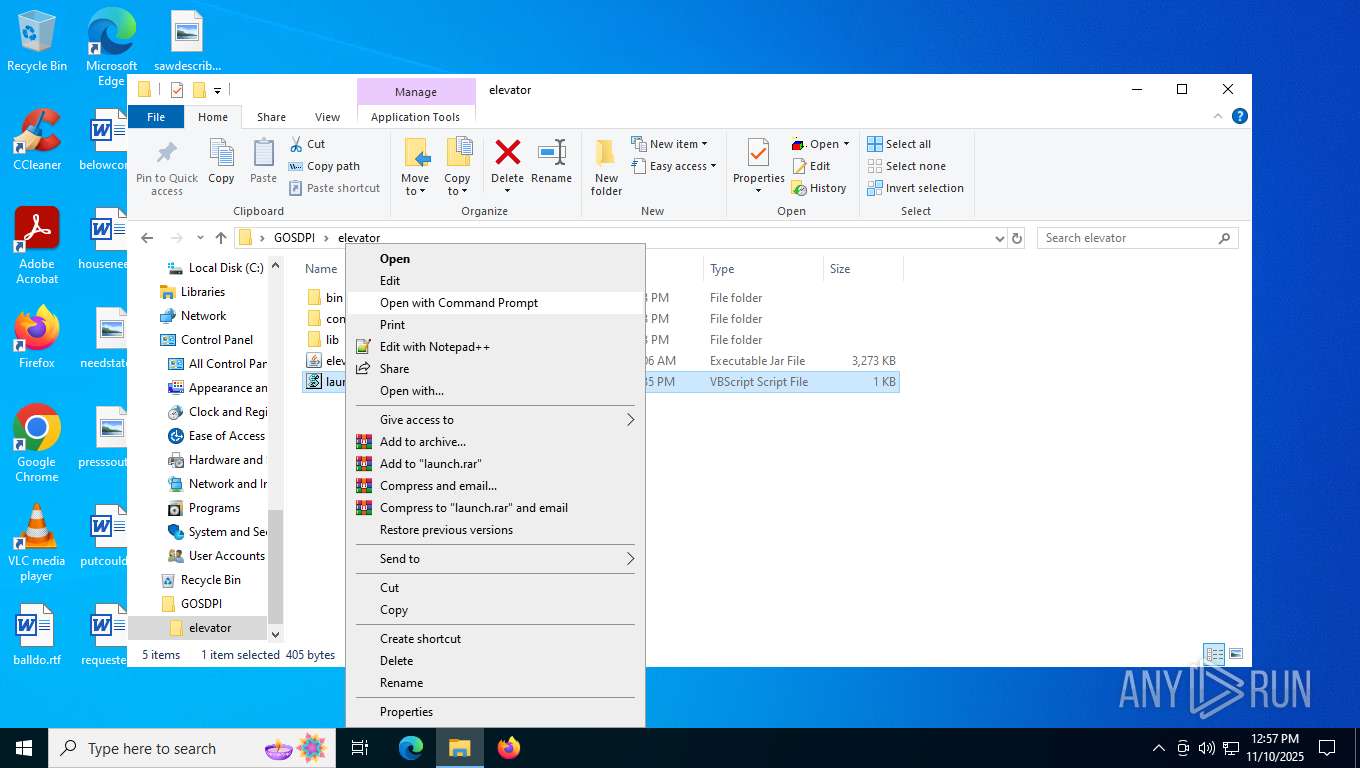
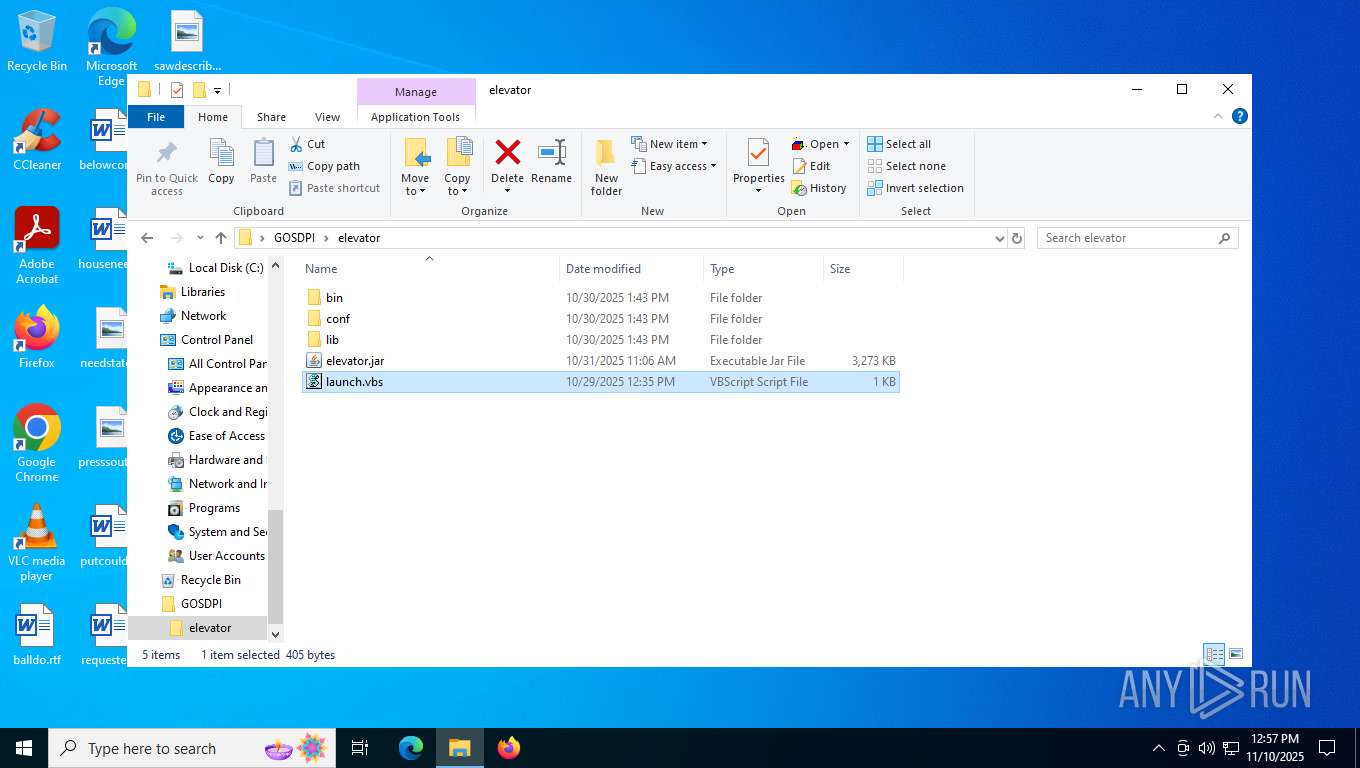
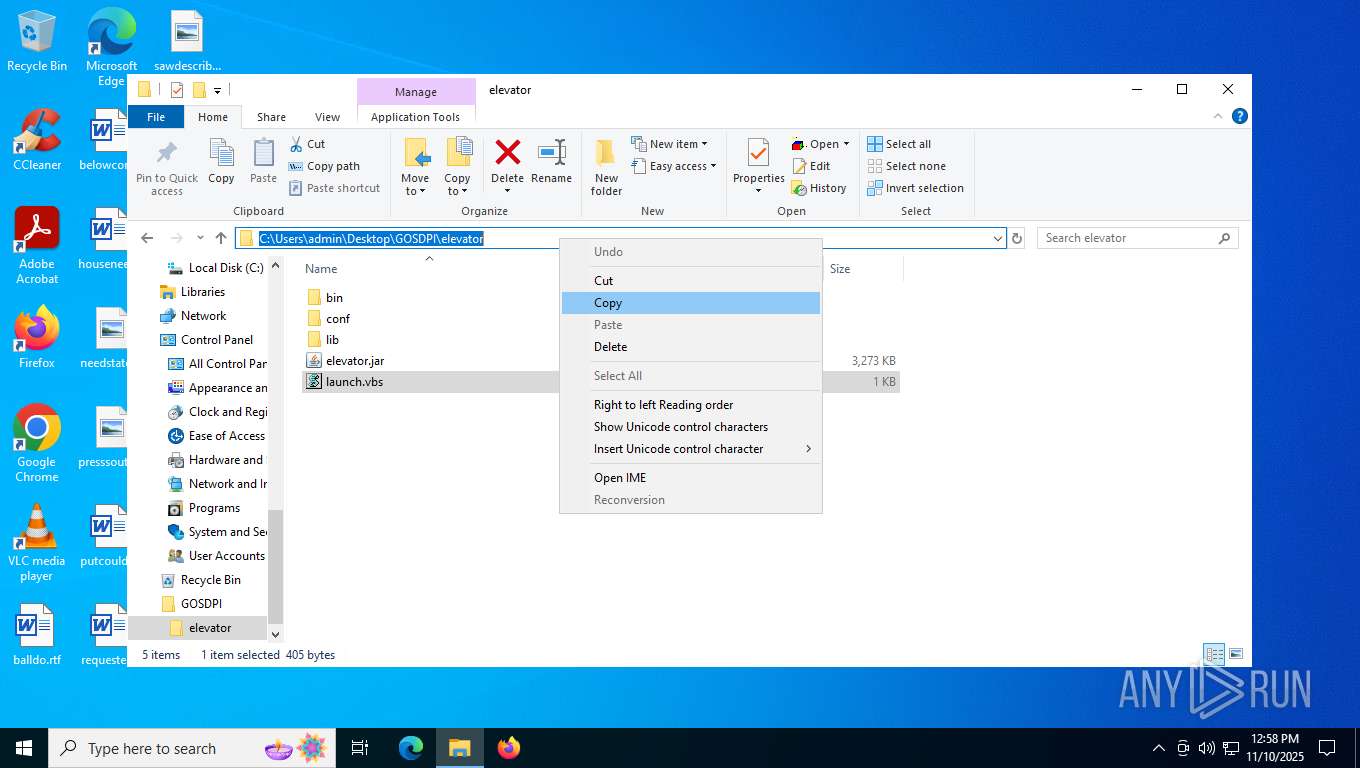
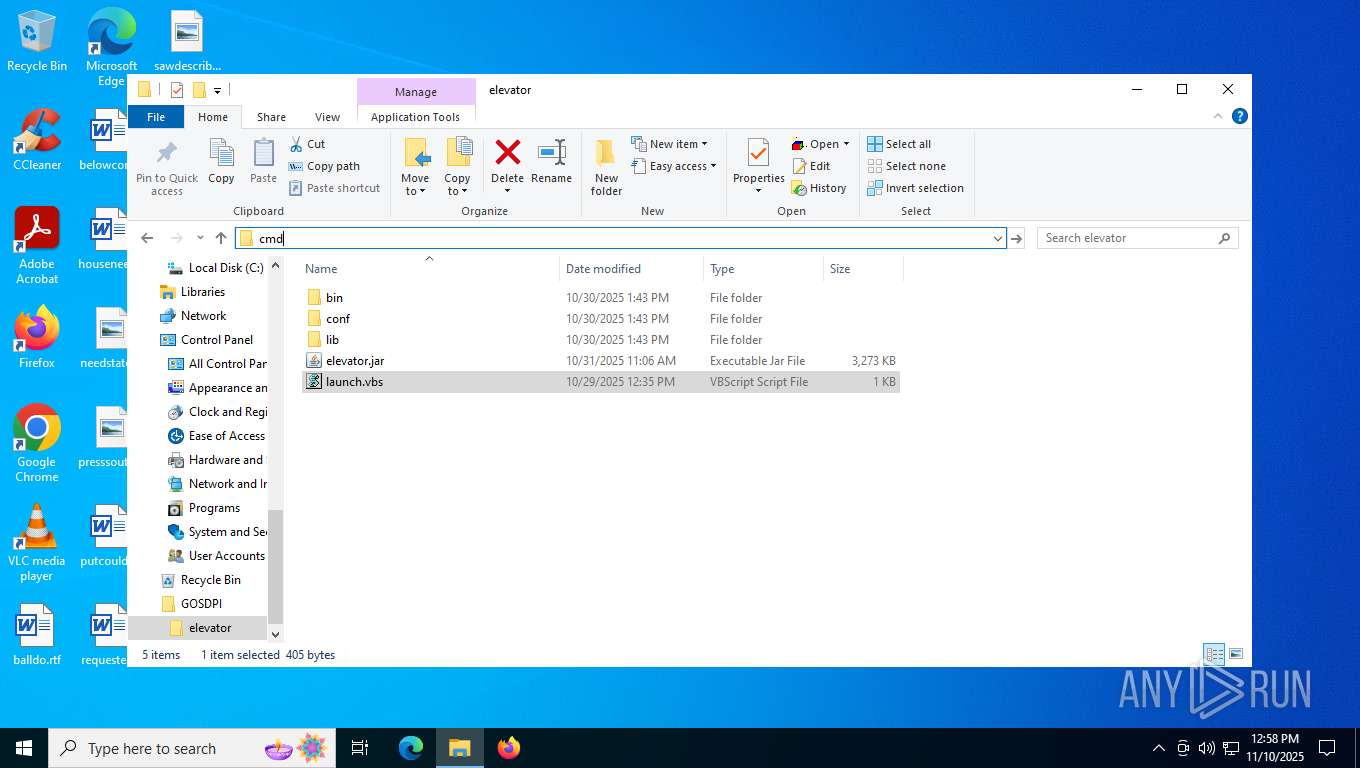
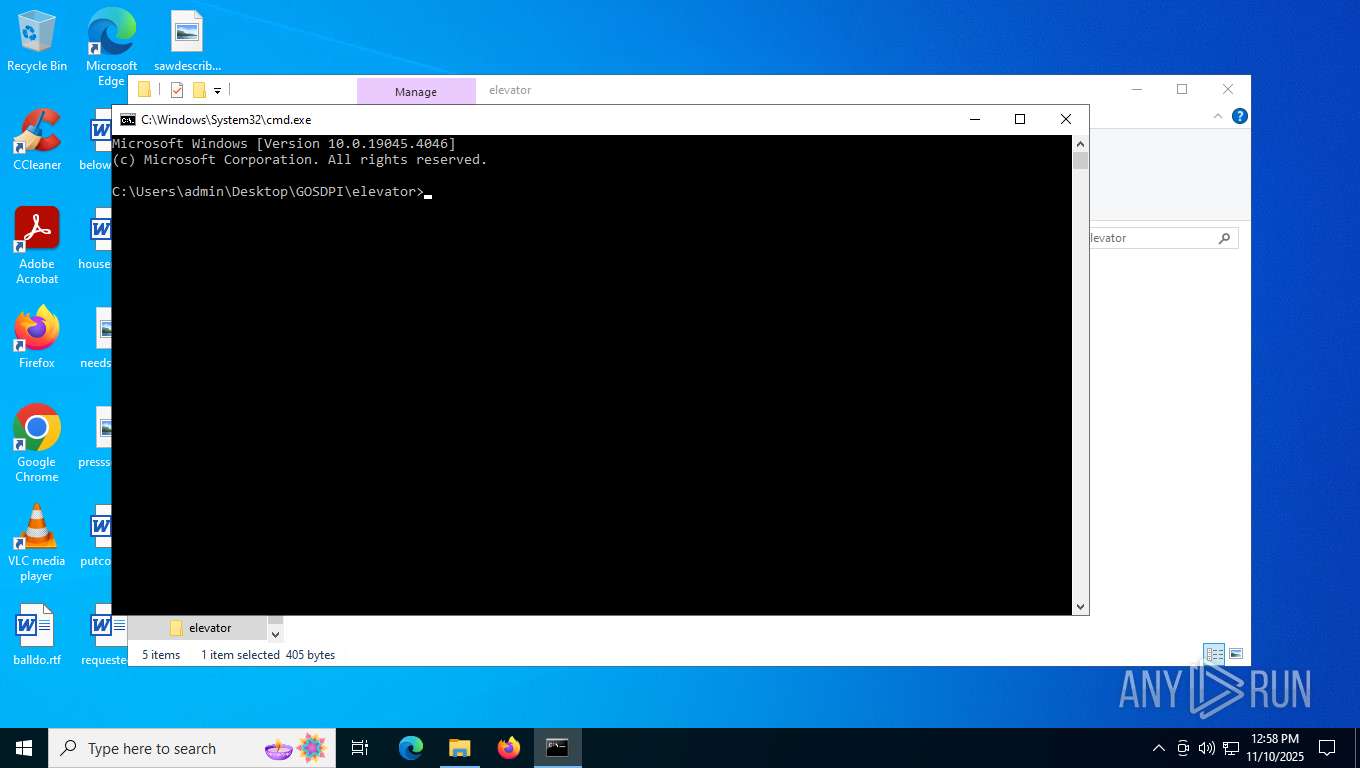
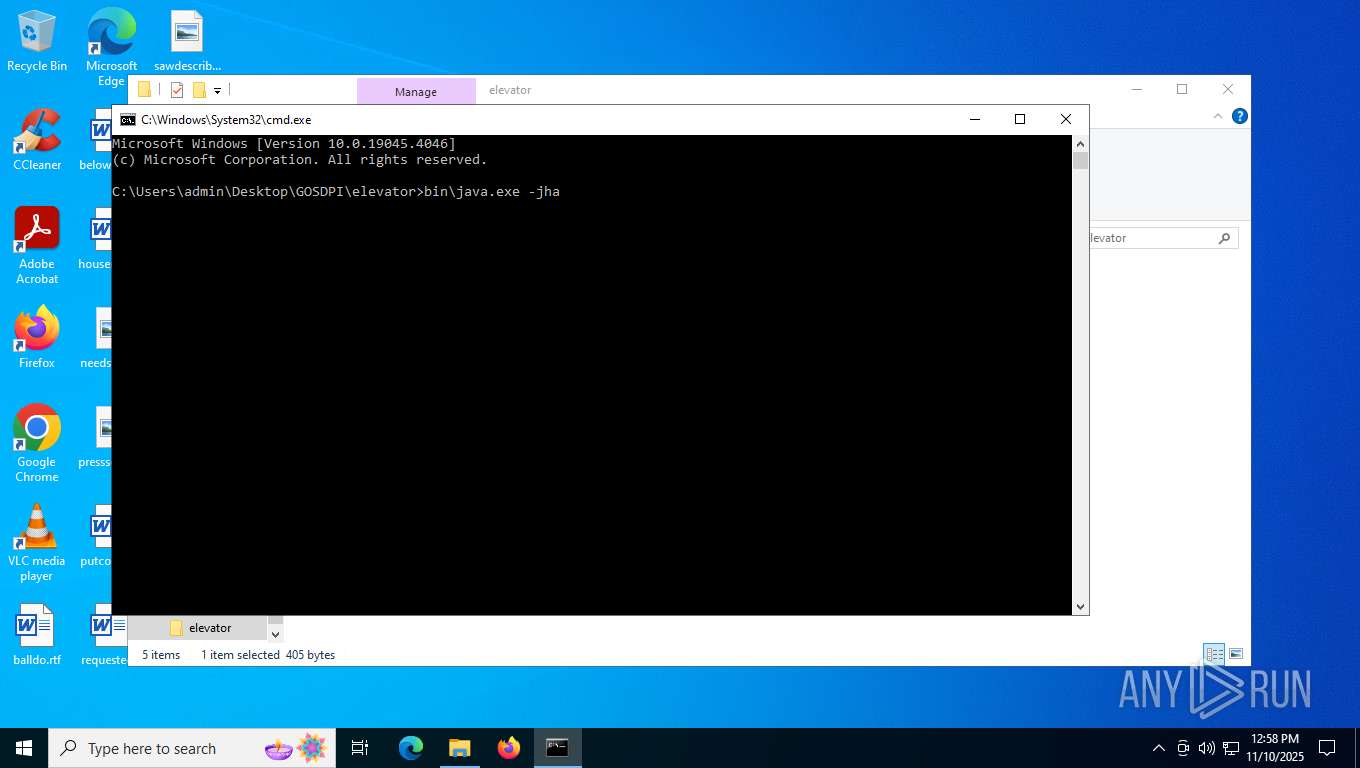
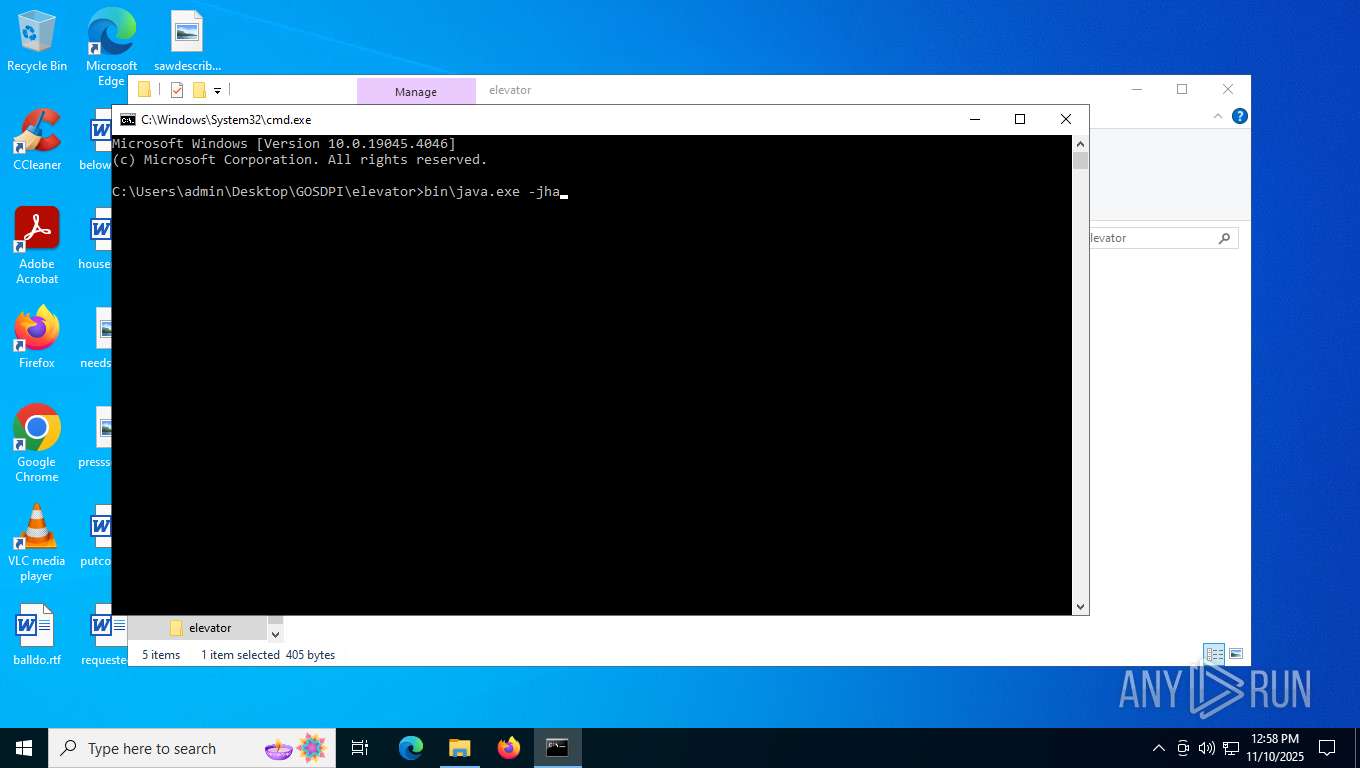
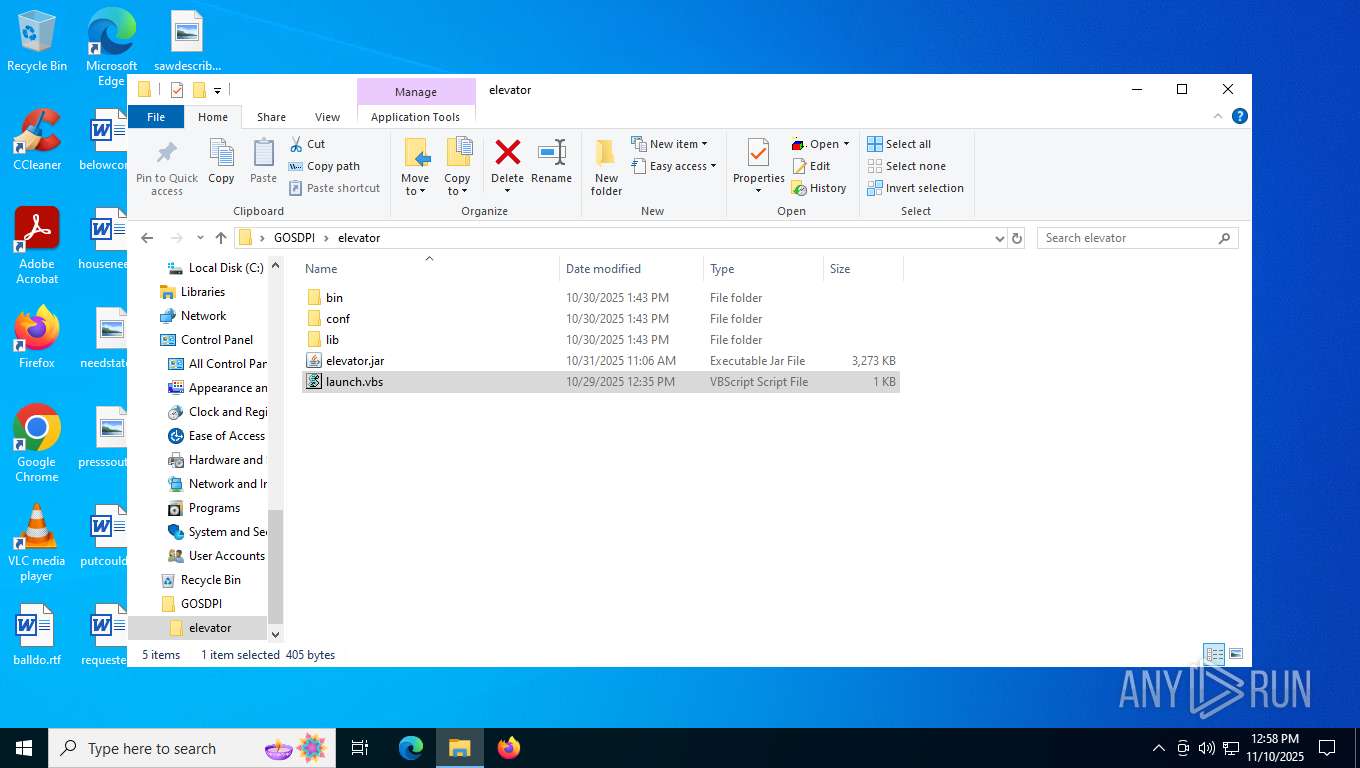
Manual execution by a user
- wscript.exe (PID: 8616)
- notepad.exe (PID: 9136)
- cmd.exe (PID: 9188)
Checks supported languages
- identity_helper.exe (PID: 3356)
- javaw.exe (PID: 8668)
- ChipsetSetup.exe (PID: 8324)
- 7df13.exe (PID: 5276)
- 7df13.exe (PID: 7848)
The sample compiled with english language support
- WinRAR.exe (PID: 8244)
- ChipsetSetup.exe (PID: 8324)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8244)
Reads CPU info
- javaw.exe (PID: 8668)
Create files in a temporary directory
- javaw.exe (PID: 8668)
- ChipsetSetup.exe (PID: 8324)
Reads security settings of Internet Explorer
- notepad.exe (PID: 9136)
Process checks computer location settings
- javaw.exe (PID: 8668)
Reads the machine GUID from the registry
- javaw.exe (PID: 8668)
- ChipsetSetup.exe (PID: 8324)
Creates files or folders in the user directory
- javaw.exe (PID: 8668)
- WerFault.exe (PID: 8156)
Disables trace logs
- cmstp.exe (PID: 8196)
- ChipsetSetup.exe (PID: 8324)
- cmstp.exe (PID: 7744)
Creates files in the program directory
- dllhost.exe (PID: 8128)
- javaw.exe (PID: 8668)
- ChipsetSetup.exe (PID: 8324)
Checks transactions between databases Windows and Oracle
- cmstp.exe (PID: 8196)
- cmstp.exe (PID: 7744)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7984)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7984)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7984)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7984)
- powershell.exe (PID: 5480)
- powershell.exe (PID: 7608)
Checks proxy server information
- ChipsetSetup.exe (PID: 8324)
- WerFault.exe (PID: 8156)
- slui.exe (PID: 5192)
Reads the software policy settings
- WerFault.exe (PID: 8156)
- slui.exe (PID: 5192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
194
Monitored processes
44
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1252 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5868,i,2209143182224826356,3912260757520392899,262144 --variations-seed-version --mojo-platform-channel-handle=5624 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6980,i,2209143182224826356,3912260757520392899,262144 --variations-seed-version --mojo-platform-channel-handle=6784 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3356 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6596,i,2209143182224826356,3912260757520392899,262144 --variations-seed-version --mojo-platform-channel-handle=6444 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4556 | taskkill /IM cmstp.exe /F | C:\Windows\System32\taskkill.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5192 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5276 | "7df13.exe" x "C:\Users\admin\AppData\Local\Temp\tmp6736.tmp" -pAum$SD2q1 -o"C:\Users\admin\AppData\Local\Programs\AMD Software\Performance Profile Client" -y | C:\Users\admin\AppData\Local\Temp\7df13.exe | — | ChipsetSetup.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Exit code: 2 Version: 22.01 Modules
| |||||||||||||||
| 5480 | "powershell" Stop-ScheduledTask -TaskName "C:\Users\admin\AppData\Local\Programs\AMD Software\Performance Profile Client\AUEPMaster.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | ChipsetSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --always-read-main-dll --field-trial-handle=6156,i,2209143182224826356,3912260757520392899,262144 --variations-seed-version --mojo-platform-channel-handle=6120 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
27 126
Read events
27 056
Write events
67
Delete events
3
Modification events
| (PID) Process: | (8244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\gosdpi.7z | |||
| (PID) Process: | (8244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (8244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
113
Suspicious files
236
Text files
90
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1620fa.TMP | — | |
MD5:— | SHA256:— | |||
| 7400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1620fa.TMP | — | |
MD5:— | SHA256:— | |||
| 7400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF16210a.TMP | — | |
MD5:— | SHA256:— | |||
| 7400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF16210a.TMP | — | |
MD5:— | SHA256:— | |||
| 7400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF162158.TMP | — | |
MD5:— | SHA256:— | |||
| 7400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF162167.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
57
DNS requests
41
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8324 | ChipsetSetup.exe | GET | 200 | 185.213.240.136:80 | http://185.213.240.136/ChipsetSetup.7z | HR | compressed | 468 Kb | unknown |
8324 | ChipsetSetup.exe | GET | — | 185.213.240.136:80 | http://185.213.240.136/XTU-User-Guide.pdf | HR | — | — | unknown |
8156 | WerFault.exe | GET | 200 | 95.101.78.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
8156 | WerFault.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
5972 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7740 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:su5PHR1qAMtJc_YoLgdqPI9Jty0aJL7CUu9EGCFHD84&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 98 b | whitelisted |
8976 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
2388 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
8976 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | DE | binary | 402 b | whitelisted |
8976 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | DE | binary | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2388 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3448 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7088 | SearchApp.exe | 92.123.104.5:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7740 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7740 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7740 | msedge.exe | 188.114.97.3:443 | tmpfiles.org | CLOUDFLARENET | NL | whitelisted |
7740 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
tmpfiles.org |
| unknown |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7740 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Domain Marked as Malicious (tmpfiles .org) |
7740 | msedge.exe | Misc activity | ET INFO Temporary File Hosting Domain in DNS Lookup (tmpfiles .org) |
7740 | msedge.exe | Misc activity | ET INFO Temporary File Hosting Domain in DNS Lookup (tmpfiles .org) |
7740 | msedge.exe | Misc activity | ET INFO Observed Temporary File Hosting Domain (tmpfiles .org in TLS SNI) |
7740 | msedge.exe | Misc activity | ET INFO Observed Temporary File Hosting Domain (tmpfiles .org in TLS SNI) |
7740 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Domain Marked as Malicious (tmpfiles .org) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8324 | ChipsetSetup.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host PDF Request |