| File name: | test |
| Full analysis: | https://app.any.run/tasks/113683c9-2ccf-4589-a034-d1221287146d |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2022, 18:42:20 |
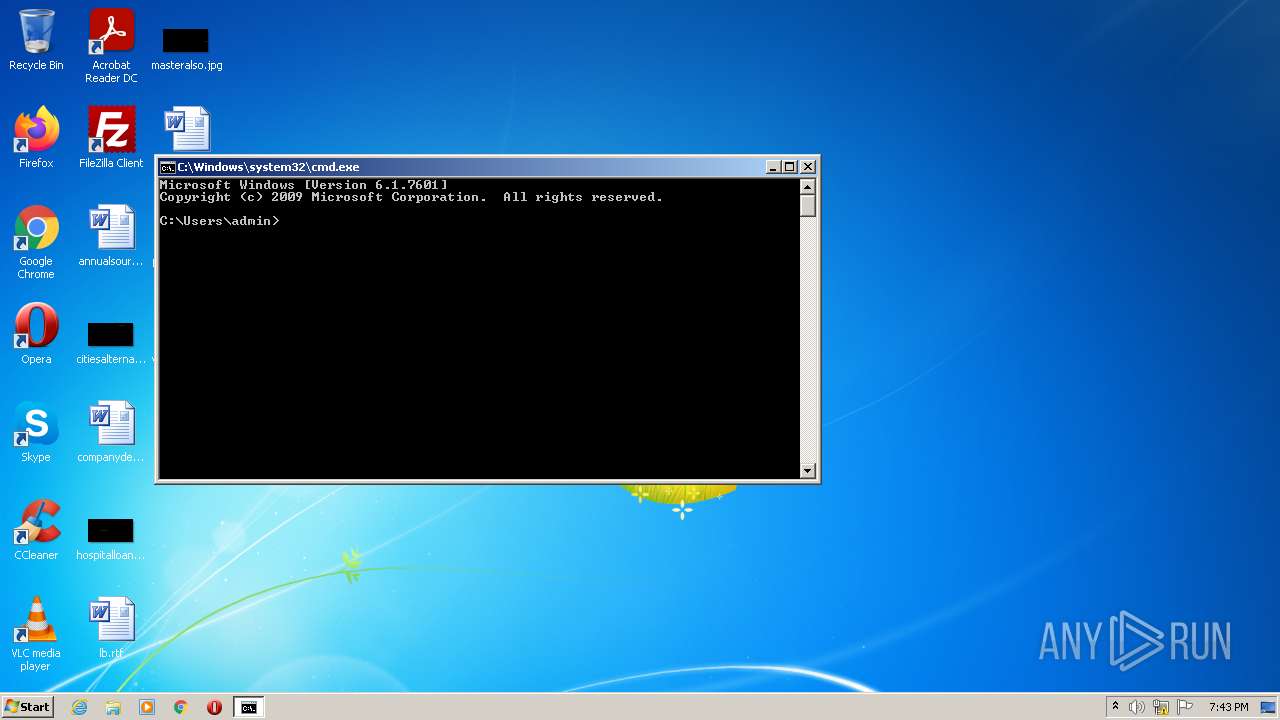
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines |
| MD5: | 0D87D4EB1326DD904D89A46505A97FEE |
| SHA1: | 921D861748CFD99C3B3DB90763892A018193EA23 |
| SHA256: | 8DFAFEDE28061407D40224A5B40D55CCE8DF62BD7124A8A9EFB0E952703E2271 |
| SSDEEP: | 6144:DvXopLp7+LE7hPxOmOSD11T/Z2CyVVxqes5bB6lzIND:DScLq25c5fyVTcAOD |
MALICIOUS
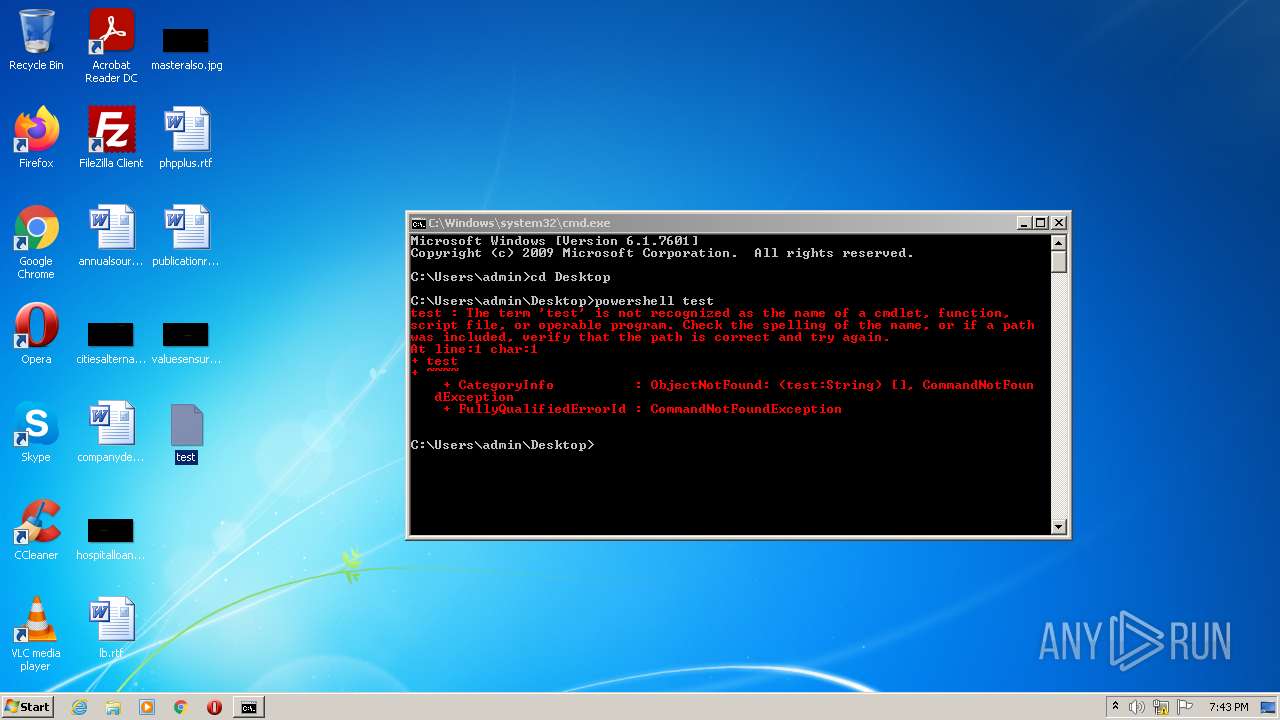
Runs app for hidden code execution
- powershell.exe (PID: 1268)
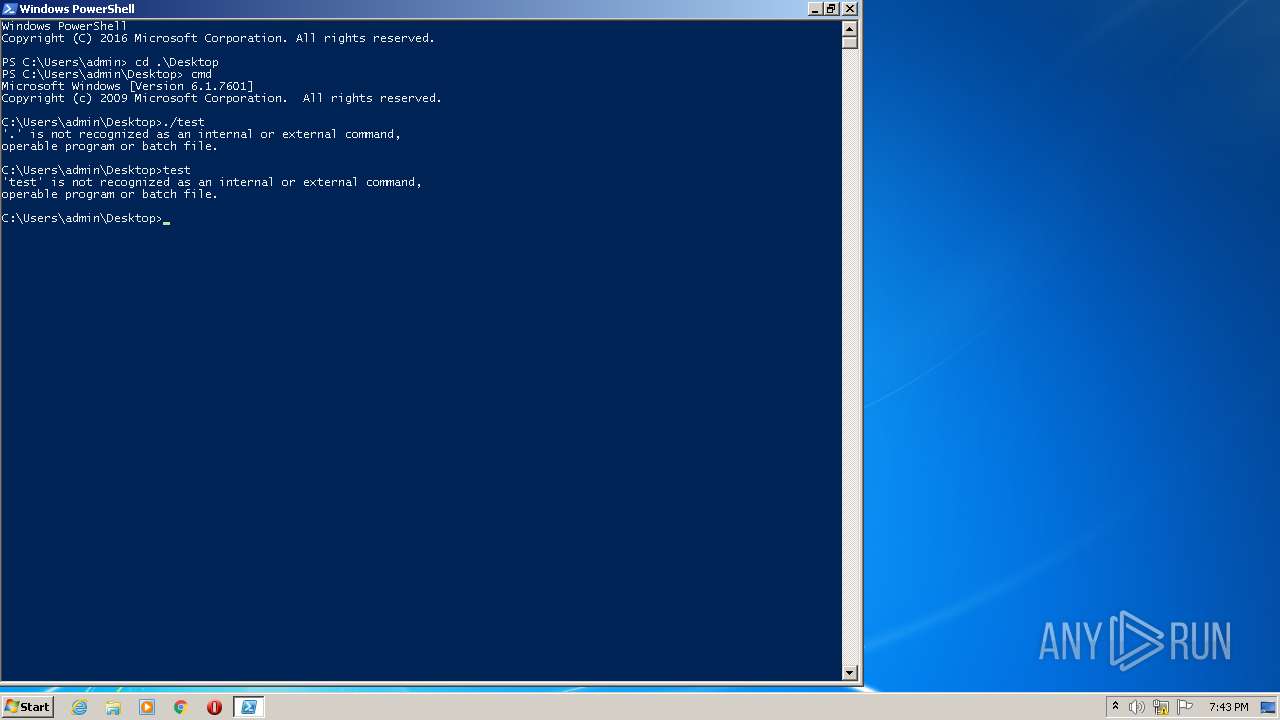
Executes PowerShell scripts
- cmd.exe (PID: 3628)
COBALT detected by memory dumps
- powershell.exe (PID: 3140)
SUSPICIOUS
Executed as Windows Service
- SearchIndexer.exe (PID: 1352)
Checks supported languages
- powershell.exe (PID: 1268)
- cmd.exe (PID: 4048)
- cmd.exe (PID: 3628)
- powershell.exe (PID: 2348)
- powershell.exe (PID: 320)
- powershell.exe (PID: 3140)
Reads the computer name
- powershell.exe (PID: 1268)
- powershell.exe (PID: 320)
- powershell.exe (PID: 3140)
- powershell.exe (PID: 2348)
Reads the date of Windows installation
- powershell.exe (PID: 1268)
- powershell.exe (PID: 3140)
Executes PowerShell scripts
- powershell.exe (PID: 1268)
- powershell.exe (PID: 3140)
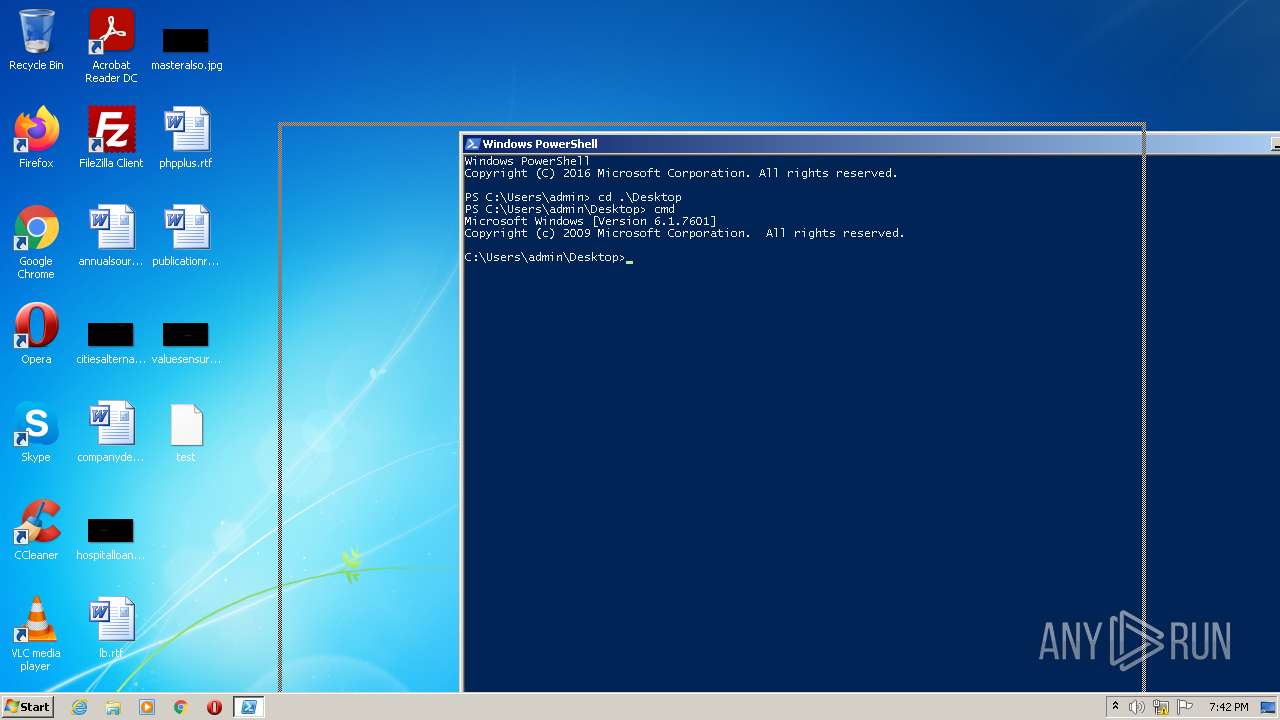
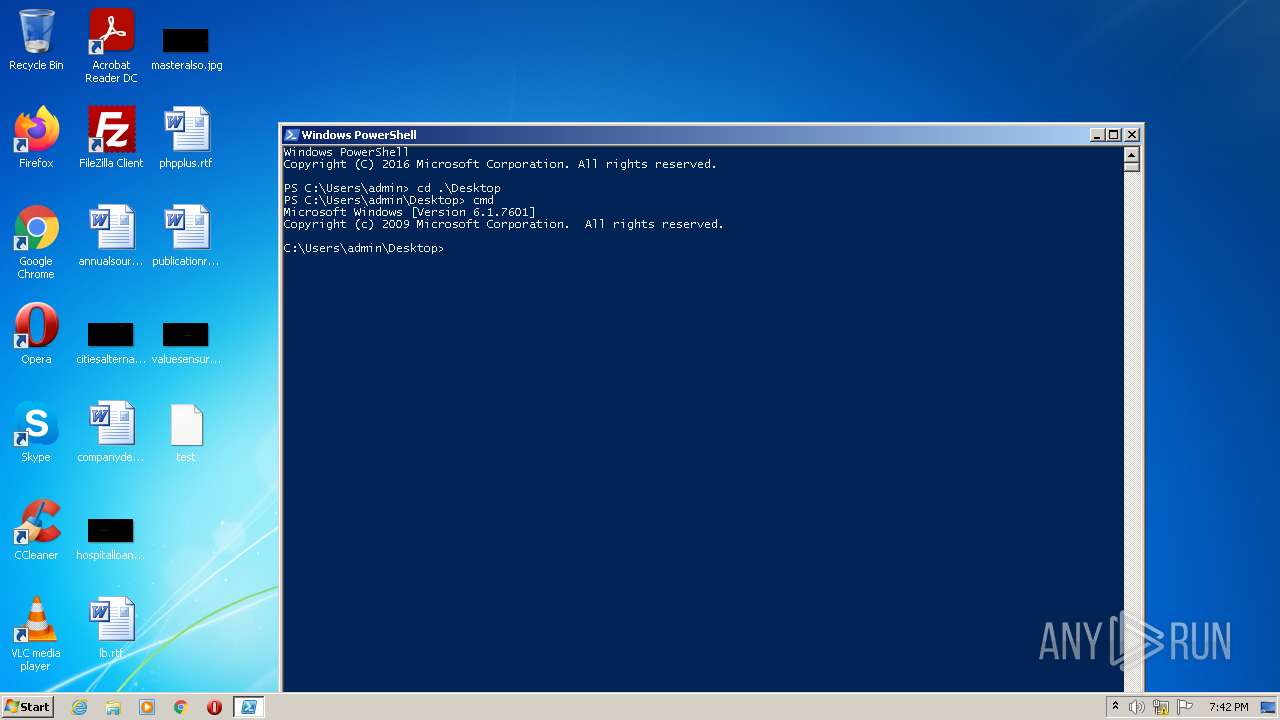
Starts CMD.EXE for commands execution
- powershell.exe (PID: 1268)
Creates files in the user directory
- powershell.exe (PID: 1268)
- powershell.exe (PID: 3140)
Creates files in the program directory
- SearchIndexer.exe (PID: 1352)
INFO
Checks supported languages
- rundll32.exe (PID: 2972)
- SearchIndexer.exe (PID: 1352)
- SearchFilterHost.exe (PID: 2532)
- SearchProtocolHost.exe (PID: 740)
- SearchProtocolHost.exe (PID: 2880)
Reads the computer name
- rundll32.exe (PID: 2972)
- SearchIndexer.exe (PID: 1352)
- SearchProtocolHost.exe (PID: 740)
- SearchFilterHost.exe (PID: 2532)
- SearchProtocolHost.exe (PID: 2880)
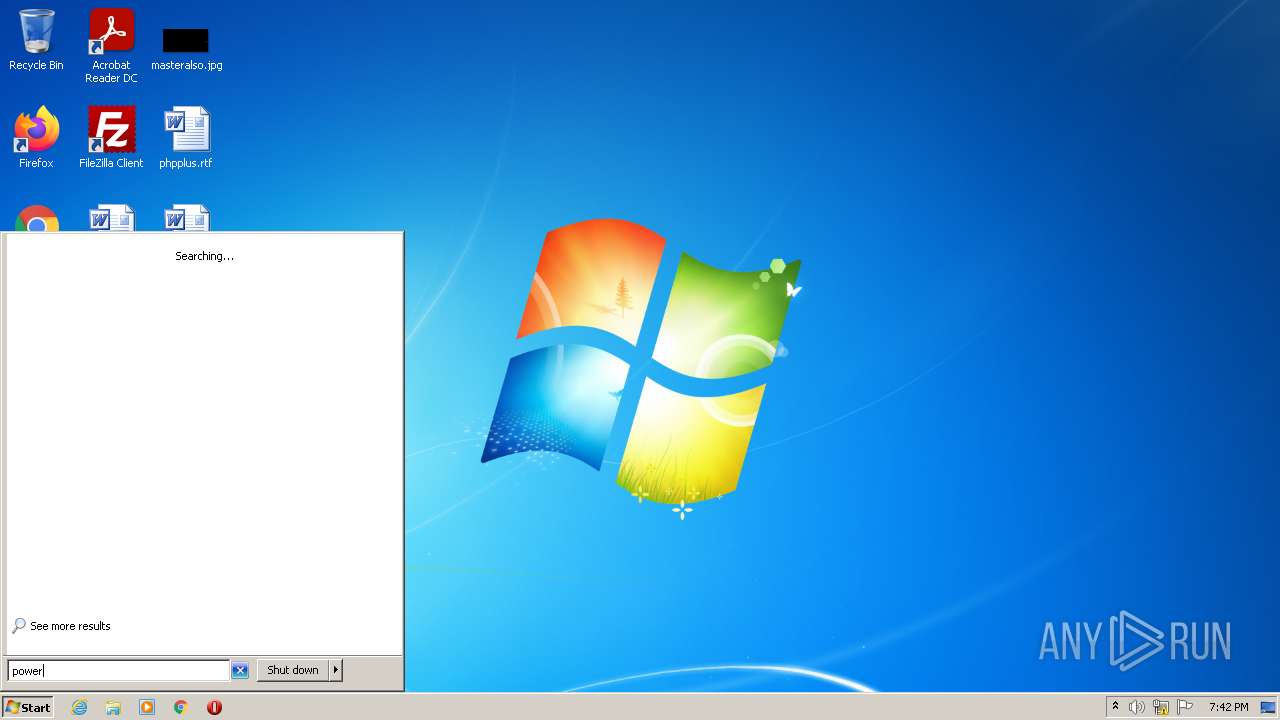
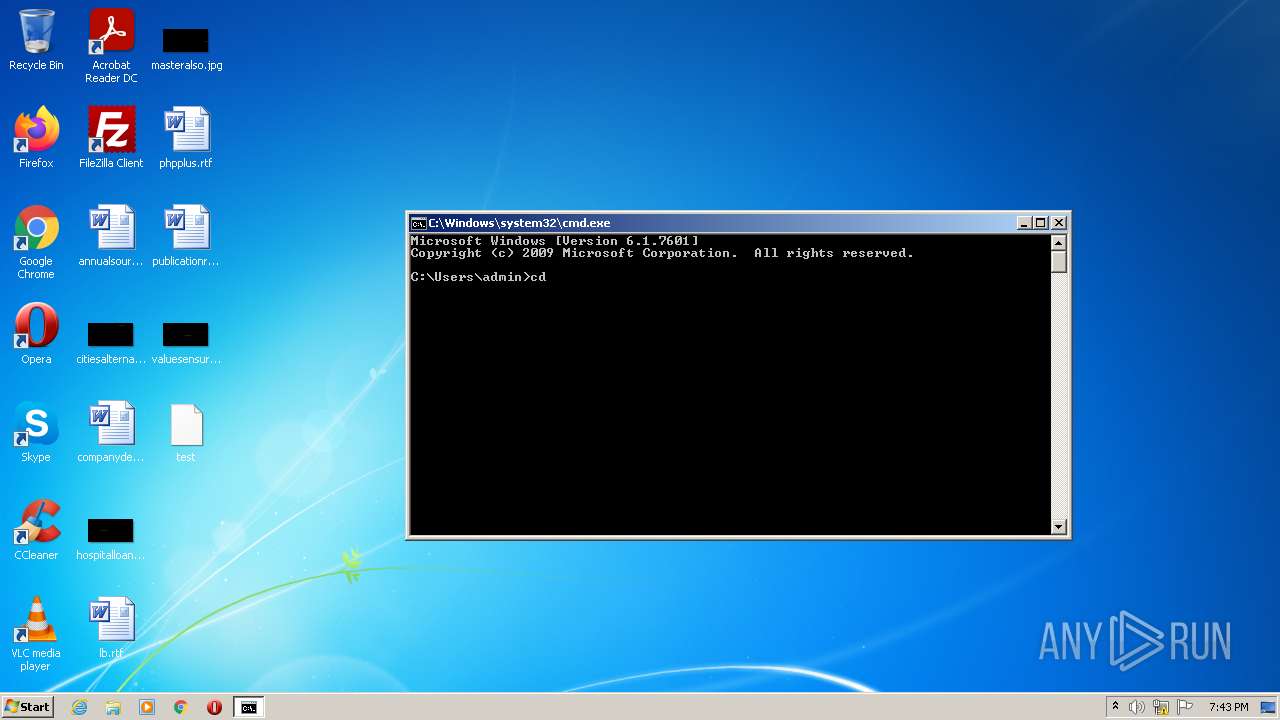
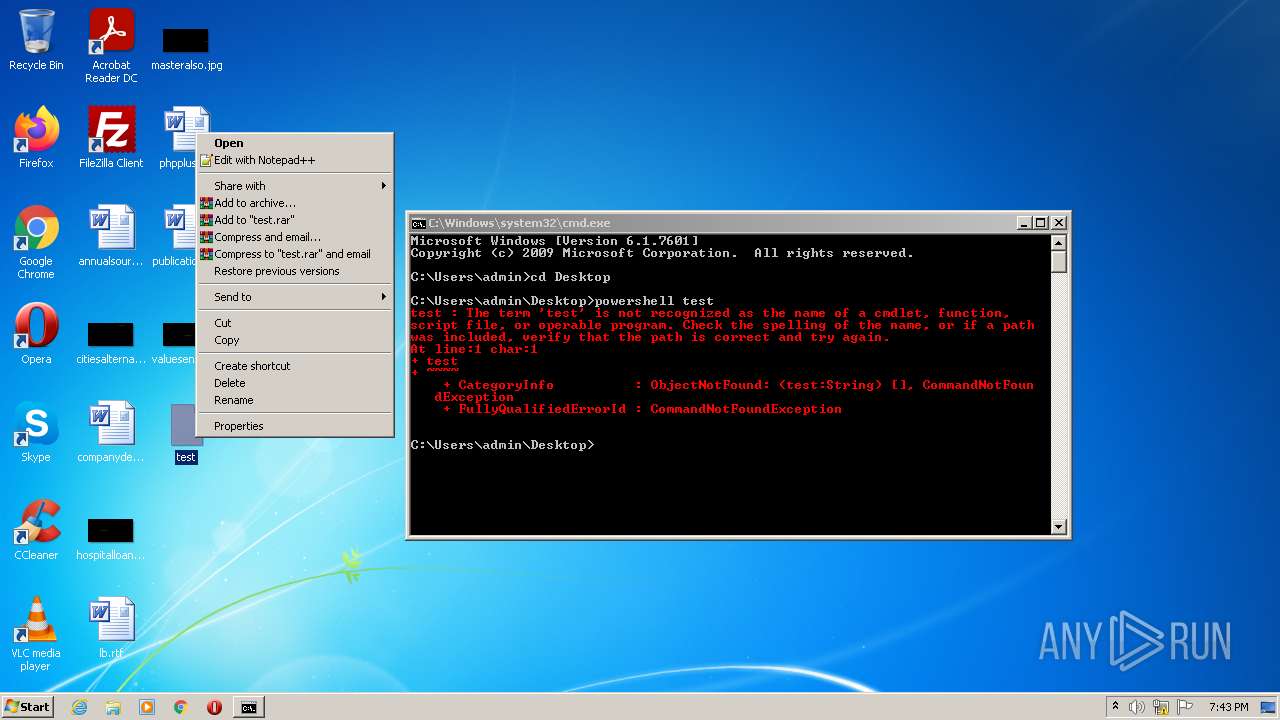
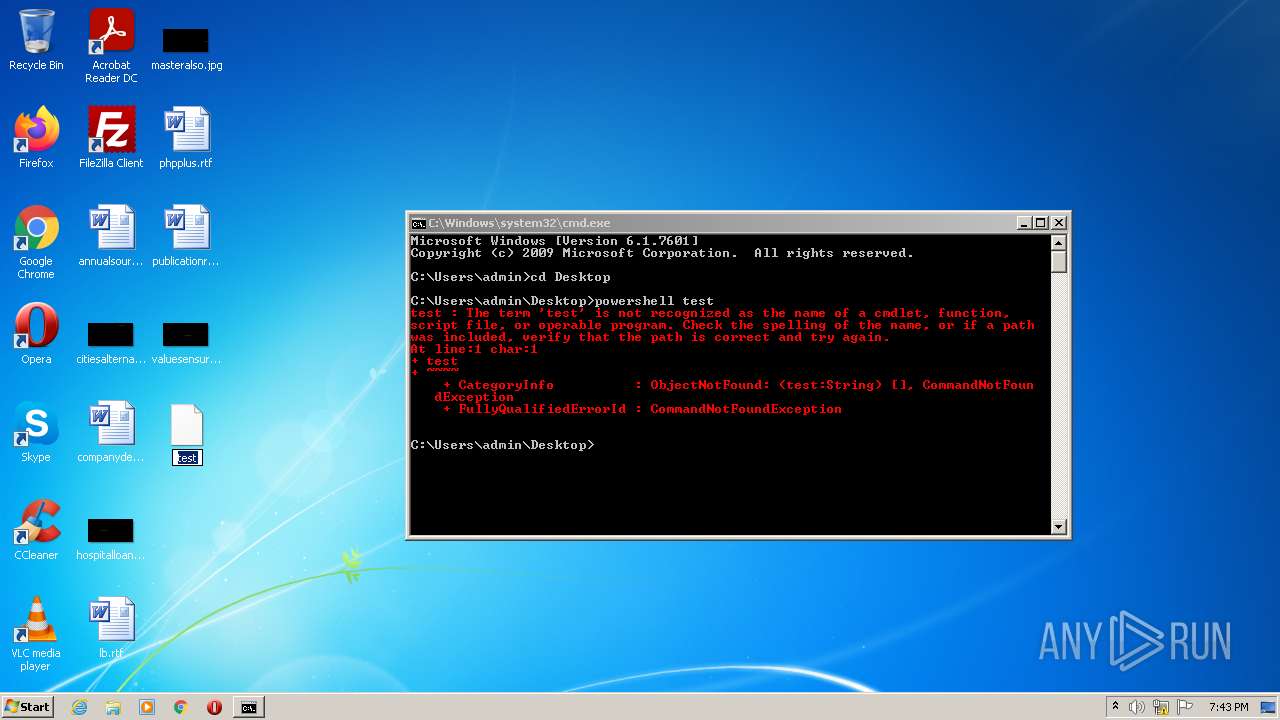
Manual execution by user
- powershell.exe (PID: 1268)
- cmd.exe (PID: 3628)
- powershell.exe (PID: 3140)
Checks Windows Trust Settings
- powershell.exe (PID: 1268)
- powershell.exe (PID: 320)
- powershell.exe (PID: 3140)
- powershell.exe (PID: 2348)
Reads settings of System Certificates
- powershell.exe (PID: 320)
- powershell.exe (PID: 3140)
- powershell.exe (PID: 2348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
CobalStrike
(PID) Process(3140) powershell.exe
C2 (1)secdisks.com/safebrowsing/rd/CltOb12nLW1IbHehcmUtd2hUdmFzEBAY7-0KIOkUDC7h2
BeaconTypeHTTPS
Port443
SleepTime30000
MaxGetSize1048576
Jitter20
PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCnOM3nXx+7HBhkbDd+AwFrFisS
unK999w2tM0uTpuuEiBalcJhcL+QgQWtf6S7zPp5hjImG+2YcPl18geU4f5JlSPX
HwilbK4DFb/ePWyKFjhrA7emVRqhM21QMlo1ANsn14rY/RO2pzuft8P7TXoIjjI/
B2GGVuzYNZX6X4I2EwIDAQAB
-----END PUBLIC KEY-----
DNS_strategyround-robin
DNS_strategy_rotate_seconds-1
DNS_strategy_fail_x-1
DNS_strategy_fail_seconds-1
SpawnTo00000000000000000000000000000000
Spawnto_x86%windir%\syswow64\rundll32.exe
Spawnto_x64%windir%\sysnative\rundll32.exe
CryptoScheme0
HttpGet_VerbGET
HttpPost_VerbPOST
HttpPostChunk0
Watermark0
bStageCleanupFalse
bCFGCautionFalse
UserAgentMozilla/5.0 (Windows NT 6.1; WOW64; Trident/7.0; rv:11.0) like Gecko
HttpPostUri/safebrowsing/rd/CINnu27nLO8hbHdfgmUtc2ihdmFyEAcY4
HttpGet_Metadata
ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
SessionId (3)netbios
prepend: PREF=ID=
header: Cookie
HttpPost_Metadata
ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
SessionId (4)netbios
prepend: U=779b64e1a7ed737a
prepend: PREF=ID=
header: Cookie
Output (1)print
bUsesCookies0001
Proxy_BehaviorUse IE settings
tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
smbFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
KillDate0-0-0
bProcInject_StartRWXTrue
bProcInject_UseRWXTrue
bProcInject_MinAllocSize0
ProcInject_PrependAppend_x86000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000...
ProcInject_PrependAppend_x64000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000...
ProcInject_Stub32cd41edf0810c5b5f498edf4731cc6d
ProcInject_AllocationMethodVirtualAllocEx
C2 (1)secdisks.com/safebrowsing/rd/CltOb12nLW1IbHehcmUtd2hUdmFzEBAY7-0KIOkUDC7h2
BeaconTypeHTTPS
Port443
SleepTime30000
MaxGetSize1048576
Jitter20
PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCnOM3nXx+7HBhkbDd+AwFrFisS
unK999w2tM0uTpuuEiBalcJhcL+QgQWtf6S7zPp5hjImG+2YcPl18geU4f5JlSPX
HwilbK4DFb/ePWyKFjhrA7emVRqhM21QMlo1ANsn14rY/RO2pzuft8P7TXoIjjI/
B2GGVuzYNZX6X4I2EwIDAQAB
-----END PUBLIC KEY-----
DNS_strategyround-robin
DNS_strategy_rotate_seconds-1
DNS_strategy_fail_x-1
DNS_strategy_fail_seconds-1
SpawnTo00000000000000000000000000000000
Spawnto_x86%windir%\syswow64\rundll32.exe
Spawnto_x64%windir%\sysnative\rundll32.exe
CryptoScheme0
HttpGet_VerbGET
HttpPost_VerbPOST
HttpPostChunk0
Watermark0
bStageCleanupFalse
bCFGCautionFalse
UserAgentMozilla/5.0 (Windows NT 6.1; WOW64; Trident/7.0; rv:11.0) like Gecko
HttpPostUri/safebrowsing/rd/CINnu27nLO8hbHdfgmUtc2ihdmFyEAcY4
HttpGet_Metadata
ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
SessionId (3)netbios
prepend: PREF=ID=
header: Cookie
HttpPost_Metadata
ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
SessionId (4)netbios
prepend: U=779b64e1a7ed737a
prepend: PREF=ID=
header: Cookie
Output (1)print
bUsesCookies0001
Proxy_BehaviorUse IE settings
tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
smbFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
KillDate0-0-0
bProcInject_StartRWXTrue
bProcInject_UseRWXTrue
bProcInject_MinAllocSize0
ProcInject_PrependAppend_x86000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000...
ProcInject_PrependAppend_x64000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000...
ProcInject_Stub32cd41edf0810c5b5f498edf4731cc6d
ProcInject_AllocationMethodVirtualAllocEx
C2 (1)secdisks.com/safebrowsing/rd/CltOb12nLW1IbHehcmUtd2hUdmFzEBAY7-0KIOkUDC7h2
BeaconTypeHTTPS
Port443
SleepTime30000
MaxGetSize1048576
Jitter20
PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCnOM3nXx+7HBhkbDd+AwFrFisS
unK999w2tM0uTpuuEiBalcJhcL+QgQWtf6S7zPp5hjImG+2YcPl18geU4f5JlSPX
HwilbK4DFb/ePWyKFjhrA7emVRqhM21QMlo1ANsn14rY/RO2pzuft8P7TXoIjjI/
B2GGVuzYNZX6X4I2EwIDAQAB
-----END PUBLIC KEY-----
DNS_strategyround-robin
DNS_strategy_rotate_seconds-1
DNS_strategy_fail_x-1
DNS_strategy_fail_seconds-1
SpawnTo00000000000000000000000000000000
Spawnto_x86%windir%\syswow64\rundll32.exe
Spawnto_x64%windir%\sysnative\rundll32.exe
CryptoScheme0
HttpGet_VerbGET
HttpPost_VerbPOST
HttpPostChunk0
Watermark0
bStageCleanupFalse
bCFGCautionFalse
UserAgentMozilla/5.0 (Windows NT 6.1; WOW64; Trident/7.0; rv:11.0) like Gecko
HttpPostUri/safebrowsing/rd/CINnu27nLO8hbHdfgmUtc2ihdmFyEAcY4
HttpGet_Metadata
ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
SessionId (3)netbios
prepend: PREF=ID=
header: Cookie
HttpPost_Metadata
ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
SessionId (4)netbios
prepend: U=779b64e1a7ed737a
prepend: PREF=ID=
header: Cookie
Output (1)print
bUsesCookies0001
Proxy_BehaviorUse IE settings
tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
smbFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
KillDate0-0-0
bProcInject_StartRWXTrue
bProcInject_UseRWXTrue
bProcInject_MinAllocSize0
ProcInject_PrependAppend_x86000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000...
ProcInject_PrependAppend_x64000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000...
ProcInject_Stub32cd41edf0810c5b5f498edf4731cc6d
ProcInject_AllocationMethodVirtualAllocEx
Total processes
49
Monitored processes
11
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
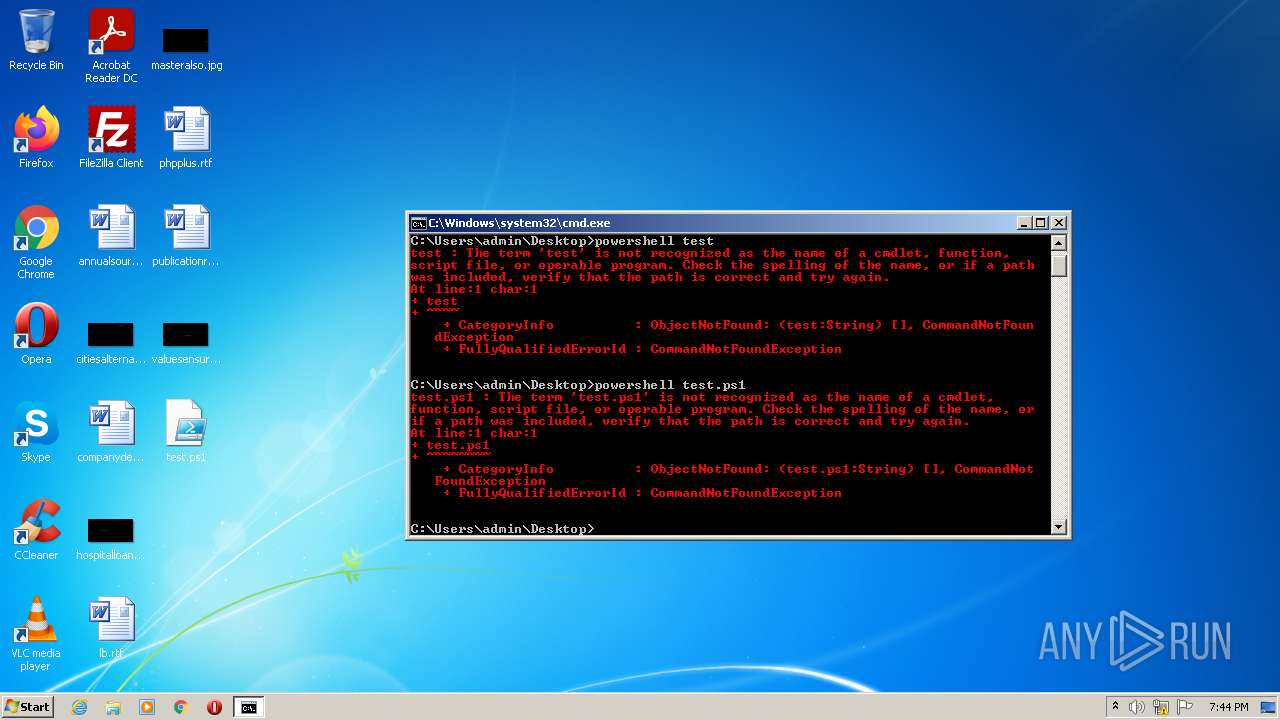
| 320 | powershell test.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 740 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe1_ Global\UsGthrCtrlFltPipeMssGthrPipe1 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 1268 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1352 | C:\Windows\system32\SearchIndexer.exe /Embedding | C:\Windows\system32\SearchIndexer.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2348 | powershell test | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2532 | "C:\Windows\system32\SearchFilterHost.exe" 0 520 524 532 65536 528 | C:\Windows\system32\SearchFilterHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Filter Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 2880 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10002_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10002 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
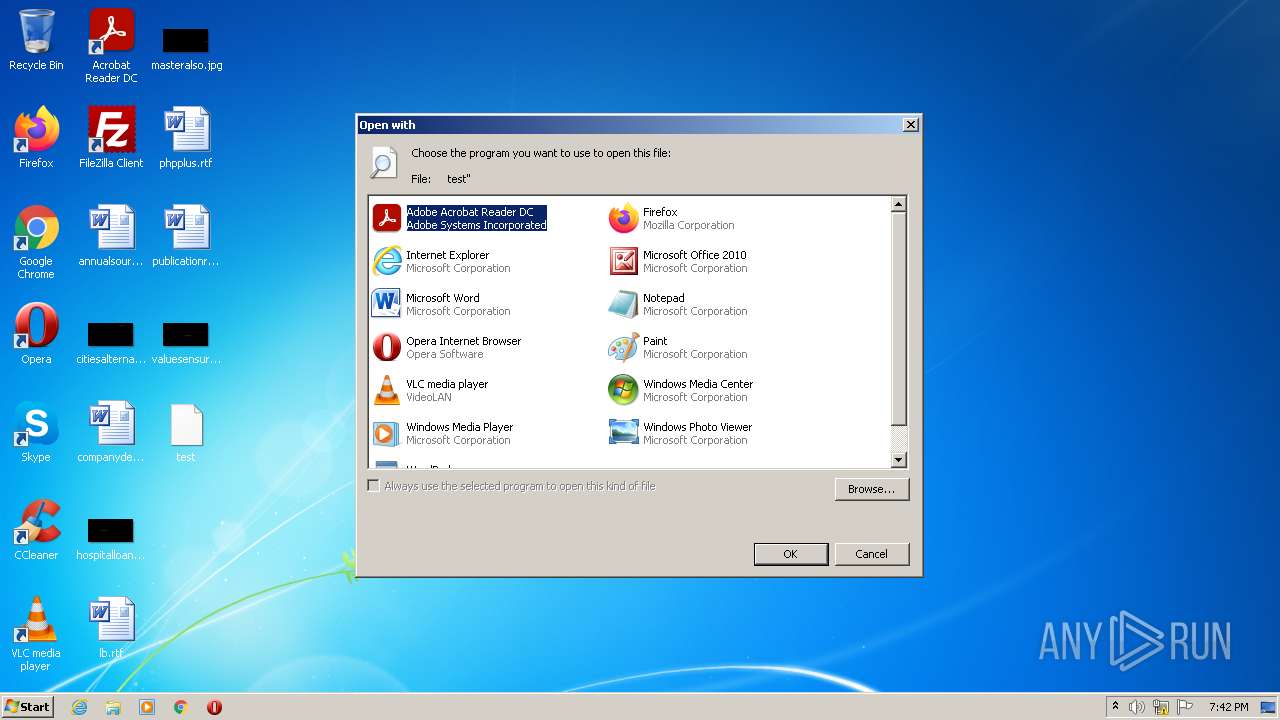
| 2972 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\Desktop\test" | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
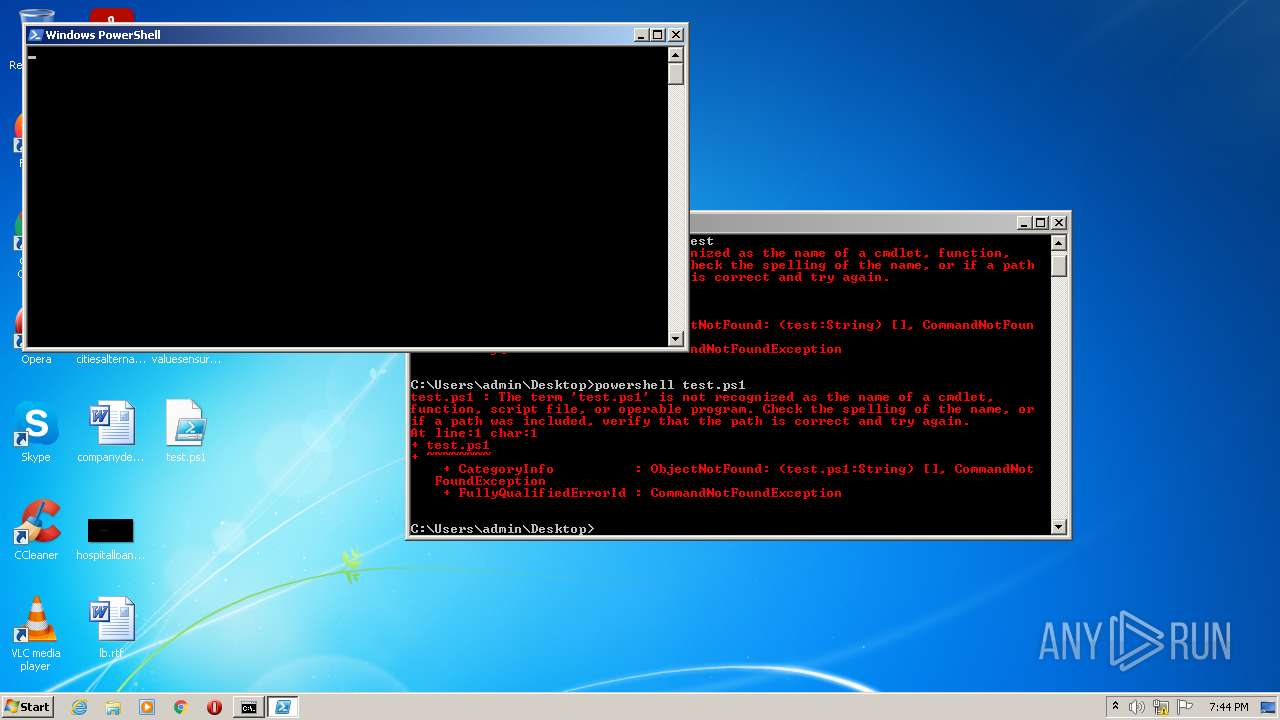
| 3140 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\test.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
CobalStrike(PID) Process(3140) powershell.exe C2 (1)secdisks.com/safebrowsing/rd/CltOb12nLW1IbHehcmUtd2hUdmFzEBAY7-0KIOkUDC7h2 BeaconTypeHTTPS Port443 SleepTime30000 MaxGetSize1048576 Jitter20 PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCnOM3nXx+7HBhkbDd+AwFrFisS
unK999w2tM0uTpuuEiBalcJhcL+QgQWtf6S7zPp5hjImG+2YcPl18geU4f5JlSPX
HwilbK4DFb/ePWyKFjhrA7emVRqhM21QMlo1ANsn14rY/RO2pzuft8P7TXoIjjI/
B2GGVuzYNZX6X4I2EwIDAQAB
-----END PUBLIC KEY----- DNS_strategyround-robin DNS_strategy_rotate_seconds-1 DNS_strategy_fail_x-1 DNS_strategy_fail_seconds-1 SpawnTo00000000000000000000000000000000 Spawnto_x86%windir%\syswow64\rundll32.exe Spawnto_x64%windir%\sysnative\rundll32.exe CryptoScheme0 HttpGet_VerbGET HttpPost_VerbPOST HttpPostChunk0 Watermark0 bStageCleanupFalse bCFGCautionFalse UserAgentMozilla/5.0 (Windows NT 6.1; WOW64; Trident/7.0; rv:11.0) like Gecko HttpPostUri/safebrowsing/rd/CINnu27nLO8hbHdfgmUtc2ihdmFyEAcY4 HttpGet_Metadata ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate SessionId (3)netbios prepend: PREF=ID= header: Cookie HttpPost_Metadata ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate SessionId (4)netbios prepend: U=779b64e1a7ed737a prepend: PREF=ID= header: Cookie Output (1)print bUsesCookies0001 Proxy_BehaviorUse IE settings tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 smbFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 KillDate0-0-0 bProcInject_StartRWXTrue bProcInject_UseRWXTrue bProcInject_MinAllocSize0 ProcInject_PrependAppend_x86000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000... ProcInject_PrependAppend_x64000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000... ProcInject_Stub32cd41edf0810c5b5f498edf4731cc6d ProcInject_AllocationMethodVirtualAllocEx (PID) Process(3140) powershell.exe C2 (1)secdisks.com/safebrowsing/rd/CltOb12nLW1IbHehcmUtd2hUdmFzEBAY7-0KIOkUDC7h2 BeaconTypeHTTPS Port443 SleepTime30000 MaxGetSize1048576 Jitter20 PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCnOM3nXx+7HBhkbDd+AwFrFisS
unK999w2tM0uTpuuEiBalcJhcL+QgQWtf6S7zPp5hjImG+2YcPl18geU4f5JlSPX
HwilbK4DFb/ePWyKFjhrA7emVRqhM21QMlo1ANsn14rY/RO2pzuft8P7TXoIjjI/
B2GGVuzYNZX6X4I2EwIDAQAB
-----END PUBLIC KEY----- DNS_strategyround-robin DNS_strategy_rotate_seconds-1 DNS_strategy_fail_x-1 DNS_strategy_fail_seconds-1 SpawnTo00000000000000000000000000000000 Spawnto_x86%windir%\syswow64\rundll32.exe Spawnto_x64%windir%\sysnative\rundll32.exe CryptoScheme0 HttpGet_VerbGET HttpPost_VerbPOST HttpPostChunk0 Watermark0 bStageCleanupFalse bCFGCautionFalse UserAgentMozilla/5.0 (Windows NT 6.1; WOW64; Trident/7.0; rv:11.0) like Gecko HttpPostUri/safebrowsing/rd/CINnu27nLO8hbHdfgmUtc2ihdmFyEAcY4 HttpGet_Metadata ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate SessionId (3)netbios prepend: PREF=ID= header: Cookie HttpPost_Metadata ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate SessionId (4)netbios prepend: U=779b64e1a7ed737a prepend: PREF=ID= header: Cookie Output (1)print bUsesCookies0001 Proxy_BehaviorUse IE settings tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 smbFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 KillDate0-0-0 bProcInject_StartRWXTrue bProcInject_UseRWXTrue bProcInject_MinAllocSize0 ProcInject_PrependAppend_x86000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000... ProcInject_PrependAppend_x64000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000... ProcInject_Stub32cd41edf0810c5b5f498edf4731cc6d ProcInject_AllocationMethodVirtualAllocEx (PID) Process(3140) powershell.exe C2 (1)secdisks.com/safebrowsing/rd/CltOb12nLW1IbHehcmUtd2hUdmFzEBAY7-0KIOkUDC7h2 BeaconTypeHTTPS Port443 SleepTime30000 MaxGetSize1048576 Jitter20 PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCnOM3nXx+7HBhkbDd+AwFrFisS
unK999w2tM0uTpuuEiBalcJhcL+QgQWtf6S7zPp5hjImG+2YcPl18geU4f5JlSPX
HwilbK4DFb/ePWyKFjhrA7emVRqhM21QMlo1ANsn14rY/RO2pzuft8P7TXoIjjI/
B2GGVuzYNZX6X4I2EwIDAQAB
-----END PUBLIC KEY----- DNS_strategyround-robin DNS_strategy_rotate_seconds-1 DNS_strategy_fail_x-1 DNS_strategy_fail_seconds-1 SpawnTo00000000000000000000000000000000 Spawnto_x86%windir%\syswow64\rundll32.exe Spawnto_x64%windir%\sysnative\rundll32.exe CryptoScheme0 HttpGet_VerbGET HttpPost_VerbPOST HttpPostChunk0 Watermark0 bStageCleanupFalse bCFGCautionFalse UserAgentMozilla/5.0 (Windows NT 6.1; WOW64; Trident/7.0; rv:11.0) like Gecko HttpPostUri/safebrowsing/rd/CINnu27nLO8hbHdfgmUtc2ihdmFyEAcY4 HttpGet_Metadata ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate SessionId (3)netbios prepend: PREF=ID= header: Cookie HttpPost_Metadata ConstHeaders (3)Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate SessionId (4)netbios prepend: U=779b64e1a7ed737a prepend: PREF=ID= header: Cookie Output (1)print bUsesCookies0001 Proxy_BehaviorUse IE settings tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 smbFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 KillDate0-0-0 bProcInject_StartRWXTrue bProcInject_UseRWXTrue bProcInject_MinAllocSize0 ProcInject_PrependAppend_x86000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000... ProcInject_PrependAppend_x64000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000... ProcInject_Stub32cd41edf0810c5b5f498edf4731cc6d ProcInject_AllocationMethodVirtualAllocEx | |||||||||||||||
| 3628 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
15 627
Read events
15 308
Write events
316
Delete events
3
Modification events
| (PID) Process: | (2972) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2972) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: Firefox | |||
| (PID) Process: | (2972) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2972) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2972) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2972) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2972) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2972) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (2972) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (2972) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
19
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1352 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\tmp.edb | — | |
MD5:— | SHA256:— | |||
| 1268 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 1268 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X0A9FVSHA54IZAEFNB4X.temp | binary | |
MD5:— | SHA256:— | |||
| 1268 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1268 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ujt1oii0.ipm.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2348 | powershell.exe | C:\Users\admin\AppData\Local\Temp\i0yck2kd.ur0.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1268 | powershell.exe | C:\Users\admin\AppData\Local\Temp\t1bhwg4a.ck4.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2348 | powershell.exe | C:\Users\admin\AppData\Local\Temp\pho4wdua.mcg.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1352 | SearchIndexer.exe | C:\programdata\microsoft\search\data\applications\windows\projects\systemindex\indexer\cifiles\00010010.wid | binary | |
MD5:— | SHA256:— | |||
| 1352 | SearchIndexer.exe | C:\programdata\microsoft\search\data\applications\windows\projects\systemindex\indexer\cifiles\00010010.ci | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3140 | powershell.exe | 91.195.240.117:443 | secdisks.com | SEDO GmbH | DE | malicious |
— | — | 91.195.240.117:443 | secdisks.com | SEDO GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
secdisks.com |
| malicious |