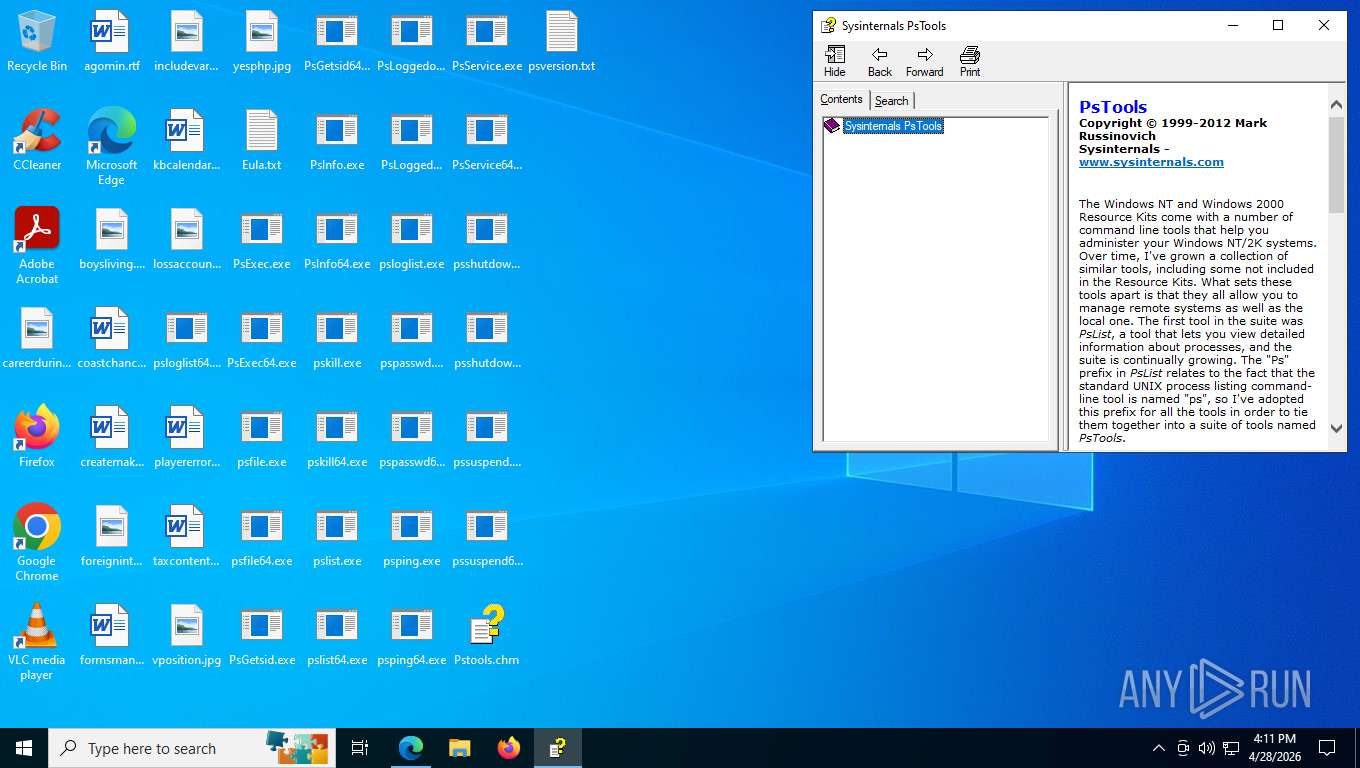
| URL: | https://learn.microsoft.com/en-us/sysinternals/downloads/pstools |
| Full analysis: | https://app.any.run/tasks/f1eea02f-9eb3-4a21-bb88-0d0f12ed3cf4 |
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2026, 20:10:58 |
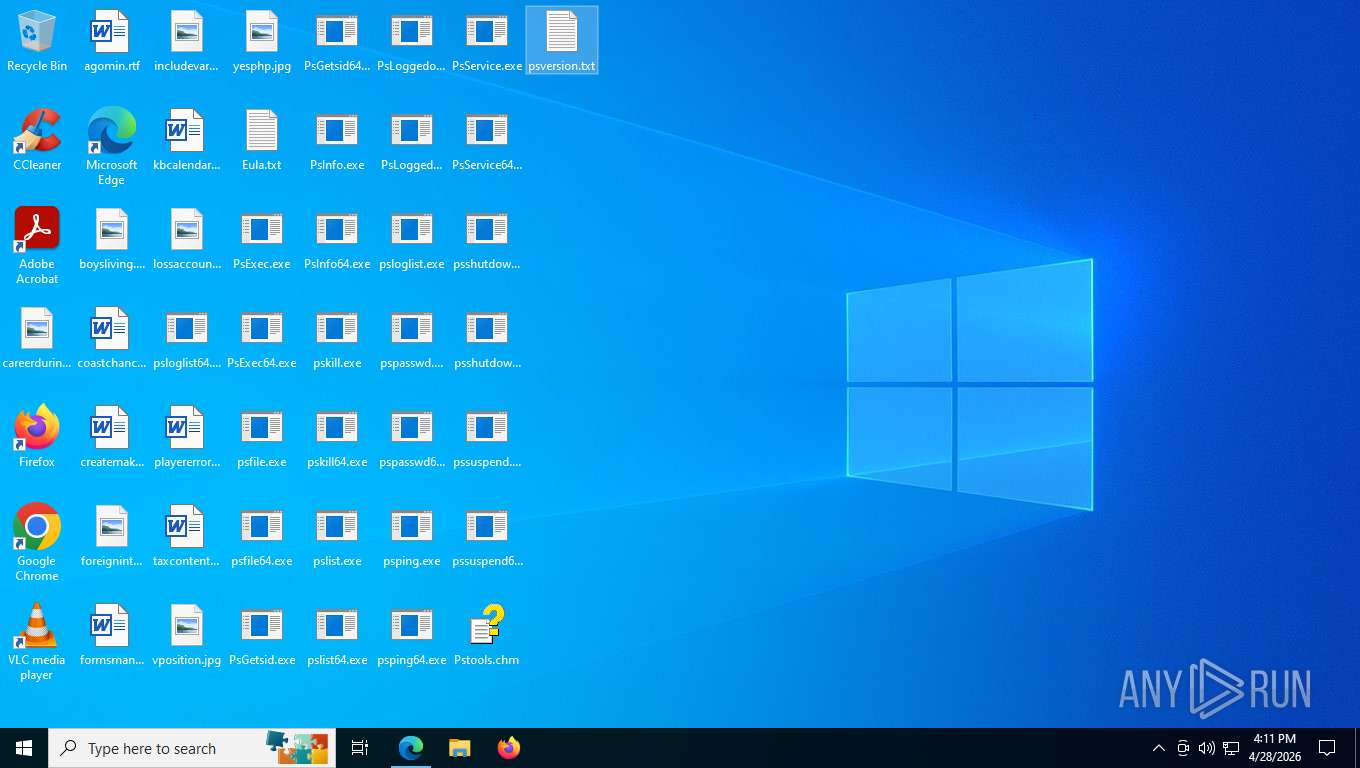
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2E6E02CE9C3EC92284E40C483EE228C5 |
| SHA1: | A3EABE635C0DE7672BFC26B403C943F9FC609A3E |
| SHA256: | 8E09E3AF3B22EC74D2E1C793D9F96E1F968C015E08C9992381E0E065AAA9C9C8 |
| SSDEEP: | 3:N8AEvTtRH6+XHaKXK8Un:2AEvTDHNKKa8Un |
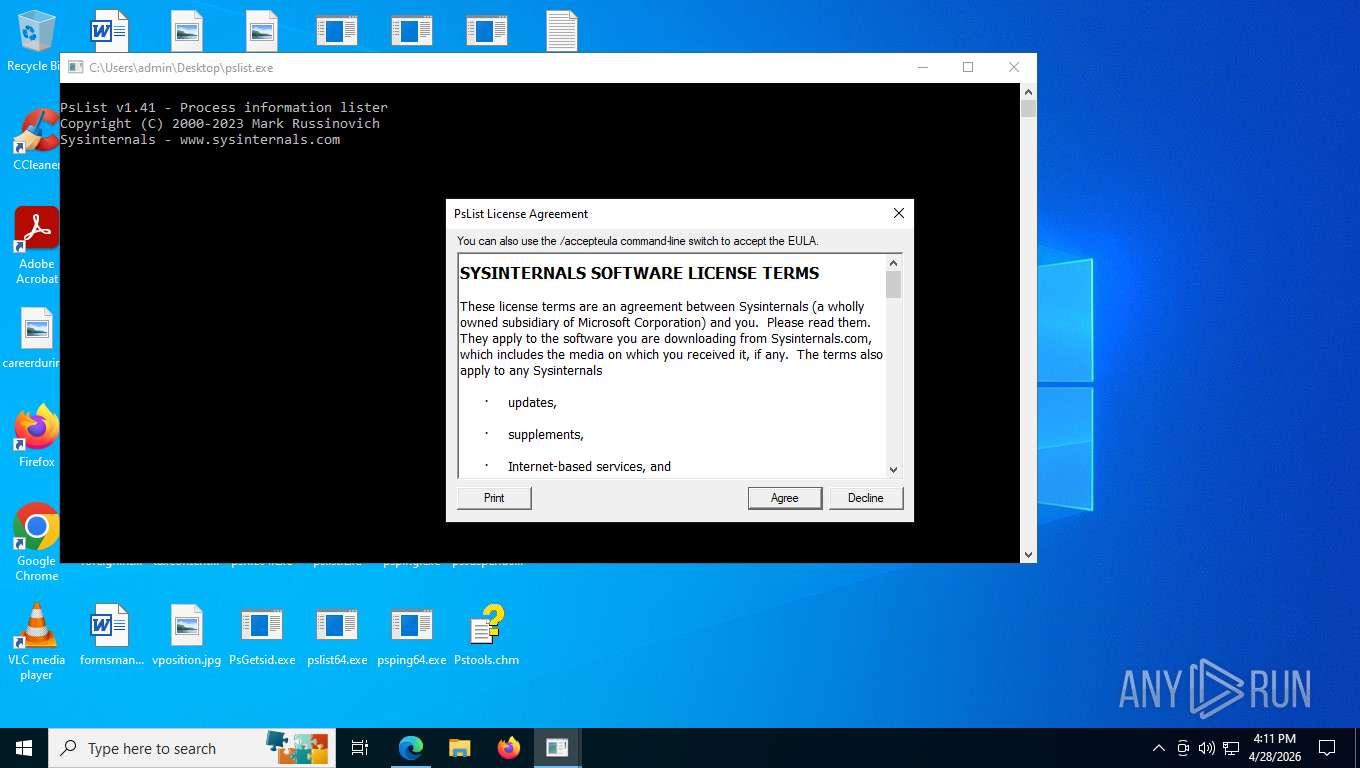
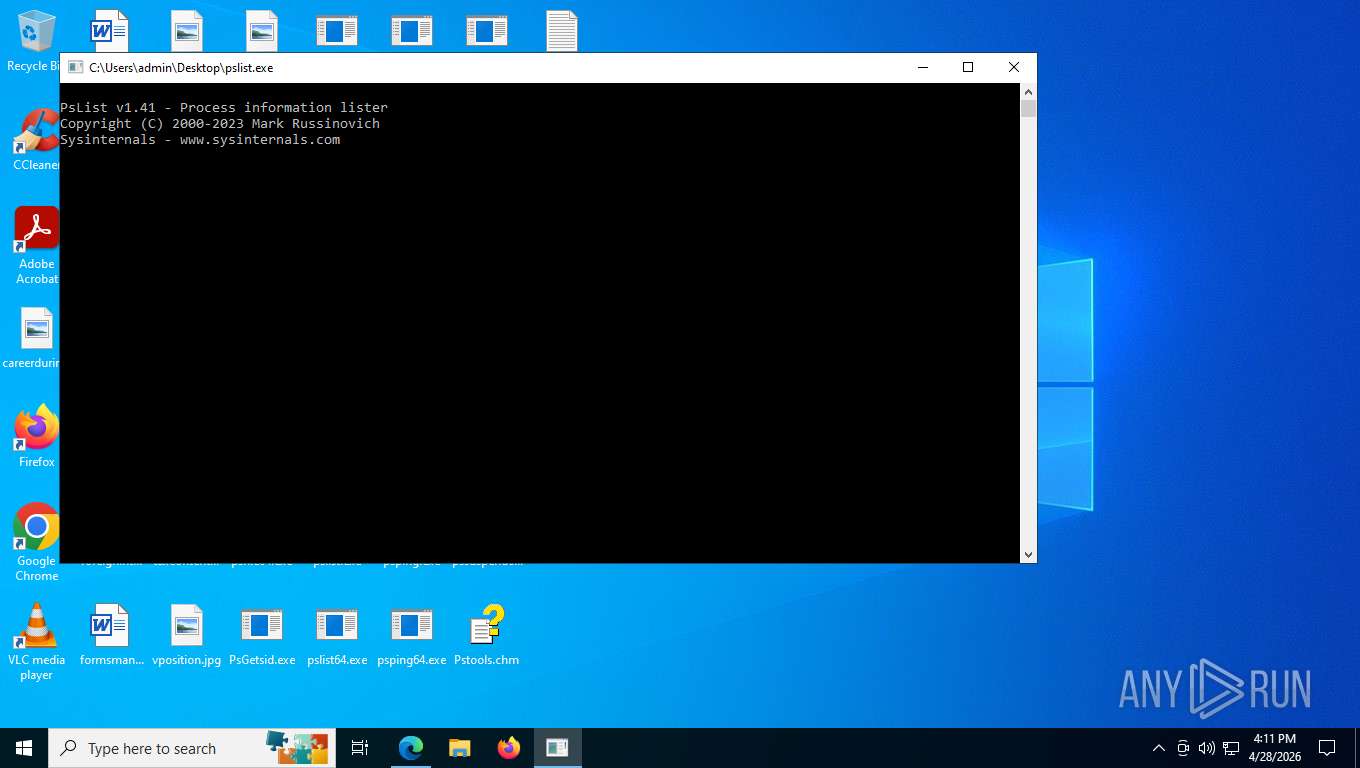
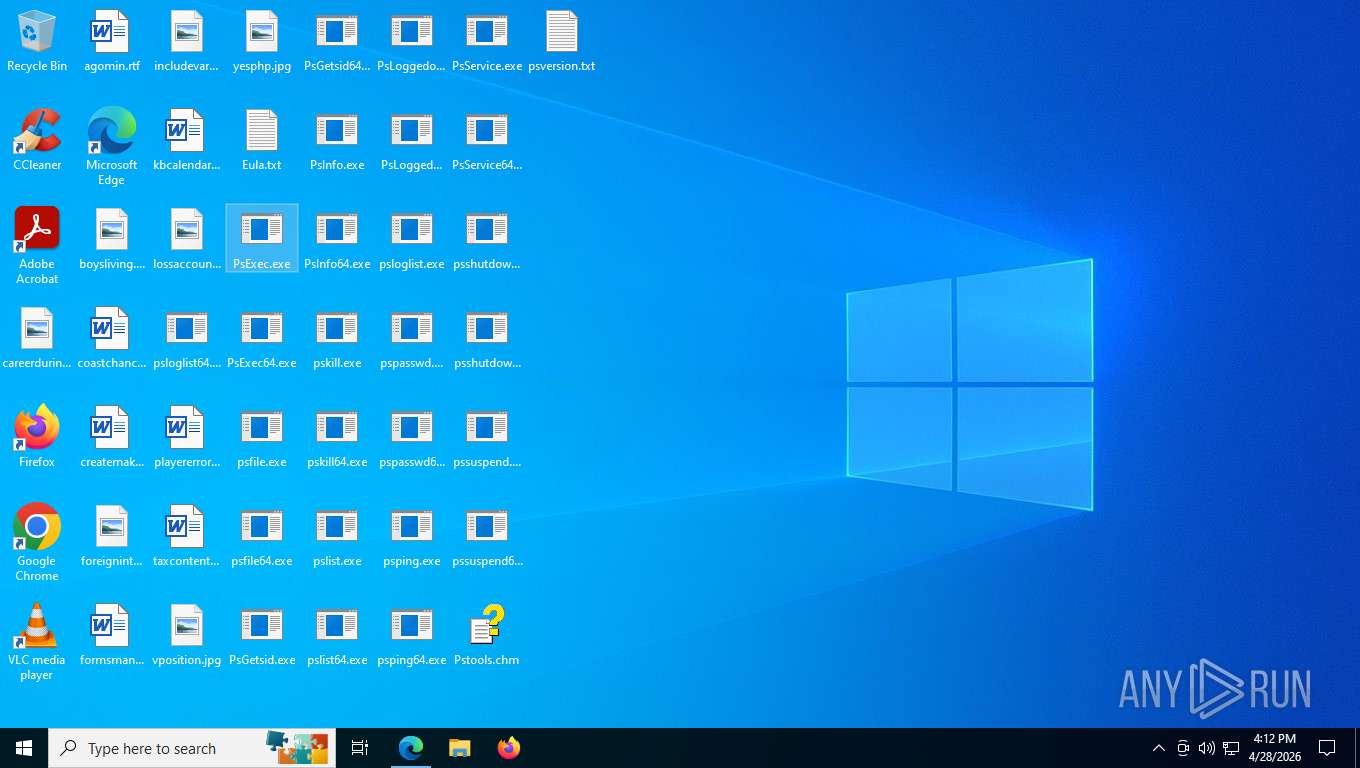
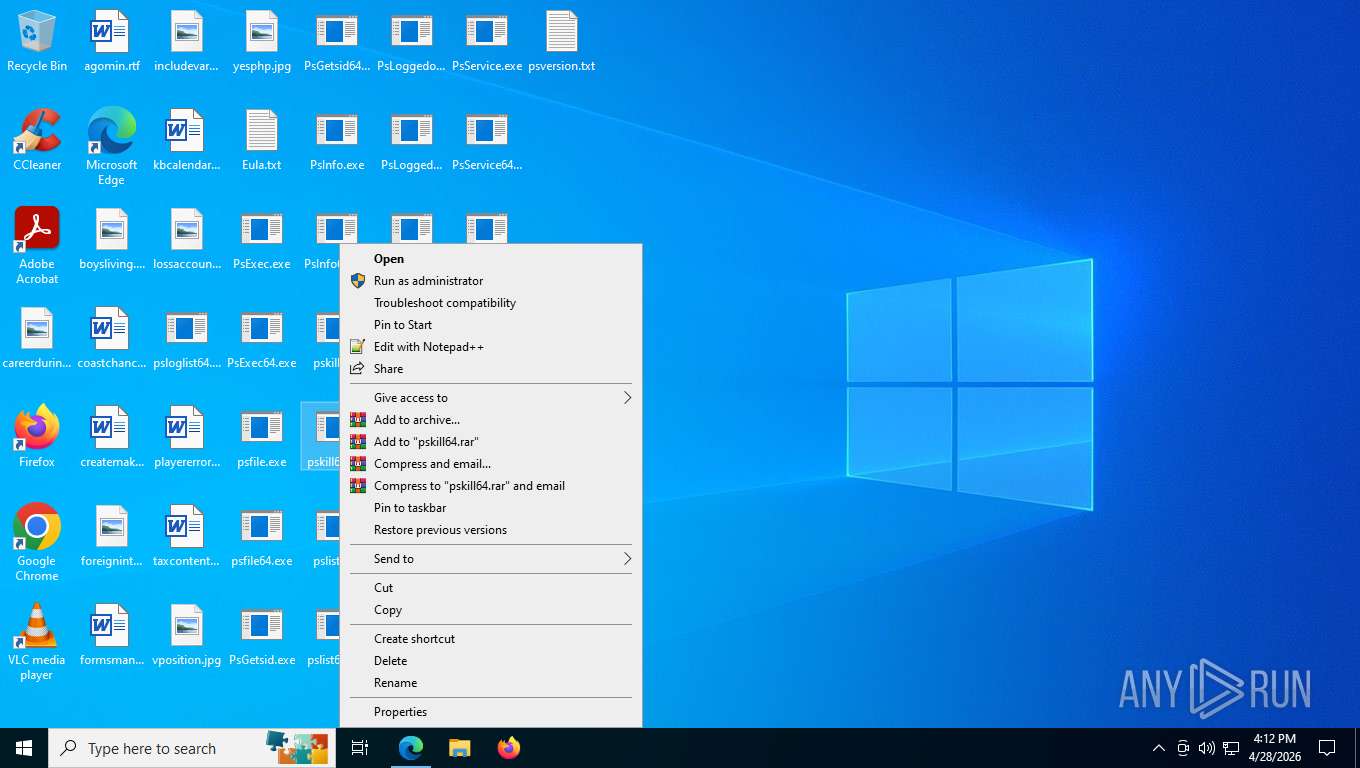
MALICIOUS
Executing a file with an untrusted certificate
- pslist.exe (PID: 8828)
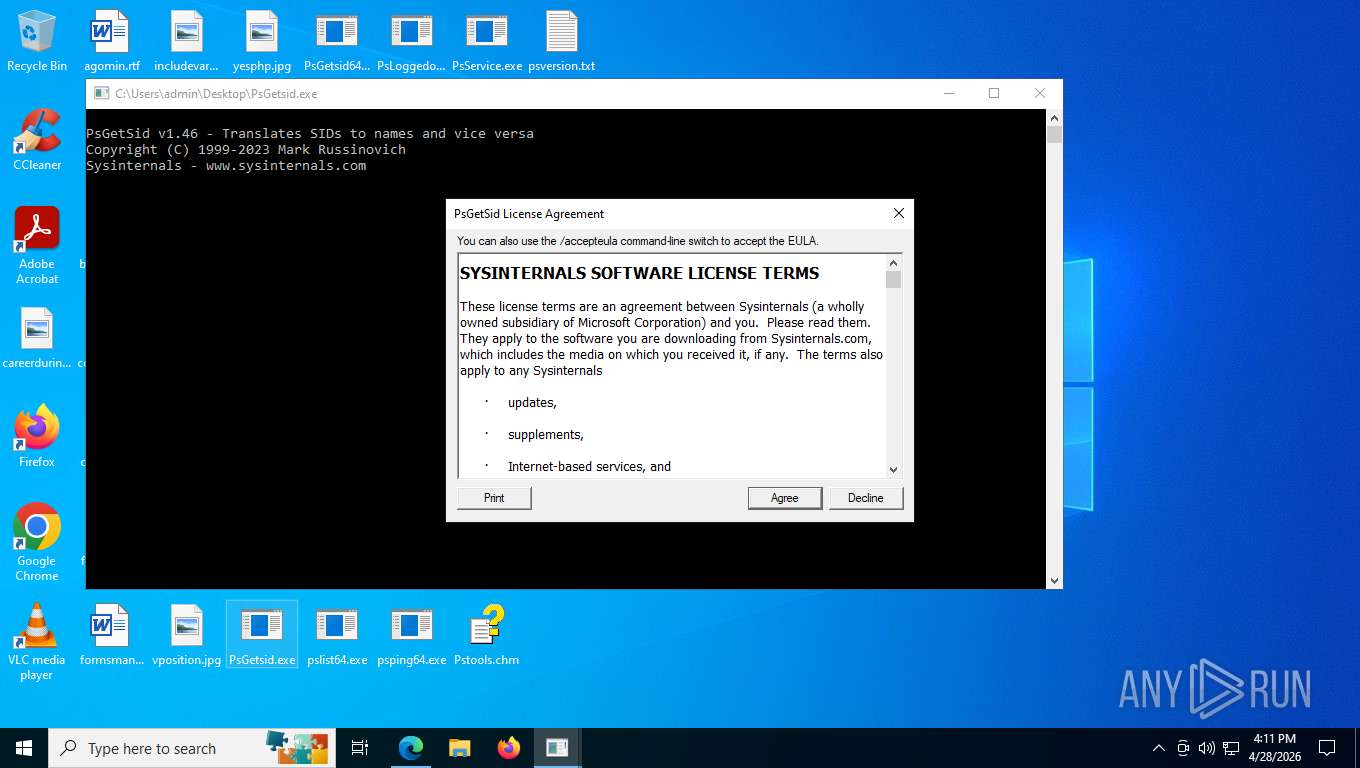
- PsGetsid.exe (PID: 8220)
- PsExec.exe (PID: 5100)
- PsExec.exe (PID: 8876)
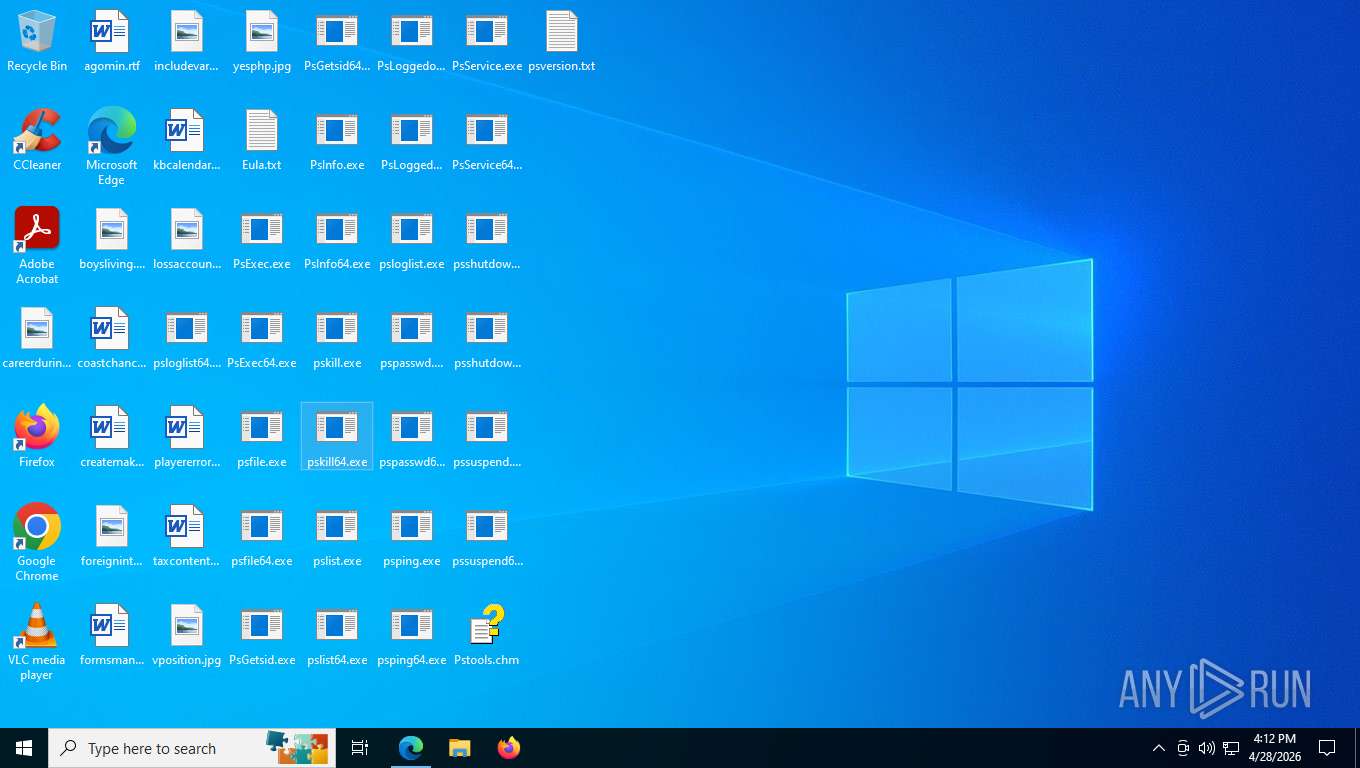
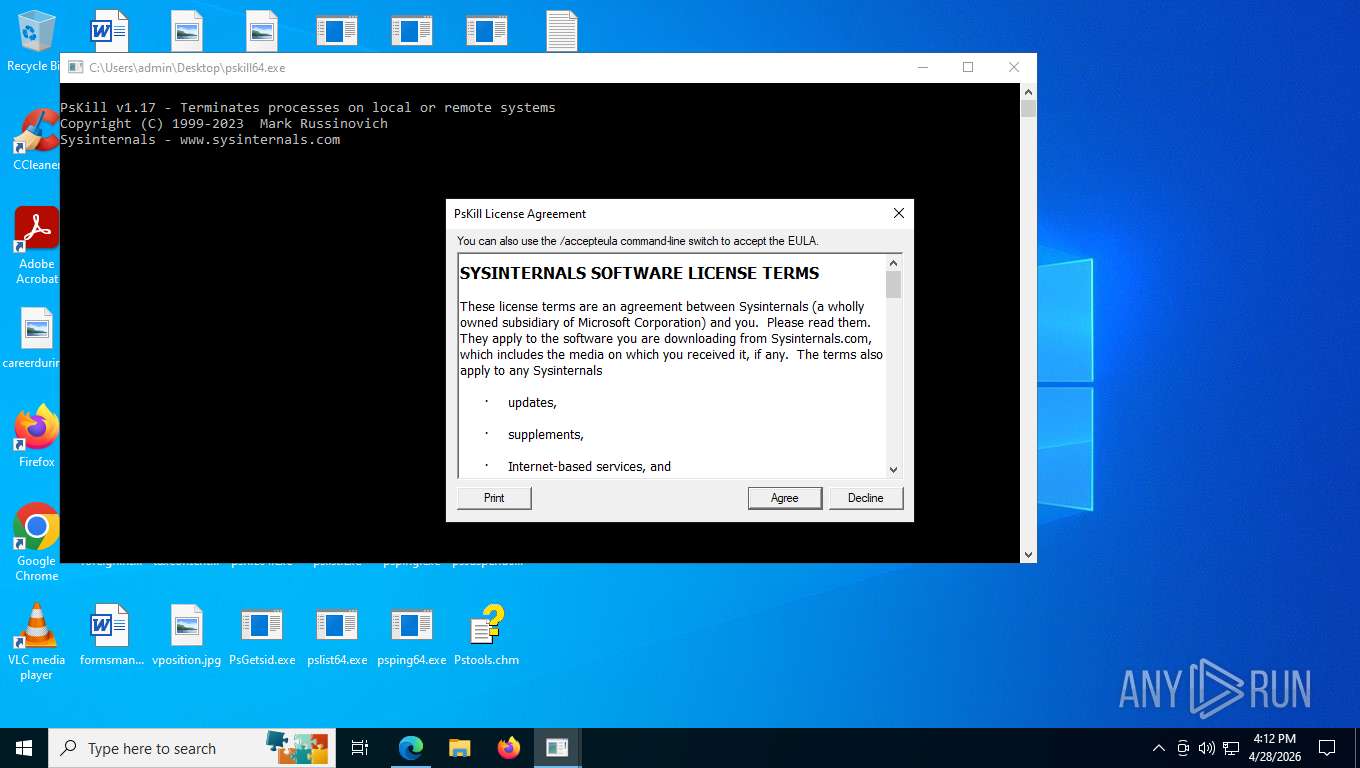
- pskill64.exe (PID: 1192)
- pskill64.exe (PID: 4944)
- pskill64.exe (PID: 9192)
- PsLoggedon.exe (PID: 8416)
- pskill64.exe (PID: 8496)
- pskill64.exe (PID: 8140)
SUSPICIOUS
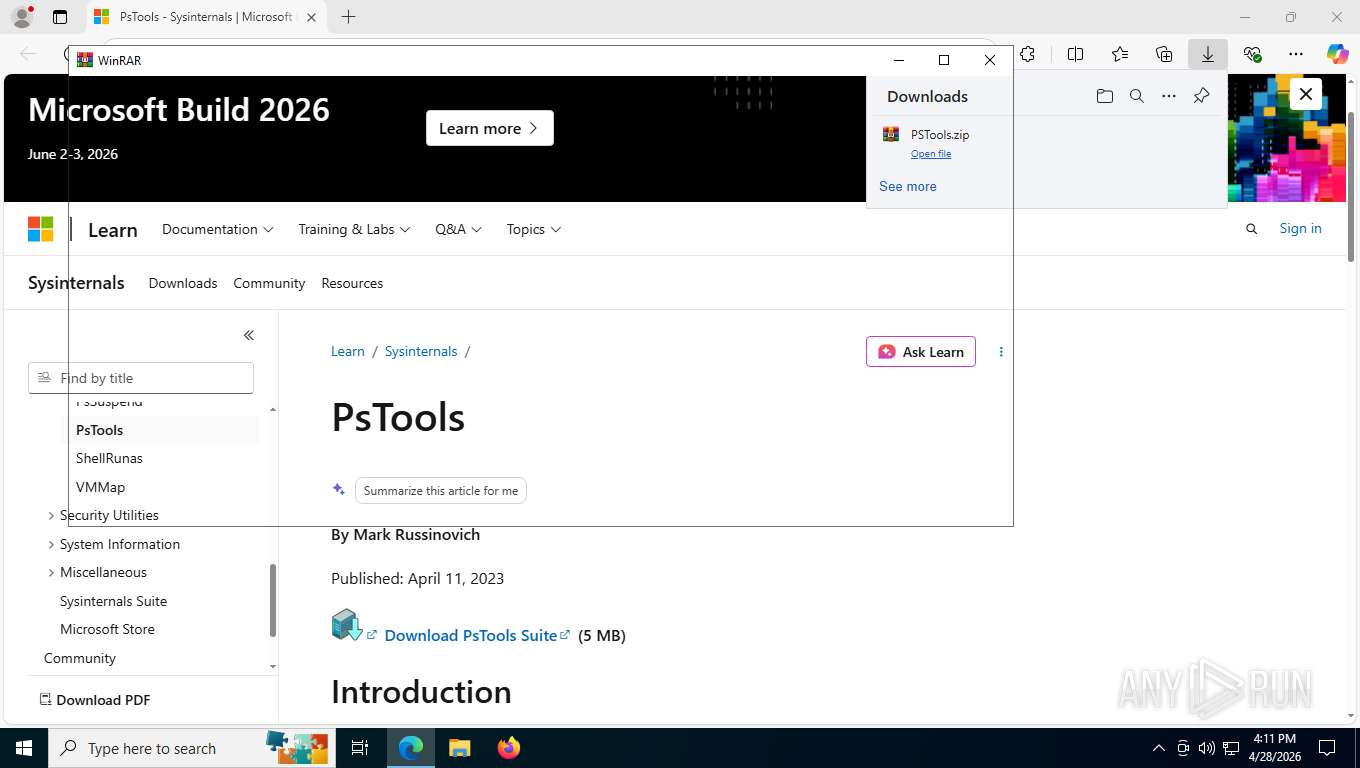
The process creates files with name similar to system file names
- WinRAR.exe (PID: 8816)
Reads Microsoft Outlook installation path
- hh.exe (PID: 6408)
Reads Internet Explorer settings
- hh.exe (PID: 6408)
The process checks if it is being run in the virtual environment
- pslist.exe (PID: 8828)
PSEXEC has been detected
- PsExec.exe (PID: 5100)
- PsExec.exe (PID: 8876)
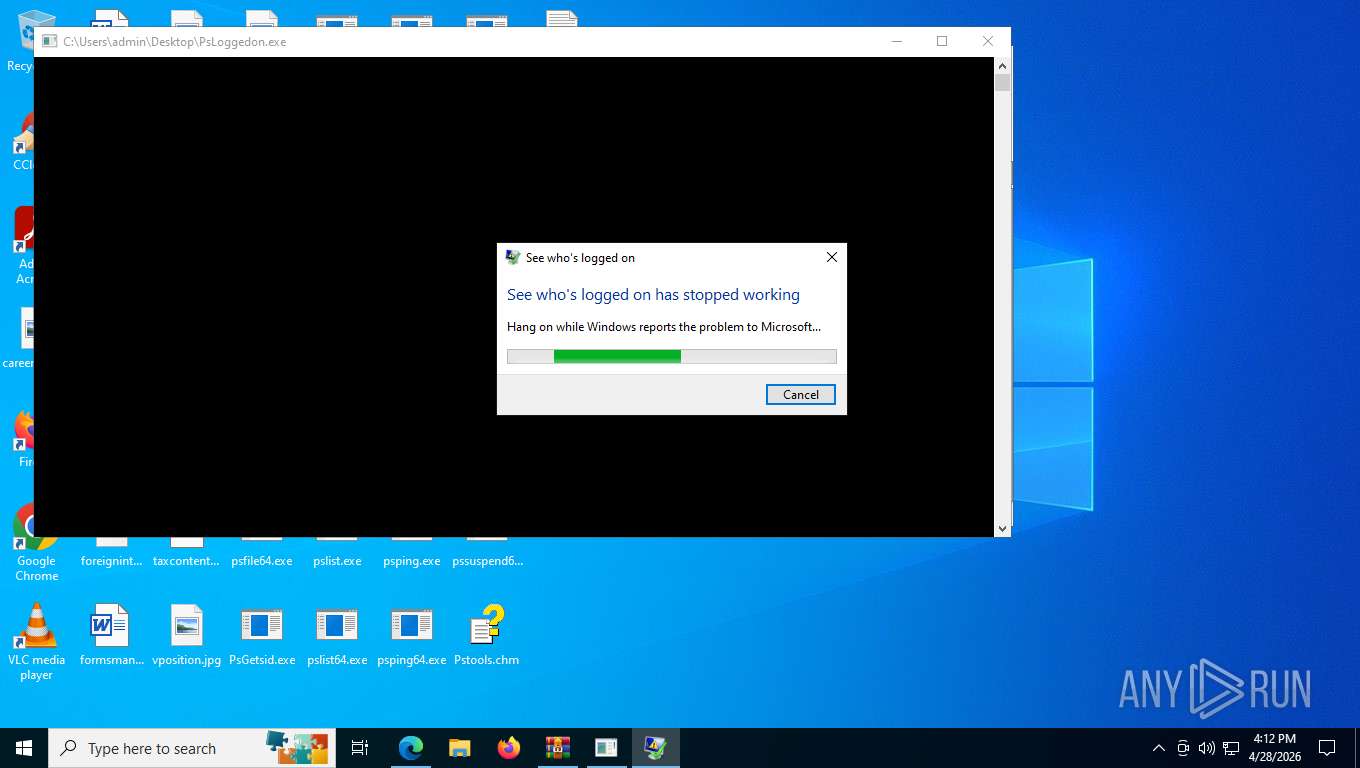
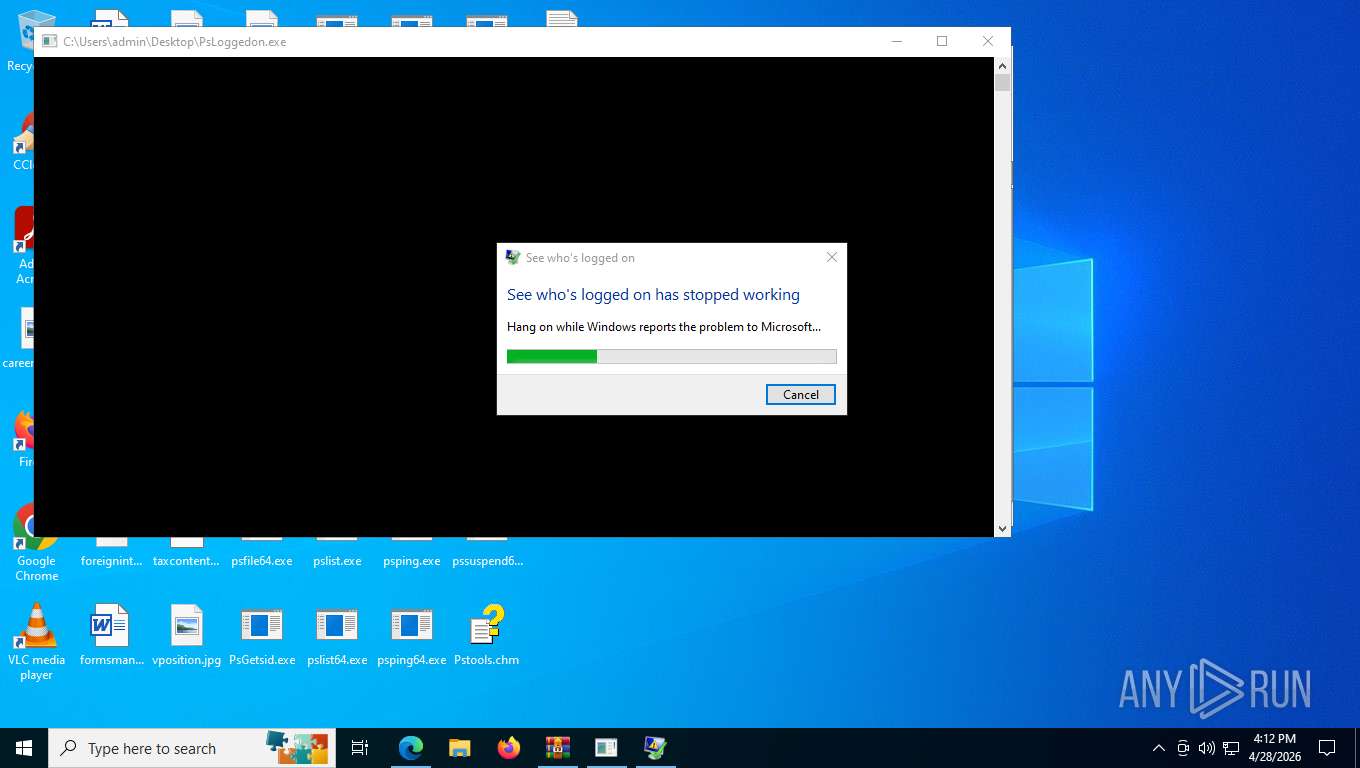
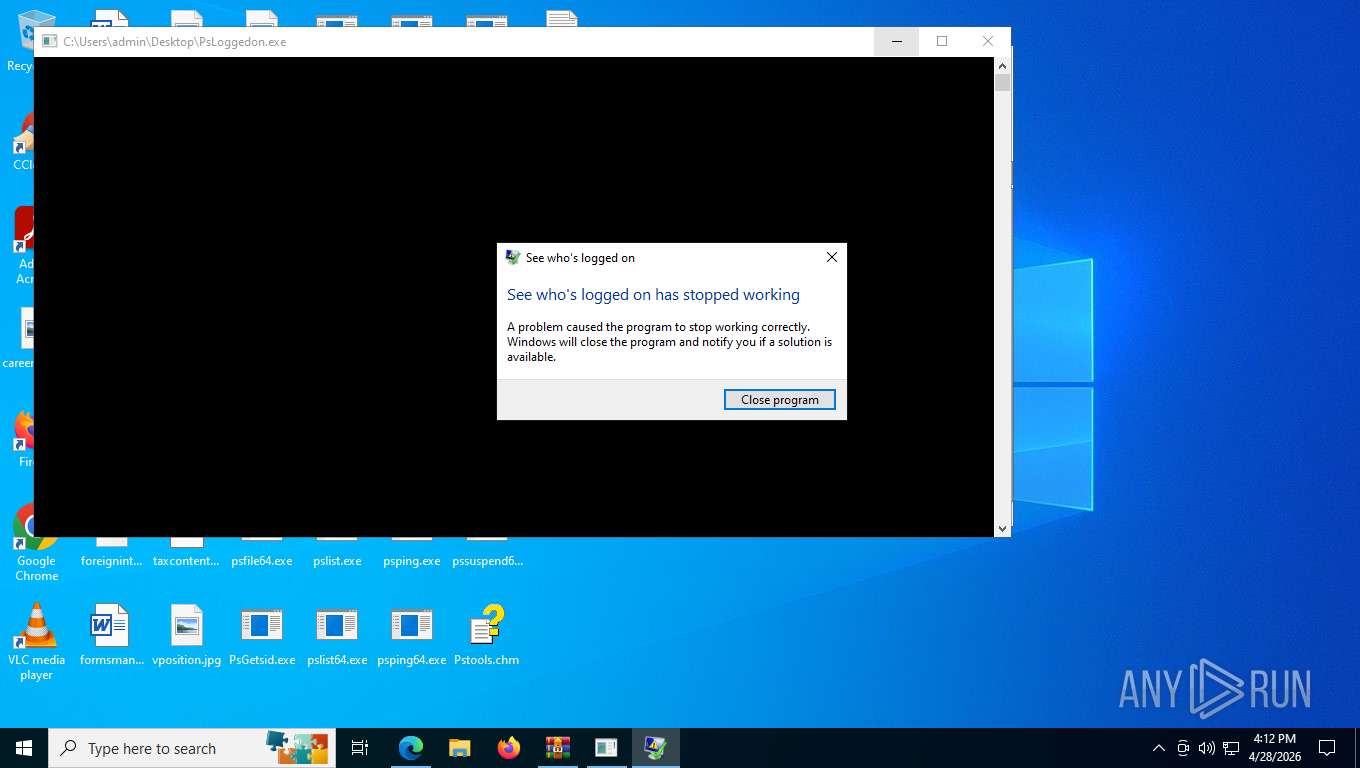
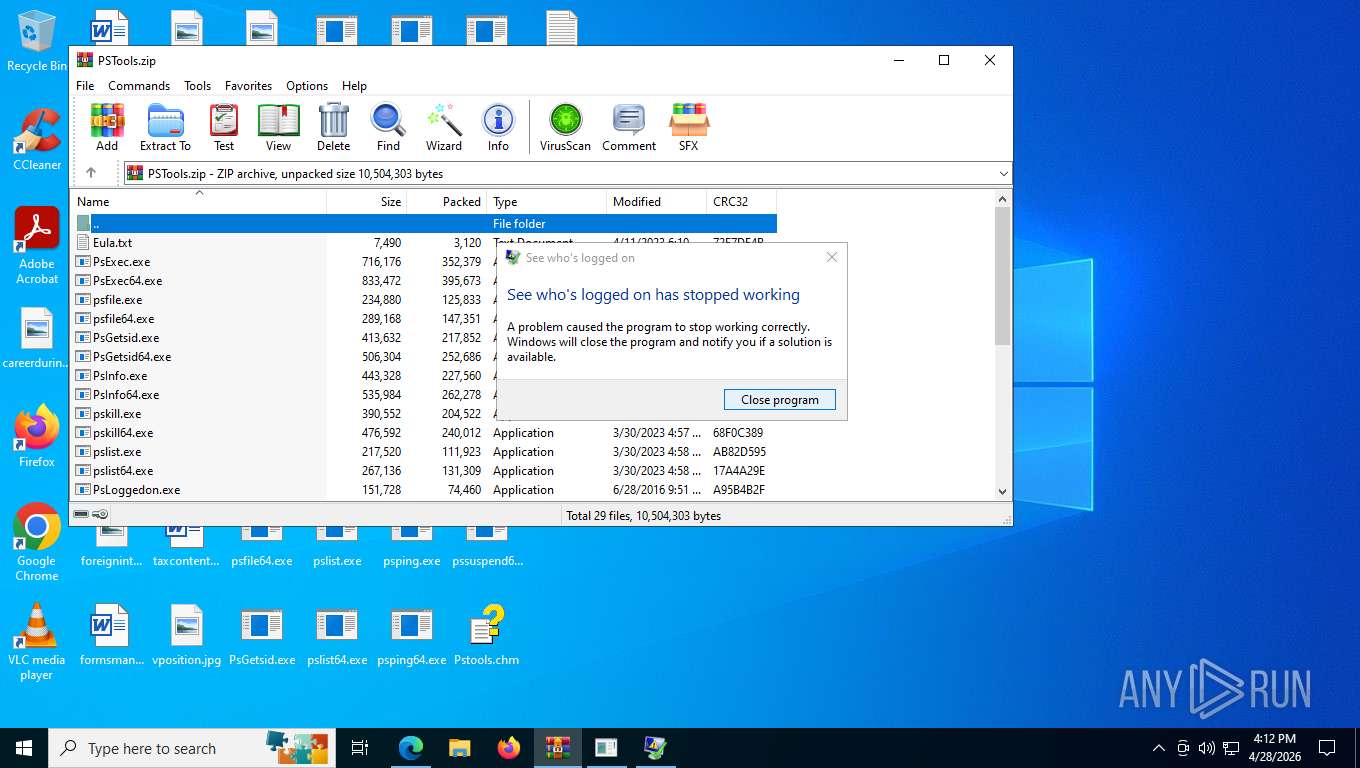
Executes application which crashes
- PsLoggedon.exe (PID: 8416)
INFO
Application launched itself
- msedge.exe (PID: 572)
Reads Environment values
- identity_helper.exe (PID: 7916)
- pskill64.exe (PID: 1192)
Checks supported languages
- identity_helper.exe (PID: 7916)
- PsExec.exe (PID: 5100)
- PsExec.exe (PID: 8876)
- pslist.exe (PID: 8828)
- PsGetsid.exe (PID: 8220)
- PsLoggedon.exe (PID: 8416)
- pskill64.exe (PID: 1192)
- pskill64.exe (PID: 4944)
- pskill64.exe (PID: 8496)
- pskill64.exe (PID: 9192)
- pskill64.exe (PID: 8140)
Reads the computer name
- identity_helper.exe (PID: 7916)
- pslist.exe (PID: 8828)
- PsGetsid.exe (PID: 8220)
- PsExec.exe (PID: 8876)
- PsExec.exe (PID: 5100)
- pskill64.exe (PID: 1192)
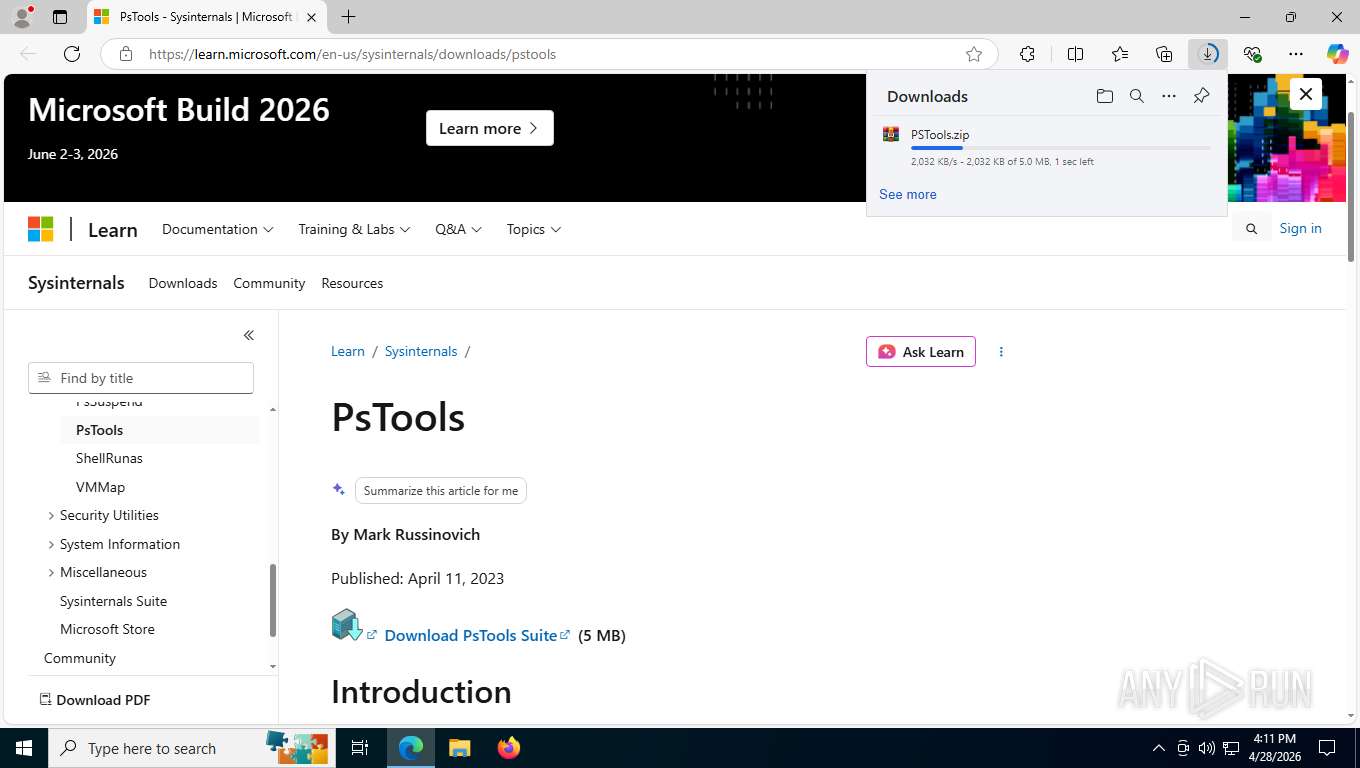
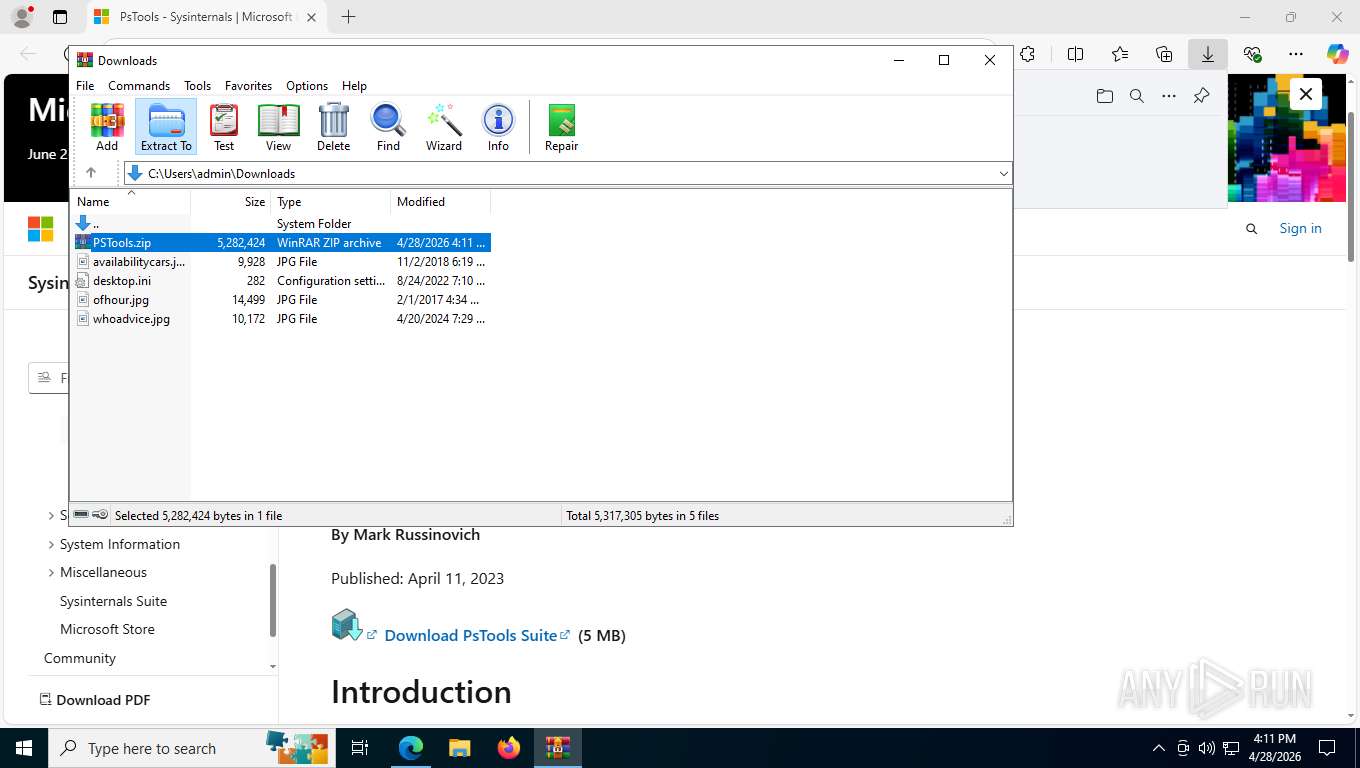
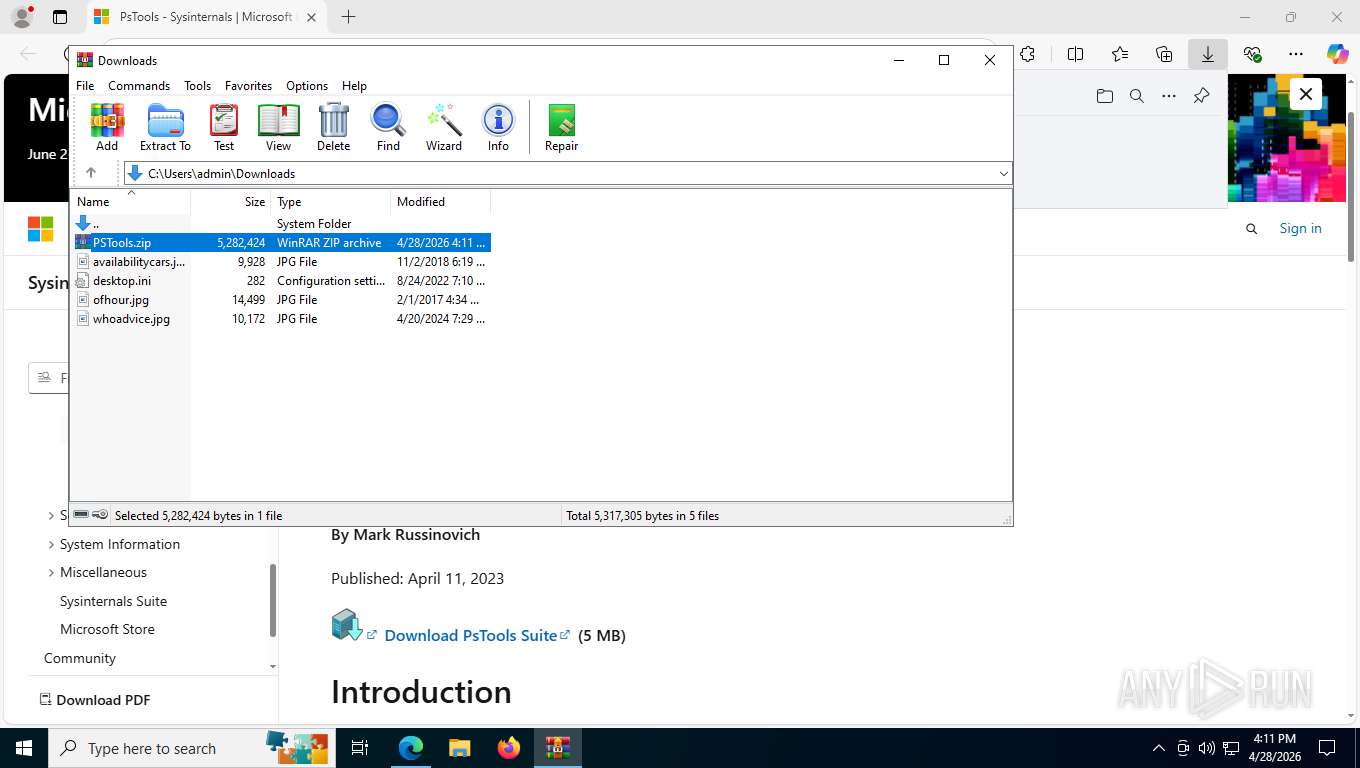
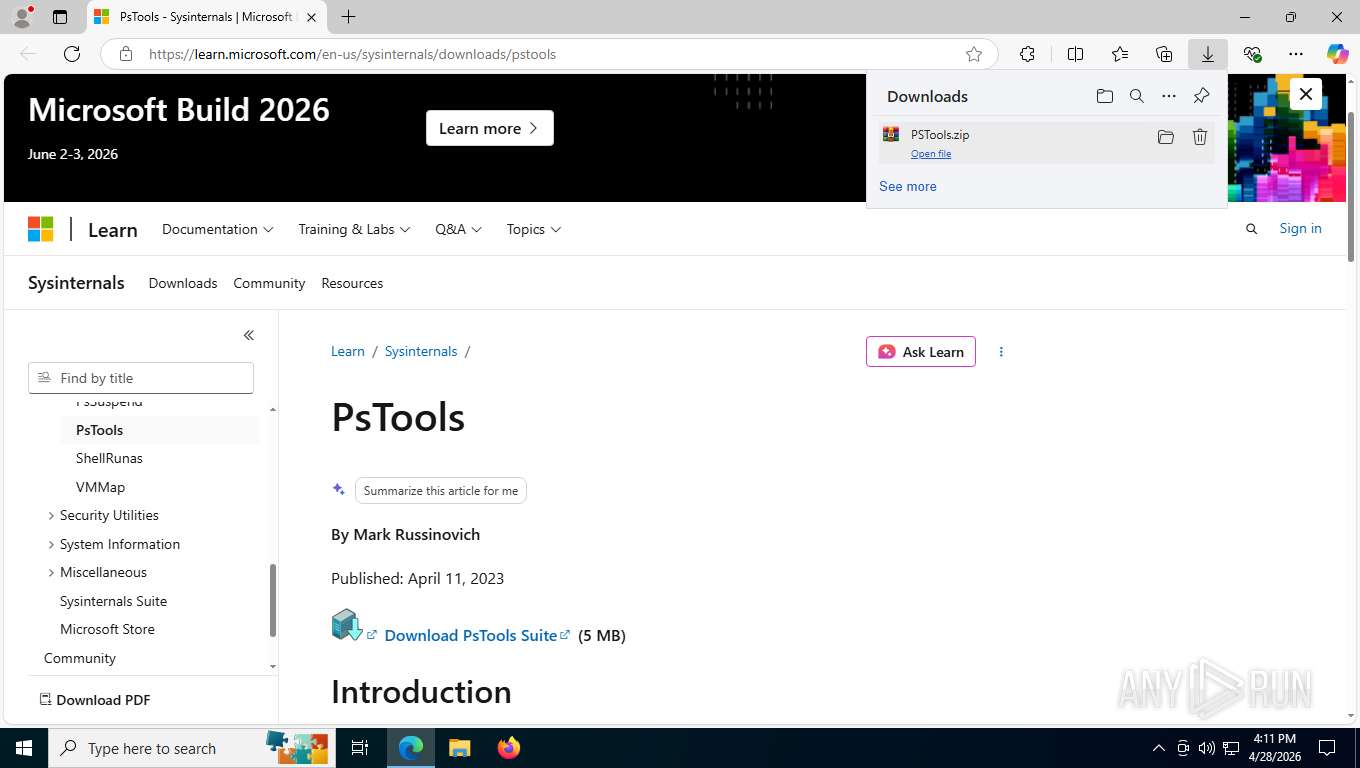
Launching a file from the Downloads directory
- msedge.exe (PID: 572)
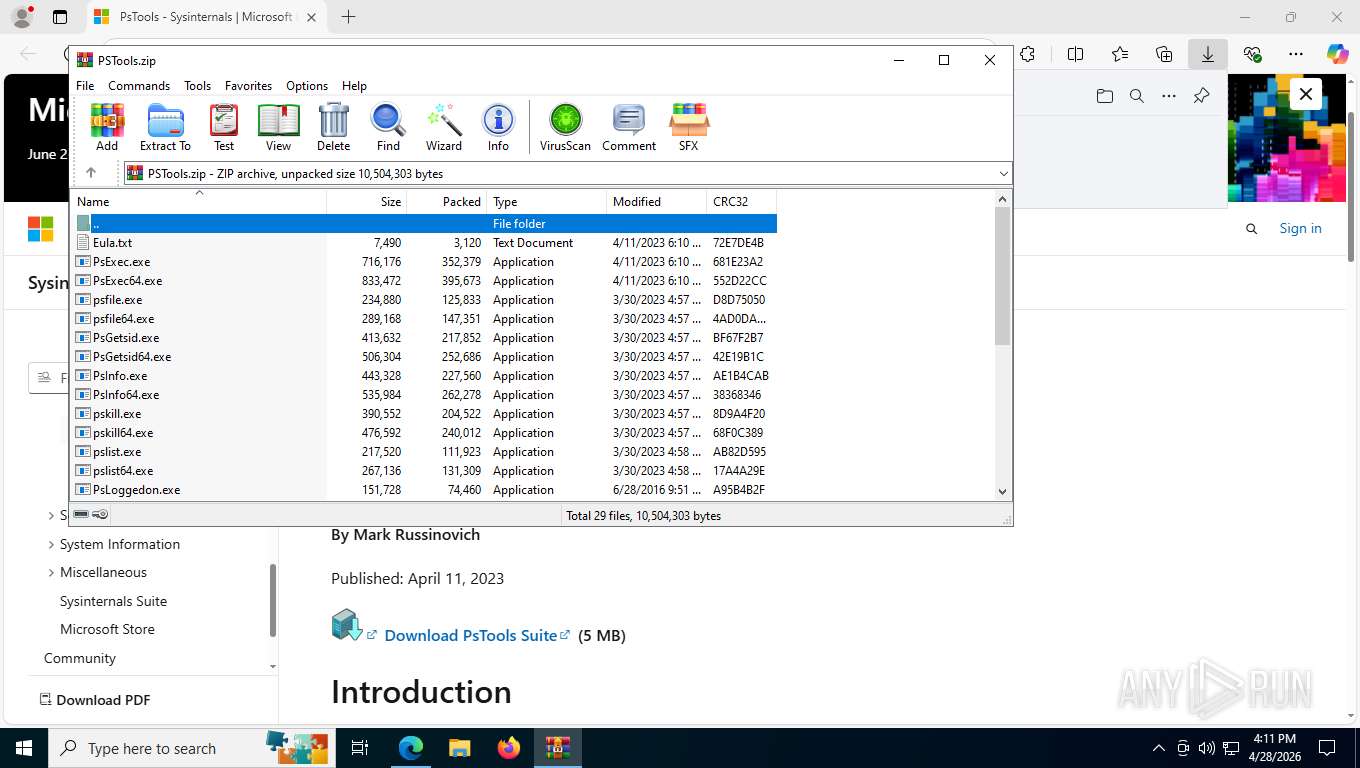
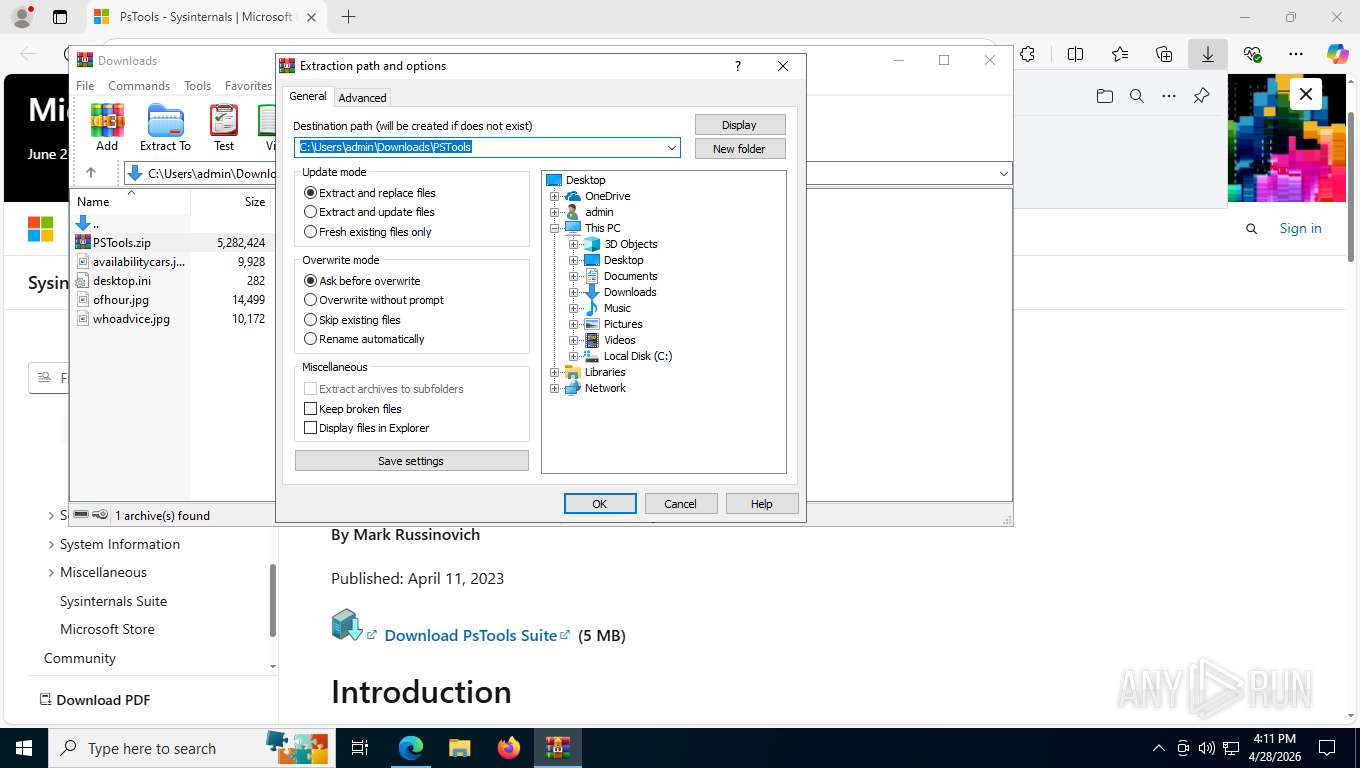
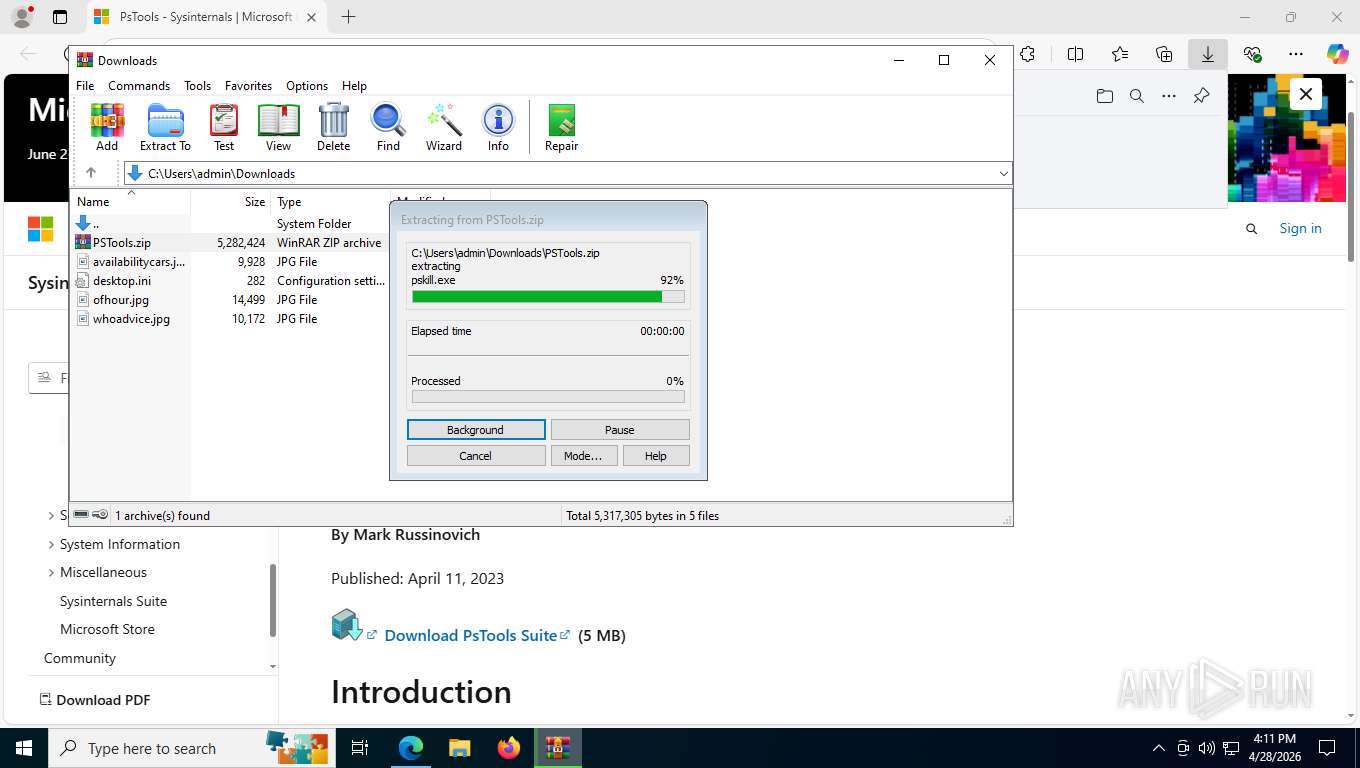
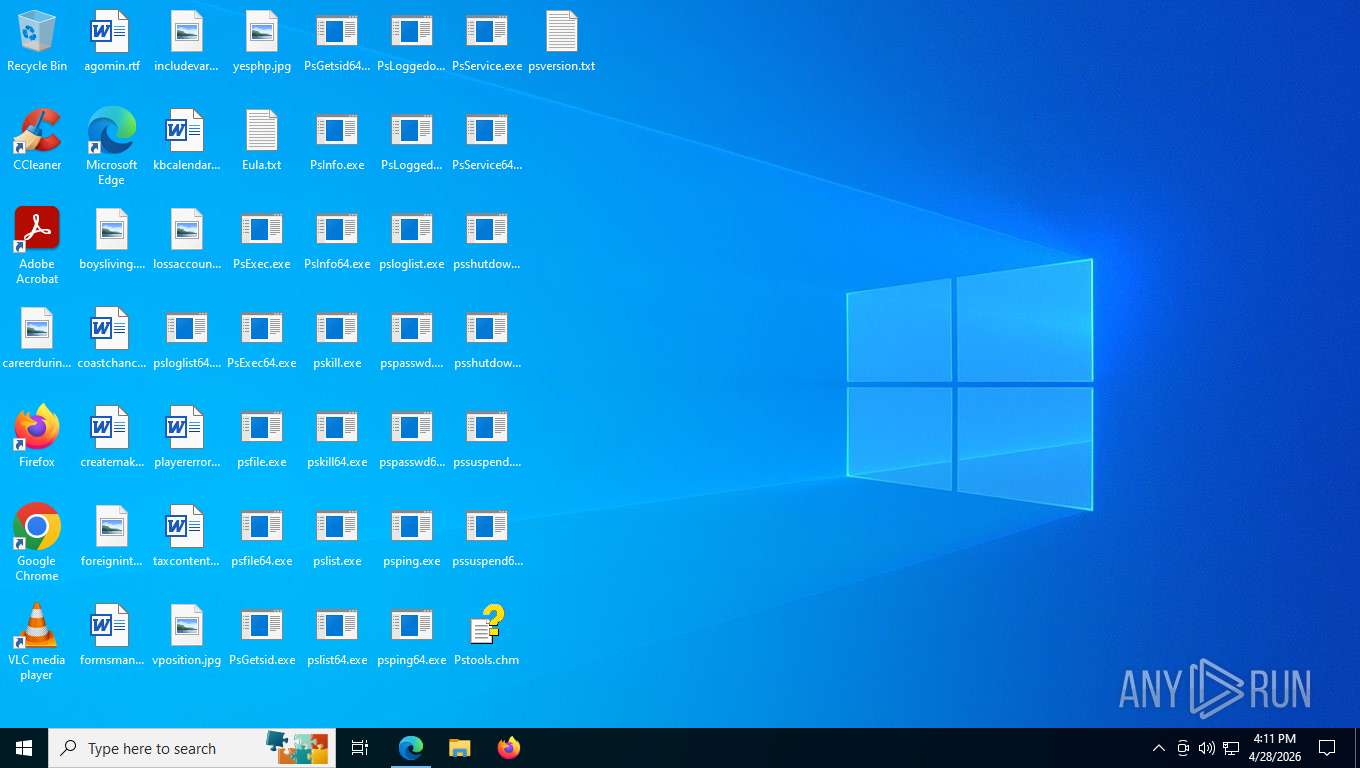
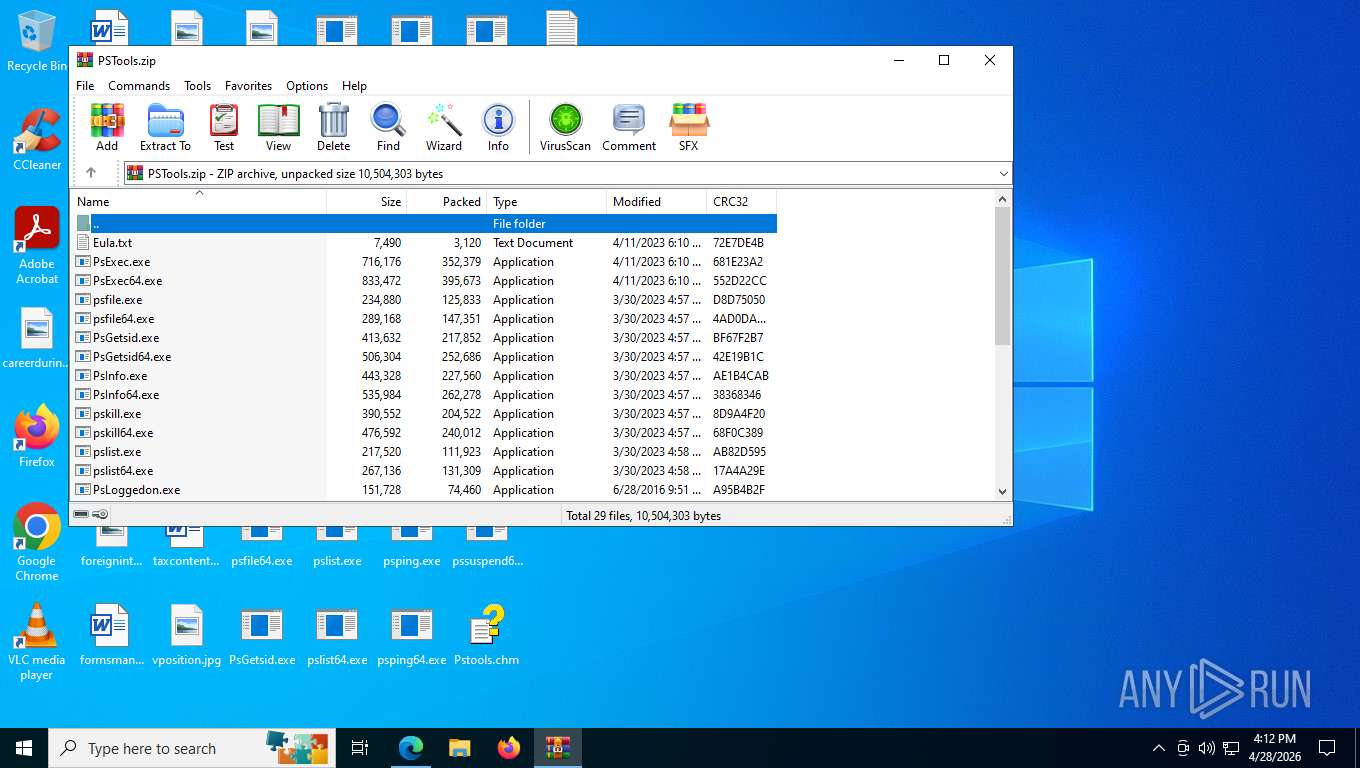
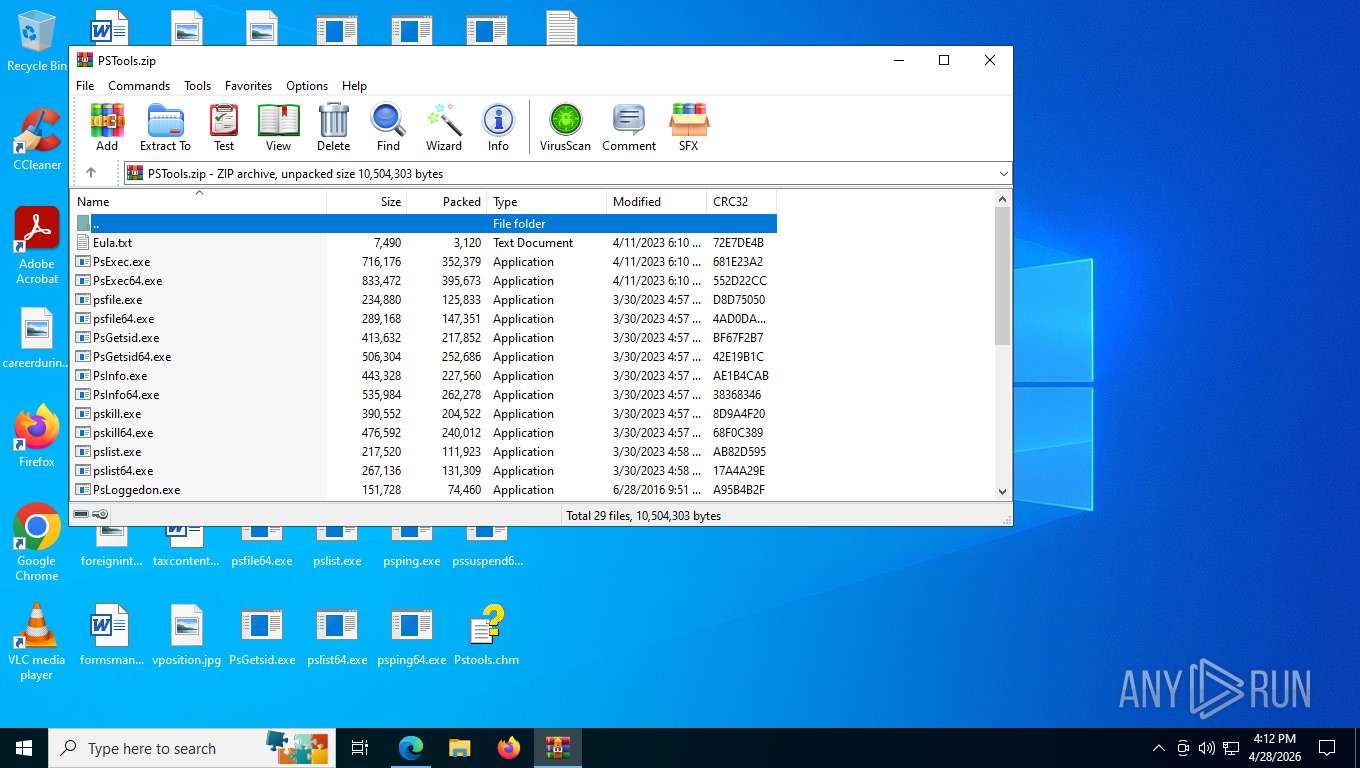
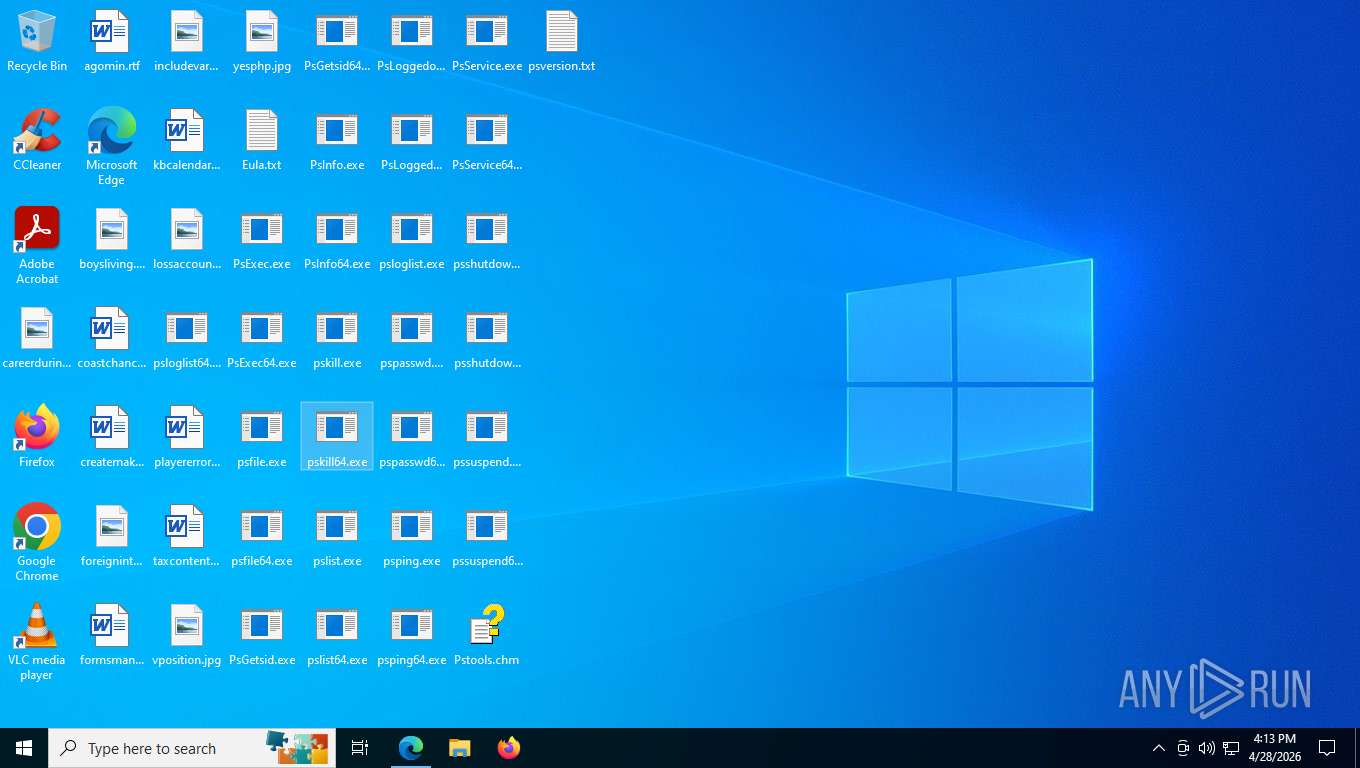
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8816)
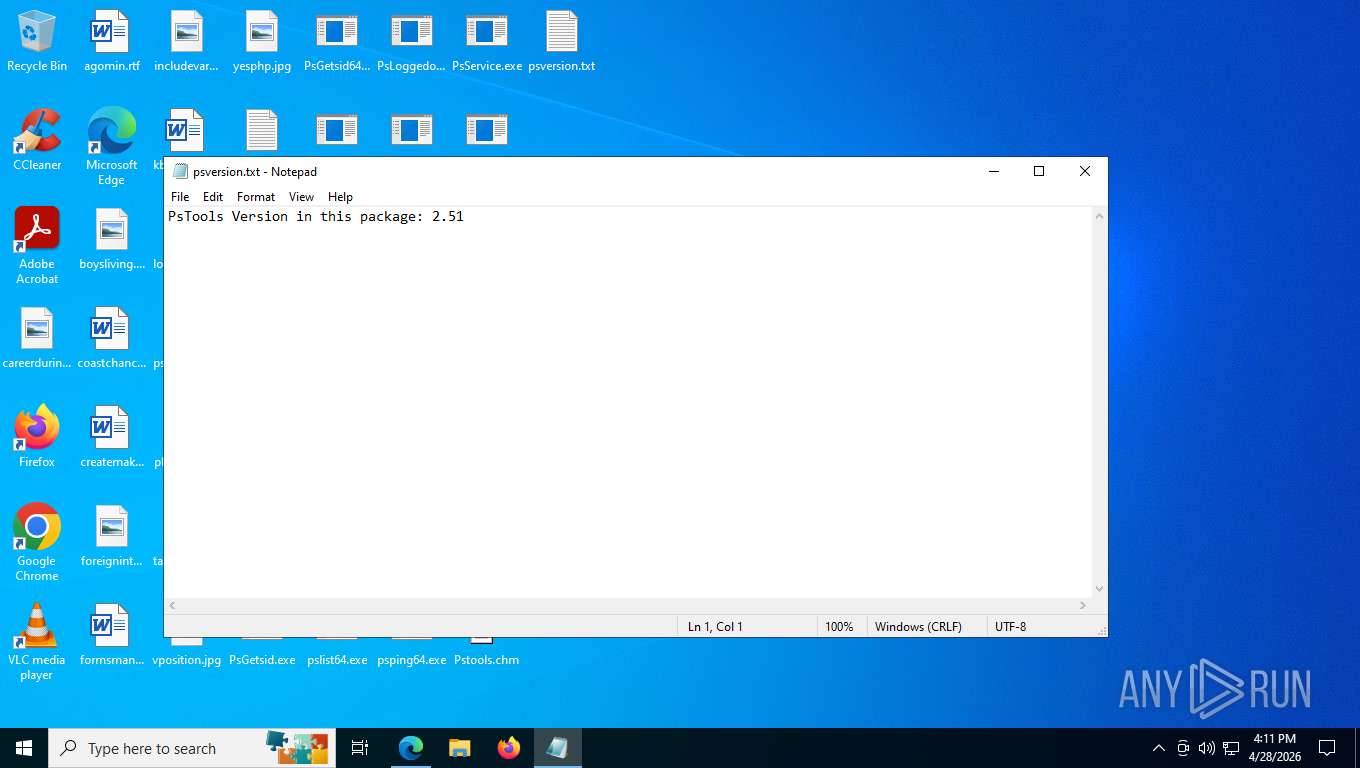
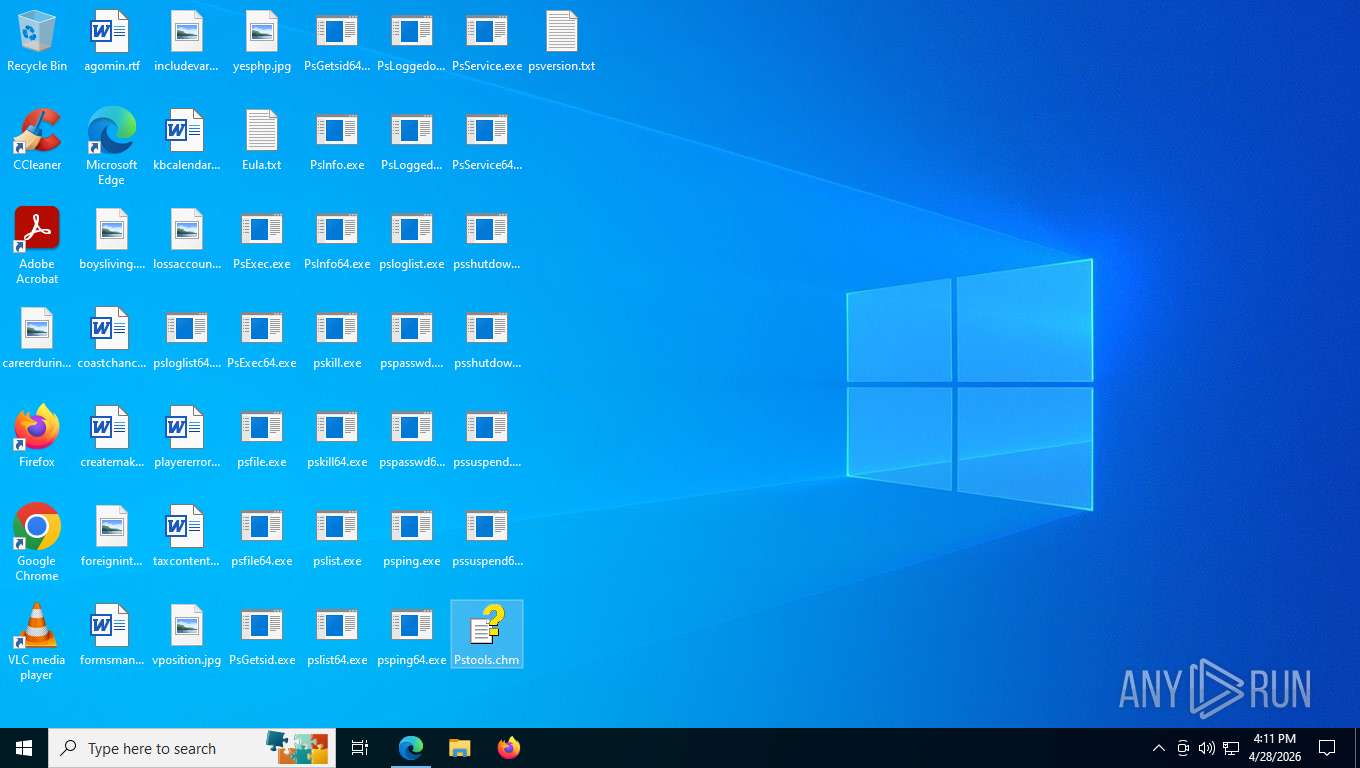
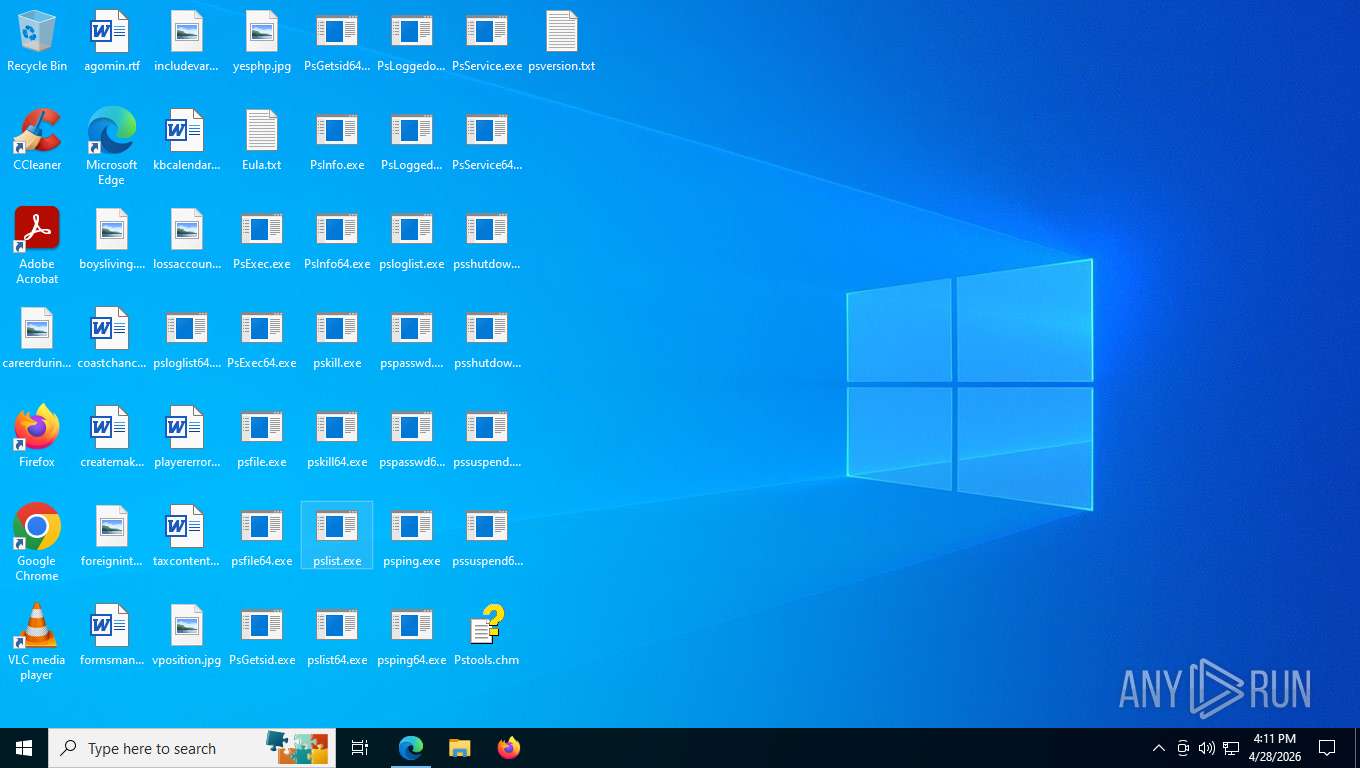
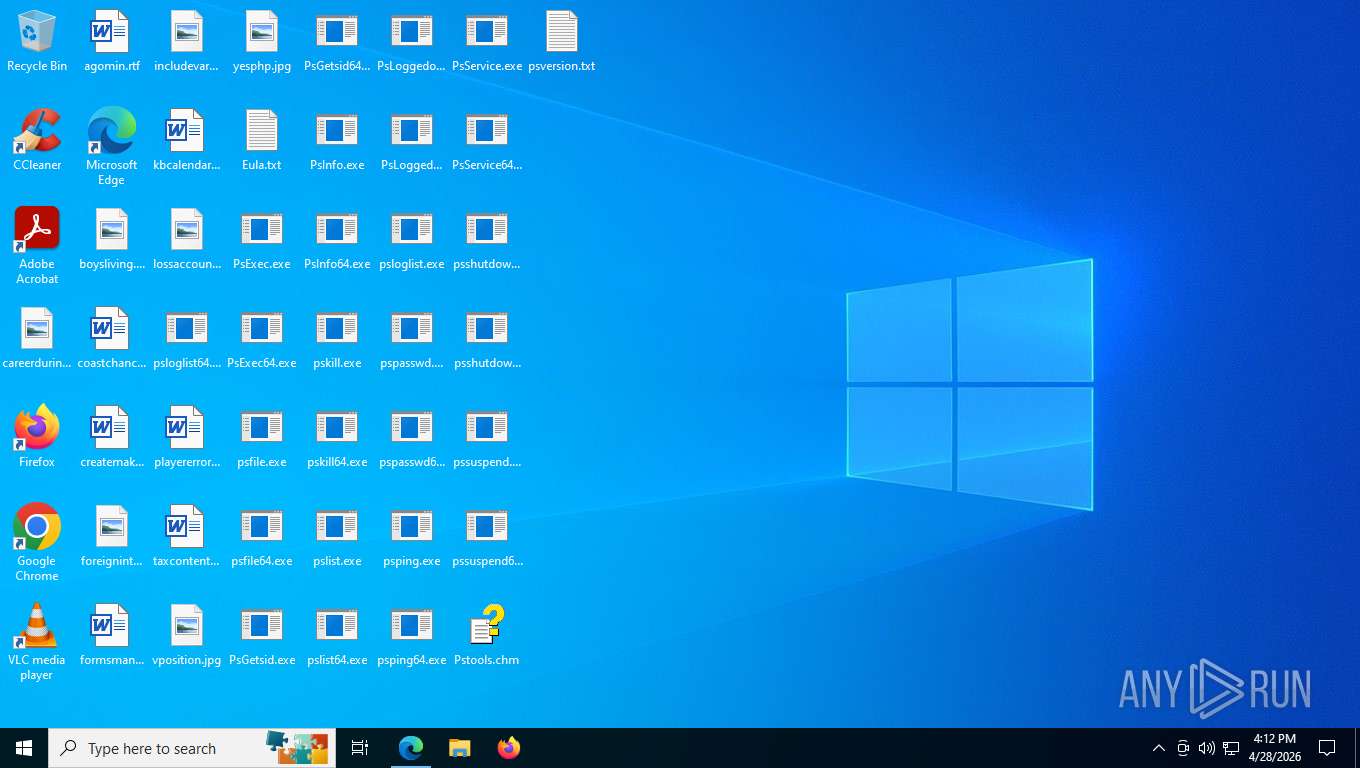
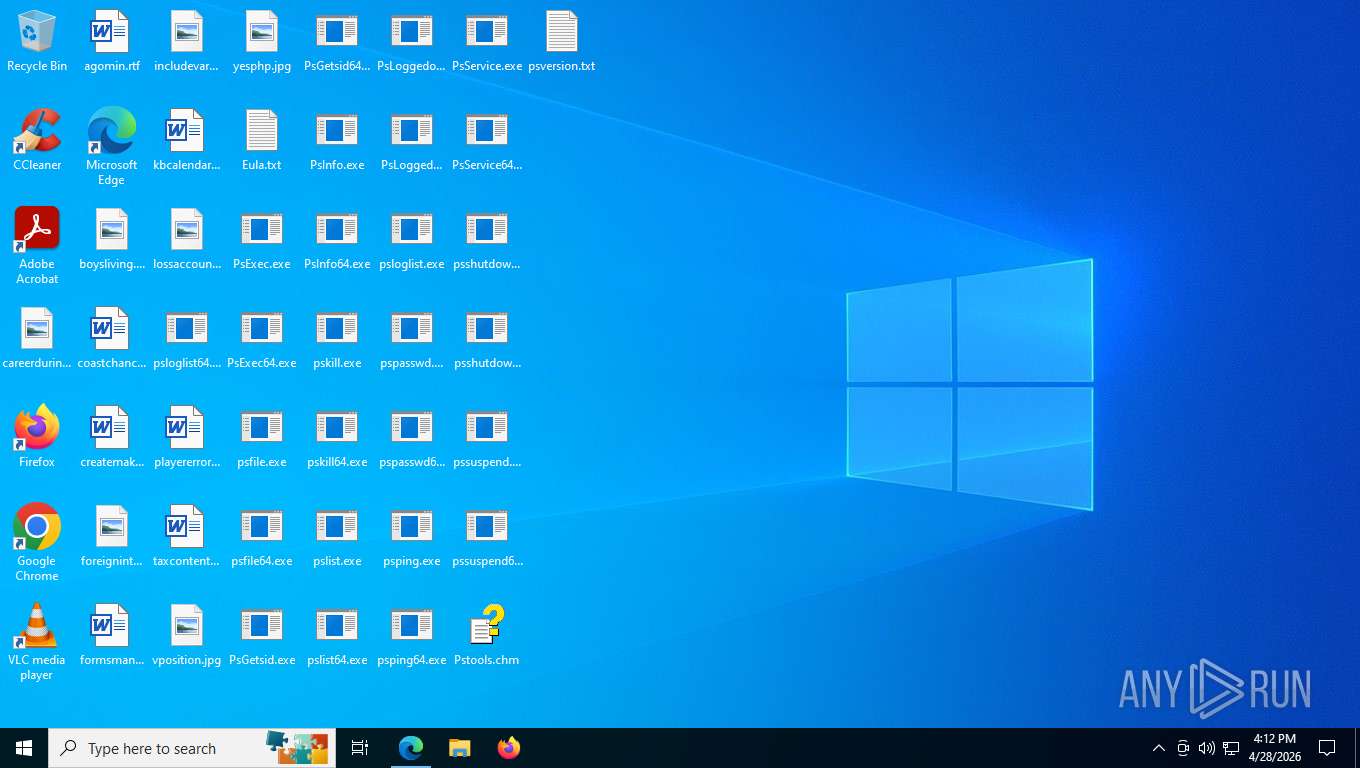
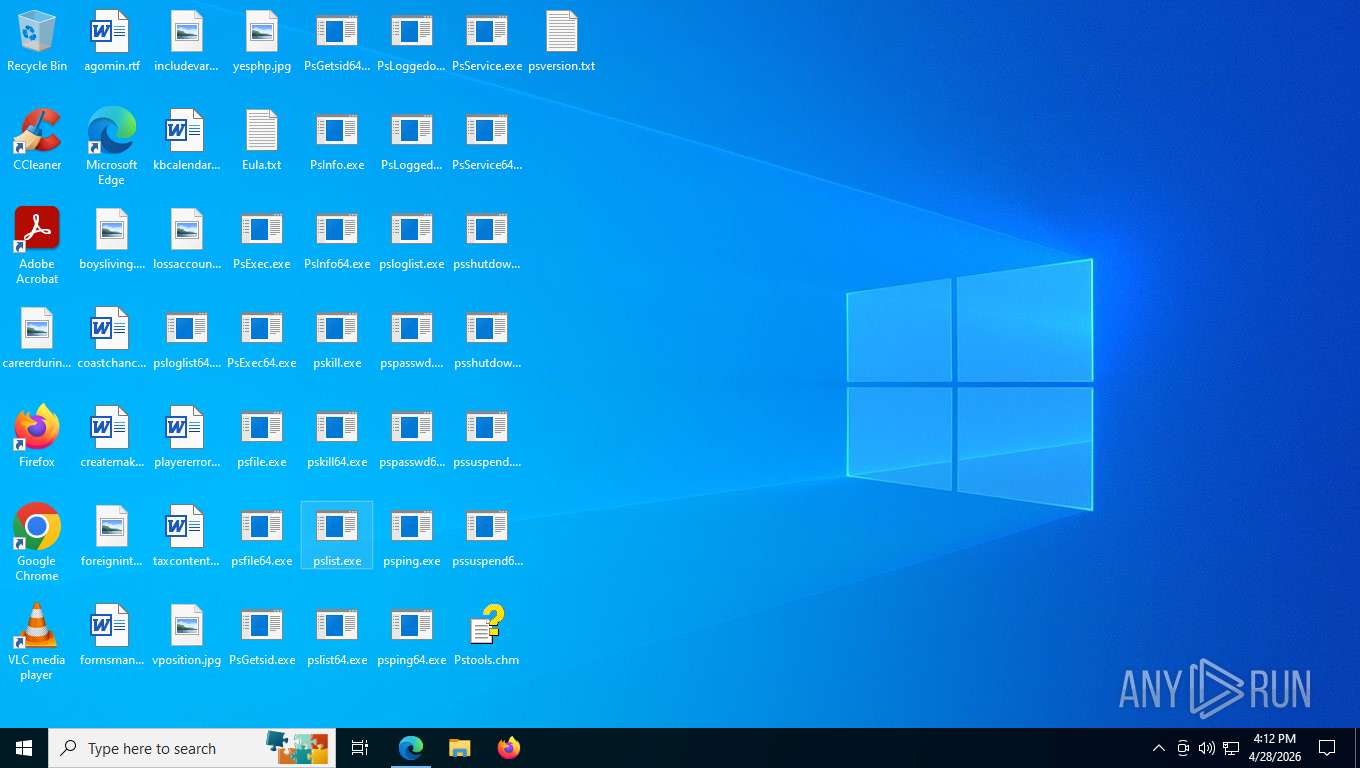
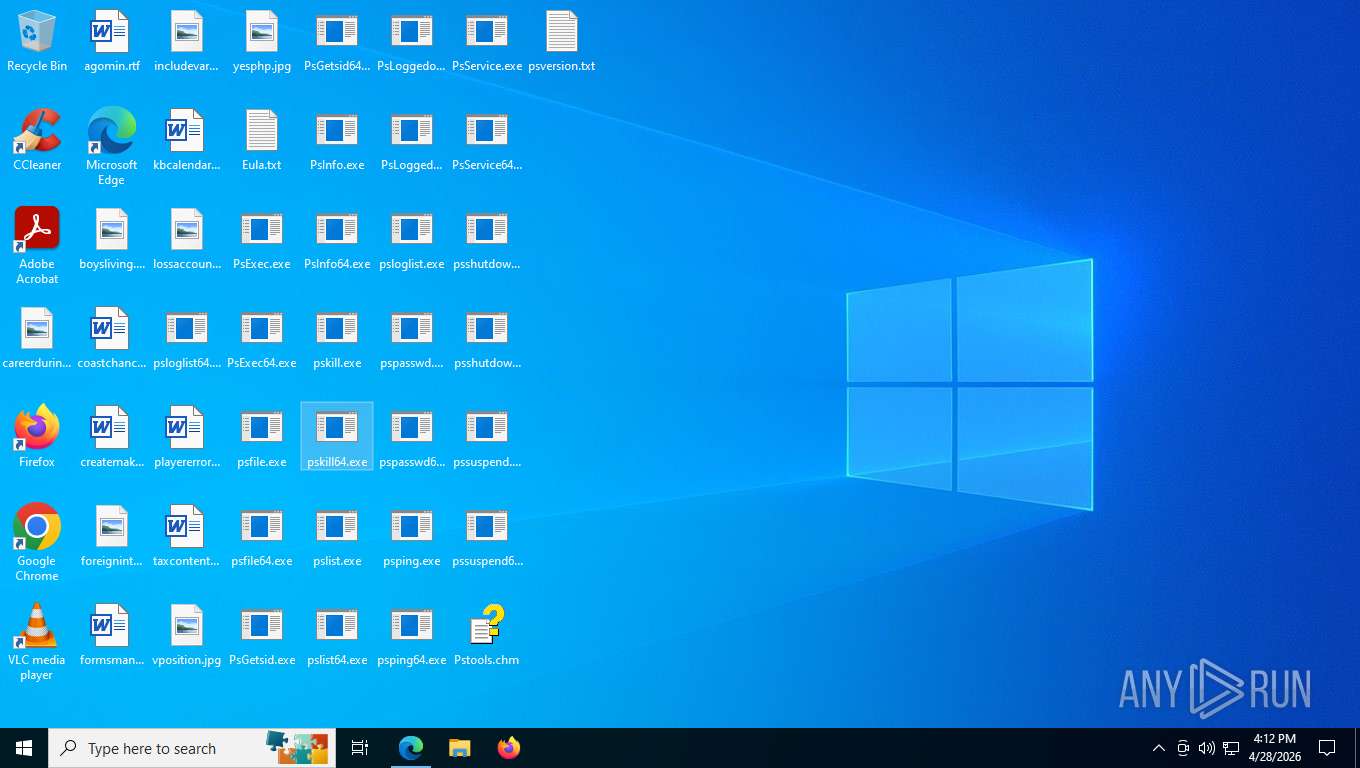
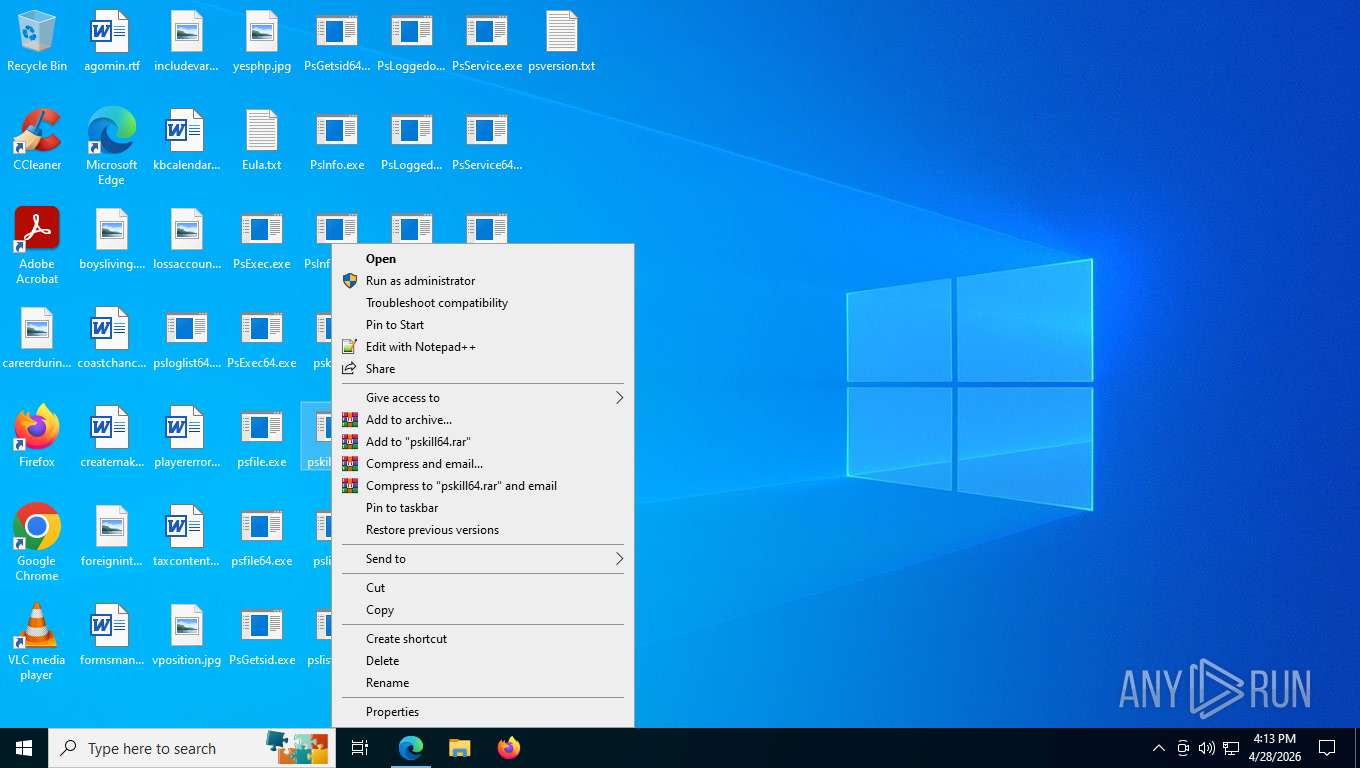
Manual execution by a user
- notepad.exe (PID: 9148)
