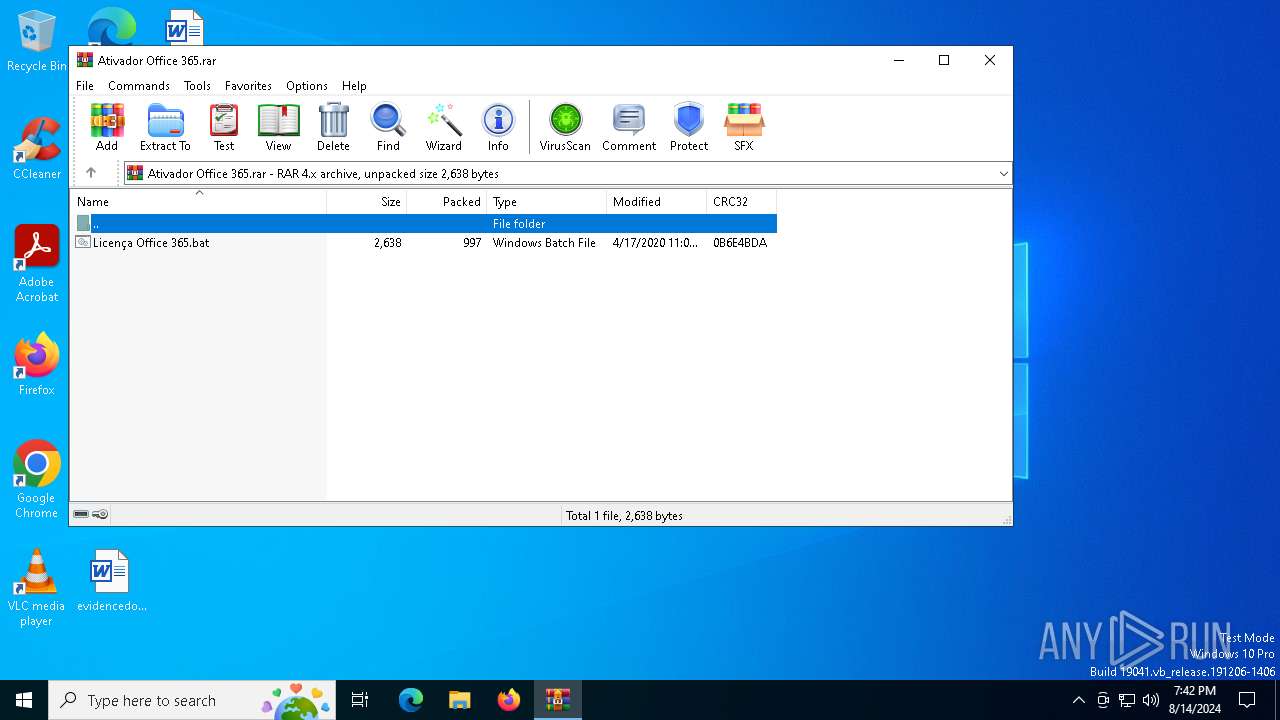
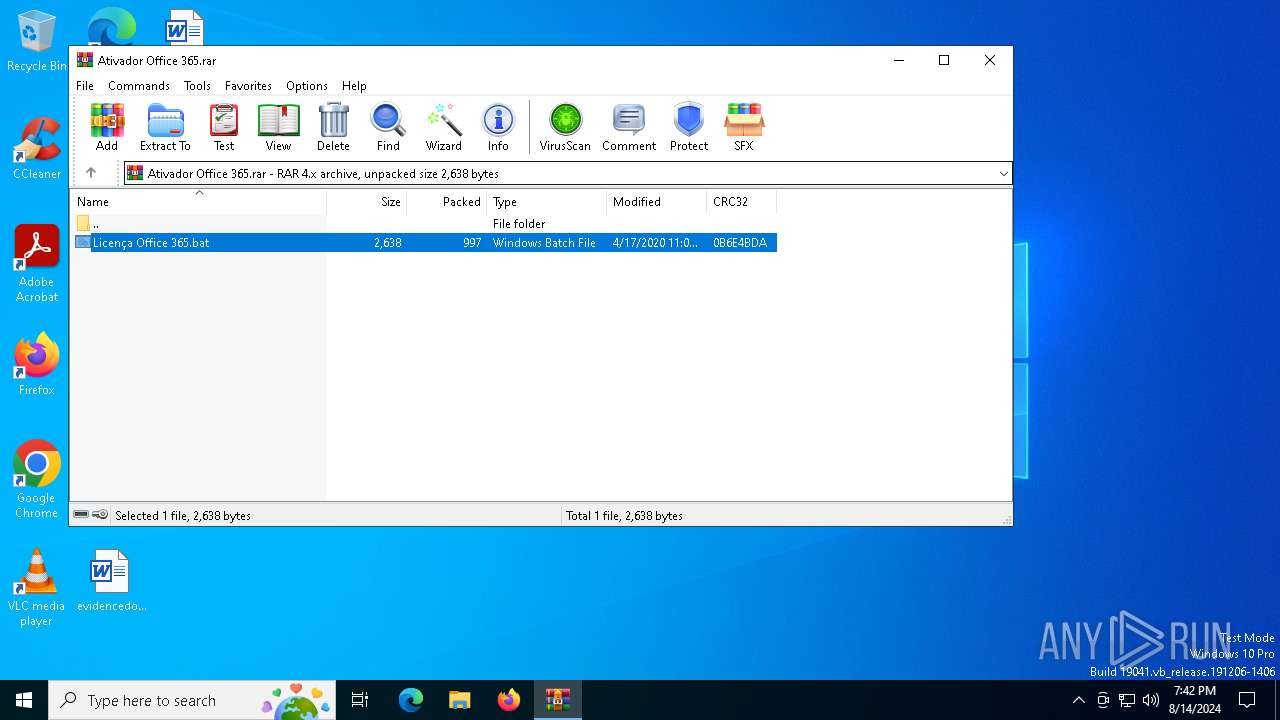
| File name: | Ativador Office 365.rar |
| Full analysis: | https://app.any.run/tasks/902a68c8-a593-4796-ad96-c00d9d2c651c |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2024, 19:41:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | ED9B00E639EFCF0D0A183E8F4AA57485 |
| SHA1: | BFC4898BCBD5E52D3460E6217C22DB77FF3CE4CC |
| SHA256: | 8E08ACD804BDE4BD54305CED3B8D0FE7E217FC4ED301173A24D82E13996345E8 |
| SSDEEP: | 24:hCWKECtekHuBuX1EucRYuCKwmTZXm6fQRDIG5zVnh/AAdY90uWQ:YWKtZHuBA1vmTCK1TZmEG5zFpndYCg |
MALICIOUS
No malicious indicators.SUSPICIOUS
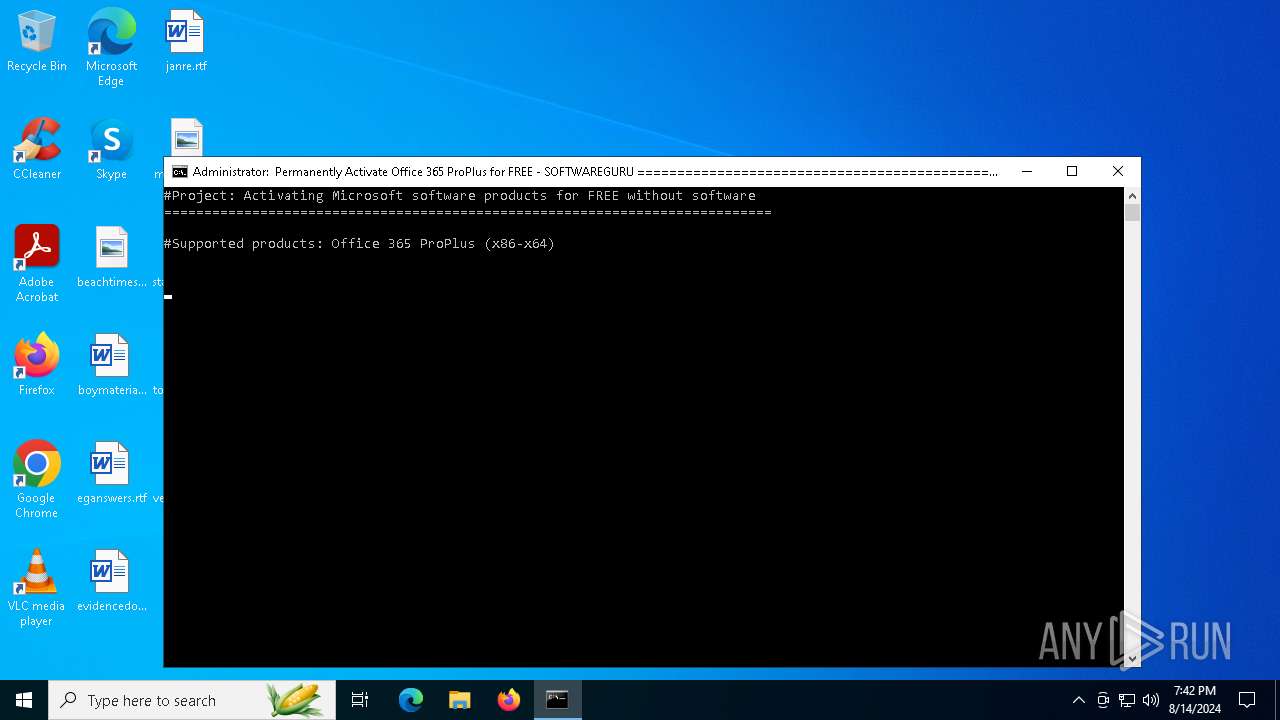
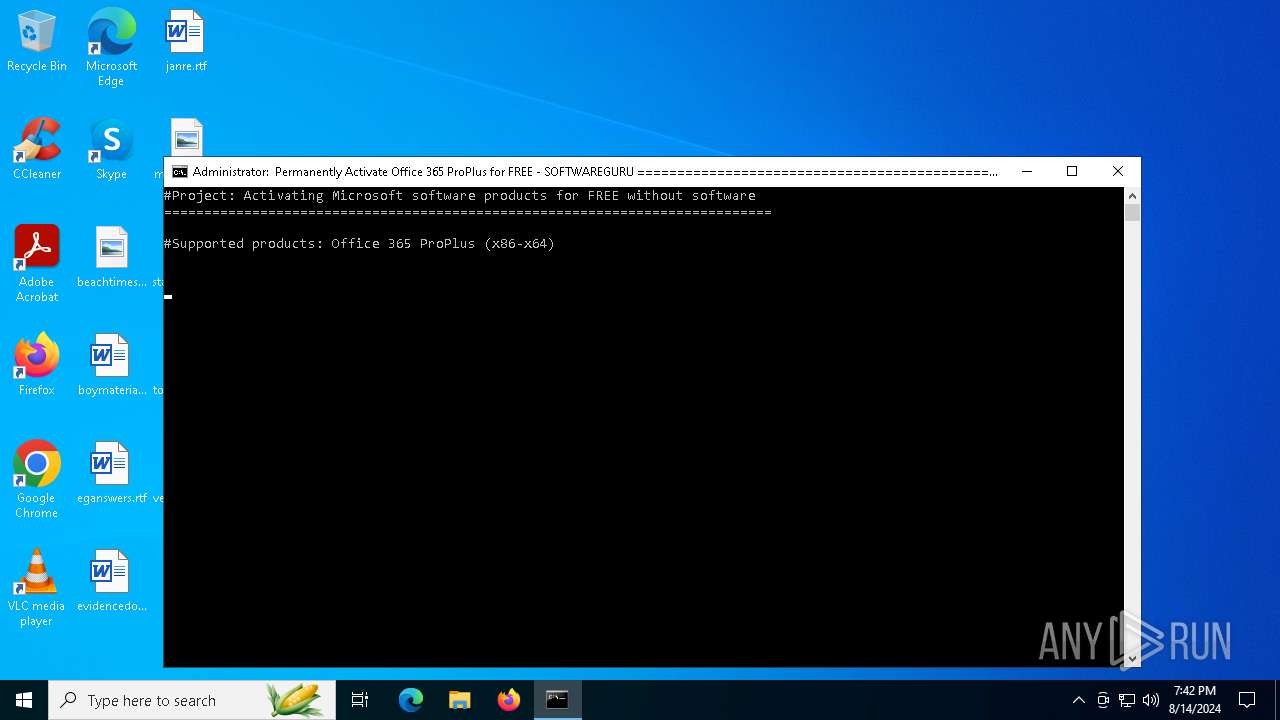
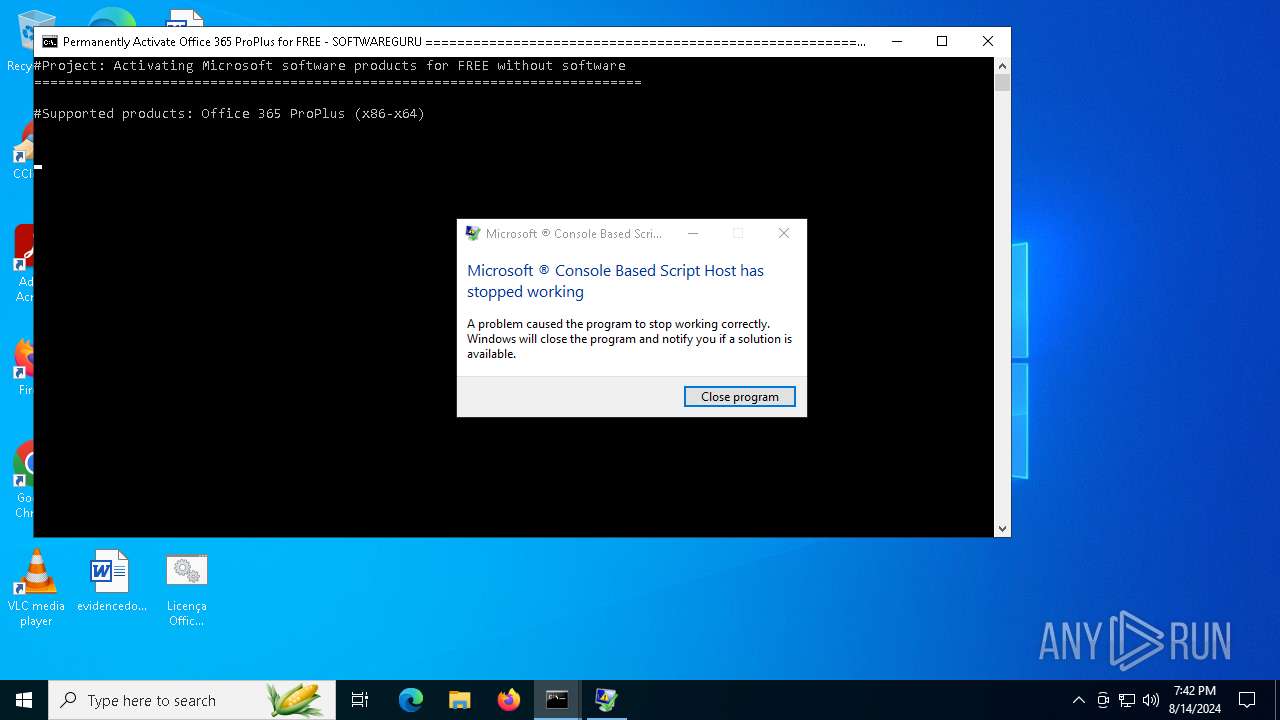
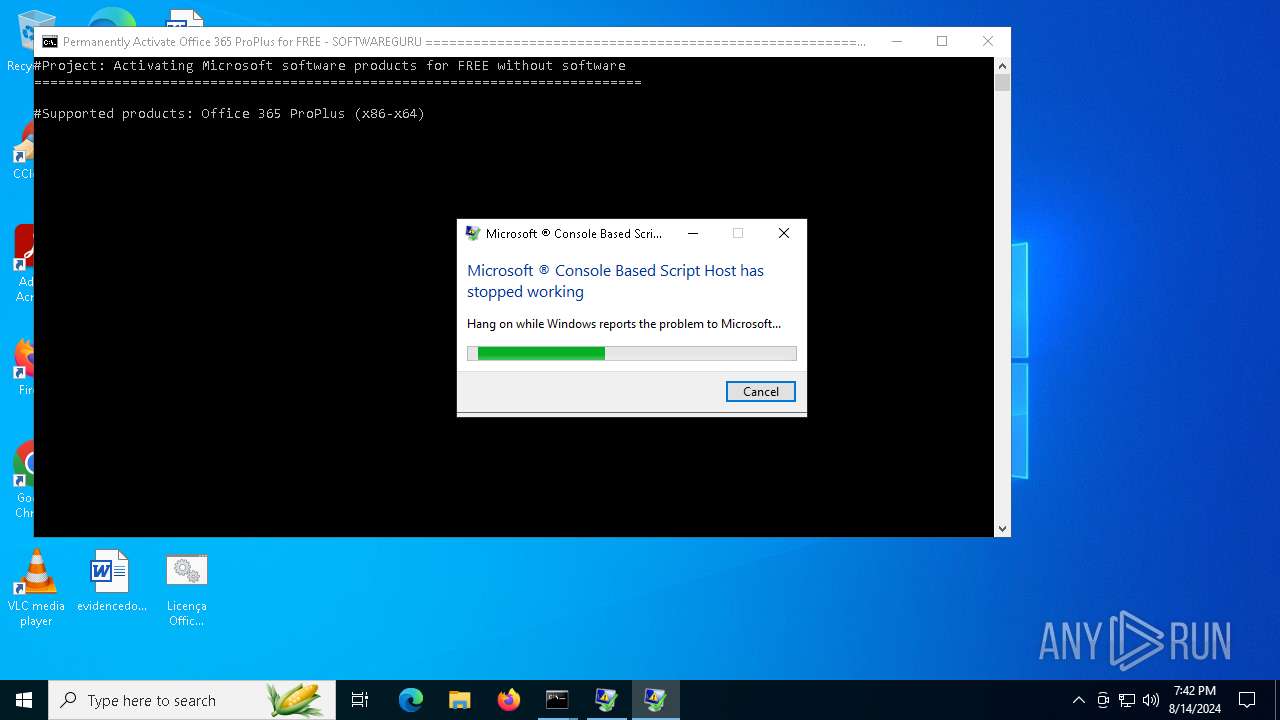
The process executes VB scripts
- cmd.exe (PID: 7044)
- cmd.exe (PID: 6936)
Application launched itself
- cmd.exe (PID: 7044)
- cmd.exe (PID: 6936)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 5880)
- cscript.exe (PID: 6372)
- cscript.exe (PID: 6260)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7044)
- cmd.exe (PID: 6936)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 5880)
- cscript.exe (PID: 6372)
- cscript.exe (PID: 6260)
Gets a collection of all available drive names (SCRIPT)
- cscript.exe (PID: 5880)
- cscript.exe (PID: 6372)
- cscript.exe (PID: 6260)
Accesses computer name via WMI (SCRIPT)
- cscript.exe (PID: 5880)
- cscript.exe (PID: 6372)
- cscript.exe (PID: 6260)
Gets the drive type (SCRIPT)
- cscript.exe (PID: 5880)
- cscript.exe (PID: 6372)
- cscript.exe (PID: 6260)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- cscript.exe (PID: 5880)
- cscript.exe (PID: 6372)
- cscript.exe (PID: 6260)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 5880)
- cscript.exe (PID: 6372)
- cscript.exe (PID: 6260)
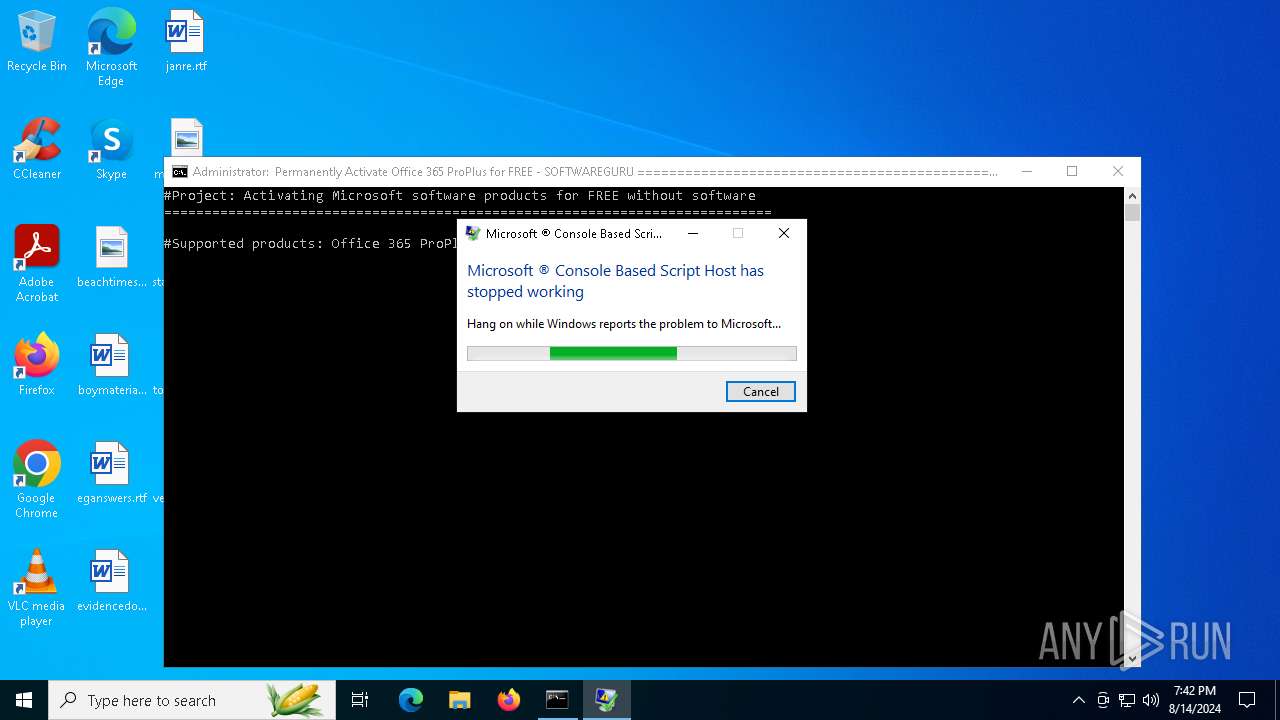
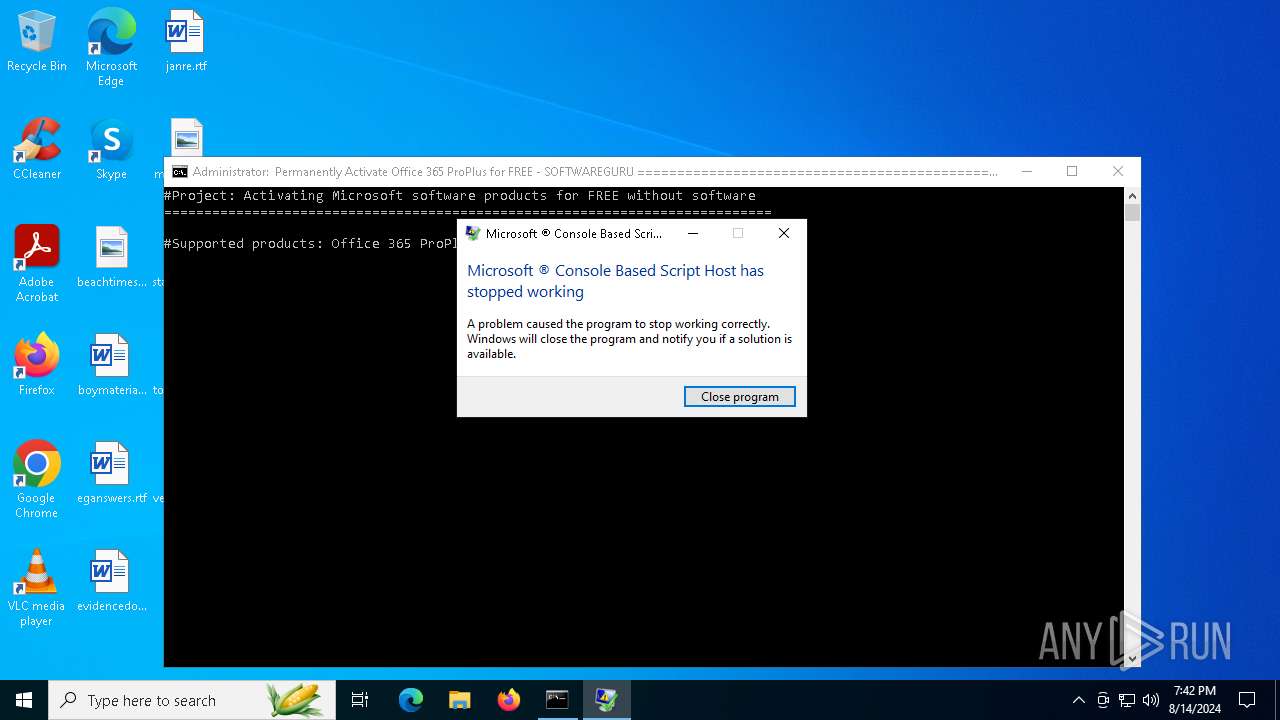
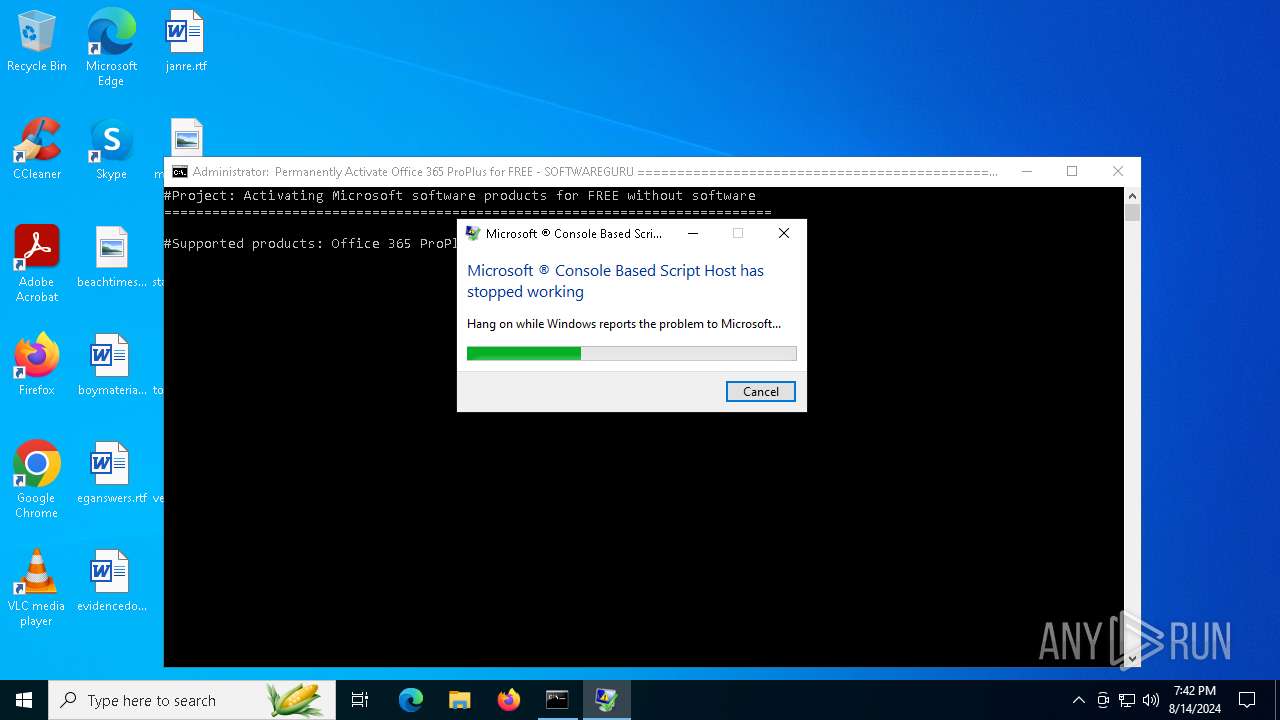
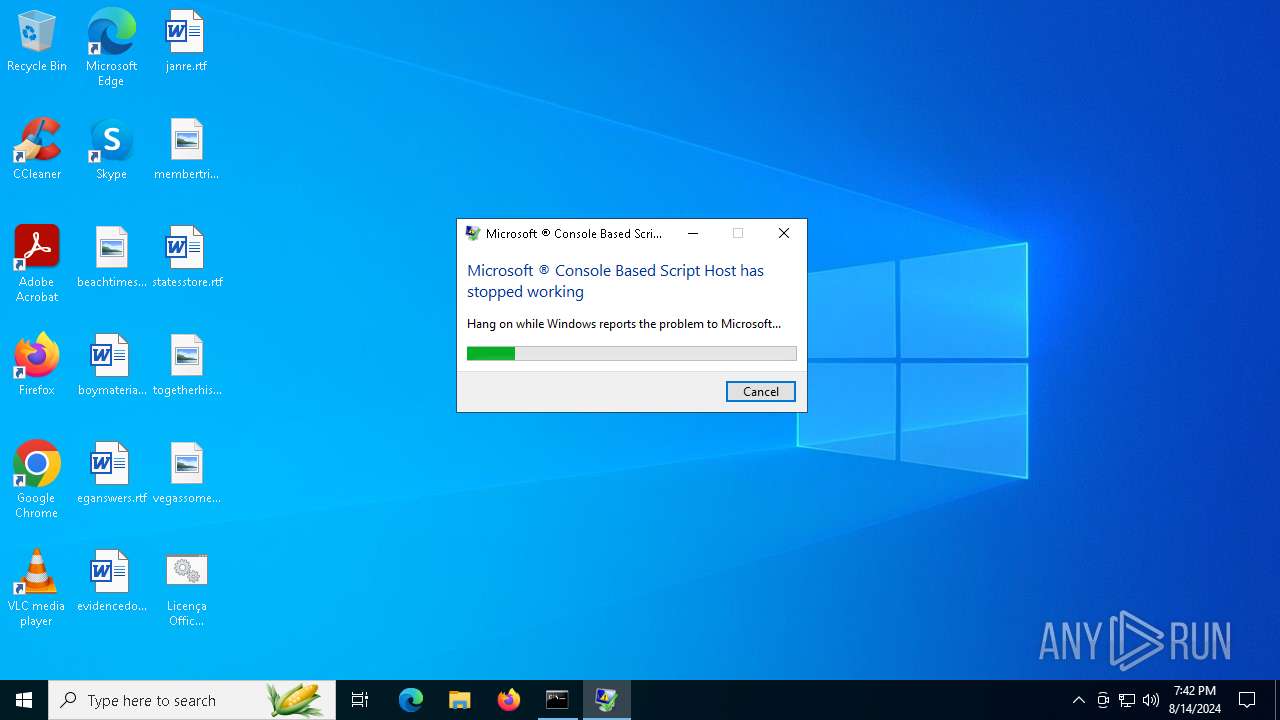
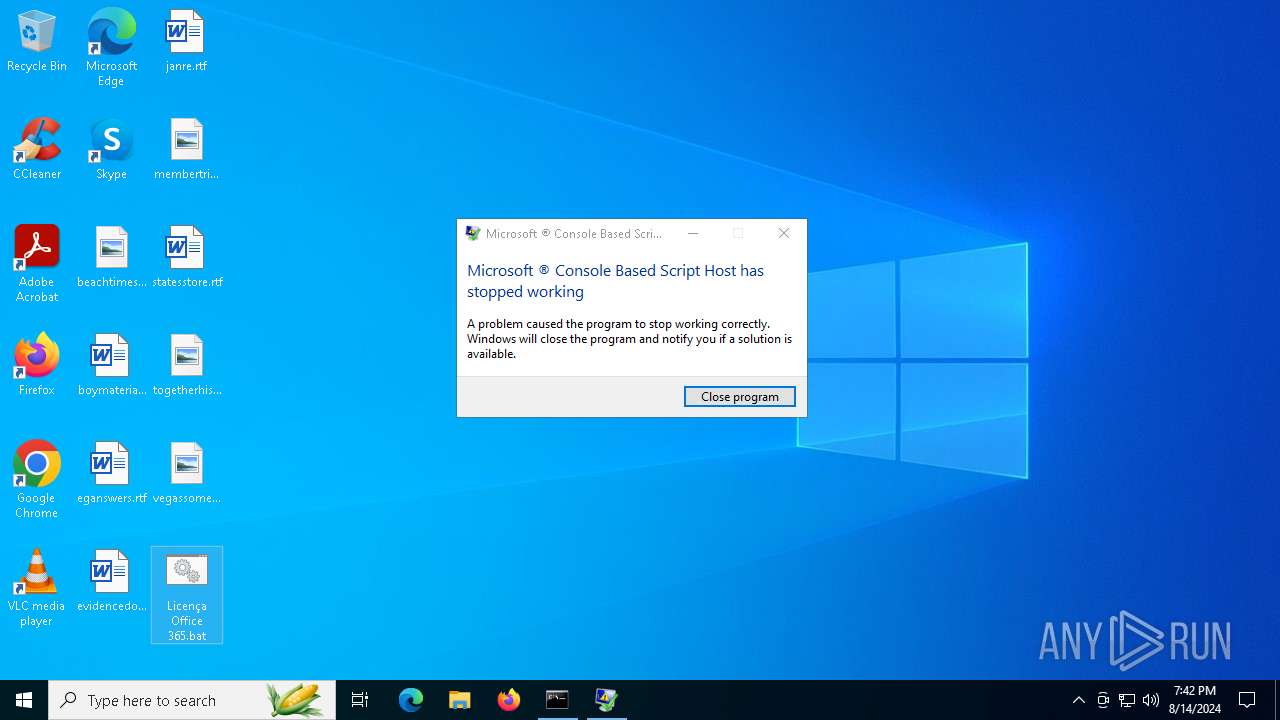
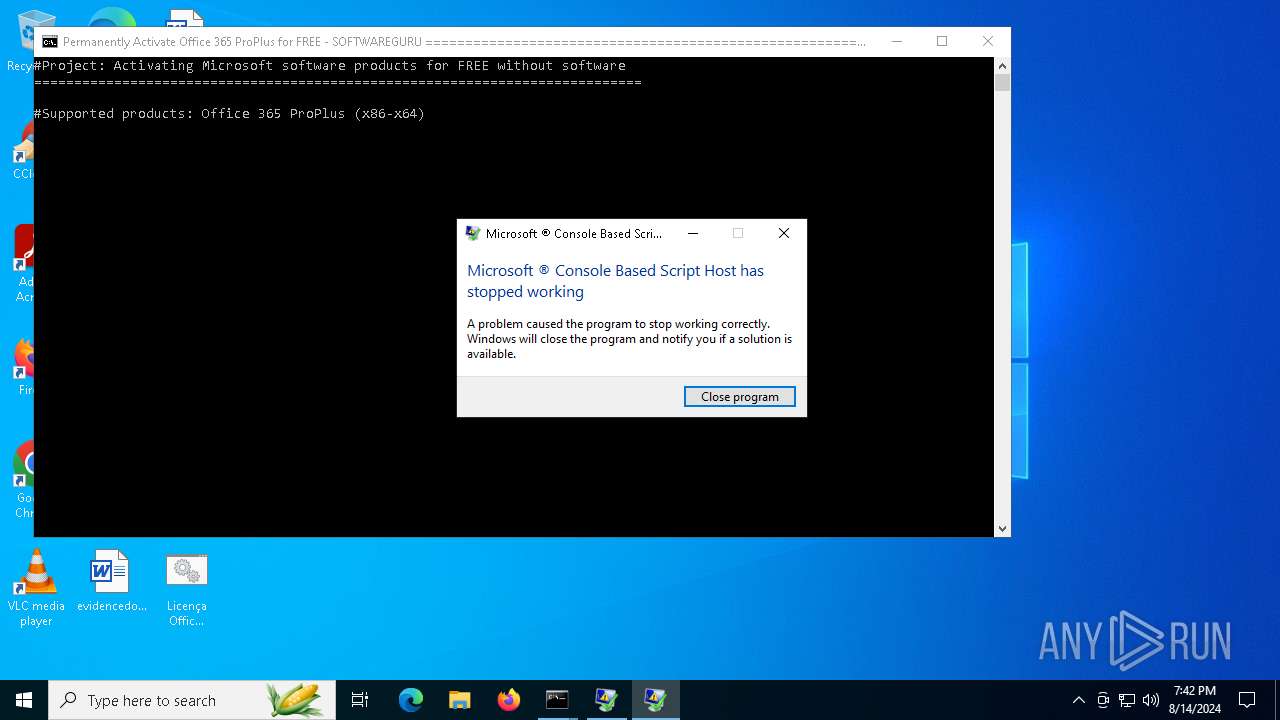
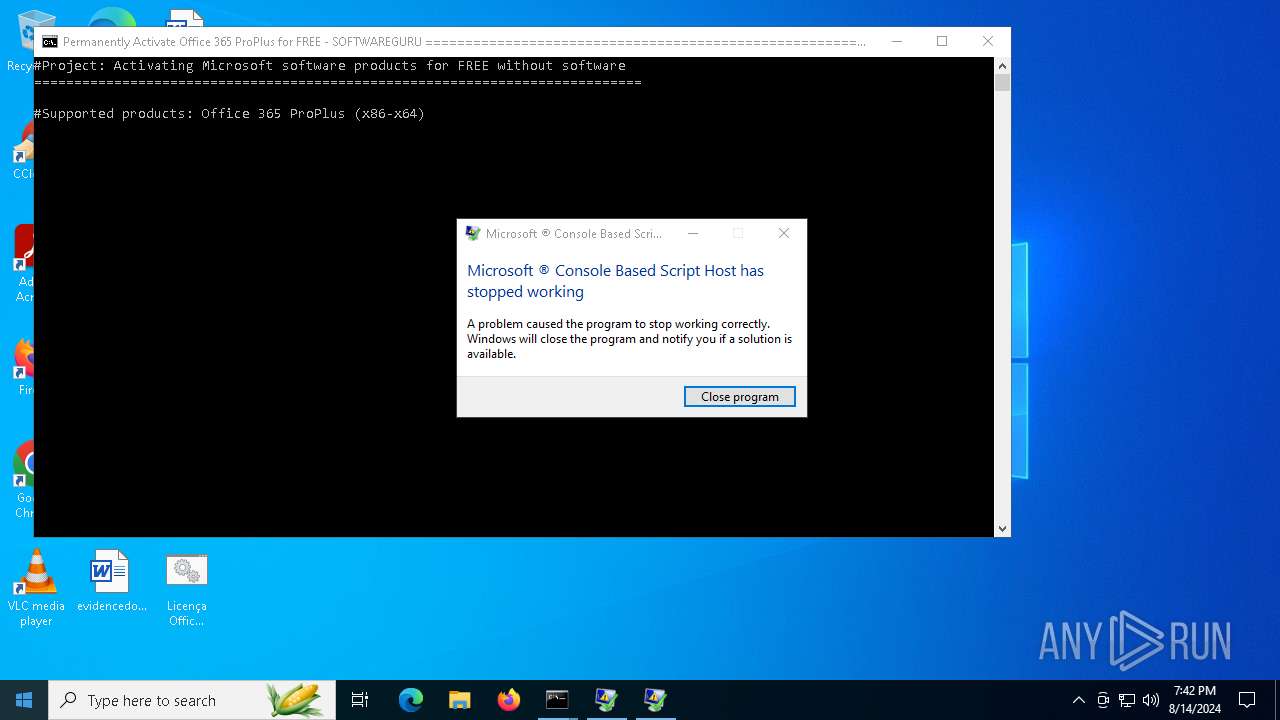
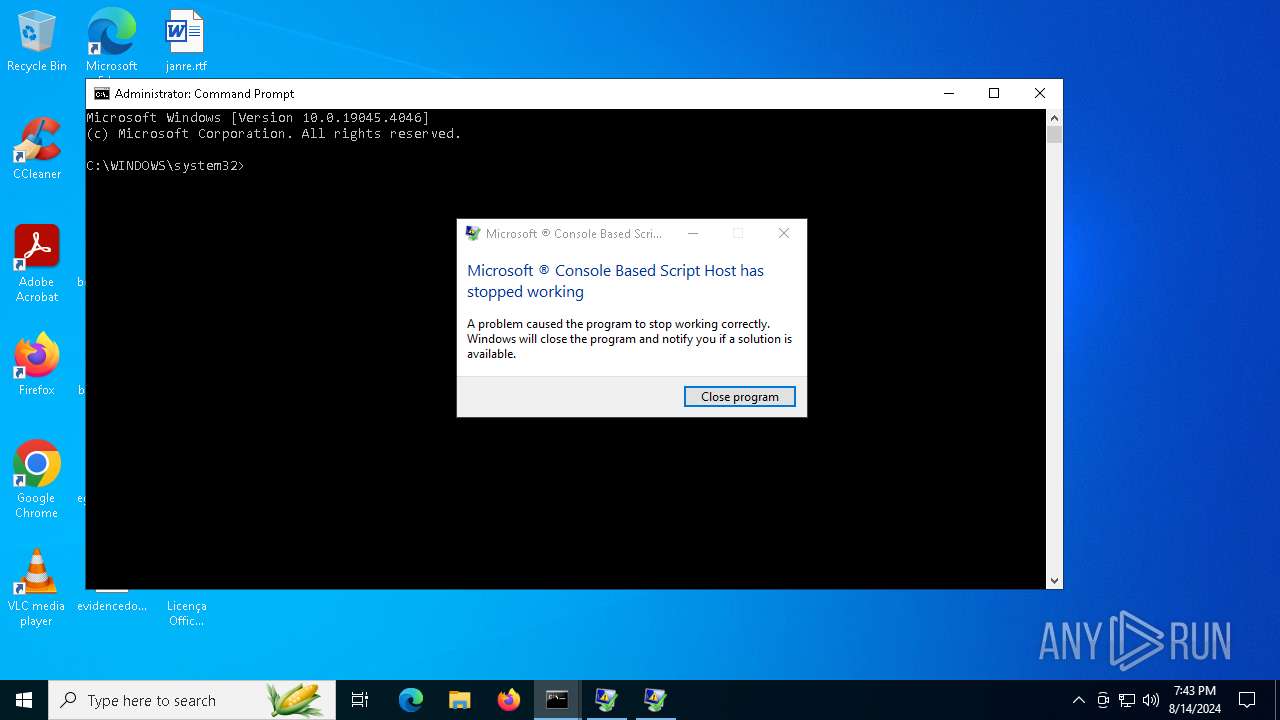
Executes application which crashes
- cscript.exe (PID: 5880)
- cscript.exe (PID: 6372)
- cscript.exe (PID: 6260)
The process creates files with name similar to system file names
- WerFault.exe (PID: 7124)
- WerFault.exe (PID: 5984)
- WerFault.exe (PID: 6696)
INFO
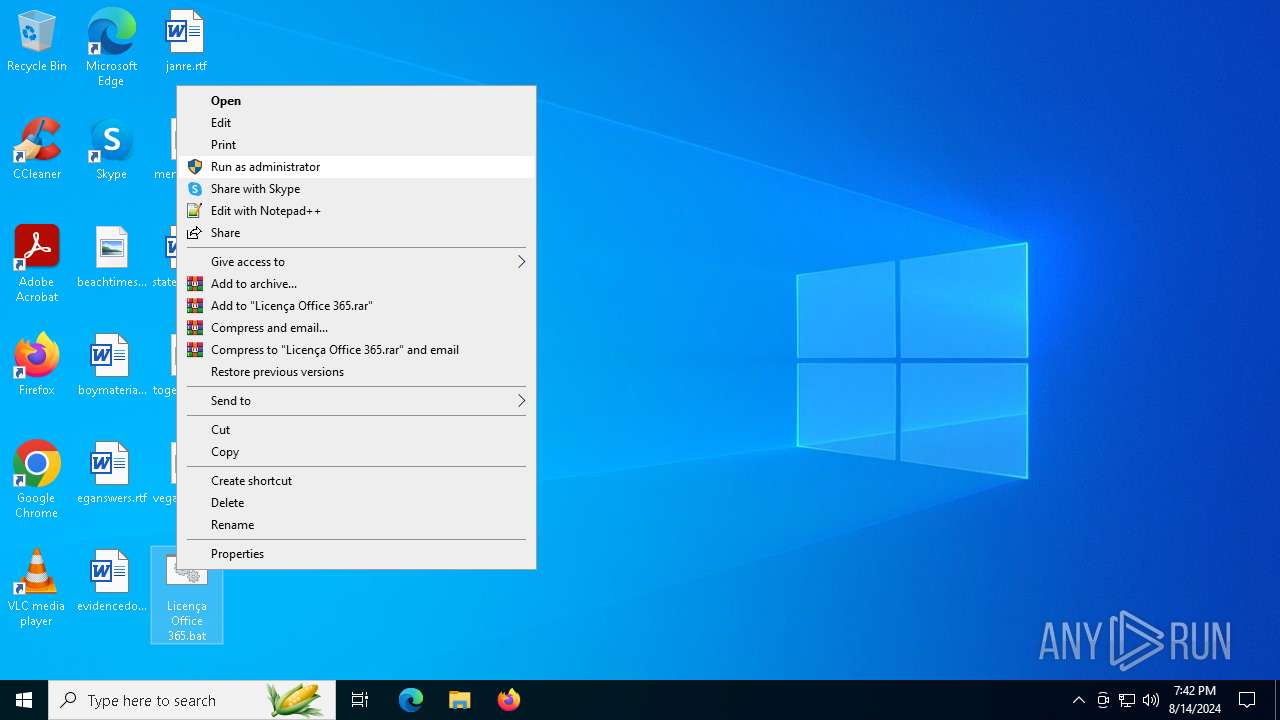
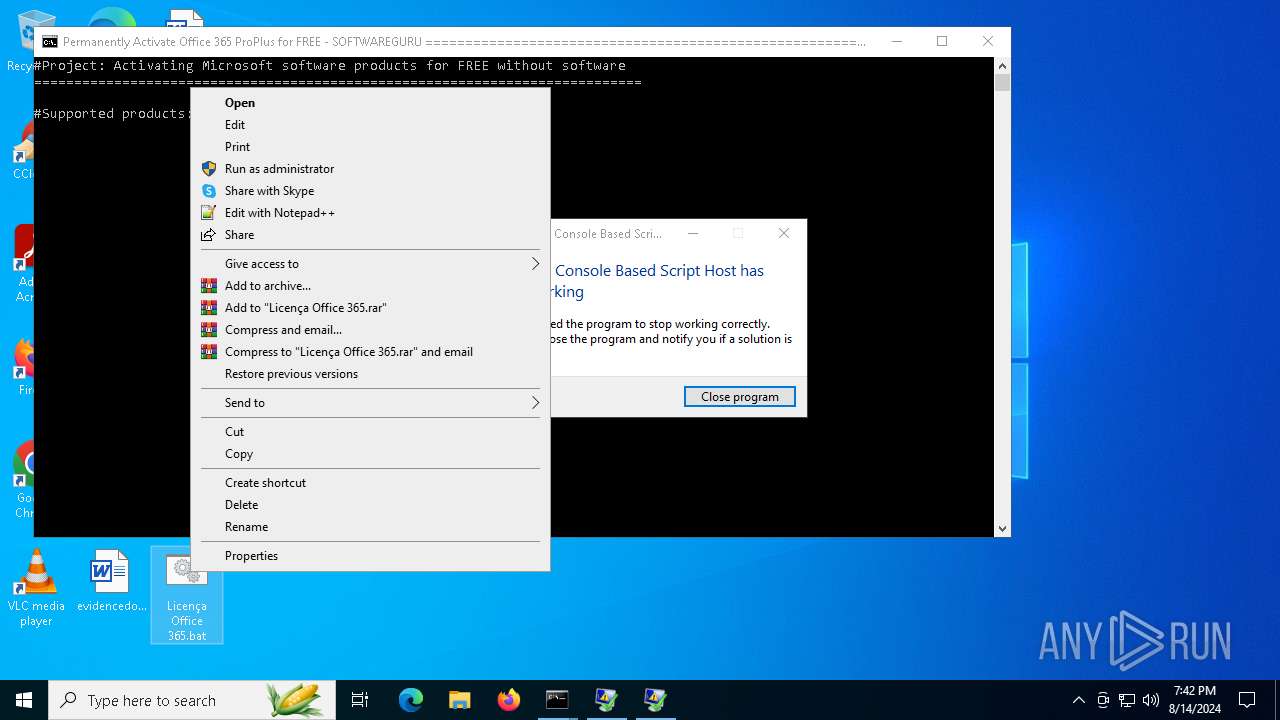
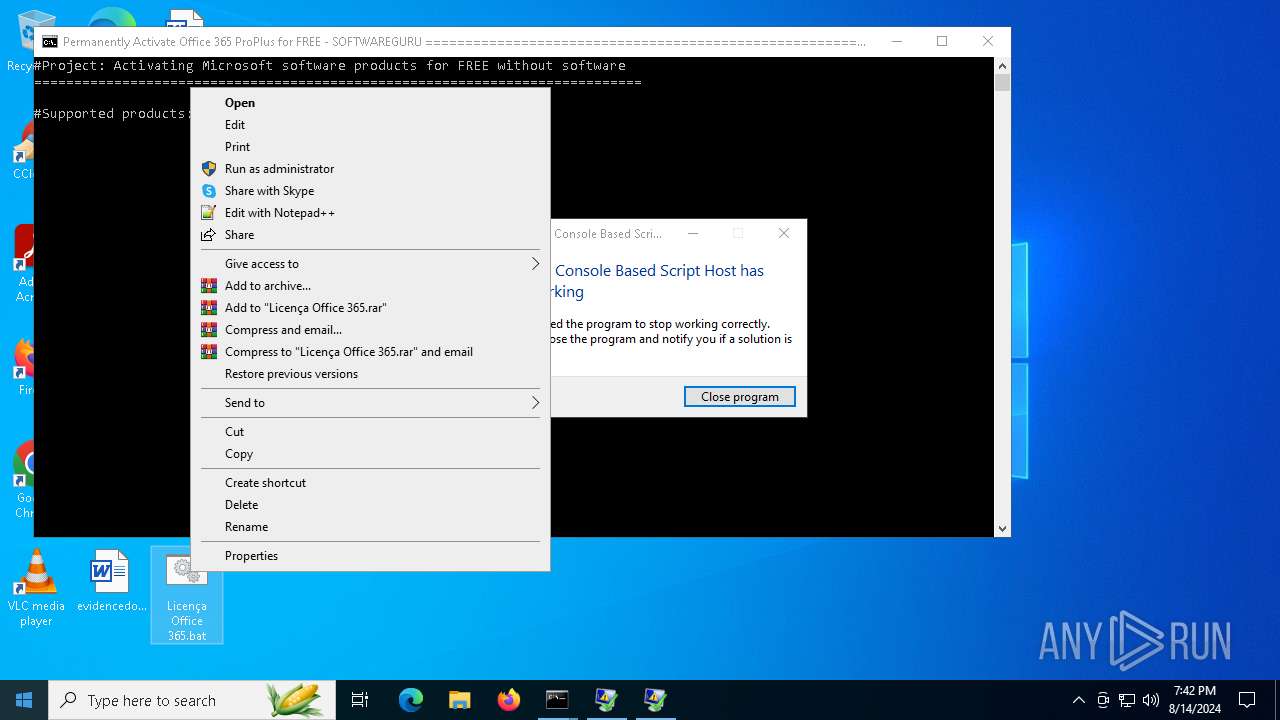
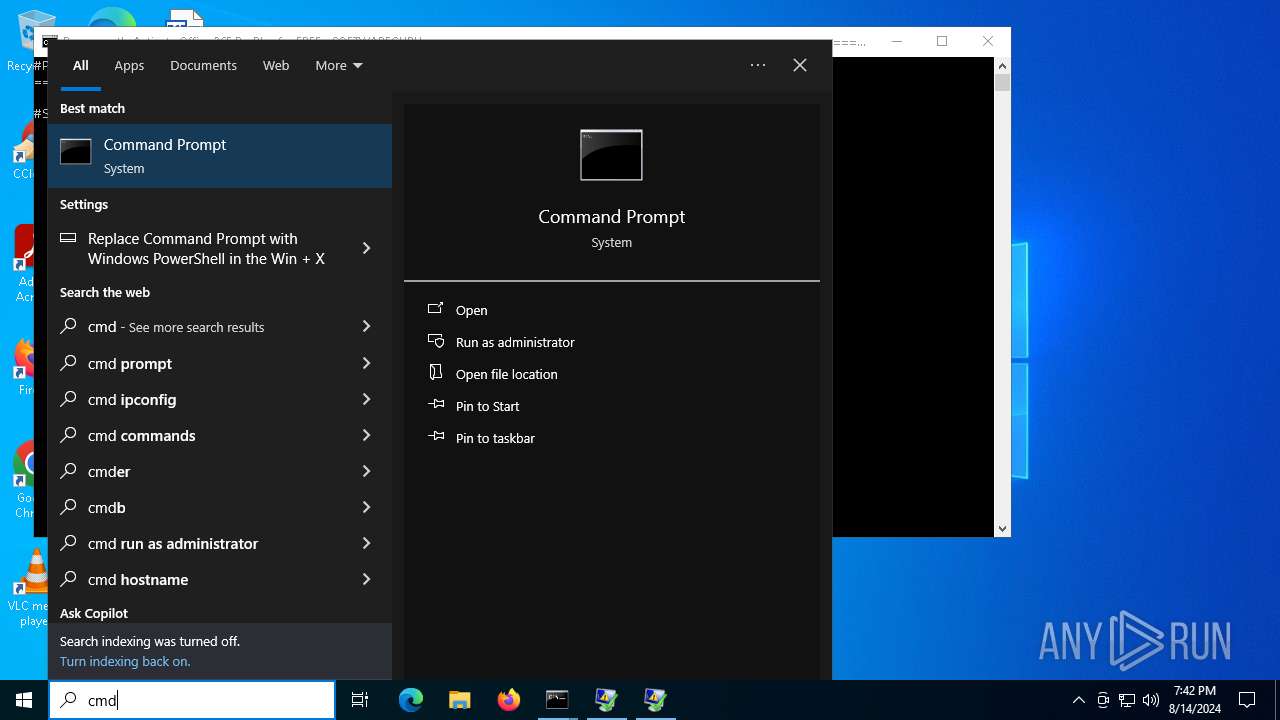
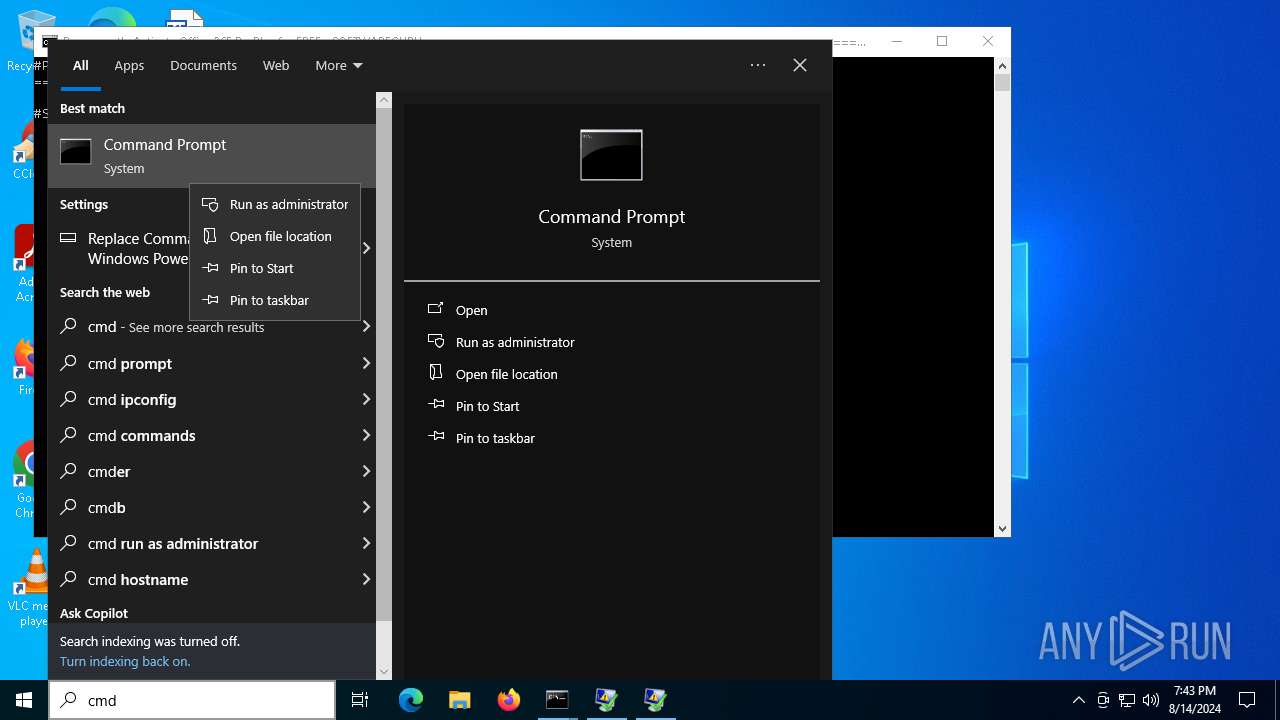
Manual execution by a user
- cmd.exe (PID: 7044)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 2456)
Reads security settings of Internet Explorer
- cscript.exe (PID: 5880)
- cscript.exe (PID: 6260)
- cscript.exe (PID: 6372)
Creates files or folders in the user directory
- cscript.exe (PID: 5880)
- WerFault.exe (PID: 7124)
Reads the software policy settings
- cscript.exe (PID: 5880)
- WerFault.exe (PID: 7124)
- WerFault.exe (PID: 5984)
- cscript.exe (PID: 6372)
- cscript.exe (PID: 6260)
- WerFault.exe (PID: 6696)
Checks proxy server information
- cscript.exe (PID: 5880)
- WerFault.exe (PID: 7124)
- WerFault.exe (PID: 5984)
- WerFault.exe (PID: 6696)
Reads the computer name
- TextInputHost.exe (PID: 6376)
Checks supported languages
- TextInputHost.exe (PID: 6376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
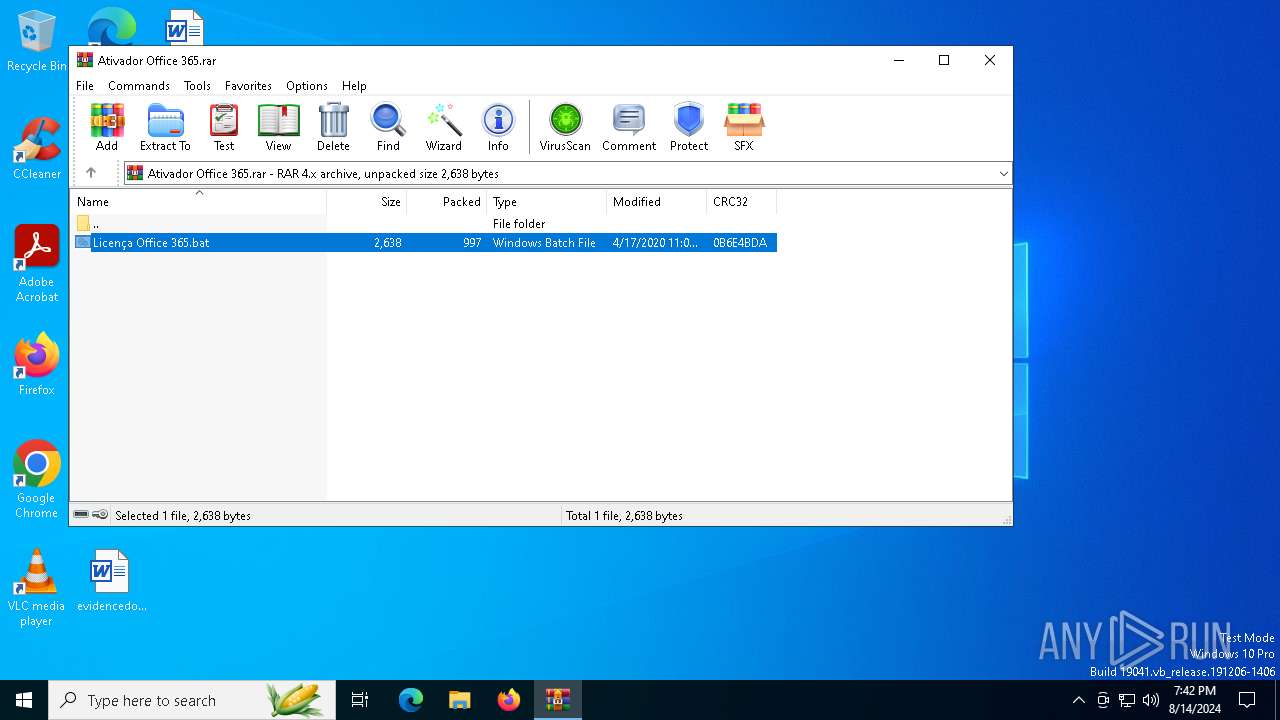
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
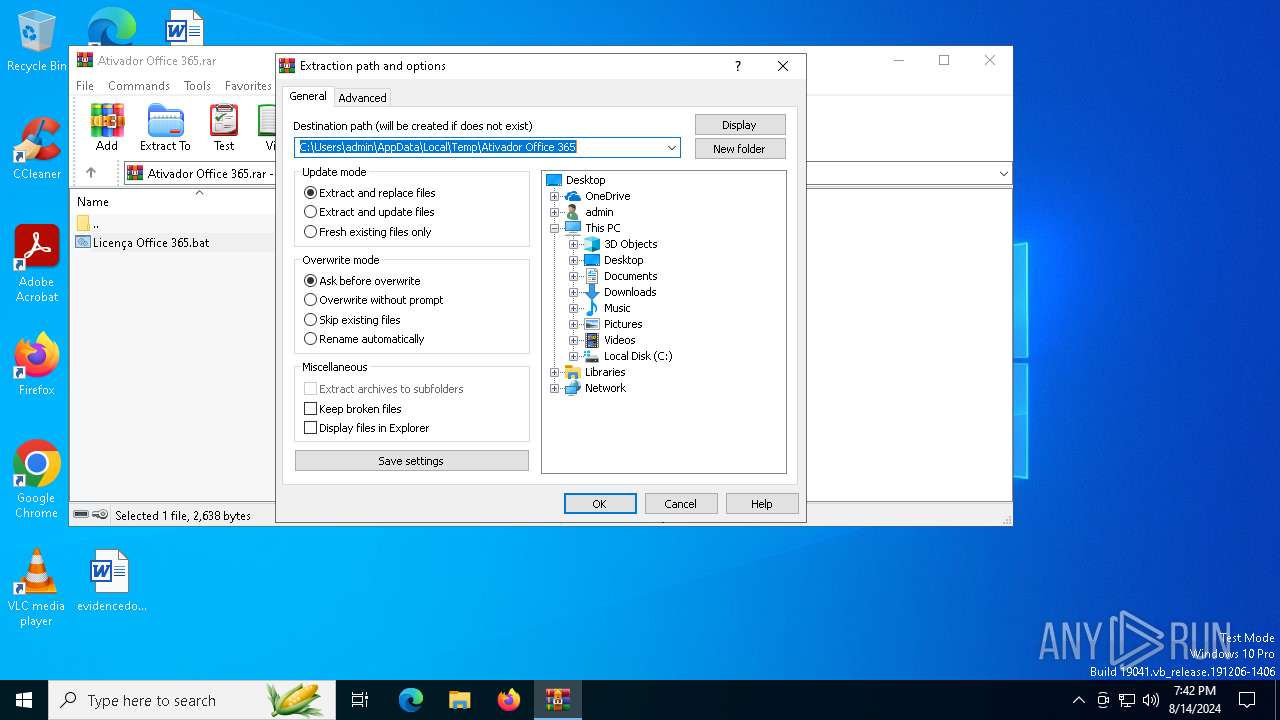
| CompressedSize: | 1051 |
|---|---|
| UncompressedSize: | 2638 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2020:04:17 23:03:02 |
| PackingMethod: | Normal |
| ArchivedFileName: | Licen?a Office 365.bat |
Total processes
159
Monitored processes
16
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2456 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5880 | cscript ospp.vbs /inslic:"..\root\Licenses16\ProPlusVL_KMS_Client-ppd.xrm-ms" | C:\Windows\System32\cscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 3221225477 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5984 | C:\WINDOWS\system32\WerFault.exe -u -p 6372 -s 1316 | C:\Windows\System32\WerFault.exe | cscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6012 | C:\WINDOWS\system32\cmd.exe /c dir /b ..\root\Licenses16\proplusvl_kms*.xrm-ms | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6260 | cscript ospp.vbs /inslic:"..\root\Licenses16\ProPlusVL_KMS_Client-ppd.xrm-ms" | C:\Windows\System32\cscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 3221225786 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6372 | cscript ospp.vbs /inslic:"..\root\Licenses16\ProPlusVL_KMS_Client-ul-oob.xrm-ms" | C:\Windows\System32\cscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6376 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 6420 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Ativador Office 365.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6696 | C:\WINDOWS\system32\WerFault.exe -u -p 6260 -s 1460 | C:\Windows\System32\WerFault.exe | cscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 393
Read events
34 330
Write events
51
Delete events
12
Modification events
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Ativador Office 365.rar | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
7
Text files
7
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7124 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_cscript.exe_418e8ac587e5ed2e4f3fb7b5fce6fa024c8d28_d25c8a3a_fd92d301-bb19-4e4c-abfb-45866ac9875f\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5984 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_cscript.exe_418e8ac587e5ed2e4f3fb7b5fce6fa024c8d28_d25c8a3a_4ea35723-f596-444e-b0a9-3dc6c853f42a\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6696 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_cscript.exe_418e8ac587e5ed2e4f3fb7b5fce6fa024c8d28_d25c8a3a_de52e8c2-e10a-455f-9209-9d6a9959e66b\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6420 | WinRAR.exe | C:\Users\admin\Desktop\Licença Office 365.bat | text | |
MD5:563AC0420376BC6D50BF97101B2DB279 | SHA256:A32AA7E7DA7C39B555534C531053FC386006E6FFE208B6EFB930926D2F2FABF4 | |||
| 5880 | cscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A583E2A51BFBDC1E492A57B7C8325850 | der | |
MD5:C7D1234376F3389D6C220F0DCF24341B | SHA256:F67F7E62B47D1C4D9059F9F01FF40D52044EE81F594C5B8C8925C254381061E5 | |||
| 5880 | cscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\36AC0BE60E1243344AE145F746D881FE | binary | |
MD5:858FBA59B5640273B7221532FDDD4593 | SHA256:C9C2F2696BCB6BD09C136E89E7BF23572E3E96E9850CBE3B513AB90A991B5F5E | |||
| 5984 | WerFault.exe | C:\Windows\appcompat\Programs\Amcache.hve | binary | |
MD5:BE3A9BDDDFD05788C637AA381E1F620D | SHA256:CD3CA6763864F1198AE5FE117F6C09626FEBC8CBA939A88A5833FA6920EA6CE3 | |||
| 7124 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:82C30E45BF5F93A5DB1D5E47F913053B | SHA256:2C6BBFF9207065E8800C4AF0CB2748818ABB3CFFC0D6D518FE17F76A232F8967 | |||
| 5984 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD136.tmp.dmp | dmp | |
MD5:B546C2560419642D6FC181E3DF126DA7 | SHA256:CC25E3AD863BCED5AC336478C727E7285DFA98C78121B16A26354A281B67050F | |||
| 5984 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD1D4.tmp.xml | xml | |
MD5:7489BD10DBC0A01E02AC77A870F886F8 | SHA256:4598C8DE027F7BAF0868C05317A47BD365CC0661BF8E022B44D943C3F0E13FDC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
53
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6752 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1344 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1344 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5880 | cscript.exe | GET | 200 | 23.48.23.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
6804 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5880 | cscript.exe | GET | 200 | 23.48.23.193:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_2010-07-06.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5600 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3980 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3980 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 184.86.251.17:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1344 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |