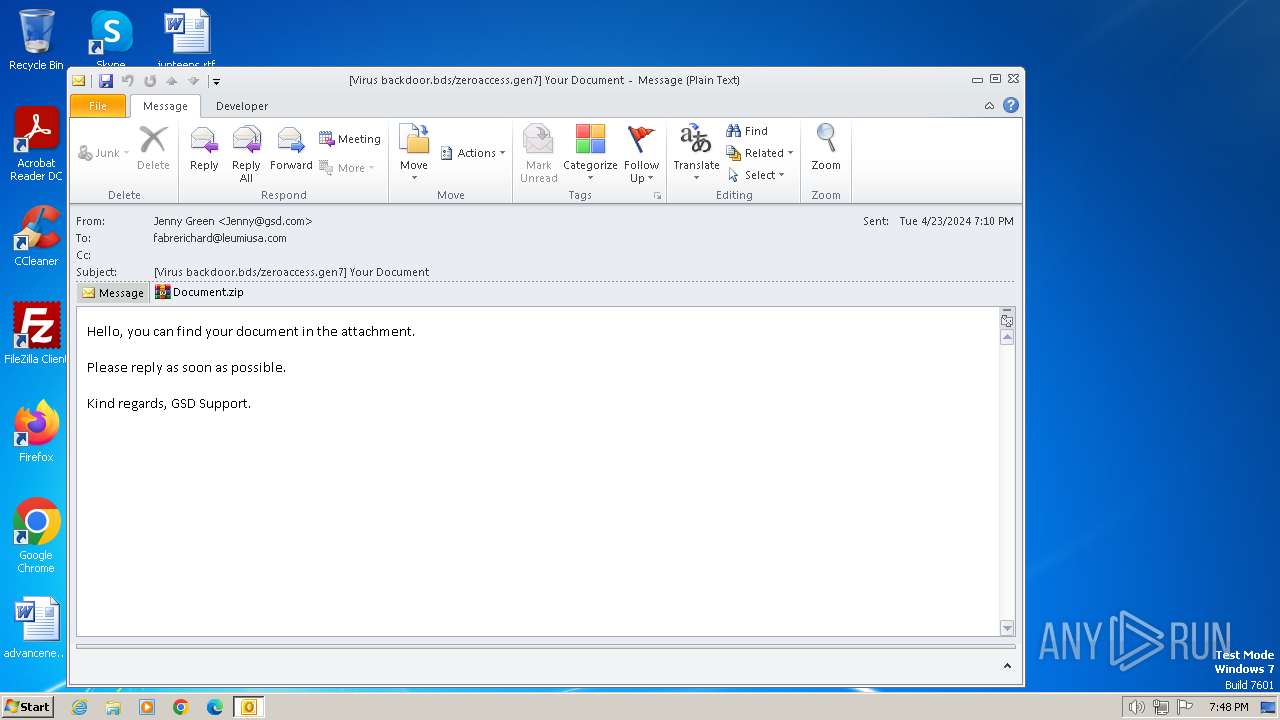
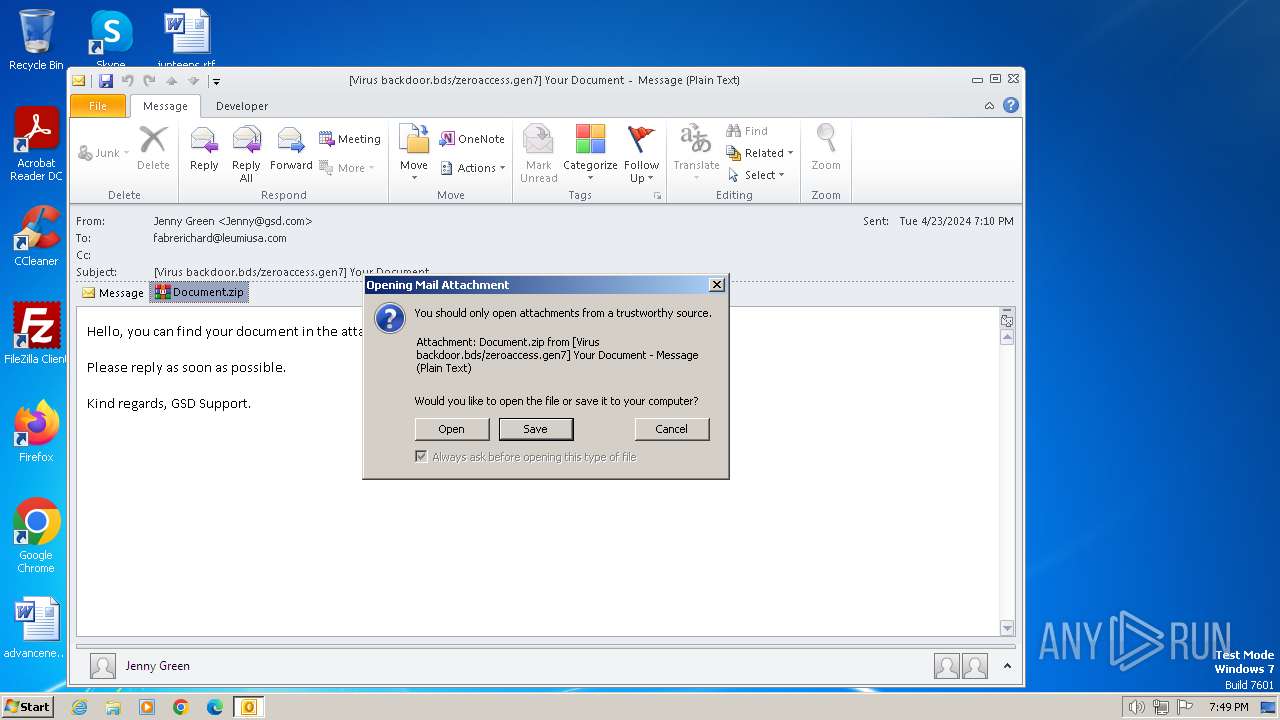
| File name: | Virus backdoor.bdszeroaccess.gen7 Your Document.msg |
| Full analysis: | https://app.any.run/tasks/6c8de84d-89f8-4aa1-a67b-352b48e3b799 |
| Verdict: | Malicious activity |
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | April 23, 2024, 18:48:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | FF9A8096ECB97C5F3136543476F1FBEB |
| SHA1: | BEBD66455EB2ABFD488BD57DC9F5B7C20D40B903 |
| SHA256: | 8E0146A8174F796443A22D7328FEA1DE4A52A246054B1C43ECEA1093609B0FD0 |
| SSDEEP: | 6144:tDWlVnAzUOAyLrHCOQha4YhNqQqx8G6sW:sNOAyLrHyha4YhNqQqx8L |
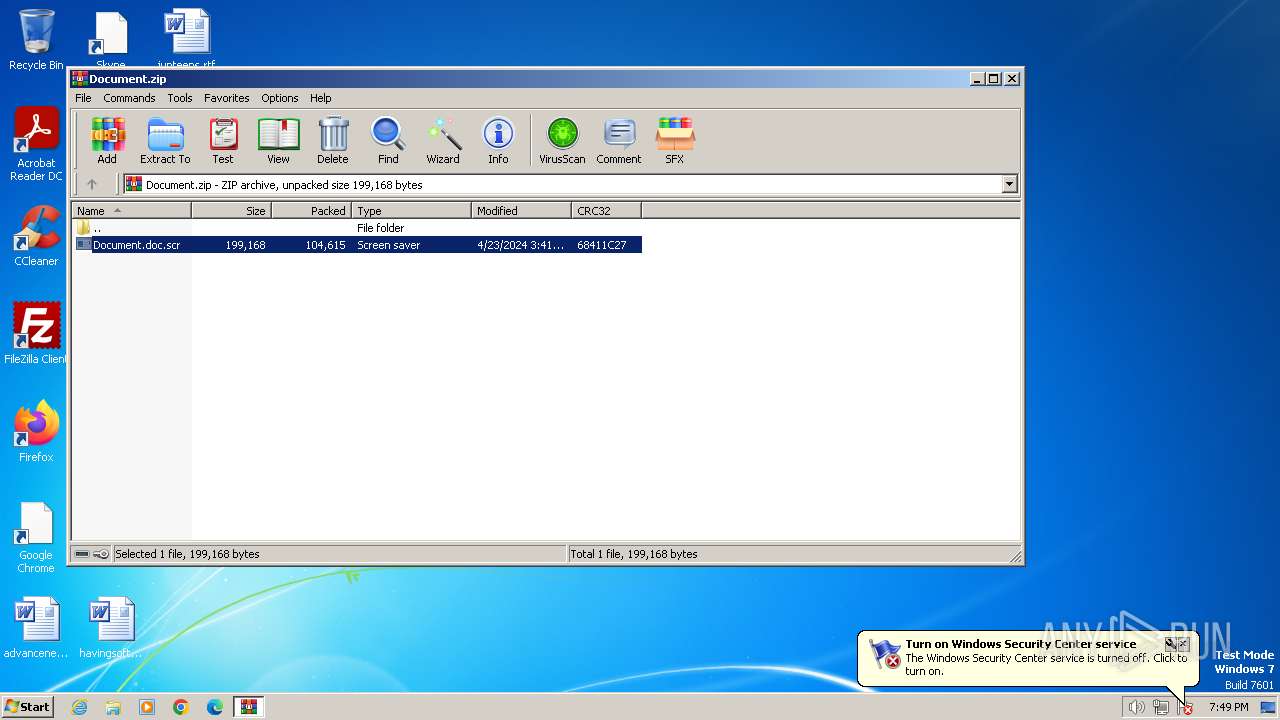
MALICIOUS
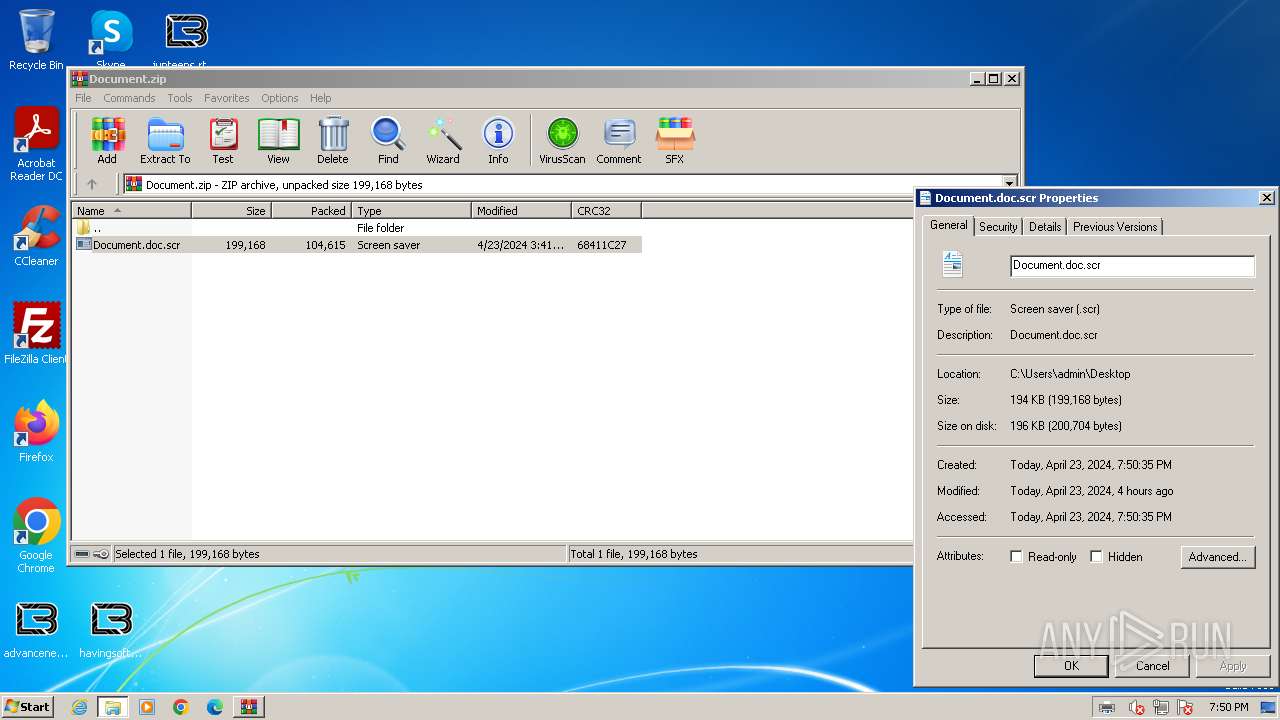
Drops the executable file immediately after the start
- OUTLOOK.EXE (PID: 1196)
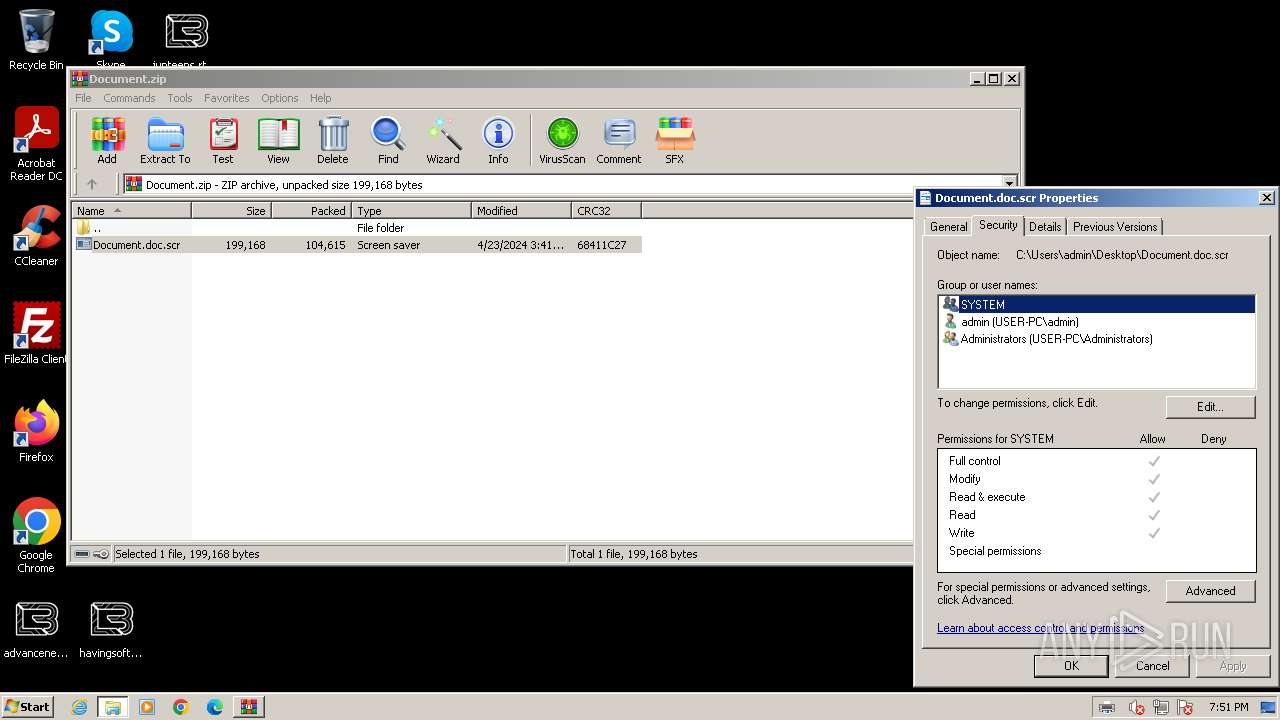
- Document.doc.scr (PID: 2260)
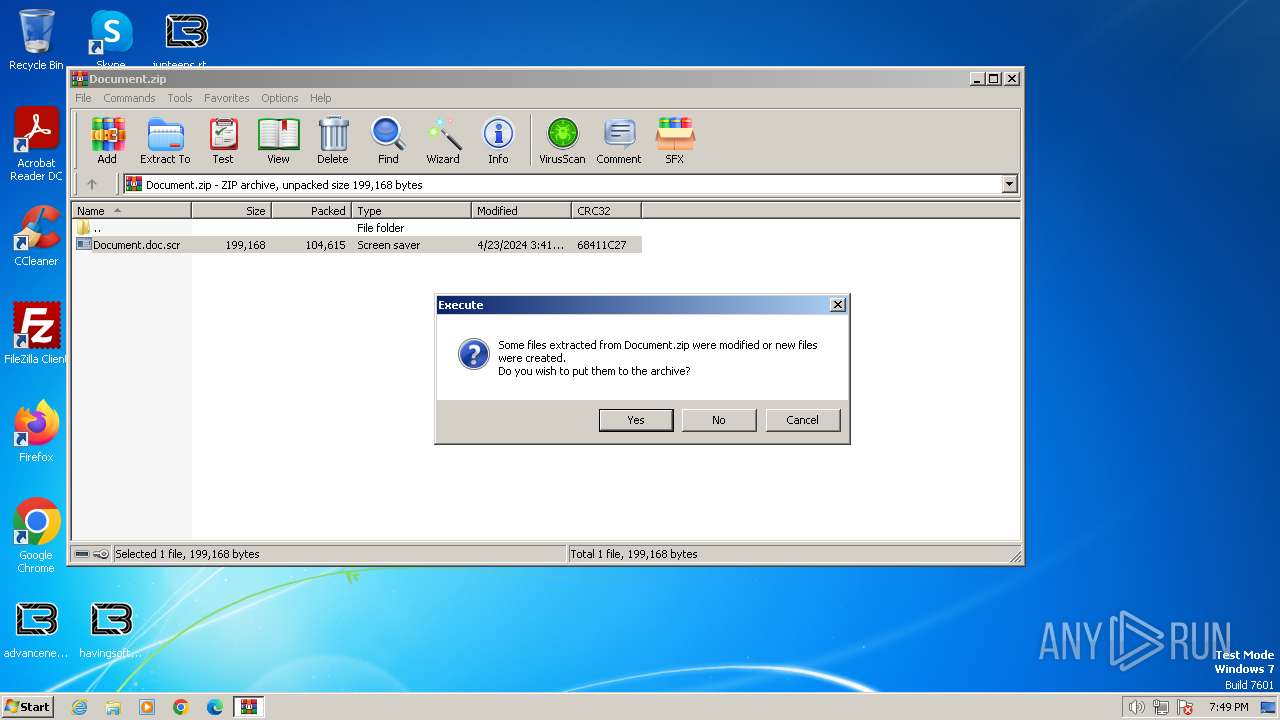
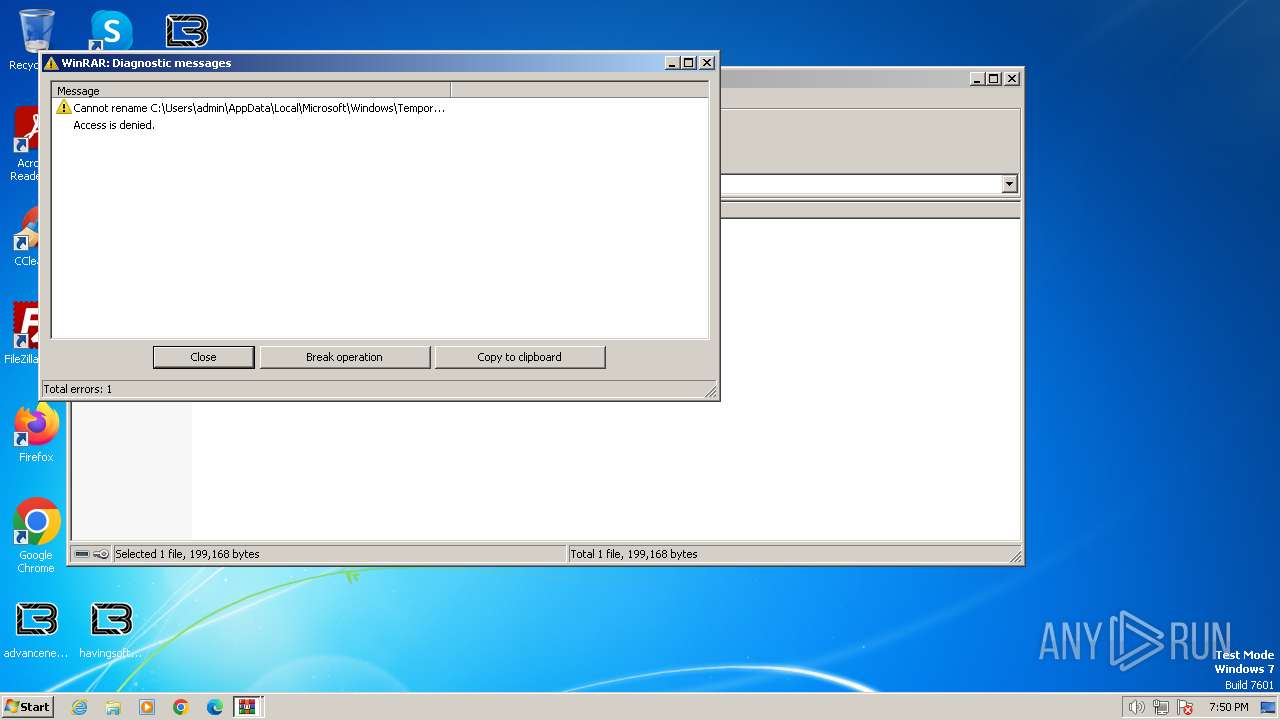
Renames files like ransomware
- Document.doc.scr (PID: 2260)
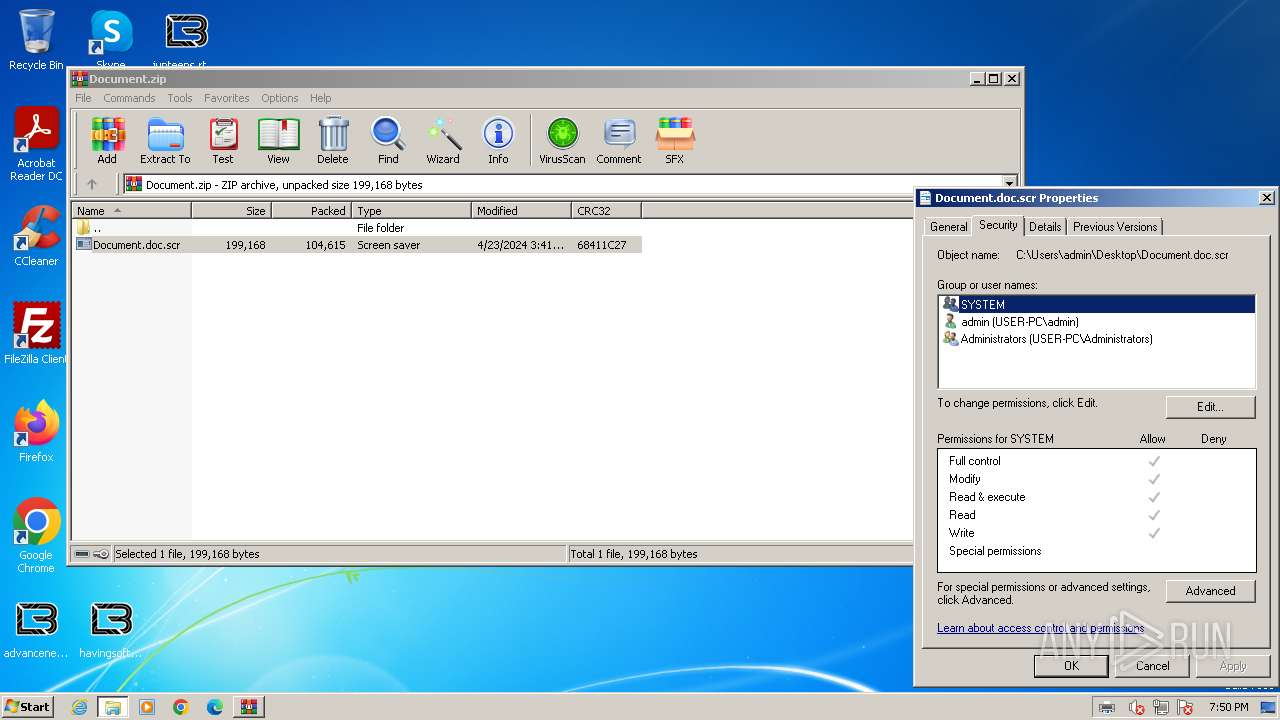
Known privilege escalation attack
- dllhost.exe (PID: 3404)
Creates a writable file in the system directory
- printfilterpipelinesvc.exe (PID: 2484)
- Document.doc.scr (PID: 2260)
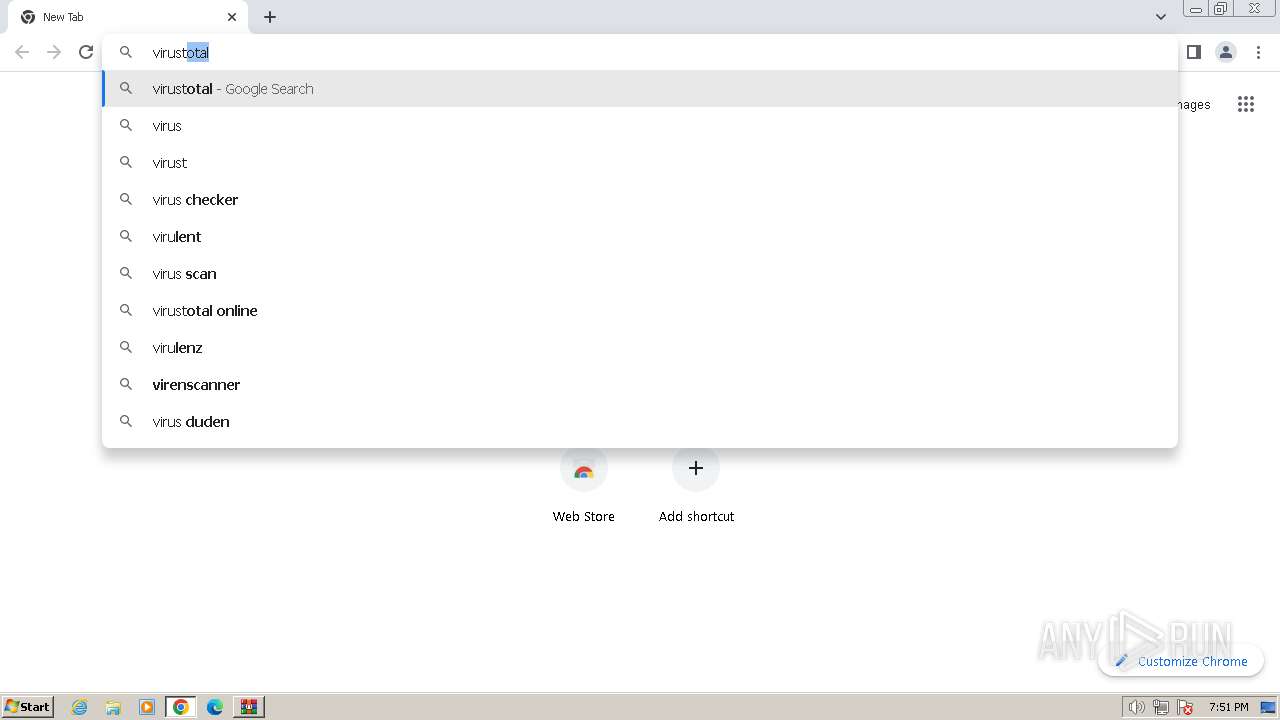
Steals credentials from Web Browsers
- Document.doc.scr (PID: 2260)
[YARA] LockBit is detected
- Document.doc.scr (PID: 2260)
Actions looks like stealing of personal data
- Document.doc.scr (PID: 2260)
SUSPICIOUS
Non-standard symbols in registry
- OUTLOOK.EXE (PID: 1196)
- Document.doc.scr (PID: 2260)
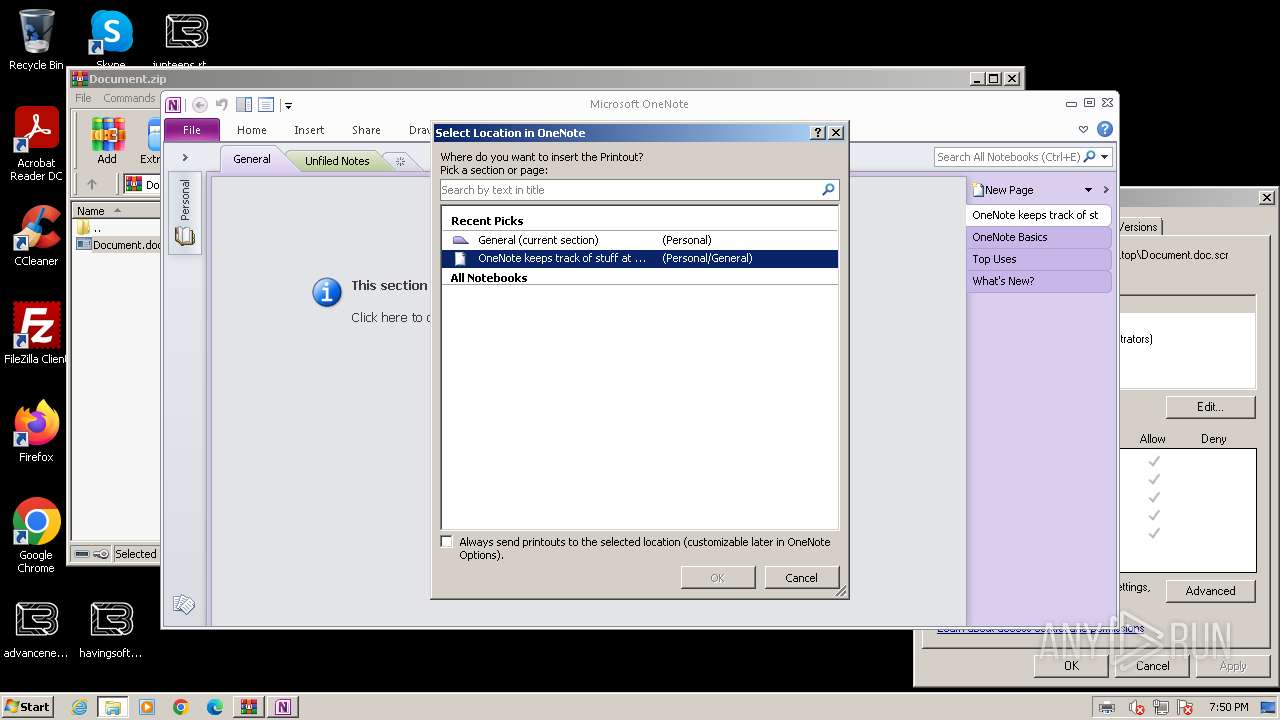
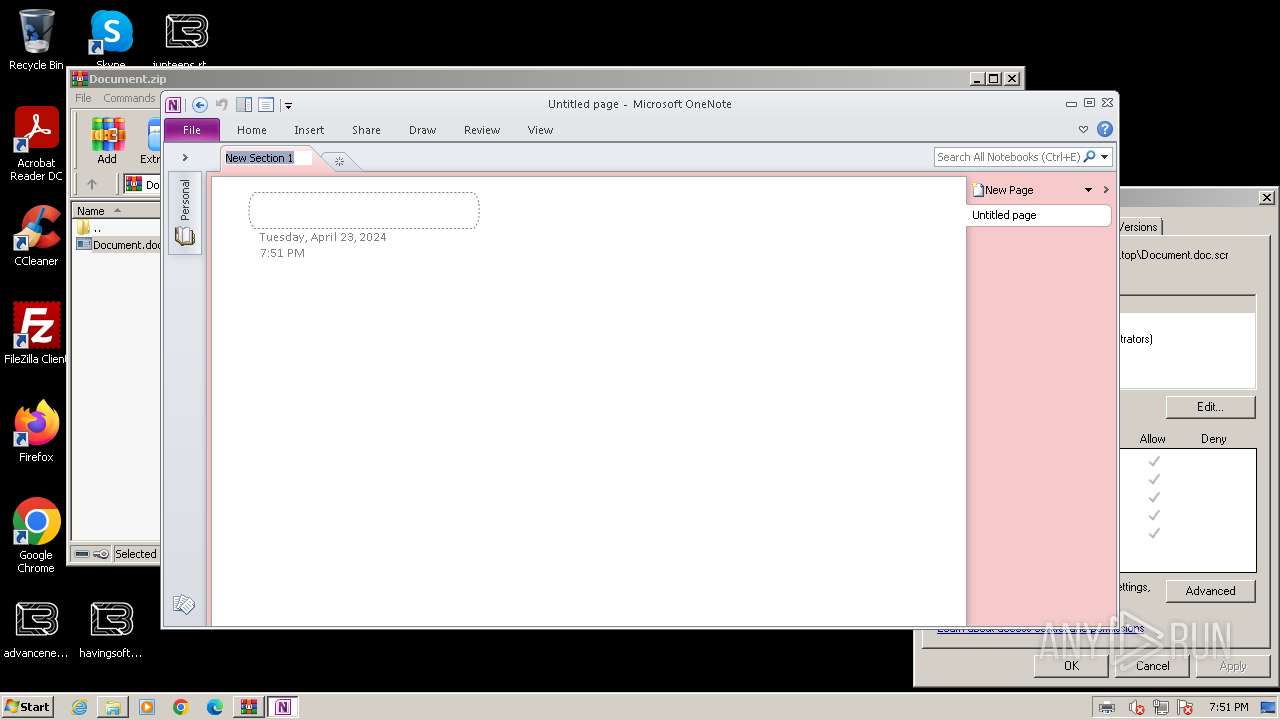
- ONENOTE.EXE (PID: 3164)
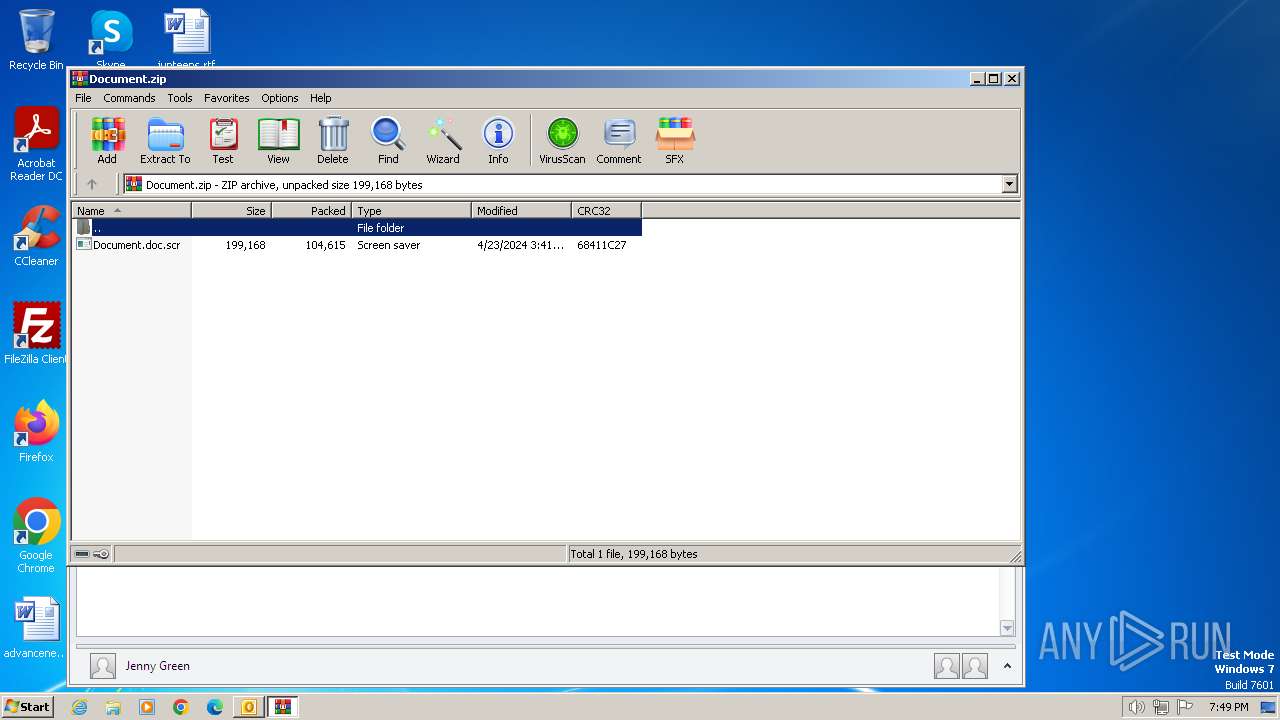
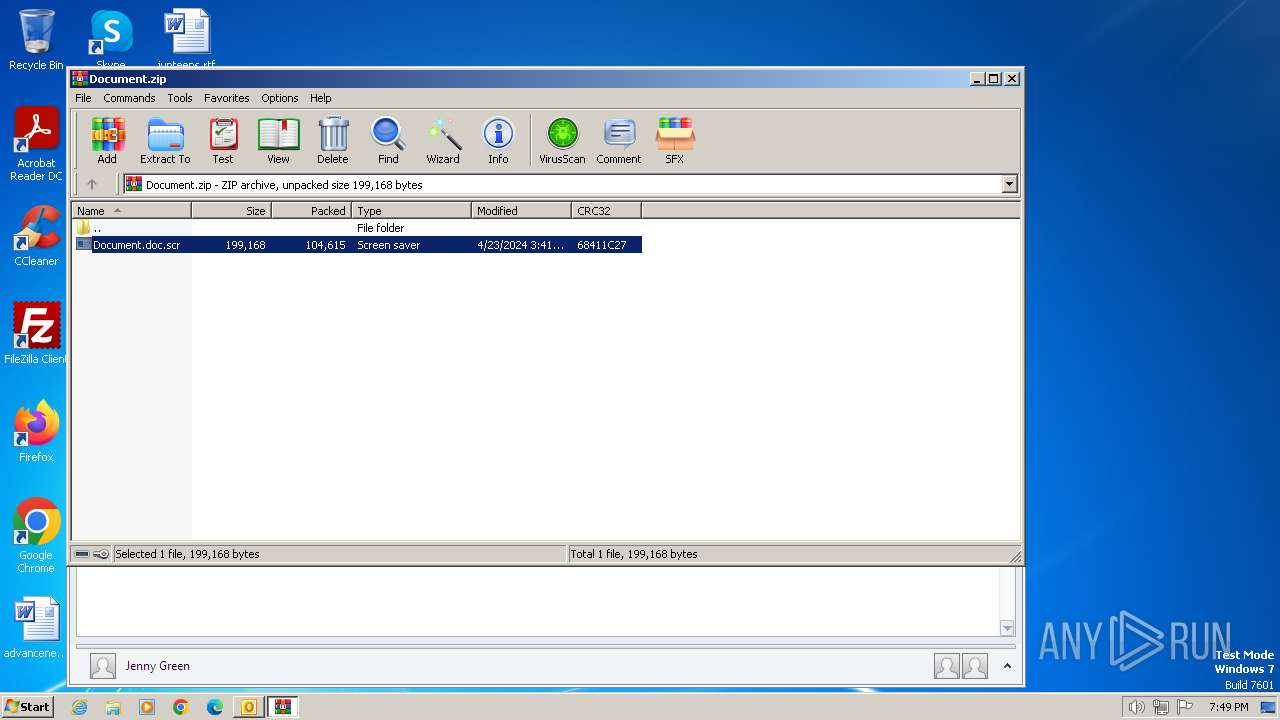
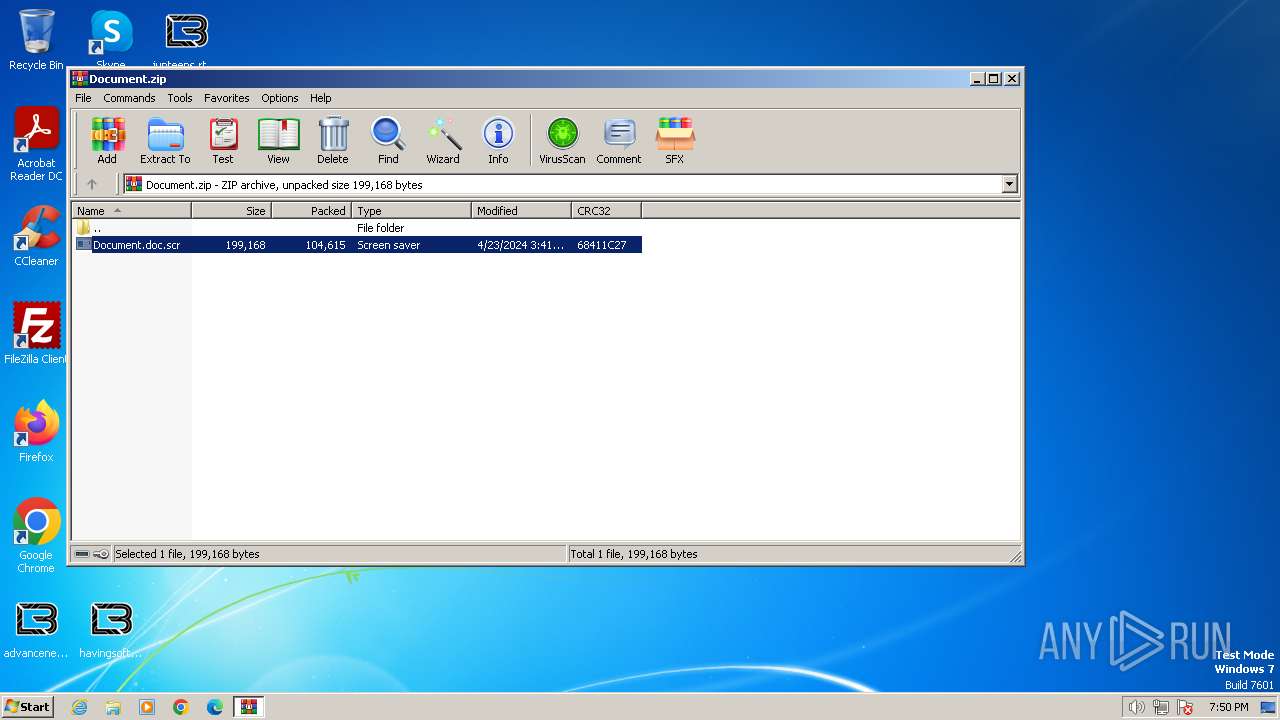
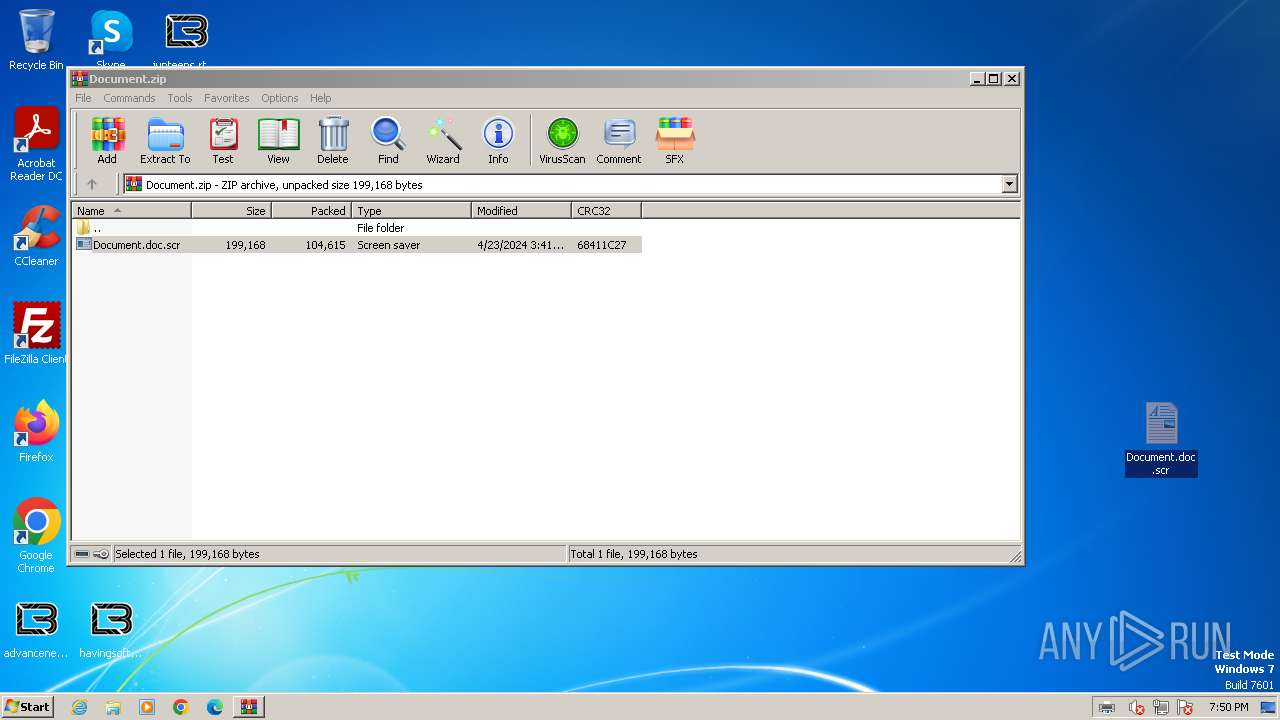
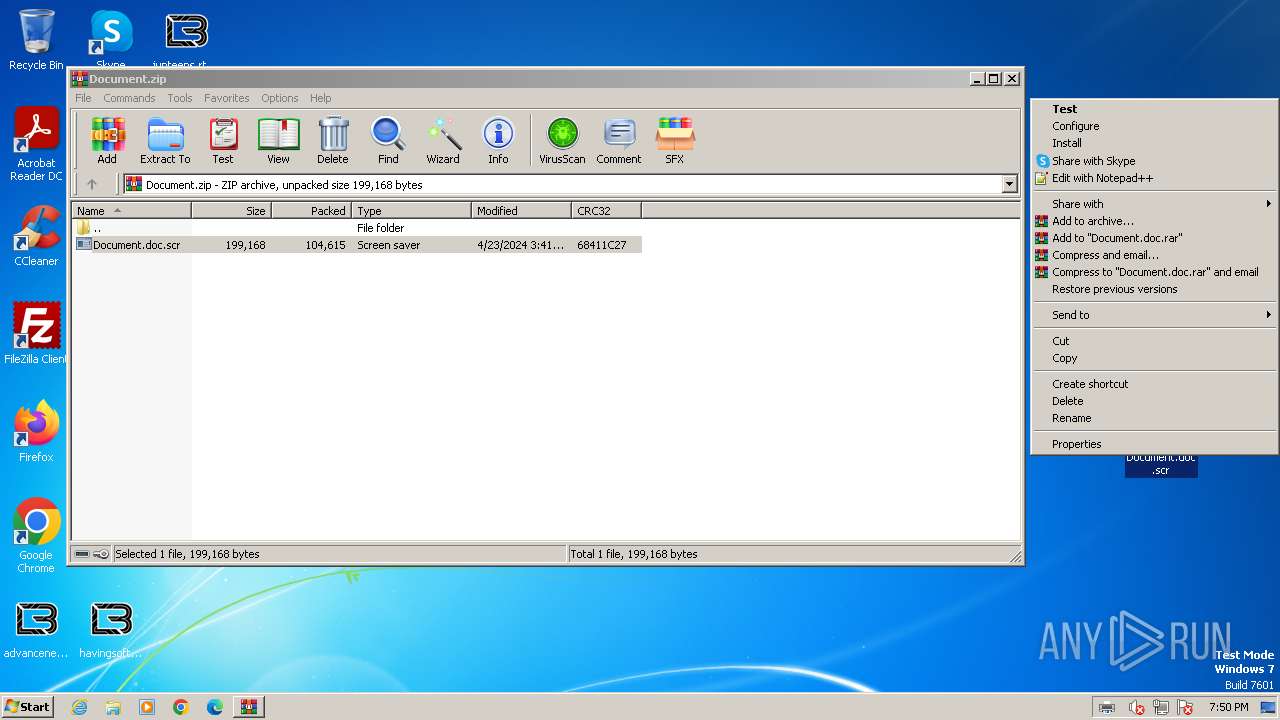
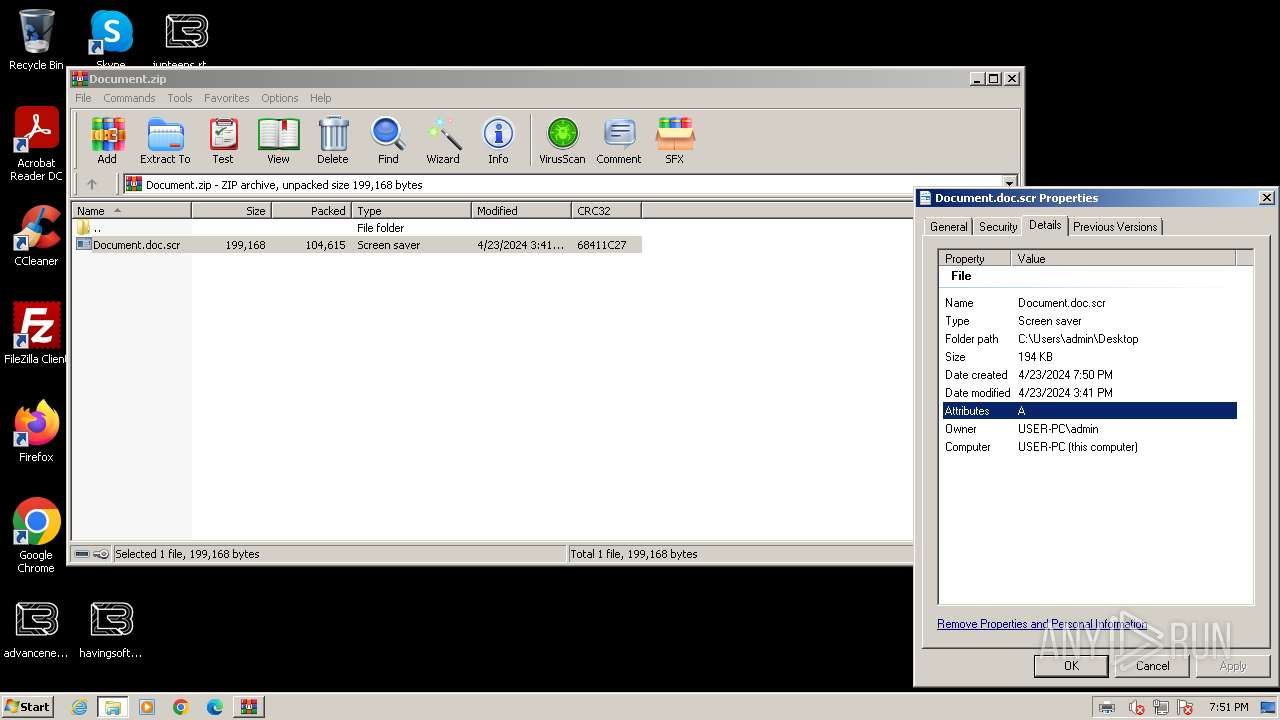
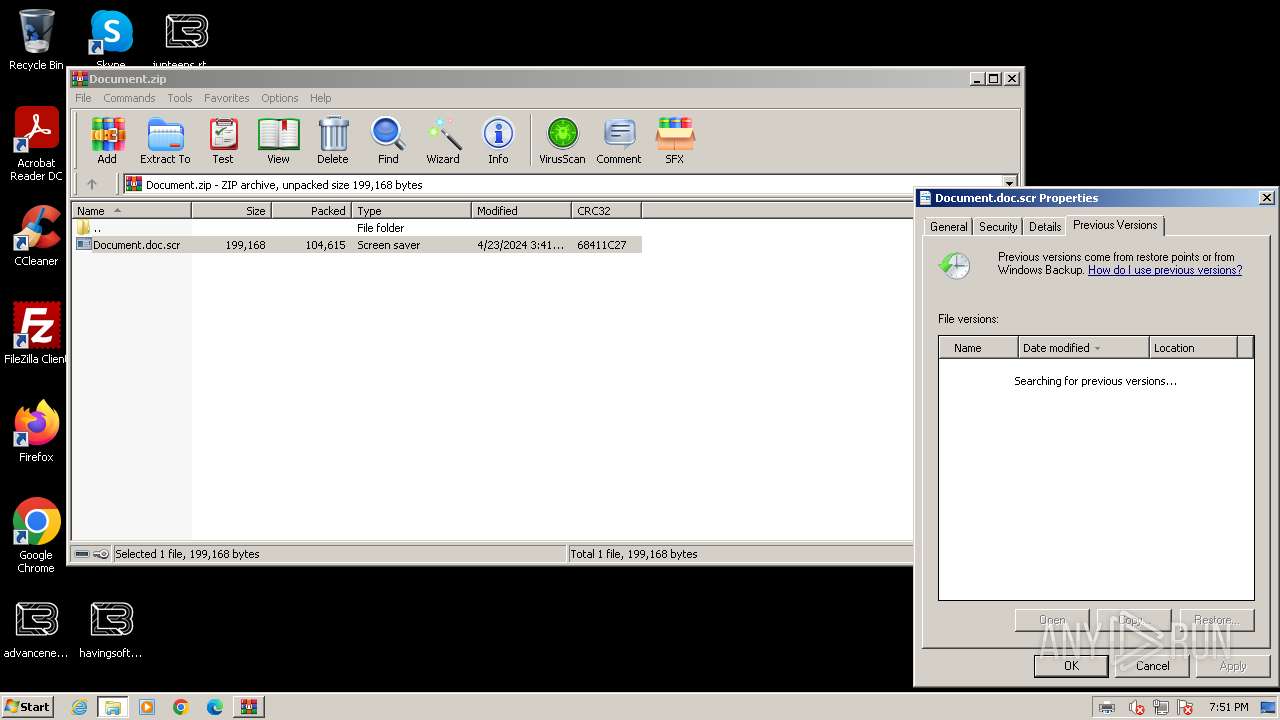
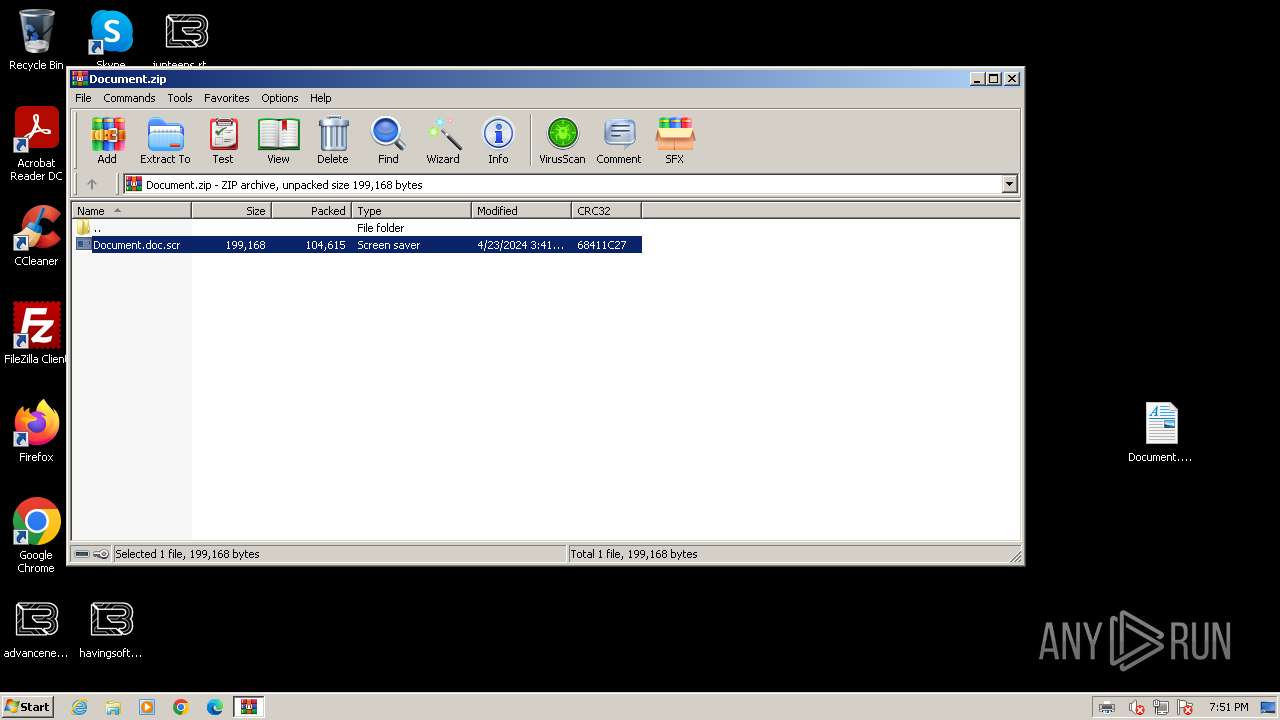
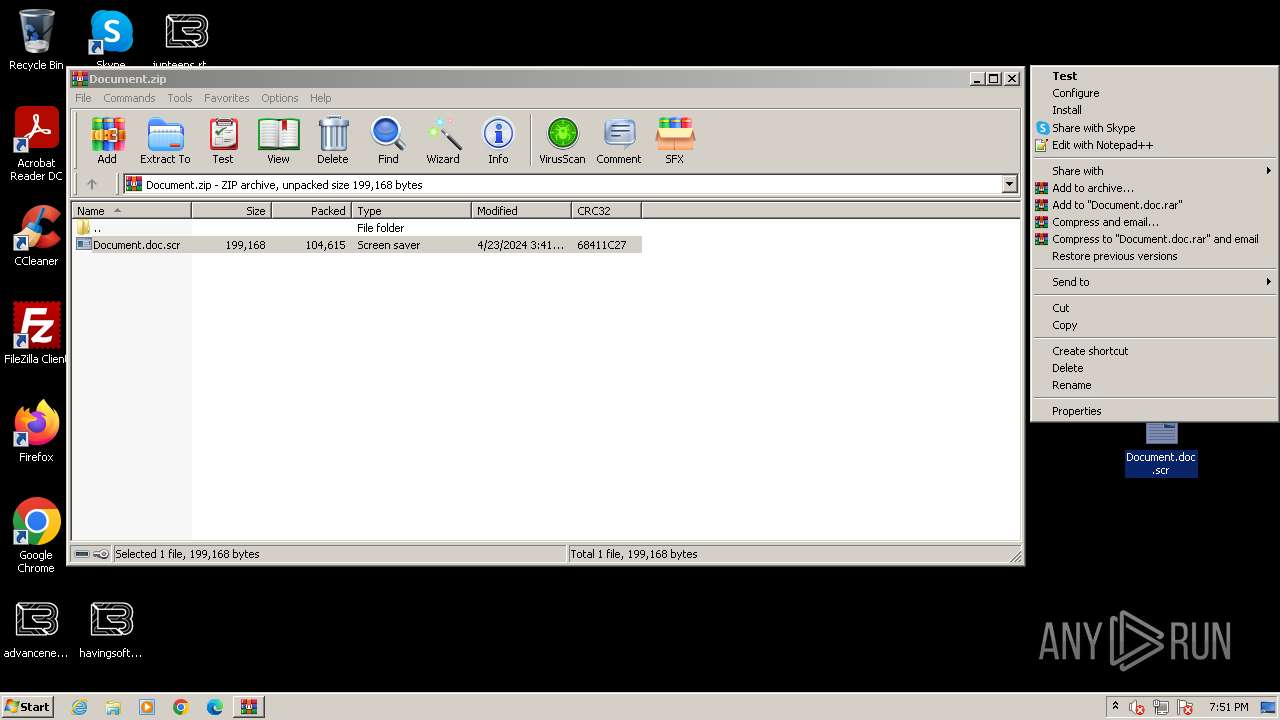
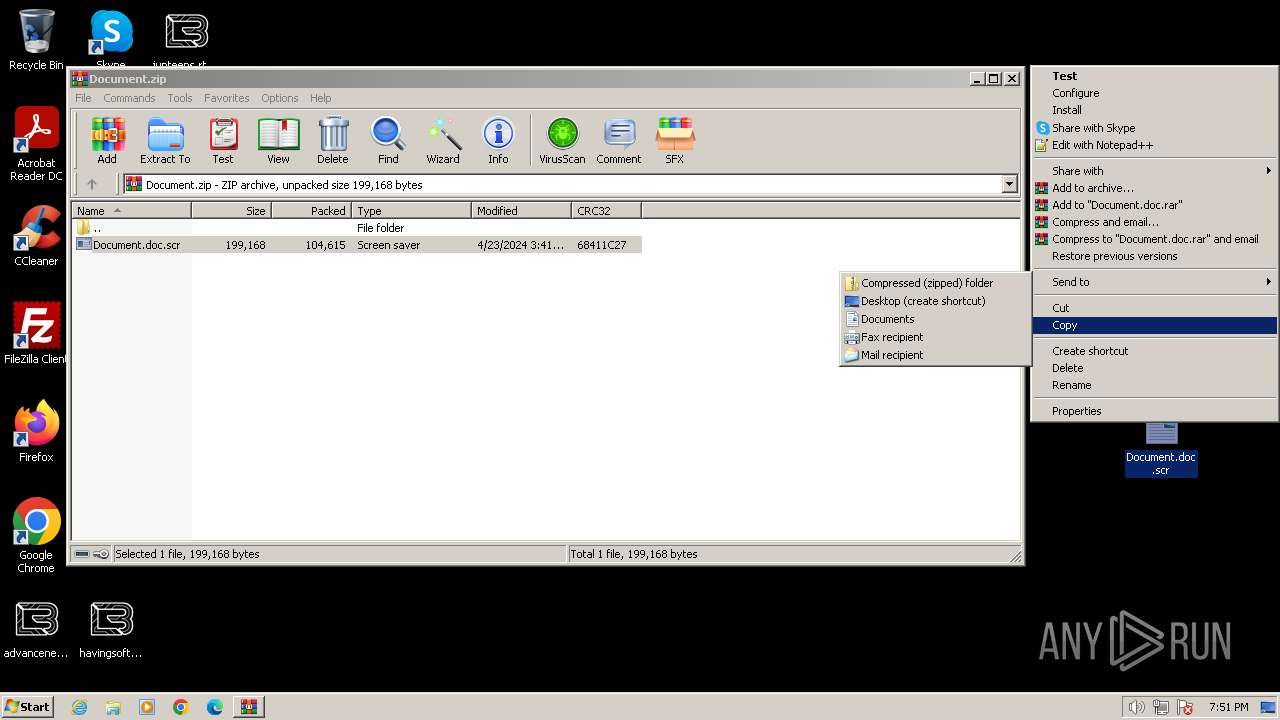
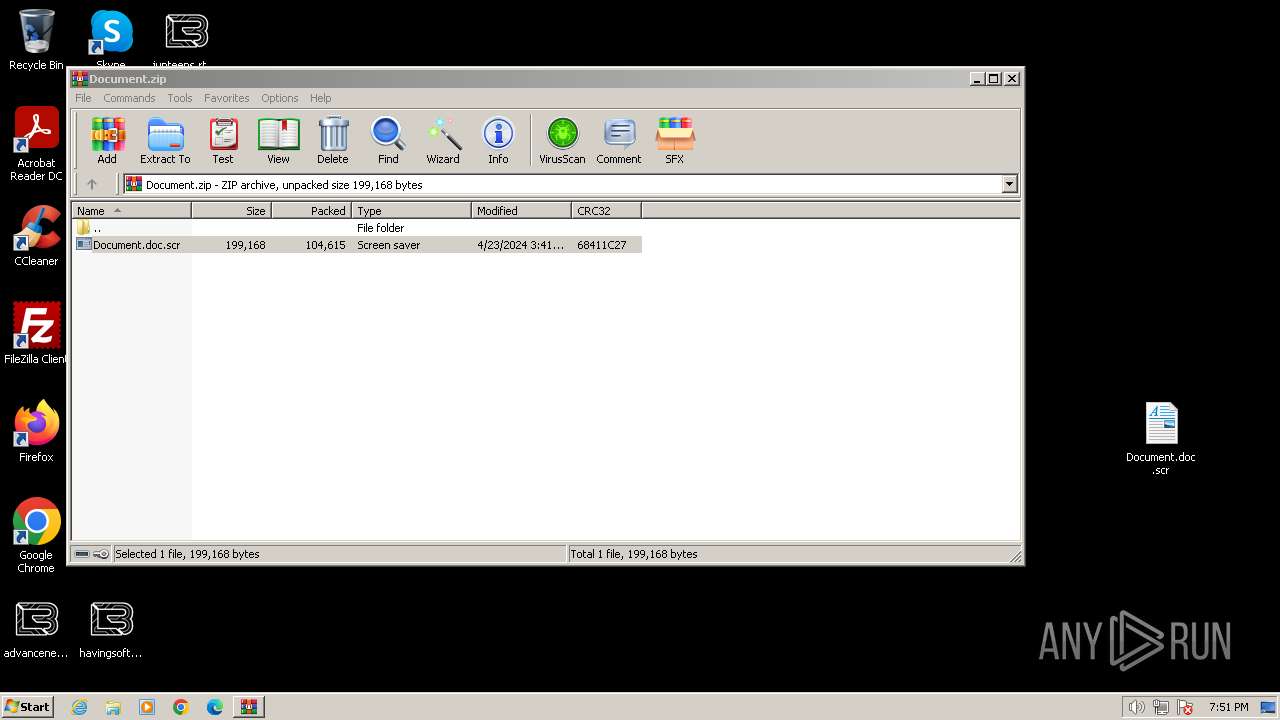
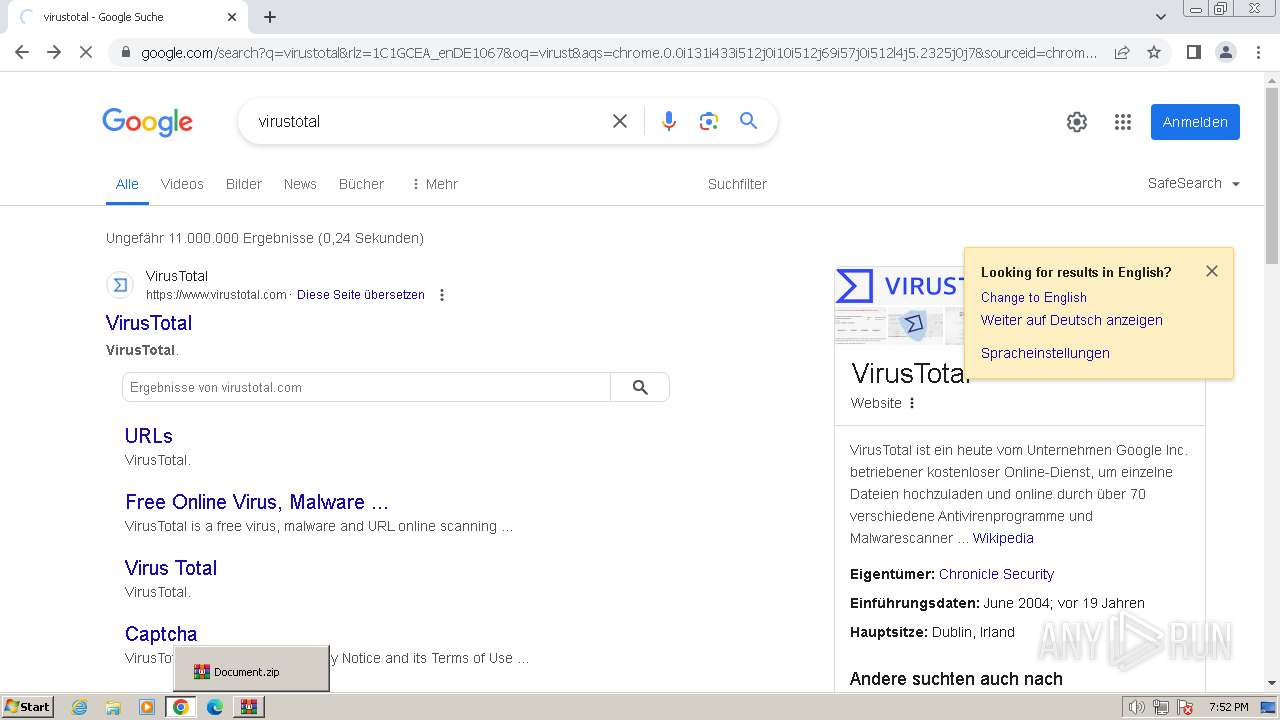
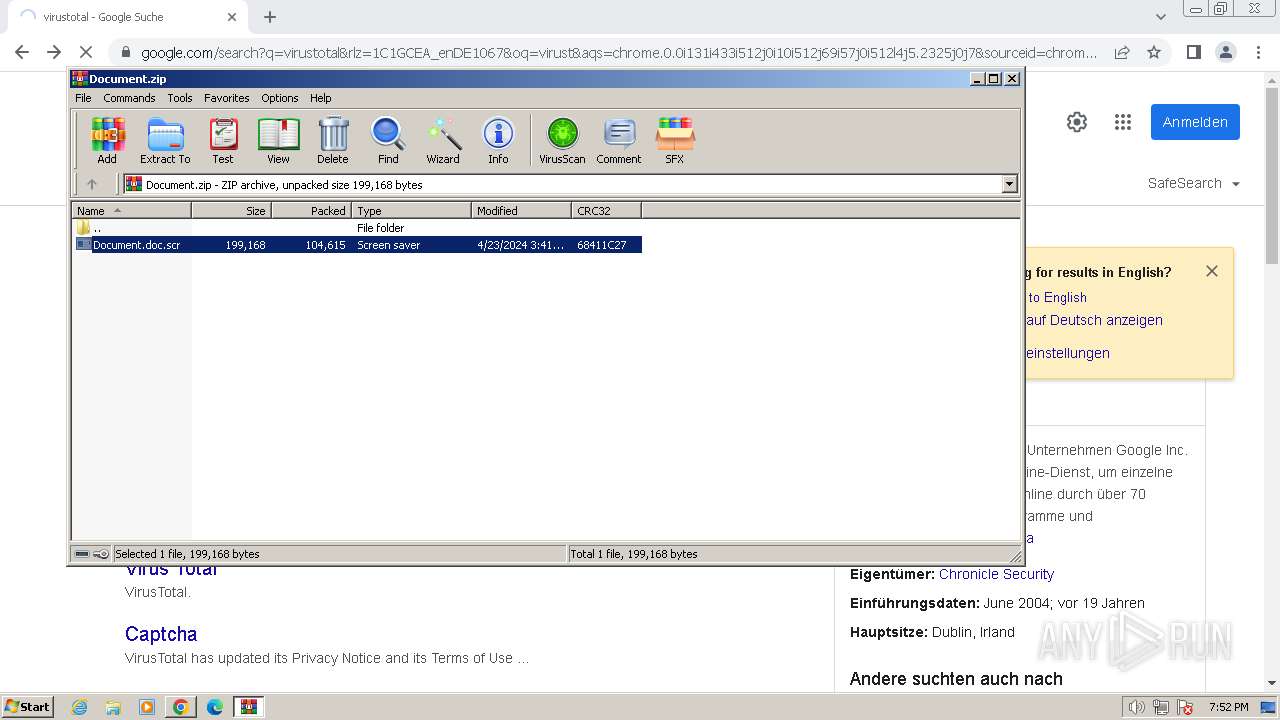
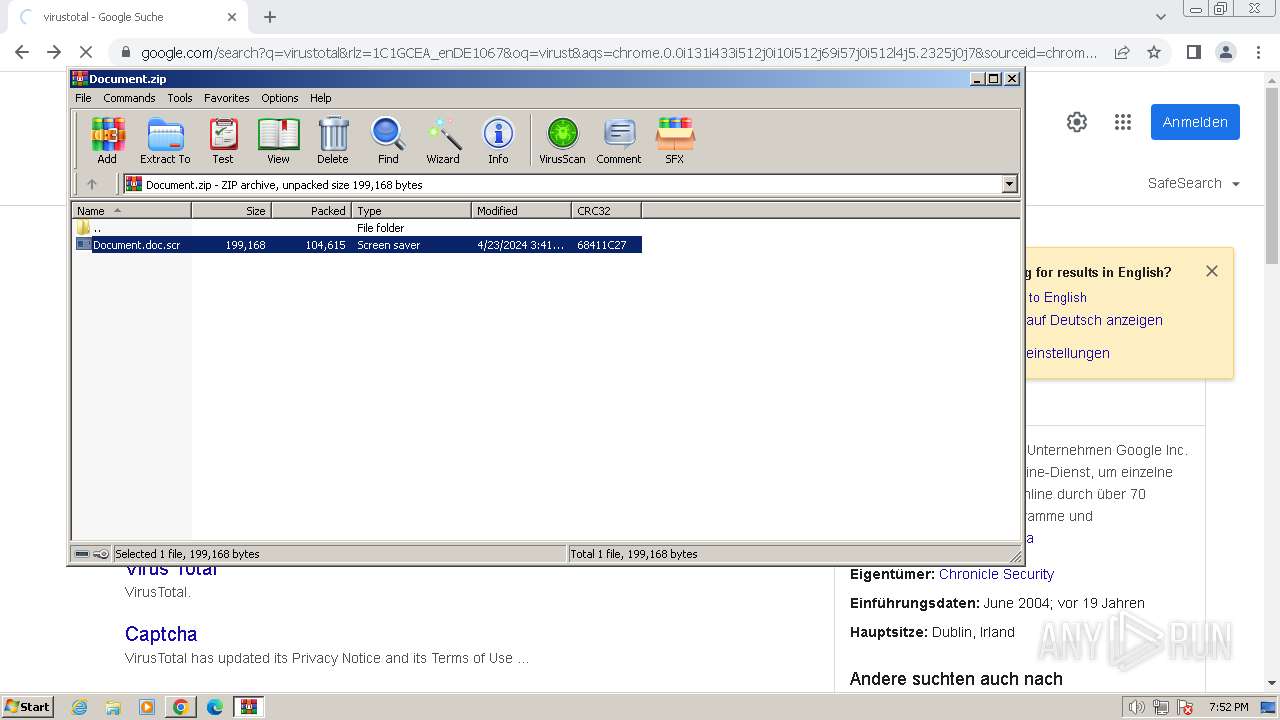
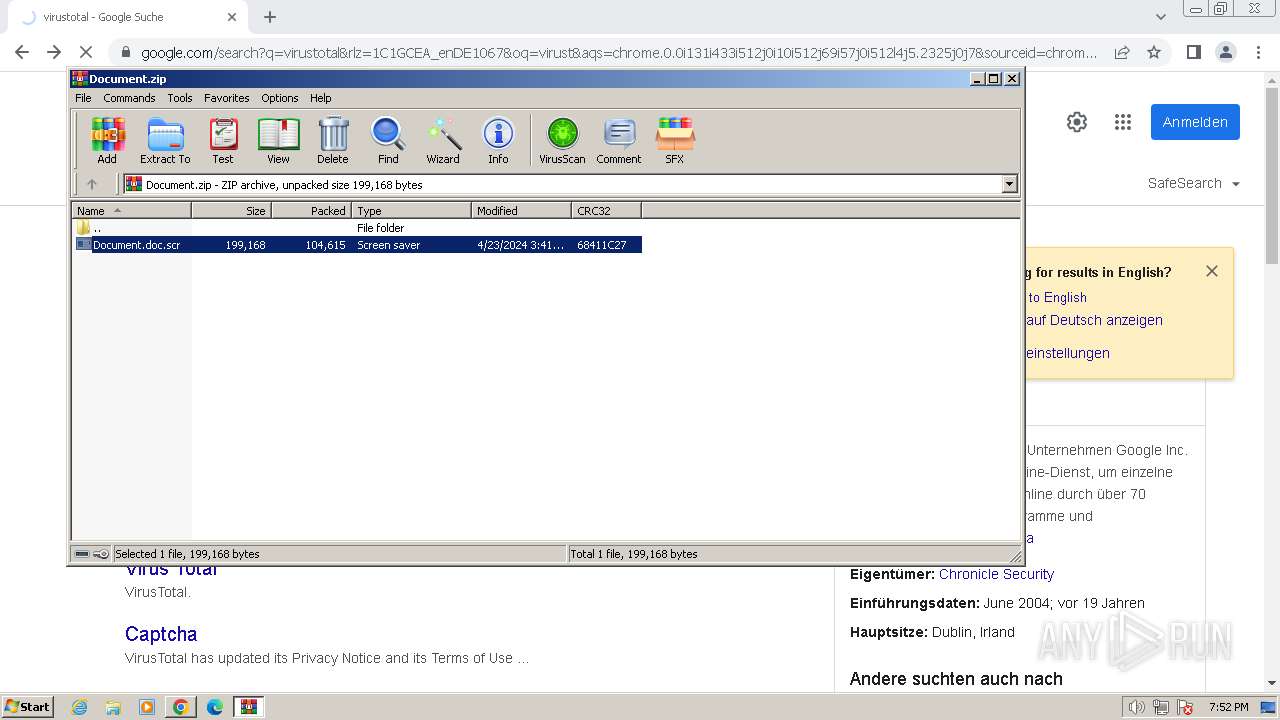
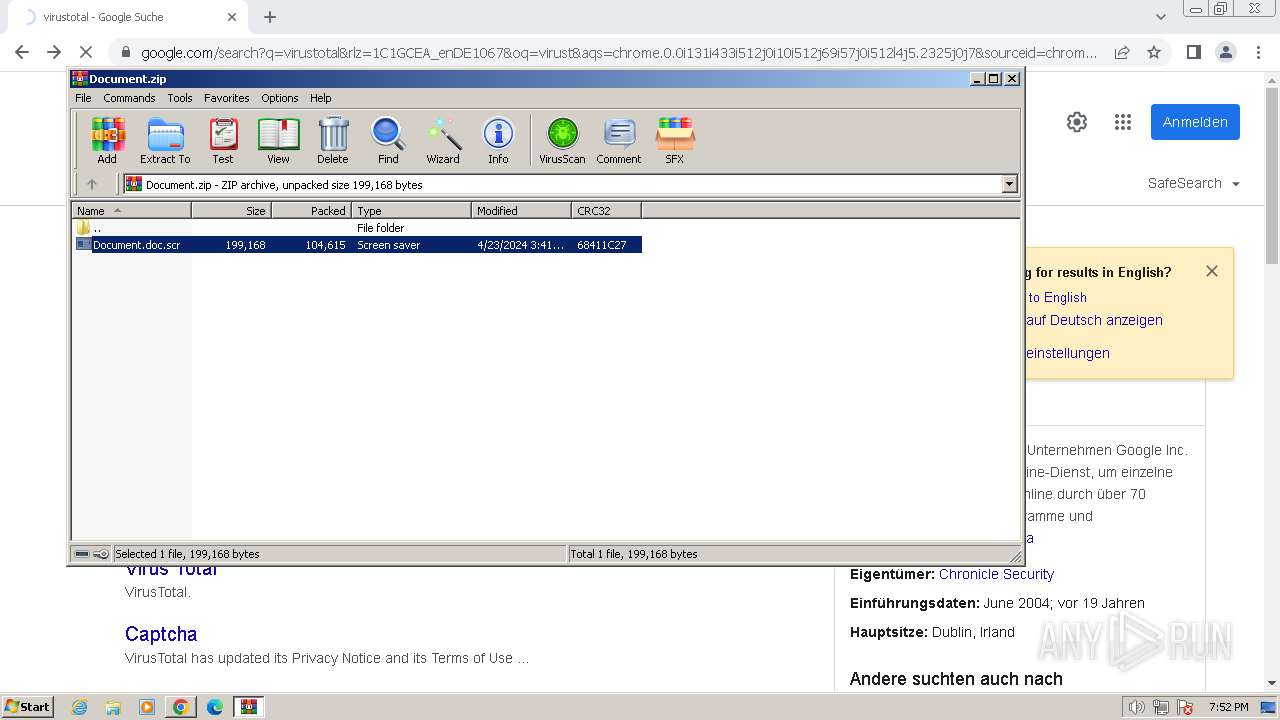
Starts application with an unusual extension
- WinRAR.exe (PID: 696)
- dllhost.exe (PID: 3404)
- Document.doc.scr (PID: 2260)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 696)
- A52D.tmp (PID: 2848)
Creates files like ransomware instruction
- Document.doc.scr (PID: 2260)
Write to the desktop.ini file (may be used to cloak folders)
- Document.doc.scr (PID: 2260)
Reads the Internet Settings
- printfilterpipelinesvc.exe (PID: 2484)
- A52D.tmp (PID: 2848)
Changes the desktop background image
- Document.doc.scr (PID: 2260)
Executable content was dropped or overwritten
- Document.doc.scr (PID: 2260)
Reads browser cookies
- Document.doc.scr (PID: 2260)
Starts CMD.EXE for commands execution
- A52D.tmp (PID: 2848)
Hides command output
- cmd.exe (PID: 3940)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 696)
The process uses the downloaded file
- WinRAR.exe (PID: 696)
- OUTLOOK.EXE (PID: 1196)
Checks supported languages
- Document.doc.scr (PID: 1560)
- Document.doc.scr (PID: 2260)
- A52D.tmp (PID: 2848)
- ONENOTE.EXE (PID: 3164)
Checks transactions between databases Windows and Oracle
- Document.doc.scr (PID: 1560)
Reads the machine GUID from the registry
- Document.doc.scr (PID: 1560)
- Document.doc.scr (PID: 2260)
- ONENOTE.EXE (PID: 3164)
Reads the computer name
- Document.doc.scr (PID: 1560)
- Document.doc.scr (PID: 2260)
- ONENOTE.EXE (PID: 3164)
- A52D.tmp (PID: 2848)
Creates files or folders in the user directory
- Document.doc.scr (PID: 2260)
- printfilterpipelinesvc.exe (PID: 2484)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 696)
Creates files in the program directory
- Document.doc.scr (PID: 2260)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 3404)
Create files in a temporary directory
- Document.doc.scr (PID: 2260)
- ONENOTE.EXE (PID: 3164)
Dropped object may contain TOR URL's
- Document.doc.scr (PID: 2260)
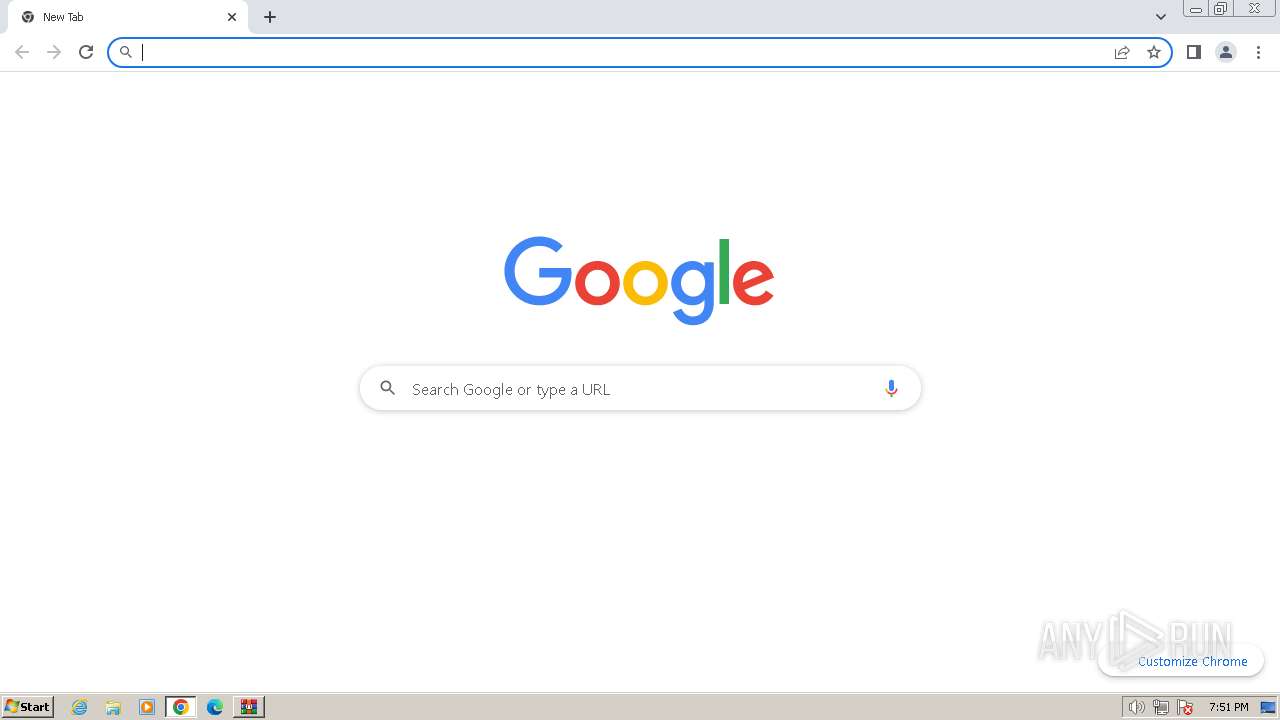
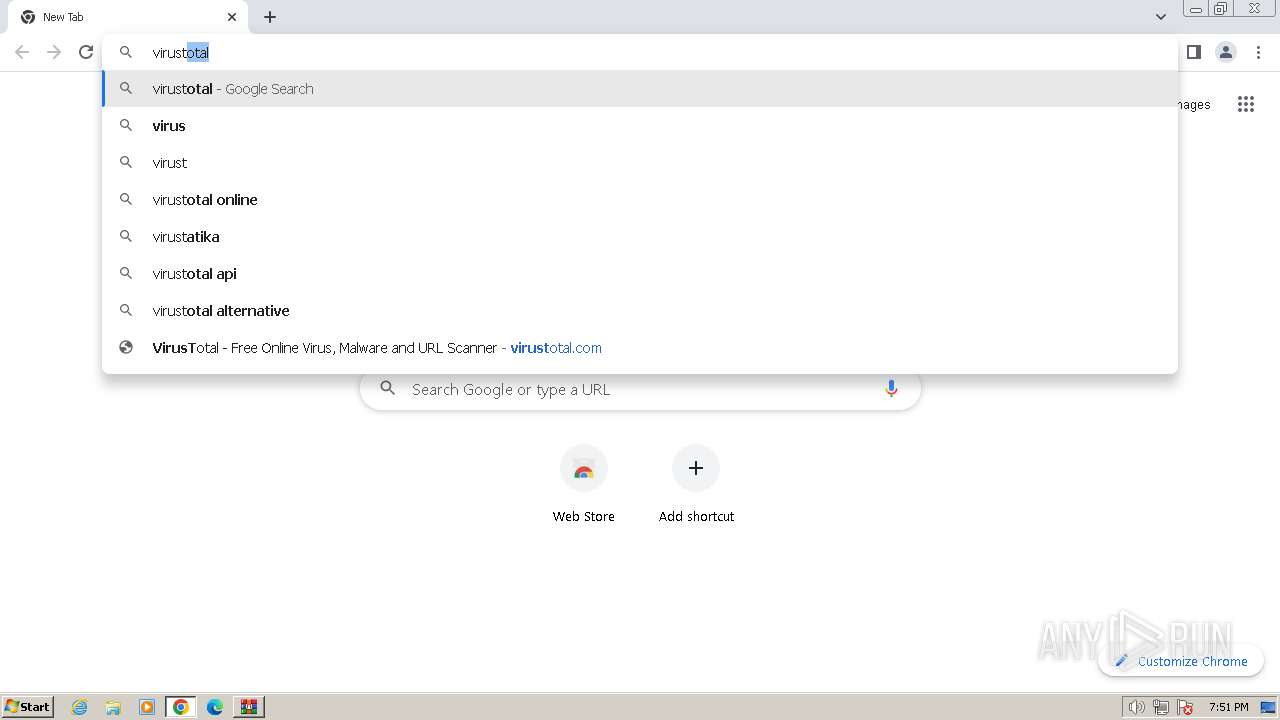
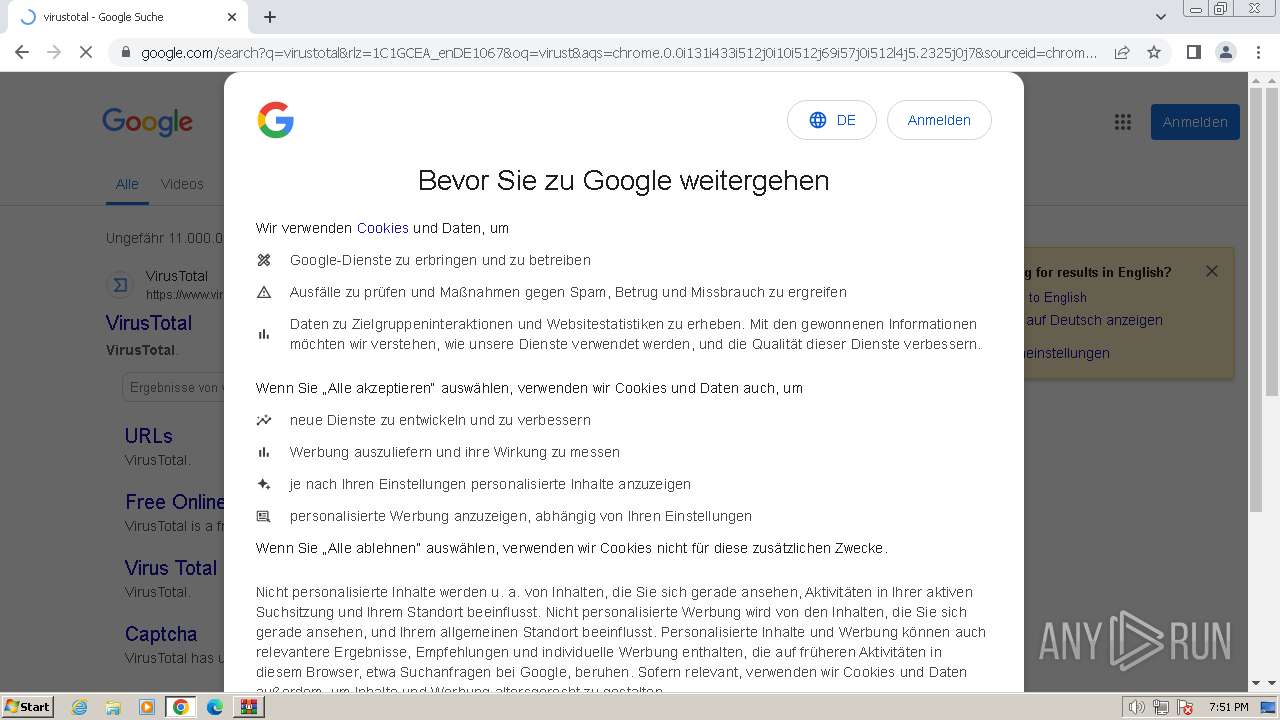
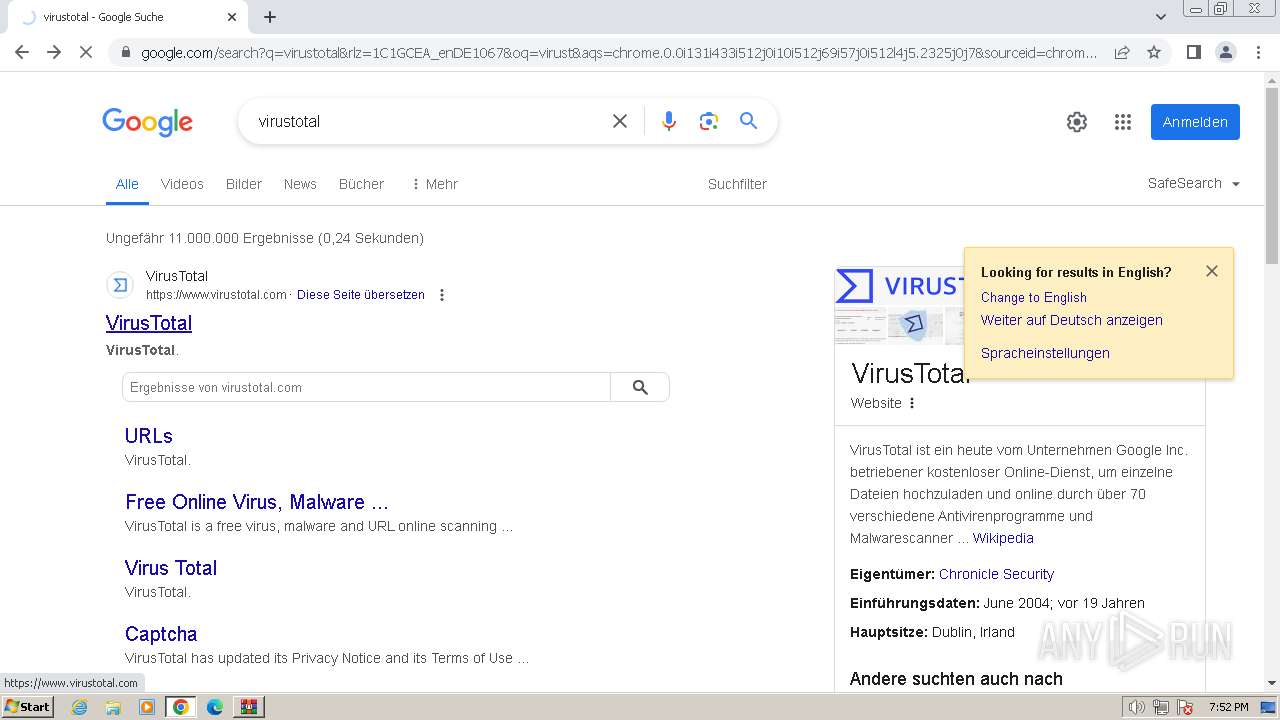
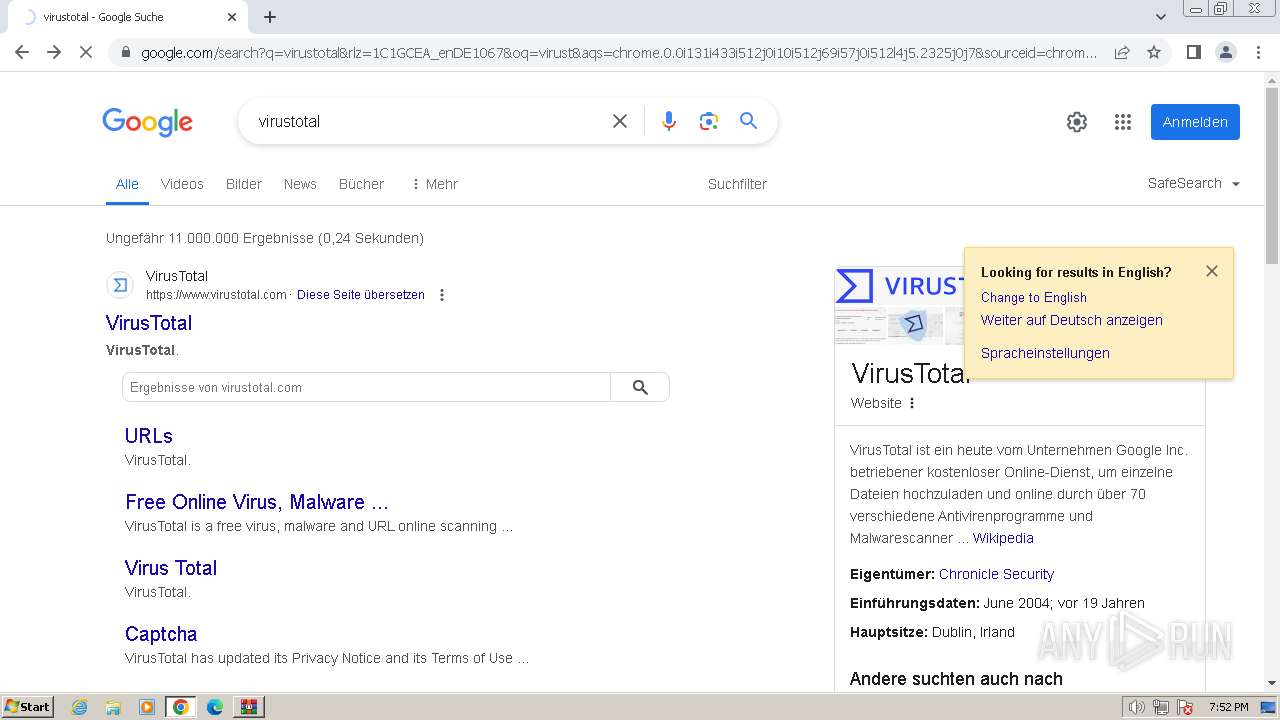
Manual execution by a user
- chrome.exe (PID: 3012)
Process checks computer location settings
- ONENOTE.EXE (PID: 3164)
Reads Environment values
- ONENOTE.EXE (PID: 3164)
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 3164)
Application launched itself
- chrome.exe (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
79
Monitored processes
28
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3372 --field-trial-handle=1160,i,2861432540257821809,2861076611158322033,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 696 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\UOWTSX3X\Document.zip" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=4116 --field-trial-handle=1160,i,2861432540257821809,2861076611158322033,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=984 --field-trial-handle=1160,i,2861432540257821809,2861076611158322033,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Virus backdoor.bdszeroaccess.gen7 Your Document.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\Temp\Rar$DIa696.45476\Document.doc.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIa696.45476\Document.doc.scr | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ba68b38,0x6ba68b48,0x6ba68b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=2624 --field-trial-handle=1160,i,2861432540257821809,2861076611158322033,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2200 --field-trial-handle=1160,i,2861432540257821809,2861076611158322033,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1280 --field-trial-handle=1160,i,2861432540257821809,2861076611158322033,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
27 601
Read events
25 849
Write events
1 689
Delete events
63
Modification events
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1196) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
4
Suspicious files
1 171
Text files
1 048
Unknown types
323
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRDCA1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:E9E152E7F3709A6D2C345898E25ABD43 | SHA256:BD1D434C956D5B2EBBA53EF1B5FFE235457ED17480EFA8B77F9E77C234401174 | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\UOWTSX3X\Document (2).zip | compressed | |
MD5:BF87F364563B7C38275E0E474D2E5E13 | SHA256:13916D6B1FDDB42F3146B641D37F3A69B491F183146E310AA972DD469E3417BF | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\UOWTSX3X\Document.zip | compressed | |
MD5:BF87F364563B7C38275E0E474D2E5E13 | SHA256:13916D6B1FDDB42F3146B641D37F3A69B491F183146E310AA972DD469E3417BF | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\UOWTSX3X\Document (2).zip:Zone.Identifier:$DATA | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 2260 | Document.doc.scr | C:\ProgramData\kZd6jLIwz.ico | image | |
MD5:88D9337C4C9CFE2D9AFF8A2C718EC76B | SHA256:95E059EF72686460884B9AEA5C292C22917F75D56FE737D43BE440F82034F438 | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\UOWTSX3X\Document.zip:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa696.45476\Document.doc.scr | executable | |
MD5:AE811BD6440B425E6777F0CA001A9743 | SHA256:86E17AA882C690EDE284F3E445439DFE589D8F36E31CBC09D102305499D5C498 | |||
| 1196 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{B88B9EF3-8563-4B9D-9EE1-757DD9E0FC22}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
43
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2812 | chrome.exe | GET | 204 | 172.217.18.3:80 | http://www.gstatic.com/generate_204 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1196 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2812 | chrome.exe | 142.250.185.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3012 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
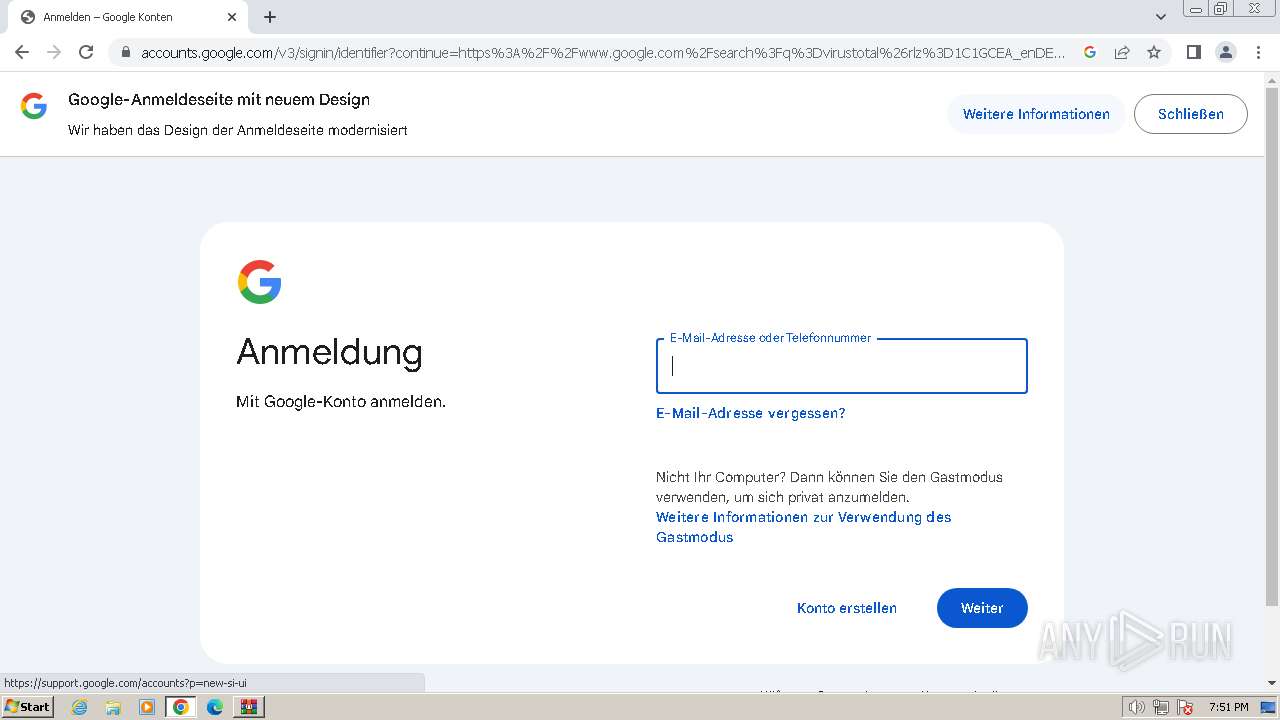
2812 | chrome.exe | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2812 | chrome.exe | 142.250.185.132:443 | www.google.com | GOOGLE | US | whitelisted |
2812 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
dns.msftncsi.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
update.googleapis.com |
| unknown |