- hh.exe (PID: 6408)
- pslist.exe (PID: 8828)
- PsExec.exe (PID: 5100)
- PsGetsid.exe (PID: 8220)
- PsExec.exe (PID: 8876)
- WinRAR.exe (PID: 7648)
- pskill64.exe (PID: 9192)
- pskill64.exe (PID: 8140)
- pskill64.exe (PID: 4944)
- PsLoggedon.exe (PID: 8416)
- pskill64.exe (PID: 1192)
- pskill64.exe (PID: 8496)
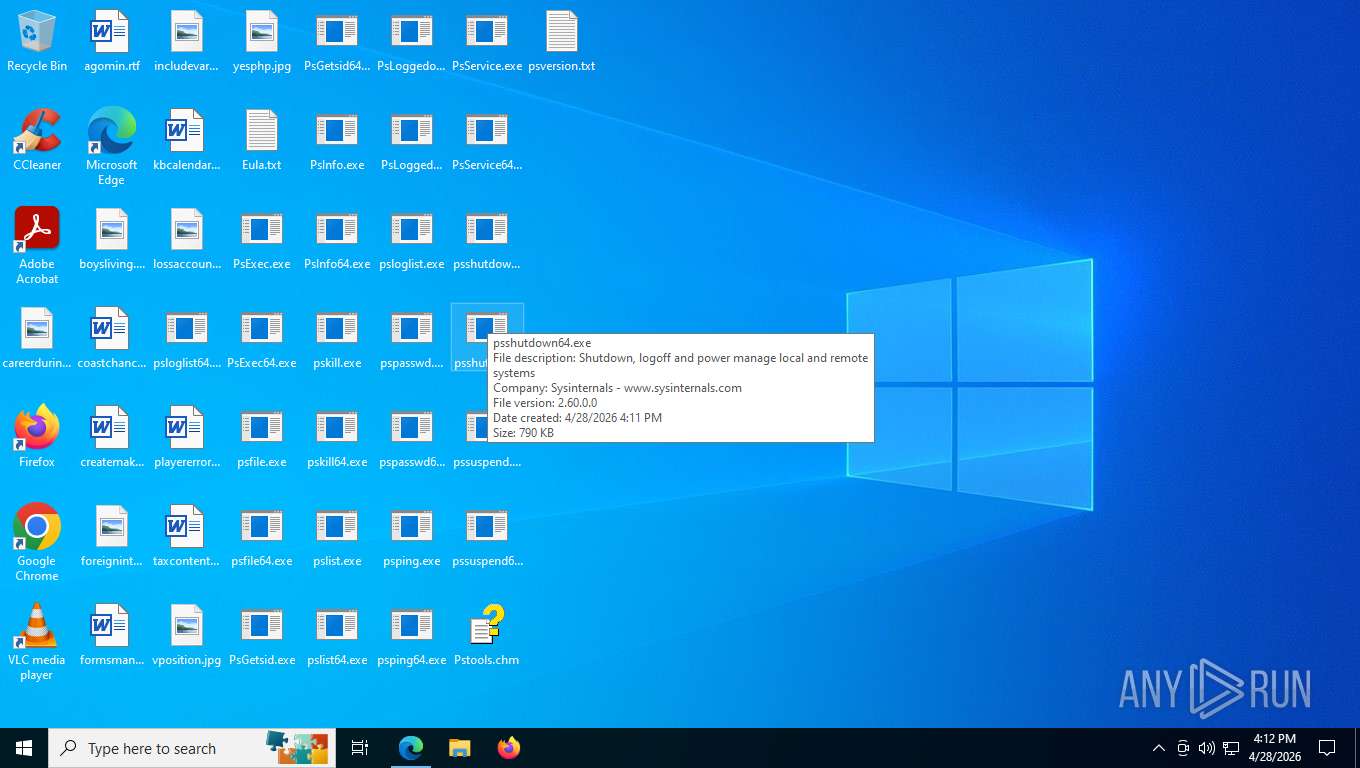
The sample compiled with english language support
- WinRAR.exe (PID: 8816)
- msedge.exe (PID: 1504)
- hh.exe (PID: 6408)
Reads security settings of Internet Explorer
- notepad.exe (PID: 9148)
- hh.exe (PID: 6408)
Creates files or folders in the user directory
- hh.exe (PID: 6408)
- WerFault.exe (PID: 3036)
Create files in a temporary directory
- hh.exe (PID: 6408)
Reads product name
- pskill64.exe (PID: 1192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
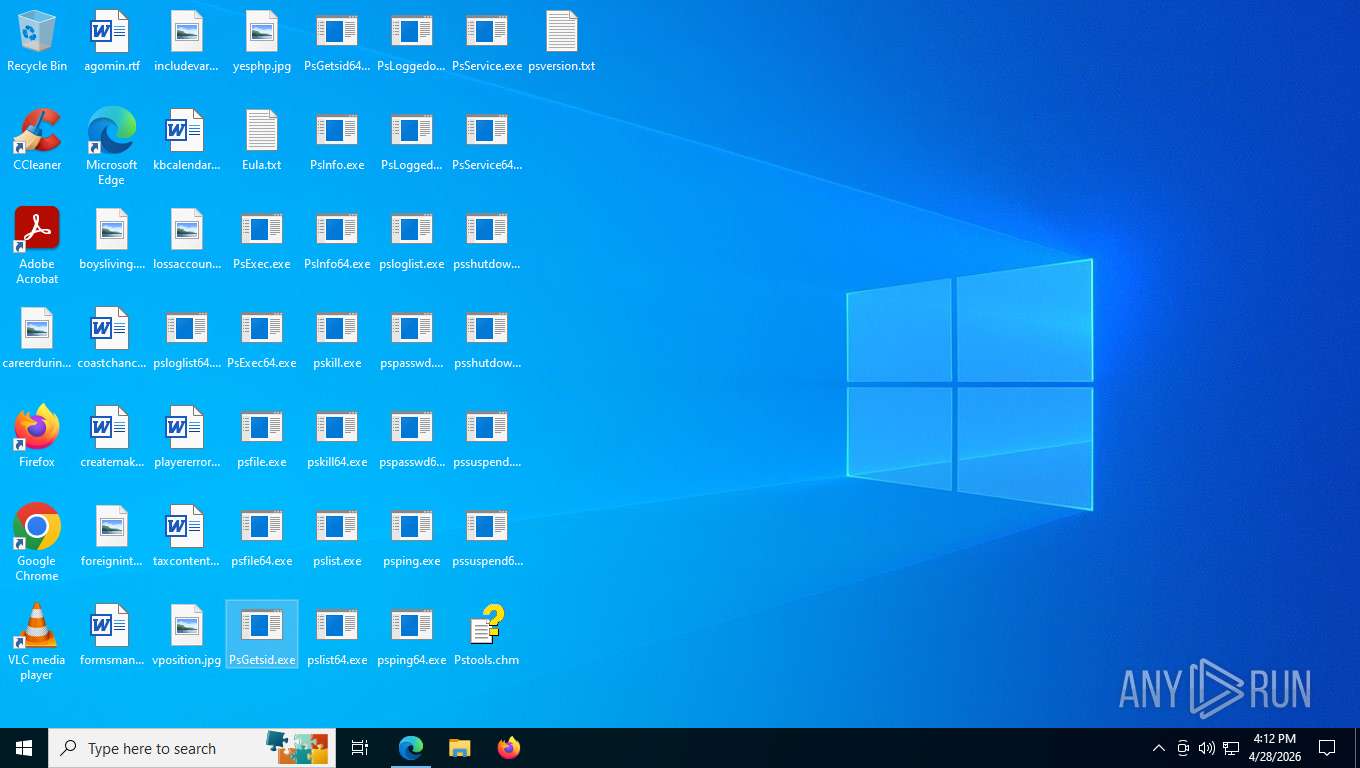
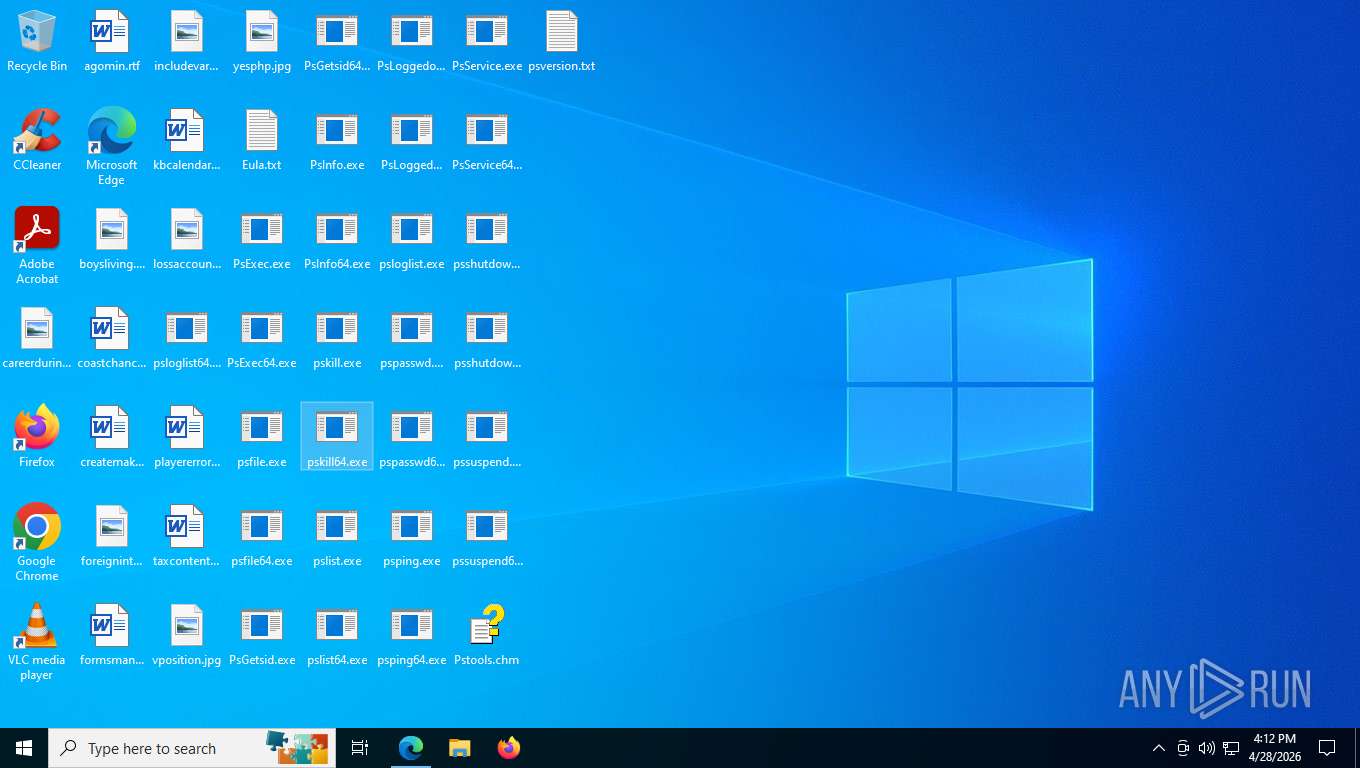
Total processes
202
Monitored processes
58
Malicious processes
3
Suspicious processes
7
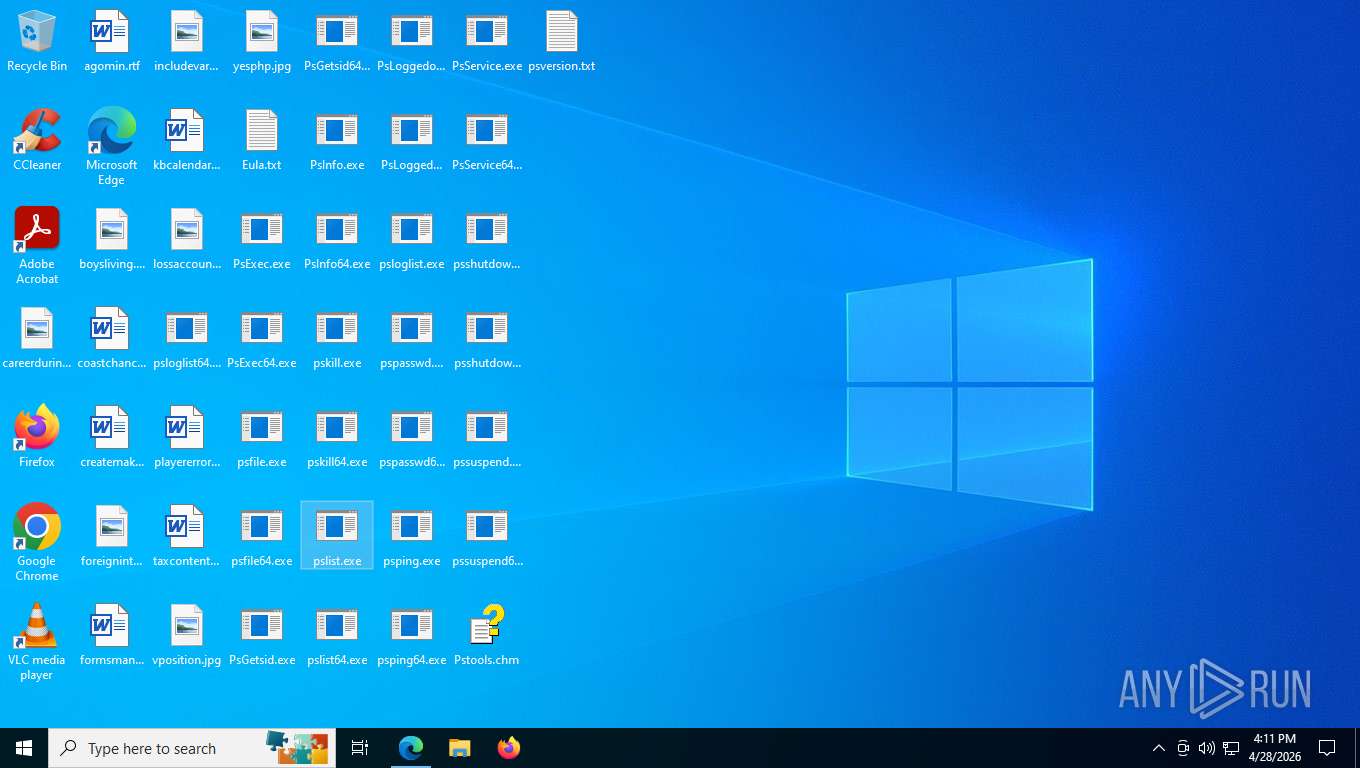
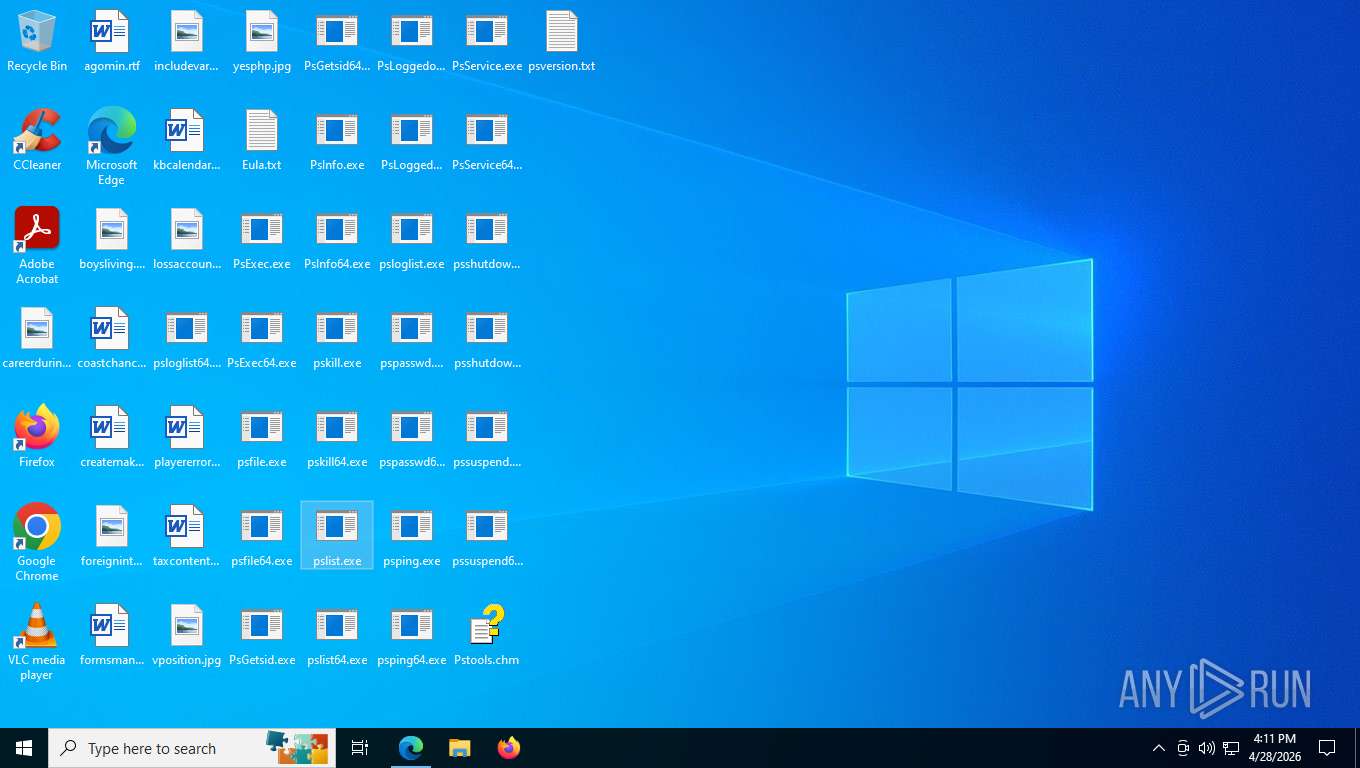
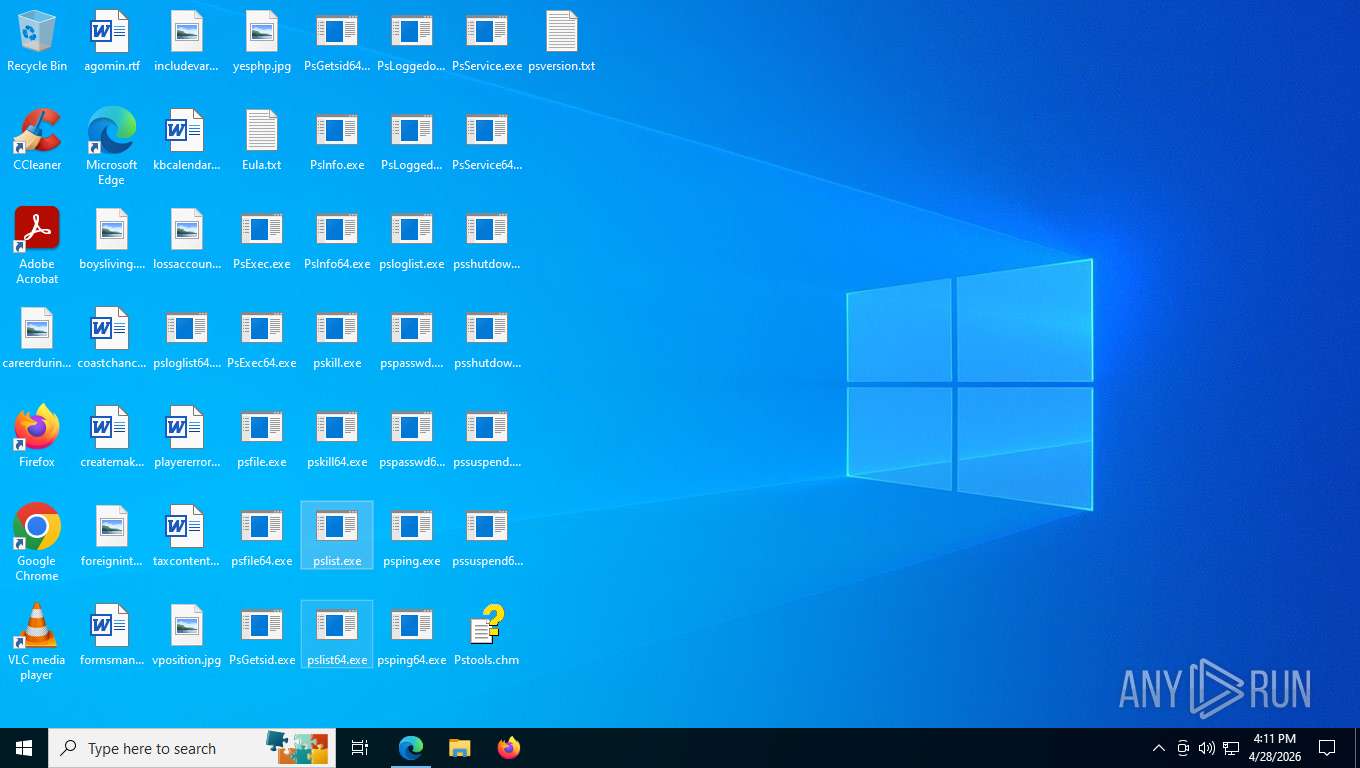
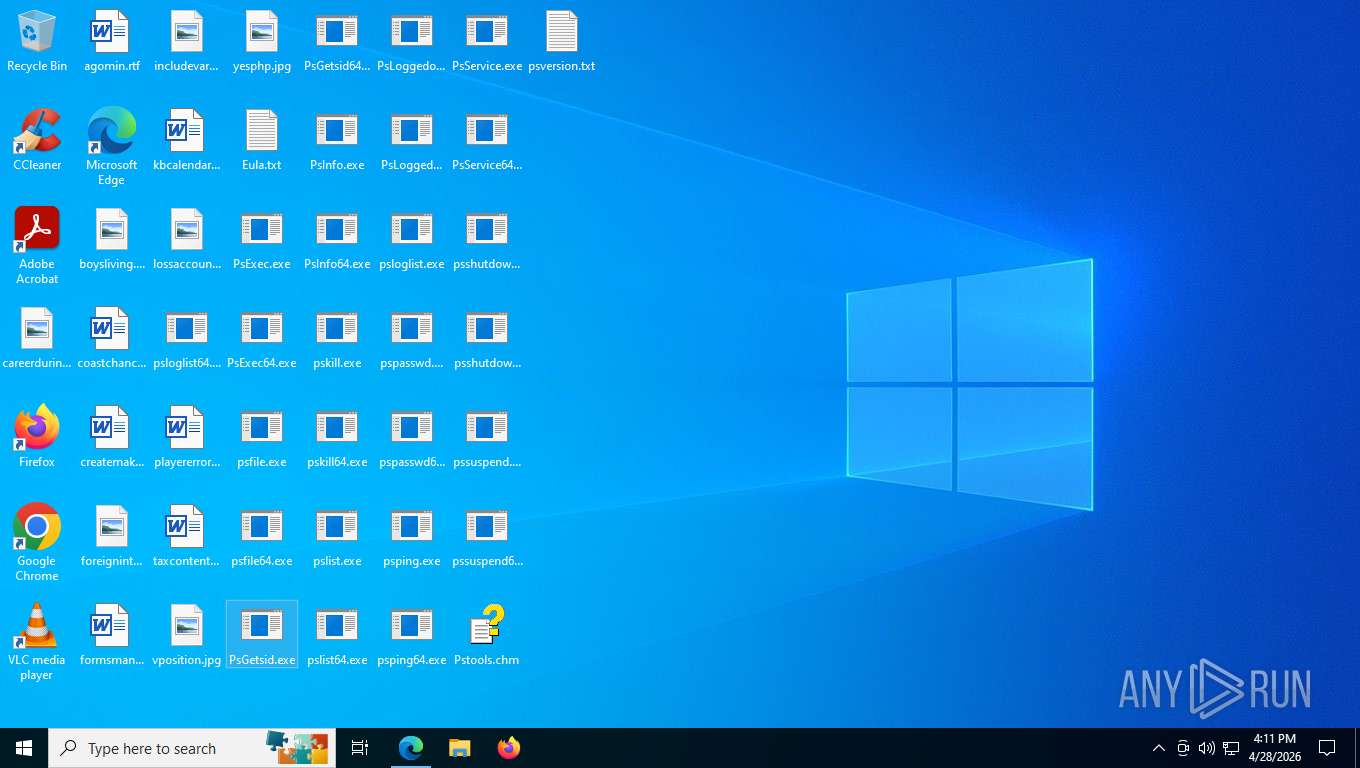
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --disable-features=HttpsUpgrades,HttpsFirstModeV2,HttpsOnlyMode,HttpsFirstBalancedMode --no-first-run --no-default-browser-check https://learn.microsoft.com/en-us/sysinternals/downloads/pstools | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4964,i,14150907173769180247,3782891758751853722,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4976 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | pskill64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
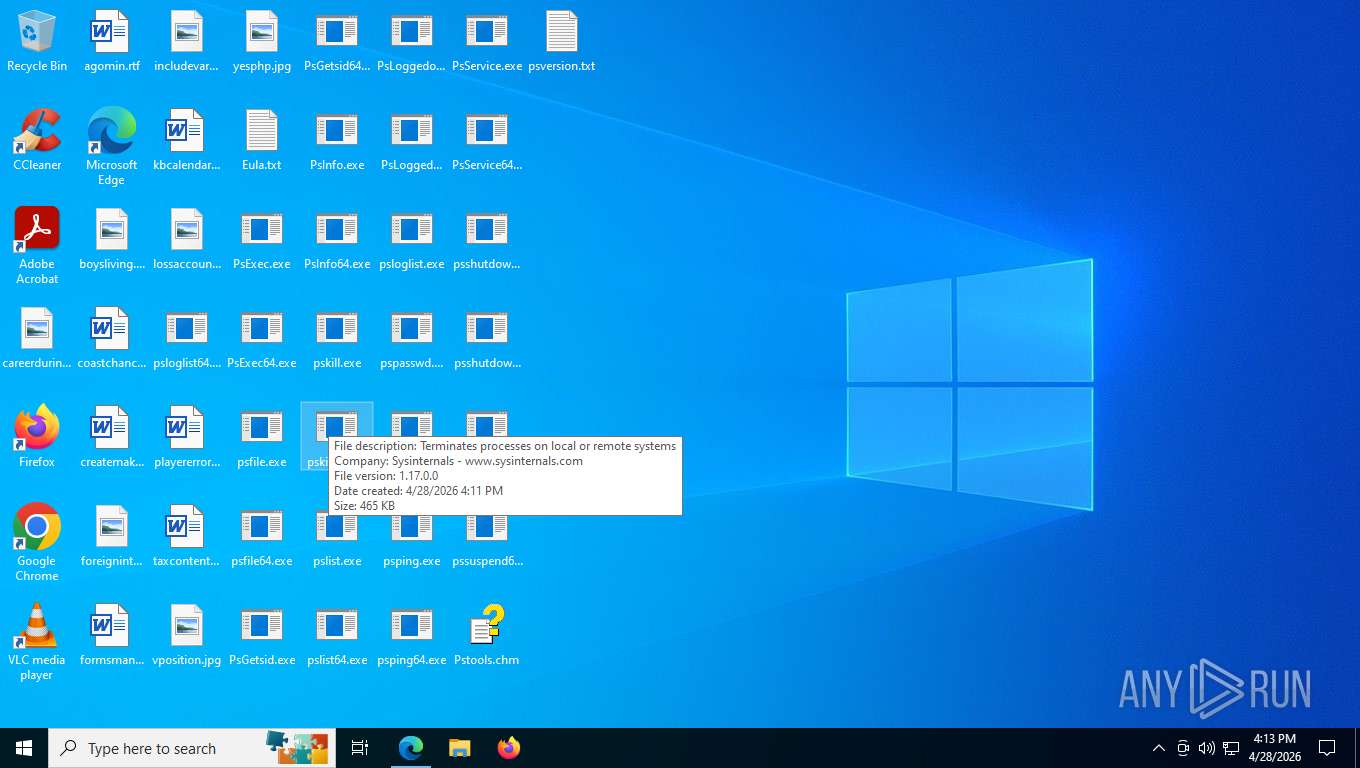
| 1192 | "C:\Users\admin\Desktop\pskill64.exe" | C:\Users\admin\Desktop\pskill64.exe | — | explorer.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Terminates processes on local or remote systems Exit code: 4294967295 Version: 1.17 Modules
| |||||||||||||||
| 1404 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3652,i,14150907173769180247,3782891758751853722,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3916 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1504 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1484,i,14150907173769180247,3782891758751853722,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2368 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3636,i,14150907173769180247,3782891758751853722,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3580 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2916 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5008,i,14150907173769180247,3782891758751853722,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5016 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3036 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 8416 -s 260 | C:\Windows\SysWOW64\WerFault.exe | PsLoggedon.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffe2392f208,0x7ffe2392f214,0x7ffe2392f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
9 771
Read events
9 703
Write events
53
Delete events
15
Modification events
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\PSTools.zip | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
37
Suspicious files
151
Text files
318
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFdff11.TMP | — | |
MD5:— | SHA256:— | |||
| 572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFdff11.TMP | — | |
MD5:— | SHA256:— | |||
| 572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFdff21.TMP | — | |
MD5:— | SHA256:— | |||
| 572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFdff21.TMP | — | |
MD5:— | SHA256:— | |||
| 572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFdff30.TMP | — | |
MD5:— | SHA256:— | |||
| 572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
301
TCP/UDP connections
88
DNS requests
99
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 313 b | whitelisted |
1504 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:1pijzheGezcGpqjMXQjWAogN1t9h6c-z77xj6FE4zYw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 99 b | whitelisted |
1504 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 132 b | whitelisted |
1504 | msedge.exe | GET | 200 | 23.52.181.208:443 | https://learn.microsoft.com/_themes/docs.theme/master/en-us/_themes/global/deprecation.js | US | text | 1.40 Kb | whitelisted |
1504 | msedge.exe | GET | 200 | 23.52.181.208:443 | https://learn.microsoft.com/static/assets/0.4.03403.7766-505fcacb/styles/site.css | US | text | 454 Kb | whitelisted |
1504 | msedge.exe | GET | 200 | 23.52.181.208:443 | https://learn.microsoft.com/static/assets/0.4.03403.7766-505fcacb/scripts/en-us/index-docs.js | US | text | 1.77 Mb | whitelisted |
1504 | msedge.exe | GET | 200 | 23.52.181.208:443 | https://learn.microsoft.com/en-us/sysinternals/downloads/media/shared/download_sm.png | US | image | 2.23 Kb | whitelisted |
1504 | msedge.exe | GET | 200 | 52.123.243.75:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.28 Kb | whitelisted |
1504 | msedge.exe | GET | 200 | 150.171.109.194:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
1504 | msedge.exe | POST | 200 | 23.52.181.208:443 | https://learn.microsoft.com/api/recommendations/3c7e82b0-7a93-5a0a-6e13-c073ce540b54/batch | US | text | 394 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6792 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 92.123.104.50:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
1504 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1504 | msedge.exe | 52.123.243.75:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
learn.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6792 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |